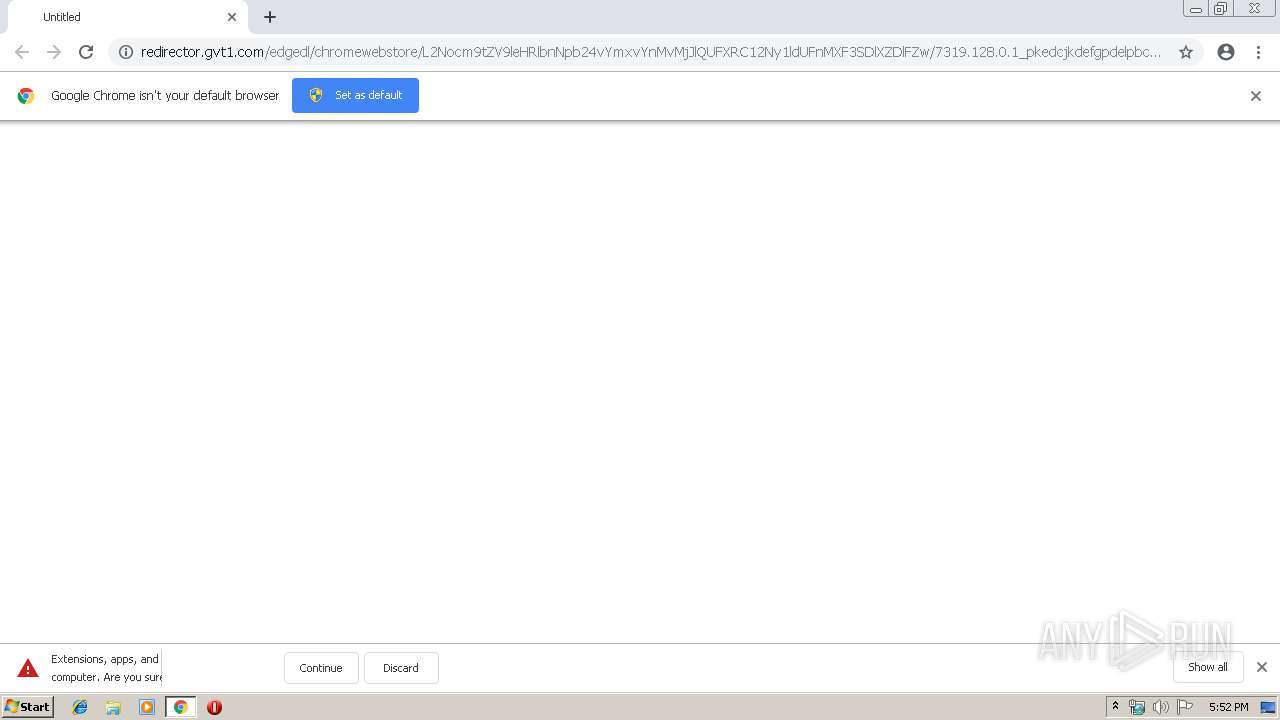
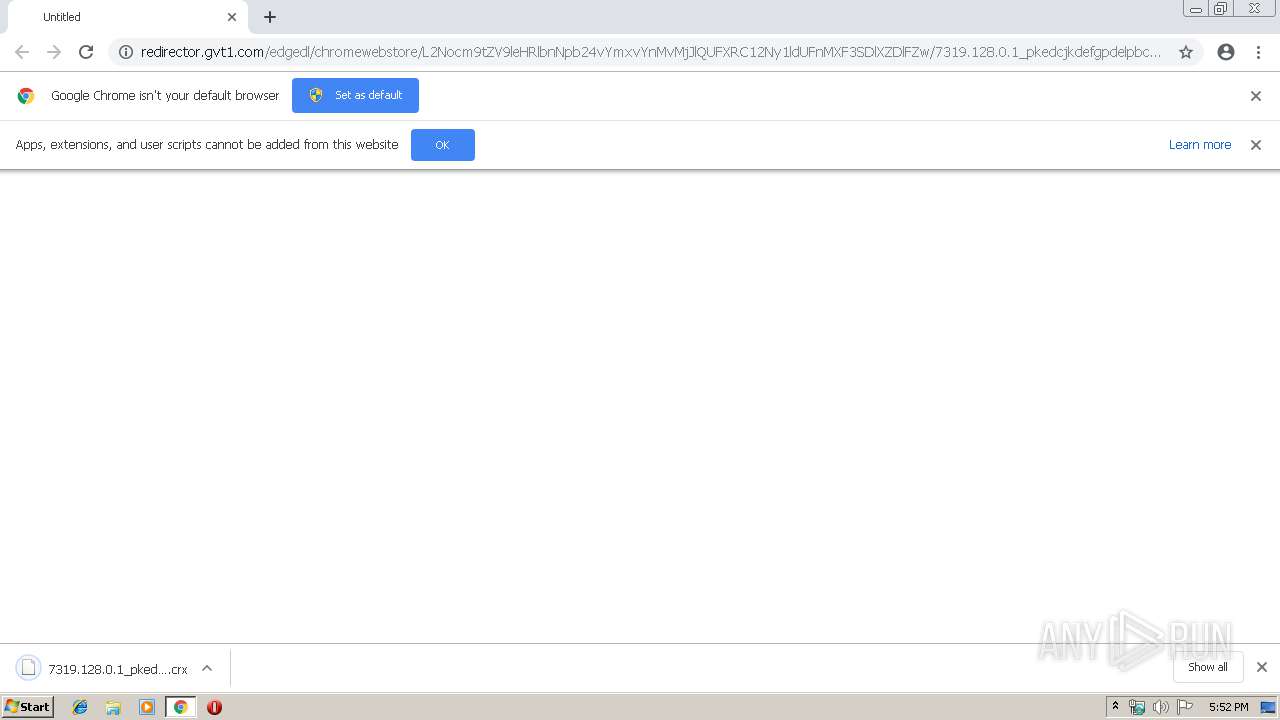
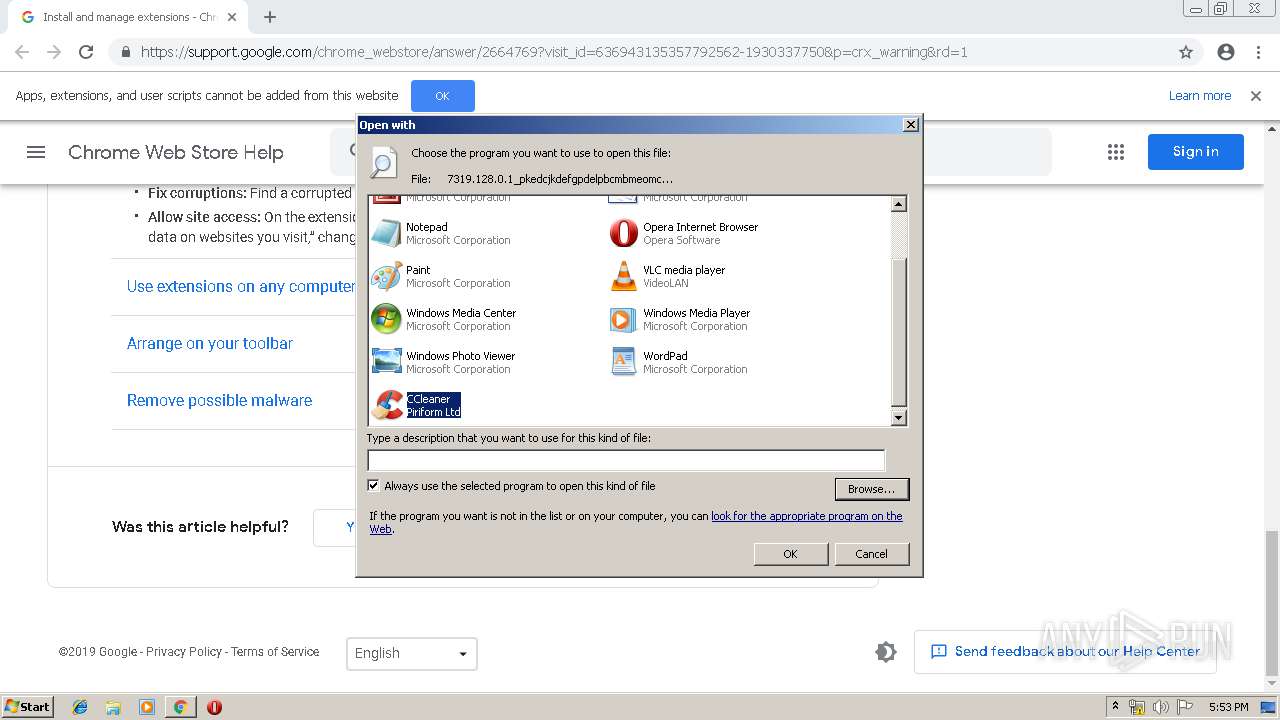
| URL: | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx |
| Full analysis: | https://app.any.run/tasks/a9e016bb-55f1-42a1-8b36-fc56ec831cf1 |
| Verdict: | Malicious activity |
| Analysis date: | May 24, 2019, 16:51:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | FE0FFFAC48EA0A14C3369F7CE581FC53 |
| SHA1: | 7D7D0E1AE8034E0104E4EC6BA7D4F476583E67E8 |
| SHA256: | FAC8727ECFA91C21A65475B419252E124247BA63BB2F48C368E823460BD71D50 |
| SSDEEP: | 3:N1KMVdUyGLkVAzfXrHZzNt3J/VHm7L50+pUob9OKSWU6Urd4zKjb9L4n:CMVdOUAzf7H3Iy+pUA9OYU6UB4zKx4 |
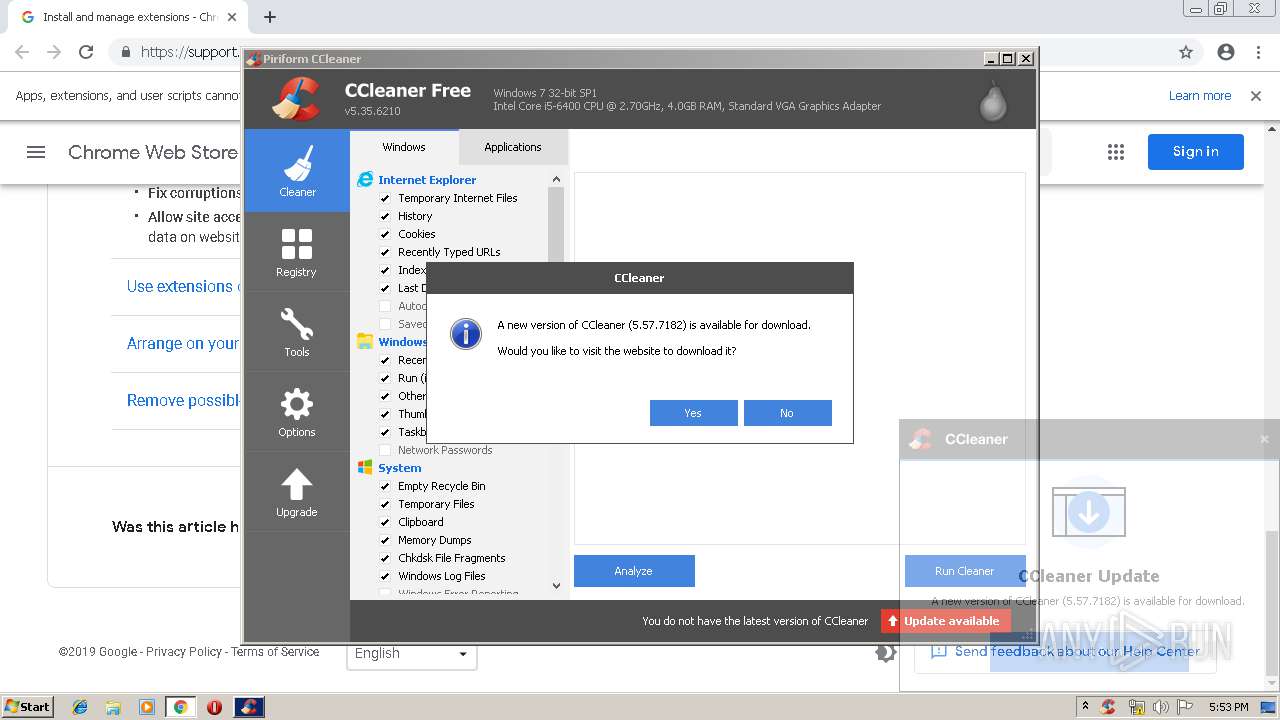
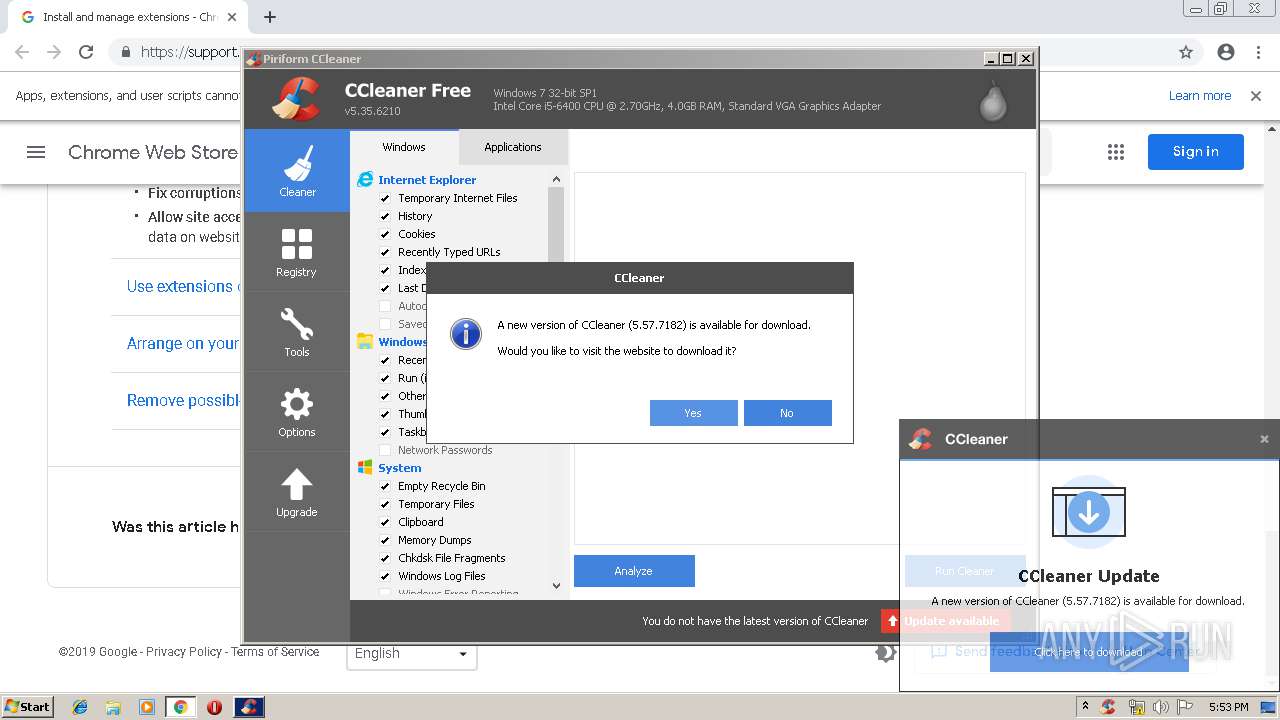
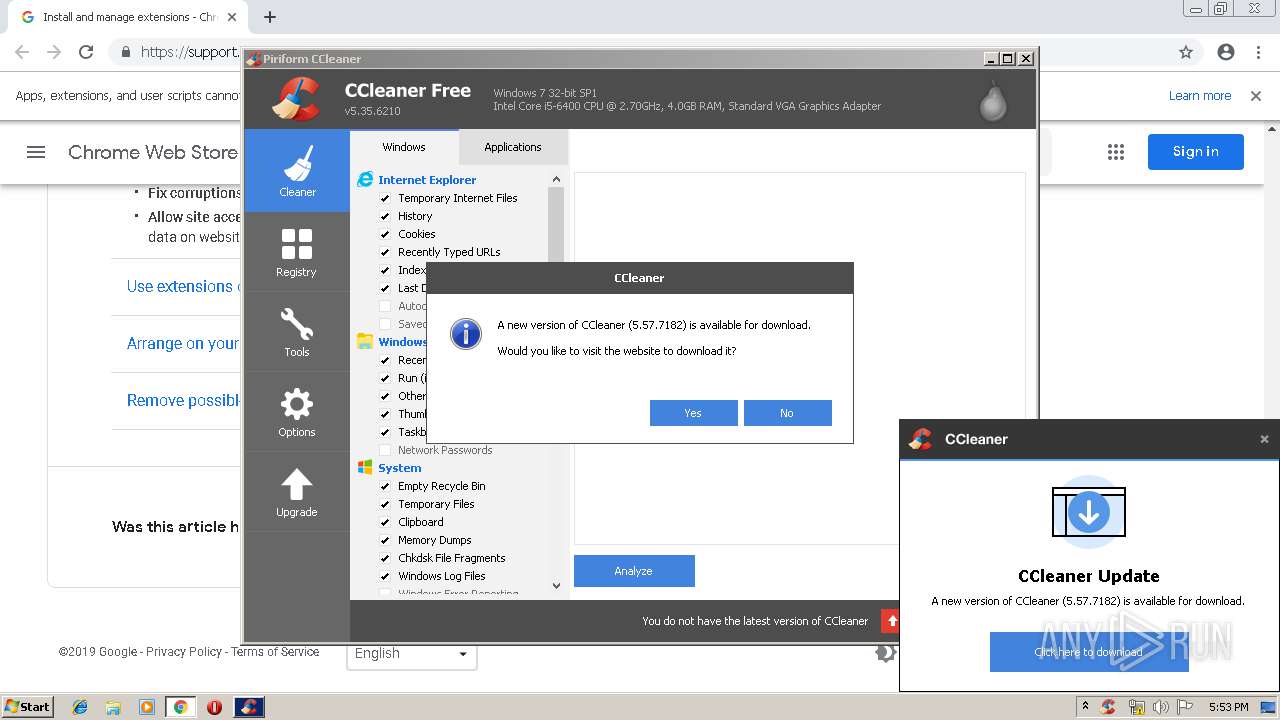
MALICIOUS
Loads the Task Scheduler COM API
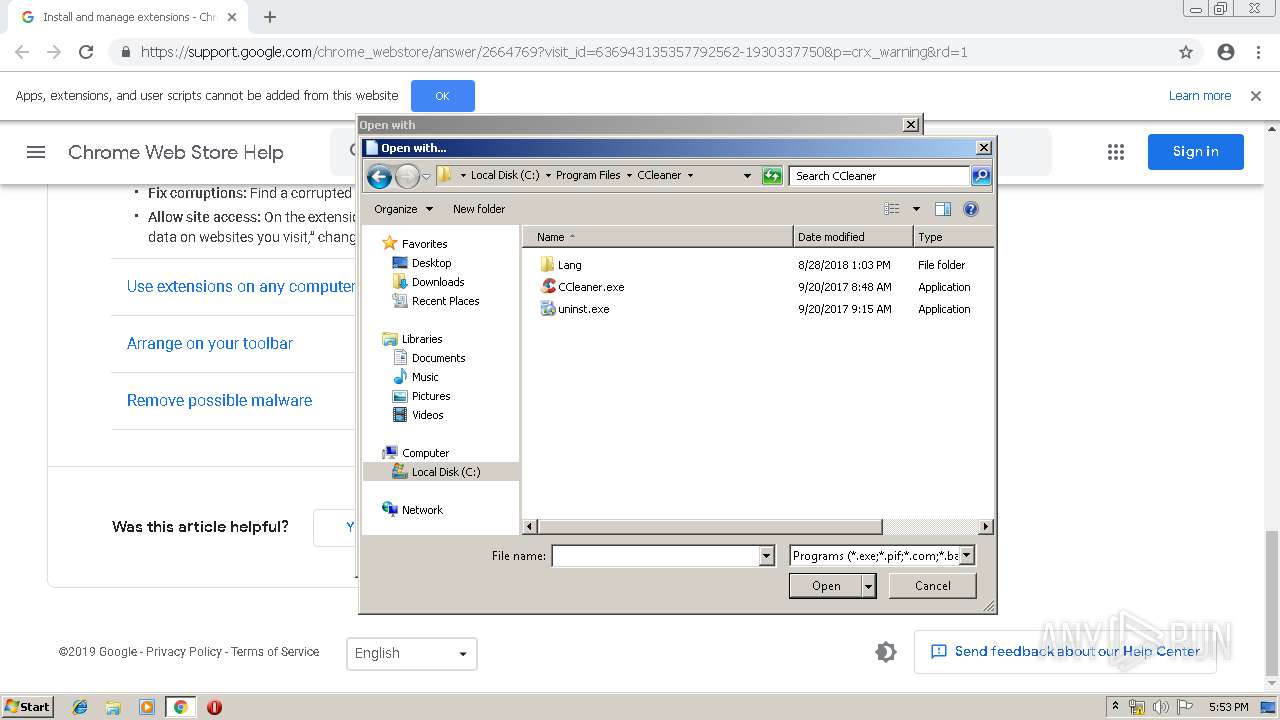
- CCleaner.exe (PID: 4036)
- CCleaner.exe (PID: 3812)
Actions looks like stealing of personal data
- CCleaner.exe (PID: 2452)
- CCleaner.exe (PID: 3812)
Changes settings of System certificates
- CCleaner.exe (PID: 2452)
Changes the autorun value in the registry
- CCleaner.exe (PID: 3812)
SUSPICIOUS
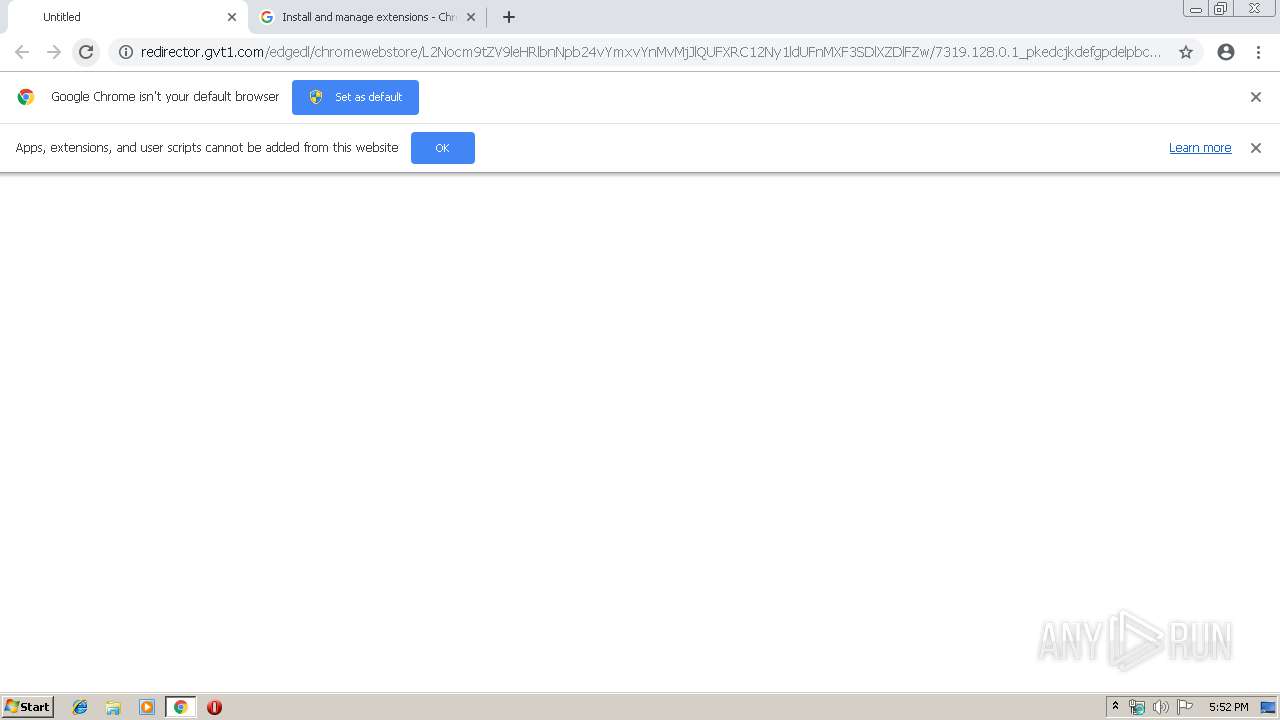
Uses RUNDLL32.EXE to load library
- chrome.exe (PID: 2856)
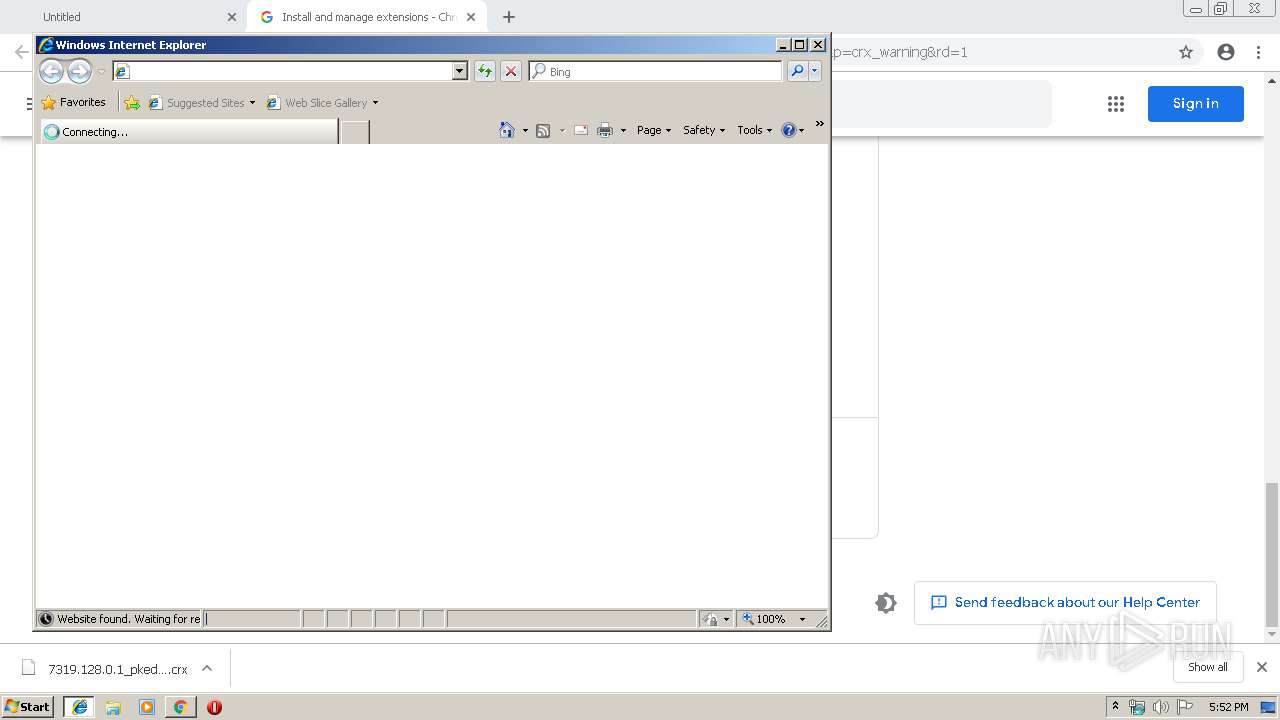
Starts Internet Explorer
- rundll32.exe (PID: 2820)
Reads the cookies of Mozilla Firefox
- CCleaner.exe (PID: 2452)
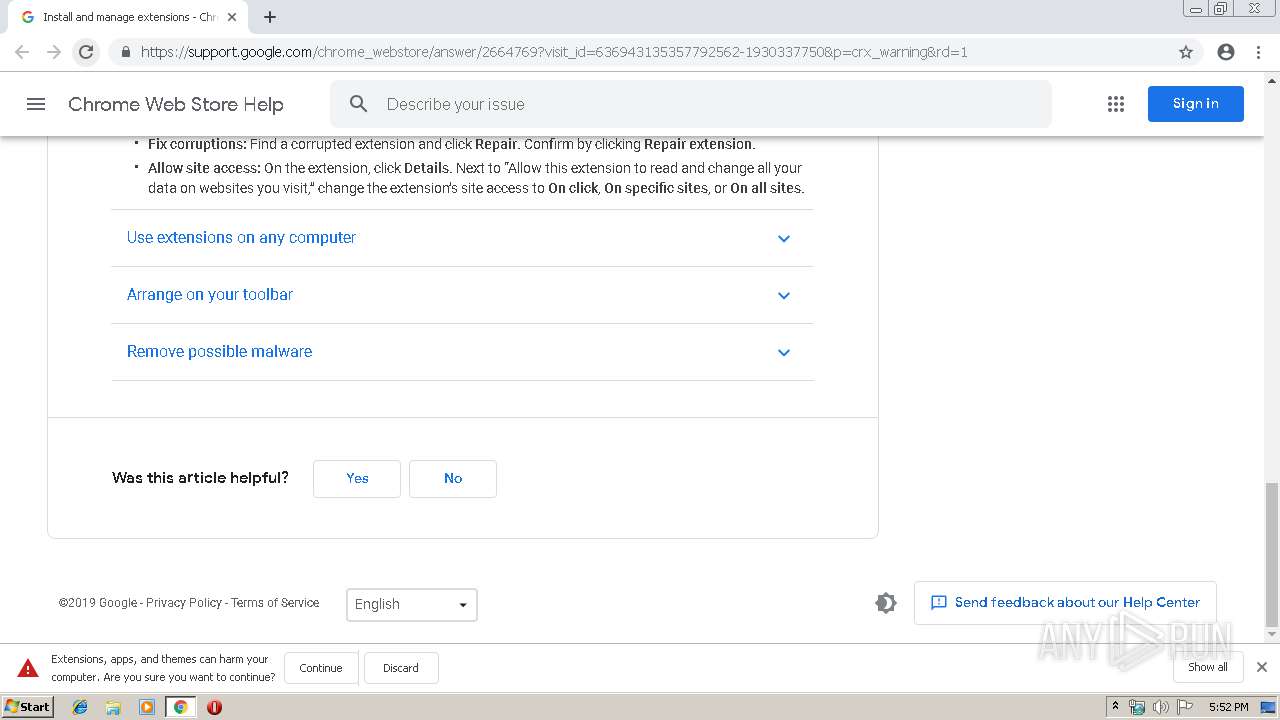
Modifies files in Chrome extension folder
- chrome.exe (PID: 2856)
Reads internet explorer settings
- CCleaner.exe (PID: 2452)
- CCleaner.exe (PID: 3812)
Executed via Task Scheduler
- CCleaner.exe (PID: 2452)
Creates files in the user directory
- CCleaner.exe (PID: 2452)
Reads the cookies of Google Chrome
- CCleaner.exe (PID: 2452)
Adds / modifies Windows certificates
- CCleaner.exe (PID: 2452)
Application launched itself
- CCleaner.exe (PID: 2452)
Low-level read access rights to disk partition
- CCleaner.exe (PID: 2452)
INFO
Application launched itself
- chrome.exe (PID: 2856)
Reads Internet Cache Settings
- iexplore.exe (PID: 3920)
- chrome.exe (PID: 2856)
Changes internet zones settings
- iexplore.exe (PID: 2608)
Creates files in the user directory
- iexplore.exe (PID: 3920)
Reads internet explorer settings
- iexplore.exe (PID: 3920)
Changes settings of System certificates
- iexplore.exe (PID: 2608)
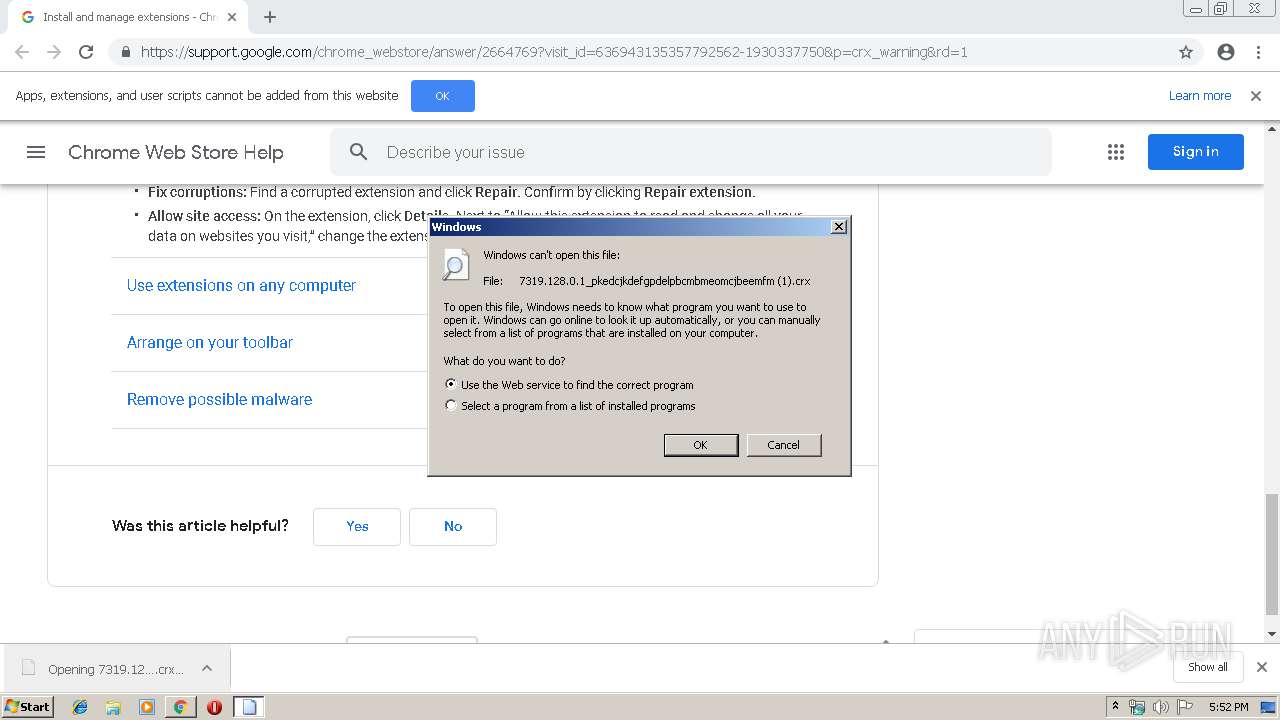
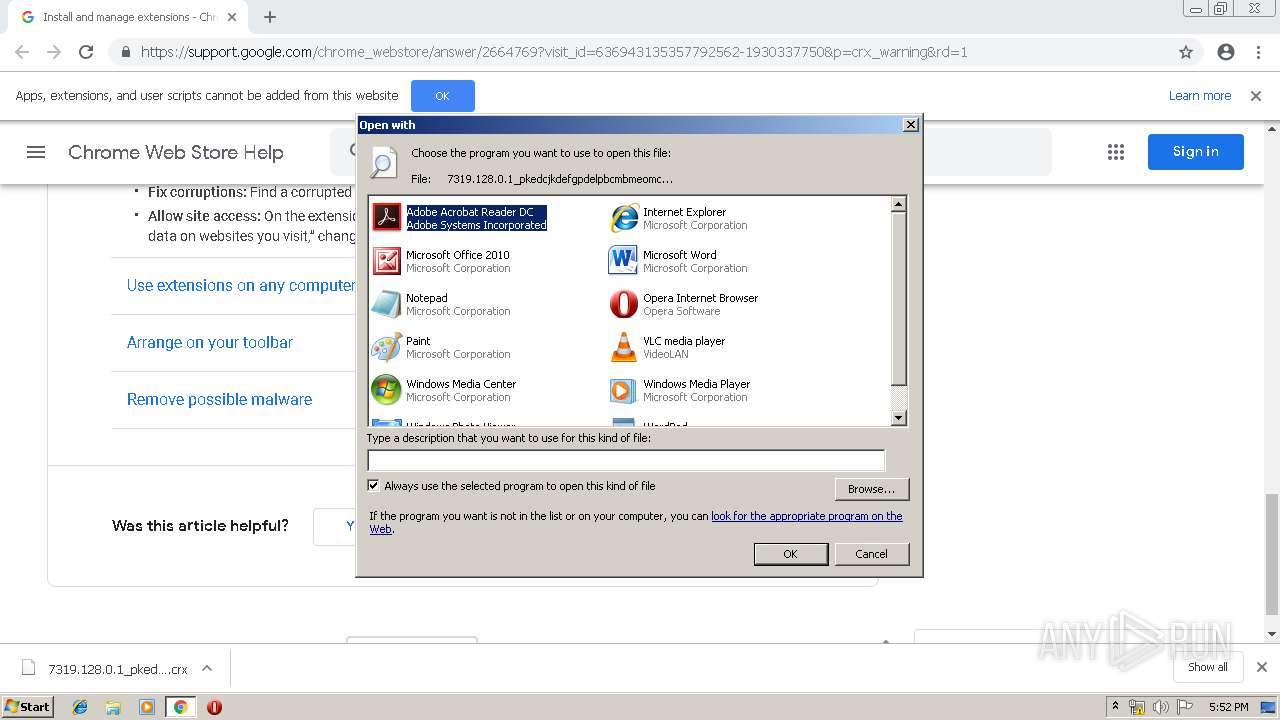
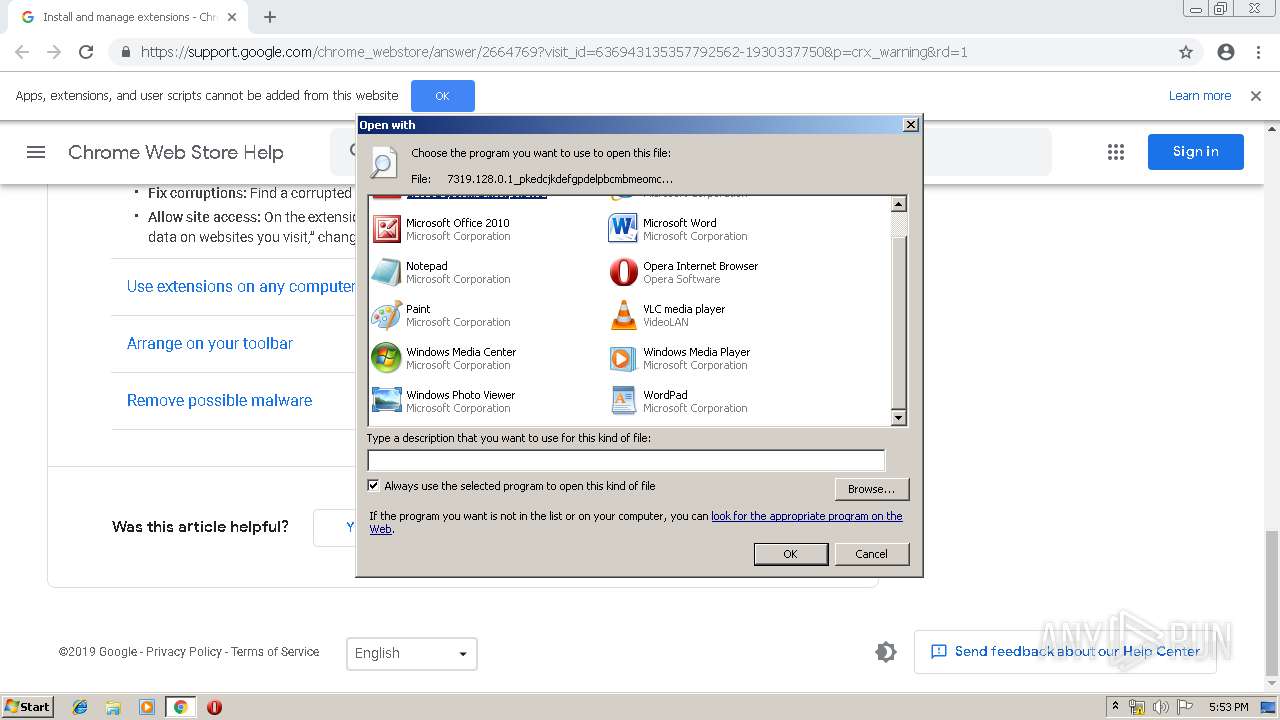
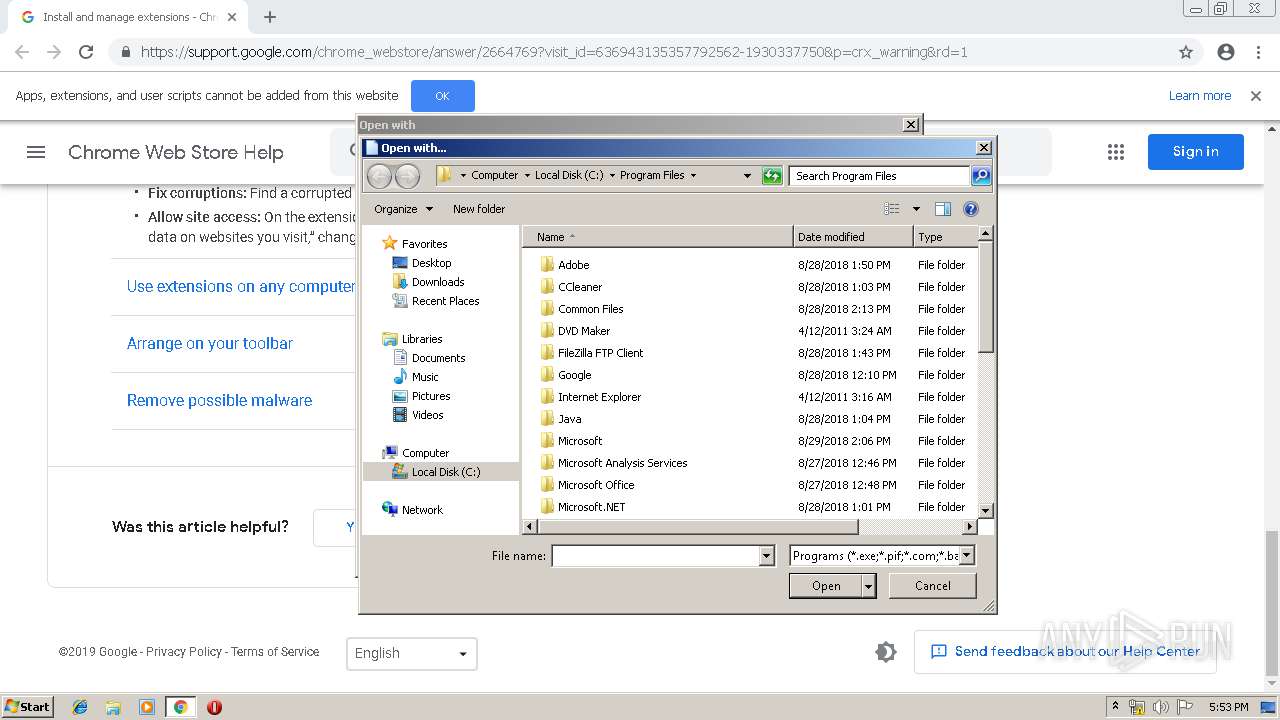
Modifies the open verb of a shell class
- rundll32.exe (PID: 3660)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2608)
Reads settings of System Certificates
- iexplore.exe (PID: 2608)
- CCleaner.exe (PID: 2452)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
74
Monitored processes
39
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11895733925857165460 --mojo-platform-channel-handle=4452 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2774066493471855733 --mojo-platform-channel-handle=2388 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=940,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6684960472551445434 --mojo-platform-channel-handle=4696 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1136038519988273149 --mojo-platform-channel-handle=4464 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3036654183818132388 --mojo-platform-channel-handle=3900 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=15438886644407039456 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15438886644407039456 --renderer-client-id=29 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4760 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2260 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=358781012310508011 --mojo-platform-channel-handle=4252 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7212095712483019482 --mojo-platform-channel-handle=4988 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,10658757632699496643,17954541270075751283,131072 --enable-features=PasswordImport --service-pipe-token=2421393210364245799 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2421393210364245799 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1968 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2452 | "C:\Program Files\CCleaner\CCleaner.exe" "C:\Users\admin\Downloads\7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm (1).crx" /uac | C:\Program Files\CCleaner\CCleaner.exe | taskeng.exe | ||||||||||||
User: admin Company: Piriform Ltd Integrity Level: HIGH Description: CCleaner Exit code: 0 Version: 5, 35, 0, 6210 Modules
| |||||||||||||||
Total events
2 465
Read events
2 019
Write events
434
Delete events
12
Modification events
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2856-13203190321802625 |
Value: 259 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2856) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
57
Text files
287
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\bba3b1ae-e562-4241-8ad6-5251d14aeb71.tmp | — | |
MD5:— | SHA256:— | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2856 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
49
DNS requests
25
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
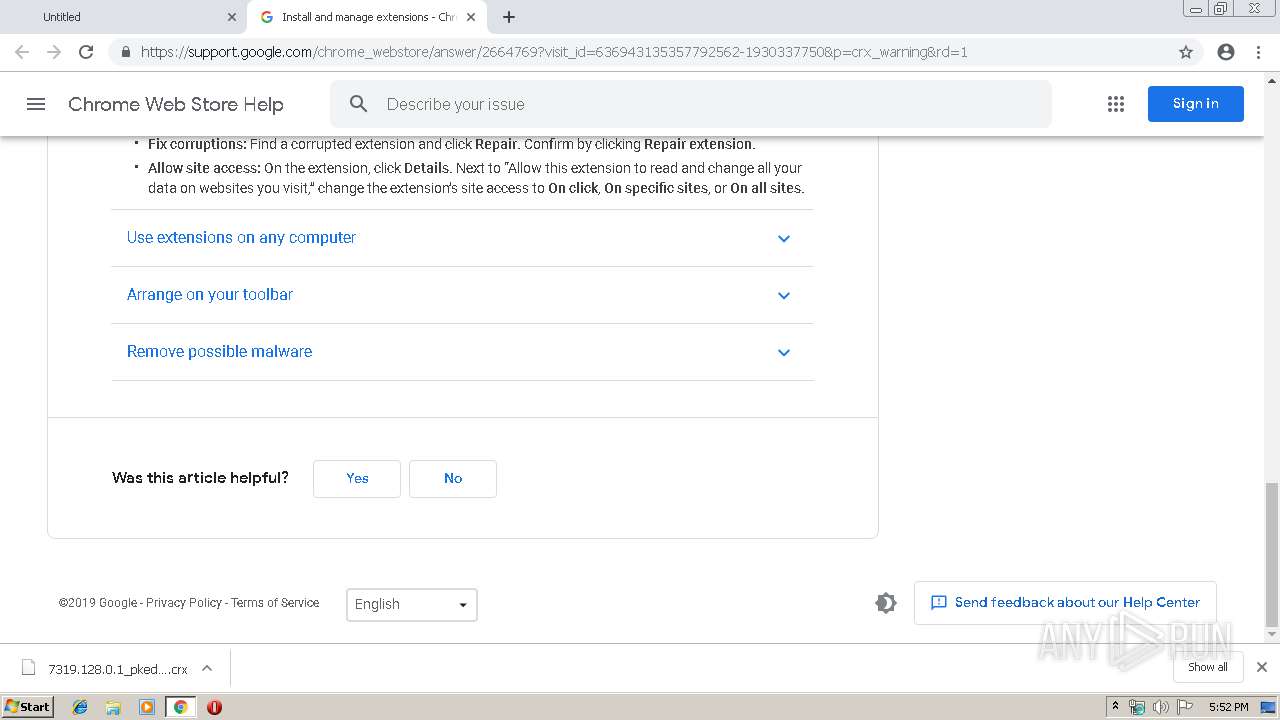
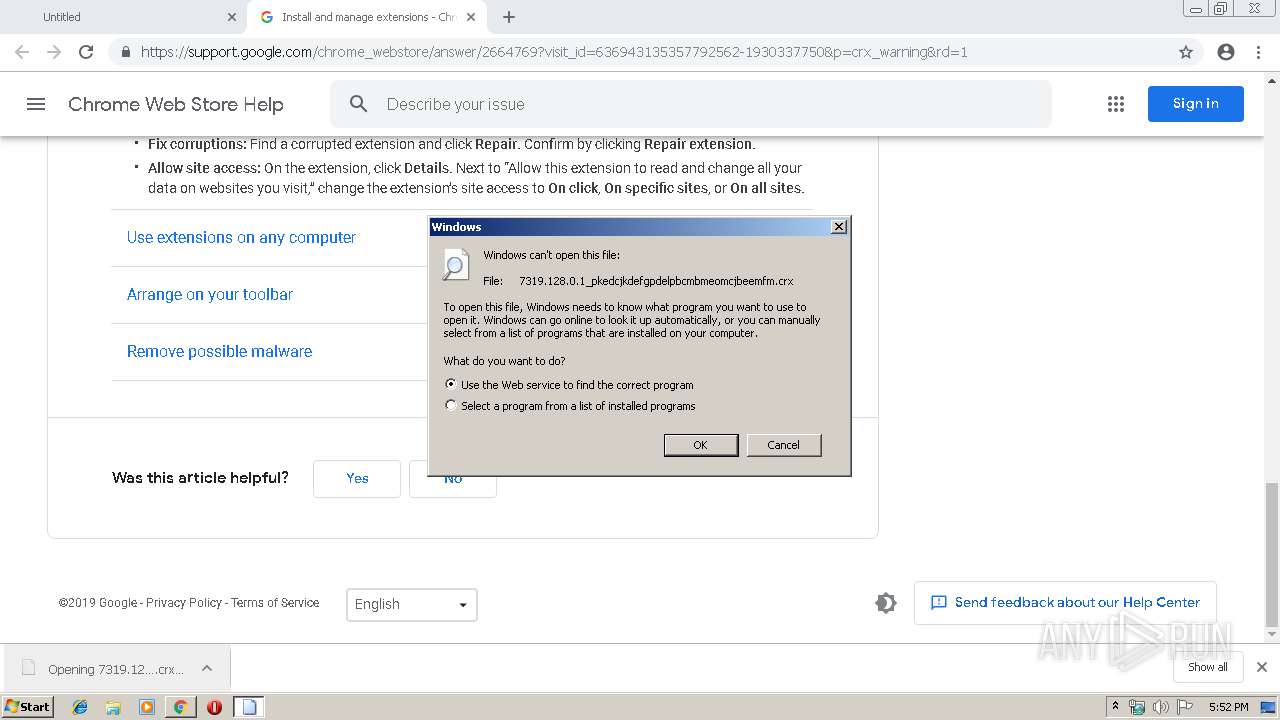
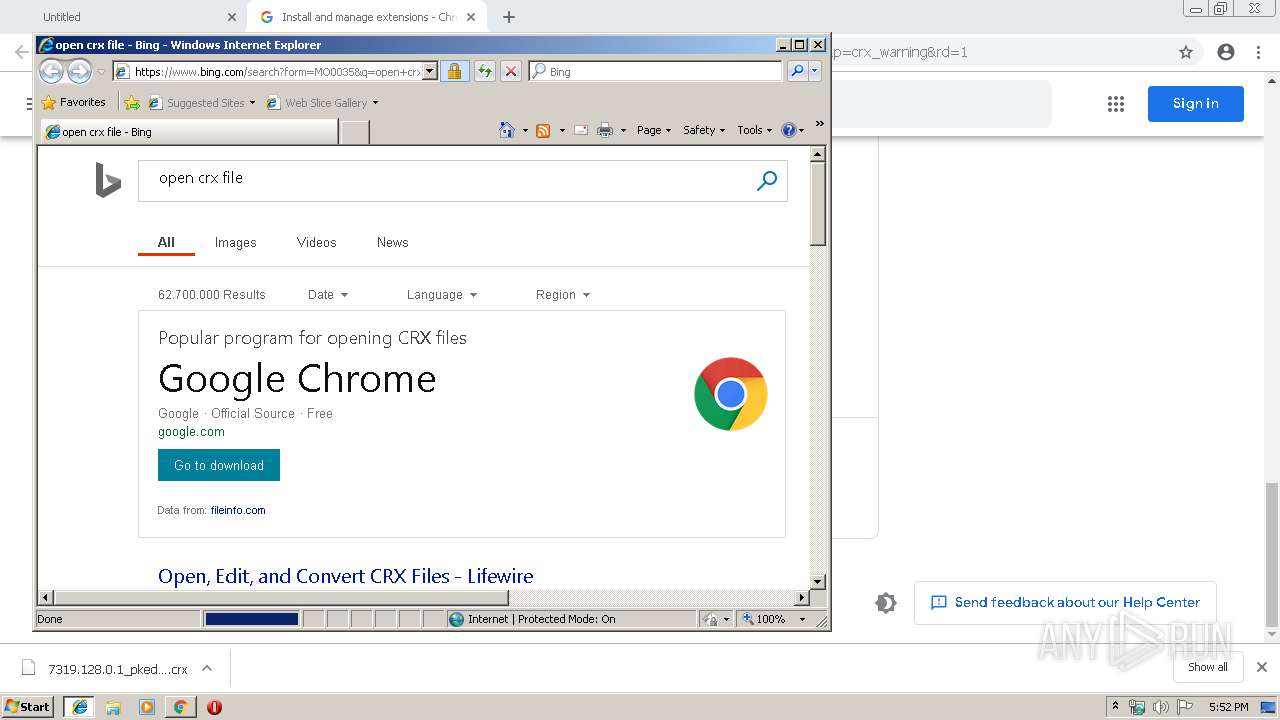
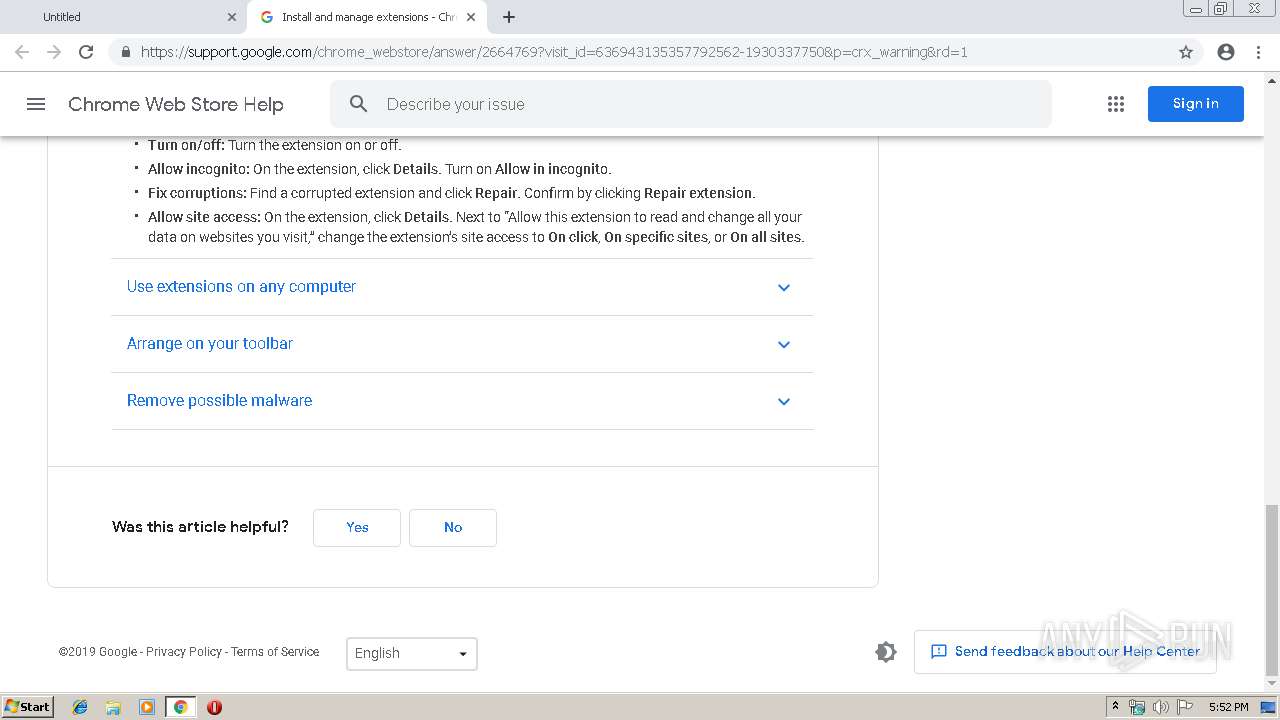
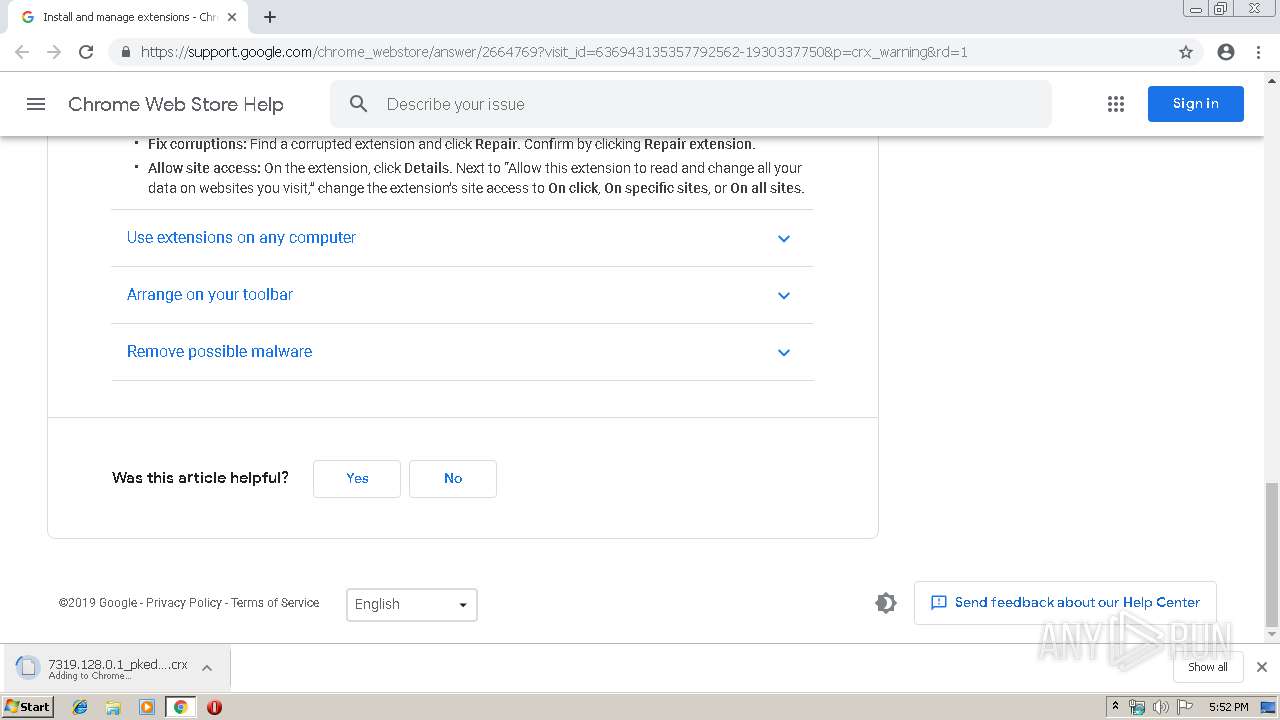
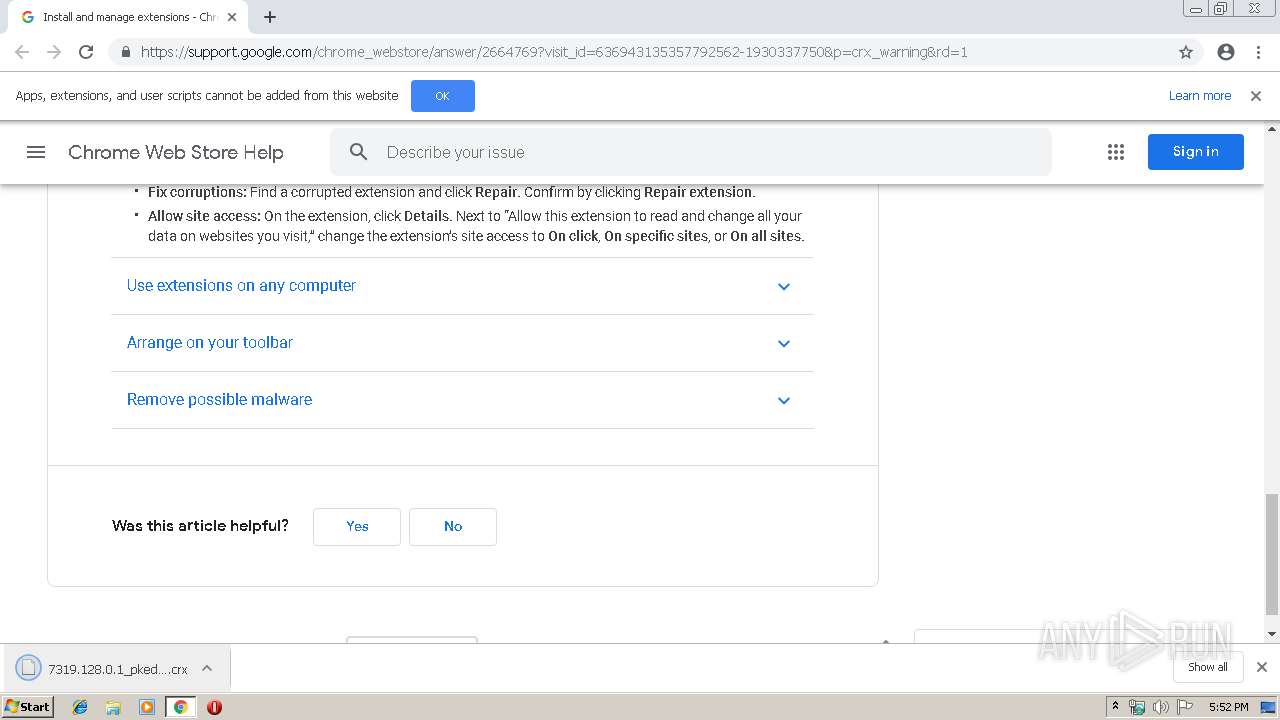
3920 | iexplore.exe | GET | 302 | 23.222.42.9:80 | http://go.microsoft.com/fwlink/?LinkId=57426&Ext=crx | NL | — | — | whitelisted |
3920 | iexplore.exe | GET | 301 | 2.16.186.24:80 | http://shell.windows.com/fileassoc/fileassoc.asp?Ext=crx | unknown | — | — | whitelisted |
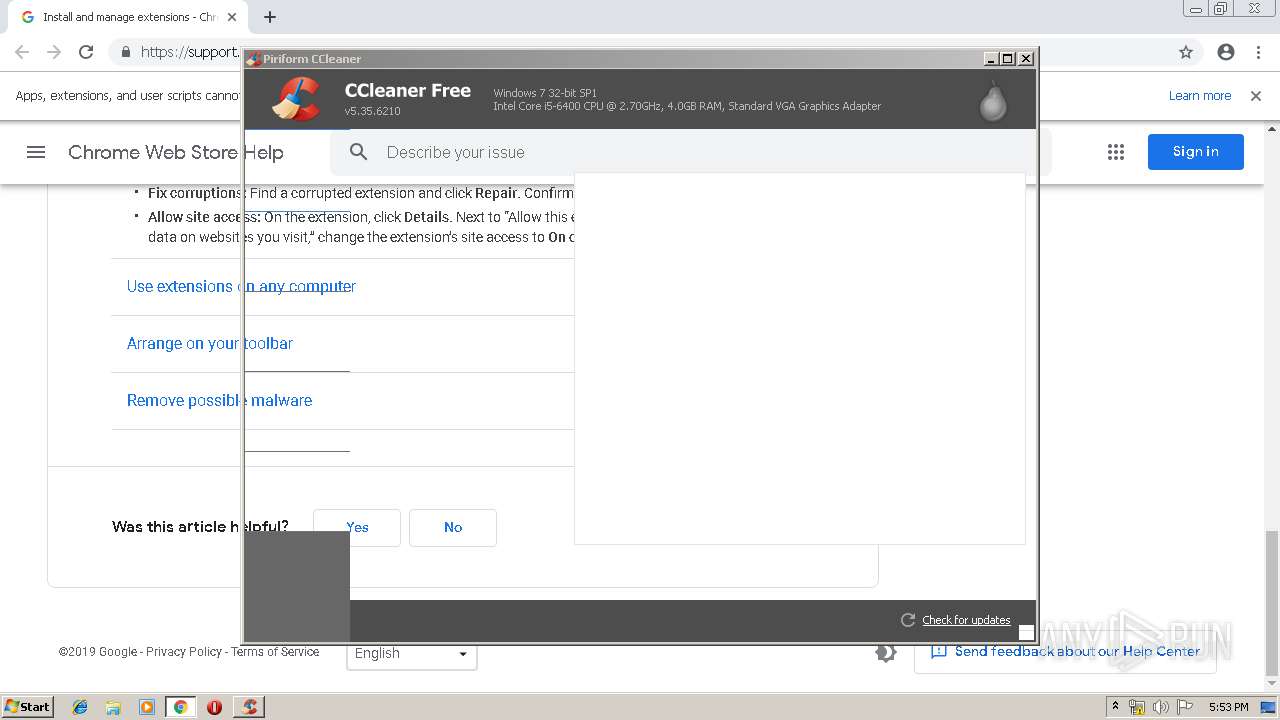
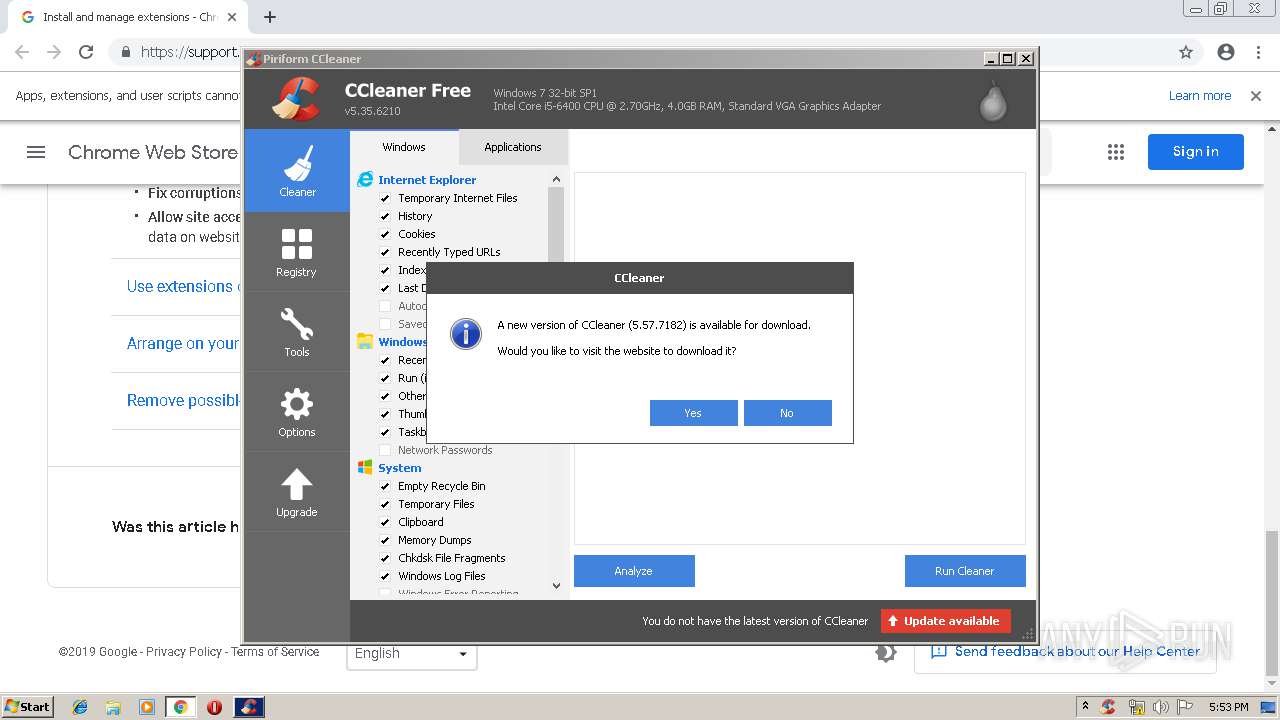
2452 | CCleaner.exe | GET | 301 | 151.101.0.64:80 | http://www.piriform.com/auto?a=0&p=cc&v=5.35.6210&l=1033&lk=&mk=IJR6-W5SV-5KYR-QBZD-6BY4-RN5Z-WAV9-RVK2-VJCA&o=6.1W3&au=1&mx=97B7721C4994E2556FF6A439510F665DB45337A341A47E15F4997584423BF714&gu=00000000-0000-4000-8000-d6f7f2be5127 | US | — | — | whitelisted |
2856 | chrome.exe | GET | 200 | 74.125.100.104:80 | http://r3---sn-5hnekn7z.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=85.203.44.3&mm=28&mn=sn-5hnekn7z&ms=nvh&mt=1558716577&mv=m&pl=26&shardbypass=yes | US | crx | 842 Kb | whitelisted |
2856 | chrome.exe | GET | 302 | 172.217.23.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 502 b | whitelisted |
2856 | chrome.exe | GET | 200 | 74.125.100.104:80 | http://r3---sn-5hnekn7z.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=85.203.44.3&mm=28&mn=sn-5hnekn7z&ms=nvh&mt=1558716577&mv=m&pl=26&shardbypass=yes | US | crx | 842 Kb | whitelisted |
2856 | chrome.exe | GET | 302 | 172.217.23.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 502 b | whitelisted |
2856 | chrome.exe | GET | 302 | 172.217.23.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 502 b | whitelisted |
2856 | chrome.exe | GET | 200 | 74.125.8.12:80 | http://r6---sn-5hne6n7e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=85.203.44.3&mm=28&mn=sn-5hne6n7e&ms=nvh&mt=1558716706&mv=m&pl=26&shardbypass=yes | US | crx | 842 Kb | whitelisted |
2608 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2856 | chrome.exe | 172.217.23.174:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2856 | chrome.exe | 74.125.100.104:80 | r3---sn-5hnekn7z.gvt1.com | Google Inc. | US | whitelisted |
2856 | chrome.exe | 172.217.18.100:443 | www.google.com | Google Inc. | US | whitelisted |
2856 | chrome.exe | 172.217.23.129:443 | lh3.googleusercontent.com | Google Inc. | US | whitelisted |
2856 | chrome.exe | 216.58.206.14:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2856 | chrome.exe | 172.217.23.142:443 | clients4.google.com | Google Inc. | US | whitelisted |
2856 | chrome.exe | 172.217.21.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2856 | chrome.exe | 172.217.21.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2856 | chrome.exe | 172.217.22.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2856 | chrome.exe | 172.217.16.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
accounts.google.com |
| shared |
r3---sn-5hnekn7z.gvt1.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| malicious |
clients4.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
support.google.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |