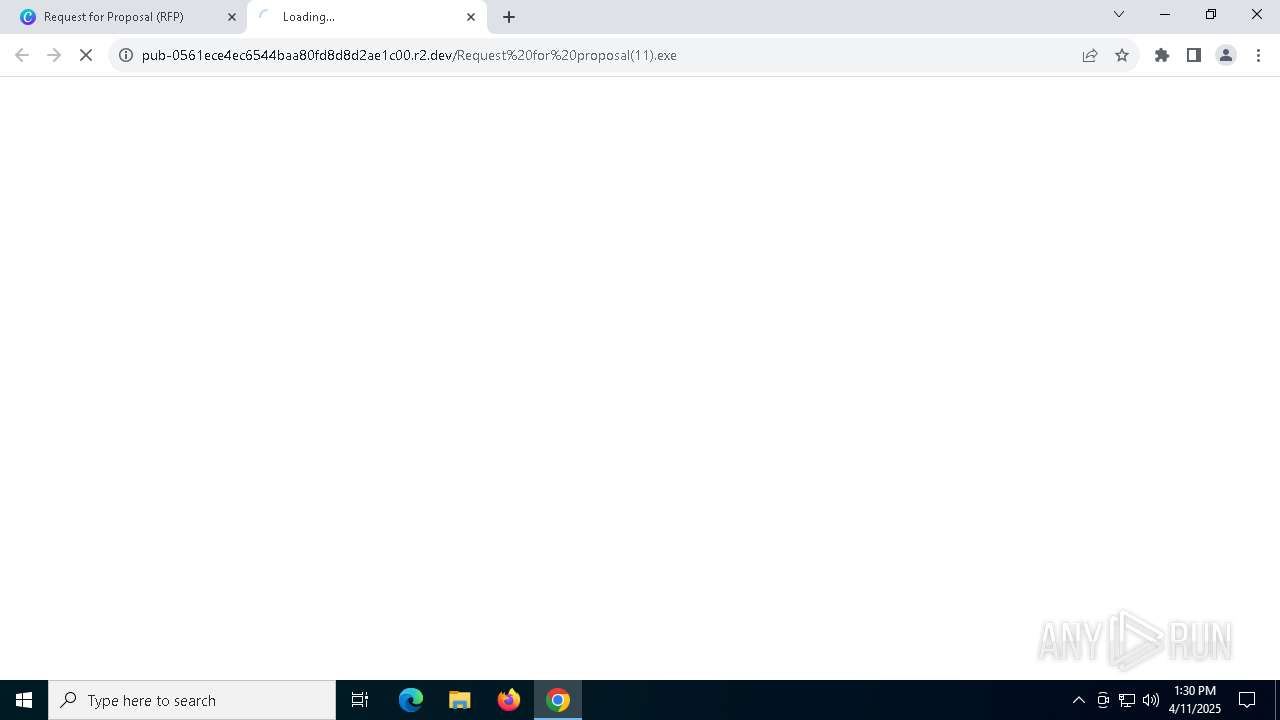
| URL: | https://url.us.m.mimecastprotect.com/s/u9-HCYEB9XTpoAjmzc0f0cx-d8x?domain=canva.com |
| Full analysis: | https://app.any.run/tasks/ee9cb77b-b28b-4127-9b85-c30fd2c27905 |
| Verdict: | Malicious activity |
| Analysis date: | April 11, 2025, 13:29:21 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 2733AEE703B9C42B28662F47F83870ED |
| SHA1: | C1D09EBC7785C5B8843DF6E3CA85F028DD850E8E |
| SHA256: | FAC488BD37E2DBBD4027E579F93FB7425AE905F1EC143C980569999022005DE4 |
| SSDEEP: | 3:N8UjmTSCK7gGb5b:2Ujw8gGNb |
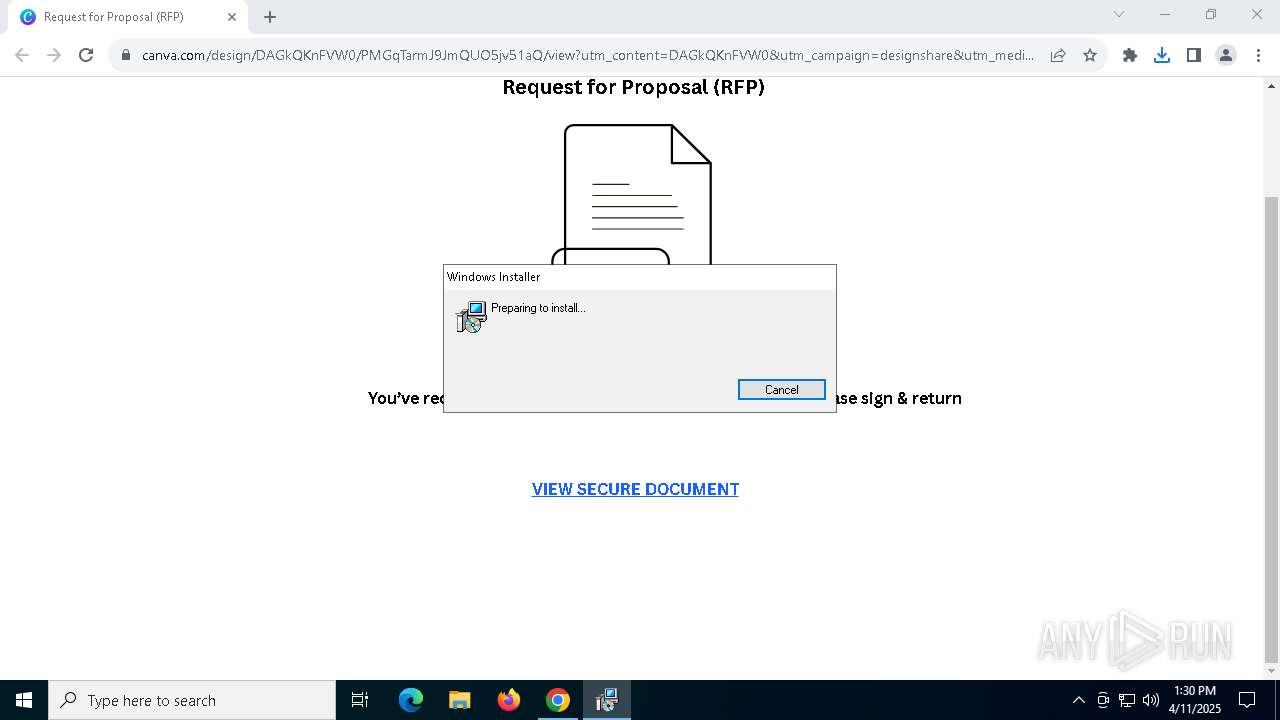
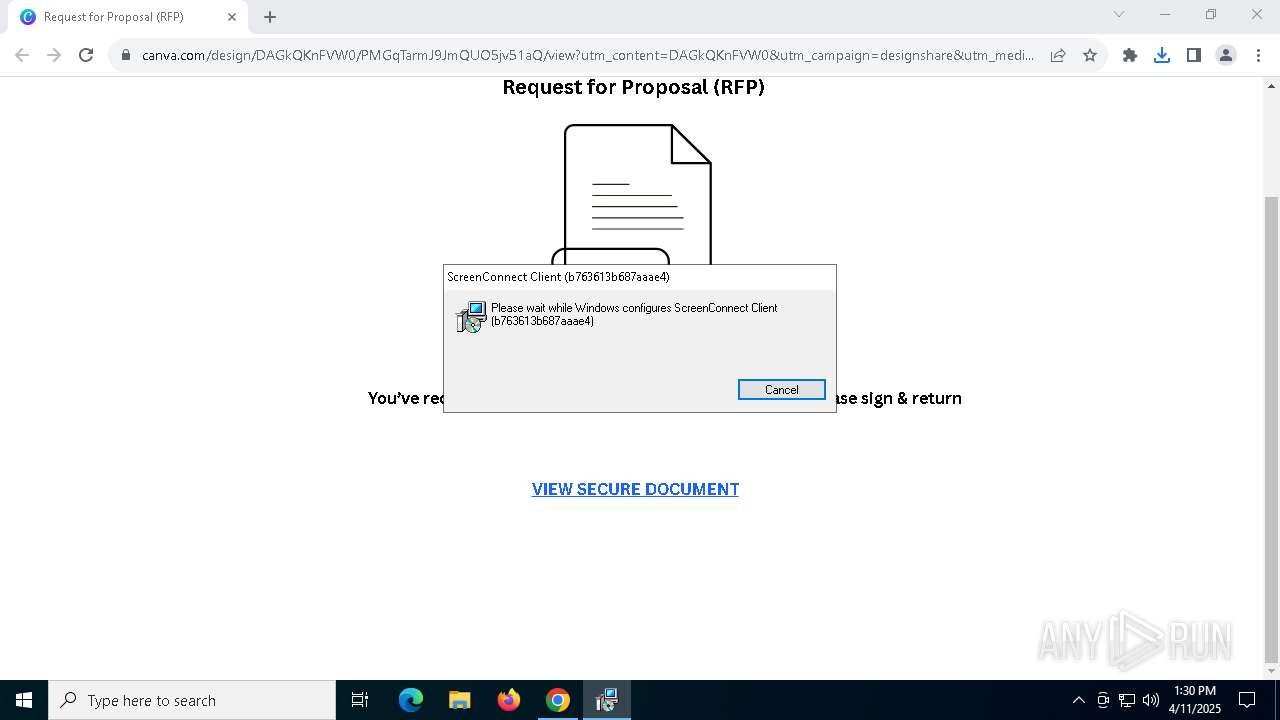
MALICIOUS
SCREENCONNECT has been detected (SURICATA)
- ScreenConnect.ClientService.exe (PID: 456)
SUSPICIOUS
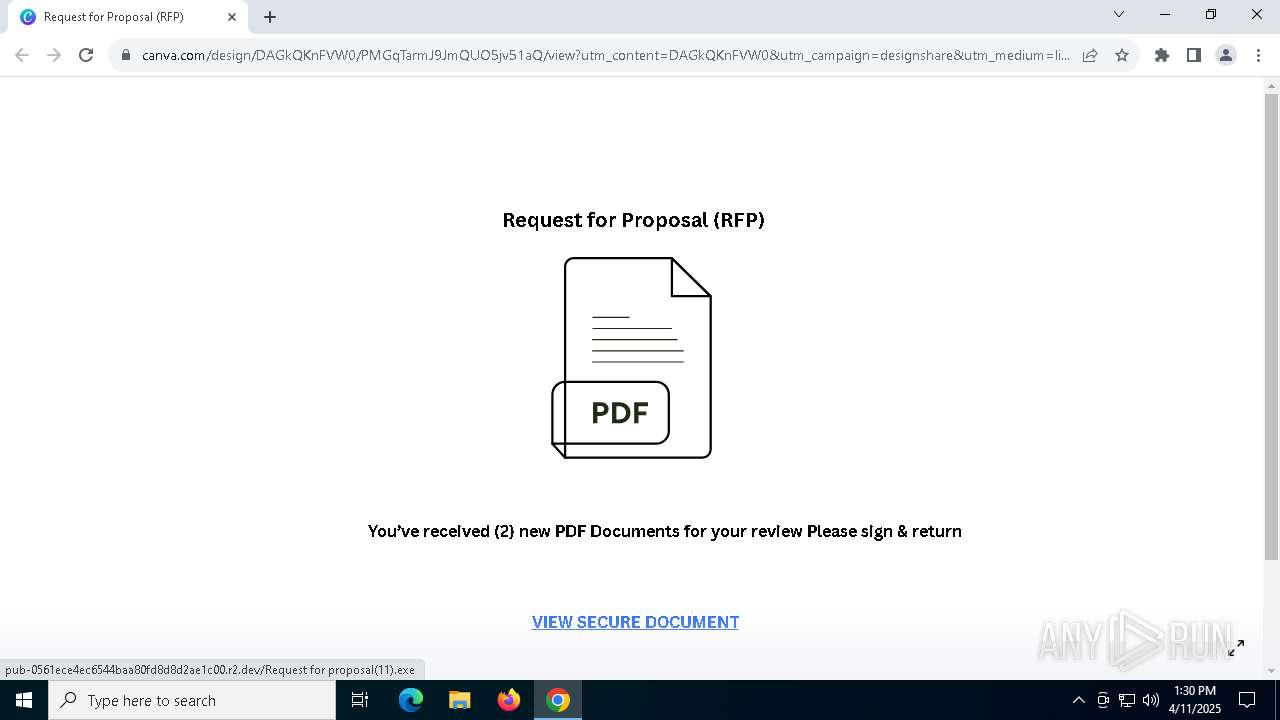
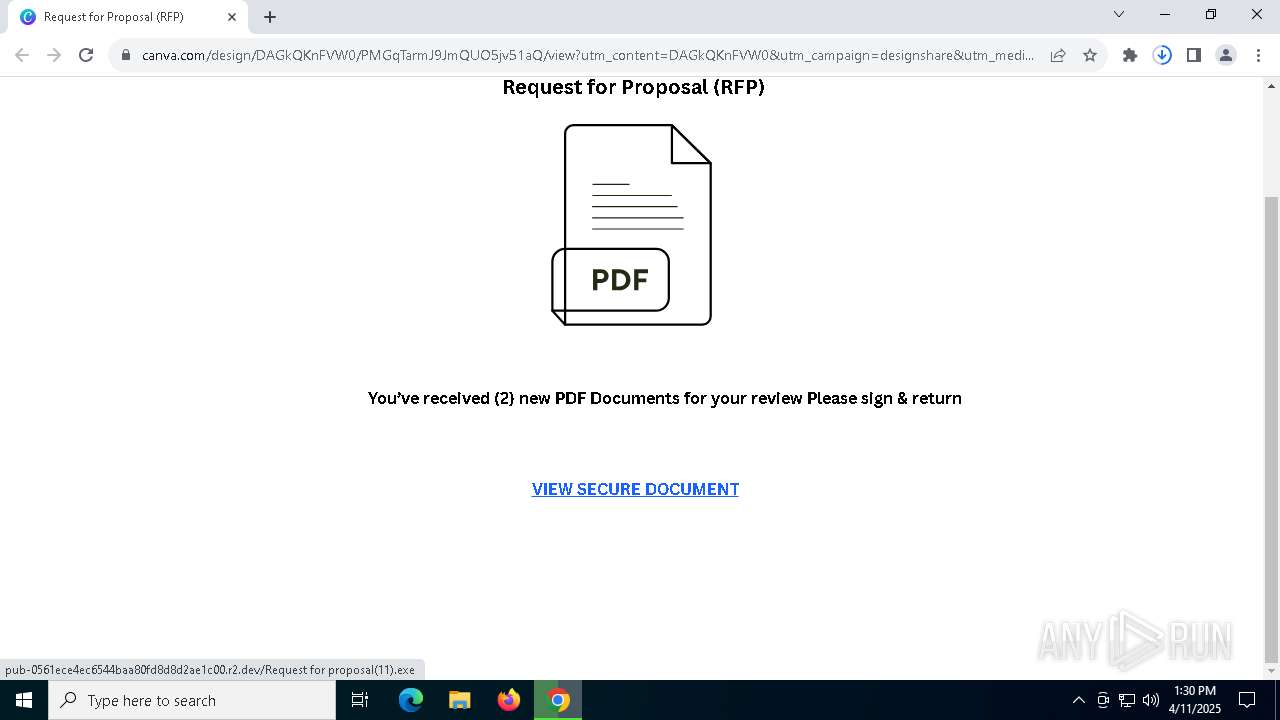
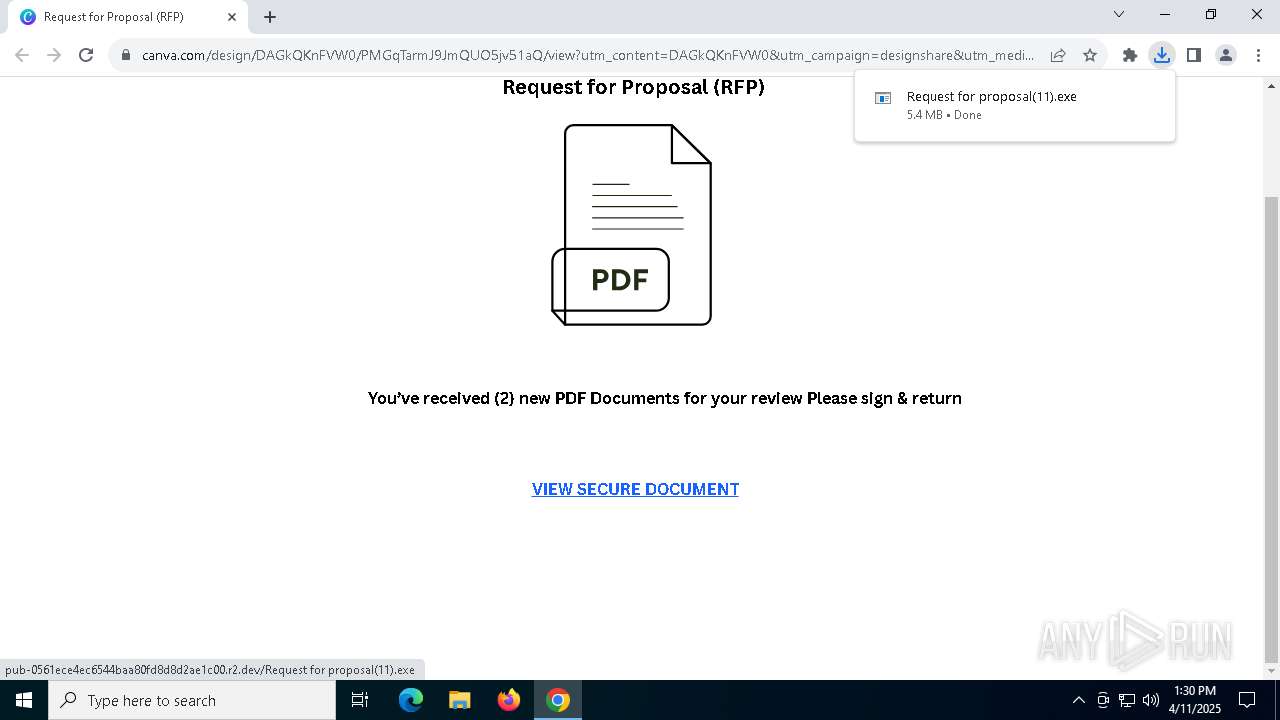
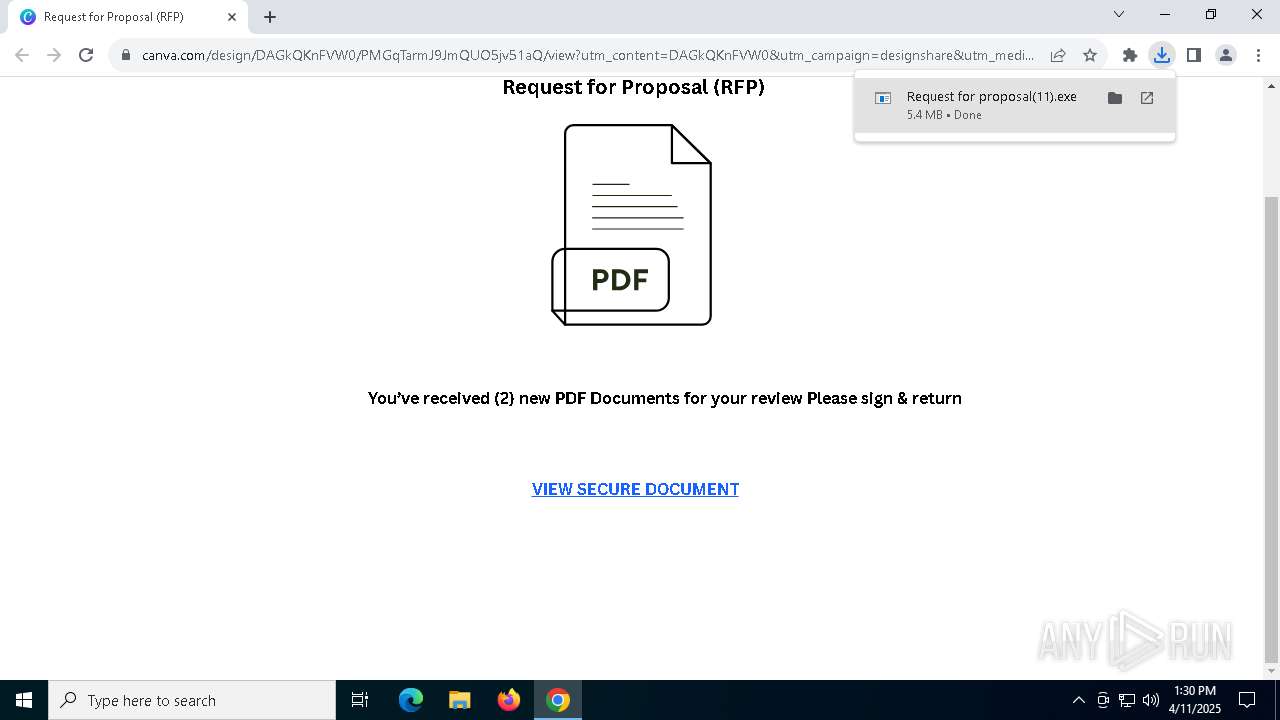
Possible Social Engineering Attempted
- chrome.exe (PID: 7252)
Reads security settings of Internet Explorer
- Request for proposal(11).exe (PID: 8028)
- ScreenConnect.WindowsClient.exe (PID: 6112)
- ScreenConnect.WindowsClient.exe (PID: 8044)
Executable content was dropped or overwritten
- rundll32.exe (PID: 5680)
Executes as Windows Service
- VSSVC.exe (PID: 2392)
- ScreenConnect.ClientService.exe (PID: 456)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 8184)
Screenconnect has been detected
- msiexec.exe (PID: 8184)
- ScreenConnect.ClientService.exe (PID: 456)
- ScreenConnect.ClientService.exe (PID: 456)
Connects to unusual port
- ScreenConnect.ClientService.exe (PID: 456)
Potential Corporate Privacy Violation
- ScreenConnect.ClientService.exe (PID: 456)
Creates or modifies Windows services
- ScreenConnect.ClientService.exe (PID: 456)
SCREENCONNECT mutex has been found
- ScreenConnect.ClientService.exe (PID: 456)
INFO
Executable content was dropped or overwritten
- chrome.exe (PID: 1852)
- msiexec.exe (PID: 5332)
- chrome.exe (PID: 7692)
- msiexec.exe (PID: 8184)
Application launched itself
- chrome.exe (PID: 1852)
Reads the software policy settings
- slui.exe (PID: 7856)
Checks supported languages
- Request for proposal(11).exe (PID: 8028)
- msiexec.exe (PID: 3020)
- msiexec.exe (PID: 8184)
- msiexec.exe (PID: 4164)
- ScreenConnect.ClientService.exe (PID: 456)
- ScreenConnect.WindowsClient.exe (PID: 6112)
- ScreenConnect.WindowsClient.exe (PID: 8044)
Reads the computer name
- Request for proposal(11).exe (PID: 8028)
- msiexec.exe (PID: 3020)
- msiexec.exe (PID: 8184)
- msiexec.exe (PID: 4164)
- ScreenConnect.ClientService.exe (PID: 456)
- ScreenConnect.WindowsClient.exe (PID: 6112)
Create files in a temporary directory
- Request for proposal(11).exe (PID: 8028)
- rundll32.exe (PID: 5680)
Autorun file from Downloads
- chrome.exe (PID: 736)
- chrome.exe (PID: 1852)
Process checks computer location settings
- Request for proposal(11).exe (PID: 8028)
Reads the machine GUID from the registry
- Request for proposal(11).exe (PID: 8028)
- ScreenConnect.WindowsClient.exe (PID: 6112)
- ScreenConnect.ClientService.exe (PID: 456)
- ScreenConnect.WindowsClient.exe (PID: 8044)
CONNECTWISE has been detected
- msiexec.exe (PID: 5332)
- msiexec.exe (PID: 8184)
- ScreenConnect.ClientService.exe (PID: 456)
- ScreenConnect.WindowsClient.exe (PID: 6112)
- ScreenConnect.WindowsClient.exe (PID: 8044)
Creates a software uninstall entry
- msiexec.exe (PID: 8184)
SCREENCONNECT has been detected
- msiexec.exe (PID: 8184)
- ScreenConnect.ClientService.exe (PID: 456)
The sample compiled with english language support
- chrome.exe (PID: 7692)
Manages system restore points
- SrTasks.exe (PID: 7552)
Reads CPU info
- ScreenConnect.WindowsClient.exe (PID: 8044)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
166
Monitored processes
33
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | "C:\Program Files (x86)\ScreenConnect Client (b763613b687aaae4)\ScreenConnect.ClientService.exe" "?e=Access&y=Guest&h=relay.shamrockkfoods.com&p=8041&s=27b202ac-8864-4651-8dd1-96ca5f91d175&k=BgIAAACkAABSU0ExAAgAAAEAAQDBt26z3MvkQbEYq2w%2f0x8wxjXEFi1gsirDmJryUsT3KpbMew6hvoJ5DNi9IiHwvmIpTeciD%2bPbnejHz697Zjmz83noCx5YLqquh5fWojq6r7fIoRLqBhnhA1O85AT3GdalEkn7mhcbswnTxi2n3ht9Kg9FHHH6XzTxBh5ux%2fSCOWklgPalrtS4D8WnTfmJO3IQUV0pxF7tbqLqcG4LHZgqJEqUPFOl4IRMSIJ%2bw0cXMbXh8zIo7pzeY2xQI7PG7H%2bJWH665x7OJBdEmaVOnKBUMYJ9eY2CusujO%2fuXQN7YnxK2IDEhyN5V1HvnPkIGG0qQ3UChhDbJLQPp995wOS6f" | C:\Program Files (x86)\ScreenConnect Client (b763613b687aaae4)\ScreenConnect.ClientService.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Version: 24.3.7.9067 Modules
| |||||||||||||||
| 736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=3776 --field-trial-handle=1880,i,233828714810761417,10679955545648195961,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 780 | C:\Windows\syswow64\MsiExec.exe -Embedding 2D1EB554365429BA6519878BC9343006 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1852 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://url.us.m.mimecastprotect.com/s/u9-HCYEB9XTpoAjmzc0f0cx-d8x?domain=canva.com" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2392 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3020 | C:\Windows\syswow64\MsiExec.exe -Embedding 44648212E4D90917F9B647A7C2876F48 C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4164 | C:\Windows\syswow64\MsiExec.exe -Embedding 38E7C98DDD225F9F0E67C99BEEB69AC3 E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=122.0.6261.70 --initial-client-data=0x230,0x234,0x238,0x204,0x23c,0x7ffc87aadc40,0x7ffc87aadc4c,0x7ffc87aadc58 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 5332 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\ScreenConnect\24.3.7.9067\b763613b687aaae4\ScreenConnect.ClientSetup.msi" | C:\Windows\SysWOW64\msiexec.exe | Request for proposal(11).exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5680 | rundll32.exe "C:\Users\admin\AppData\Local\Temp\MSIB3DC.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1160234 1 ScreenConnect.InstallerActions!ScreenConnect.ClientInstallerActions.FixupServiceArguments | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
13 411
Read events
13 109
Write events
279
Delete events
23
Modification events
| (PID) Process: | (1852) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1852) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1852) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1852) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1852) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (736) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 01000000000000004730E0E1E5AADB01 | |||
| (PID) Process: | (8184) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000A3AD0EE6E5AADB01F81F0000B0100000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8184) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 48000000000000005C1111E6E5AADB01F81F0000B0100000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8184) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000BCD853E6E5AADB01F81F0000B0100000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8184) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000D58C58E6E5AADB01F81F0000B0100000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
26
Suspicious files
93
Text files
32
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10ca18.TMP | — | |
MD5:— | SHA256:— | |||
| 1852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10ca28.TMP | — | |
MD5:— | SHA256:— | |||
| 1852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10ca28.TMP | — | |
MD5:— | SHA256:— | |||
| 1852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10ca37.TMP | — | |
MD5:— | SHA256:— | |||
| 1852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10ca37.TMP | — | |
MD5:— | SHA256:— | |||
| 1852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1852 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
56
DNS requests
51
Threats
19
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.72:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.72:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7488 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7488 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5776 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
5776 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
5776 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
5776 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
5776 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 2.16.164.72:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.164.72:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
7252 | chrome.exe | 205.139.111.117:443 | url.us.m.mimecastprotect.com | MIMECAST | US | whitelisted |
1852 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7252 | chrome.exe | 108.177.96.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
7252 | chrome.exe | 104.16.103.112:443 | www.canva.com | CLOUDFLARENET | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
url.us.m.mimecastprotect.com |
| whitelisted |
accounts.google.com |
| whitelisted |
www.canva.com |
| whitelisted |
static.canva.com |
| whitelisted |
static.cloudflareinsights.com |
| whitelisted |
o13855.ingest.sentry.io |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7252 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Canva designs and to share platform (static .canva .com) |
7252 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Canva designs and to share platform (static .canva .com) |
7252 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Canva designs and to share platform (static .canva .com) |
7252 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Canva designs and to share platform (static .canva .com) |
7252 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to sentry .io |
7252 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to sentry .io |
7252 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Canva designs and to share platform (static .canva .com) |
7252 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Canva designs and to share platform (static .canva .com) |
7252 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Canva designs and to share platform (static .canva .com) |
7252 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Canva designs and to share platform (static .canva .com) |