| File name: | 3.5.5_45852.exe |
| Full analysis: | https://app.any.run/tasks/b3f39dbf-d1c8-4f56-8f86-89ddfde06aaa |
| Verdict: | Malicious activity |
| Analysis date: | December 31, 2020, 00:15:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 43085603A0706882A4FB79E442763E8B |
| SHA1: | 65A99E4C64EB7615DFBAA9519CCC5031390D9B3A |
| SHA256: | FAAE421A6E1110AC673B9886A5DC254F84AA220AC7FCC23A94C23464098B1014 |
| SSDEEP: | 49152:TuSznLTkFSLLu50ajJJWvTRUvD2X1ZURlS/QxFDo5qzcHj5/Px38re:CSHTkFSLLu50A4rWrsZU6/eDIqwD5/pD |
MALICIOUS
Runs PING.EXE for delay simulation
- mshta.exe (PID: 2060)
SUSPICIOUS
Application launched itself
- 3.5.5_45852.exe (PID: 1844)
Creates files in the user directory
- 3.5.5_45852.exe (PID: 2492)
- 3.5.5_45852.exe (PID: 1844)
Starts MSHTA.EXE for opening HTA or HTMLS files
- 3.5.5_45852.exe (PID: 2492)
Executes scripts
- mshta.exe (PID: 2060)
Checks for external IP
- mshta.exe (PID: 2060)
INFO
Reads internet explorer settings
- mshta.exe (PID: 2060)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (43.5) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (42.7) |
| .exe | | | Win32 Executable (generic) (7.2) |
| .exe | | | Generic Win/DOS Executable (3.2) |
| .exe | | | DOS Executable Generic (3.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:12:09 01:05:14+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 2002944 |
| InitializedDataSize: | 126976 |
| UninitializedDataSize: | 3616768 |
| EntryPoint: | 0x55b690 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.5.5.45852 |
| ProductVersionNumber: | 3.5.5.45852 |
| FileFlagsMask: | 0x002b |
| FileFlags: | Special build |
| FileOS: | Unknown (0) |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
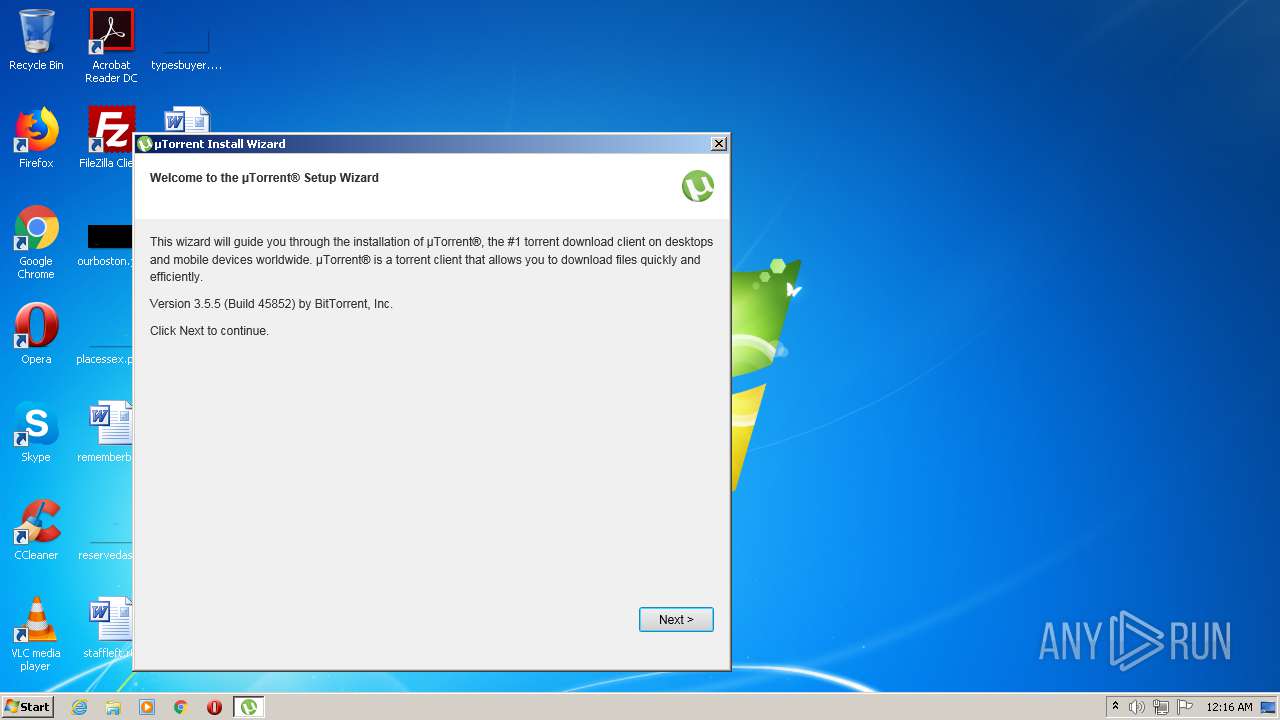
| CompanyName: | BitTorrent Inc. |
| FileDescription: | µTorrent |
| FileVersion: | 3.5.5.45852 |
| InternalName: | uTorrent.exe |
| OriginalFileName: | uTorrent.exe |
| LegalCopyright: | ©2020 BitTorrent, Inc. All Rights Reserved. |
| ProductName: | µTorrent |
| ProductVersion: | 3.5.5.45852 |
| SpecialBuild: | stable34 stable |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 09-Dec-2020 00:05:14 |
| Detected languages: |
|
| CompanyName: | BitTorrent Inc. |
| FileDescription: | µTorrent |
| FileVersion: | 3.5.5.45852 |
| InternalName: | uTorrent.exe |
| OriginalFilename: | uTorrent.exe |
| LegalCopyright: | ©2020 BitTorrent, Inc. All Rights Reserved. |
| ProductName: | µTorrent |
| ProductVersion: | 3.5.5.45852 |
| SpecialBuild: | stable34 stable |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000150 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 09-Dec-2020 00:05:14 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00373000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00374000 | 0x001E9000 | 0x001E8400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99987 |
.rsrc | 0x0055D000 | 0x0001F000 | 0x0001F000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.99174 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.11079 | 1835 | UNKNOWN | Swedish - Sweden | RT_MANIFEST |
2 | 7.78815 | 1003 | UNKNOWN | Swedish - Sweden | RT_HTML |
3 | 5.72839 | 62 | UNKNOWN | Swedish - Sweden | RT_GROUP_ICON |
4 | 7.98134 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 4.32193 | 20 | UNKNOWN | Swedish - Sweden | RT_GROUP_ICON |
6 | 7.9823 | 9640 | UNKNOWN | English - United States | RT_ICON |
7 | 7.97789 | 9640 | UNKNOWN | English - United States | RT_ICON |
8 | 7.98195 | 9640 | UNKNOWN | English - United States | RT_ICON |
9 | 7.98016 | 9640 | UNKNOWN | English - United States | RT_ICON |
10 | 6.49061 | 114 | UNKNOWN | Swedish - Sweden | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
DNSAPI.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.DLL |
MSIMG32.dll |
OLEAUT32.dll |
PSAPI.DLL |
Total processes
46
Monitored processes
6
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1844 | "C:\Users\admin\AppData\Local\Temp\3.5.5_45852.exe" | C:\Users\admin\AppData\Local\Temp\3.5.5_45852.exe | explorer.exe | ||||||||||||
User: admin Company: BitTorrent Inc. Integrity Level: MEDIUM Description: µTorrent Exit code: 0 Version: 3.5.5.45852 Modules
| |||||||||||||||
| 2060 | "C:\Windows\System32\mshta.exe" "C:\Users\admin\AppData\Local\Temp\HYD3373.tmp.1609373763\HTA\index.hta?utorrent" "C:\Users\admin\AppData\Local\Temp\3.5.5_45852.exe" /LOG "C:\Users\admin\AppData\Local\Temp\HYD3373.tmp.1609373763\index.hta.log" /PID "2492" /CID "Gkr0xblGvZABvBKz" /VERSION "111915804" /BUCKET "0" /SSB "8" /COUNTRY "US" /OS "6.1" /BROWSERS "\"C:\Program Files\Mozilla Firefox\firefox.exe\",\"C:\Program Files\Google\Chrome\Application\chrome.exe\",C:\Program Files\Internet Explorer\iexplore.exe,\"C:\Program Files\Opera\Opera.exe\"" /ARCHITECTURE "32" /LANG "en" /USERNAME "admin" /SID "S-1-5-21-1302019708-1500728564-335382590-1000" /CLIENT "utorrent" | C:\Windows\System32\mshta.exe | 3.5.5_45852.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2492 | "C:\Users\admin\AppData\Local\Temp\3.5.5_45852.exe" /HYDRA_PERMISSIONS_RESTART /HYDRA_LOG "C:\Users\admin\AppData\Local\Temp\HYD3373.tmp.1609373763\index.hta.log" /HYDRA_HTADIR "C:\Users\admin\AppData\Local\Temp\HYD3373.tmp.1609373763\HTA" | C:\Users\admin\AppData\Local\Temp\3.5.5_45852.exe | 3.5.5_45852.exe | ||||||||||||
User: admin Company: BitTorrent Inc. Integrity Level: HIGH Description: µTorrent Exit code: 0 Version: 3.5.5.45852 Modules
| |||||||||||||||
| 2824 | "C:\Windows\System32\PING.EXE" 8.8.8.8 -n 2 -w 500 | C:\Windows\System32\PING.EXE | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3228 | "C:\Windows\System32\cscript.exe" "shell_scripts/check_if_cscript_is_working.js" | C:\Windows\System32\cscript.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 99 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 4084 | "C:\Windows\System32\cscript.exe" shell_scripts/shell_ping_after_close.js "http://i-50.b-000.XYZ.bench.utorrent.com/e?i=50&e=eyJldmVudE5hbWUiOiJoeWRyYTEiLCJhY3Rpb24iOiJodGFiZWdpbiIsInBpZCI6IjI0OTIiLCJoIjoiR2tyMHhibEd2WkFCdkJLeiIsInYiOiIxMTE5MTU4MDQiLCJiIjo0NTg1MiwiY2wiOiJ1VG9ycmVudCIsIm9zYSI6IjMyIiwic2xuZyI6ImVuIiwiZGIiOiJJbnRlcm5ldCBFeHBsb3JlciIsImRidiI6IjExLjAiLCJpYnIiOlt7Im5hbWUiOiJGaXJlZm94IiwidmVyc2lvbiI6IjY4LjAiLCJleGVOYW1lIjoiZmlyZWZveCJ9LHsibmFtZSI6Ikdvb2dsZSBDaHJvbWUiLCJ2ZXJzaW9uIjoiNzUuMCIsImV4ZU5hbWUiOiJjaHJvbWUifSx7Im5hbWUiOiJJbnRlcm5ldCBFeHBsb3JlciIsInZlcnNpb24iOiIxMS4wIiwiZXhlTmFtZSI6ImlleHBsb3JlIn0seyJuYW1lIjoiT3BlcmEgSW50ZXJuZXQgQnJvd3NlciIsInZlcnNpb24iOiIxMi4xNSIsImV4ZU5hbWUiOiJvcGVyYSJ9XSwiaXAiOiI0NS4xMzUuMTg3LjMwIiwiY24iOiJTd2VkZW4iLCJwYWNraWQiOiJsYXZhc29mdF9iaW5nIn0=" | C:\Windows\System32\cscript.exe | mshta.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
619
Read events
590
Write events
29
Delete events
0
Modification events
| (PID) Process: | (1844) 3.5.5_45852.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1844) 3.5.5_45852.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1844) 3.5.5_45852.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1844) 3.5.5_45852.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2060) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2060) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2060) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2060) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2060) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2492) 3.5.5_45852.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
0
Suspicious files
7
Text files
31
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1844 | 3.5.5_45852.exe | C:\Users\admin\AppData\Local\Temp\utt31FB.tmp | — | |
MD5:— | SHA256:— | |||
| 1844 | 3.5.5_45852.exe | C:\Users\admin\AppData\Roaming\uTorrent\settings.dat.new | — | |
MD5:— | SHA256:— | |||
| 1844 | 3.5.5_45852.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1302019708-1500728564-335382590-1000\1f91d2d17ea675d4c2c3192e241743f9_90059c37-1320-41a4-b58d-2b75a9850d2f | binary | |
MD5:— | SHA256:— | |||
| 1844 | 3.5.5_45852.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\H7Y9KM5W.txt | text | |
MD5:— | SHA256:— | |||
| 1844 | 3.5.5_45852.exe | C:\Users\admin\AppData\Roaming\uTorrent\settings.dat | binary | |
MD5:— | SHA256:— | |||
| 1844 | 3.5.5_45852.exe | C:\Users\admin\AppData\Local\Temp\HYD3373.tmp.1609373763\index.hta.log | text | |
MD5:2B632A88AF93F552846FDBF6890E8613 | SHA256:2B1D8F74B6B7EF3811B62E9320953577A736ED64AB9DD5C3E2390D994A10D234 | |||
| 1844 | 3.5.5_45852.exe | C:\Users\admin\AppData\Local\Temp\HYD3373.tmp.1609373763\HTA\i18n\fr.json | html | |
MD5:D126F1776772BE7164691F18B9FCB041 | SHA256:0416441F460D82C68525EB15CB72E6B260433E509AEDCD4ABDB1326C6D242A7D | |||
| 1844 | 3.5.5_45852.exe | C:\Users\admin\AppData\Local\Temp\HYD3373.tmp.1609373763\HTA\i18n\pt.json | html | |
MD5:FB63D52AC25CD3D272365FA75F74C279 | SHA256:E39D6A57D2F16E60C4075D07741DADD6A2742A85ACEB250083D7AB103279F737 | |||
| 1844 | 3.5.5_45852.exe | C:\Users\admin\AppData\Local\Temp\HYD3373.tmp.1609373763\HTA\i18n\ko.json | html | |
MD5:F9FEB32431F5064F711B87C31CCC8AC0 | SHA256:6CCE352F8426A6CB2D41D5D108658CFA1244F0142D6F60BC96E3C4C2904913C3 | |||
| 1844 | 3.5.5_45852.exe | C:\Users\admin\AppData\Local\Temp\HYD3373.tmp.1609373763\HTA\i18n\ru.json | html | |
MD5:4F268BCA1F6AF01246F257A141CEC972 | SHA256:28B880822283482194EA9B4B94552A94E35F659CF026F592173ED46FCF3A91F4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
14
DNS requests
7
Threats
28
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2060 | mshta.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json?callback=jQuery191019132371119621505_1609373770982&_=1609373770983 | unknown | text | 343 b | malicious |
1844 | 3.5.5_45852.exe | POST | 200 | 23.21.43.186:80 | http://i-50.b-000.xyz.bench.utorrent.com/e?i=50 | US | text | 21 b | whitelisted |
1844 | 3.5.5_45852.exe | POST | 200 | 23.21.43.186:80 | http://i-50.b-000.xyz.bench.utorrent.com/e?i=50 | US | text | 21 b | whitelisted |
1844 | 3.5.5_45852.exe | POST | 200 | 23.21.43.186:80 | http://i-50.b-000.xyz.bench.utorrent.com/e?i=50 | US | text | 21 b | whitelisted |
1844 | 3.5.5_45852.exe | POST | 200 | 23.21.43.186:80 | http://i-50.b-000.xyz.bench.utorrent.com/e?i=50 | US | text | 21 b | whitelisted |
4084 | cscript.exe | GET | 200 | 23.21.43.186:80 | http://i-50.b-000.xyz.bench.utorrent.com/e?i=50&e=eyJldmVudE5hbWUiOiJoeWRyYTEiLCJhY3Rpb24iOiJodGFiZWdpbiIsInBpZCI6IjI0OTIiLCJoIjoiR2tyMHhibEd2WkFCdkJLeiIsInYiOiIxMTE5MTU4MDQiLCJiIjo0NTg1MiwiY2wiOiJ1VG9ycmVudCIsIm9zYSI6IjMyIiwic2xuZyI6ImVuIiwiZGIiOiJJbnRlcm5ldCBFeHBsb3JlciIsImRidiI6IjExLjAiLCJpYnIiOlt7Im5hbWUiOiJGaXJlZm94IiwidmVyc2lvbiI6IjY4LjAiLCJleGVOYW1lIjoiZmlyZWZveCJ9LHsibmFtZSI6Ikdvb2dsZSBDaHJvbWUiLCJ2ZXJzaW9uIjoiNzUuMCIsImV4ZU5hbWUiOiJjaHJvbWUifSx7Im5hbWUiOiJJbnRlcm5ldCBFeHBsb3JlciIsInZlcnNpb24iOiIxMS4wIiwiZXhlTmFtZSI6ImlleHBsb3JlIn0seyJuYW1lIjoiT3BlcmEgSW50ZXJuZXQgQnJvd3NlciIsInZlcnNpb24iOiIxMi4xNSIsImV4ZU5hbWUiOiJvcGVyYSJ9XSwiaXAiOiI0NS4xMzUuMTg3LjMwIiwiY24iOiJTd2VkZW4iLCJwYWNraWQiOiJsYXZhc29mdF9iaW5nIn0= | US | text | 21 b | whitelisted |
1844 | 3.5.5_45852.exe | POST | 200 | 23.21.43.186:80 | http://i-50.b-000.xyz.bench.utorrent.com/e?i=50 | US | text | 21 b | whitelisted |
1844 | 3.5.5_45852.exe | POST | 200 | 23.21.43.186:80 | http://i-50.b-000.xyz.bench.utorrent.com/e?i=50 | US | text | 21 b | whitelisted |
2492 | 3.5.5_45852.exe | POST | 200 | 23.21.43.186:80 | http://i-50.b-000.xyz.bench.utorrent.com/e?i=50 | US | text | 21 b | whitelisted |
2492 | 3.5.5_45852.exe | POST | 200 | 23.21.43.186:80 | http://i-50.b-000.xyz.bench.utorrent.com/e?i=50 | US | text | 21 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1844 | 3.5.5_45852.exe | 174.129.255.167:80 | i-50.b-000.xyz.bench.utorrent.com | Amazon.com, Inc. | US | whitelisted |
1844 | 3.5.5_45852.exe | 23.21.43.186:80 | i-50.b-000.xyz.bench.utorrent.com | Amazon.com, Inc. | US | malicious |
1844 | 3.5.5_45852.exe | 23.23.215.82:80 | i-50.b-000.xyz.bench.utorrent.com | Amazon.com, Inc. | US | whitelisted |
1844 | 3.5.5_45852.exe | 67.215.238.66:80 | download-lb.utorrent.com | QuadraNet, Inc | US | suspicious |
2492 | 3.5.5_45852.exe | 23.21.43.186:80 | i-50.b-000.xyz.bench.utorrent.com | Amazon.com, Inc. | US | malicious |
2060 | mshta.exe | 208.95.112.1:80 | ip-api.com | IBURST | — | malicious |
4084 | cscript.exe | 23.21.43.186:80 | i-50.b-000.xyz.bench.utorrent.com | Amazon.com, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
router.bittorrent.com |
| shared |
router.utorrent.com |
| whitelisted |
i-50.b-000.xyz.bench.utorrent.com |
| whitelisted |
download-lb.utorrent.com |
| whitelisted |
ip-api.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1844 | 3.5.5_45852.exe | Misc activity | APP [PTsecurity] uTorrent Hydra Client |
1844 | 3.5.5_45852.exe | Misc activity | APP [PTsecurity] P2P uTorrent Hydra Client |
1844 | 3.5.5_45852.exe | Misc activity | APP [PTsecurity] uTorrent Hydra Client |
1844 | 3.5.5_45852.exe | Misc activity | APP [PTsecurity] uTorrent Hydra Client |
1844 | 3.5.5_45852.exe | Misc activity | APP [PTsecurity] P2P uTorrent Hydra Client |
1844 | 3.5.5_45852.exe | Misc activity | APP [PTsecurity] uTorrent Hydra Client |
1844 | 3.5.5_45852.exe | Misc activity | APP [PTsecurity] P2P uTorrent Hydra Client |
1844 | 3.5.5_45852.exe | Misc activity | APP [PTsecurity] uTorrent Hydra Client |
1844 | 3.5.5_45852.exe | Misc activity | APP [PTsecurity] uTorrent Hydra Client |
1844 | 3.5.5_45852.exe | Misc activity | APP [PTsecurity] P2P uTorrent Hydra Client |
11 ETPRO signatures available at the full report