| File name: | QSGhuPnjsCCS.dll |
| Full analysis: | https://app.any.run/tasks/ba340d57-f21f-46e6-806c-77ef271443ef |
| Verdict: | Malicious activity |
| Analysis date: | February 18, 2019, 14:49:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows |
| MD5: | 66F8D937B73CDF6D0DD8845C135366DF |
| SHA1: | C51CE05064CE13607AEC3C0468499BF454C2758D |
| SHA256: | FA9C817632A2D15BC385DD1498B2D6FE9C6A7473BB4C30534C2E80B1BB84FAB1 |
| SSDEEP: | 12288:CMVHOt9dmiJlSYSjIvy5Q9Y9TdZYJsF2Huk8kSoYtlxTsyLoFEaTdV6MEr+WIcLG:C0ORPhodT79mJd03LtS |
MALICIOUS
Loads dropped or rewritten executable
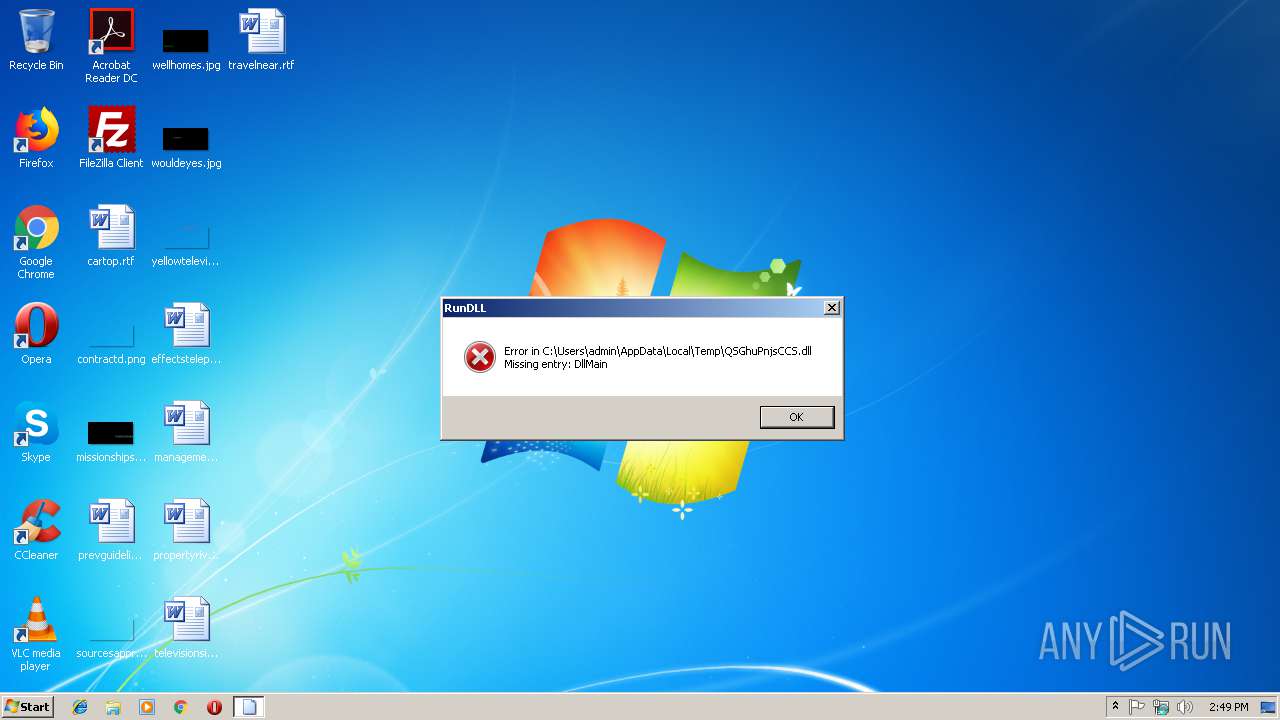
- rundll32.exe (PID: 3904)
SUSPICIOUS
Uses RUNDLL32.EXE to load library
- rundll32.exe (PID: 3000)
Application launched itself
- rundll32.exe (PID: 3000)
INFO
Loads main object executable
- rundll32.exe (PID: 3000)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:02:17 22:52:23+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 52736 |
| InitializedDataSize: | 514048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xd800 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 17-Feb-2019 21:52:23 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 17-Feb-2019 21:52:23 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000CDD6 | 0x0000CE00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.07565 |
.rdata | 0x0000E000 | 0x00000342 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.65488 |
.data | 0x0000F000 | 0x0007B400 | 0x00079600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.21309 |
.reloc | 0x0008B000 | 0x00001FEC | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.8086 |
Imports
KERNEL32.dll |
Total processes
31
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3000 | "C:\Windows\System32\rundll32.exe" "C:\Users\admin\AppData\Local\Temp\QSGhuPnjsCCS.dll", DllMain | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3904 | C:\Windows\system32\\rundll32.exe C:\Users\admin\AppData\Local\Temp\QSGhuPnjsCCS.dll,f0 | C:\Windows\system32\rundll32.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
8
Read events
8
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
10
DNS requests
2
Threats
8
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3904 | rundll32.exe | 185.92.222.238:443 | — | Choopa, LLC | NL | malicious |
3904 | rundll32.exe | 223.200.225.25:443 | — | Data Communication Business Group | TW | unknown |
3904 | rundll32.exe | 109.123.212.126:443 | — | Casablanca INT | CZ | malicious |
3904 | rundll32.exe | 123.163.78.191:443 | — | No.31,Jin-rong Street | CN | malicious |
3904 | rundll32.exe | 14.218.73.172:443 | — | CHINANET Guangdong province Dongguan MAN network | CN | unknown |
3904 | rundll32.exe | 196.206.27.37:443 | — | Itissalat Al-MAGHRIB | MA | malicious |
3904 | rundll32.exe | 192.71.249.51:443 | — | lcp nv | BE | malicious |
3904 | rundll32.exe | 3.65.134.9:443 | — | — | US | unknown |
3904 | rundll32.exe | 190.153.193.171:443 | — | Manquehuenet | CL | malicious |
3904 | rundll32.exe | 177.113.71.107:443 | — | TELEFÔNICA BRASIL S.A | BR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3904 | rundll32.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Spy.Danabot.I |
3904 | rundll32.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Spy.Danabot.I |
3904 | rundll32.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Spy.Danabot.I |
3904 | rundll32.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Spy.Danabot.I |
3904 | rundll32.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Spy.Danabot.I |
3904 | rundll32.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Spy.Danabot.I |
3904 | rundll32.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Spy.Danabot.I |
3904 | rundll32.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/Spy.Danabot.I |