| URL: | https://storage.googleapis.com/mabololoxy/besales24.html#?Z289MSZzMT0xODgzMTI5JnMyPTE0NTA4NjY3NCZzMz1HTEI= |
| Full analysis: | https://app.any.run/tasks/6eaf5775-9d4a-46d3-9cb4-6d818a264e3f |
| Verdict: | Malicious activity |
| Analysis date: | May 21, 2024, 08:54:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 0B44911C0AB9A46D4072C1C3B2C121F9 |
| SHA1: | 4B3FEBA73BE2853EE9F15A443A296E7FFD32609B |
| SHA256: | FA98F5D6383F8D7AE55302AF80BB28A3021E995F87F3845F3135DC1903B599B9 |
| SSDEEP: | 3:N8cMECYKKhmHfFEJG7HzEOiaGXoTTAJ1iu7y4f0x2:2cMLZHfFgGDzEjnoTTAJxXfX |
MALICIOUS
PHISHING has been detected (SURICATA)
- iexplore.exe (PID: 4040)
SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 3976)
Reads the computer name
- wmpnscfg.exe (PID: 312)
Manual execution by a user
- wmpnscfg.exe (PID: 312)
Checks supported languages
- wmpnscfg.exe (PID: 312)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
35
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3976 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://storage.googleapis.com/mabololoxy/besales24.html#?Z289MSZzMT0xODgzMTI5JnMyPTE0NTA4NjY3NCZzMz1HTEI=" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 4040 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3976 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
19 474
Read events
19 245
Write events
117
Delete events
112
Modification events
| (PID) Process: | (3976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31107932 | |||
| (PID) Process: | (3976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31107932 | |||
| (PID) Process: | (3976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3976) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
17
Text files
8
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4040 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:9AF7166E75A869B17D65752791D3C19F | SHA256:4E94931E18D281FFEF1AAA152FDC21973AD83ACA24C2CF505FE0F082456001A5 | |||
| 4040 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | der | |
MD5:822467B728B7A66B081C91795373789A | SHA256:AF2343382B88335EEA72251AD84949E244FF54B6995063E24459A7216E9576B9 | |||
| 4040 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\besales24[1].htm | html | |
MD5:20ECC5056E6040E662BA32D5A03AADE5 | SHA256:D1726B8EDDB15B58A36279057B23A7A280B99CAB9DB37BD57F9A7432B0B58875 | |||
| 4040 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:EDBBBE4F3EEEEF2DF5FD61C1594CB647 | SHA256:07E5A45DE0274E567FDEA7FC87F7832DD67008D7E75D19EB535ADEA0370D7E89 | |||
| 4040 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:AF3B7B913141A440F351CD5889F1DEA4 | SHA256:12D33DF611378F47D31A475B9FB967BE75B33A2403BA55165780B0D0D9307D46 | |||
| 4040 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C02877841121CC45139CB51404116B25_30B5B40563E51B58B4BB610D9DE4B44D | binary | |
MD5:6A0E0A0F1876256192E29B4D2778ED92 | SHA256:D560E40A5CC69F592FDE9568D542DCD863F7C610FD5D9343B28E0407788D84E6 | |||
| 4040 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C02877841121CC45139CB51404116B25_30B5B40563E51B58B4BB610D9DE4B44D | binary | |
MD5:BCD99E1ADFA245BC3479710477F4C660 | SHA256:41C8C39F541953D67BAED53163FCA59D6B4B74E041844C920CB4D327CC5E2117 | |||
| 3976 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\favicon[2].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 4040 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\768FFA76DFF62FE95C958265F4EA627B | der | |
MD5:2F50D80830AB1AC7DF1FBC55325F8587 | SHA256:50AC2CCB11B5DC01B8D34455F091683247D936372EA352DC224560F4EA66AB2F | |||
| 4040 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\05DDC6AA91765AACACDB0A5F96DF8199 | der | |
MD5:8D1040B12A663CA4EC7277CFC1CE44F0 | SHA256:3086094D4198A5BBD12938B0D2D5F696C4DFC77E1EAE820ADDED346A59AA8727 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
32
DNS requests
28
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4040 | iexplore.exe | GET | 304 | 199.232.210.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?d1fc3241a5fb83c4 | unknown | — | — | unknown |
4040 | iexplore.exe | GET | 200 | 142.250.186.99:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | — | — | unknown |
4040 | iexplore.exe | GET | 304 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?098b2ca3f74ef2d4 | unknown | — | — | unknown |
4040 | iexplore.exe | GET | 200 | 142.250.186.99:80 | http://c.pki.goog/r/r1.crl | unknown | — | — | unknown |
4040 | iexplore.exe | GET | 200 | 142.250.186.99:80 | http://o.pki.goog/wr2/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTQtSEi8EX%2BbYUTXd8%2ByMxD3s1zQQU3hse7XkV1D43JMMhu%2Bw0OW1CsjACEBarom1tL3iuEAq4mRr9Ufo%3D | unknown | — | — | unknown |
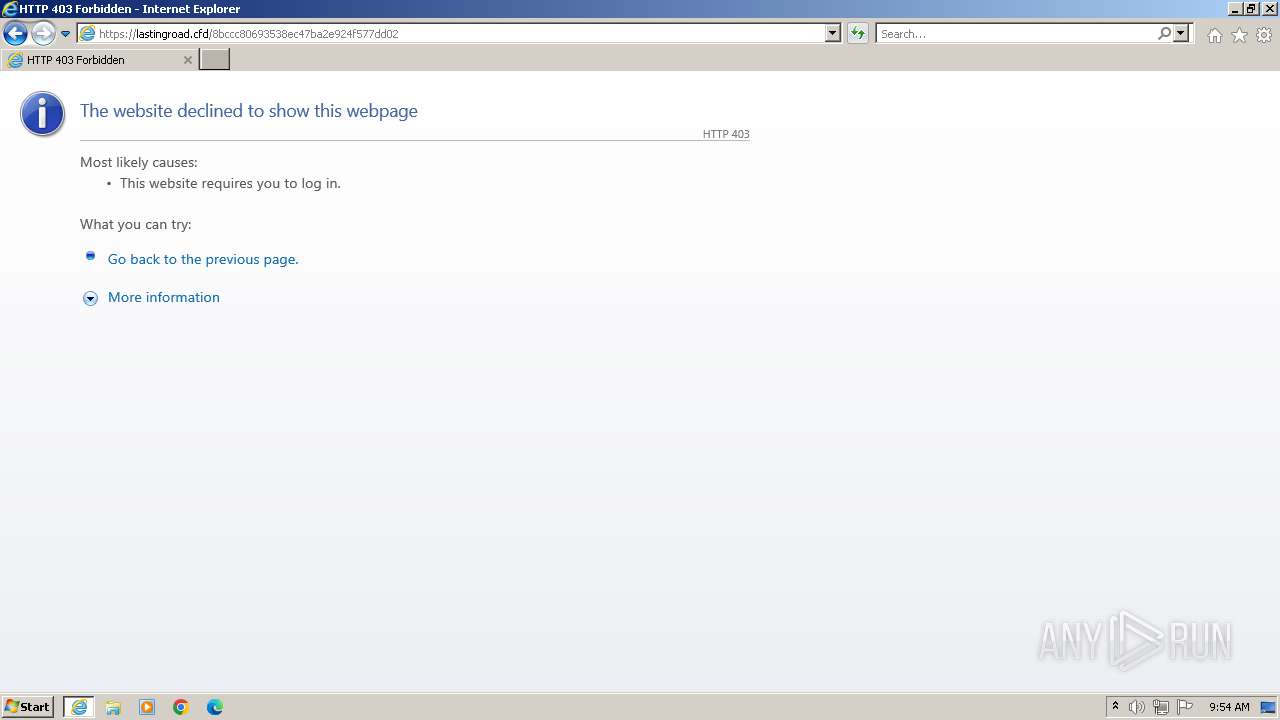
4040 | iexplore.exe | GET | 302 | 185.80.129.110:80 | http://185.80.129.110/public/?:nav=default::index&go=1&s1=1883129&s2=145086674 | unknown | — | — | unknown |
4040 | iexplore.exe | GET | 302 | 185.80.129.110:80 | http://185.80.129.110/public/?:nav=click::tracker&deploy=1883129&user=sebastiano.gasparini1%40gmail.com&email_id=145086674&url=aHR0cHM6Ly92aXNvcm1hbnRyYS5jb20vMC8yLzE4ODcyLzM0Mjk1MmYxZDAzYzZkMDQ4MDc3MzdkYTUxZGUwZTVkLzE4ODMxMjktQUQyX0FCREFBUl9TWl9HTUFJTF9QMl9JVC00NTU3NTkvMTQ1MDg2Njc0XzQ1NTc2NF8y | unknown | — | — | unknown |
4040 | iexplore.exe | GET | 302 | 185.80.129.110:80 | http://185.80.129.110/?var=Om5hdj1jbGljazo6dHJhY2tlciZkZXBsb3k9MTg4MzEyOSZ1c2VyPXNlYmFzdGlhbm8uZ2FzcGFyaW5pMSU0MGdtYWlsLmNvbSZlbWFpbF9pZD0xNDUwODY2NzQmdXJsPWFIUjBjSE02THk5MmFYTnZjbTFoYm5SeVlTNWpiMjB2TUM4eUx6RTRPRGN5THpNME1qazFNbVl4WkRBell6WmtNRFE0TURjM016ZGtZVFV4WkdVd1pUVmtMekU0T0RNeE1qa3RRVVF5WDBGQ1JFRkJVbDlUV2w5SFRVRkpURjlRTWw5SlZDMDBOVFUzTlRrdk1UUTFNRGcyTmpjMFh6UTFOVGMyTkY4eQ== | unknown | — | — | unknown |
4040 | iexplore.exe | GET | 302 | 185.80.129.110:80 | http://185.80.129.110/??Z289MSZzMT0xODgzMTI5JnMyPTE0NTA4NjY3NCZzMz1HTEI= | unknown | — | — | unknown |
4040 | iexplore.exe | GET | 200 | 95.101.54.201:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgPWCsrW2Kuw6iCGIat2lq8rXA%3D%3D | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4040 | iexplore.exe | 142.250.185.219:443 | storage.googleapis.com | GOOGLE | US | unknown |
4040 | iexplore.exe | 199.232.214.172:80 | ctldl.windowsupdate.com | FASTLY | US | unknown |
4040 | iexplore.exe | 199.232.210.172:80 | ctldl.windowsupdate.com | FASTLY | US | unknown |
4040 | iexplore.exe | 142.250.186.99:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
4040 | iexplore.exe | 185.80.129.110:80 | — | UAB ESNET | LT | unknown |
4040 | iexplore.exe | 45.141.233.55:443 | visormantra.com | Euro Crypt EOOD | DE | unknown |
4040 | iexplore.exe | 2.23.197.184:80 | x1.c.lencr.org | CW Vodafone Group PLC | GB | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
storage.googleapis.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
c.pki.goog |
| unknown |
o.pki.goog |
| unknown |
visormantra.com |
| unknown |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
persistdrum.cfd |
| unknown |
api.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4040 | iexplore.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] A suspicious URI containing an email address |