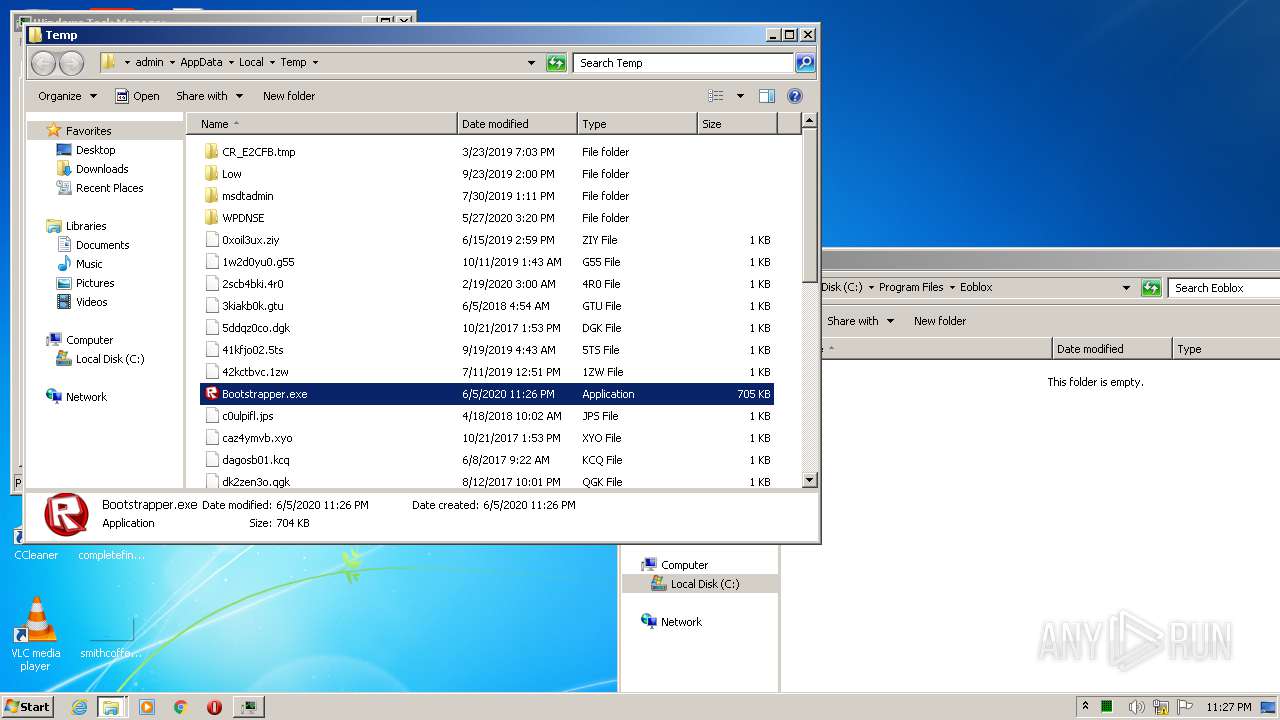
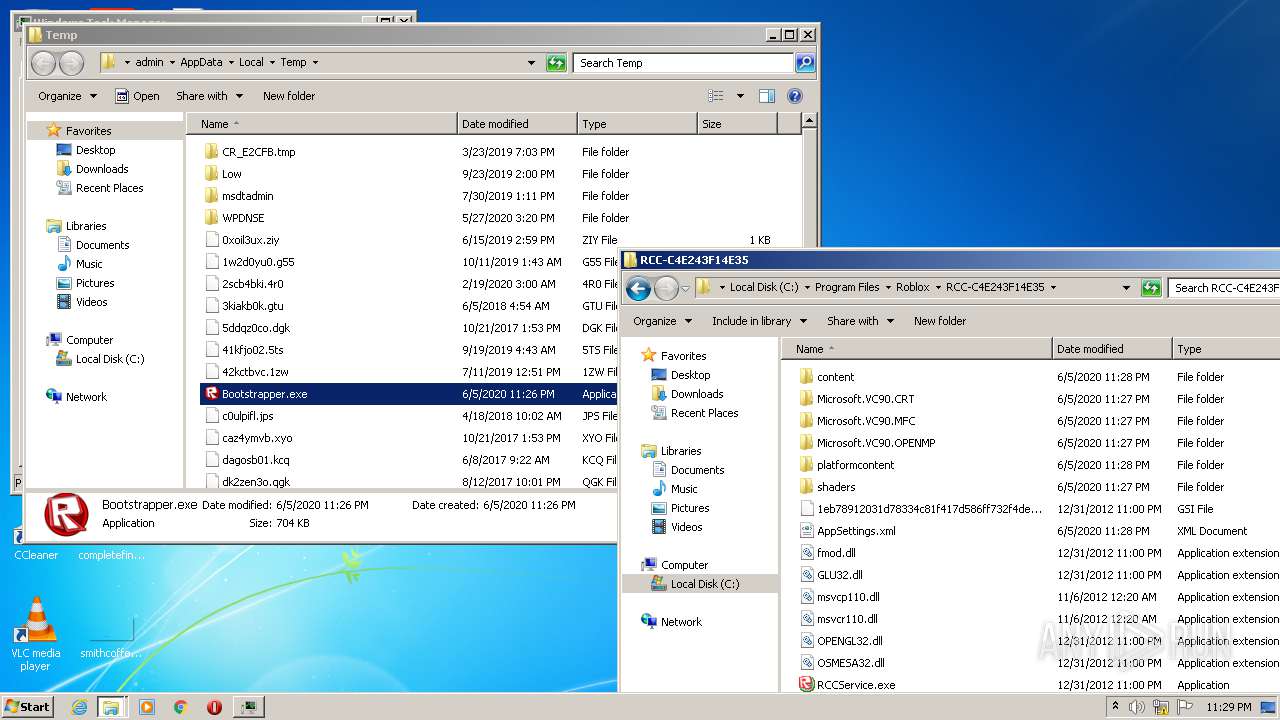
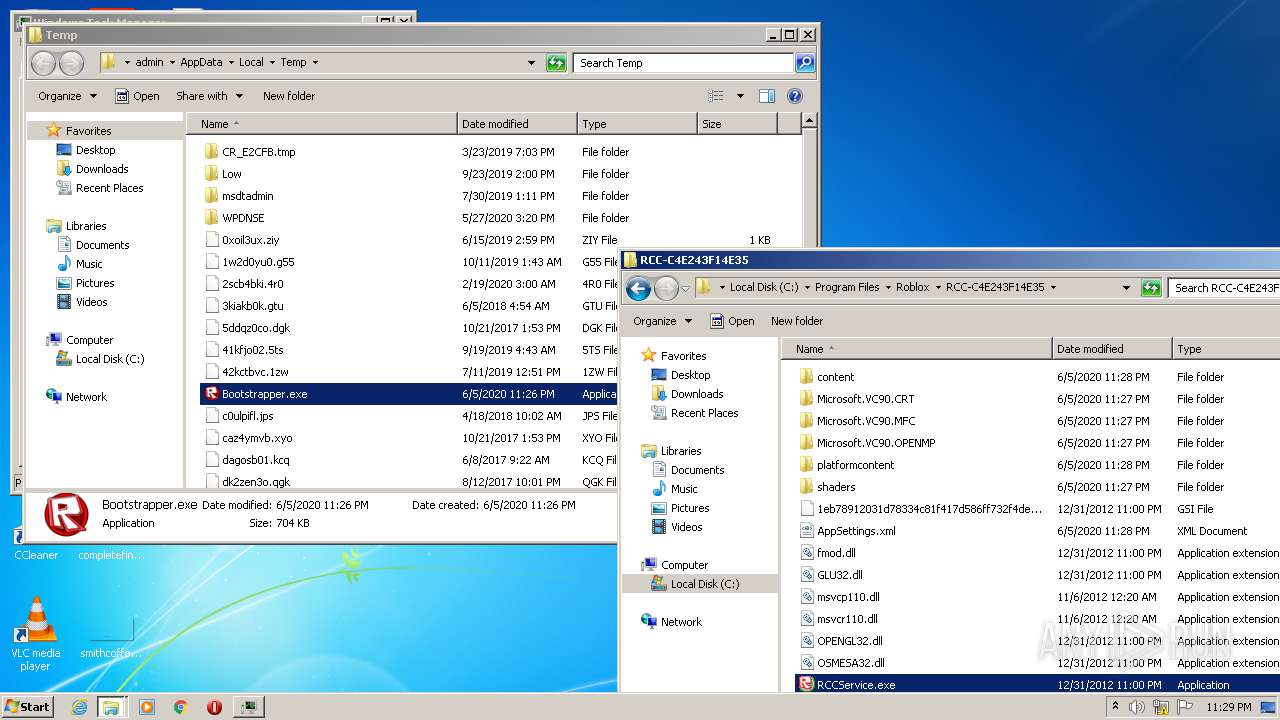
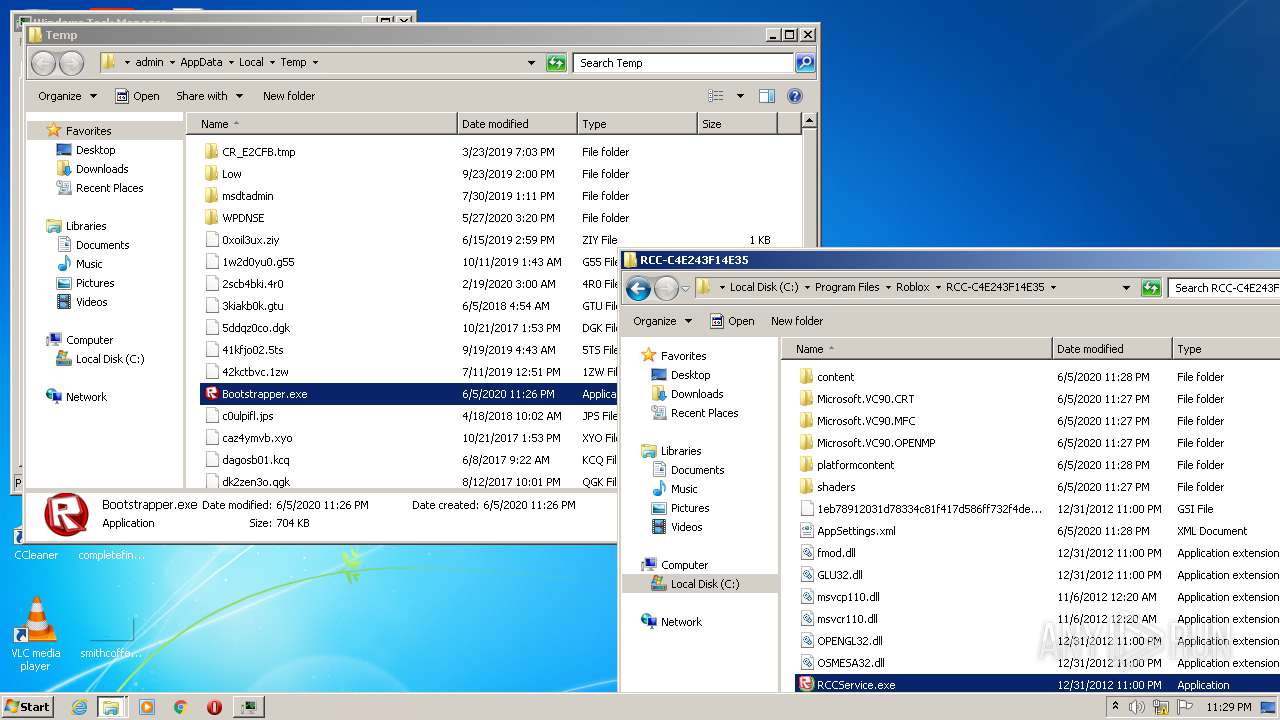
| File name: | Bootstrapper.exe |
| Full analysis: | https://app.any.run/tasks/fbcd375a-5111-4a51-b0e0-64da68385268 |
| Verdict: | Malicious activity |
| Analysis date: | June 05, 2020, 22:26:01 |
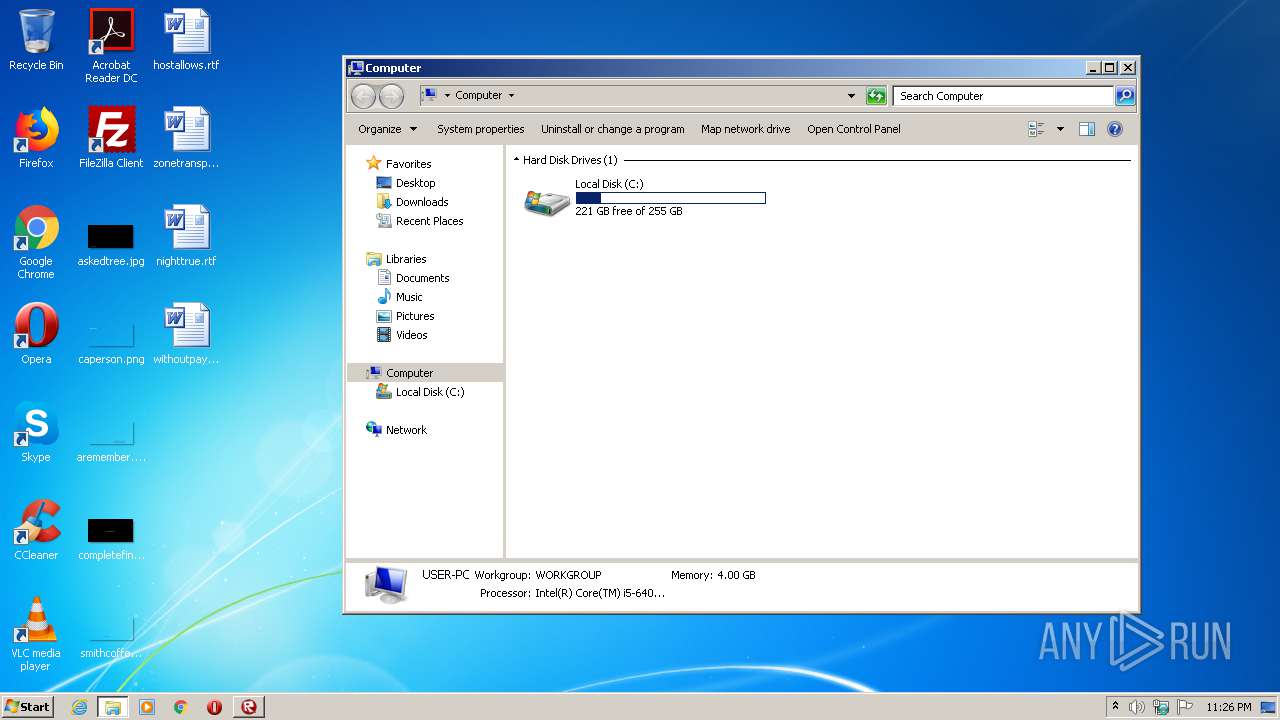
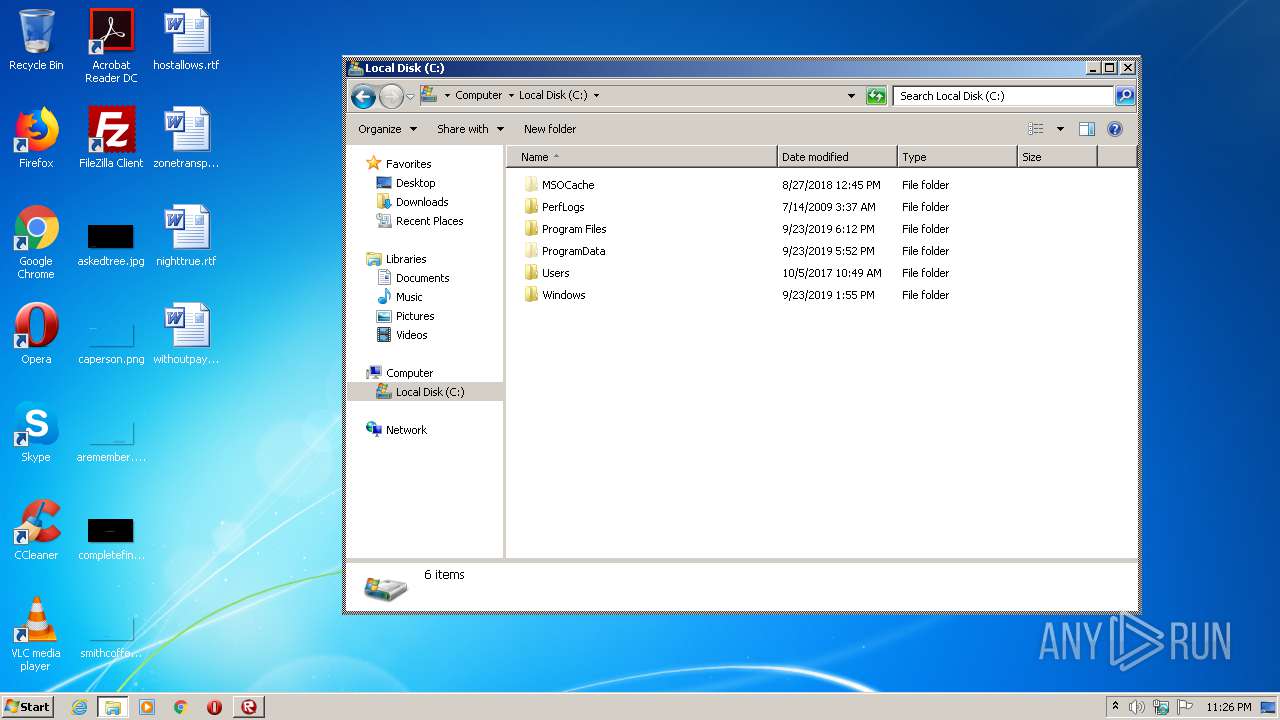
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B6D0BC4C81C6CFCAB12A93537FF044C8 |
| SHA1: | 0E6922E246438C08F8E40692BDCE695C7AECCD37 |
| SHA256: | FA887AE923B050F6D9191AC508D0083DCD67FCA457CC9E2B8251EF4583294133 |
| SSDEEP: | 12288:LcIyTivaanv0rAtXyC3v9v+GEhwPETQFDen6L7e5BJ:LcIyTiSy7X1vQGOwETkfeXJ |
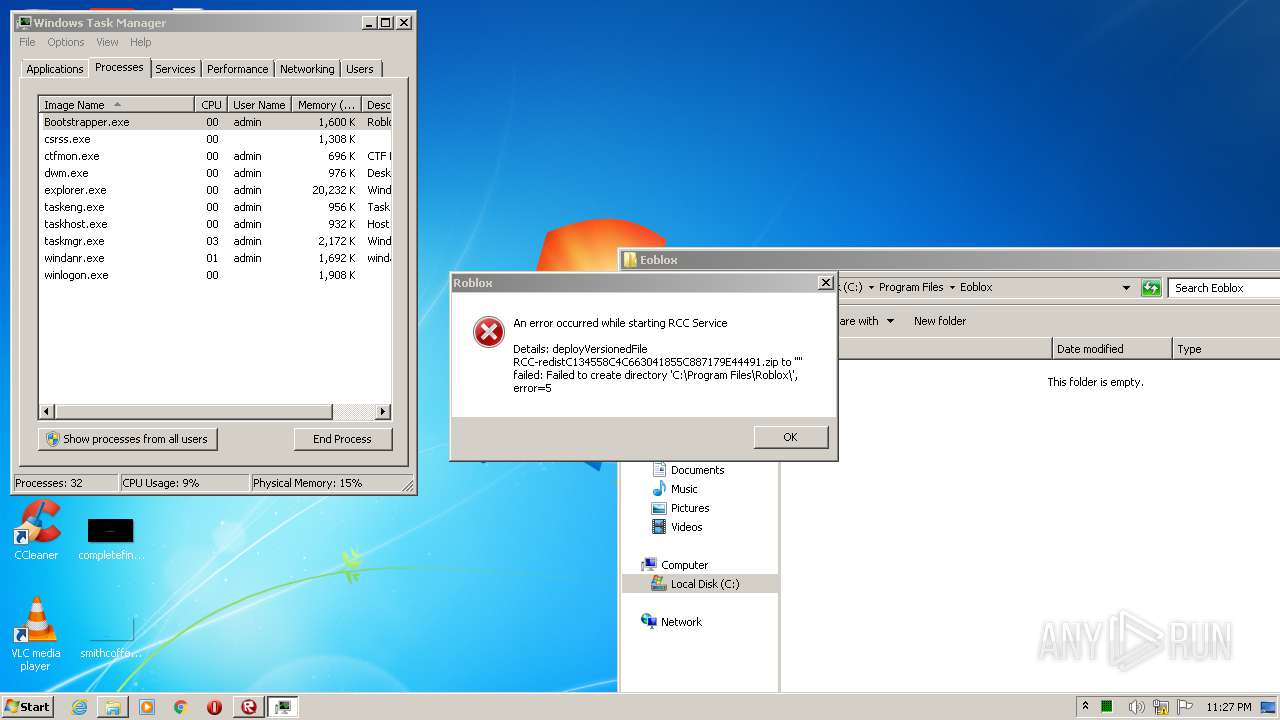
MALICIOUS
Actions looks like stealing of personal data
- explorer.exe (PID: 468)
- DllHost.exe (PID: 3388)
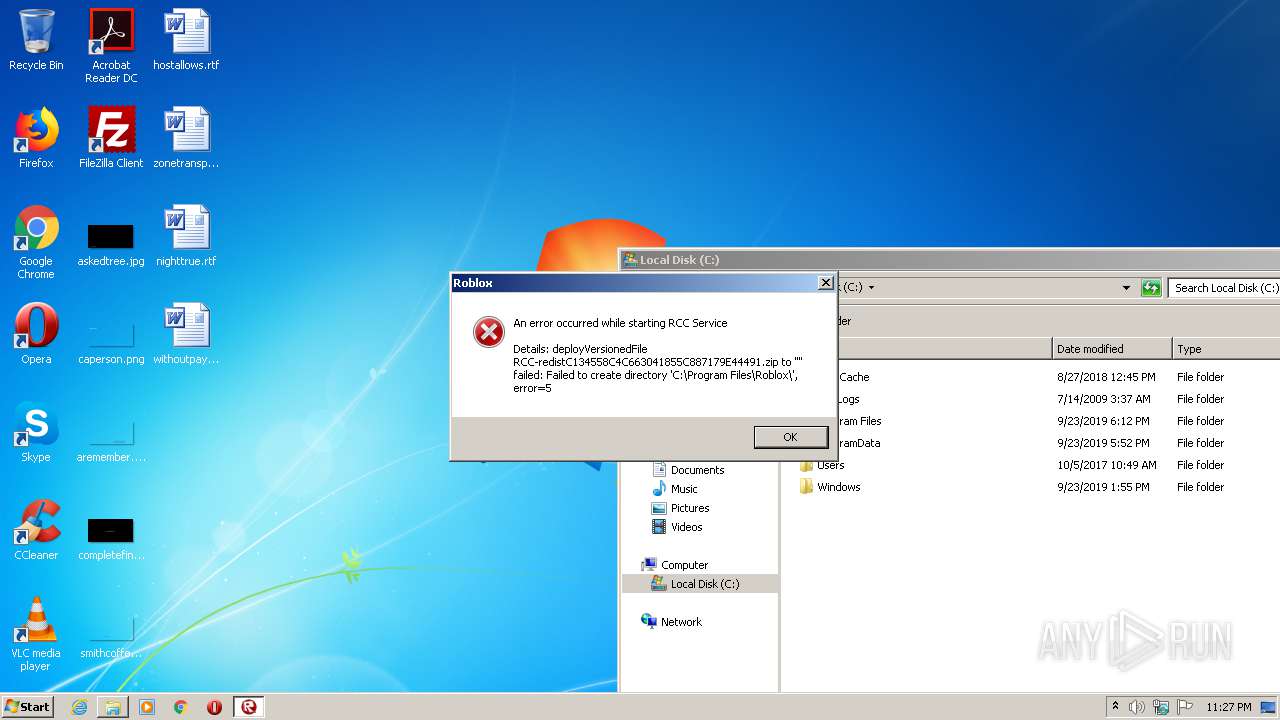
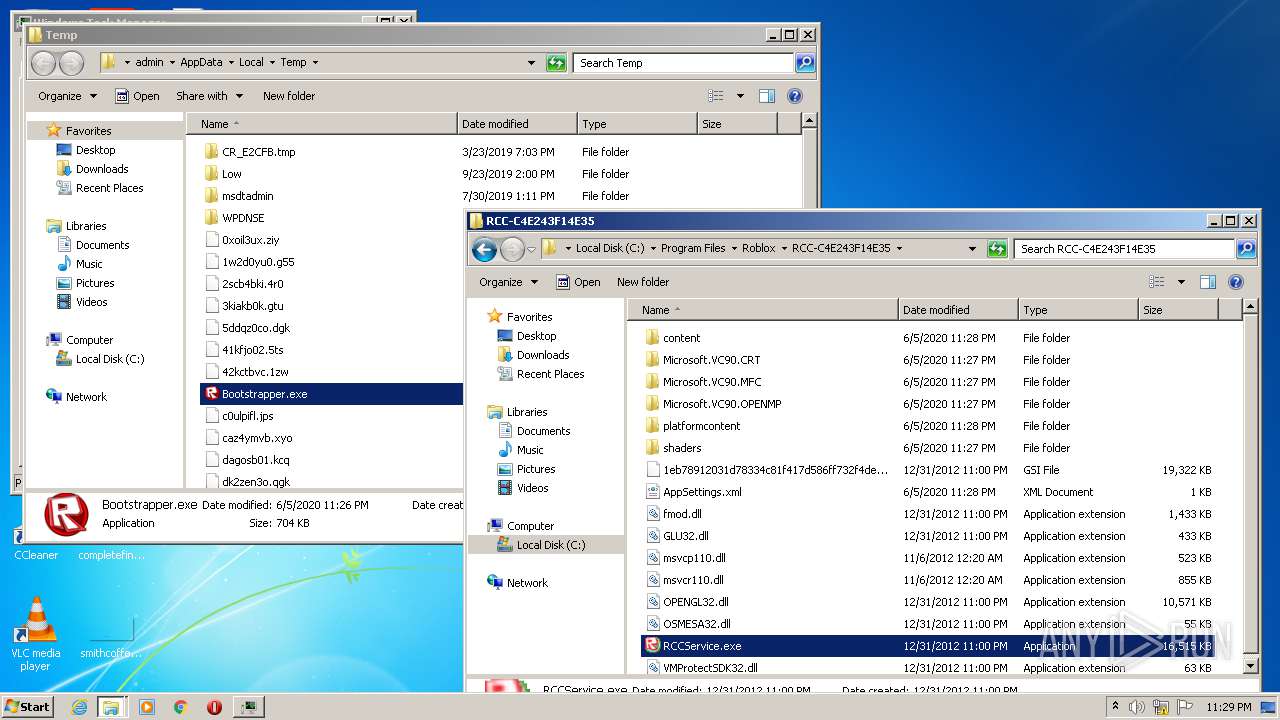
Loads dropped or rewritten executable
- RCCService.exe (PID: 2976)
- explorer.exe (PID: 468)
- RCCService.exe (PID: 2964)
- RCCService.exe (PID: 756)
- RCCService.exe (PID: 3456)
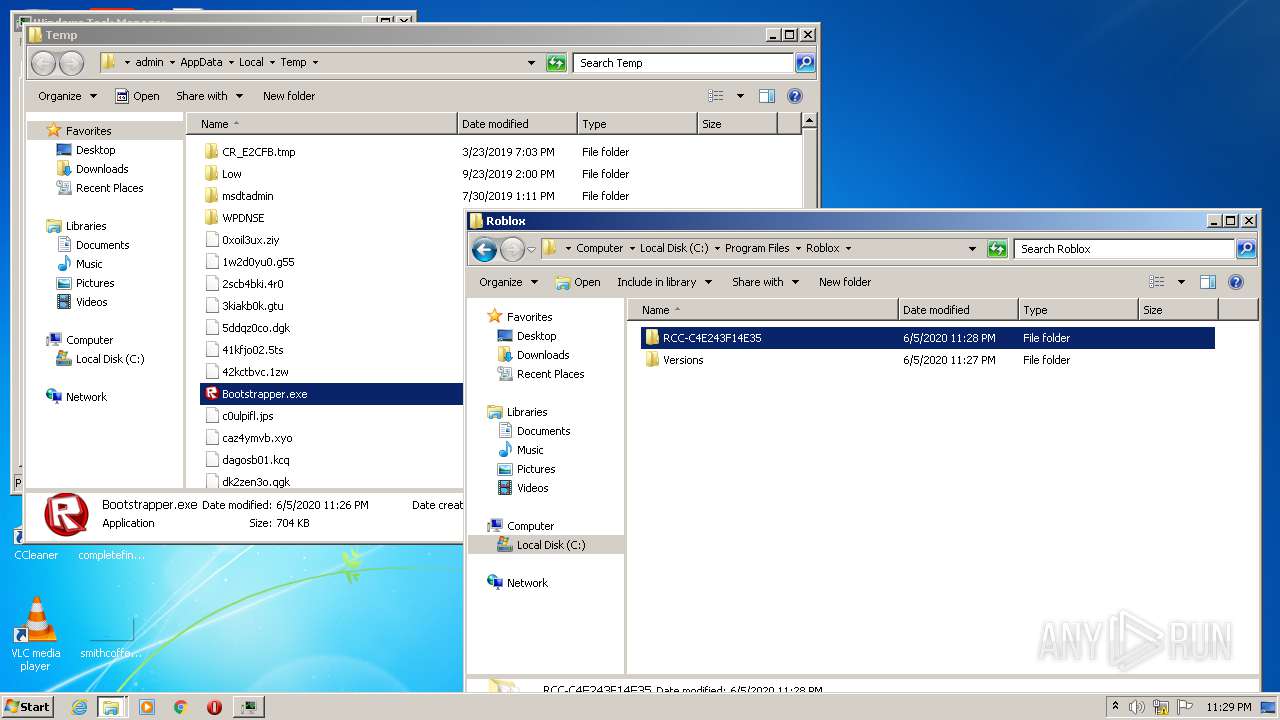
Application was dropped or rewritten from another process
- RCCService.exe (PID: 2976)
- RCCService.exe (PID: 3456)
- RCCService.exe (PID: 2964)
- RCCService.exe (PID: 756)
SUSPICIOUS
Executed via COM
- DllHost.exe (PID: 3388)
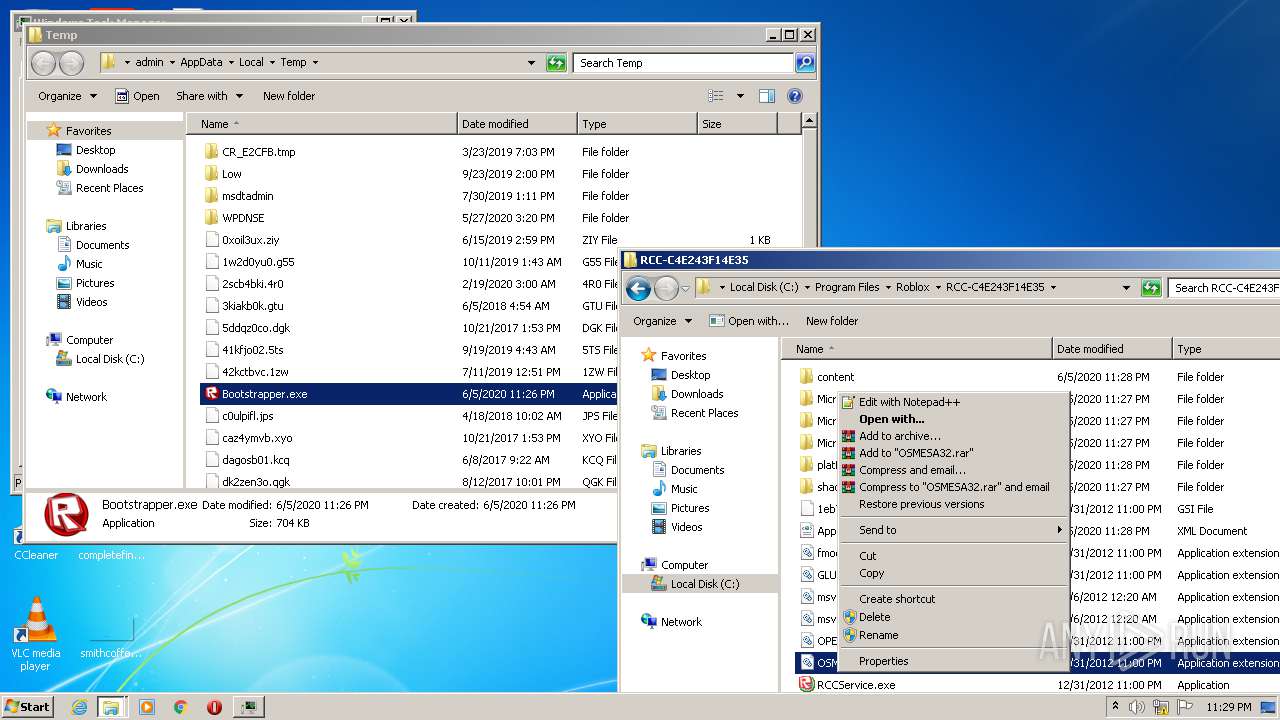
Executable content was dropped or overwritten
- Bootstrapper.exe (PID: 2240)
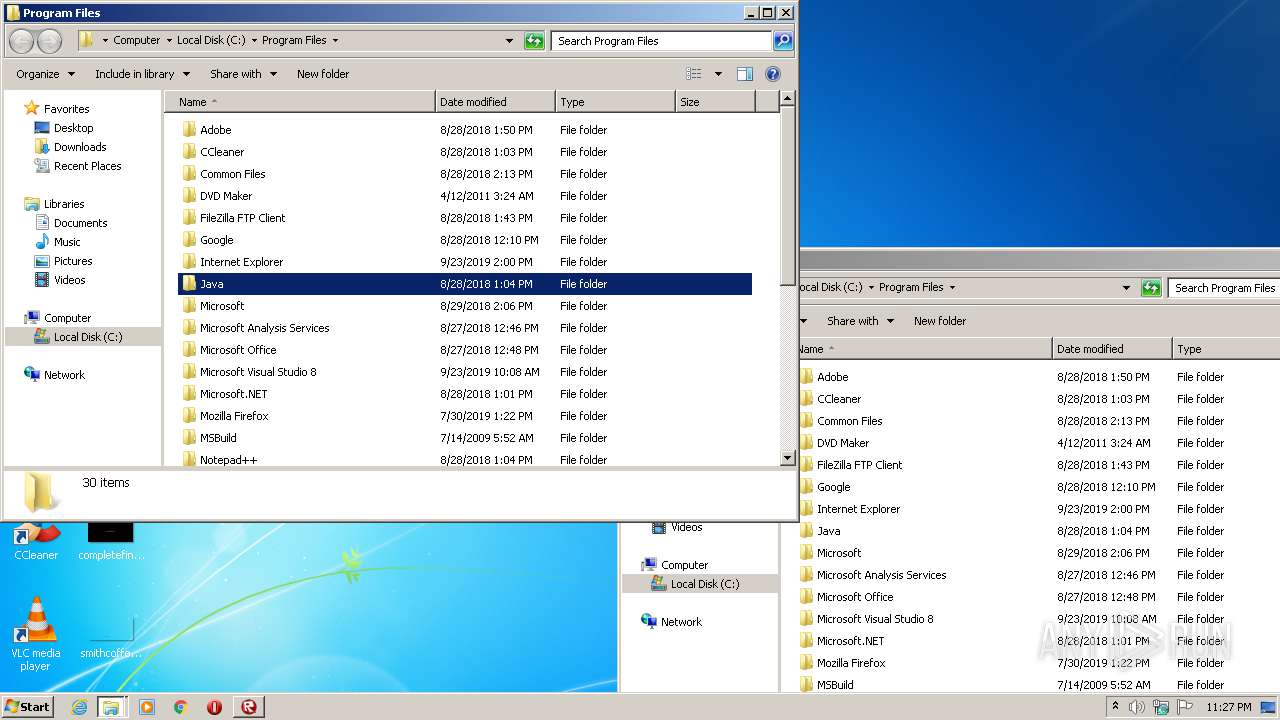
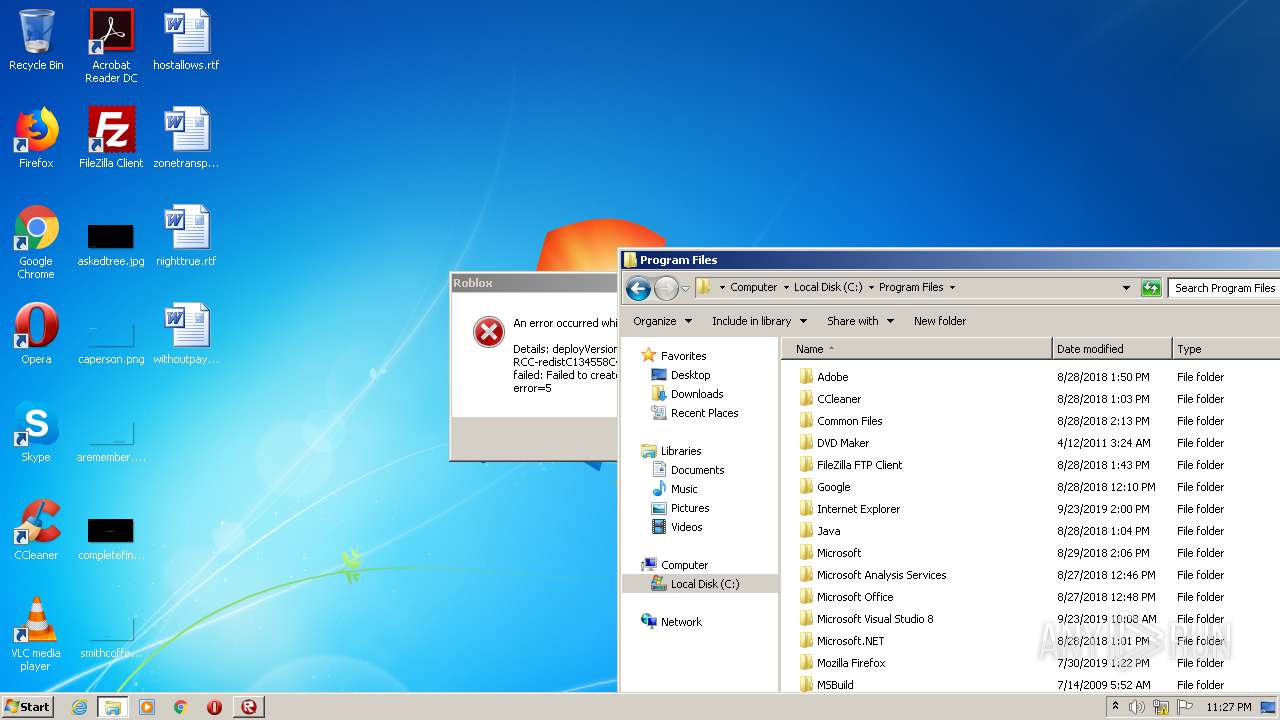
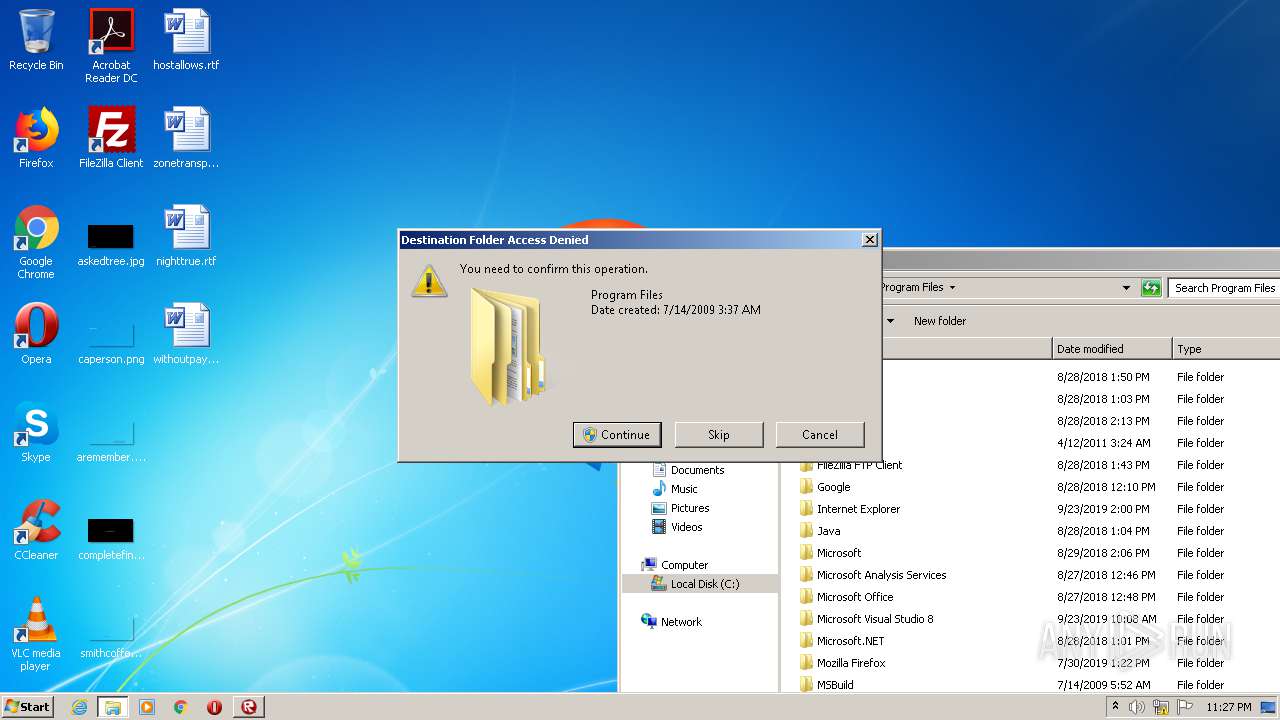
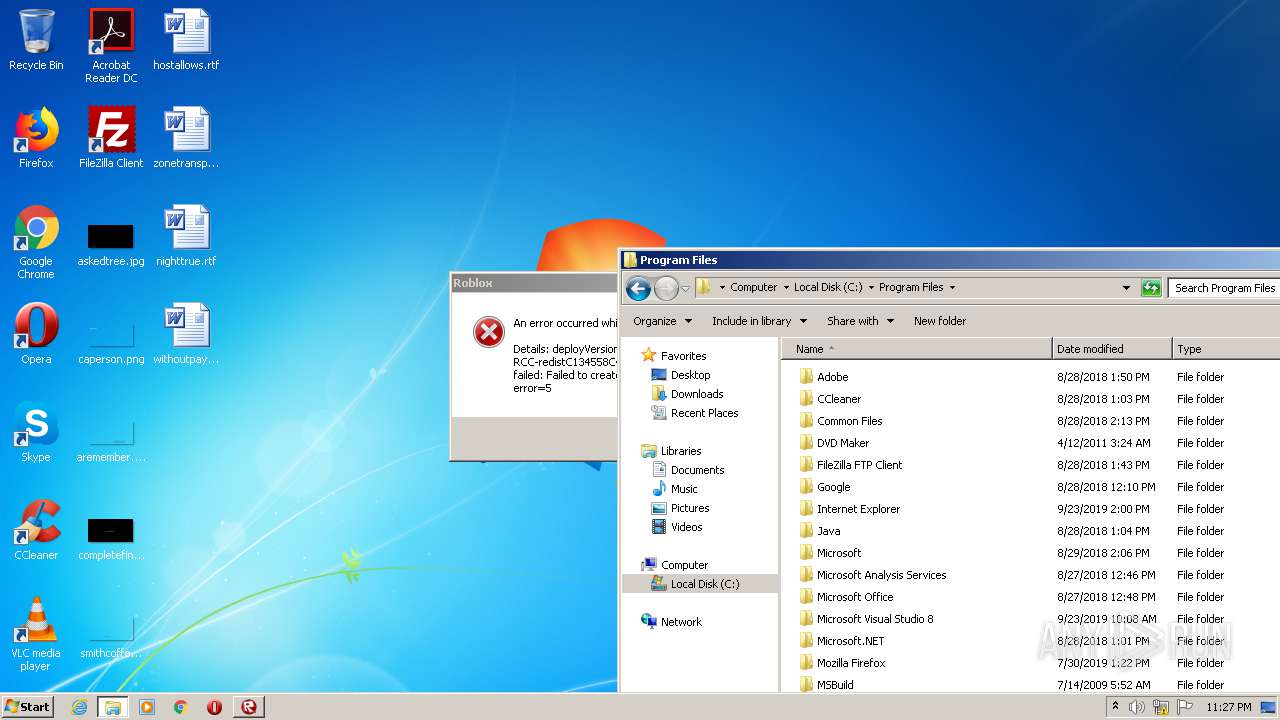
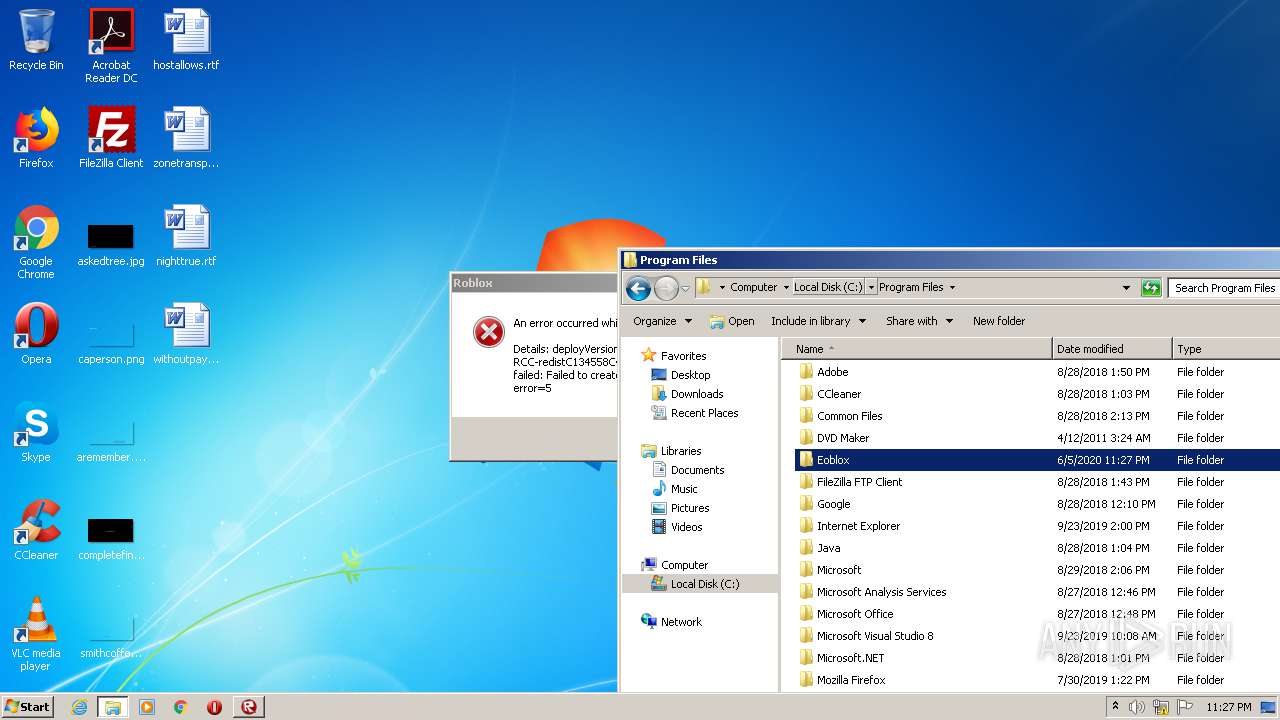
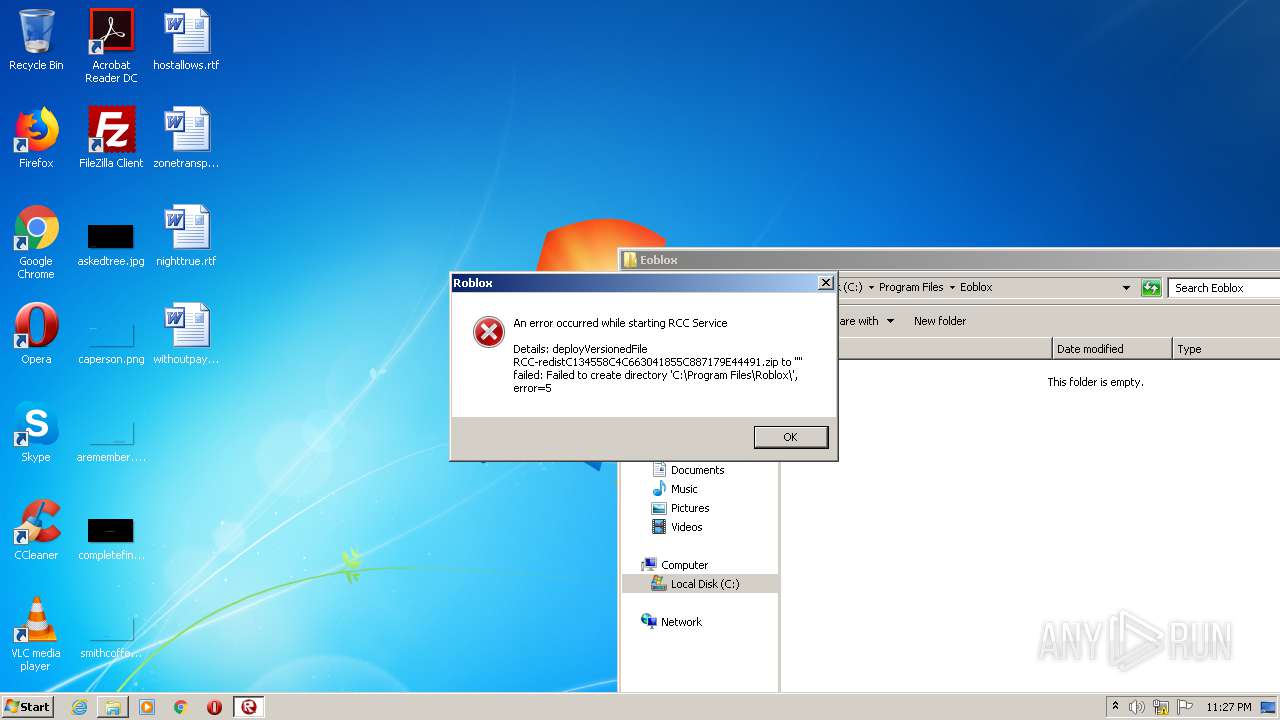
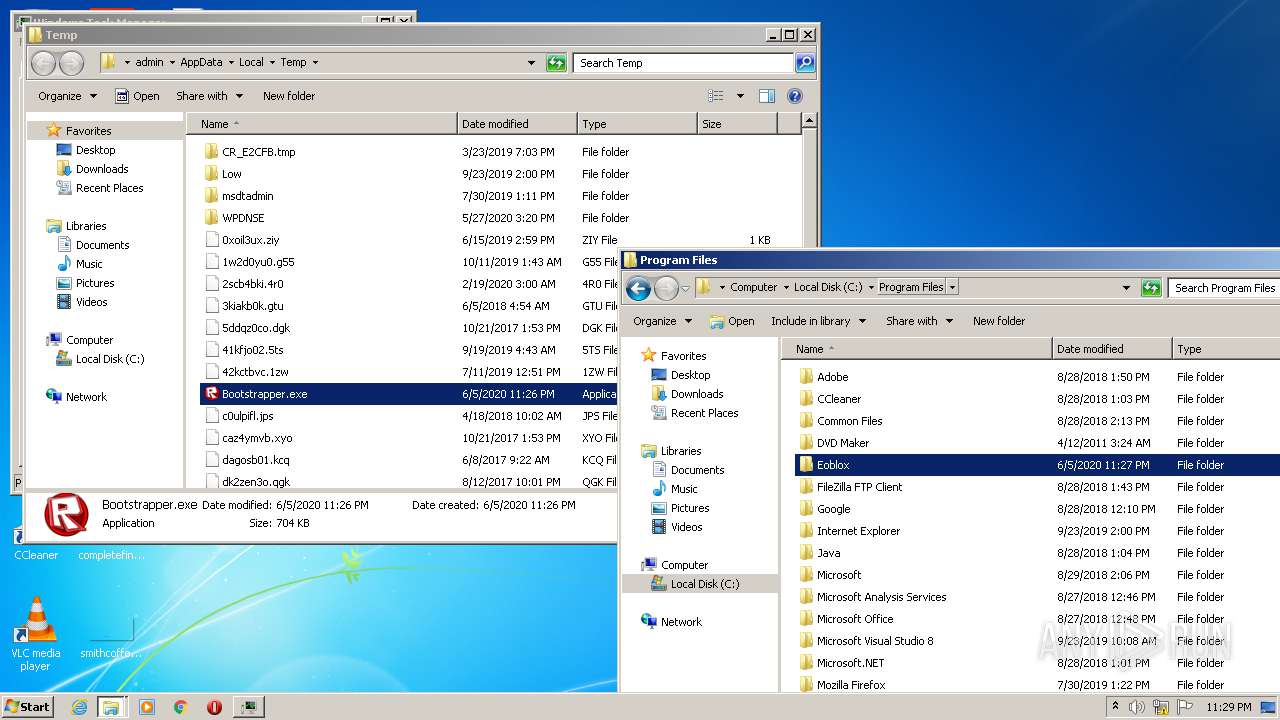
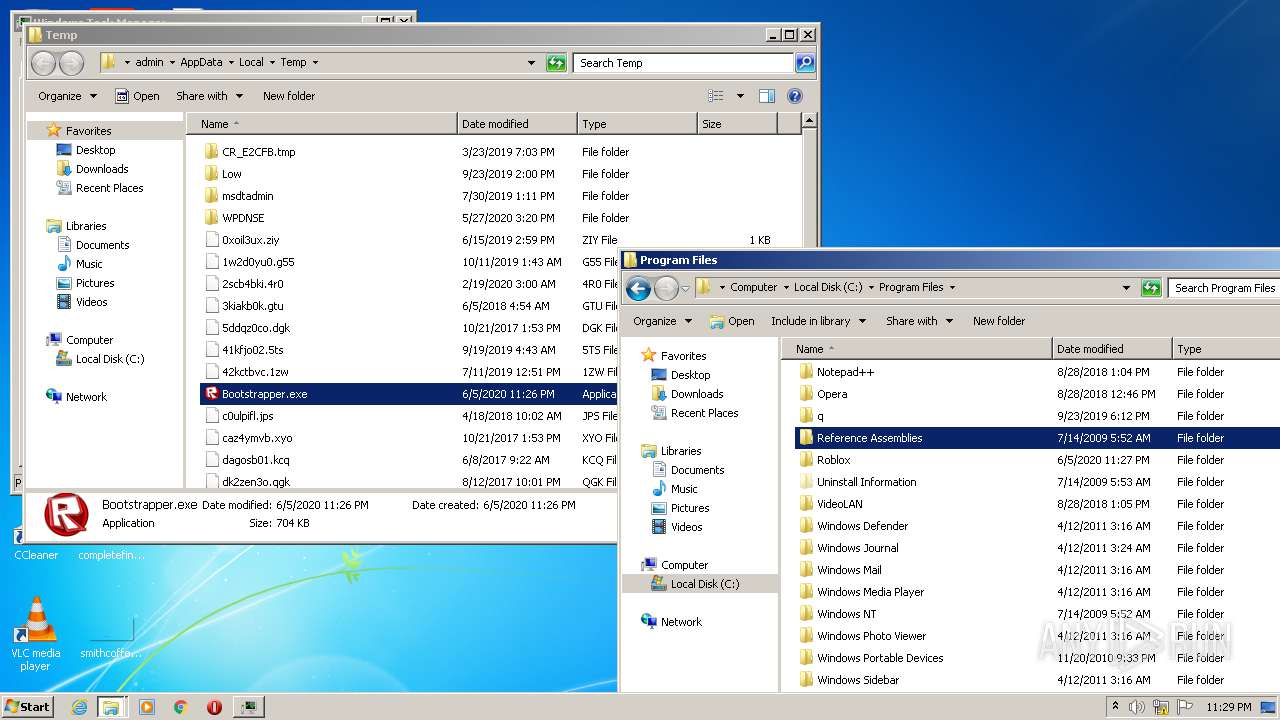
Creates files in the program directory
- Bootstrapper.exe (PID: 2240)
INFO
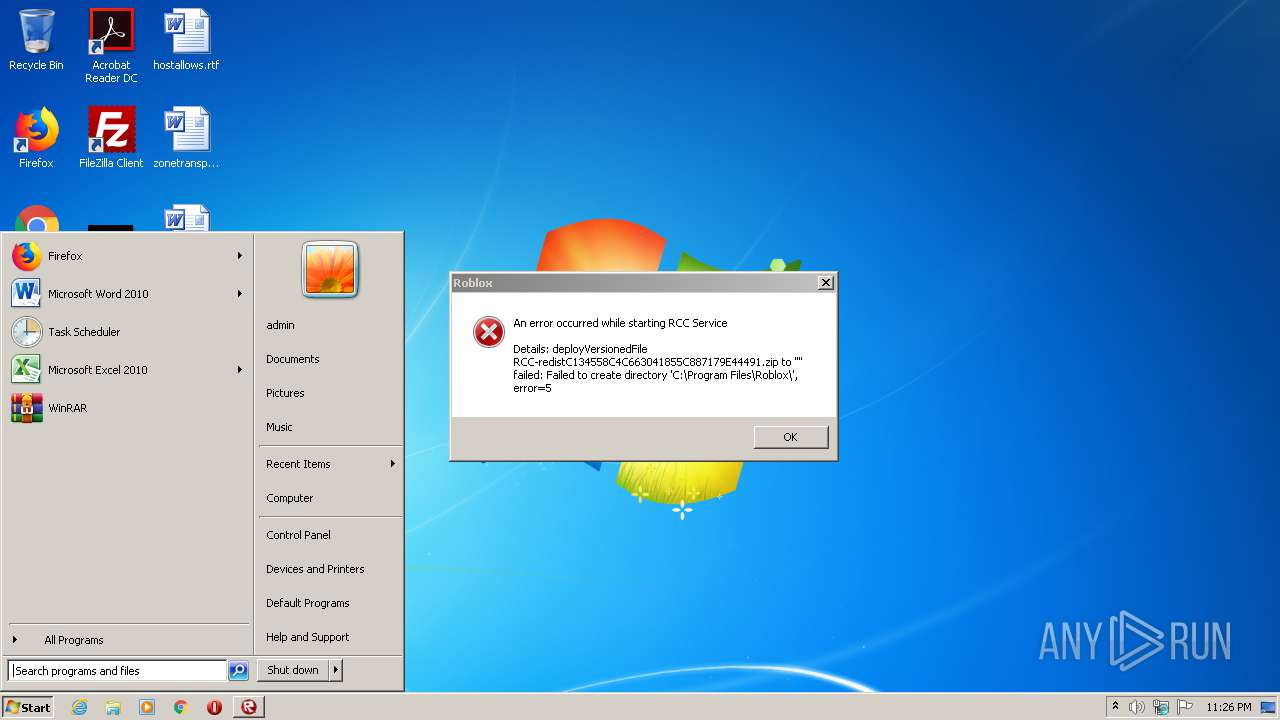
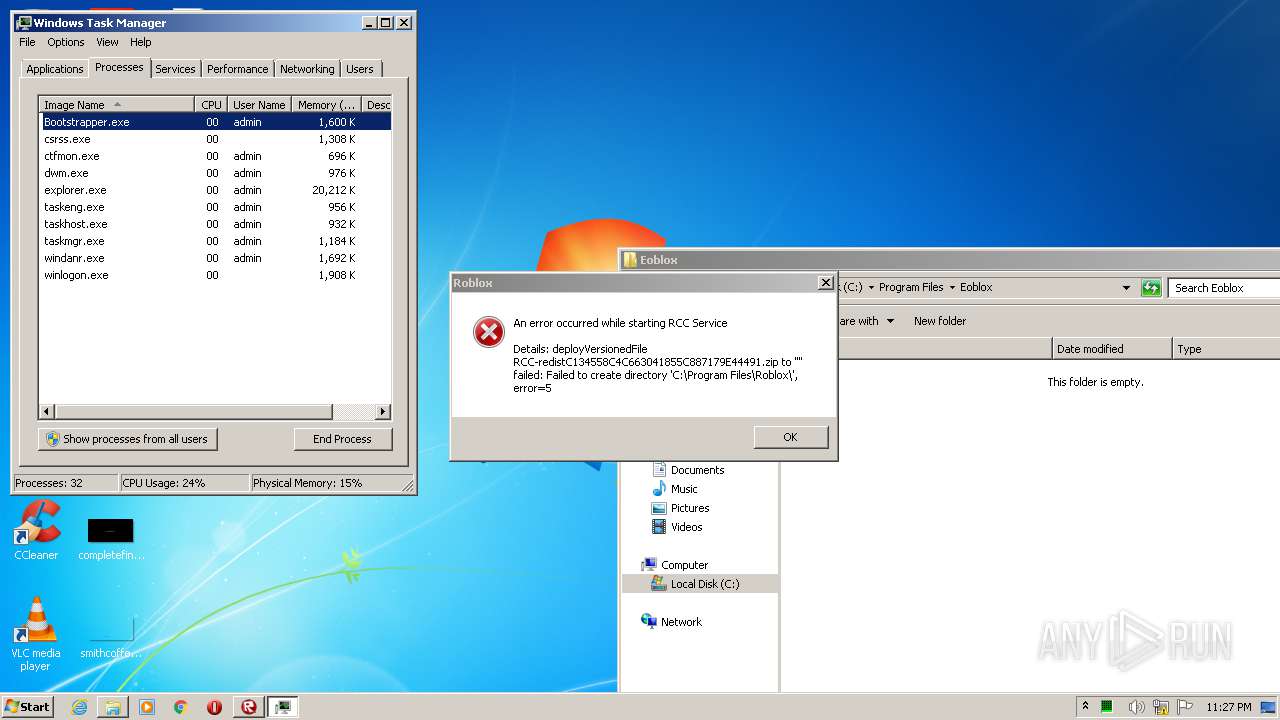
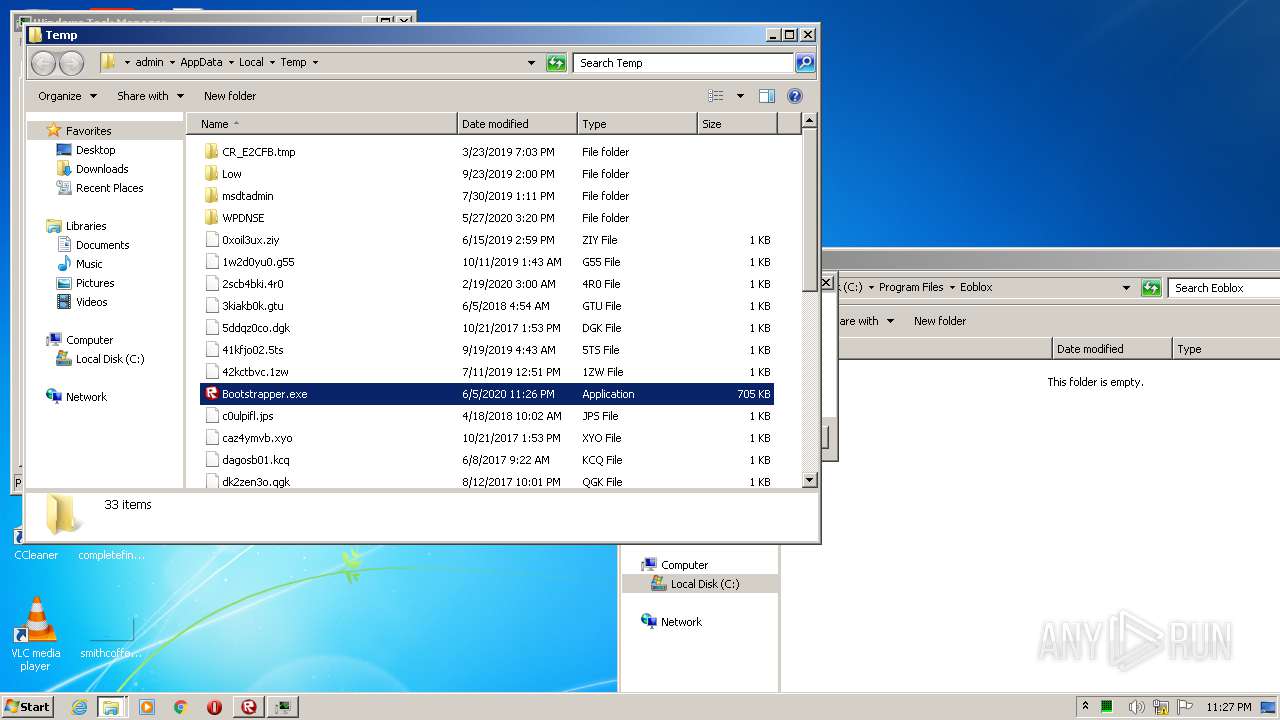
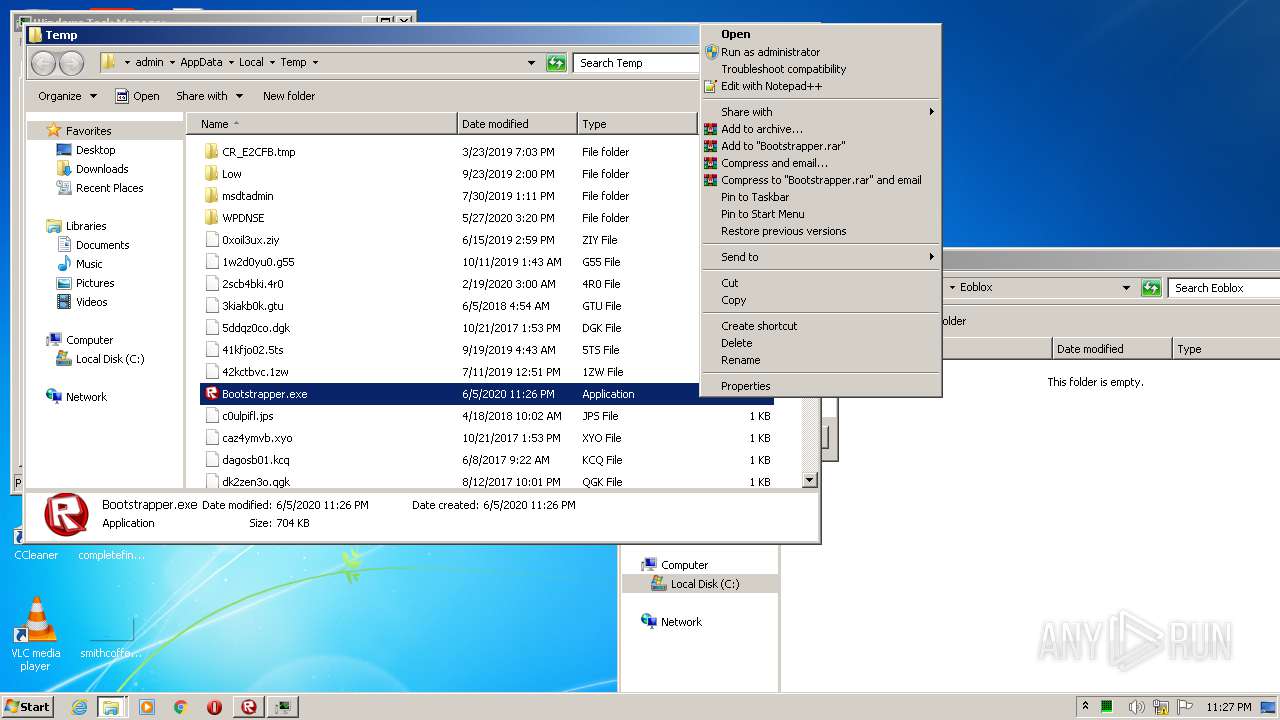
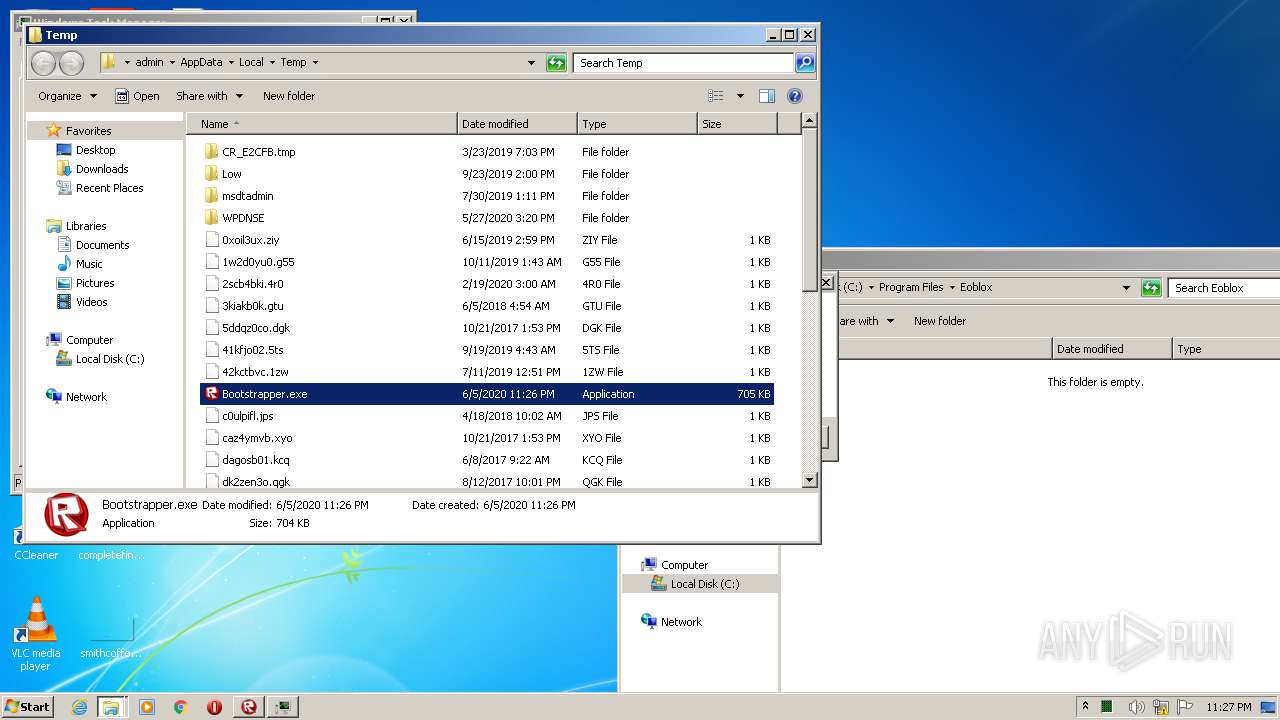
Manual execution by user
- Bootstrapper.exe (PID: 2240)
- taskmgr.exe (PID: 2912)
Dropped object may contain Bitcoin addresses
- Bootstrapper.exe (PID: 2240)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:04:06 21:17:38+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 414208 |
| InitializedDataSize: | 637952 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x44916 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.6.3.49012 |
| ProductVersionNumber: | 1.6.3.0 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
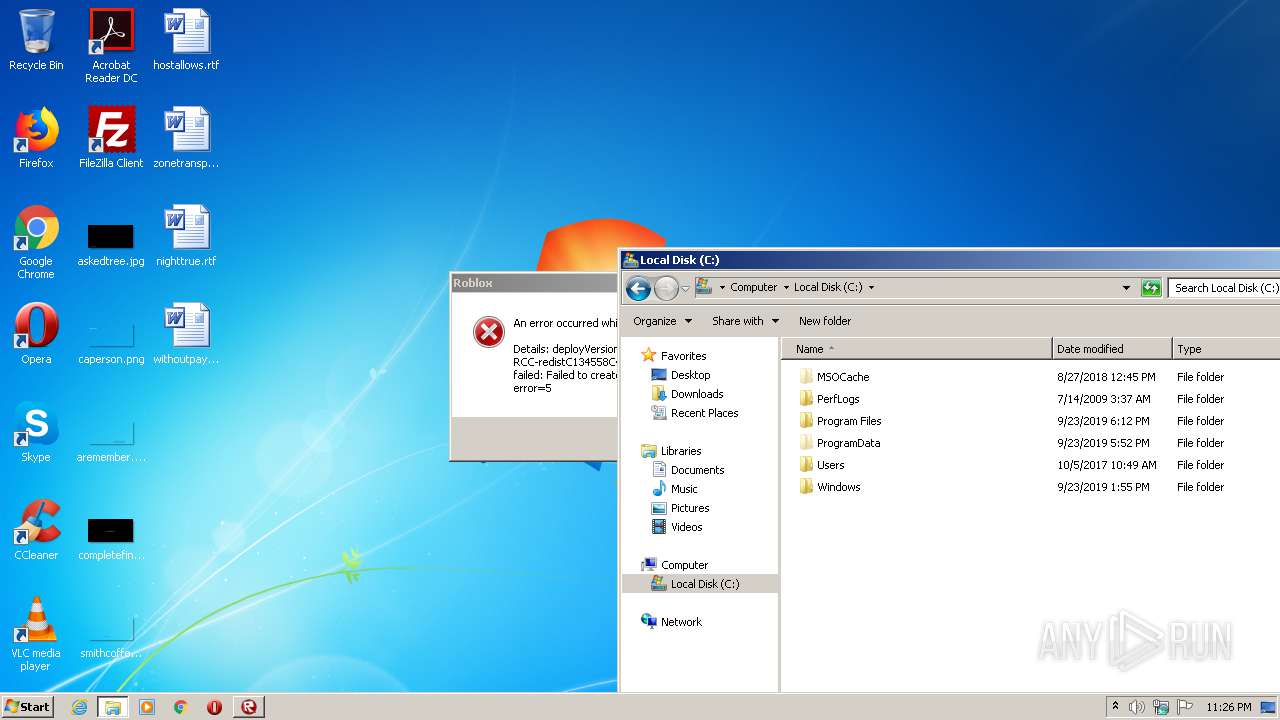
| CompanyName: | ROBLOX Corporation |
| FileDescription: | Roblox |
| FileVersion: | 1, 6, 3, 114548 |
| LegalCopyright: | (C) 2012 ROBLOX Corporation. All rights reserved. |
| OriginalFileName: | Roblox.exe |
| ProductName: | Roblox Bootstrapper |
| ProductVersion: | 1, 6, 3, 0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Apr-2017 19:17:38 |
| Detected languages: |
|
| TLS Callbacks: | 1 callback(s) detected. |
| Debug artifacts: |
|
| CompanyName: | ROBLOX Corporation |
| FileDescription: | Roblox |
| FileVersion: | 1, 6, 3, 114548 |
| LegalCopyright: | (C) 2012 ROBLOX Corporation. All rights reserved. |
| OriginalFilename: | Roblox.exe |
| ProductName: | Roblox Bootstrapper |
| ProductVersion: | 1, 6, 3, 0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 06-Apr-2017 19:17:38 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0006505B | 0x00065200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.66579 |
.rdata | 0x00067000 | 0x0002157A | 0x00021600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.28284 |
.data | 0x00089000 | 0x0005C664 | 0x0000A000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.85461 |
.tls | 0x000E6000 | 0x00000002 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x000E7000 | 0x00013738 | 0x00013800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.15907 |
.reloc | 0x000FB000 | 0x0000A2EA | 0x0000A400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.99655 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.07176 | 640 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.74545 | 76 | UNKNOWN | English - United States | RT_GROUP_ICON |
3 | 3.83833 | 5160 | UNKNOWN | English - United States | RT_ICON |
4 | 3.51468 | 11560 | UNKNOWN | English - United States | RT_ICON |
5 | 3.28699 | 20520 | UNKNOWN | English - United States | RT_ICON |
7 | 3.44591 | 446 | UNKNOWN | English - United States | RT_STRING |
130 | 3.12907 | 254 | UNKNOWN | English - United States | RT_DIALOG |
131 | 2 | 8 | UNKNOWN | English - United States | RT_ACCELERATOR |
157 | 7.30906 | 665 | UNKNOWN | English - United States | PNG |
158 | 7.56743 | 818 | UNKNOWN | English - United States | PNG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
SHLWAPI.dll |
SensApi.dll |
Total processes
58
Monitored processes
9
Malicious processes
3
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 468 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
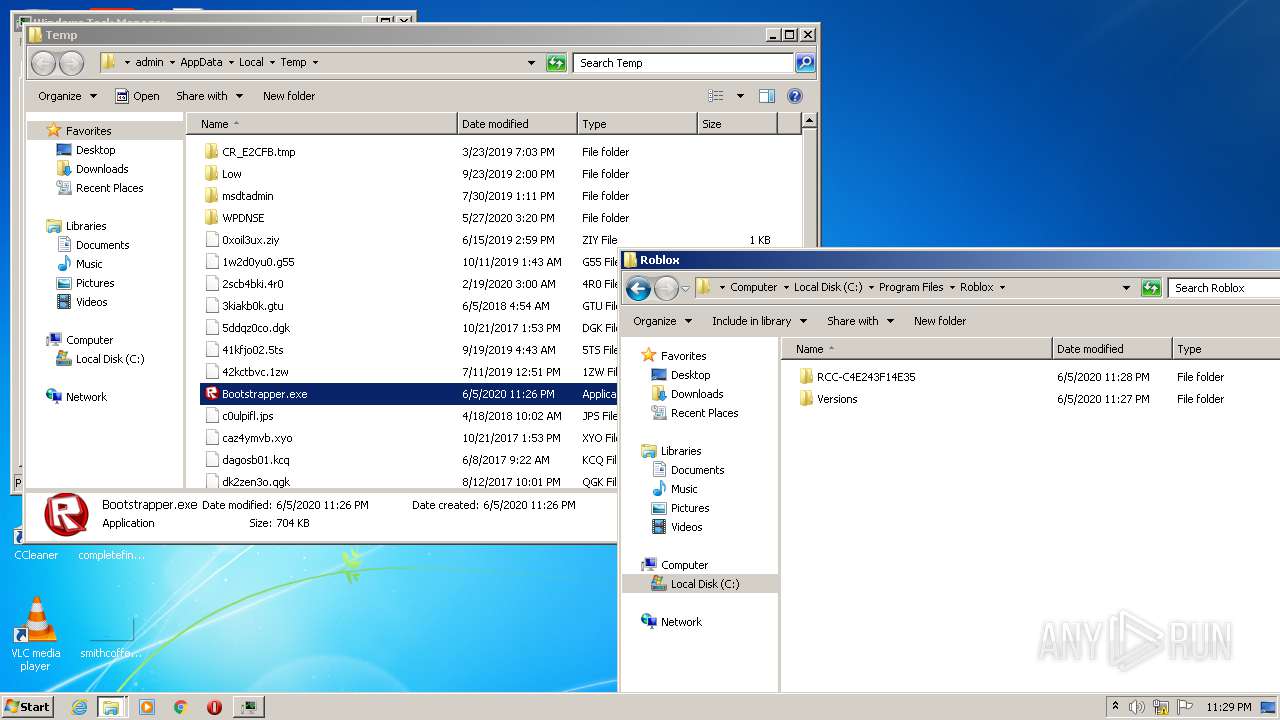
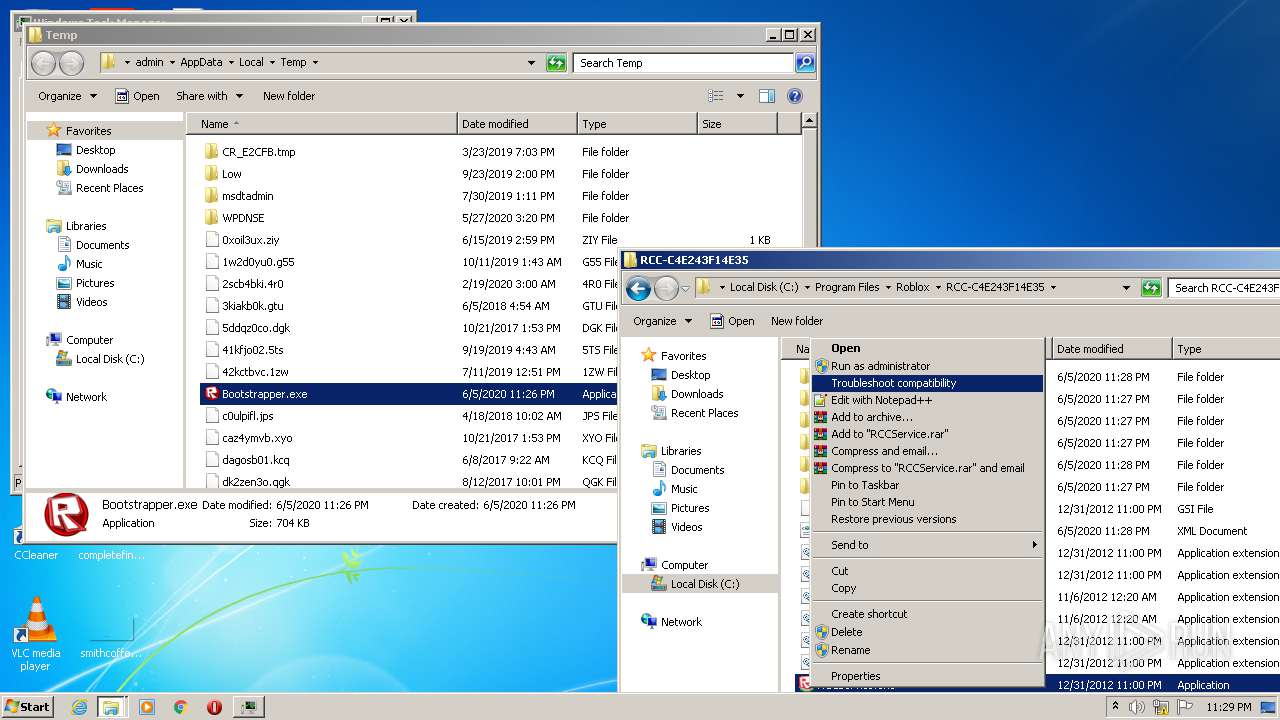
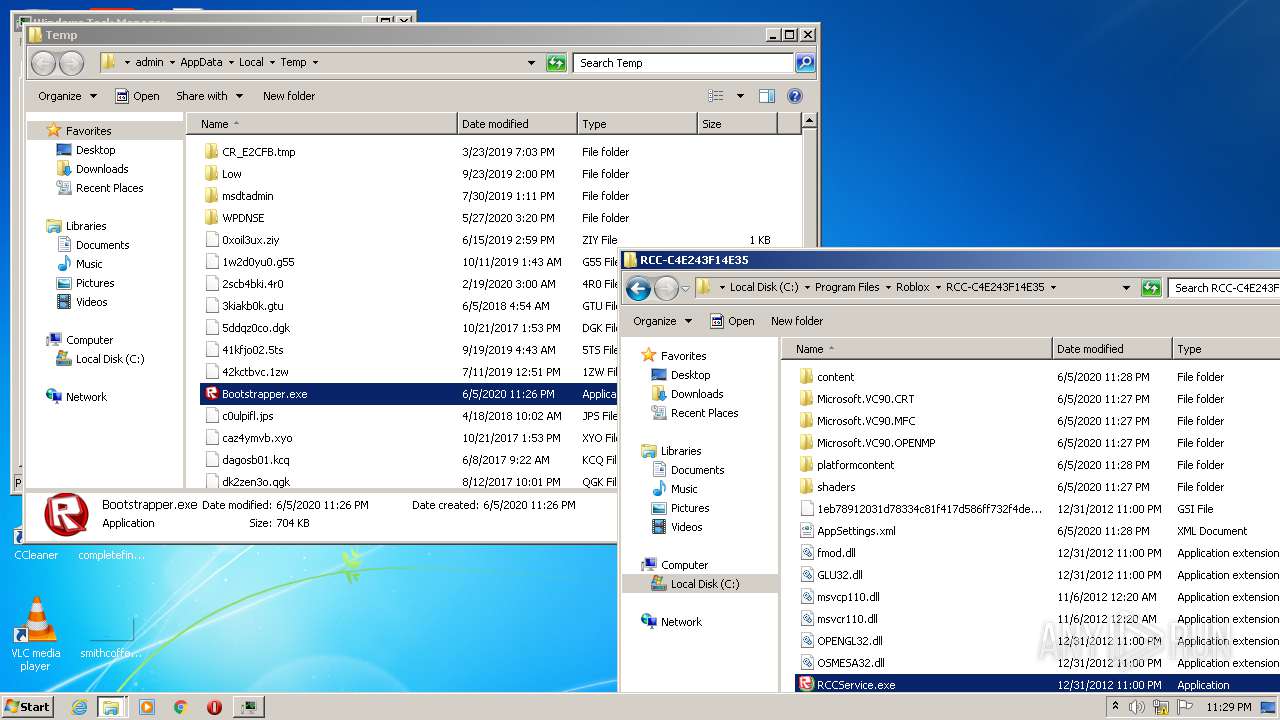
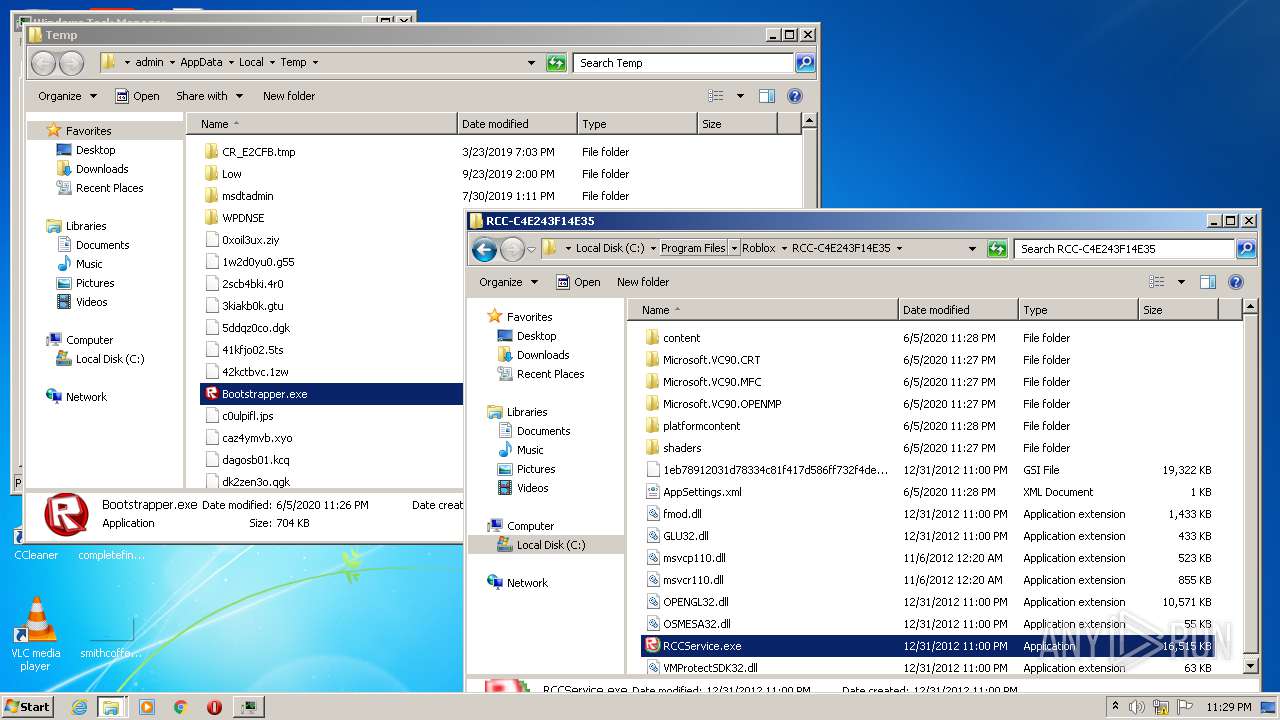
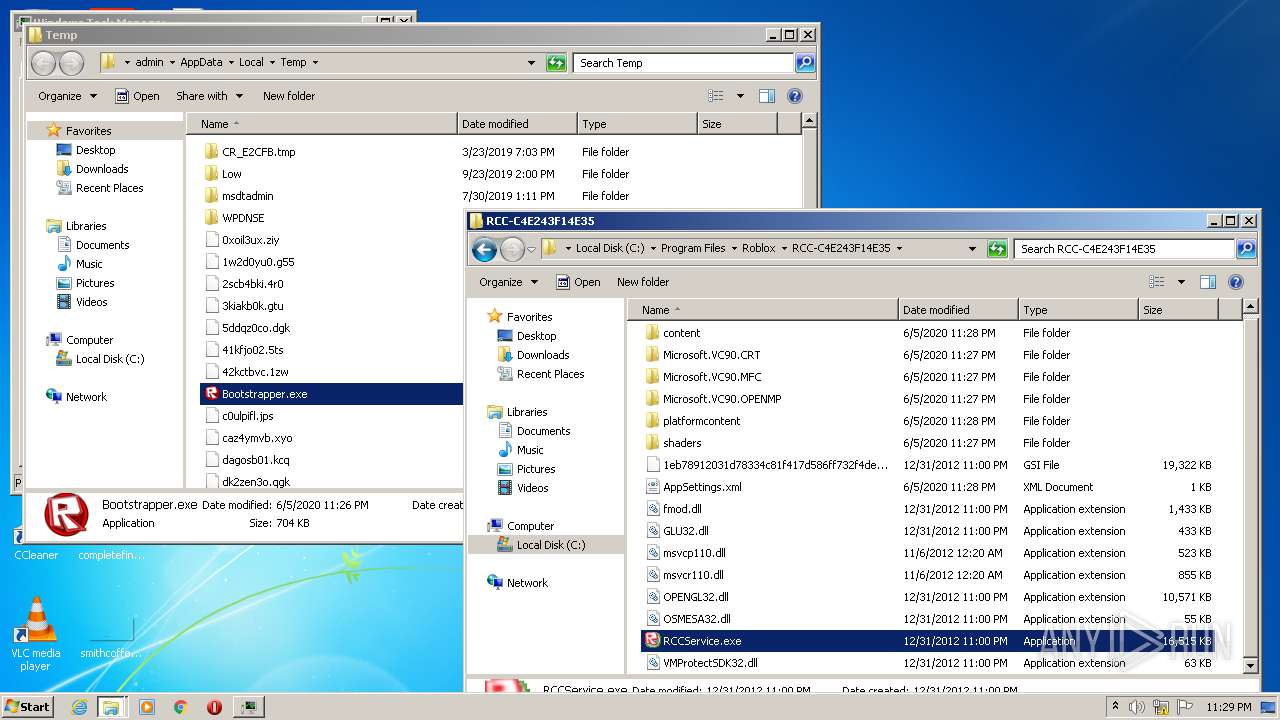
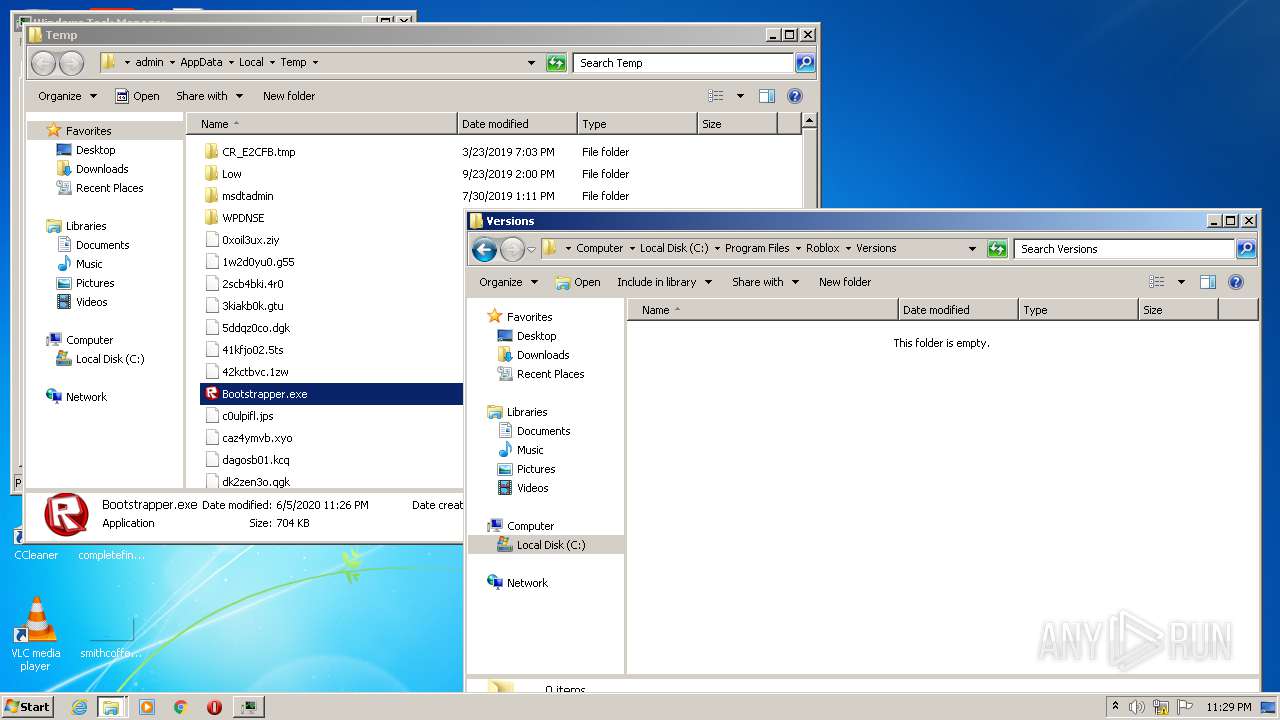
| 756 | "C:\Program Files\Roblox\RCC-C4E243F14E35\RCCService.exe" | C:\Program Files\Roblox\RCC-C4E243F14E35\RCCService.exe | — | explorer.exe | |||||||||||
User: admin Company: ROBLOX Corporation Integrity Level: MEDIUM Description: ROBLOX Compute Cloud Service Exit code: 0 Version: 0, 285, 0, 114548 Modules
| |||||||||||||||
| 2240 | "C:\Users\admin\AppData\Local\Temp\Bootstrapper.exe" | C:\Users\admin\AppData\Local\Temp\Bootstrapper.exe | explorer.exe | ||||||||||||
User: admin Company: ROBLOX Corporation Integrity Level: HIGH Description: Roblox Exit code: 0 Version: 1, 6, 3, 114548 Modules
| |||||||||||||||
| 2912 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2964 | "C:\Program Files\Roblox\RCC-C4E243F14E35\RCCService.exe" | C:\Program Files\Roblox\RCC-C4E243F14E35\RCCService.exe | explorer.exe | ||||||||||||
User: admin Company: ROBLOX Corporation Integrity Level: HIGH Description: ROBLOX Compute Cloud Service Exit code: 0 Version: 0, 285, 0, 114548 Modules
| |||||||||||||||
| 2968 | "C:\Users\admin\AppData\Local\Temp\Bootstrapper.exe" | C:\Users\admin\AppData\Local\Temp\Bootstrapper.exe | explorer.exe | ||||||||||||
User: admin Company: ROBLOX Corporation Integrity Level: MEDIUM Description: Roblox Exit code: 4294967295 Version: 1, 6, 3, 114548 Modules
| |||||||||||||||
| 2976 | "C:\Program Files\Roblox\RCC-C4E243F14E35\RCCService.exe" -stop -uninstall | C:\Program Files\Roblox\RCC-C4E243F14E35\RCCService.exe | — | Bootstrapper.exe | |||||||||||
User: admin Company: ROBLOX Corporation Integrity Level: HIGH Description: ROBLOX Compute Cloud Service Exit code: 0 Version: 0, 285, 0, 114548 Modules
| |||||||||||||||
| 3388 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3456 | "C:\Program Files\Roblox\RCC-C4E243F14E35\RCCService.exe" | C:\Program Files\Roblox\RCC-C4E243F14E35\RCCService.exe | — | explorer.exe | |||||||||||
User: admin Company: ROBLOX Corporation Integrity Level: MEDIUM Description: ROBLOX Compute Cloud Service Exit code: 0 Version: 0, 285, 0, 114548 Modules
| |||||||||||||||
Total events
3 596
Read events
2 879
Write events
717
Delete events
0
Modification events
| (PID) Process: | (2968) Bootstrapper.exe | Key: | HKEY_CURRENT_USER\Software\ROBLOX Corporation\Roblox |
| Operation: | write | Name: | CPath |
Value: C:\Users\admin\AppData\LocalLow\rbxcsettings.rbx | |||
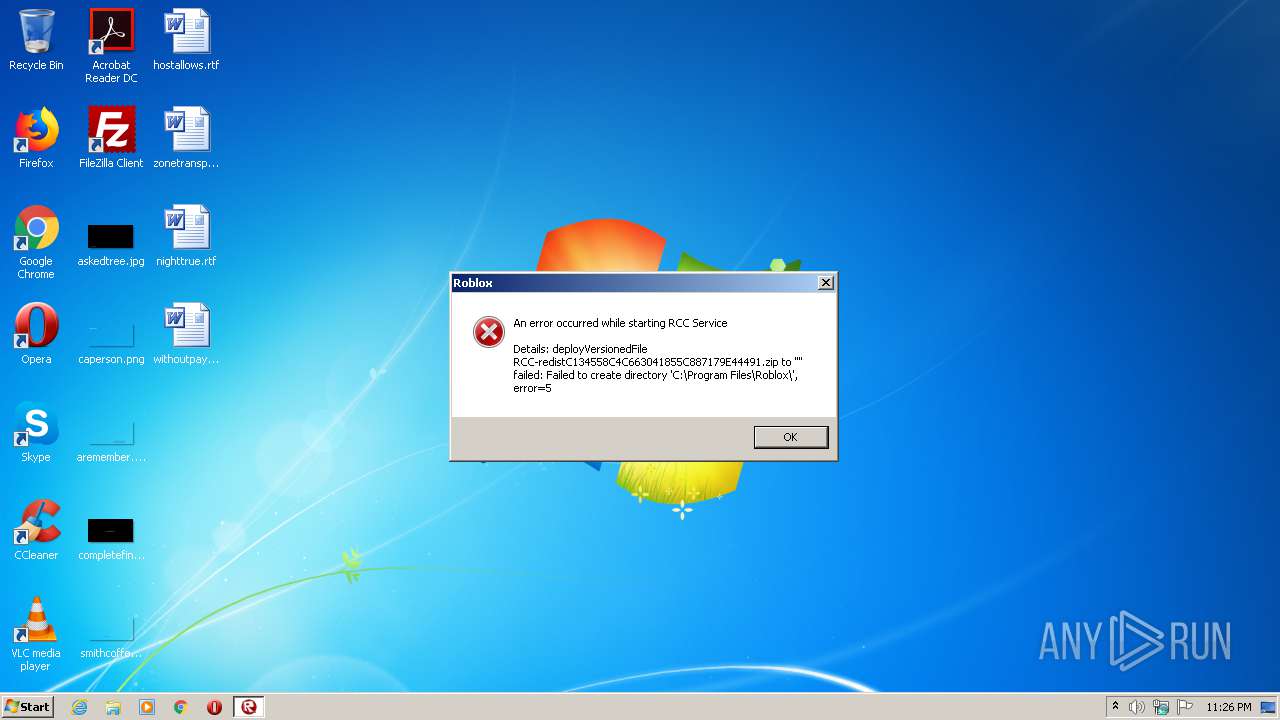
| (PID) Process: | (2968) Bootstrapper.exe | Key: | HKEY_CURRENT_USER\Software\RobloxReg\ETags |
| Operation: | write | Name: | RCC-redistC134558C4C663041855C887179E44491.zip |
Value: | |||
| (PID) Process: | (468) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\NccQngn\Ybpny\Grzc\Obbgfgenccre.rkr |
Value: 00000000000000000000000000000000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (468) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000004200000053000000C8ED25000B0000001A00000057BE0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000010000024E9ED017990C577B8006900000069000010000050E9ED01C4F6C4770000690000000000580269000002690064E9ED016C19C5770D00000000026900580269002CEBED0128EBED01000008009786217614E8ED0114EAED01D8E9ED0115E1C077C7670800FEFFFFFF8B8DC477108BC47701000000010000000000000004EAED01CCE9ED01E8E9ED012C8AC375010000000000000004EAED013F8AC375ED1805AB000000006CEFED0102000000FFFFFFFF0000000000000000000000000000E96FACE9ED01485F9B0050EEED01B514C5754D7B2BDFFEFFFFFF3F8AC375A36CC375A589C375651F05AB6CEFED0111000000483D3200403D32006CEFED017CEA0000C05704AB2CEAED018291D2767CEAED01EC430000FC5704AB40EAED01B69CD276F04311024C06000058EAED01603F110264EAED01789CD2763691D27611000000483D3200403D320000EBED01803F1102D0EA0000BC5704AB80EAED018291D276D0EAED0184EAED012795D27600000000EC431102ACEAED01CD94D276EC43110258EBED01603F1102E194D27600000000603F110258EBED01B4EAED010B0000001A00000057BE0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000010000024E9ED017990C577B8006900000069000010000050E9ED01C4F6C4770000690000000000580269000002690064E9ED016C19C5770D00000000026900580269002CEBED0128EBED01000008009786217614E8ED0114EAED01D8E9ED0115E1C077C7670800FEFFFFFF8B8DC477108BC47701000000010000000000000004EAED01CCE9ED01E8E9ED012C8AC375010000000000000004EAED013F8AC375ED1805AB000000006CEFED0102000000FFFFFFFF0000000000000000000000000000E96FACE9ED01485F9B0050EEED01B514C5754D7B2BDFFEFFFFFF3F8AC375A36CC375A589C375651F05AB6CEFED0111000000483D3200403D32006CEFED017CEA0000C05704AB2CEAED018291D2767CEAED01EC430000FC5704AB40EAED01B69CD276F04311024C06000058EAED01603F110264EAED01789CD2763691D27611000000483D3200403D320000EBED01803F1102D0EA0000BC5704AB80EAED018291D276D0EAED0184EAED012795D27600000000EC431102ACEAED01CD94D276EC43110258EBED01603F1102E194D27600000000603F110258EBED01B4EAED010B0000001A00000057BE0F007B00460033003800420046003400300034002D0031004400340033002D0034003200460032002D0039003300300035002D003600370044004500300042003200380046004300320033007D005C006500780070006C006F007200650072002E0065007800650000000010000024E9ED017990C577B8006900000069000010000050E9ED01C4F6C4770000690000000000580269000002690064E9ED016C19C5770D00000000026900580269002CEBED0128EBED01000008009786217614E8ED0114EAED01D8E9ED0115E1C077C7670800FEFFFFFF8B8DC477108BC47701000000010000000000000004EAED01CCE9ED01E8E9ED012C8AC375010000000000000004EAED013F8AC375ED1805AB000000006CEFED0102000000FFFFFFFF0000000000000000000000000000E96FACE9ED01485F9B0050EEED01B514C5754D7B2BDFFEFFFFFF3F8AC375A36CC375A589C375651F05AB6CEFED0111000000483D3200403D32006CEFED017CEA0000C05704AB2CEAED018291D2767CEAED01EC430000FC5704AB40EAED01B69CD276F04311024C06000058EAED01603F110264EAED01789CD2763691D27611000000483D3200403D320000EBED01803F1102D0EA0000BC5704AB80EAED018291D276D0EAED0184EAED012795D27600000000EC431102ACEAED01CD94D276EC43110258EBED01603F1102E194D27600000000603F110258EBED01B4EAED01 | |||
| (PID) Process: | (468) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (468) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ApplicationDestinations |
| Operation: | write | Name: | MaxEntries |
Value: 15 | |||
| (PID) Process: | (468) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\mycomput.dll,-400 |
Value: Mana&ge | |||
| (PID) Process: | (468) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (468) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0100000002000000000000000A00000007000000090000000800000006000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (468) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Toolbar |
| Operation: | write | Name: | Locked |
Value: 1 | |||
Executable files
14
Suspicious files
57
Text files
1 055
Unknown types
249
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3388 | DllHost.exe | C:\Program Files\Eoblox | — | |
MD5:— | SHA256:— | |||
| 2240 | Bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\RBX-3274BCBD.tmp | — | |
MD5:— | SHA256:— | |||
| 2240 | Bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\RBX-F948E47F.tmp | — | |
MD5:— | SHA256:— | |||
| 2240 | Bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\RBX-15828362.tmp | — | |
MD5:— | SHA256:— | |||
| 2968 | Bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\RBX-9A79FD89.log | text | |
MD5:5C1103ED5FE29C31998B90BC5067B86F | SHA256:6E44793E43982AAF8F789E5C5F412CD3458AFB3345DC35F747F726CFD0E4CD78 | |||
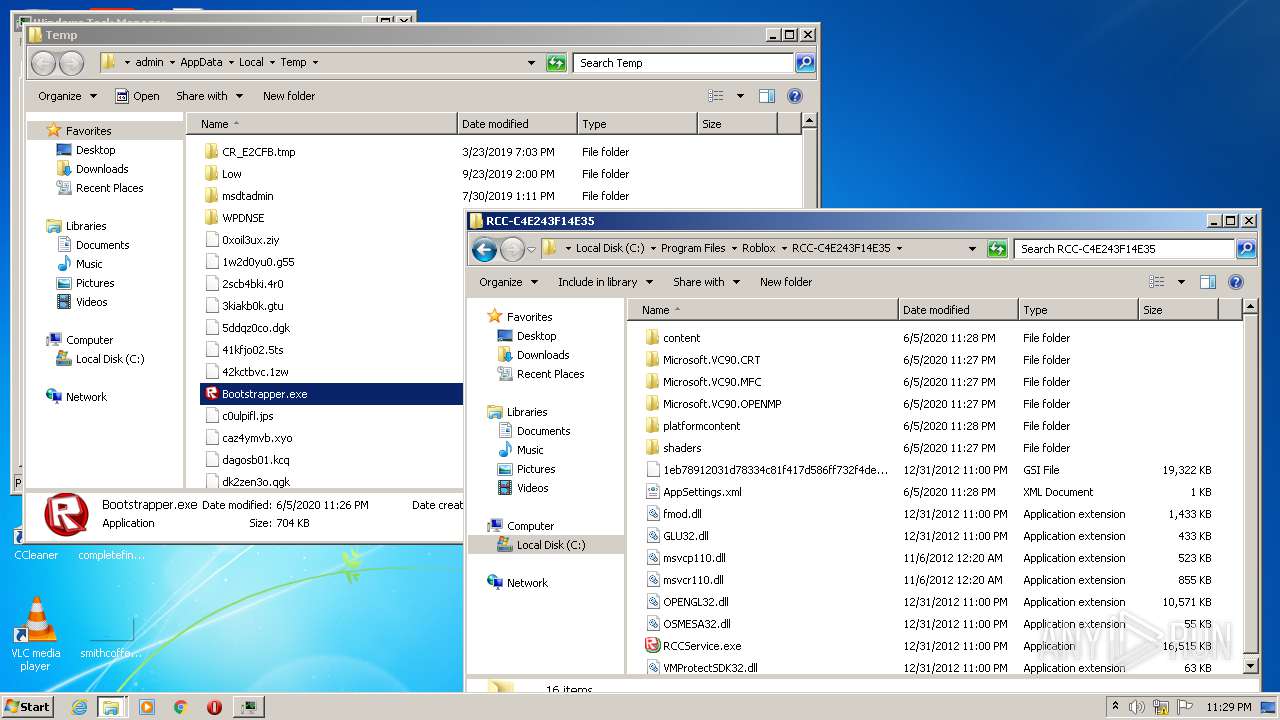
| 2240 | Bootstrapper.exe | C:\Program Files\Roblox\RCC-C4E243F14E35\Microsoft.VC90.CRT\Microsoft.VC90.CRT.manifest | xml | |
MD5:6BB5D2AAD0AE1B4A82E7DDF7CF58802A | SHA256:9E0220511D4EBDB014CC17ECB8319D57E3B0FEA09681A80D8084AA8647196582 | |||
| 2240 | Bootstrapper.exe | C:\Program Files\Roblox\RCC-C4E243F14E35\VMProtectSDK32.dll | executable | |
MD5:1E6FDCD6D847BBF9CD3A37BA72CDA3F7 | SHA256:06754CB39C2E814577AC287B7DD0083F59933C867038407CDDFB22EBC6C0F193 | |||
| 2240 | Bootstrapper.exe | C:\Program Files\Roblox\RCC-C4E243F14E35\Microsoft.VC90.MFC\mfcm90.dll | executable | |
MD5:D4E7C1546CF3131B7D84B39F8DA9E321 | SHA256:C4243BA85C2D130B4DEC972CD291916E973D9D60FAC5CEEA63A01837ECC481C2 | |||
| 2240 | Bootstrapper.exe | C:\Program Files\Roblox\RCC-C4E243F14E35\shaders\shaders_d3d10_1.pack | binary | |
MD5:A172FD0A9156D3982010AAEEDF37AC6F | SHA256:AA57B930E6CD6AFAA3B75D30F3A055B37B6B1ADE8CE7D1EAD5968420608457D2 | |||
| 2240 | Bootstrapper.exe | C:\Users\admin\AppData\Local\Temp\RBX-14FBC891.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
8
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2240 | Bootstrapper.exe | GET | 200 | 2.16.186.25:80 | http://setup.rbxcdn.com/RCC-LibrariesC134558C4C663041855C887179E44491.zip | unknown | compressed | 696 Kb | whitelisted |
2240 | Bootstrapper.exe | GET | 200 | 2.16.186.25:80 | http://setup.rbxcdn.com/RCC-redistC134558C4C663041855C887179E44491.zip | unknown | compressed | 1.68 Mb | whitelisted |
2240 | Bootstrapper.exe | GET | 200 | 2.16.186.25:80 | http://setup.rbxcdn.com/RCC-contentC134558C4C663041855C887179E44491.zip | unknown | compressed | 7.61 Mb | whitelisted |
2240 | Bootstrapper.exe | GET | 200 | 2.16.186.25:80 | http://setup.rbxcdn.com/RCC-shadersC134558C4C663041855C887179E44491.zip | unknown | compressed | 432 Kb | whitelisted |
2968 | Bootstrapper.exe | POST | 200 | 128.116.123.3:80 | http://data.roblox.com/Error/InstallLog.ashx?version=1.6.3.114548&stage=00&guid=23208 | US | text | 2 b | malicious |
2240 | Bootstrapper.exe | GET | 200 | 2.16.186.25:80 | http://setup.rbxcdn.com/RCC-platformcontentC134558C4C663041855C887179E44491.zip | unknown | compressed | 48.6 Mb | whitelisted |
2240 | Bootstrapper.exe | GET | 200 | 2.16.186.25:80 | http://setup.rbxcdn.com/RCCService2AFBA34ACD542E96B3890871CBA18F43.zip | unknown | compressed | 18.5 Mb | whitelisted |
2240 | Bootstrapper.exe | GET | 200 | 128.116.123.3:80 | http://www.roblox.com/install/GetInstallerCdns.ashx | US | text | 27 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2240 | Bootstrapper.exe | 2.16.186.25:80 | setup.rbxcdn.com | Akamai International B.V. | — | whitelisted |
2968 | Bootstrapper.exe | 128.116.123.3:80 | www.roblox.com | University Corporation for Atmospheric Research | US | suspicious |
2240 | Bootstrapper.exe | 128.116.123.3:80 | www.roblox.com | University Corporation for Atmospheric Research | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.roblox.com |
| whitelisted |
setup.rbxcdn.com |
| whitelisted |
data.roblox.com |
| malicious |