| File name: | maltest.exe |
| Full analysis: | https://app.any.run/tasks/3c556b6c-93ab-4e0e-a0c7-cbe9c71c20b3 |
| Verdict: | Malicious activity |
| Analysis date: | June 25, 2023, 03:03:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 616EC7023AF17907BBD42570D89A1B36 |
| SHA1: | 69FE1E039109C85649AC5CE73F9D46DDFCAE8358 |
| SHA256: | FA810C22308618A611BBB1A27F485906317342185A2C37F4B211DE9919FB56B3 |
| SSDEEP: | 98304:AOVsKQB4QD9OMP1Hqwe0BaratuccFJOnRvwEggZURieM35M:ZOKQB4QP1E0Ba+tykRwLaQi1pM |
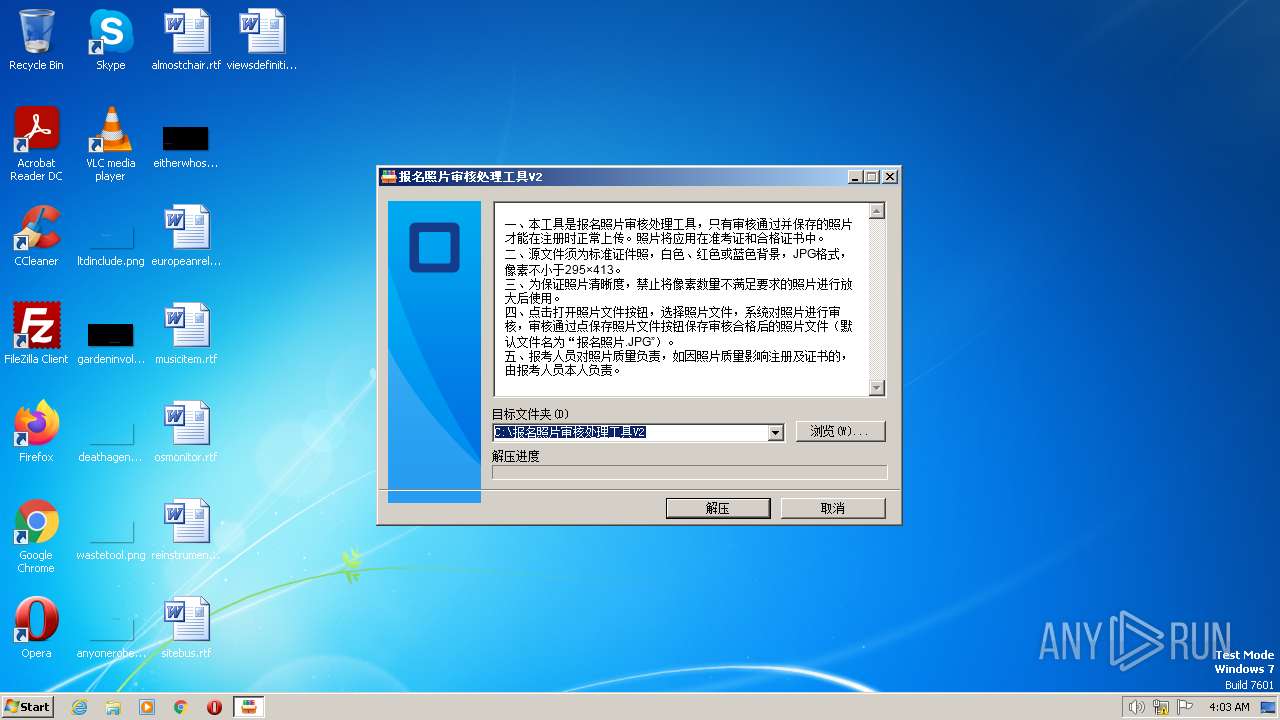
MALICIOUS
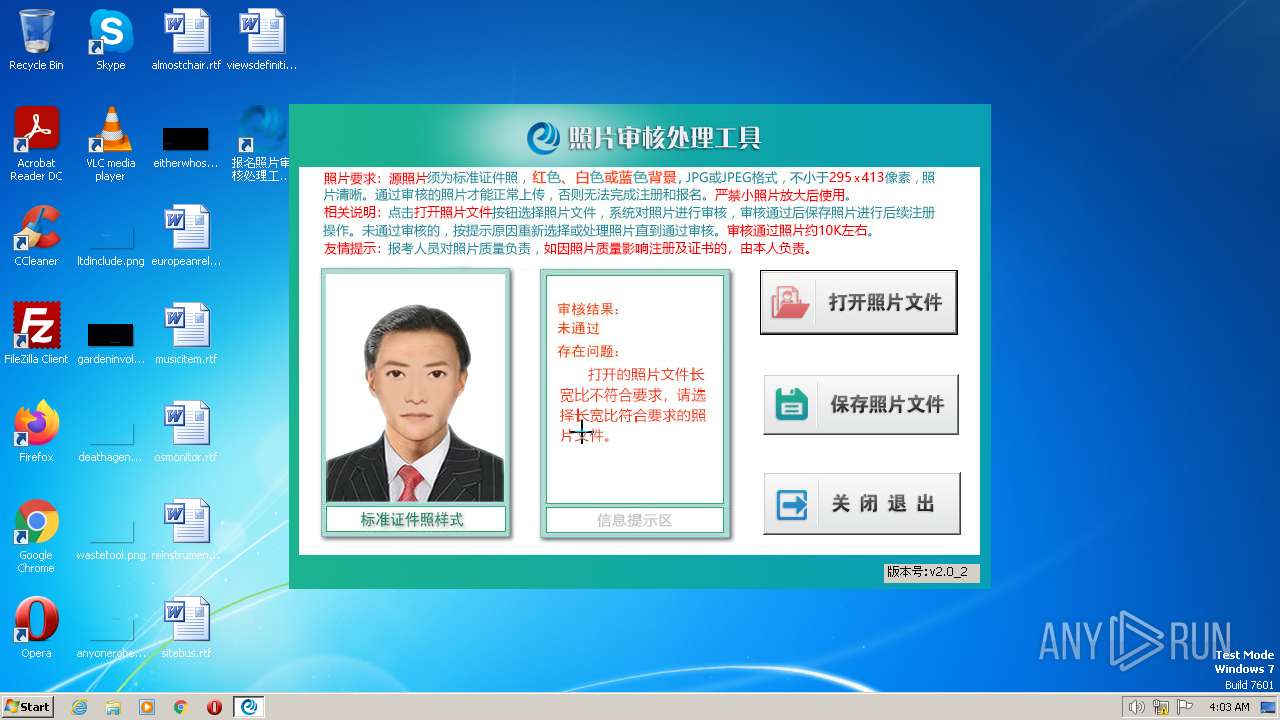
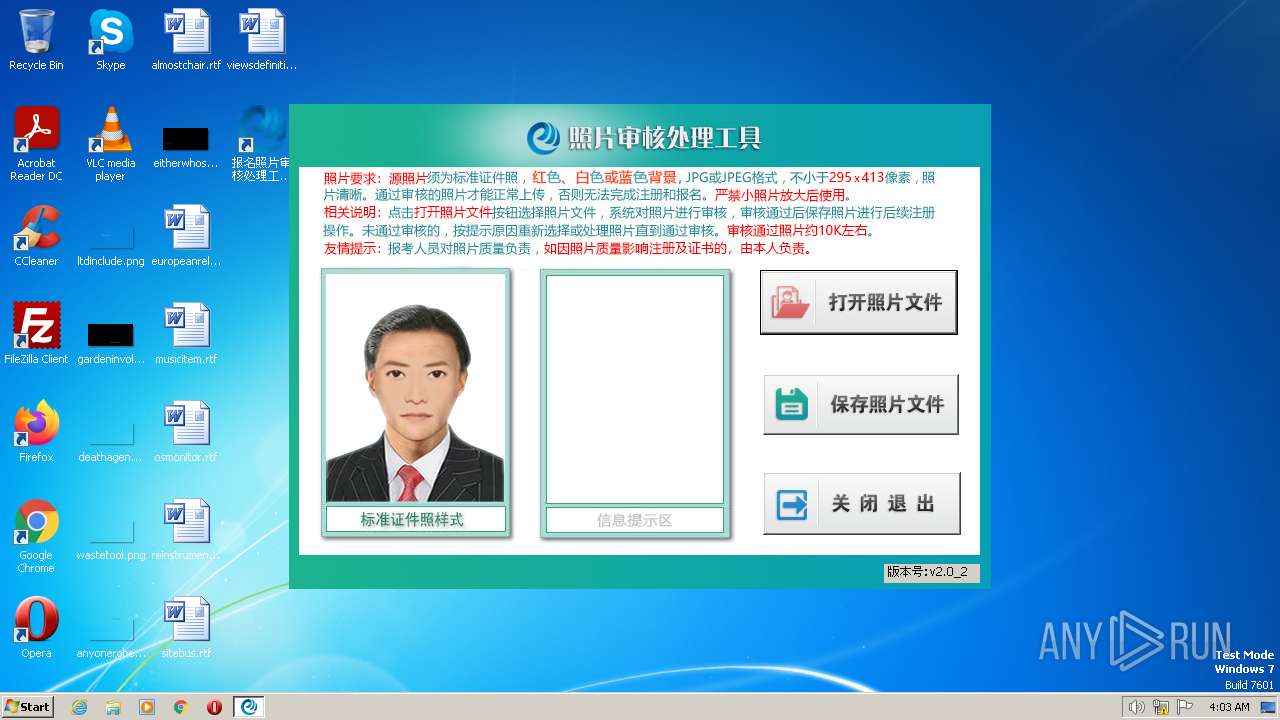
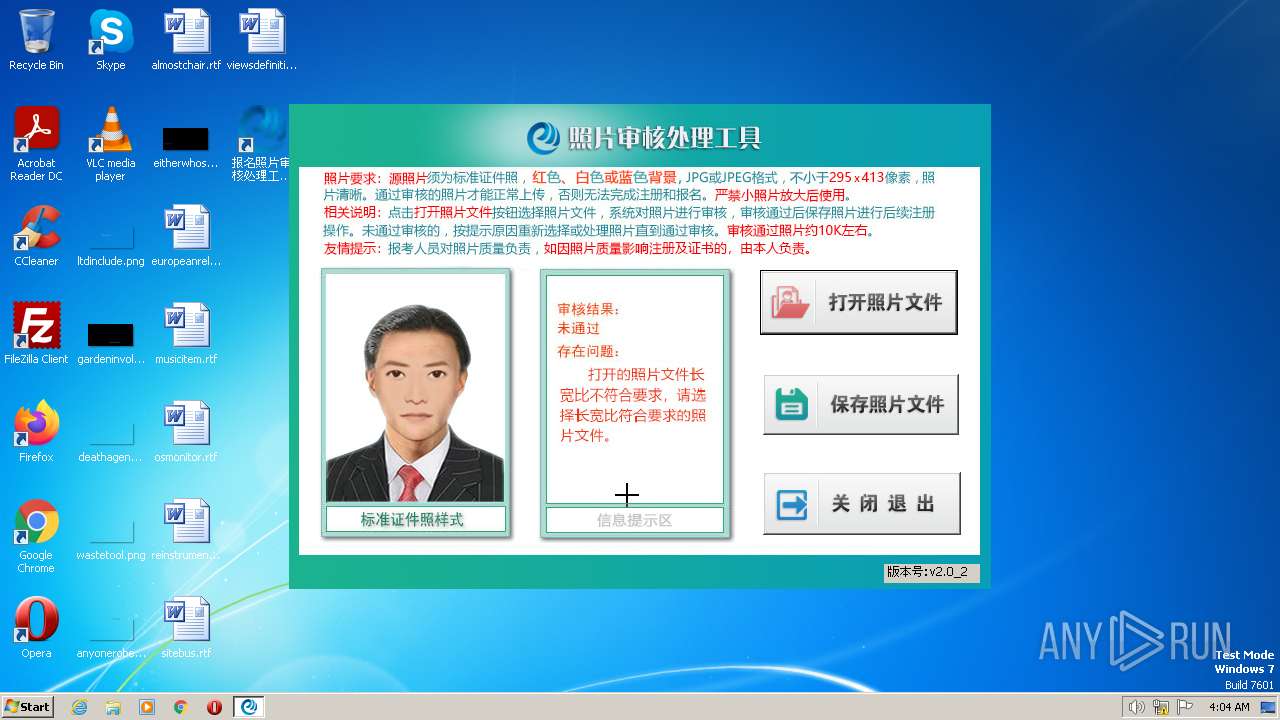
Application was dropped or rewritten from another process
- OumaPictureCheck.exe (PID: 3952)
- OumaPictureCheck.exe (PID: 3056)
Loads dropped or rewritten executable
- OumaPictureCheck.exe (PID: 3952)
- OumaPictureCheck.exe (PID: 3056)
SUSPICIOUS
Reads Microsoft Outlook installation path
- maltest.exe (PID: 3096)
Reads the Internet Settings
- maltest.exe (PID: 3096)
- OumaPictureCheck.exe (PID: 3952)
Reads Internet Explorer settings
- maltest.exe (PID: 3096)
Executable content was dropped or overwritten
- maltest.exe (PID: 3096)
INFO
Reads the computer name
- maltest.exe (PID: 3096)
- OumaPictureCheck.exe (PID: 3952)
- OumaPictureCheck.exe (PID: 3056)
The process checks LSA protection
- maltest.exe (PID: 3096)
- OumaPictureCheck.exe (PID: 3952)
- OumaPictureCheck.exe (PID: 3056)
Checks supported languages
- maltest.exe (PID: 3096)
- OumaPictureCheck.exe (PID: 3952)
- OumaPictureCheck.exe (PID: 3056)
Checks proxy server information
- maltest.exe (PID: 3096)
Reads the machine GUID from the registry
- maltest.exe (PID: 3096)
- OumaPictureCheck.exe (PID: 3952)
- OumaPictureCheck.exe (PID: 3056)
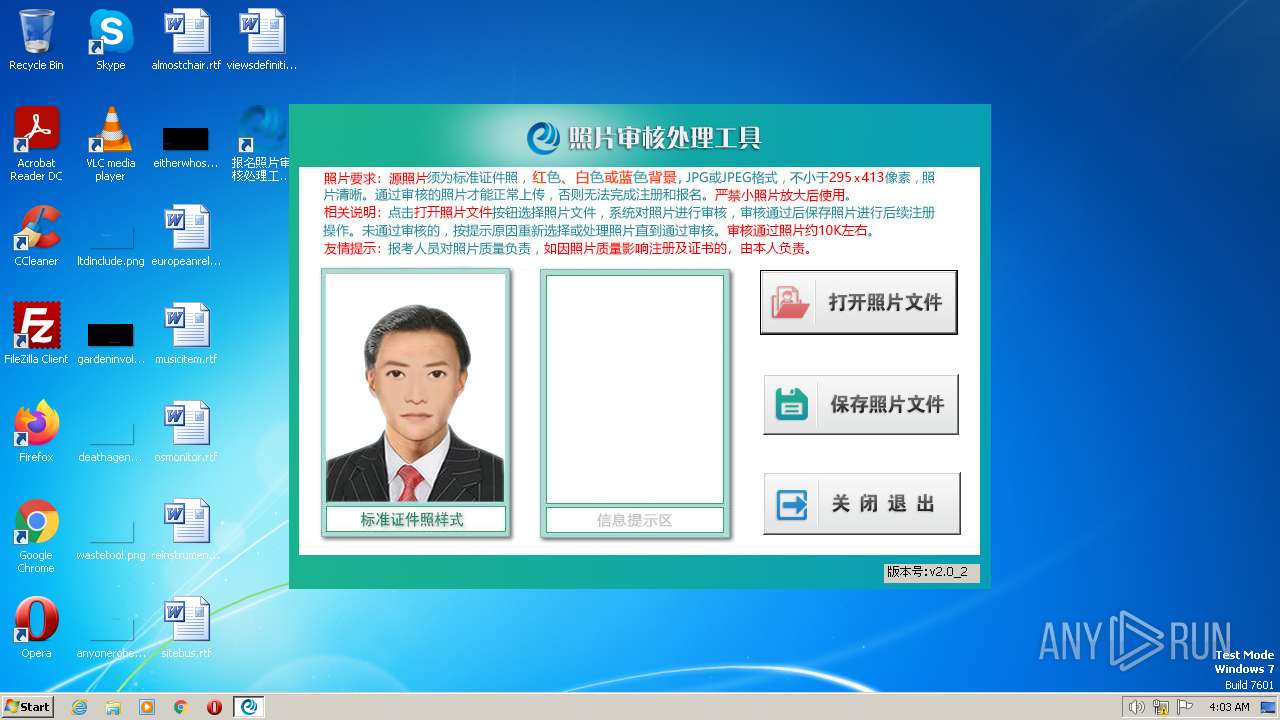
Manual execution by a user
- OumaPictureCheck.exe (PID: 3952)
- OumaPictureCheck.exe (PID: 3056)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x1f530 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 113152 |
| CodeSize: | 203776 |
| LinkerVersion: | 14.3 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit |
| TimeStamp: | 2022:03:03 13:15:57+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Mar-2022 13:15:57 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 03-Mar-2022 13:15:57 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00031BDC | 0x00031C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.71296 |
.rdata | 0x00033000 | 0x0000AEC0 | 0x0000B000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.26161 |
.data | 0x0003E000 | 0x00024720 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.38746 |
.didat | 0x00063000 | 0x00000190 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.33273 |
.rsrc | 0x00064000 | 0x0000D2AC | 0x0000D400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.85321 |
.reloc | 0x00072000 | 0x0000233C | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.62301 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.22792 | 1600 | Latin 1 / Western European | Chinese - PRC | RT_MANIFEST |
2 | 5.10026 | 2216 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 5.25868 | 3752 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
4 | 5.02609 | 1128 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
5 | 5.18109 | 4264 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
6 | 5.04307 | 9640 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
7 | 5.24197 | 182 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
8 | 5.27357 | 214 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
9 | 5.38938 | 202 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
10 | 5.08077 | 118 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
Imports
KERNEL32.dll |
OLEAUT32.dll |
USER32.dll (delay-loaded) |
gdiplus.dll |
Total processes
40
Monitored processes
3
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
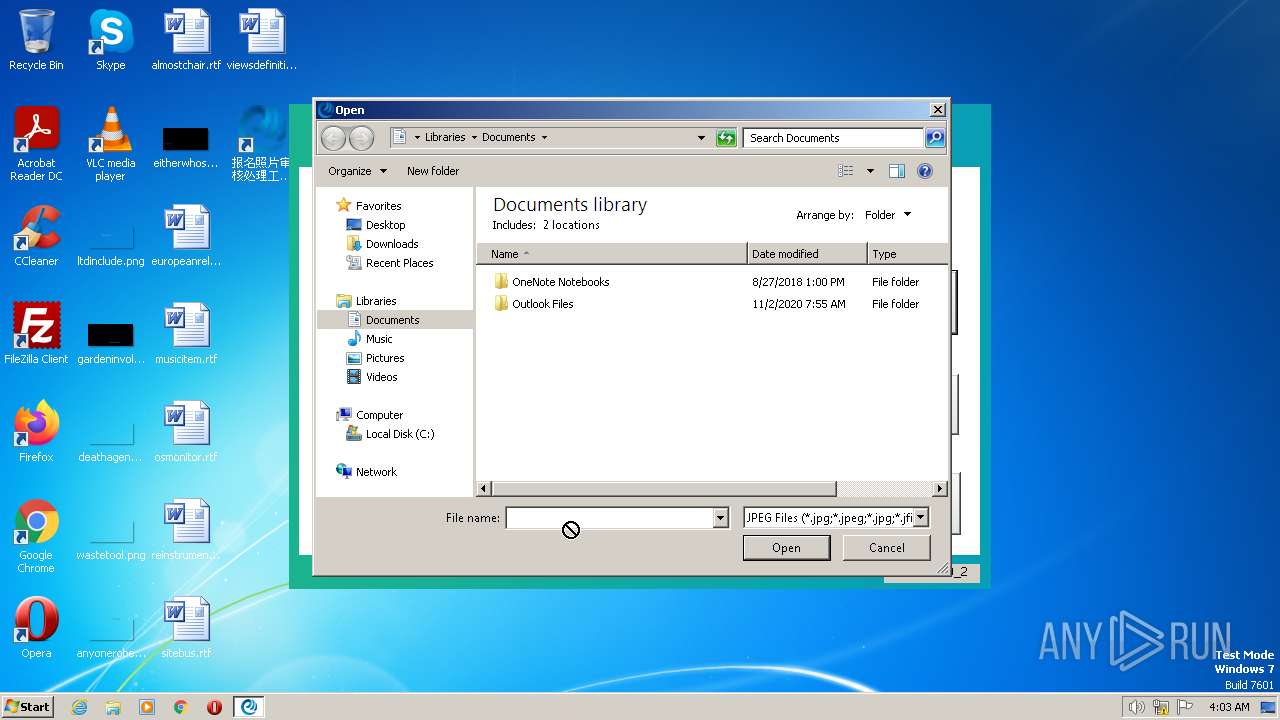
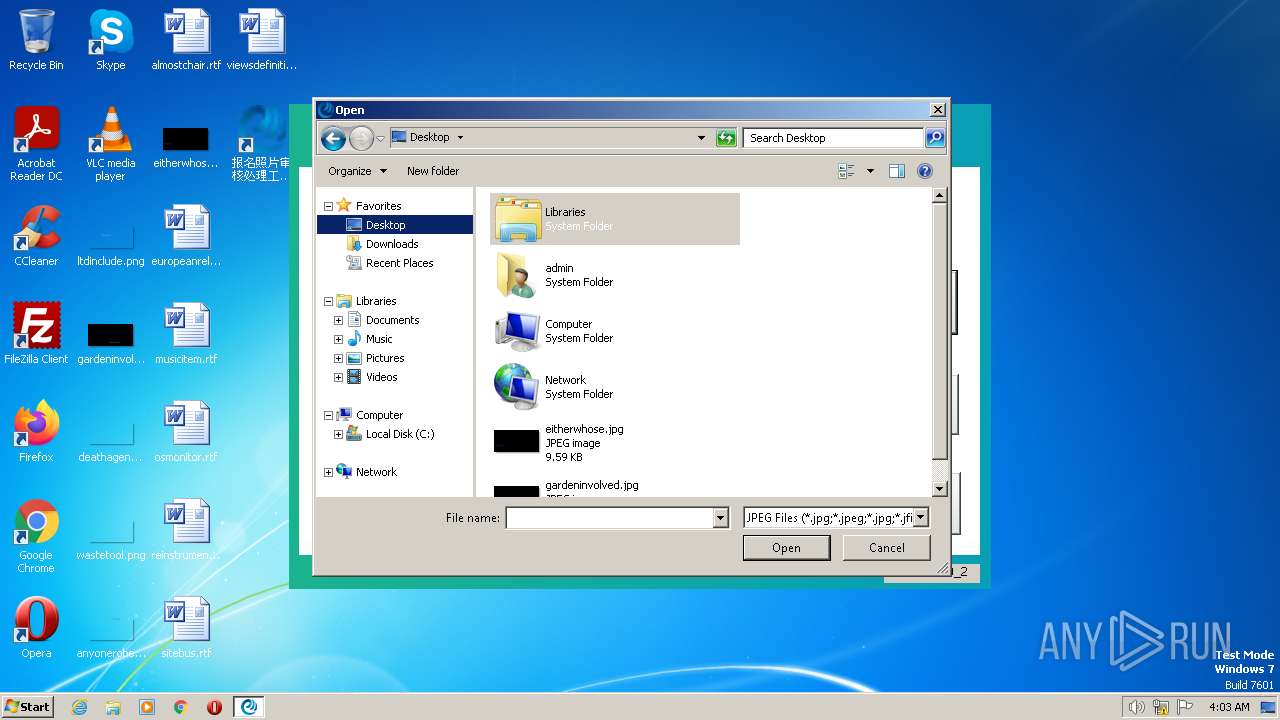
| 3056 | "C:\报名照片审核处理工具V2\OumaPictureCheck.exe" | C:\报名照片审核处理工具V2\OumaPictureCheck.exe | — | explorer.exe | |||||||||||
User: admin Company: TODO: <公司名> Integrity Level: MEDIUM Description: OumaPictureCheck Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 3096 | "C:\Users\admin\AppData\Local\Temp\maltest.exe" | C:\Users\admin\AppData\Local\Temp\maltest.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3952 | "C:\报名照片审核处理工具V2\OumaPictureCheck.exe" | C:\报名照片审核处理工具V2\OumaPictureCheck.exe | — | explorer.exe | |||||||||||
User: admin Company: TODO: <公司名> Integrity Level: MEDIUM Description: OumaPictureCheck Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
Total events
3 751
Read events
3 632
Write events
112
Delete events
7
Modification events
| (PID) Process: | (3096) maltest.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3096) maltest.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3096) maltest.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3096) maltest.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3096) maltest.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3096) maltest.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
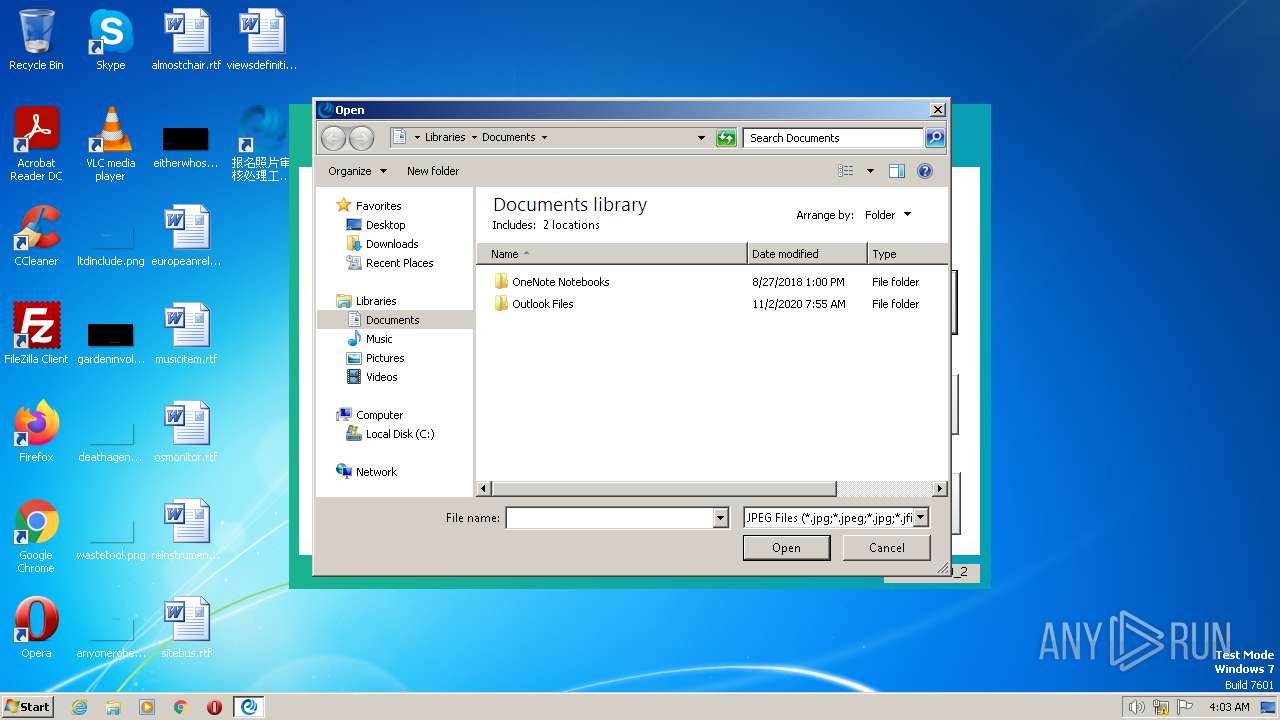
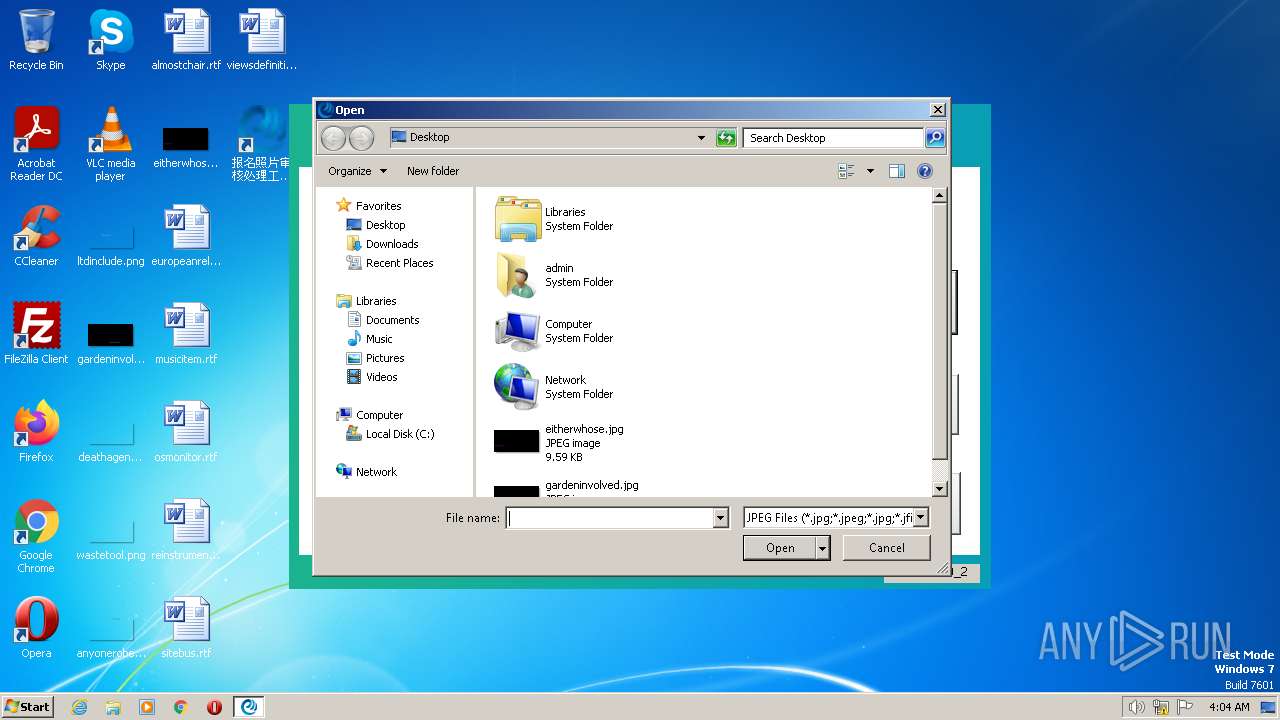
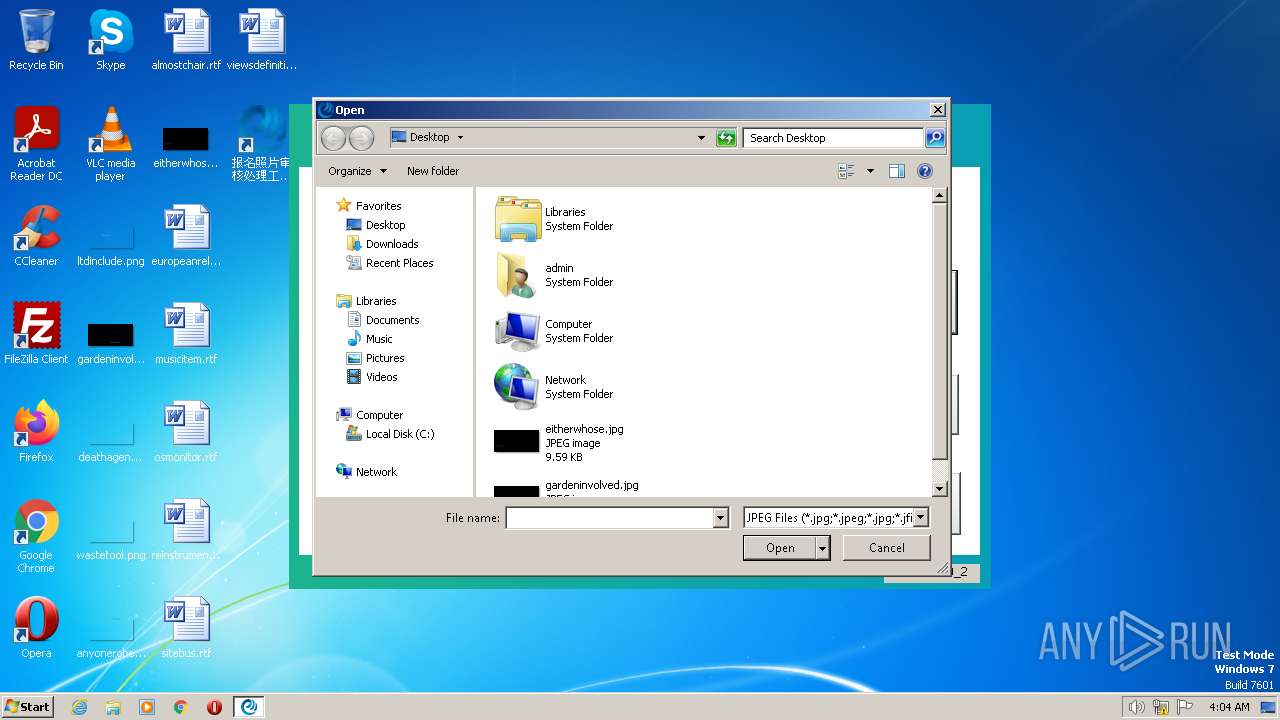
| (PID) Process: | (3952) OumaPictureCheck.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (3952) OumaPictureCheck.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 07000000020000000C000000000000000B000000010000000D000000060000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (3952) OumaPictureCheck.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 02000000070000000C000000000000000B000000010000000D000000060000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (3952) OumaPictureCheck.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
Executable files
8
Suspicious files
1
Text files
8
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
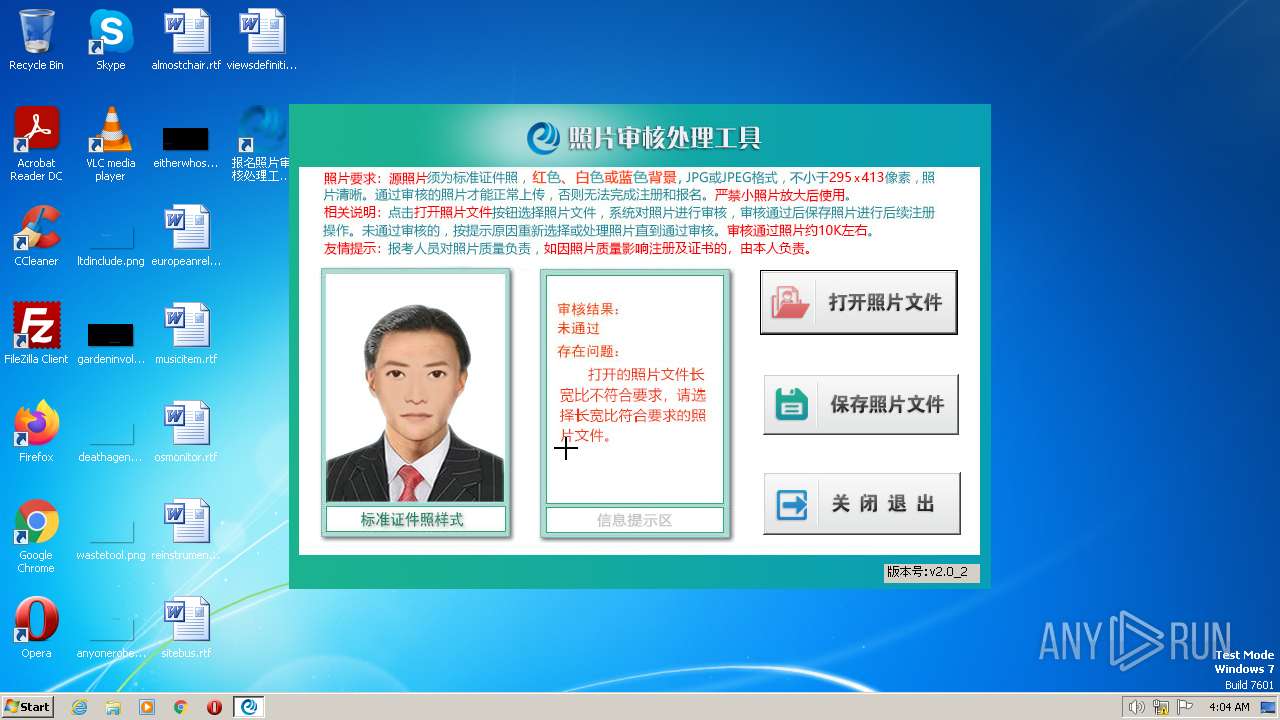
| 3096 | maltest.exe | C:\报名照片审核处理工具V2\tips\state4.jpg | image | |
MD5:E219979FAFAA6D8845CE93988BBD1F89 | SHA256:DE1F700B4B14949891C3C243CEC8AD08703EBF0F784787147C42DE3B4D62F863 | |||
| 3096 | maltest.exe | C:\报名照片审核处理工具V2\msvcp100.dll | executable | |
MD5:03E9314004F504A14A61C3D364B62F66 | SHA256:A3BA6421991241BEA9C8334B62C3088F8F131AB906C3CC52113945D05016A35F | |||
| 3096 | maltest.exe | C:\报名照片审核处理工具V2\mfc100u.dll | executable | |
MD5:F841F32AD816DBF130F10D86FAB99B1A | SHA256:7A4CFBCE1EB48D4F8988212C2E338D7781B9894EF0F525E871C22BB730A74F3E | |||
| 3096 | maltest.exe | C:\报名照片审核处理工具V2\tips\state6.jpg | image | |
MD5:2D545DCAC86D30611B217A6DB7BE41D7 | SHA256:4E59F848ABC7D06E9AA9B621D0EE58A2E7B5942ABC2425F02F2AA379A4186943 | |||
| 3096 | maltest.exe | C:\报名照片审核处理工具V2\tips\state1.jpg | image | |
MD5:DB3927D52EA711C59EBBB771B7653855 | SHA256:9BCB477E88572F36FA4152E75D5AC0B2326E4CE25CC6C9AA03D90B99AA0402F5 | |||
| 3096 | maltest.exe | C:\报名照片审核处理工具V2\tips\state3.jpg | image | |
MD5:D1BEF2B28A8F6A5C618FD74BDF75DE85 | SHA256:E9EB533770C2FB0BBA1B403538FCEB5664CD2DCADF8E9F0517DADBF7B6C44642 | |||
| 3096 | maltest.exe | C:\报名照片审核处理工具V2\tips\state7.jpg | image | |
MD5:62040539598488A499C2975190837920 | SHA256:6A8870D5CAAC23CDD72FBF4BD4CC86435310AA7A75C61A035B45BCCFBDC571FE | |||
| 3096 | maltest.exe | C:\报名照片审核处理工具V2\tips\state8.jpg | image | |
MD5:CD389856B0D9230DBDE25F5729FFE15F | SHA256:5052E7626BE3EA22B9126A6674E39690CD462234E2A4F727551414A0A34AFAD3 | |||
| 3096 | maltest.exe | C:\报名照片审核处理工具V2\haarcascade_frontalface_alt2.xml | xml | |
MD5:27968930FBBC590F038DCE22FF0E70AD | SHA256:F14CF5E321F9D9B6186E81E307F309FBE8EFC03598DDBF0CA4070F0794FFC30A | |||
| 3096 | maltest.exe | C:\报名照片审核处理工具V2\msvcr100.dll | executable | |
MD5:67EC459E42D3081DD8FD34356F7CAFC1 | SHA256:1221A09484964A6F38AF5E34EE292B9AFEFCCB3DC6E55435FD3AAF7C235D9067 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2692 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |