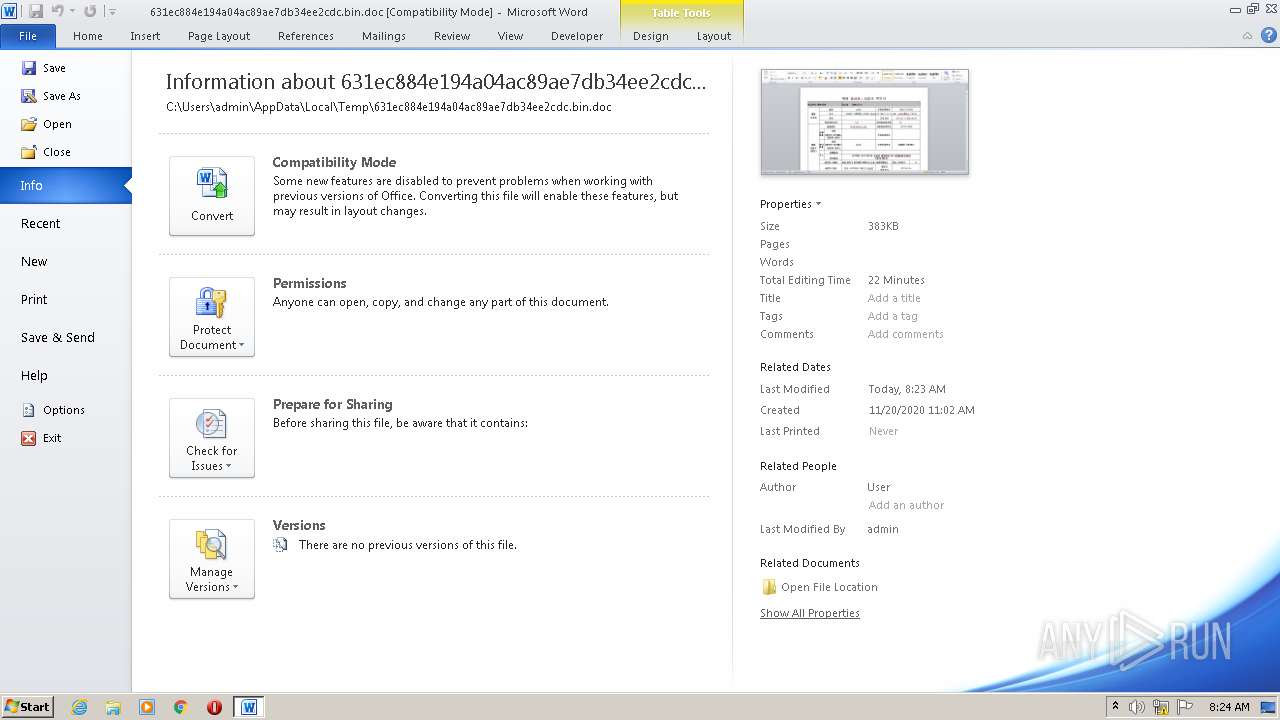
| File name: | 631ec884e194a04ac89ae7db34ee2cdc.bin |
| Full analysis: | https://app.any.run/tasks/d7abd3c7-0376-4607-a386-548bcd6e7207 |
| Verdict: | Malicious activity |
| Analysis date: | December 17, 2020, 08:23:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: -535, Author: User, Template: Normal.dotm, Last Saved By: Devil, Revision Number: 11, Name of Creating Application: Microsoft Office Word, Total Editing Time: 21:00, Create Time/Date: Fri Nov 20 02:02:00 2020, Last Saved Time/Date: Mon Dec 14 14:06:00 2020, Number of Pages: 1, Number of Words: 750, Number of Characters: 4280, Security: 8 |
| MD5: | 631EC884E194A04AC89AE7DB34EE2CDC |
| SHA1: | 0D686DAE87F79713D7382C4976ED796CAED5CA2B |
| SHA256: | FA71EEE906A7849BA3F4BAB74EDB577BD1F1F8397CA428591B4A9872CE1F1E9B |
| SSDEEP: | 6144:5LjzbI/TIwHvFzbI/TN97ONDYViv0hu7wPfY:dPIrHvFPIrN9S |
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2696)
Executes scripts
- WINWORD.EXE (PID: 2696)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1312)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2696)
Dropped object may contain Bitcoin addresses
- WINWORD.EXE (PID: 2696)
Creates files in the user directory
- WINWORD.EXE (PID: 2696)
Application launched itself
- chrome.exe (PID: 1312)
Manual execution by user
- chrome.exe (PID: 1312)
Reads the hosts file
- chrome.exe (PID: 1312)
- chrome.exe (PID: 1760)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | User |
| Keywords: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | Devil |
| RevisionNumber: | 11 |
| Software: | Microsoft Office Word |
| TotalEditTime: | 21.0 minutes |
| CreateDate: | 2020:11:20 02:02:00 |
| ModifyDate: | 2020:12:14 14:06:00 |
| Pages: | 1 |
| Words: | 750 |
| Characters: | 4280 |
| Security: | Locked for annotations |
| CodePage: | Unicode (UTF-8) |
| Company: | - |
| Lines: | 35 |
| Paragraphs: | 10 |
| CharCountWithSpaces: | 5020 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
72
Monitored processes
35
Malicious processes
1
Suspicious processes
0
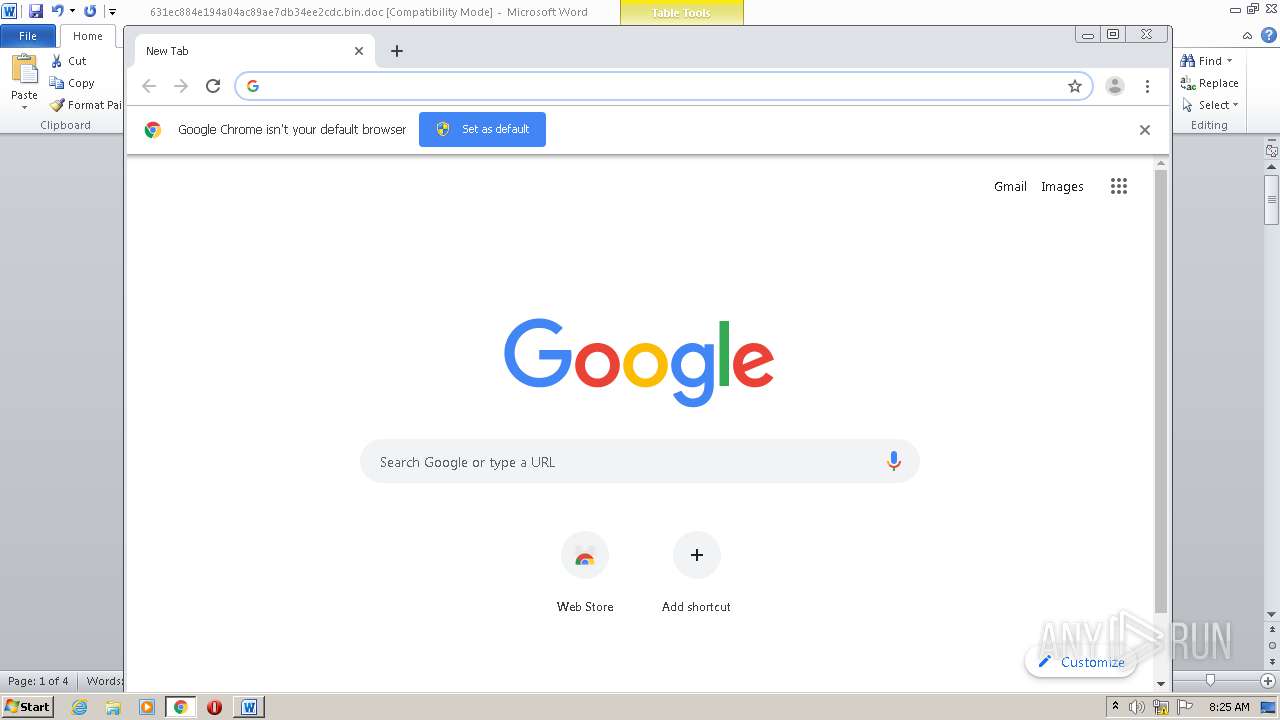
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 724 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,12964373586373542049,7678213923828936219,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6803692588389006200 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3588 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,12964373586373542049,7678213923828936219,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11907564416011215692 --mojo-platform-channel-handle=3312 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,12964373586373542049,7678213923828936219,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7595947899532219590 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3720 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,12964373586373542049,7678213923828936219,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6396641218707033616 --mojo-platform-channel-handle=3220 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=996,12964373586373542049,7678213923828936219,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=10624306623254015486 --mojo-platform-channel-handle=4208 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,12964373586373542049,7678213923828936219,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16243845276909994175 --mojo-platform-channel-handle=3832 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,12964373586373542049,7678213923828936219,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=5405528956717478297 --mojo-platform-channel-handle=1632 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1520 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,12964373586373542049,7678213923828936219,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4582447188955984995 --mojo-platform-channel-handle=4292 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 367
Read events
1 564
Write events
647
Delete events
156
Modification events
| (PID) Process: | (2696) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | rn? |
Value: 726E3F00880A0000010000000000000000000000 | |||
| (PID) Process: | (2696) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2696) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2696) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2696) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2696) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2696) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2696) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2696) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2696) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
46
Text files
206
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2696 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR4242.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2696 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~WRD0000.tmp | — | |
MD5:— | SHA256:— | |||
| 2696 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFA9F49285F17A0978.TMP | — | |
MD5:— | SHA256:— | |||
| 1312 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FDB15D9-520.pma | — | |
MD5:— | SHA256:— | |||
| 1312 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2696 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$1ec884e194a04ac89ae7db34ee2cdc.bin.doc | pgc | |
MD5:— | SHA256:— | |||
| 2696 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1312 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\8b78d9b0-119b-4eb1-84e7-18d2eec78076.tmp | — | |
MD5:— | SHA256:— | |||
| 2696 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\631ec884e194a04ac89ae7db34ee2cdc.bin.doc | document | |
MD5:— | SHA256:— | |||
| 2696 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~WRL0001.tmp | document | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
33
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
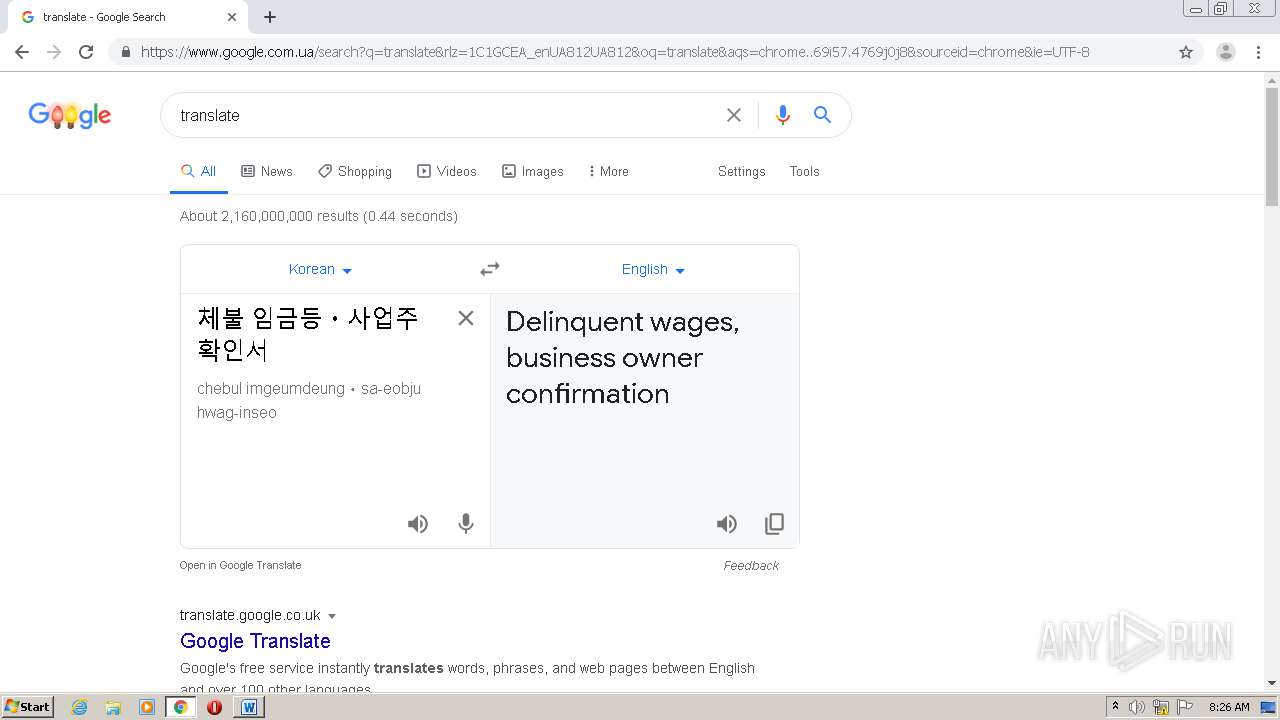
2728 | wscript.exe | GET | 404 | 211.233.50.229:80 | http://www.hahae.co.kr/new3/ISAF/Libs/php/cross.php?op=1&dt=1214&uid=01 | KR | html | 226 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1760 | chrome.exe | 172.217.23.142:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
2728 | wscript.exe | 211.233.50.229:80 | www.hahae.co.kr | LG DACOM Corporation | KR | malicious |
1760 | chrome.exe | 64.233.162.94:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1760 | chrome.exe | 216.58.212.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
1760 | chrome.exe | 216.58.205.227:443 | www.google.com.ua | Google Inc. | US | whitelisted |
1760 | chrome.exe | 64.233.162.95:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1760 | chrome.exe | 172.217.23.97:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
1760 | chrome.exe | 173.194.221.113:443 | consent.google.com | Google Inc. | US | unknown |
1760 | chrome.exe | 173.194.222.113:443 | clients1.google.com | Google Inc. | US | whitelisted |
1760 | chrome.exe | 172.217.23.110:443 | encrypted-tbn0.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.hahae.co.kr |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.google.com |
| malicious |