| File name: | fa5ce880e56b4fe51a8305319dddf16d21de8b2154a4eac0b318b42c781e46dc.bin |
| Full analysis: | https://app.any.run/tasks/cb13c048-73b9-4b81-81e1-4071537e76c5 |
| Verdict: | Malicious activity |
| Analysis date: | February 18, 2019, 14:18:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/rtf |
| File info: | Rich Text Format data, version 1, unknown character set |
| MD5: | 35668D4E0B695960EA55263ED4E62533 |
| SHA1: | 20DFD58B4F45EFC773422A5D03DFD2BE02FC5F16 |
| SHA256: | FA5CE880E56B4FE51A8305319DDDF16D21DE8B2154A4EAC0B318B42C781E46DC |
| SSDEEP: | 6144:3b2x2MNb2x2M4b2x2Mdb2x2MLb2x2MKb2x2MWb2x2M9b2x2MCb2x2Mrb2x2MM2cE:L2Fx2F02Fh2Ff2Fu2Fa2FB2Fm2F/2F0O |
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3136)
SUSPICIOUS
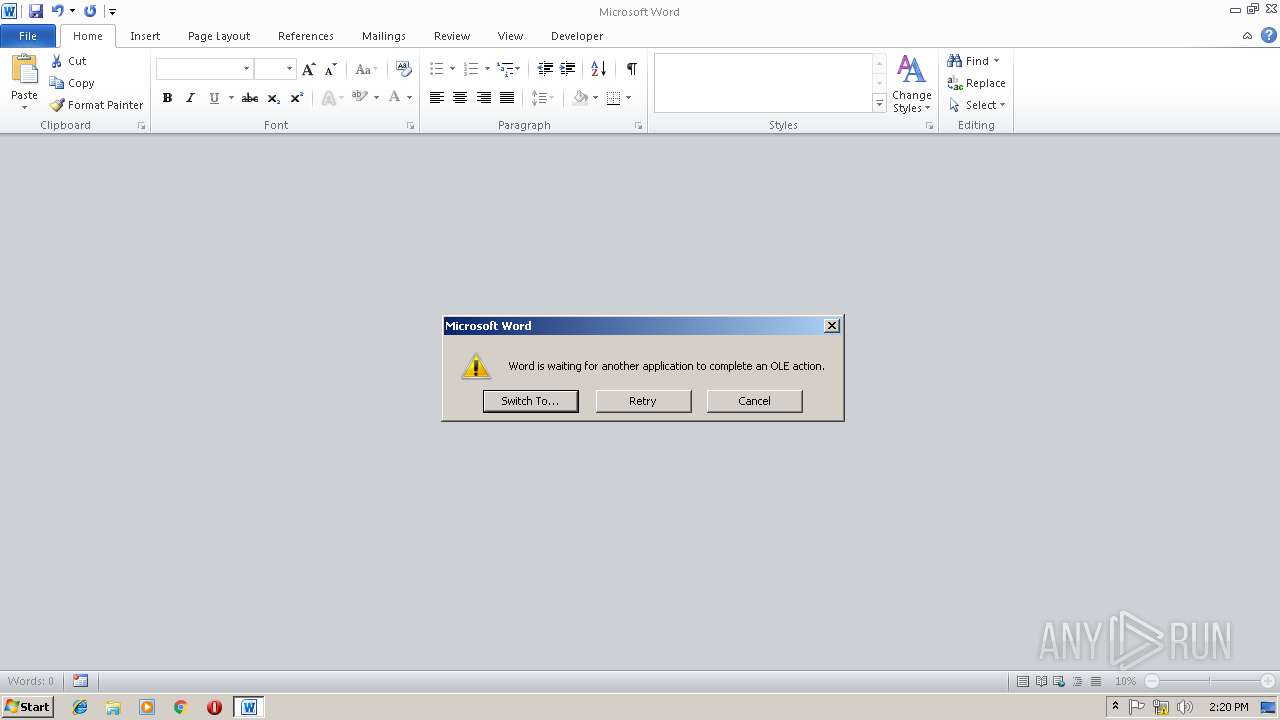
Unusual connect from Microsoft Office
- EXCEL.EXE (PID: 460)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3136)
- EXCEL.EXE (PID: 460)
Creates files in the user directory
- EXCEL.EXE (PID: 460)
- WINWORD.EXE (PID: 3136)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
EXIF
RTF
| Author: | Unknown Error!! |
|---|---|
| LastModifiedBy: | Unknown Error!! |
| CreateDate: | 2018:04:21 20:50:00 |
| ModifyDate: | 2018:04:21 20:51:00 |
| RevisionNumber: | 1 |
| TotalEditTime: | 1 minute |
| Pages: | 1 |
| Words: | 64 |
| Characters: | 367 |
| CharactersWithSpaces: | 430 |
| InternalVersionNumber: | 86 |
| Saveprevpict: | - |
Total processes
33
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 460 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
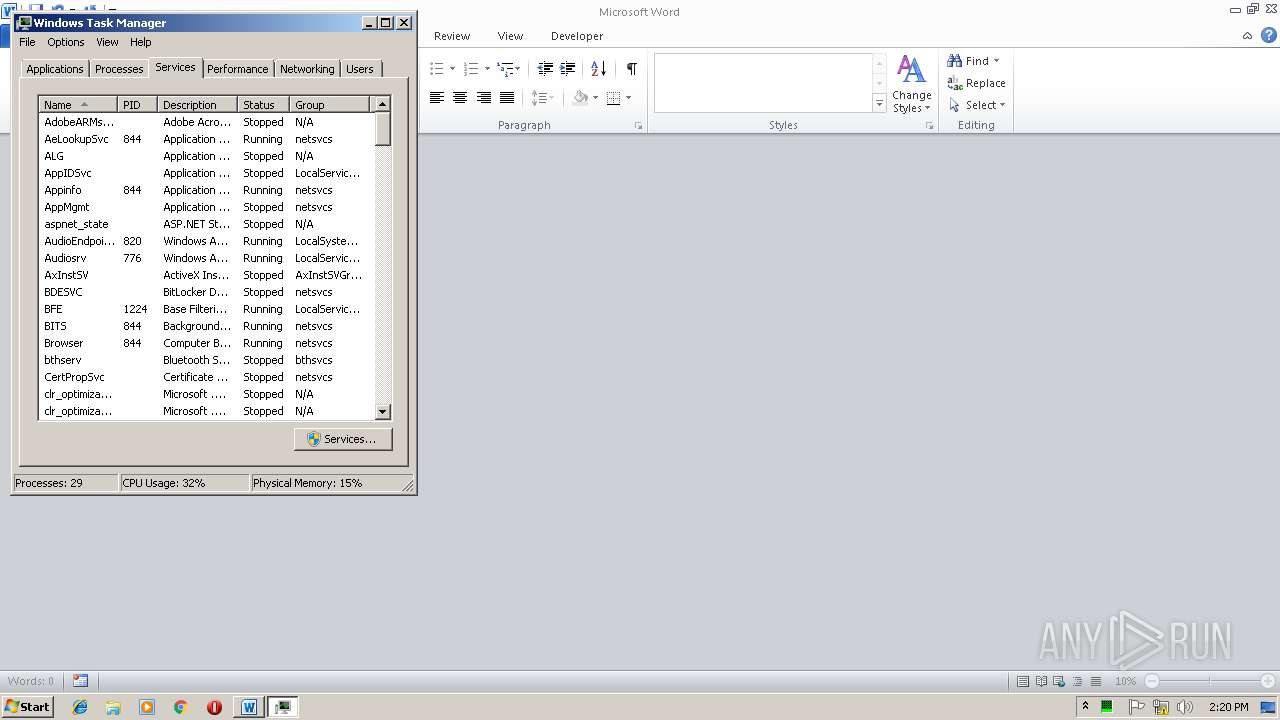
| 2748 | "C:\Windows\system32\taskmgr.exe" | C:\Windows\system32\taskmgr.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3136 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\fa5ce880e56b4fe51a8305319dddf16d21de8b2154a4eac0b318b42c781e46dc.bin.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
786
Read events
611
Write events
171
Delete events
4
Modification events
| (PID) Process: | (3136) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 10 |
Value: 20313000400C0000010000000000000000000000 | |||
| (PID) Process: | (3136) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3136) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3136) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1313996821 | |||
| (PID) Process: | (3136) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1313996940 | |||
| (PID) Process: | (3136) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1313996941 | |||
| (PID) Process: | (3136) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 400C000080622AE394C7D40100000000 | |||
| (PID) Process: | (3136) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 330 |
Value: 33333000400C000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3136) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | 330 |
Value: 33333000400C000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3136) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3136 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6D80.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 460 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR77E0.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 460 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DFC12C4062FCD4A6D5.TMP | — | |
MD5:— | SHA256:— | |||
| 3136 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 460 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3136 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\AB757F29.emf | emf | |
MD5:— | SHA256:— | |||
| 460 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\VBE\RefEdit.exd | tlb | |
MD5:— | SHA256:— | |||
| 3136 | WINWORD.EXE | C:\Users\admin\Desktop\~$5ce880e56b4fe51a8305319dddf16d21de8b2154a4eac0b318b42c781e46dc.bin.rtf | pgc | |
MD5:— | SHA256:— | |||
| 460 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Forms\RefEdit.exd | tlb | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
460 | EXCEL.EXE | GET | — | 185.139.236.218:80 | http://stevemike-fireforce.info/work/exe/2.doc | AE | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
460 | EXCEL.EXE | 185.139.236.218:80 | stevemike-fireforce.info | Digital Energy Technologies Limited | AE | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
stevemike-fireforce.info |
| malicious |