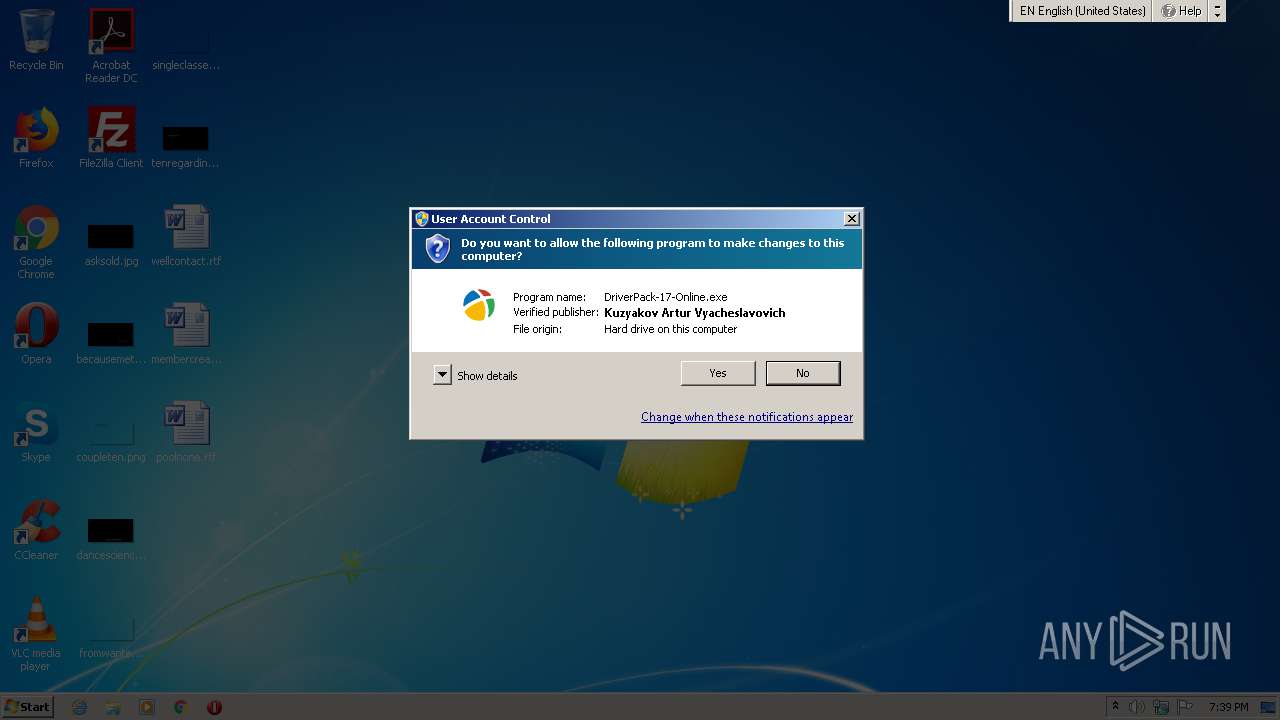
| File name: | DriverPack-17-Online.exe |
| Full analysis: | https://app.any.run/tasks/5c8ac683-63ef-49c0-8f1f-37e2bb0e52c2 |
| Verdict: | Malicious activity |
| Analysis date: | May 07, 2021, 18:39:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
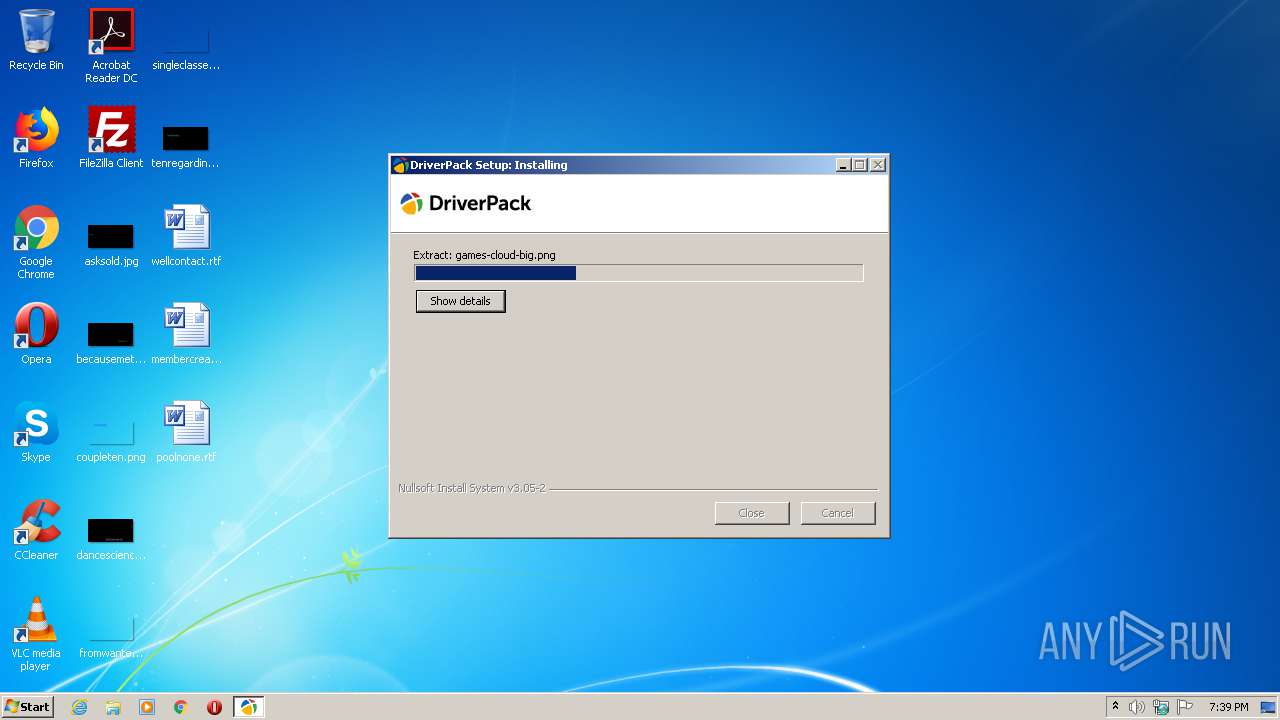
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | B2E44D9A821A3CA7E7BE9C61033569C7 |
| SHA1: | 22F6161E939C4A54CE06E28C9843C7E1C23AF451 |
| SHA256: | FA5BA472C2F3629AE581F19D03990265F3A121E00E6EB551147C092BDC7AE5C1 |
| SSDEEP: | 196608:eOCz54hpqG/YejQ7VqcQPnyYuwwd8B//a9fSuAS:eOCz54Sg87VqcQ/ypz8BX0oS |
MALICIOUS
Loads dropped or rewritten executable
- DriverPack-17-Online.exe (PID: 3400)
Drops executable file immediately after starts
- DriverPack-17-Online.exe (PID: 3400)
Changes settings of System certificates
- mshta.exe (PID: 2832)
SUSPICIOUS
Adds / modifies Windows certificates
- mshta.exe (PID: 2832)
Executable content was dropped or overwritten
- DriverPack-17-Online.exe (PID: 3400)
Uses REG.EXE to modify Windows registry
- DriverPack-17-Online.exe (PID: 3400)
Drops a file that was compiled in debug mode
- DriverPack-17-Online.exe (PID: 3400)
Starts MSHTA.EXE for opening HTA or HTMLS files
- DriverPack-17-Online.exe (PID: 3400)
INFO
Reads internet explorer settings
- mshta.exe (PID: 2832)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0x433c |
| UninitializedDataSize: | 108032 |
| InitializedDataSize: | 40448 |
| CodeSize: | 36864 |
| LinkerVersion: | 2.34 |
| PEType: | PE32 |
| TimeStamp: | 2020:03:31 20:05:25+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 31-Mar-2020 18:05:25 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 31-Mar-2020 18:05:25 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00008F54 | 0x00009000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.9641 |
.data | 0x0000A000 | 0x000000C0 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.42446 |
.rdata | 0x0000B000 | 0x0000736C | 0x00007400 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.28118 |
.bss | 0x00013000 | 0x0001A500 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0002E000 | 0x0000133C | 0x00001400 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.30969 |
.ndata | 0x00030000 | 0x0000B000 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0003B000 | 0x00006DF0 | 0x00006E00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.45806 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28991 | 1072 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.58588 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 4.36124 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 4.91149 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 2.97923 | 1640 | UNKNOWN | English - United States | RT_ICON |
6 | 4.97199 | 1384 | UNKNOWN | English - United States | RT_ICON |
7 | 5.66158 | 1128 | UNKNOWN | English - United States | RT_ICON |
8 | 3.35004 | 744 | UNKNOWN | English - United States | RT_ICON |
9 | 3.10795 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 2.89097 | 132 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.DLL |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
45
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 568 | "C:\Users\admin\AppData\Local\Temp\DriverPack-17-Online.exe" | C:\Users\admin\AppData\Local\Temp\DriverPack-17-Online.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2760 | C:\Windows\system32\reg.exe import "C:\Users\admin\AppData\Local\Temp\DriverPack-20210507193956\Tools\patch.reg" | C:\Windows\system32\reg.exe | — | DriverPack-17-Online.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2832 | C:\Windows\system32\mshta.exe "C:\Users\admin\AppData\Local\Temp\DriverPack-20210507193956\run.hta" --sfx "DriverPack-17-Online.exe" | C:\Windows\system32\mshta.exe | DriverPack-17-Online.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3400 | "C:\Users\admin\AppData\Local\Temp\DriverPack-17-Online.exe" | C:\Users\admin\AppData\Local\Temp\DriverPack-17-Online.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
535
Read events
505
Write events
30
Delete events
0
Modification events
| (PID) Process: | (2760) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap\Domains\drp.su\update |
| Operation: | write | Name: | http |
Value: 1 | |||
| (PID) Process: | (2760) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap\Domains\drp.su\update |
| Operation: | write | Name: | https |
Value: 1 | |||
| (PID) Process: | (2760) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | GlobalUserOffline |
Value: 0 | |||
| (PID) Process: | (2760) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Styles |
| Operation: | write | Name: | MaxScriptStatements |
Value: 4294967295 | |||
| (PID) Process: | (2760) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\Styles |
| Operation: | write | Name: | MaxScriptStatements |
Value: 4294967295 | |||
| (PID) Process: | (2832) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2832) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2832) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2832) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2832) mshta.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
6
Suspicious files
3
Text files
469
Unknown types
33
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3400 | DriverPack-17-Online.exe | C:\Users\admin\AppData\Local\Temp\DriverPack-20210507193956\Tools\run.hta | html | |
MD5:F4499E8AD06CE5D39EAB7AF33500EFF6 | SHA256:871DB2D195F628C2A4CB56B68FB87101504042BB9110396C58B6EA575EFCD3F3 | |||
| 3400 | DriverPack-17-Online.exe | C:\Users\admin\AppData\Local\Temp\nsu6FD6.tmp\System.dll | executable | |
MD5:825B584EA5FCB8F9173539EA0421CB65 | SHA256:21B23E46F2737B89200F90A2A783289F37D6B713161243677419849B2BCEEC66 | |||
| 3400 | DriverPack-17-Online.exe | C:\Users\admin\AppData\Local\Temp\DriverPack-20210507193956\config.js | text | |
MD5:6EC1DD6405BA130D773B1549528A3E0B | SHA256:FD46C9B5EA3299749CF28D767A3C0A610A5C5014B9576BF0215601B02CBB2585 | |||
| 3400 | DriverPack-17-Online.exe | C:\Users\admin\AppData\Local\Temp\DriverPack-20210507193956\drp.js | binary | |
MD5:D2A8709C8E4E5894BC8A043513F7B3DB | SHA256:E2C653A5E255F91558DE09B5FCE9388669BF554122F92FCE8E4DB0D6A47FA23C | |||
| 3400 | DriverPack-17-Online.exe | C:\Users\admin\AppData\Local\Temp\DriverPack-20210507193956\Tools\Icon.ico | image | |
MD5:733D67C2E70BC804CD9497D20FE96696 | SHA256:0A3EDD3D1FD9AE649D0D6164858705017DC482CE56D090A478F57D02619E88CE | |||
| 3400 | DriverPack-17-Online.exe | C:\Users\admin\AppData\Local\Temp\DriverPack-20210507193956\Tools\load8.gif | image | |
MD5:8A061EF740FA2801AB4BF78CB123D9BE | SHA256:EE0CC89EF293B559B64FCB35B469DCB144180FF048B0B6EB14F326847A544903 | |||
| 3400 | DriverPack-17-Online.exe | C:\Users\admin\AppData\Local\Temp\DriverPack-20210507193956\Tools\patch.reg | text | |
MD5:D49DB2EC30494B46D332D516CEAD4969 | SHA256:C86EF9ED6E111D166818E8E0ADB3CF5E2A3A5DFC6EDC932ABC298141ED6F2208 | |||
| 3400 | DriverPack-17-Online.exe | C:\Users\admin\AppData\Local\Temp\DriverPack-20210507193956\run.hta | html | |
MD5:ED292CB8F313B1BA861D555BAC9C82FD | SHA256:79EDC163FB9BF7D4F56941114EC374DBB5F631371E524A6AF7BCB23F479319BA | |||
| 3400 | DriverPack-17-Online.exe | C:\Users\admin\AppData\Local\Temp\DriverPack-20210507193956\Tools\modules\bugreport.hta | html | |
MD5:492B077CD9C947C4CCCAB9ACD25E6C43 | SHA256:14763E4336A3F96FA2D9AEB5A55DFAD39672BA2CE68114C582C56D874350C386 | |||
| 3400 | DriverPack-17-Online.exe | C:\Users\admin\AppData\Local\Temp\DriverPack-20210507193956\css\icons.css | text | |
MD5:EBAE852F3327FDAF3E2FC2BF1CDECB8F | SHA256:B5F111103F7F090C246A223B1FF497B94C4DD3AC64BF5B3FB2D91555FCFD6F2C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2832 | mshta.exe | GET | 301 | 172.67.215.78:80 | http://allfont.ru/allfont.css?fonts=lucida-console | US | — | — | whitelisted |
2832 | mshta.exe | GET | 301 | 172.67.215.78:80 | http://allfont.ru/cache/css/lucida-console.css | US | — | — | whitelisted |
2832 | mshta.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2832 | mshta.exe | 172.67.215.78:80 | allfont.ru | — | US | suspicious |
2832 | mshta.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2832 | mshta.exe | 172.67.215.78:443 | allfont.ru | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
allfont.ru |
| whitelisted |
ocsp.digicert.com |
| whitelisted |