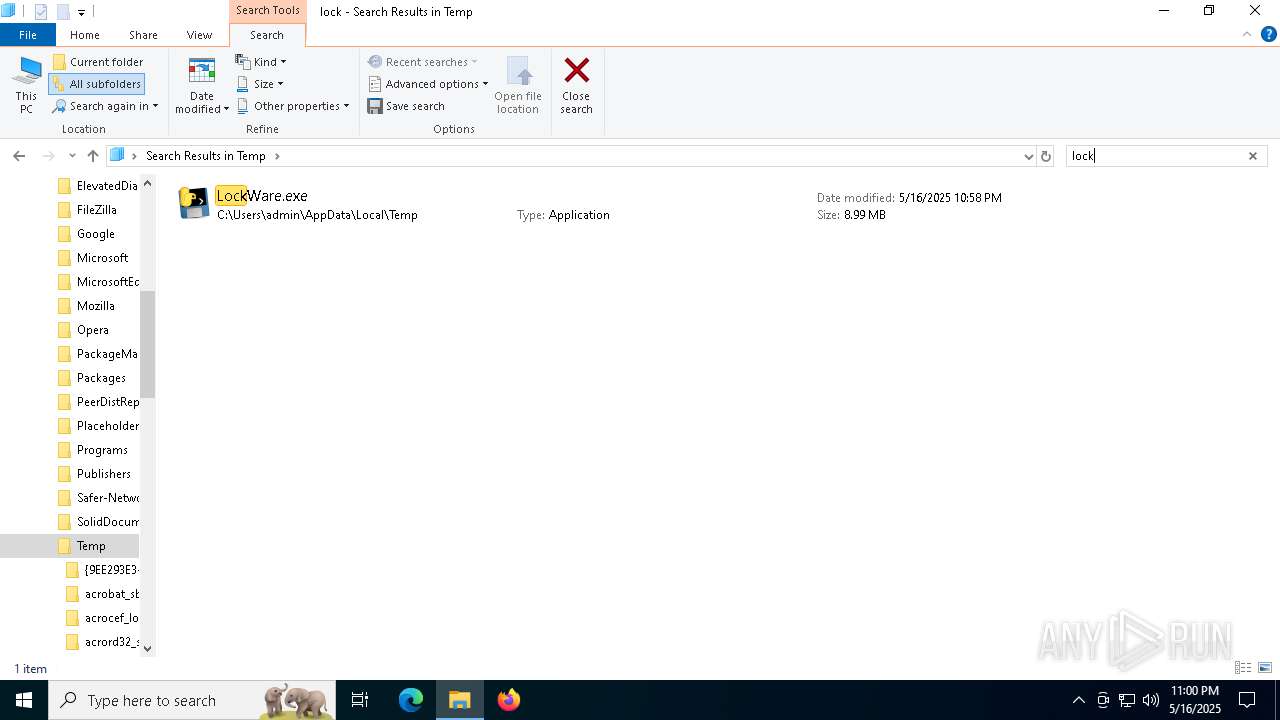
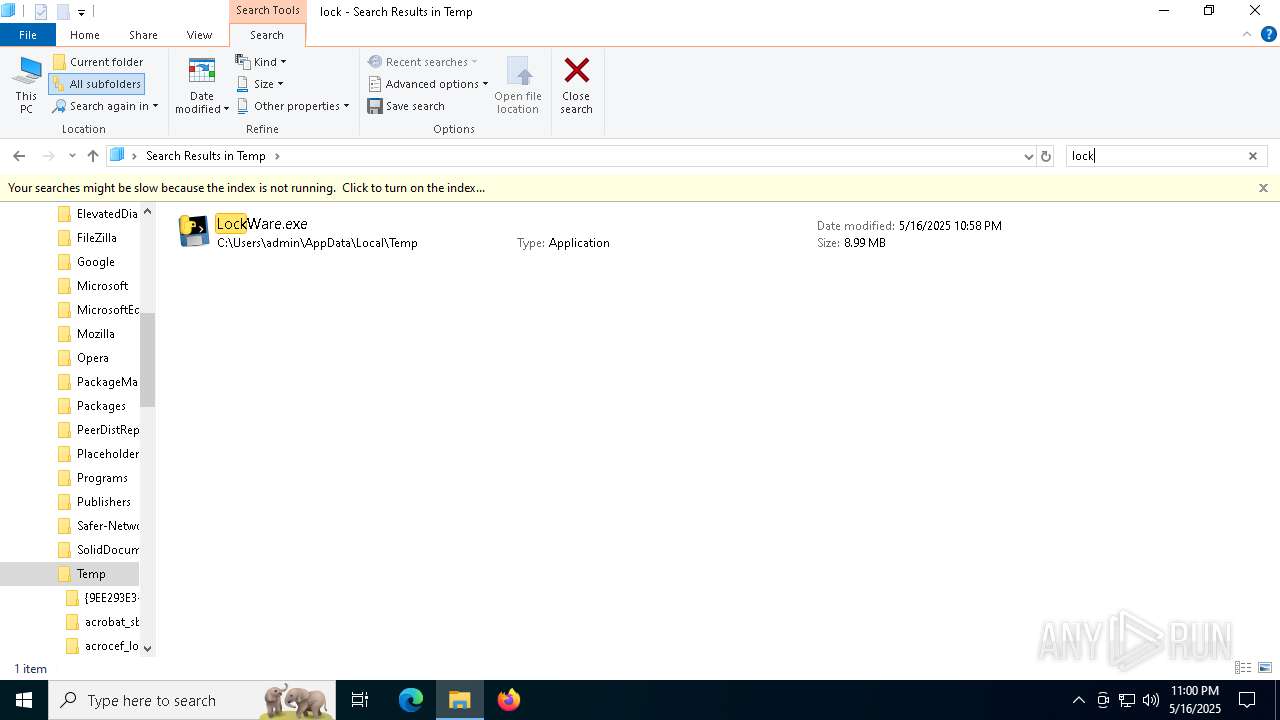
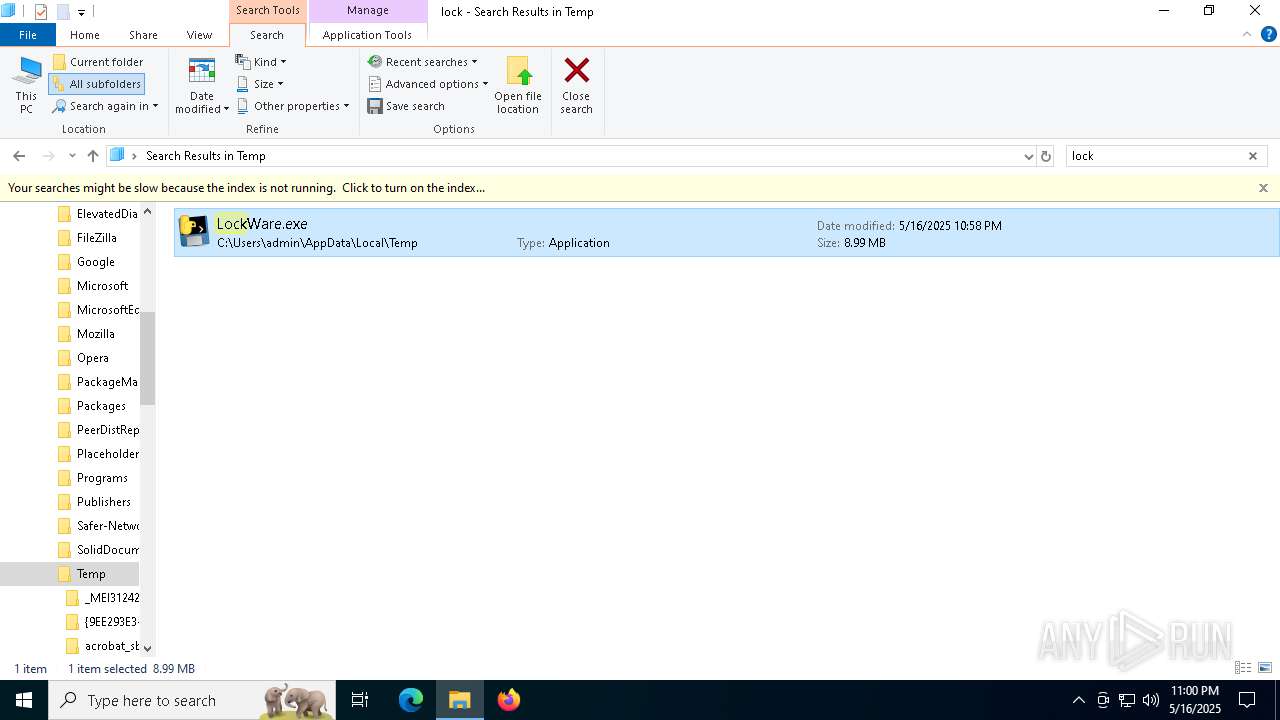
| File name: | LockWare.exe |
| Full analysis: | https://app.any.run/tasks/56cab398-0fdc-4745-817f-2f5def803595 |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2025, 22:58:19 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 7 sections |
| MD5: | 71B5ED6A376D0599C6EEAFFCDEF5D851 |
| SHA1: | E56FFC00F1940D014607ECAC28A008D1B6717BF1 |
| SHA256: | FA531EBCFEB7D76BC3C619A550A1F3145B127ACD79107C4E33672DD1B6DF4B76 |
| SSDEEP: | 98304:exb2m39YdSUgcXLl0w10hpqt3/bxst+KkJKNueaoUNM6/cdQvccdxpRSVBUDwREH:Zduh+XG44aBw4W |
MALICIOUS
No malicious indicators.SUSPICIOUS
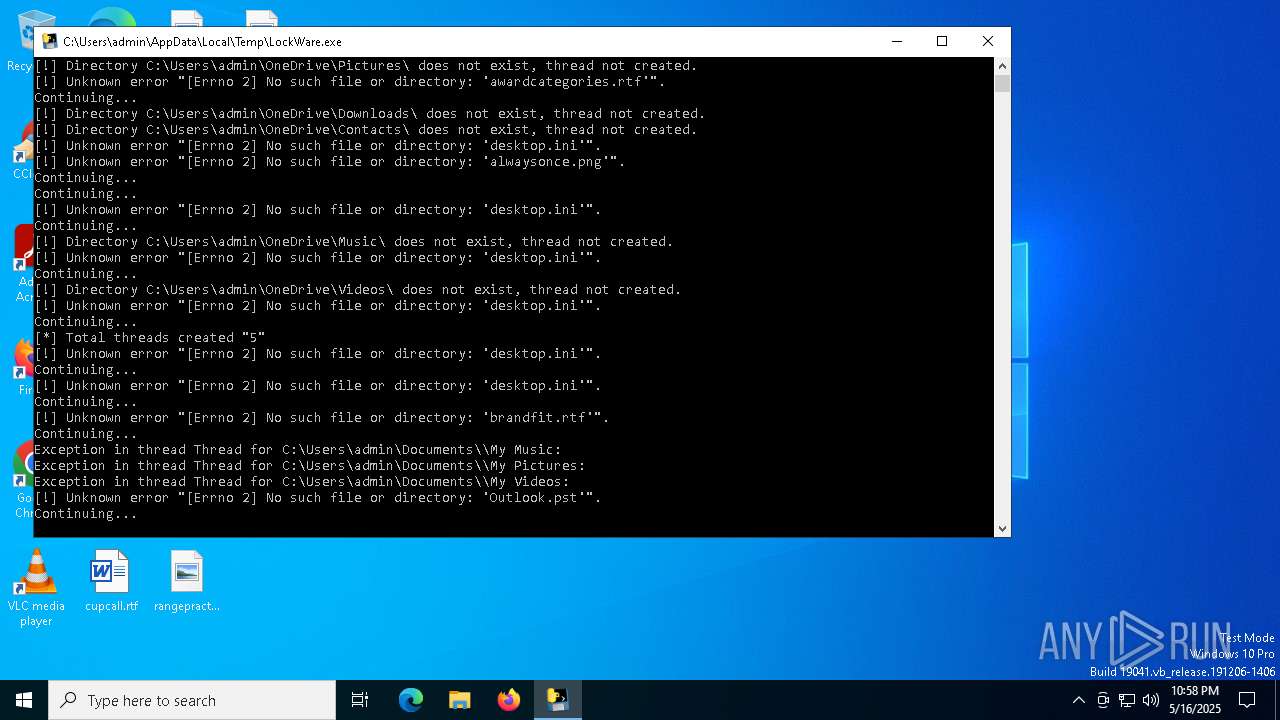
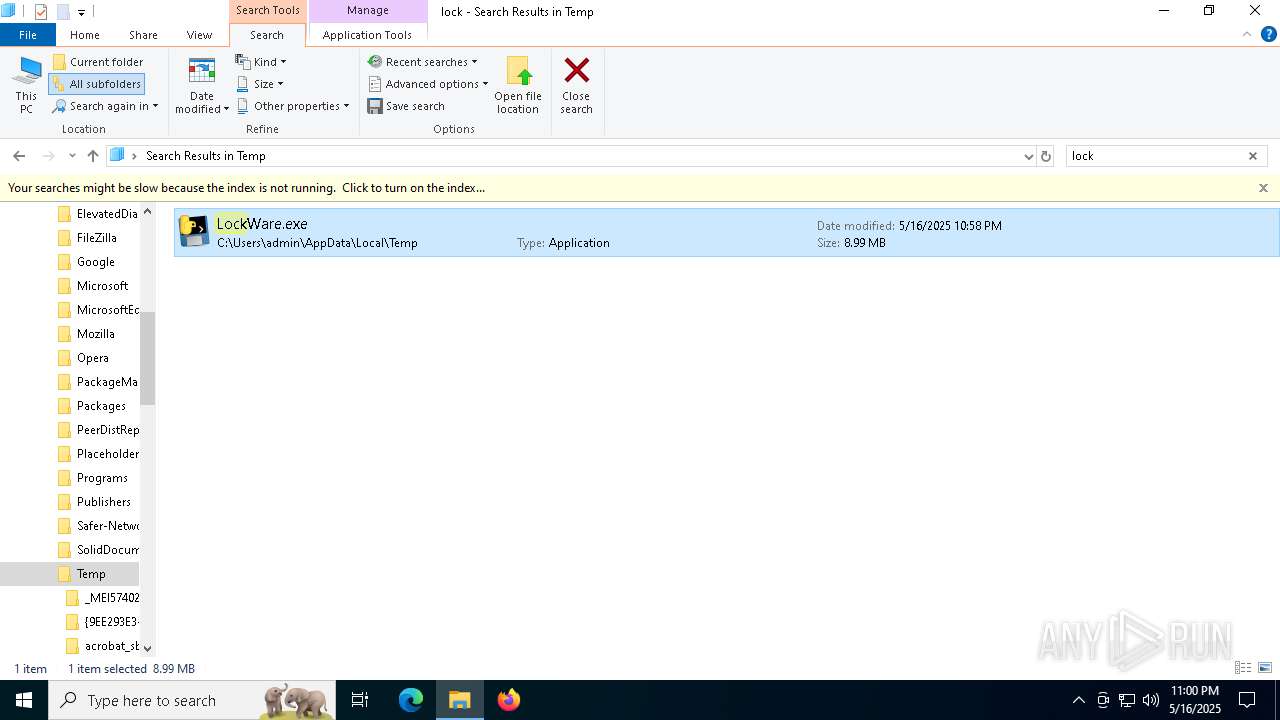
The process drops C-runtime libraries
- LockWare.exe (PID: 1672)
- LockWare.exe (PID: 5740)
- LockWare.exe (PID: 3124)
- LockWare.exe (PID: 4012)
Process drops python dynamic module
- LockWare.exe (PID: 1672)
- LockWare.exe (PID: 3124)
- LockWare.exe (PID: 4012)
- LockWare.exe (PID: 5740)
Process drops legitimate windows executable
- LockWare.exe (PID: 1672)
- LockWare.exe (PID: 5740)
- LockWare.exe (PID: 3124)
- LockWare.exe (PID: 4012)
Executable content was dropped or overwritten
- LockWare.exe (PID: 1672)
- LockWare.exe (PID: 3124)
- LockWare.exe (PID: 4012)
- LockWare.exe (PID: 5740)
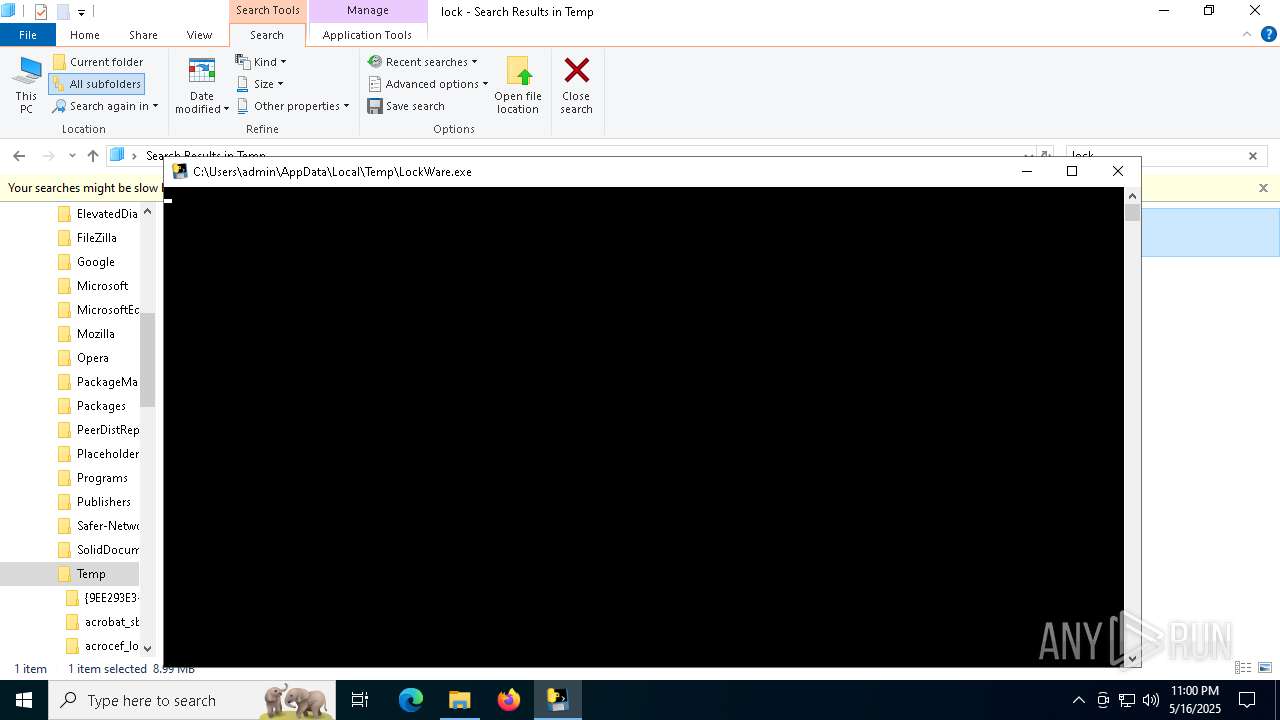
Application launched itself
- LockWare.exe (PID: 1672)
- LockWare.exe (PID: 5740)
- LockWare.exe (PID: 3124)
- LockWare.exe (PID: 4012)
Loads Python modules
- LockWare.exe (PID: 6800)
- LockWare.exe (PID: 1568)
- LockWare.exe (PID: 5112)
- LockWare.exe (PID: 2780)
INFO
Checks supported languages
- LockWare.exe (PID: 1672)
- LockWare.exe (PID: 6800)
- LockWare.exe (PID: 5740)
- LockWare.exe (PID: 1568)
- LockWare.exe (PID: 3124)
- LockWare.exe (PID: 5112)
- LockWare.exe (PID: 4012)
- LockWare.exe (PID: 2780)
Reads the computer name
- LockWare.exe (PID: 1672)
- LockWare.exe (PID: 5740)
- LockWare.exe (PID: 3124)
- LockWare.exe (PID: 4012)
The sample compiled with english language support
- LockWare.exe (PID: 1672)
- LockWare.exe (PID: 5740)
- LockWare.exe (PID: 4012)
- LockWare.exe (PID: 3124)
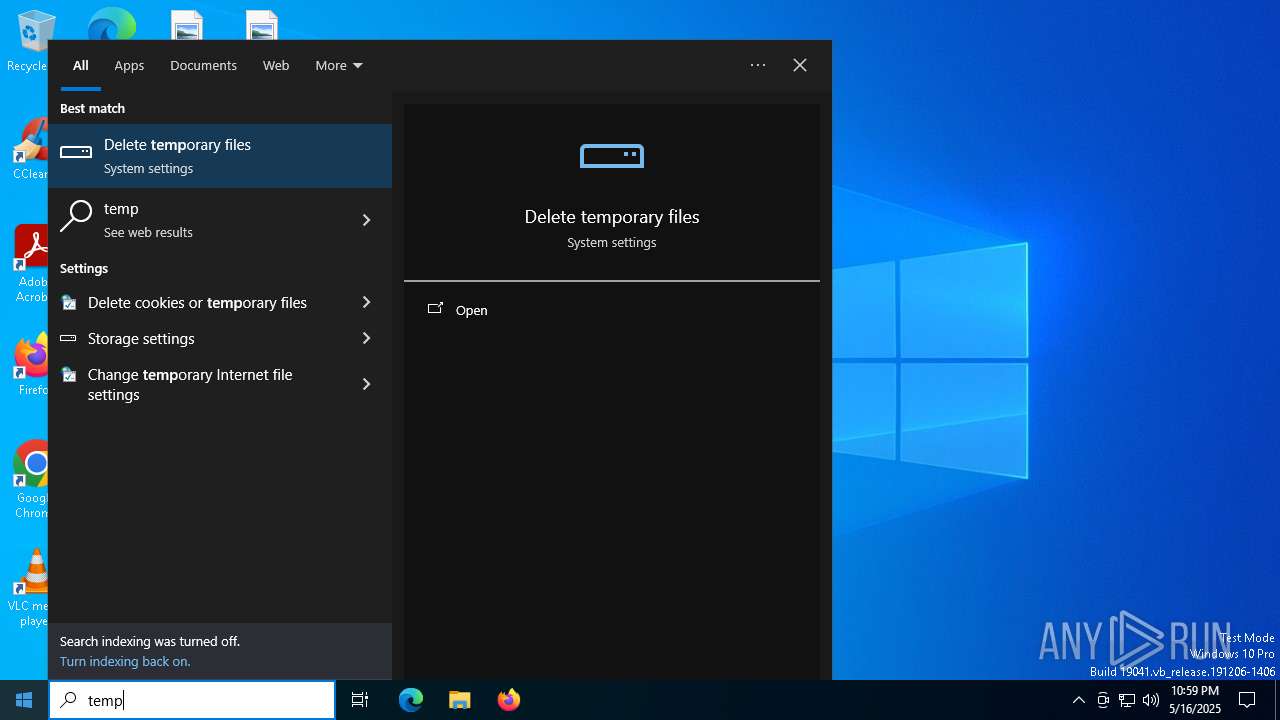
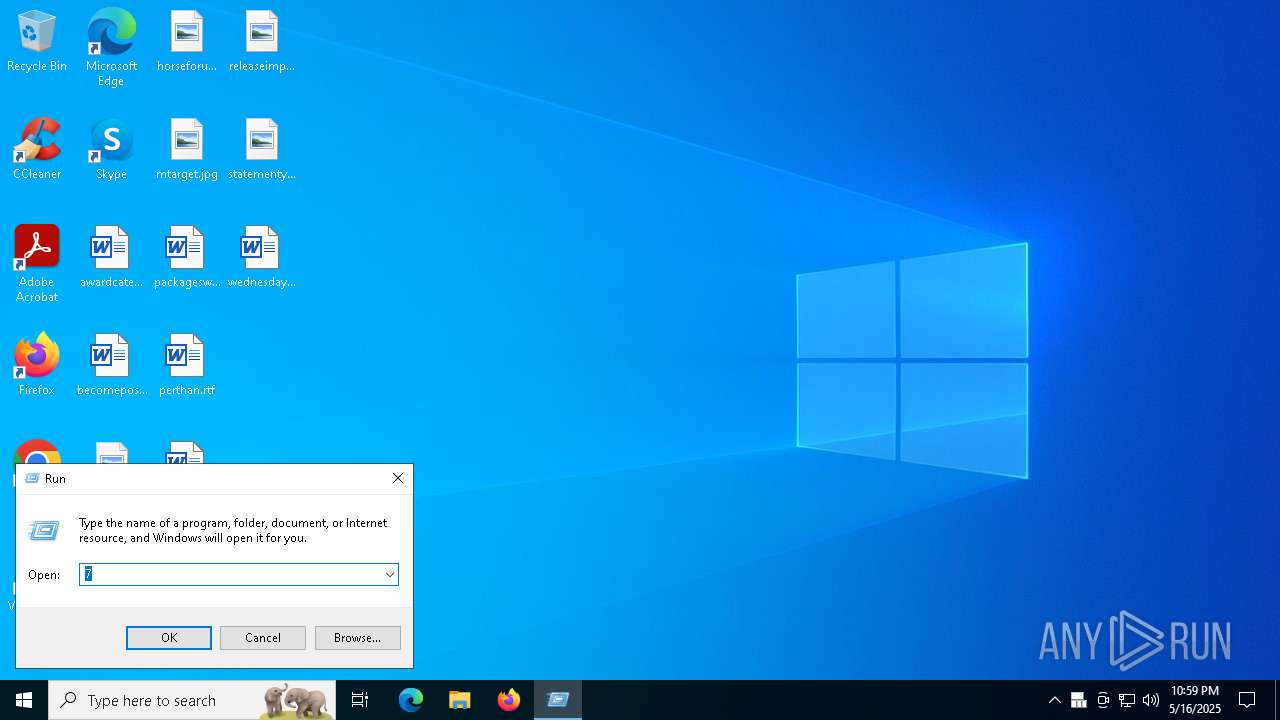
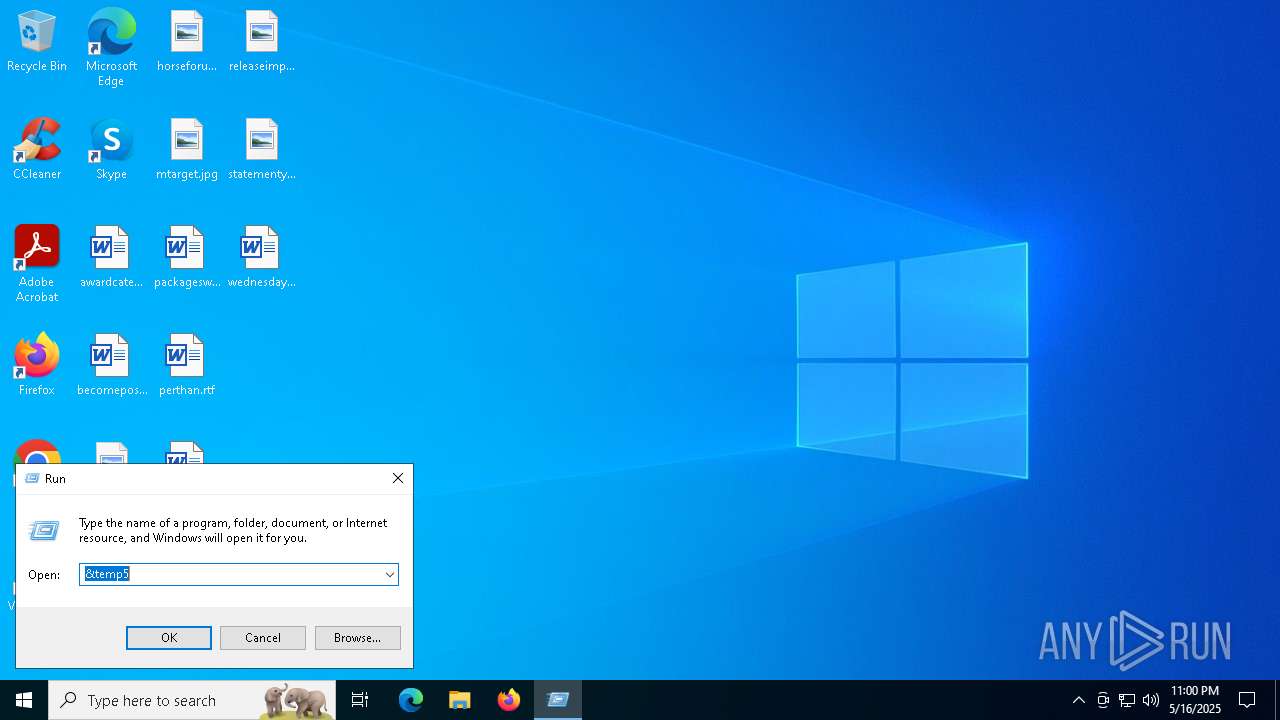
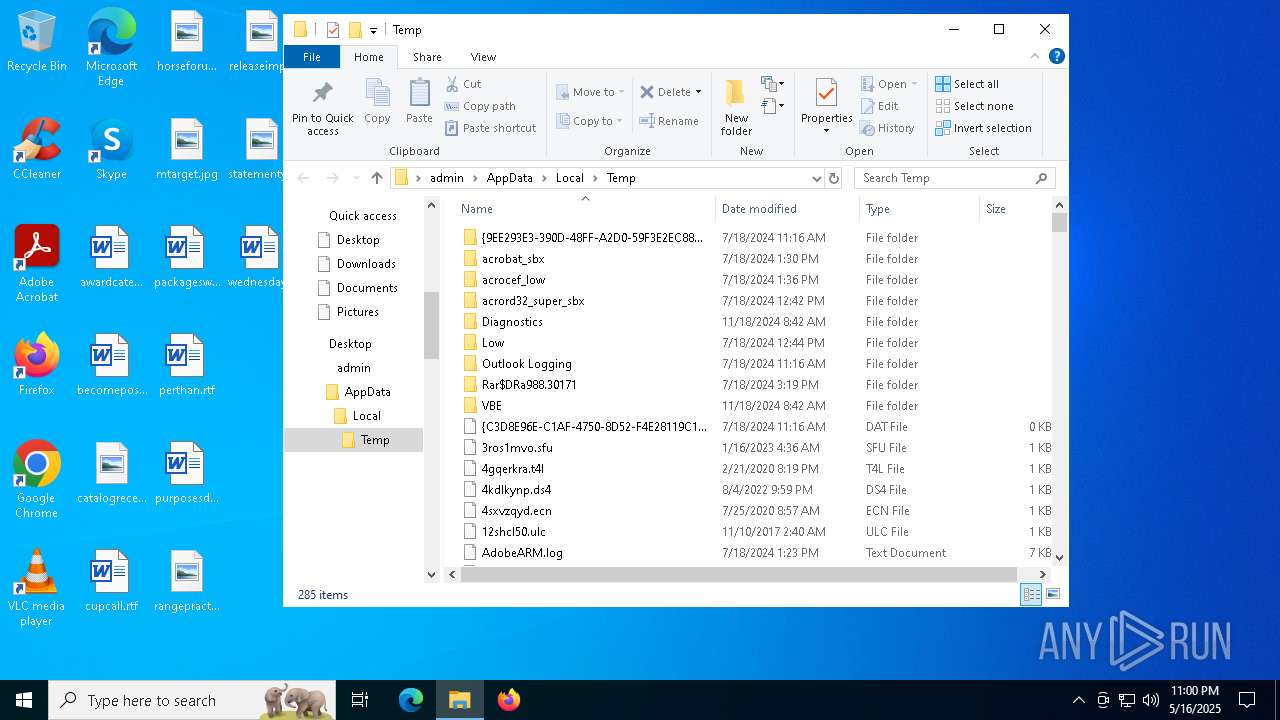
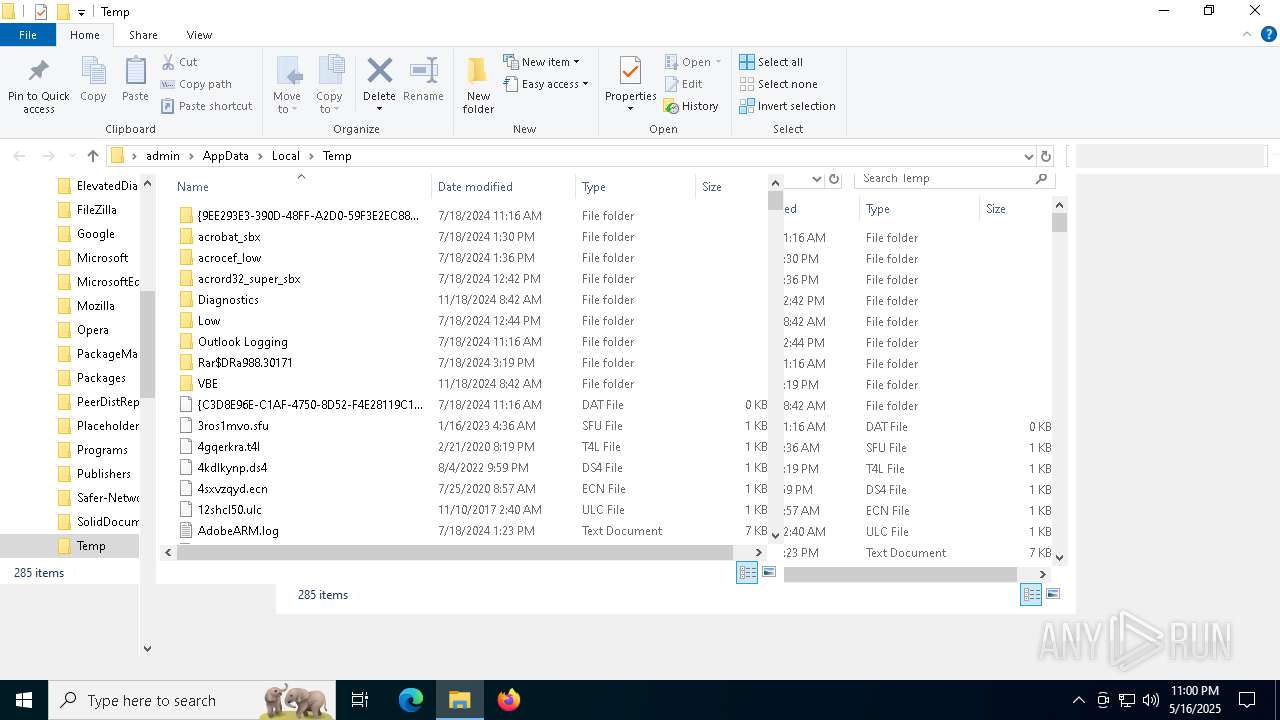
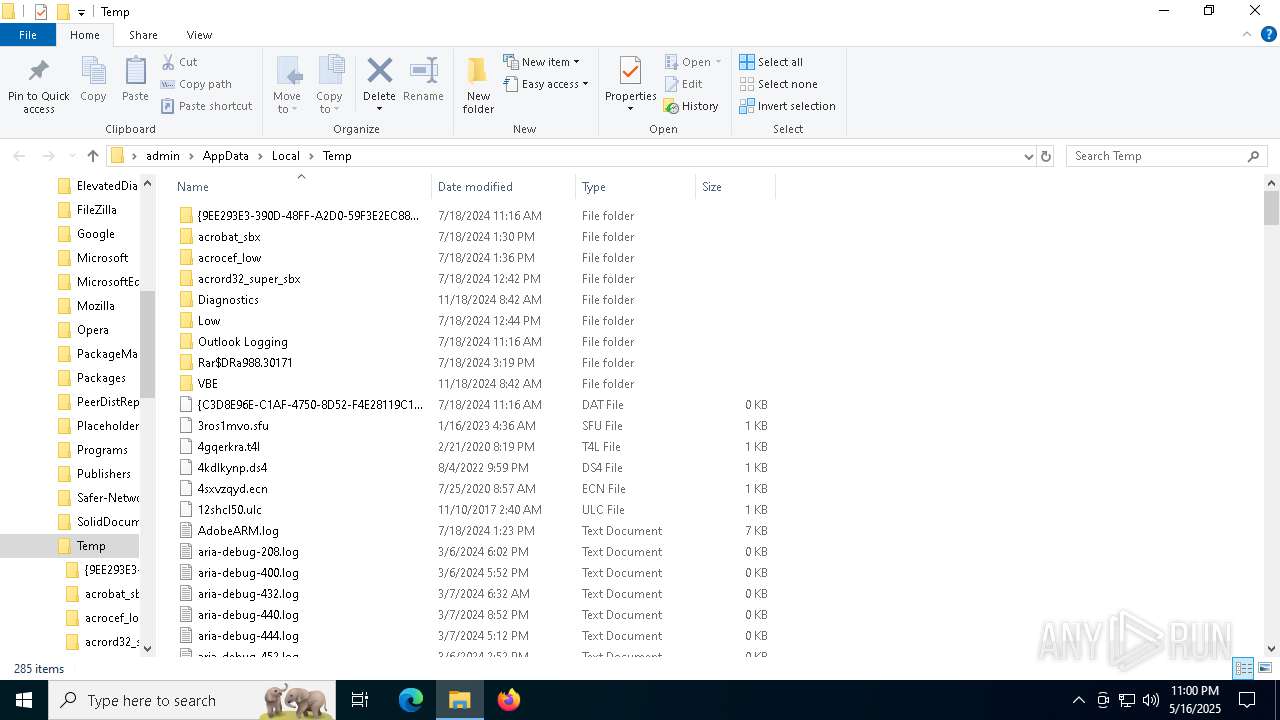
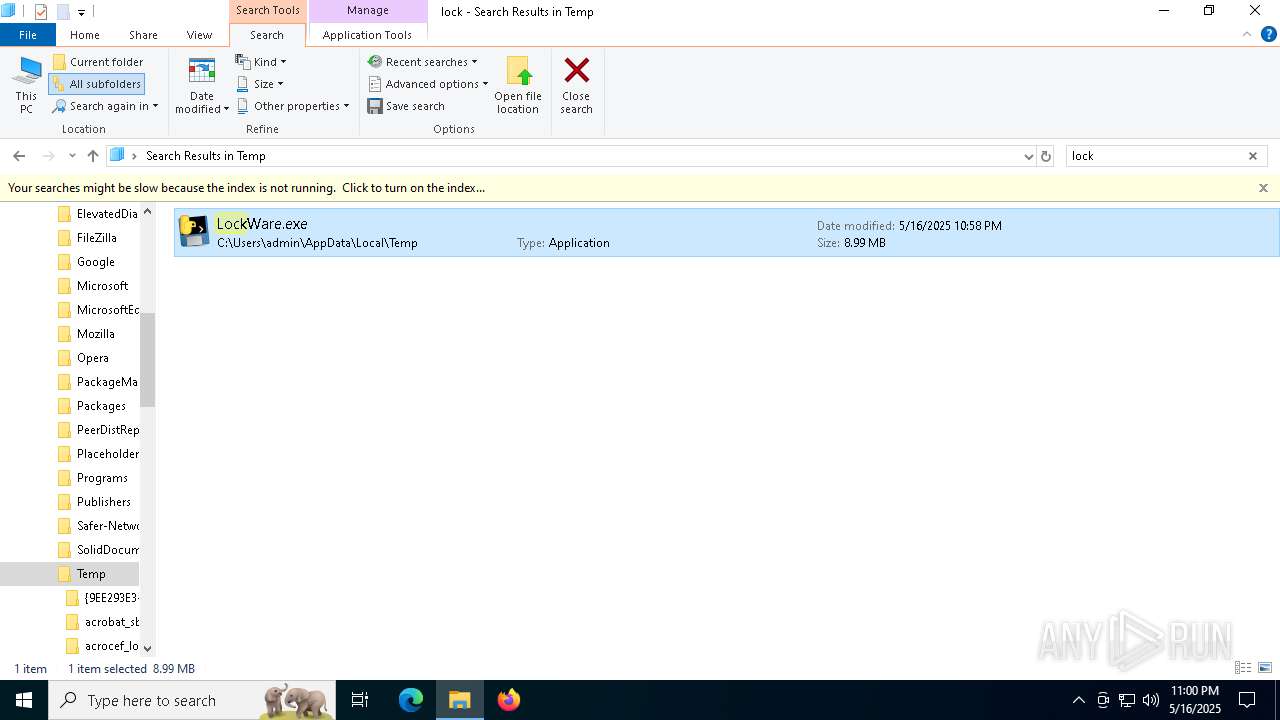
Create files in a temporary directory
- LockWare.exe (PID: 1672)
- LockWare.exe (PID: 5740)
- LockWare.exe (PID: 3124)
- LockWare.exe (PID: 4012)
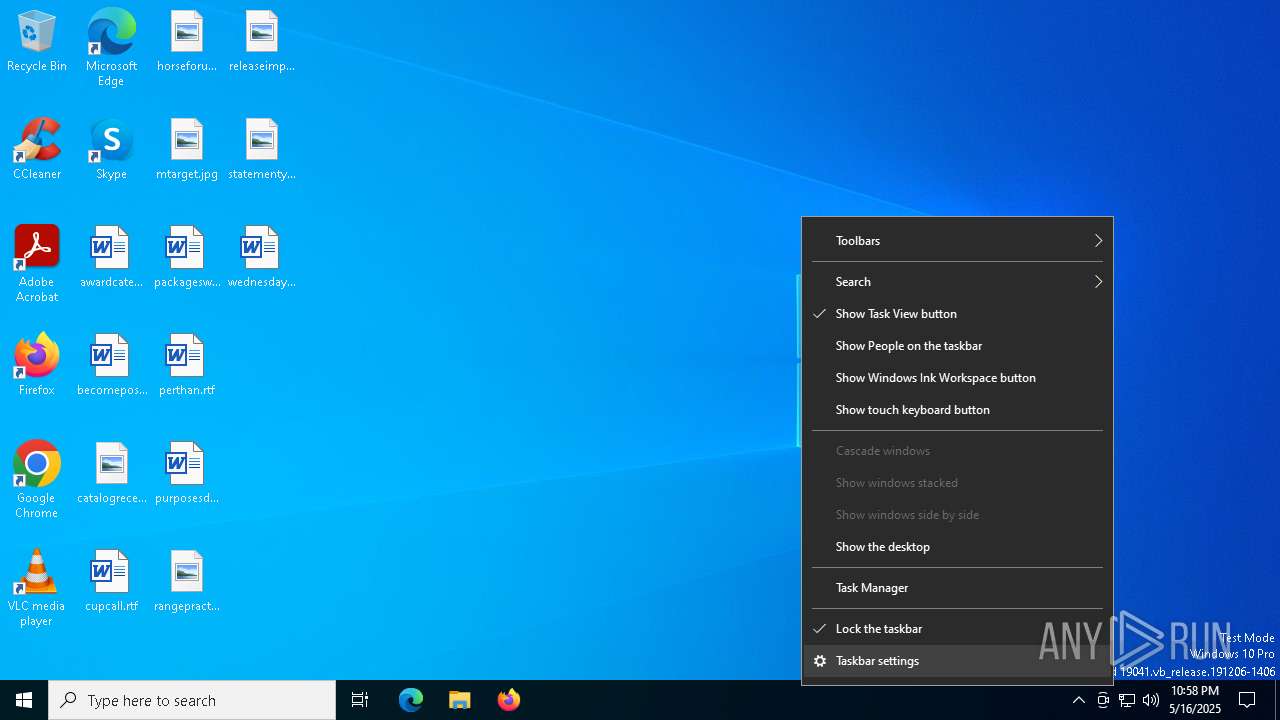
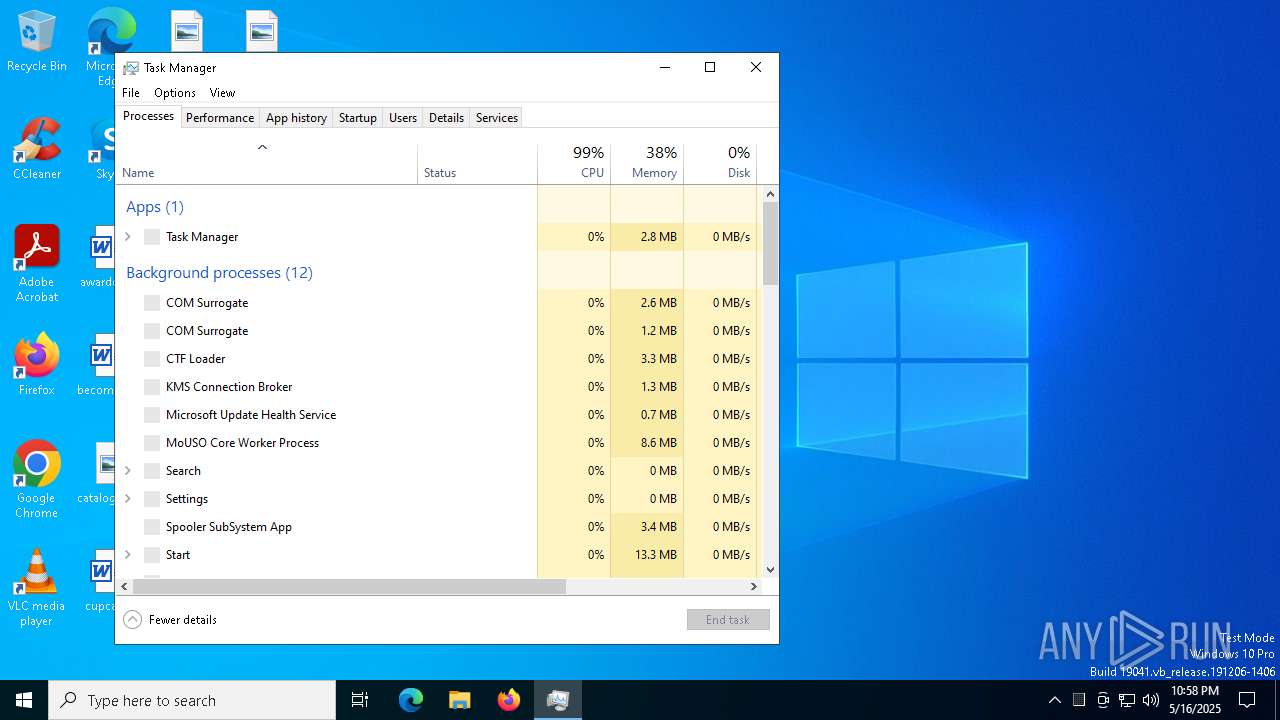
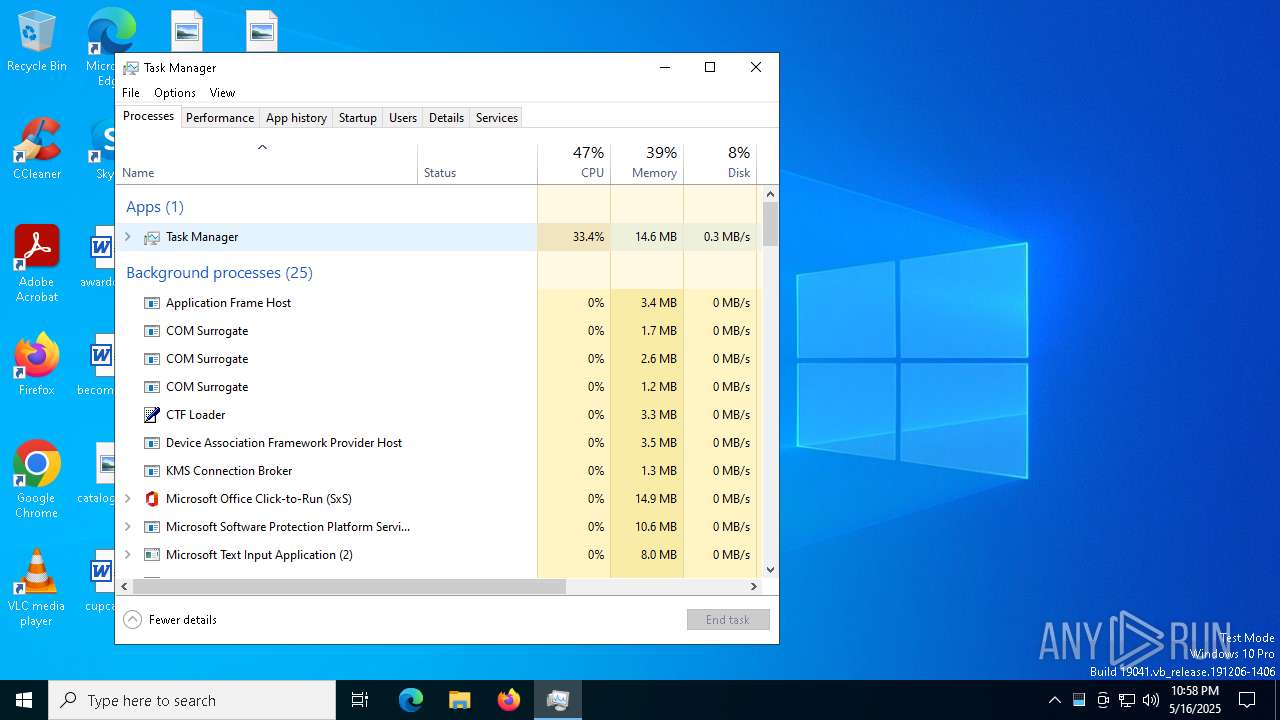
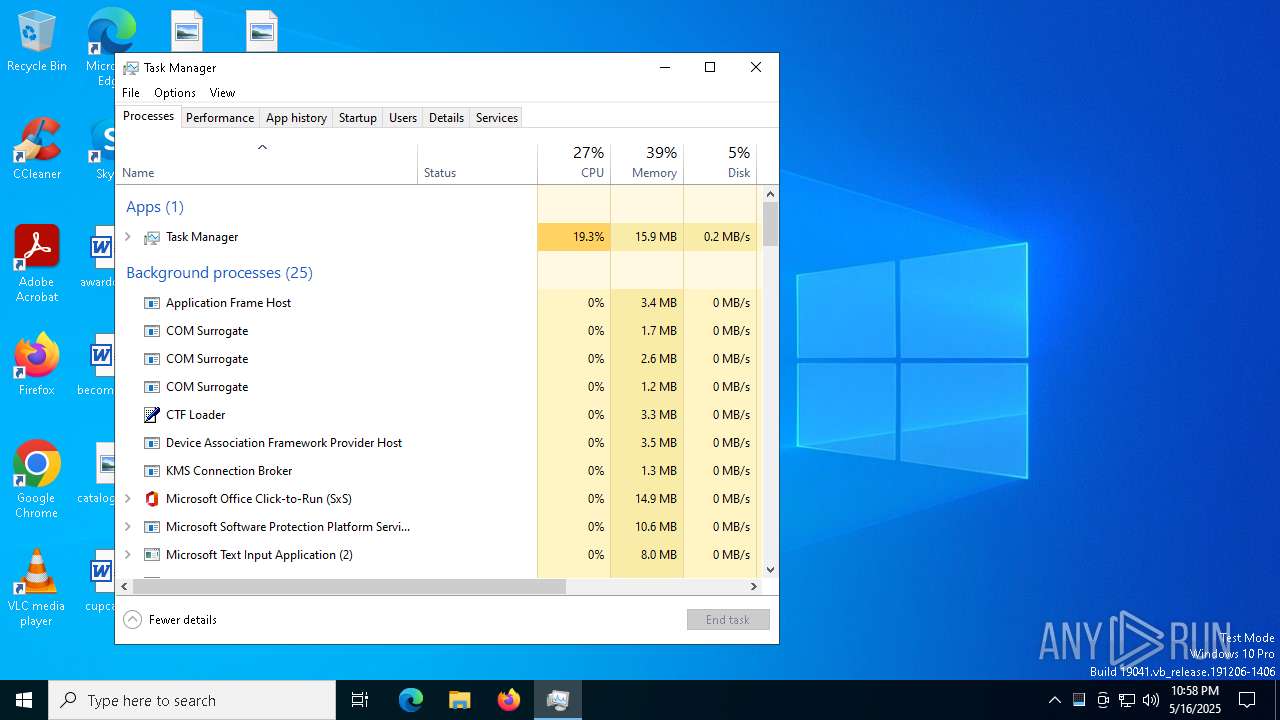
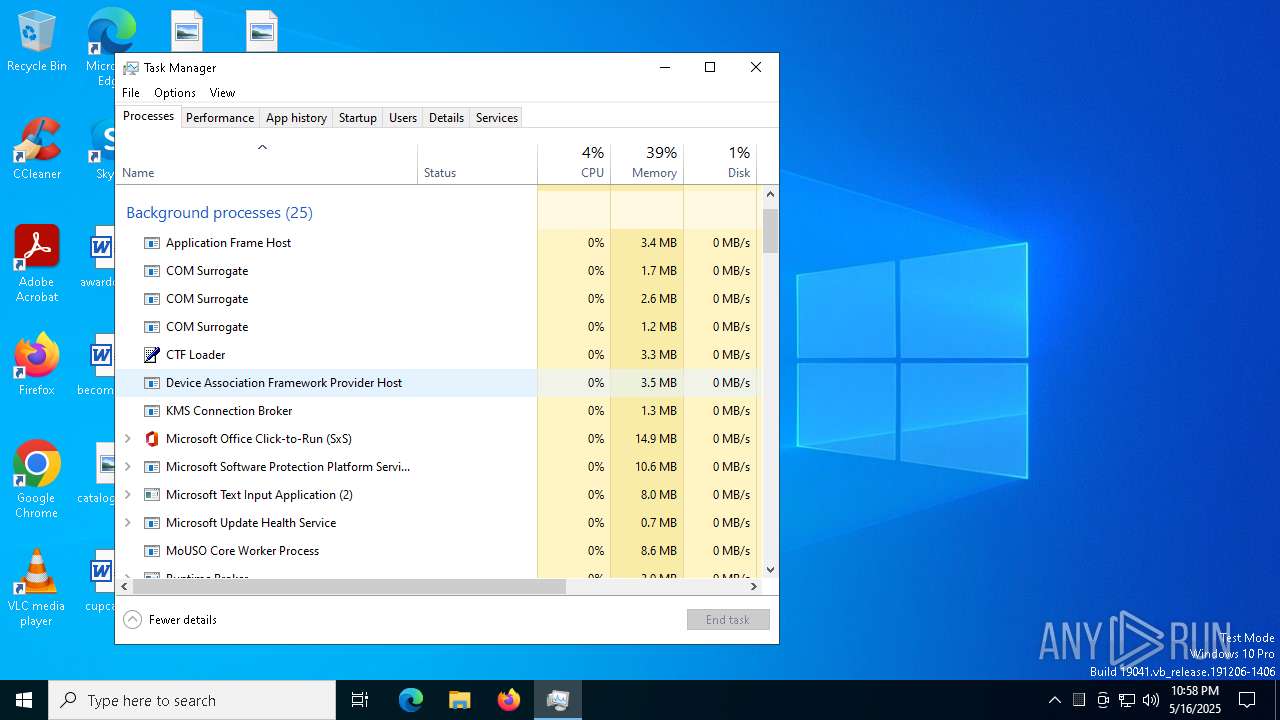
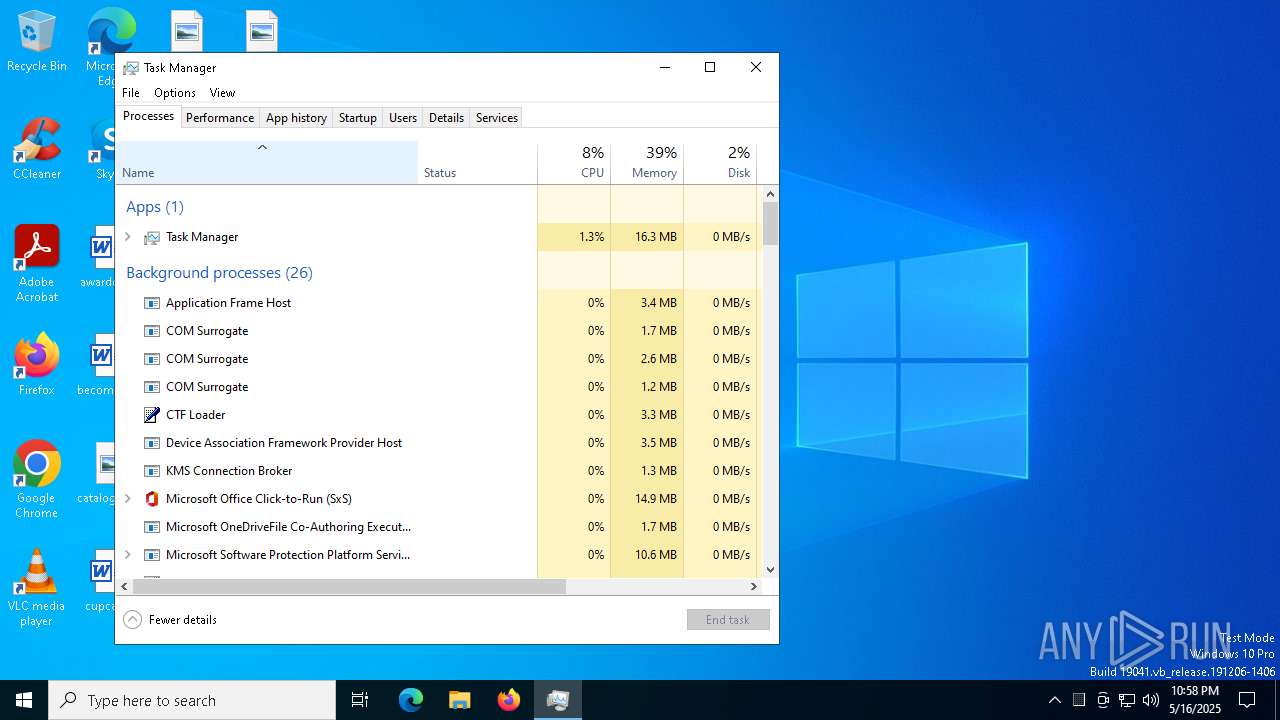
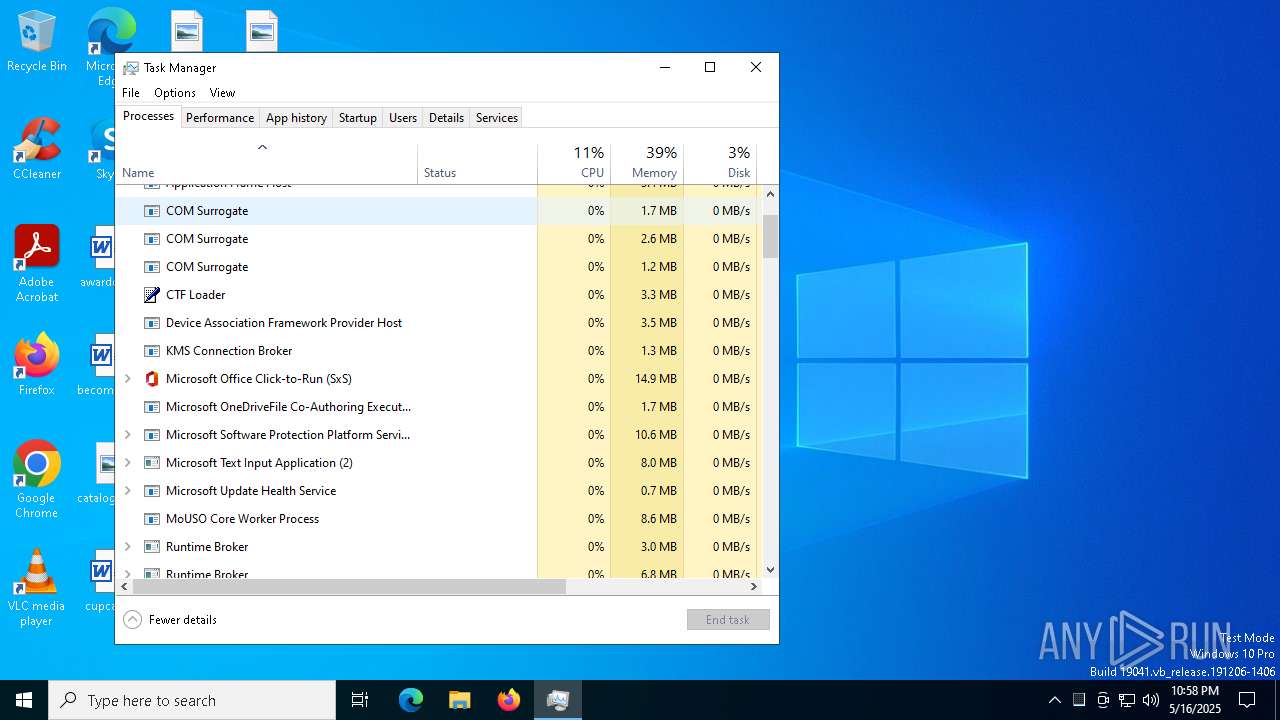
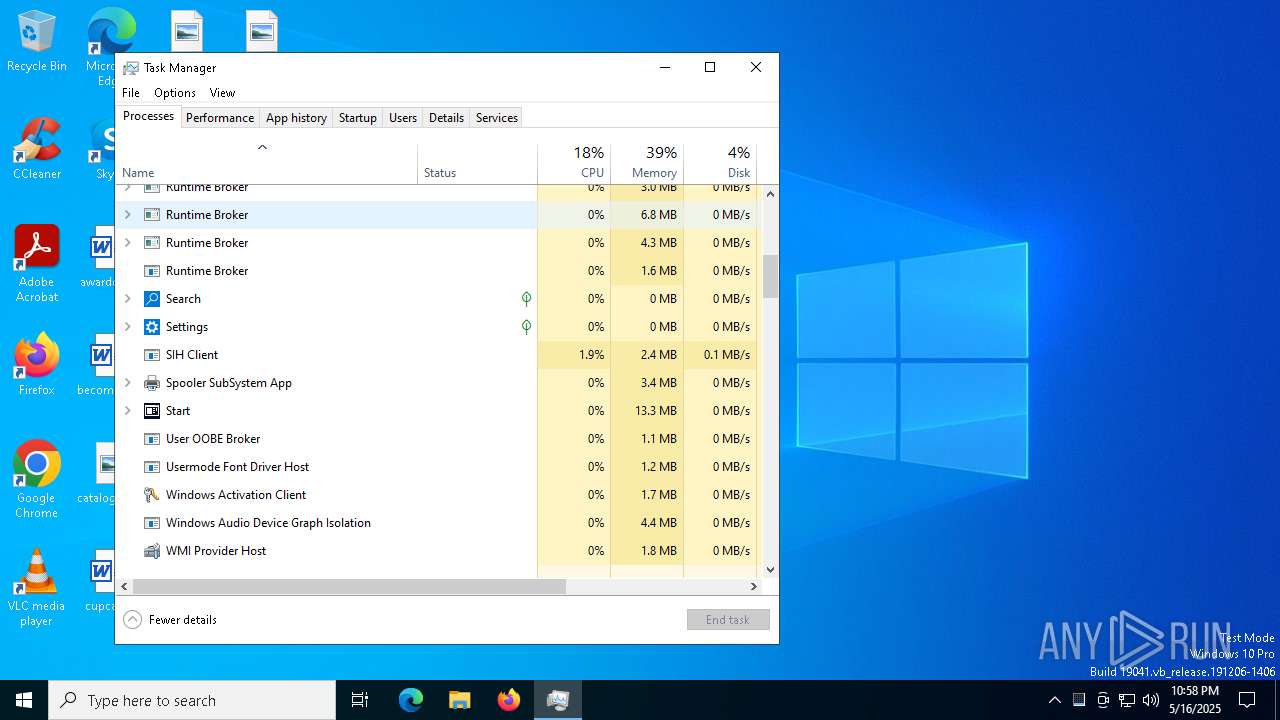
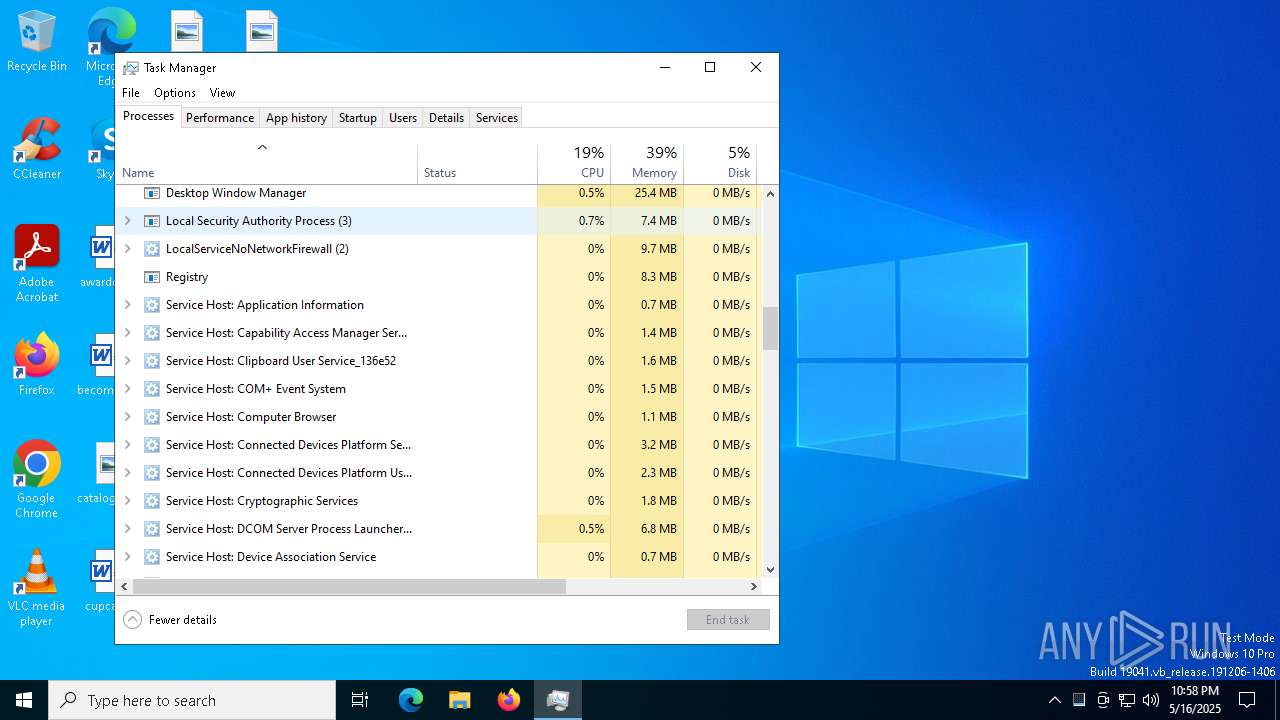
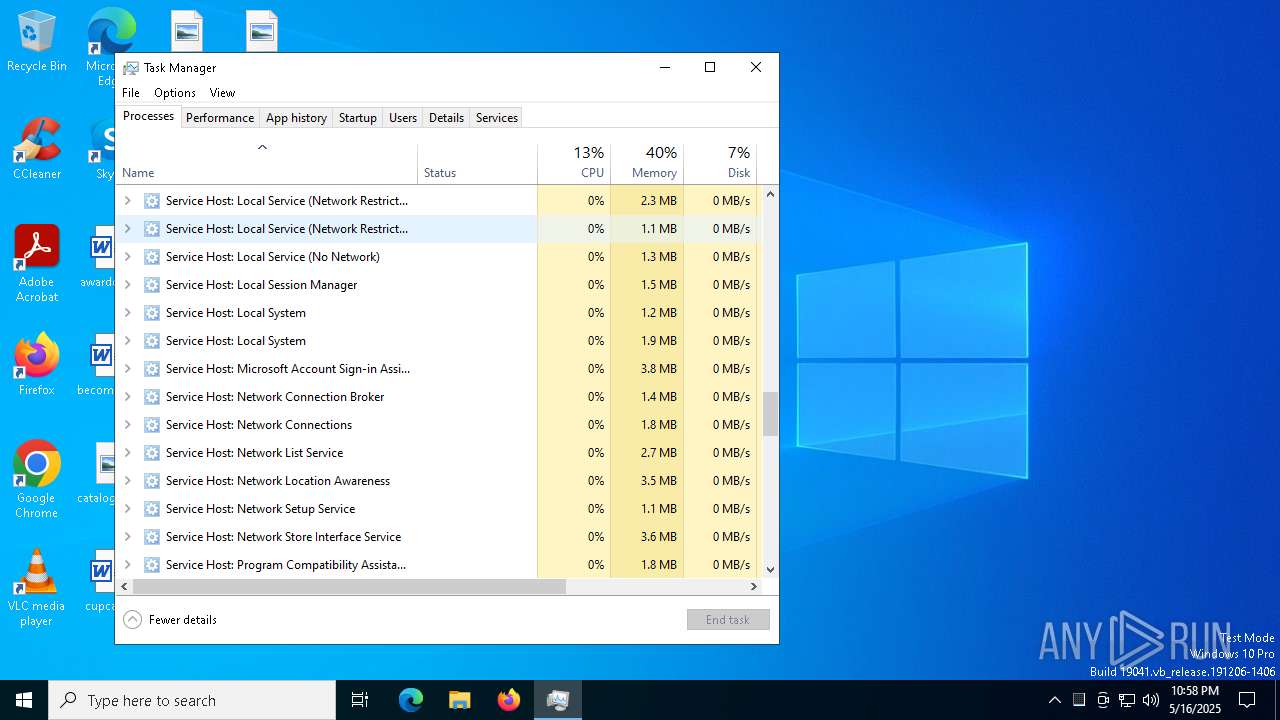
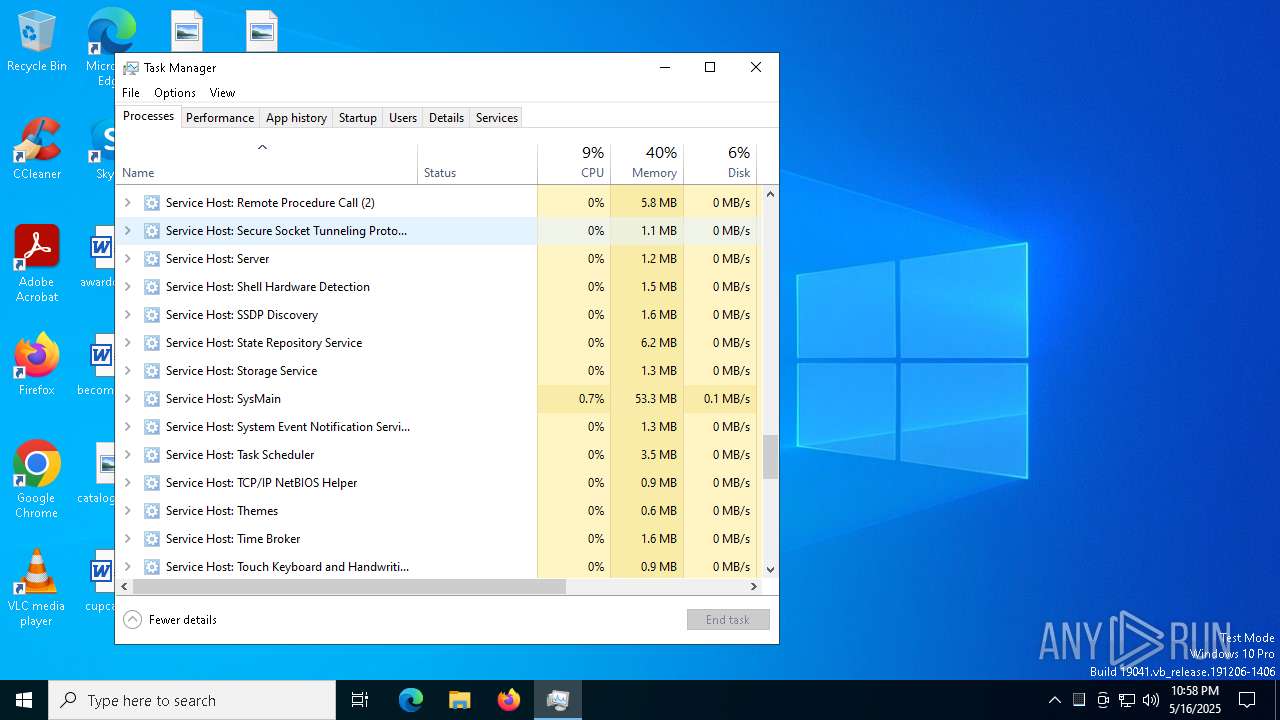
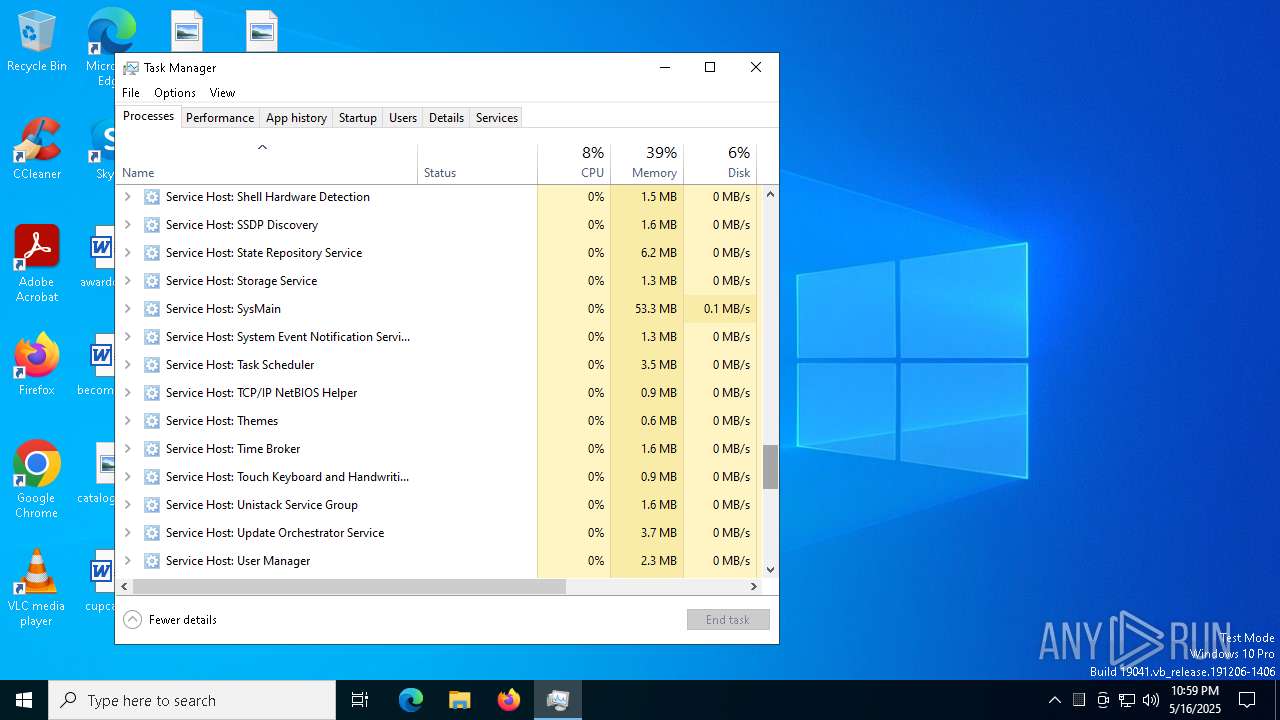
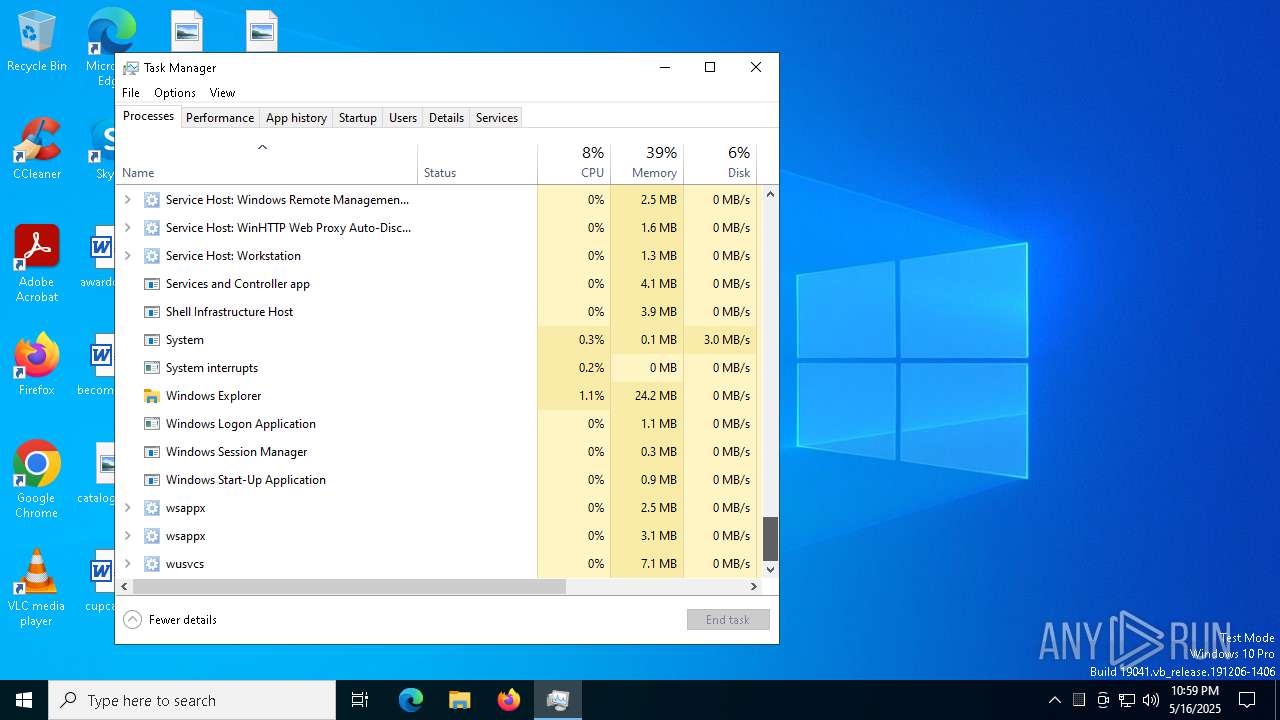
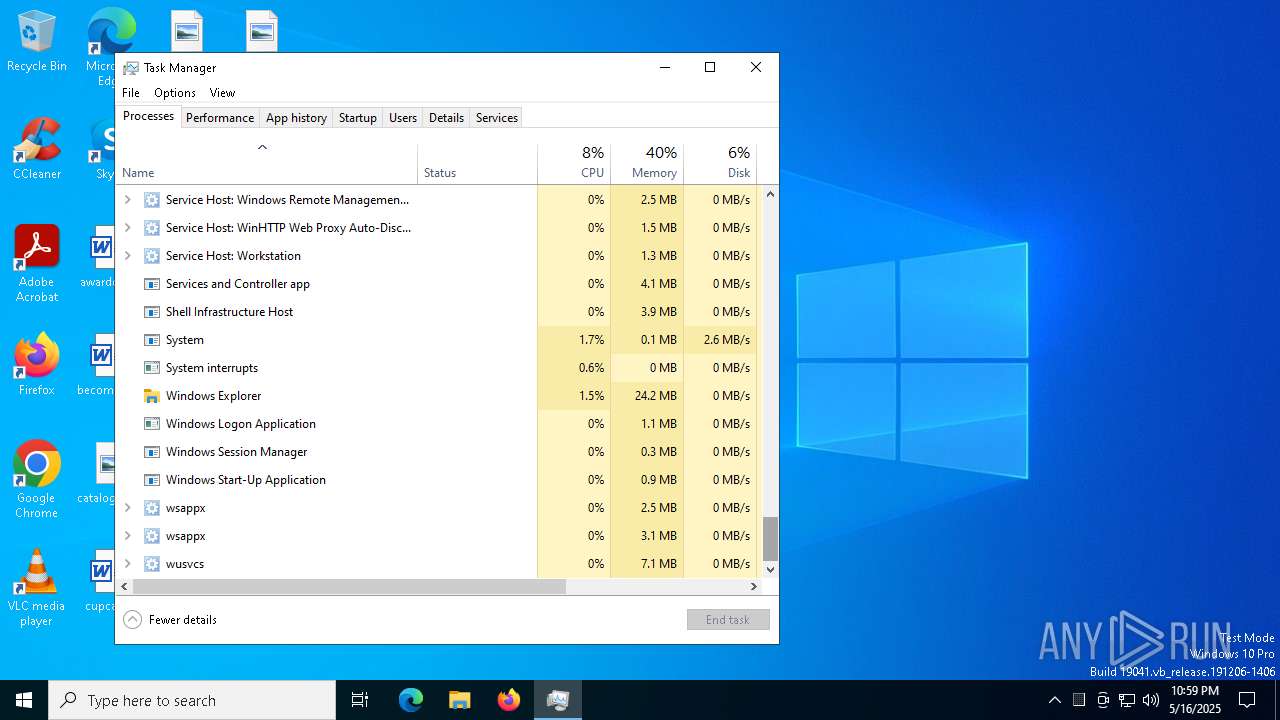
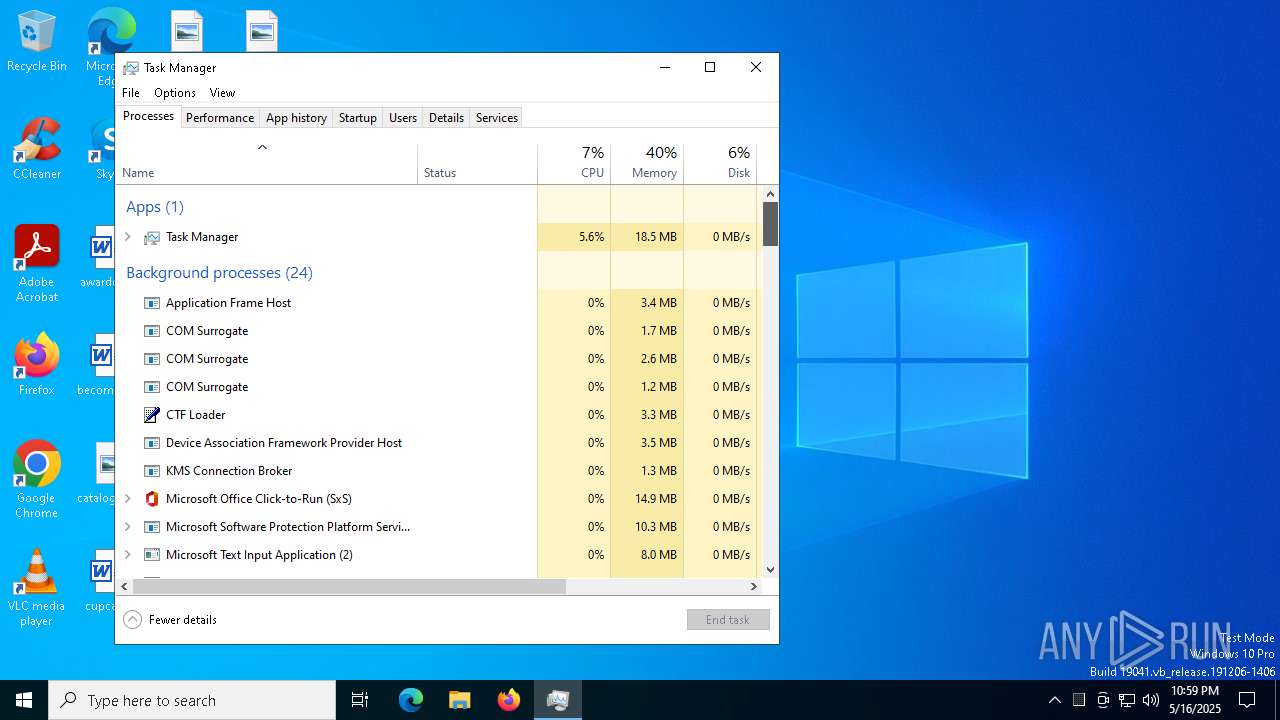
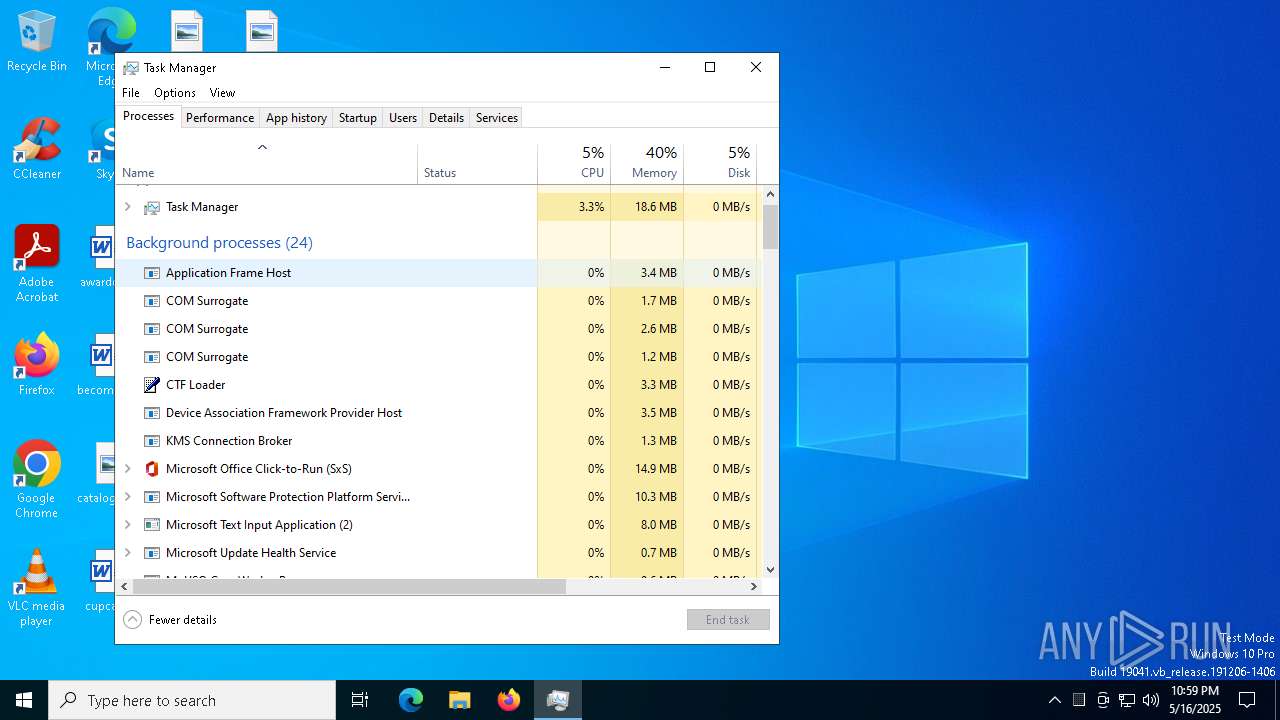
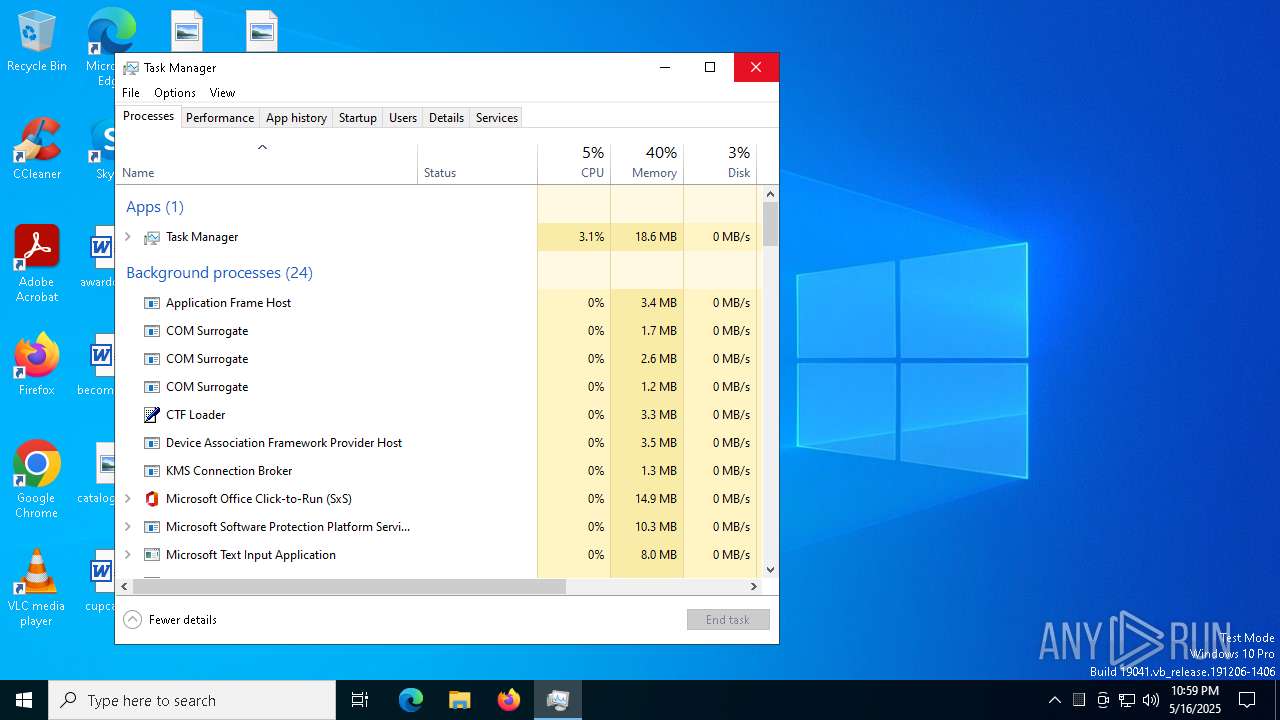
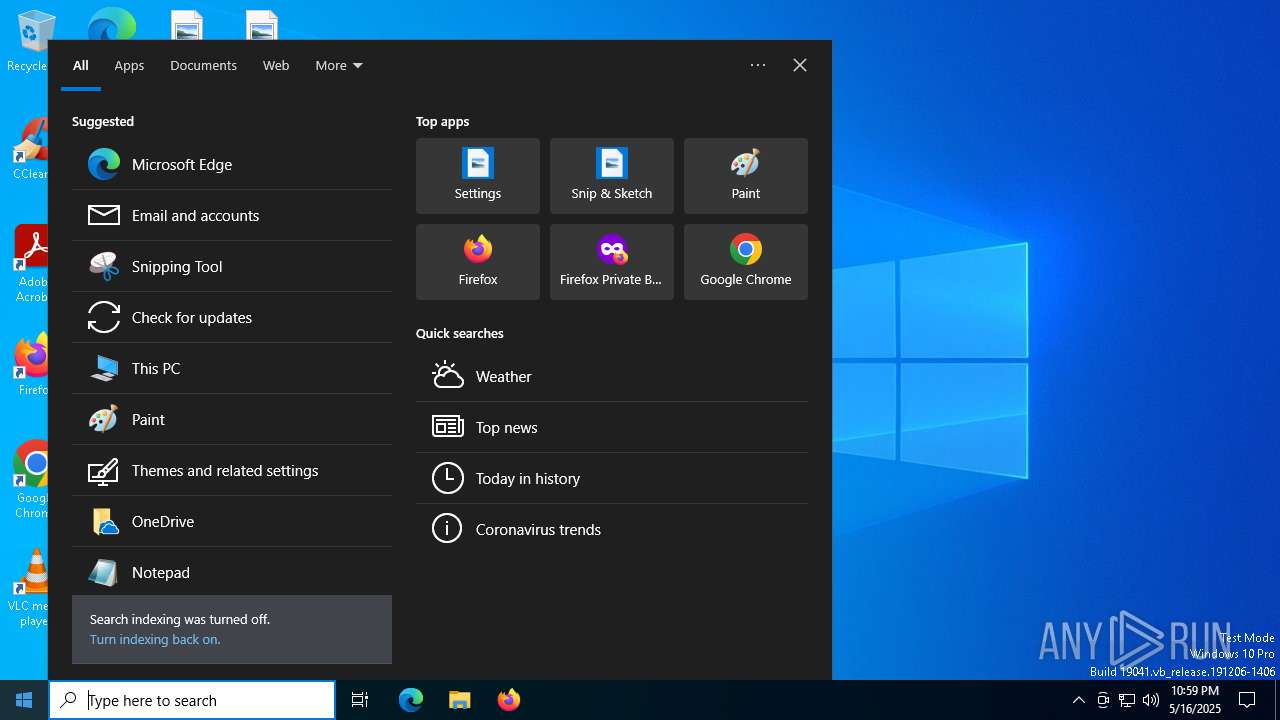
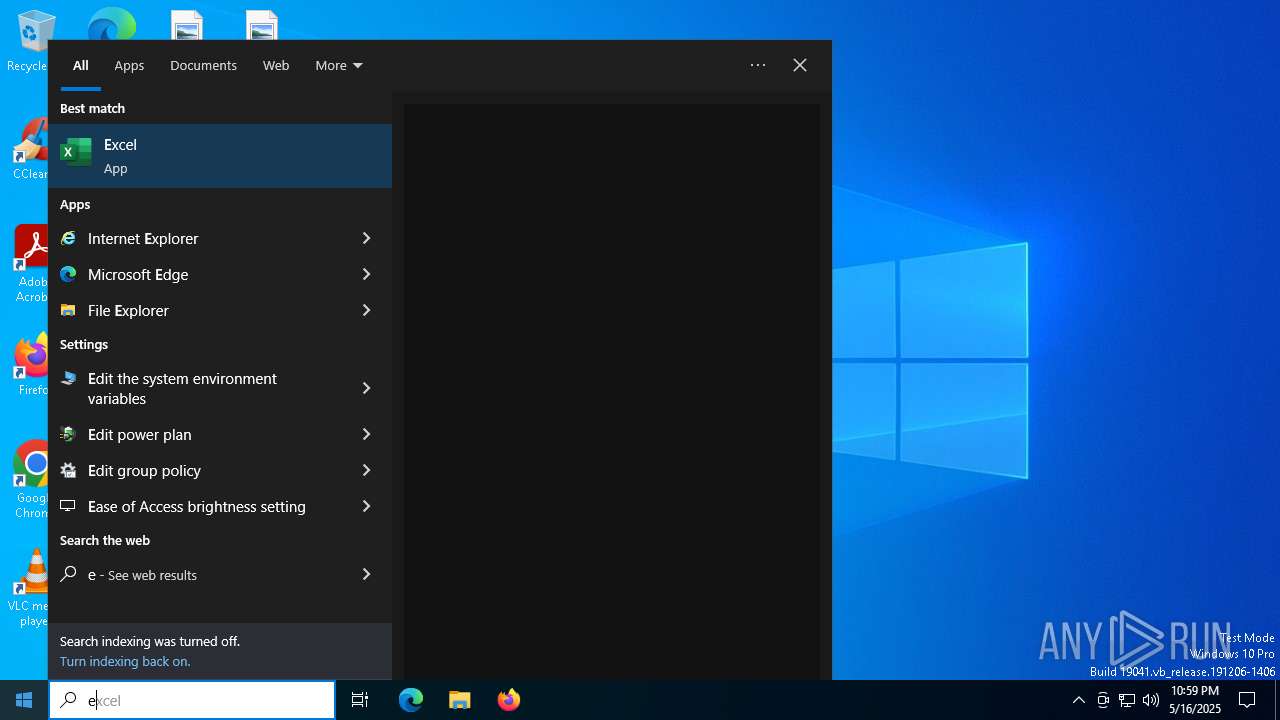
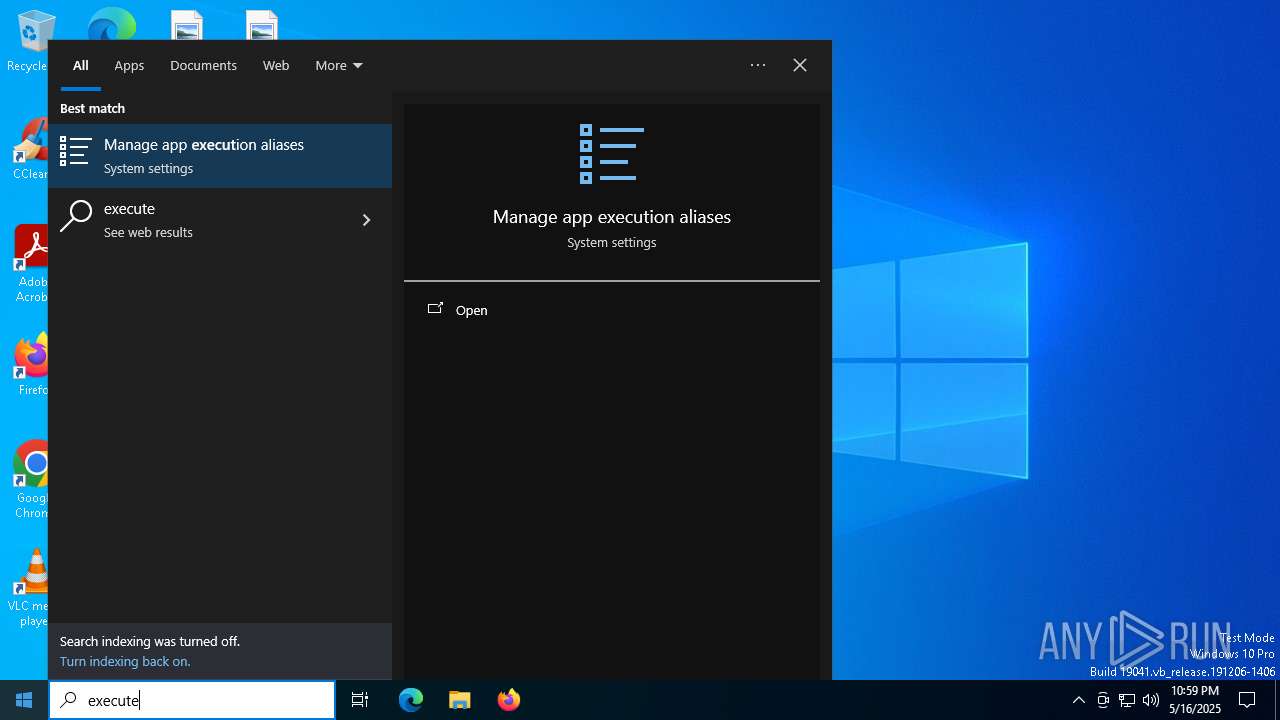
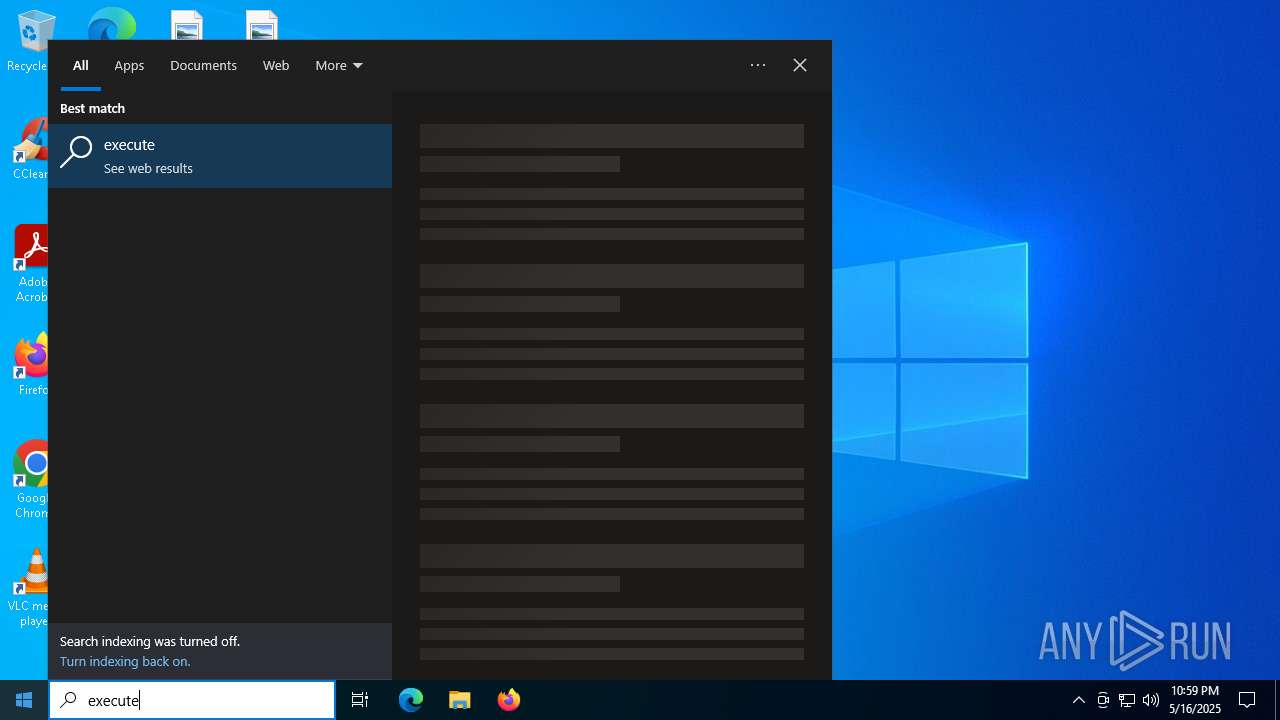
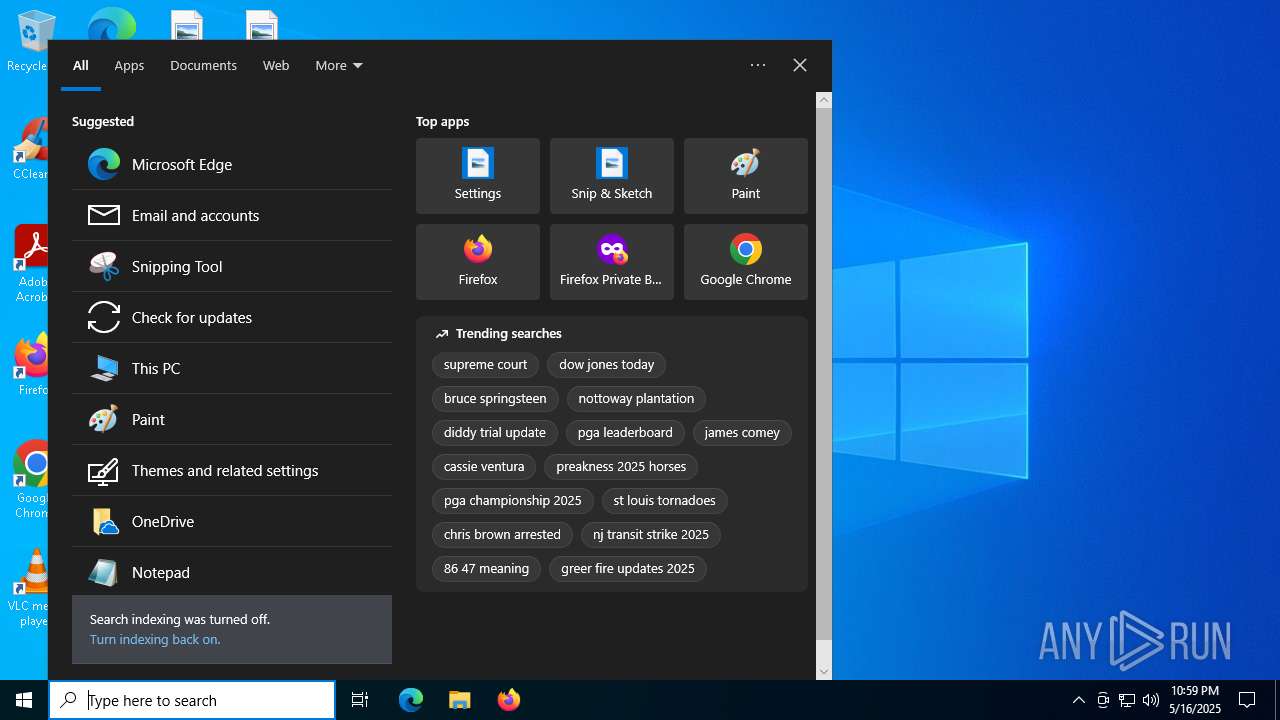
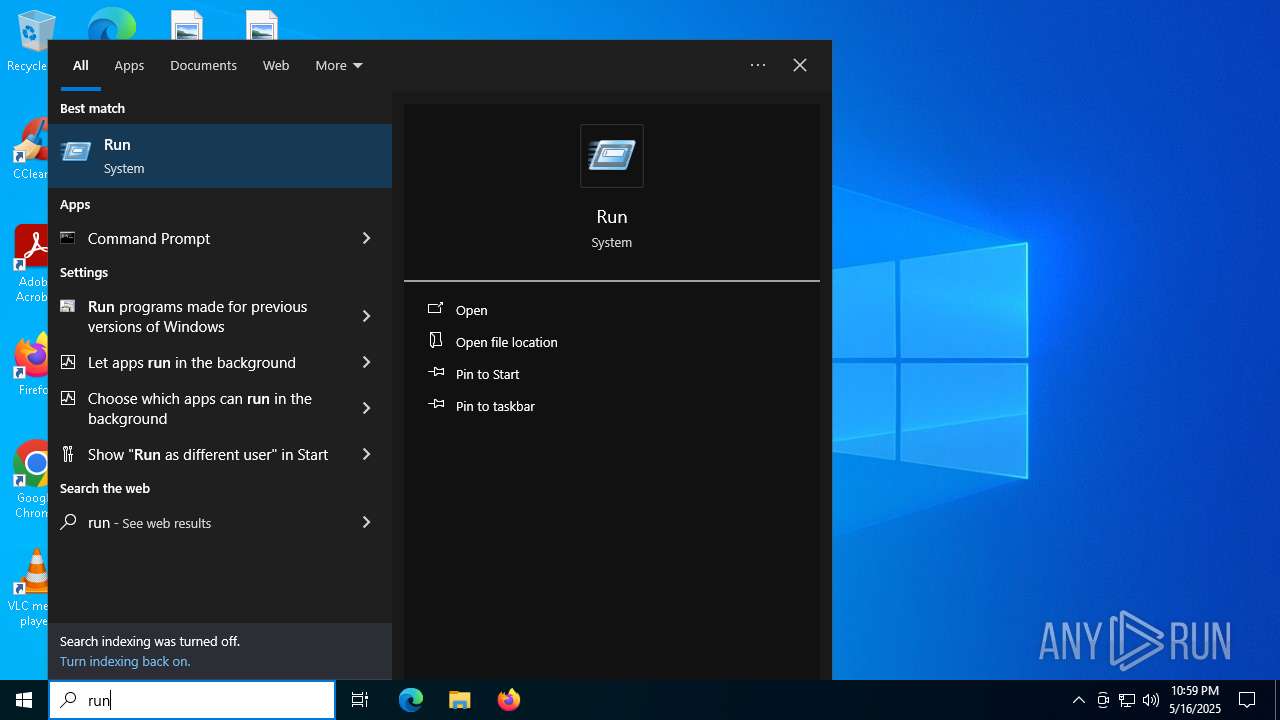
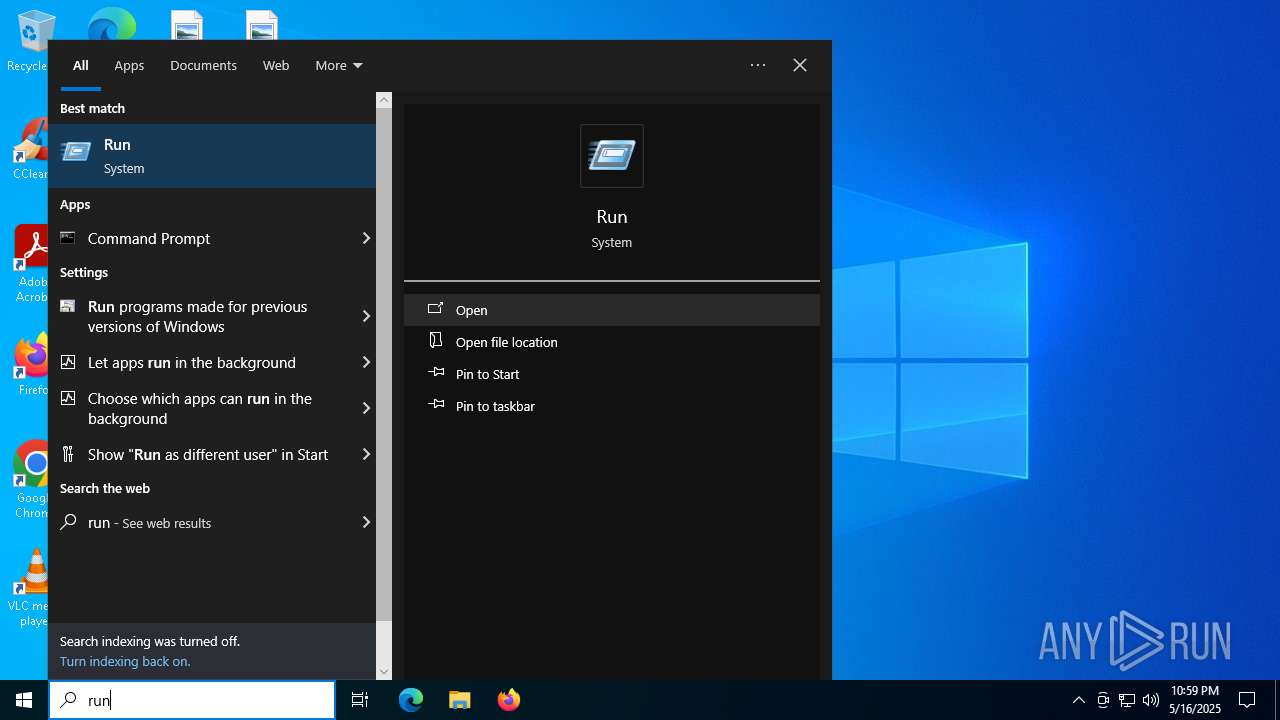
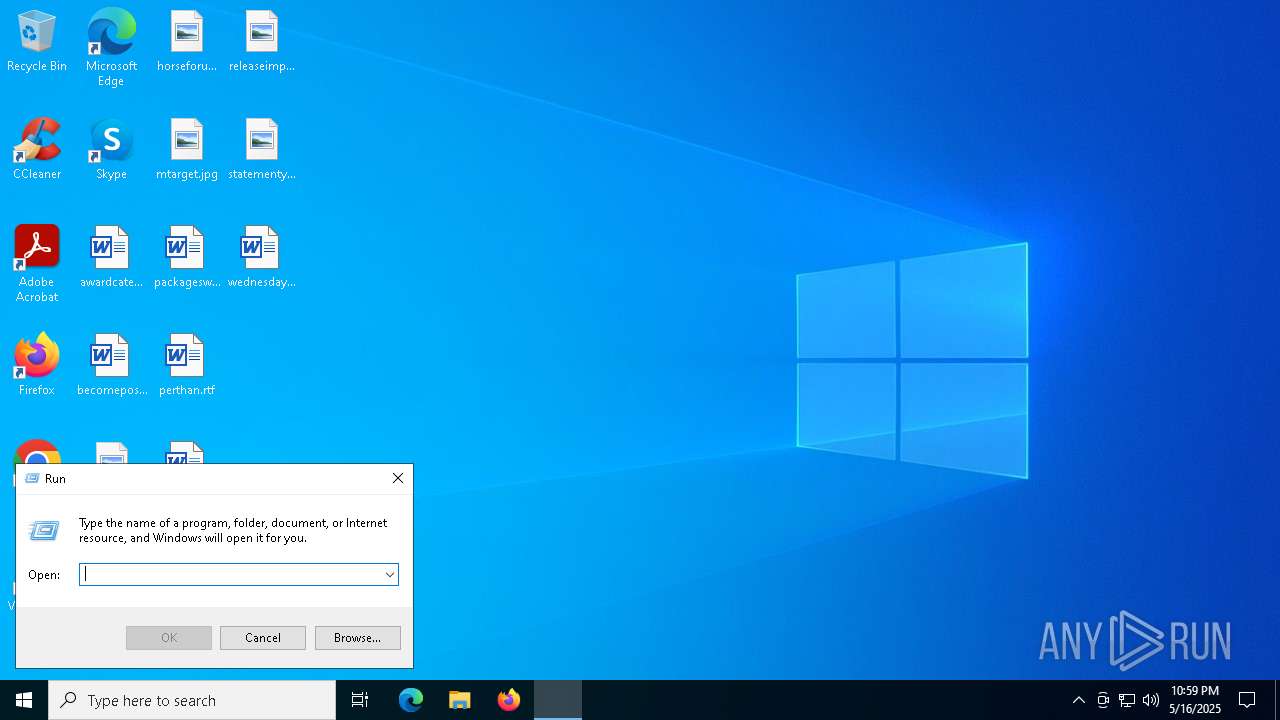
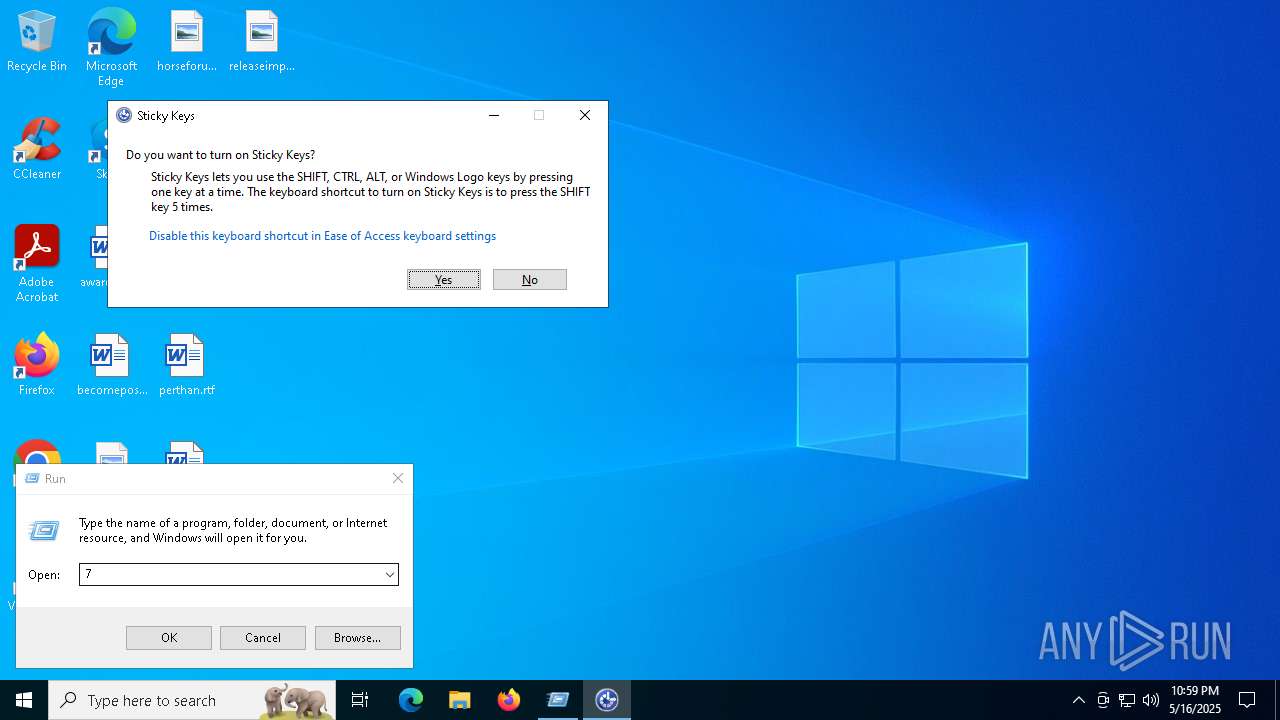
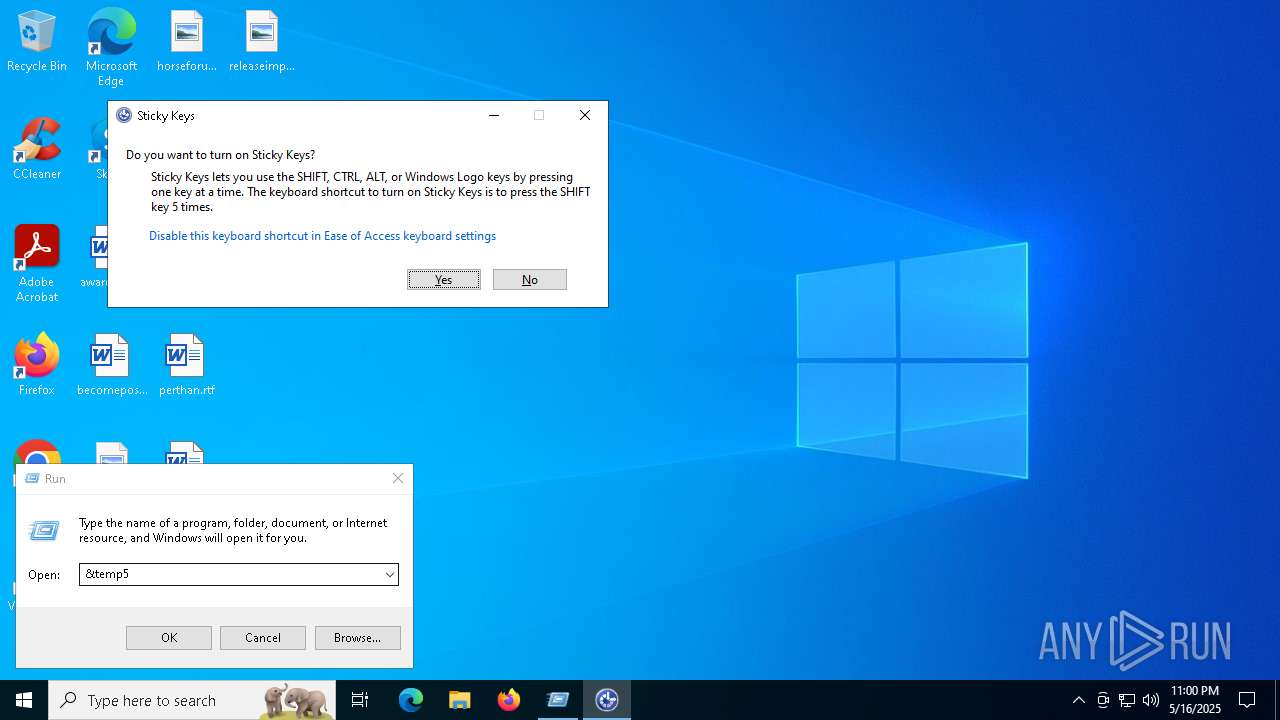
Manual execution by a user
- Taskmgr.exe (PID: 2244)
- Taskmgr.exe (PID: 5024)
- LockWare.exe (PID: 5740)
- LockWare.exe (PID: 3124)
- LockWare.exe (PID: 4012)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 5024)
Reads the software policy settings
- slui.exe (PID: 5212)
Checks proxy server information
- slui.exe (PID: 5212)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:05:16 22:57:49+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.42 |
| CodeSize: | 178688 |
| InitializedDataSize: | 153600 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc380 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
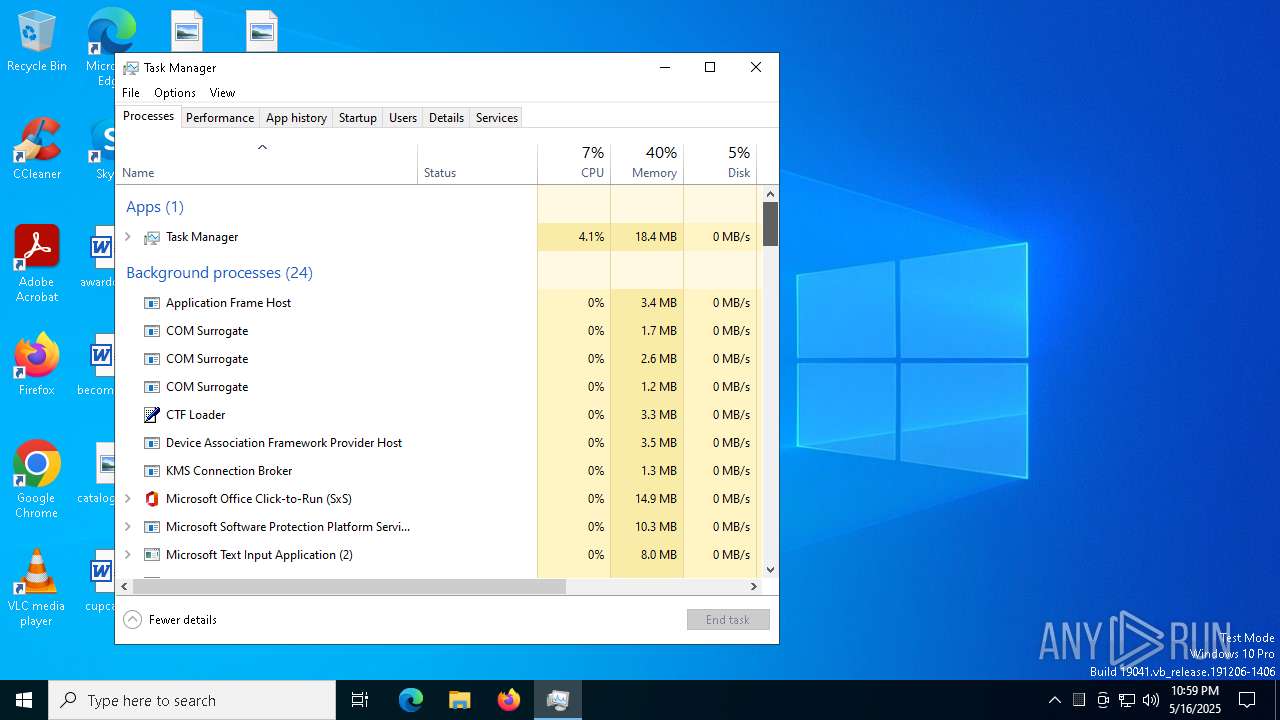
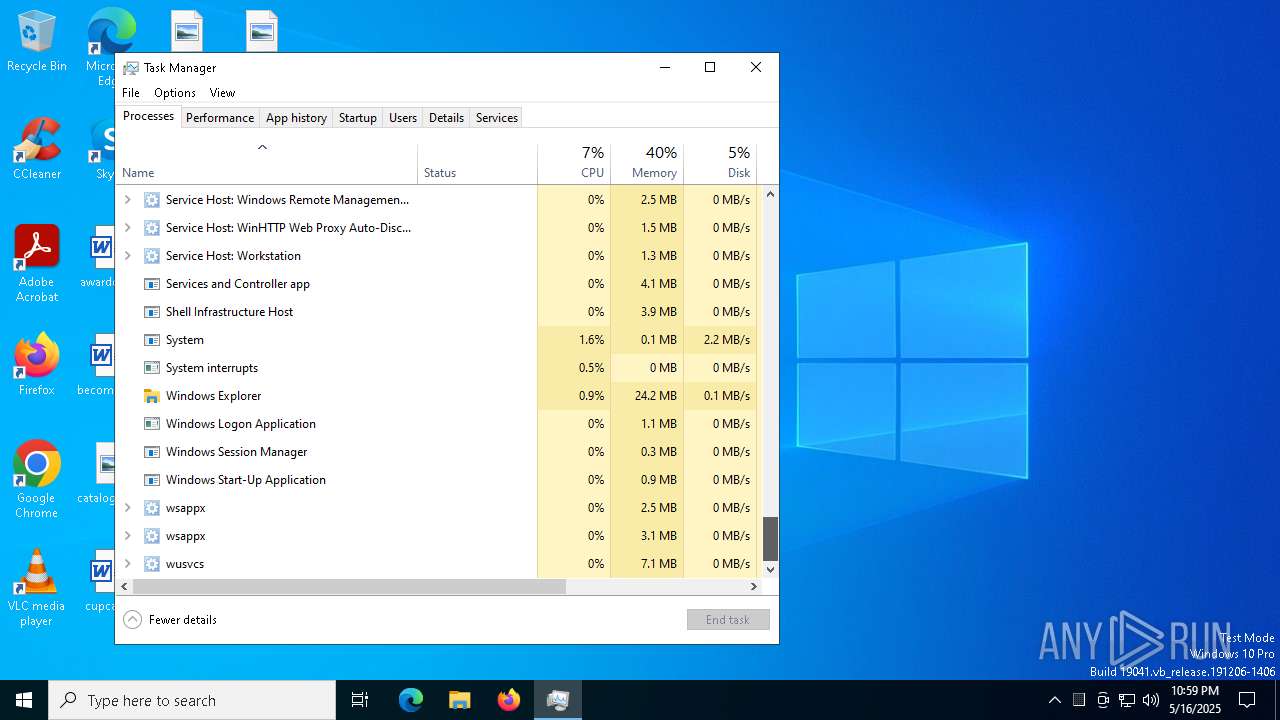
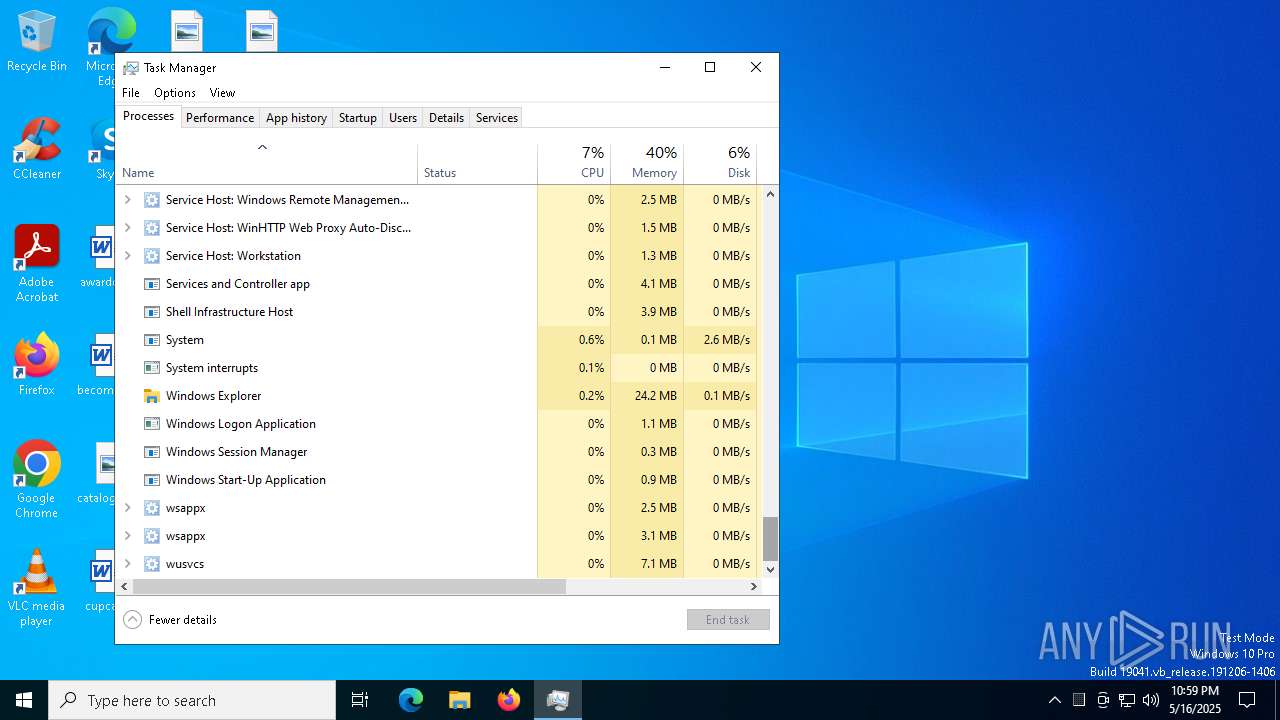
Total processes
156
Monitored processes
16
Malicious processes
4
Suspicious processes
0
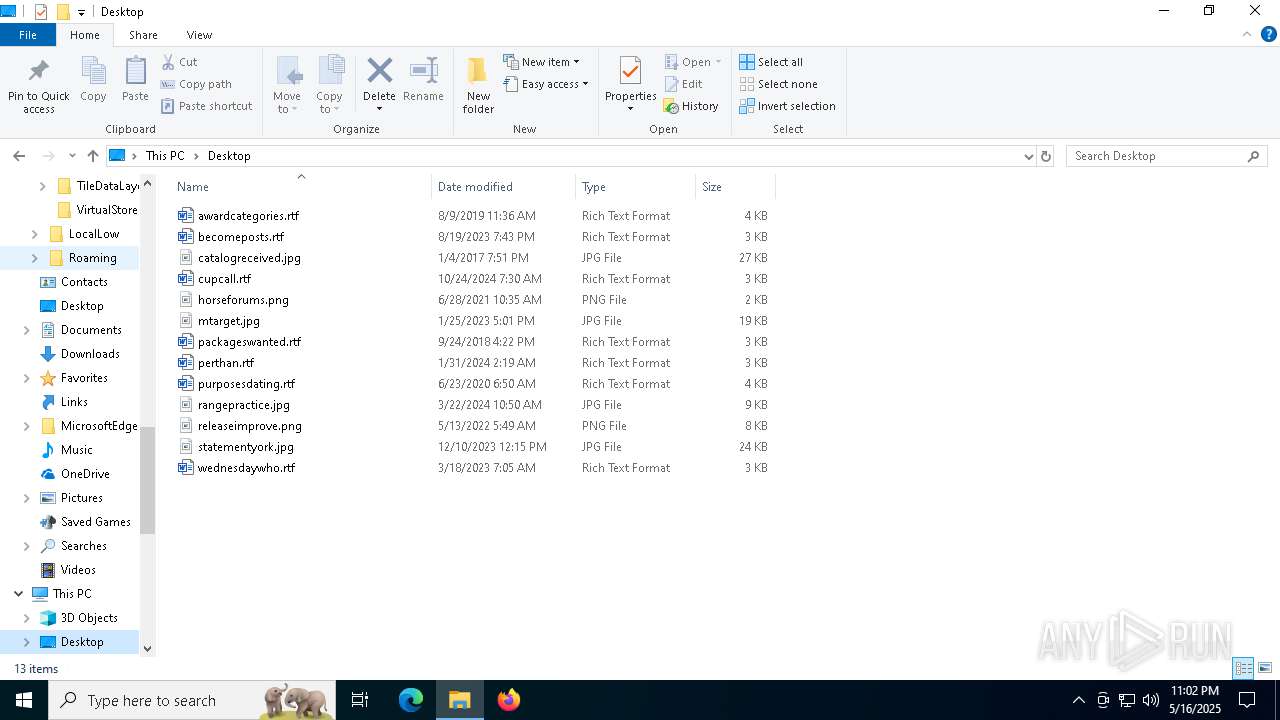
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1568 | "C:\Users\admin\AppData\Local\Temp\LockWare.exe" | C:\Users\admin\AppData\Local\Temp\LockWare.exe | — | LockWare.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1672 | "C:\Users\admin\AppData\Local\Temp\LockWare.exe" | C:\Users\admin\AppData\Local\Temp\LockWare.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2236 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2244 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Manager Exit code: 3221226540 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2780 | "C:\Users\admin\AppData\Local\Temp\LockWare.exe" | C:\Users\admin\AppData\Local\Temp\LockWare.exe | — | LockWare.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2852 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | LockWare.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3124 | "C:\Users\admin\AppData\Local\Temp\LockWare.exe" | C:\Users\admin\AppData\Local\Temp\LockWare.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3176 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | LockWare.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4012 | "C:\Users\admin\AppData\Local\Temp\LockWare.exe" | C:\Users\admin\AppData\Local\Temp\LockWare.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4620 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | LockWare.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 433
Read events
2 430
Write events
2
Delete events
1
Modification events
| (PID) Process: | (5024) Taskmgr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\TaskManager |
| Operation: | delete value | Name: | Preferences |
Value: | |||
| (PID) Process: | (5024) Taskmgr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\TaskManager |
| Operation: | write | Name: | Preferences |
Value: 0D00000060000000600000006800000068000000E3010000DC010000000001000000008000000080D8010080DF010080000100016B00000034000000130300008C020000E80300000000000000000000000000000F000000010000000000000058AA043AF67F00000000000000000000000000002E0100001E0000008990000000000000FF00000001015002000000000D0000000000000098AA043AF67F00000000000000000000FFFFFFFF960000001E0000008B900000010000000000000000101001000000000300000000000000B0AA043AF67F00000000000000000000FFFFFFFF780000001E0000008C900000020000000000000001021200000000000400000000000000C8AA043AF67F00000000000000000000FFFFFFFF960000001E0000008D900000030000000000000000011001000000000200000000000000E8AA043AF67F00000000000000000000FFFFFFFF320000001E0000008A90000004000000000000000008200100000000050000000000000000AB043AF67F00000000000000000000FFFFFFFFC80000001E0000008E90000005000000000000000001100100000000060000000000000028AB043AF67F00000000000000000000FFFFFFFF040100001E0000008F90000006000000000000000001100100000000070000000000000050AB043AF67F00000000000000000000FFFFFFFF49000000490000009090000007000000000000000004250000000000080000000000000080AA043AF67F00000000000000000000FFFFFFFF49000000490000009190000008000000000000000004250000000000090000000000000070AB043AF67F00000000000000000000FFFFFFFF490000004900000092900000090000000000000000042508000000000A0000000000000088AB043AF67F00000000000000000000FFFFFFFF4900000049000000939000000A0000000000000000042508000000000B00000000000000A8AB043AF67F00000000000000000000FFFFFFFF490000004900000039A000000B0000000000000000042509000000001C00000000000000C8AB043AF67F00000000000000000000FFFFFFFFC8000000490000003AA000000C0000000000000000011009000000001D00000000000000F0AB043AF67F00000000000000000000FFFFFFFF64000000490000004CA000000D0000000000000000021508000000001E0000000000000010AC043AF67F00000000000000000000FFFFFFFF64000000490000004DA000000E000000000000000002150800000000030000000A000000010000000000000058AA043AF67F0000000000000000000000000000D70000001E0000008990000000000000FF00000001015002000000000400000000000000C8AA043AF67F0000000000000000000001000000960000001E0000008D900000010000000000000001011000000000000300000000000000B0AA043AF67F00000000000000000000FFFFFFFF640000001E0000008C900000020000000000000000021000000000000C0000000000000040AC043AF67F0000000000000000000003000000640000001E00000094900000030000000000000001021000000000000D0000000000000068AC043AF67F00000000000000000000FFFFFFFF640000001E00000095900000040000000000000000011001000000000E0000000000000090AC043AF67F0000000000000000000005000000320000001E00000096900000050000000000000001042001000000000F00000000000000B8AC043AF67F0000000000000000000006000000320000001E00000097900000060000000000000001042001000000001000000000000000D8AC043AF67F0000000000000000000007000000460000001E00000098900000070000000000000001011001000000001100000000000000F8AC043AF67F00000000000000000000FFFFFFFF640000001E0000009990000008000000000000000001100100000000060000000000000028AB043AF67F0000000000000000000009000000040100001E0000008F9000000900000000000000010110010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000040000000B000000010000000000000058AA043AF67F0000000000000000000000000000D70000001E0000009E90000000000000FF0000000101500200000000120000000000000020AD043AF67F00000000000000000000FFFFFFFF2D0000001E0000009B90000001000000000000000004200100000000140000000000000040AD043AF67F00000000000000000000FFFFFFFF640000001E0000009D90000002000000000000000001100100000000130000000000000068AD043AF67F00000000000000000000FFFFFFFF640000001E0000009C900000030000000000000000011001000000000300000000000000B0AA043AF67F00000000000000000000FFFFFFFF640000001E0000008C90000004000000000000000102100000000000070000000000000050AB043AF67F000000000000000000000500000049000000490000009090000005000000000000000104210000000000080000000000000080AA043AF67F000000000000000000000600000049000000490000009190000006000000000000000104210000000000090000000000000070AB043AF67F0000000000000000000007000000490000004900000092900000070000000000000001042108000000000A0000000000000088AB043AF67F0000000000000000000008000000490000004900000093900000080000000000000001042108000000000B00000000000000A8AB043AF67F0000000000000000000009000000490000004900000039A00000090000000000000001042109000000001C00000000000000C8AB043AF67F000000000000000000000A00000064000000490000003AA000000A00000000000000000110090000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000200000008000000010000000000000058AA043AF67F0000000000000000000000000000C60000001E000000B090000000000000FF0000000101500200000000150000000000000088AD043AF67F00000000000000000000FFFFFFFF6B0000001E000000B1900000010000000000000000042500000000001600000000000000B8AD043AF67F00000000000000000000FFFFFFFF6B0000001E000000B2900000020000000000000000042500000000001800000000000000E0AD043AF67F00000000000000000000FFFFFFFF6B0000001E000000B490000003000000000000000004250000000000170000000000000008AE043AF67F00000000000000000000FFFFFFFF6B0000001E000000B390000004000000000000000004250000000000190000000000000040AE043AF67F00000000000000000000FFFFFFFFA00000001E000000B5900000050000000000000000042001000000001A0000000000000070AE043AF67F00000000000000000000FFFFFFFF7D0000001E000000B6900000060000000000000000042001000000001B00000000000000A0AE043AF67F00000000000000000000FFFFFFFF7D0000001E000000B790000007000000000000000004200100000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000DA00000000000000000000000000000000000000000000009D200000200000009100000064000000320000006400000050000000320000003200000028000000500000003C0000005000000050000000320000005000000050000000500000005000000050000000500000002800000050000000230000002300000023000000230000005000000050000000500000003200000032000000320000007800000078000000500000003C00000050000000500000009700000032000000780000003200000050000000500000005000000050000000000000000100000002000000030000000400000005000000060000000700000008000000090000000A0000000B0000000C0000000D0000000E0000000F000000100000001100000012000000130000001400000015000000160000001700000018000000190000001A0000001B0000001C0000001D0000001E0000001F000000200000002100000022000000230000002400000025000000260000002700000028000000290000002A0000002B0000002C00000000000000000000001F00000000000000B400000032000000D8000000640000006400000000000000000000000000000000000000000000000000000000000000000000000000000000000000DA000000000000000000000000000000000000009D200000200000009100000064000000320000009700000050000000320000003200000028000000500000003C000000500000005000000032000000500000005000000050000000500000005000000050000000500000002800000050000000230000002300000023000000230000005000000050000000500000003200000032000000320000007800000078000000500000003C0000005000000064000000780000003200000078000000780000003200000050000000500000005000000050000000C8000000000000000100000002000000030000000400000005000000060000000700000008000000090000000A0000000B0000000C0000000D0000000E0000000F000000100000001100000012000000130000001400000015000000160000001700000018000000190000001A0000001B0000001C0000001D0000001E0000001F000000200000002100000022000000230000002400000025000000260000002700000028000000290000002A0000002B0000002C0000002D0000002E0000002F00000000000000000000001F00000000000000B400000032000000D8000000640000006400000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000100000002000000030000000400000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000001000000000000000000000000000000 | |||
Executable files
212
Suspicious files
4
Text files
29
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1672 | LockWare.exe | C:\Users\admin\AppData\Local\Temp\_MEI16722\_lzma.pyd | executable | |
MD5:BEDB9684A240B94347C93CC08763BA73 | SHA256:4B88355F6DB4F98EBD90F74FC0F87CD9867D7569E0929BE7ED1AECDD6A2D4A6A | |||
| 1672 | LockWare.exe | C:\Users\admin\AppData\Local\Temp\_MEI16722\_cffi_backend.cp313-win_amd64.pyd | executable | |
MD5:35E7FD41D0865BE0AFC5B0F946FEFE6A | SHA256:84F3D195EFE08DB36CCDBE3DA834A49EED4A85F1F1C729FA1D8DFF23640D81E7 | |||
| 1672 | LockWare.exe | C:\Users\admin\AppData\Local\Temp\_MEI16722\VCRUNTIME140.dll | executable | |
MD5:862F820C3251E4CA6FC0AC00E4092239 | SHA256:36585912E5EAF83BA9FEA0631534F690CCDC2D7BA91537166FE53E56C221E153 | |||
| 1672 | LockWare.exe | C:\Users\admin\AppData\Local\Temp\_MEI16722\api-ms-win-core-console-l1-1-0.dll | executable | |
MD5:AB7E867E9C1E8AF927BCF316DAF1BD5D | SHA256:FF8B590BEE71BCCE9D7CD7E40540E4093AAE26D8AAB4AF4AF43983EC9CA3A652 | |||
| 1672 | LockWare.exe | C:\Users\admin\AppData\Local\Temp\_MEI16722\api-ms-win-core-errorhandling-l1-1-0.dll | executable | |
MD5:D755D3165174669240CF8B4673BF13EB | SHA256:29996C70B1C4E4A8FE80E33FF0C5D0658A12AB9B2A0C578ABD6AB3C395341AD7 | |||
| 1672 | LockWare.exe | C:\Users\admin\AppData\Local\Temp\_MEI16722\_hashlib.pyd | executable | |
MD5:5416D4A5FC54AD332670750B848237E6 | SHA256:7D06C81BAA3475F08540FC51CE0EFB3F8D4129C20299CDF38CFF0B0666298ADA | |||
| 1672 | LockWare.exe | C:\Users\admin\AppData\Local\Temp\_MEI16722\_socket.pyd | executable | |
MD5:C5C4F38D896C04C2CF3EB1B847617E79 | SHA256:2AD92C25176D055371F031E169451A819A2C15923345C3F6DBAAE4E1EAC15856 | |||
| 1672 | LockWare.exe | C:\Users\admin\AppData\Local\Temp\_MEI16722\api-ms-win-core-debug-l1-1-0.dll | executable | |
MD5:067935E239F90BA8262D1D083603EEBD | SHA256:FB2DE5DAD6046472BC2C41906E4BEC6532AF8BBB2D3D70D31434FFBD801A6359 | |||
| 1672 | LockWare.exe | C:\Users\admin\AppData\Local\Temp\_MEI16722\api-ms-win-core-heap-l1-1-0.dll | executable | |
MD5:E8BCD292FED33FE4F7477EAEBA0B9232 | SHA256:1992A274E98CE1FB7ED658A393A729A191542C9C5B89C7FDB35A74937A02A165 | |||
| 1672 | LockWare.exe | C:\Users\admin\AppData\Local\Temp\_MEI16722\api-ms-win-core-file-l1-2-0.dll | executable | |
MD5:399A356813BC768093F851BDF1066B9B | SHA256:CDDC95AE534E0A0D15287B72F7C6DF529DB7E331F1A98BE253A4504820CAAD55 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
34
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5304 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5304 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.23:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |