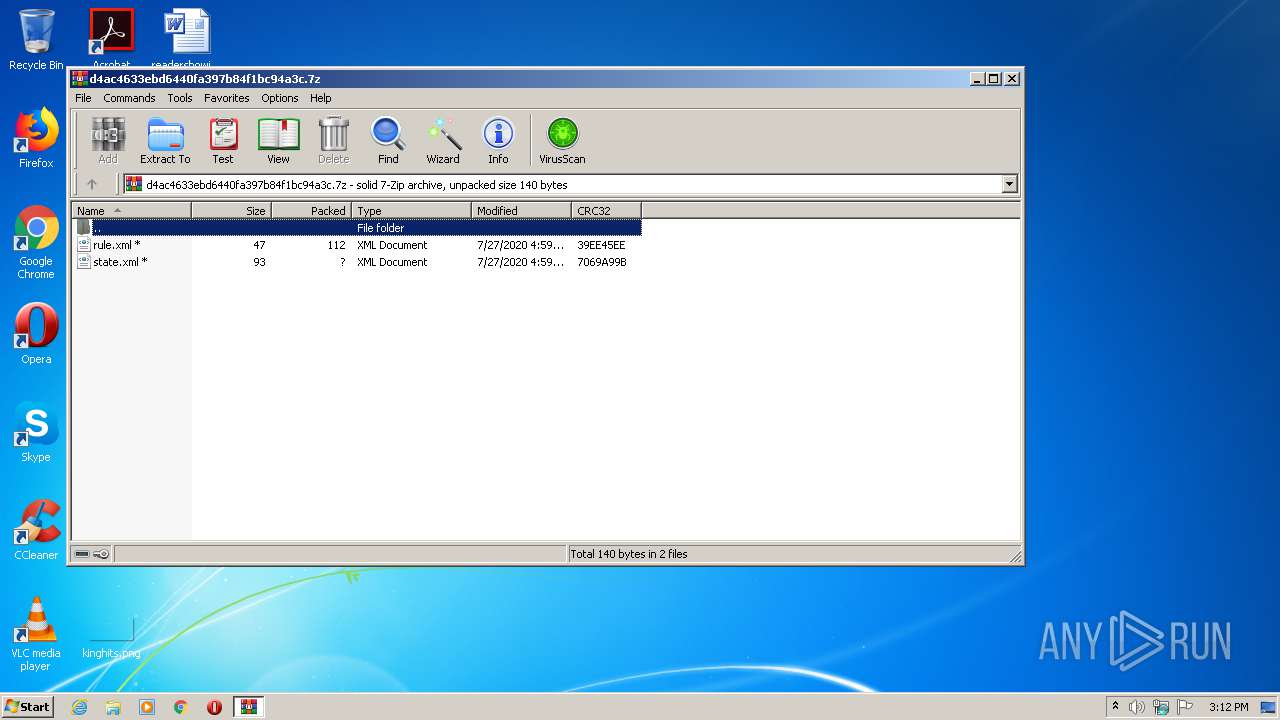
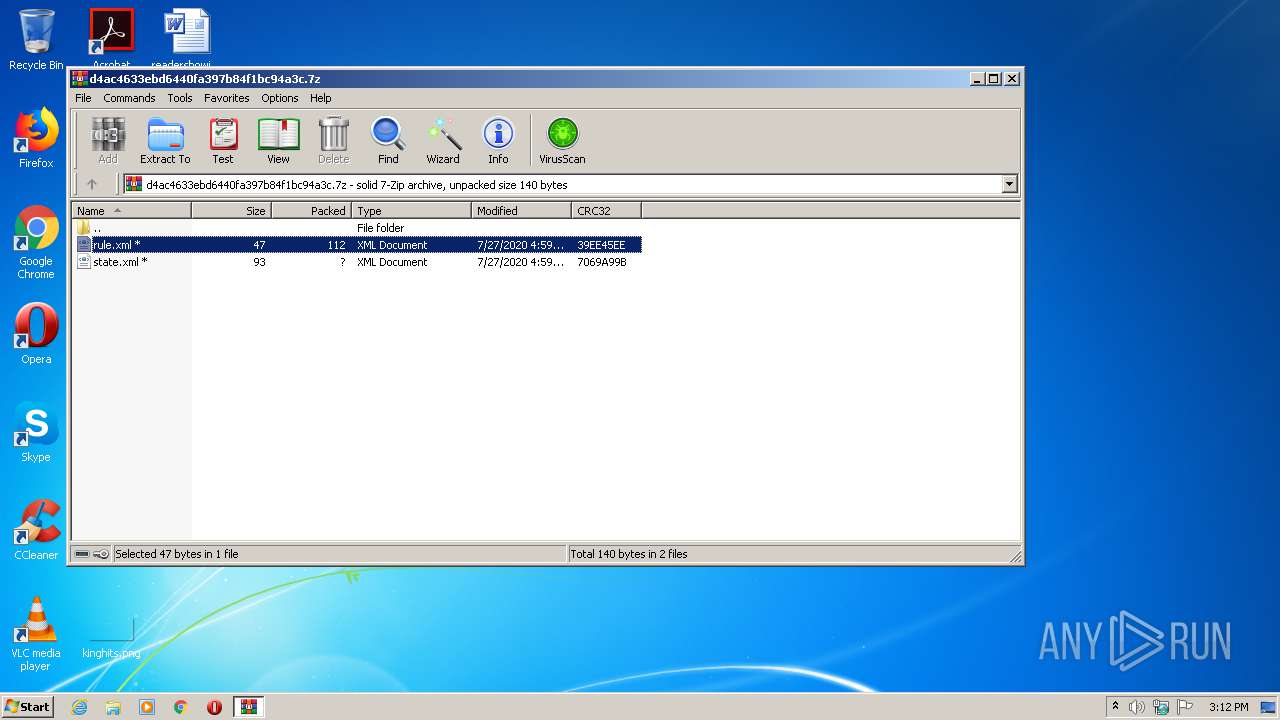
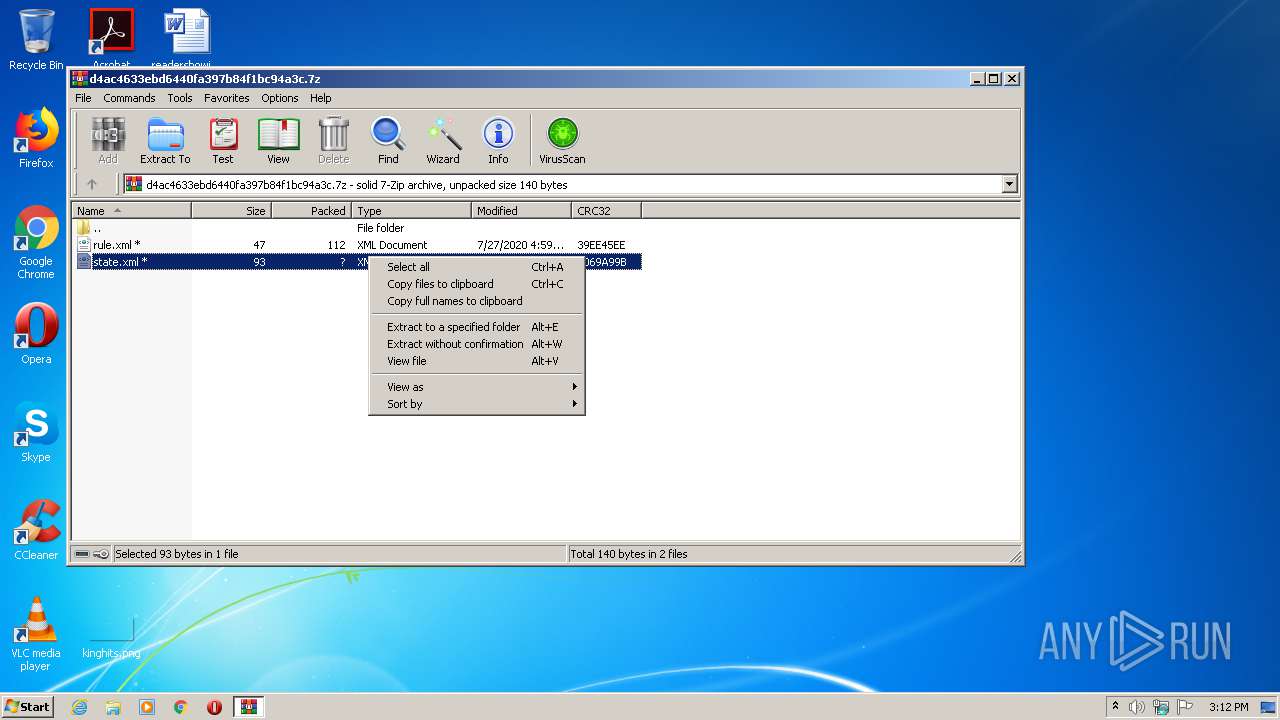
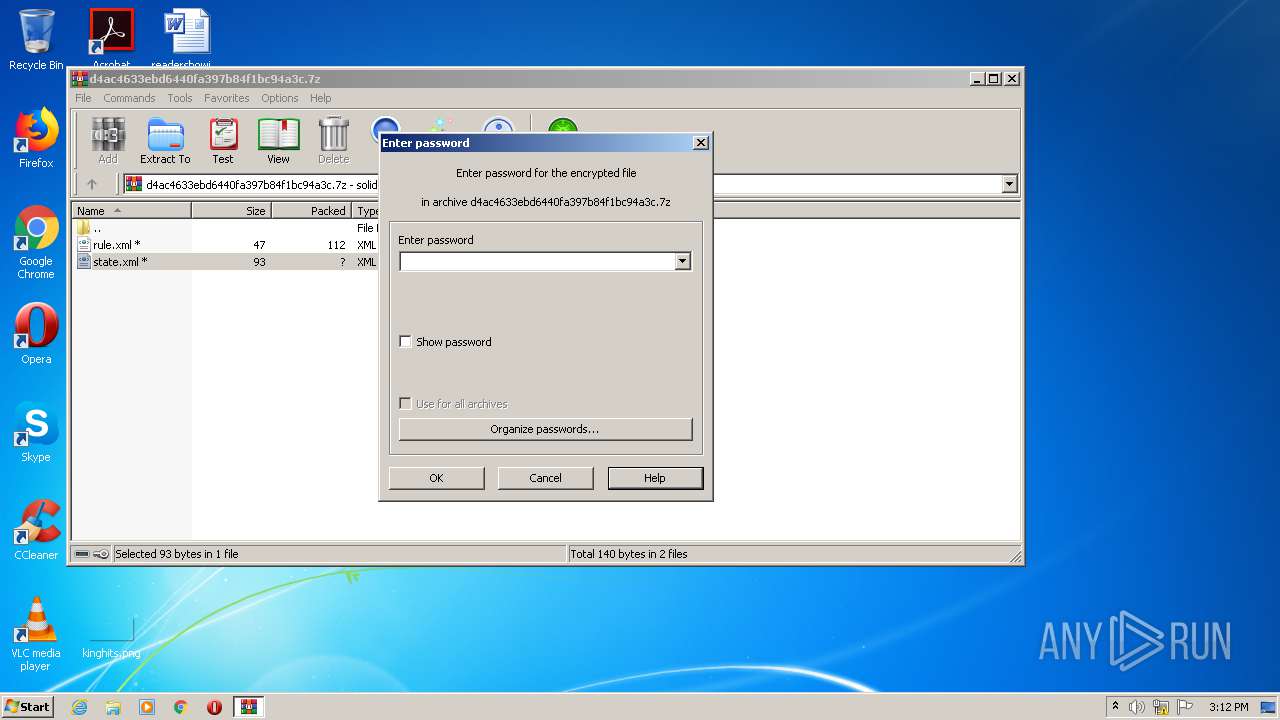
| File name: | d4ac4633ebd6440fa397b84f1bc94a3c.7z |
| Full analysis: | https://app.any.run/tasks/24c0ba4e-0af3-44f7-b743-93206bc00f1d |
| Verdict: | No threats detected |
| Analysis date: | August 08, 2020, 14:11:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 244C60B6CC74FC331C00E7EF44F314D0 |
| SHA1: | B2743832E9380A537E5892135A1F6002C2976B69 |
| SHA256: | FA4E07E7CD83FF63CD378CCC21CDB8E0358FEA7950458A845D417F822D537FA0 |
| SSDEEP: | 6:ul2Ya+NzrKC1DtMU4XfdQN6AI8nvsRzsjTZT8lfKd3ln:bH81D2NXfKxIUs4TZ/bn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads internet explorer settings
- WinRAR.exe (PID: 280)
Reads Internet Cache Settings
- WinRAR.exe (PID: 280)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
Total processes
37
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
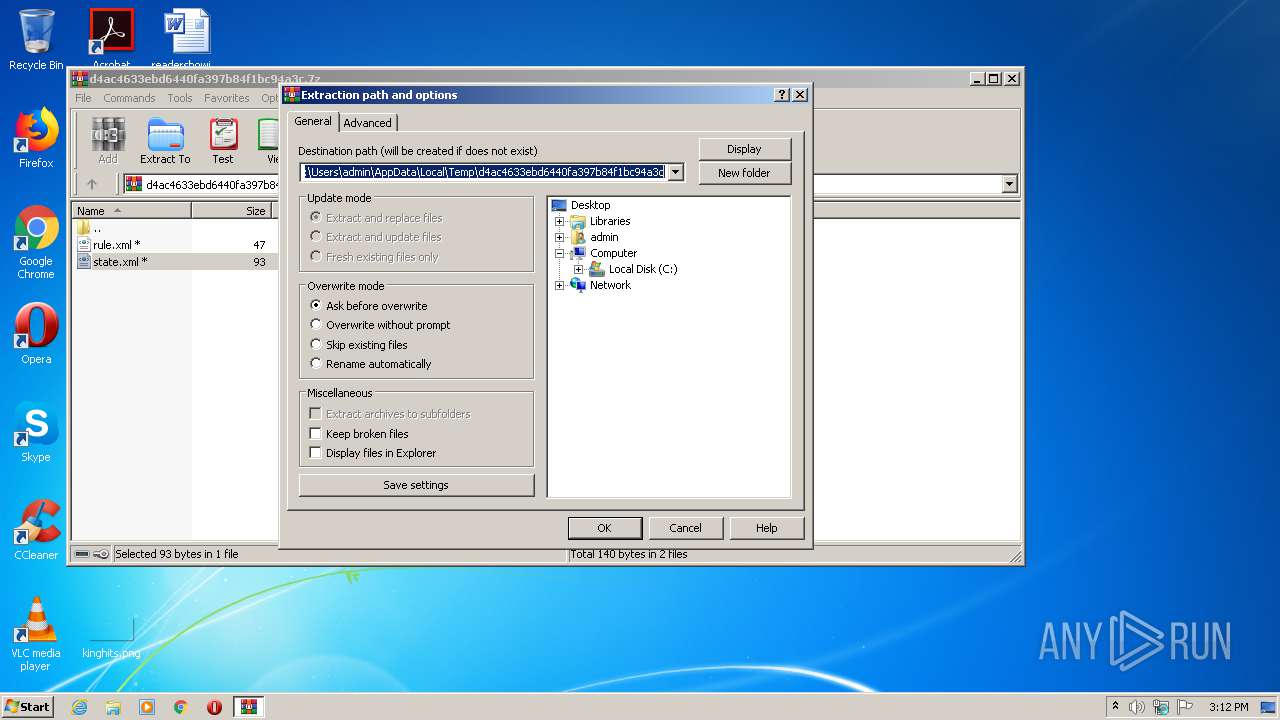
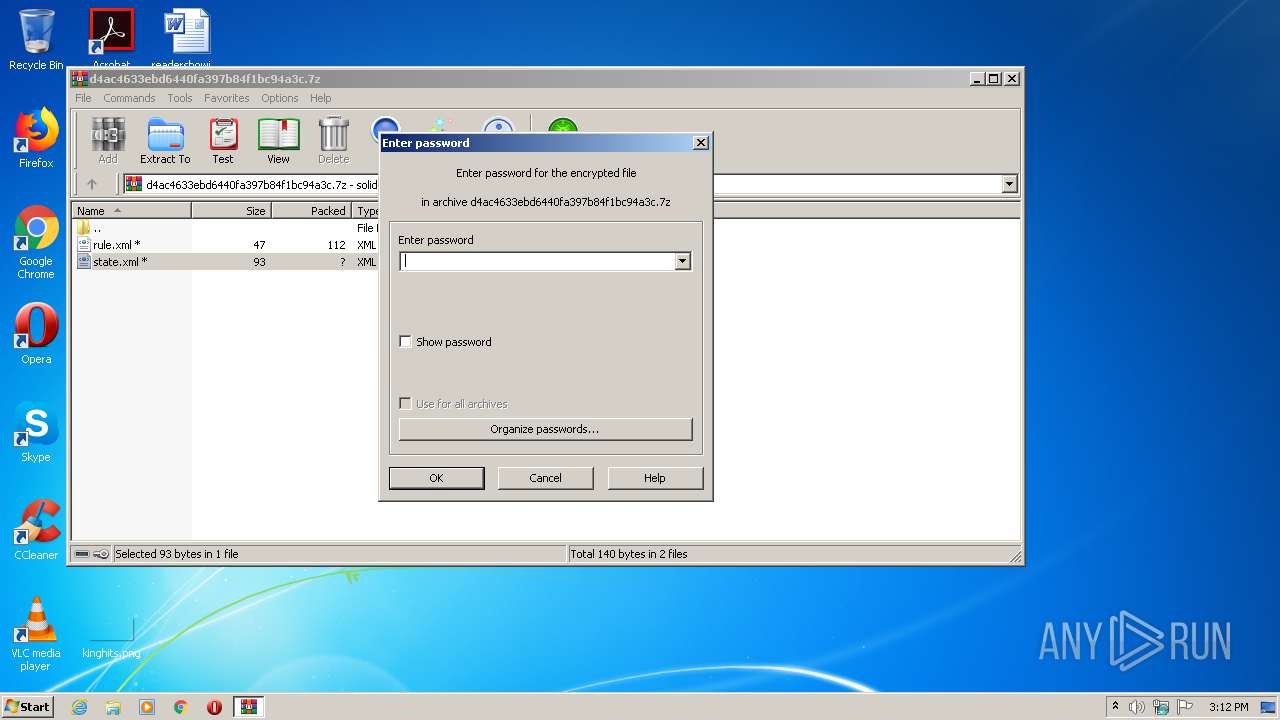
| 280 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\d4ac4633ebd6440fa397b84f1bc94a3c.7z" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
495
Read events
475
Write events
20
Delete events
0
Modification events
| (PID) Process: | (280) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (280) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (280) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\136\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (280) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\136\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (280) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\d4ac4633ebd6440fa397b84f1bc94a3c.7z | |||
| (PID) Process: | (280) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (280) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (280) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (280) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (280) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\136\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\msxml3r.dll,-1 |
Value: XML Document | |||
Executable files
0
Suspicious files
0
Text files
1
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 280 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\~DF0AA68A30F400DCBB.TMP | — | |
MD5:— | SHA256:— | |||
| 280 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\~DF5EBCEC823CE44DC9.TMP | — | |
MD5:— | SHA256:— | |||
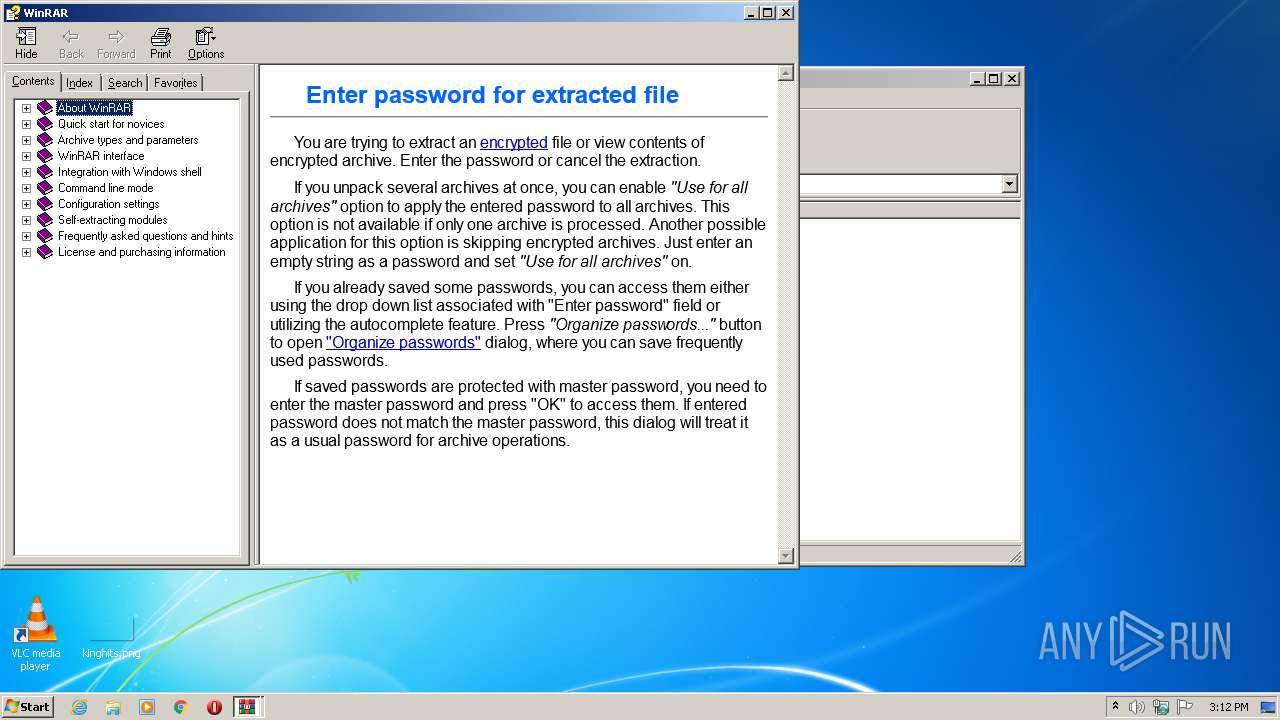
| 280 | WinRAR.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\style[1].css | text | |
MD5:D0E81A97B0BF393FACB2790C89A03D54 | SHA256:9F83FADD6AB0D45ACCAE671D0D13AAAAC730079F81D0539C374A251CD3FD0036 | |||
| 280 | WinRAR.exe | C:\Users\admin\AppData\Roaming\Microsoft\HTML Help\hh.dat | chm | |
MD5:54339081FECC850448492C6837B6F3AD | SHA256:FC1B9FB17F4F69E8DF4B24B0320ACD5B2E171600174C836647ACECD10816AD72 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report