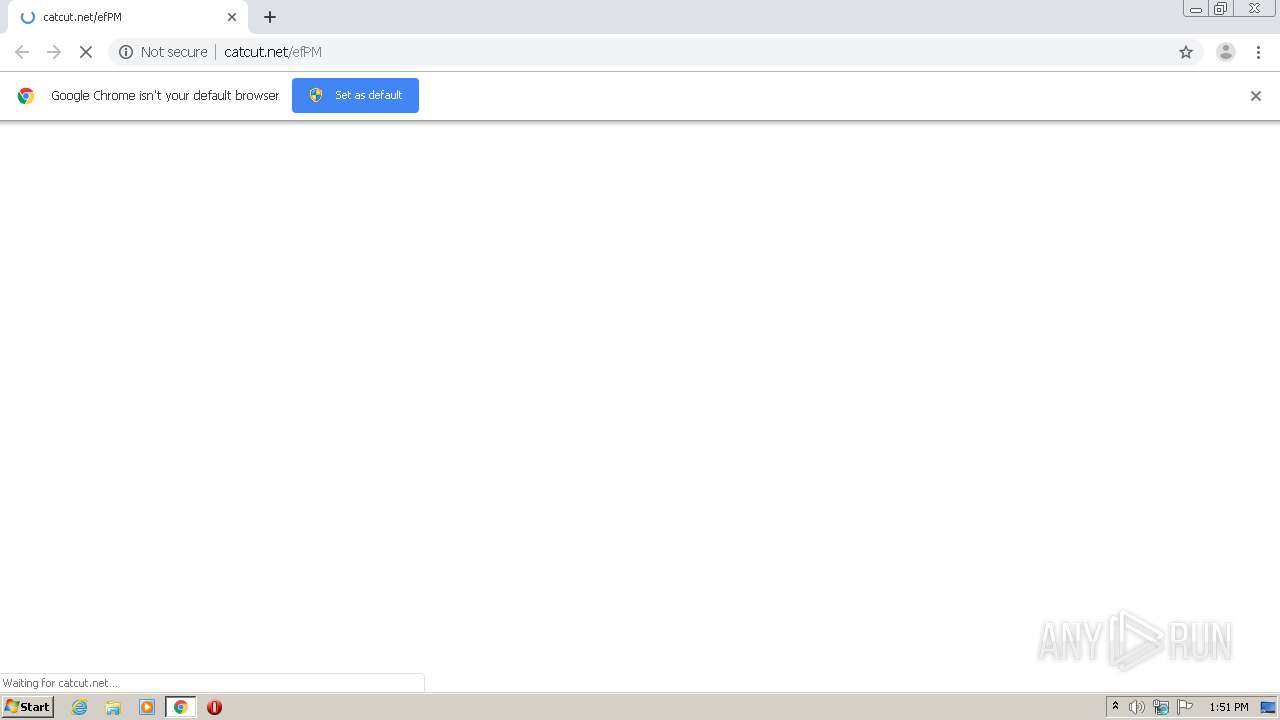
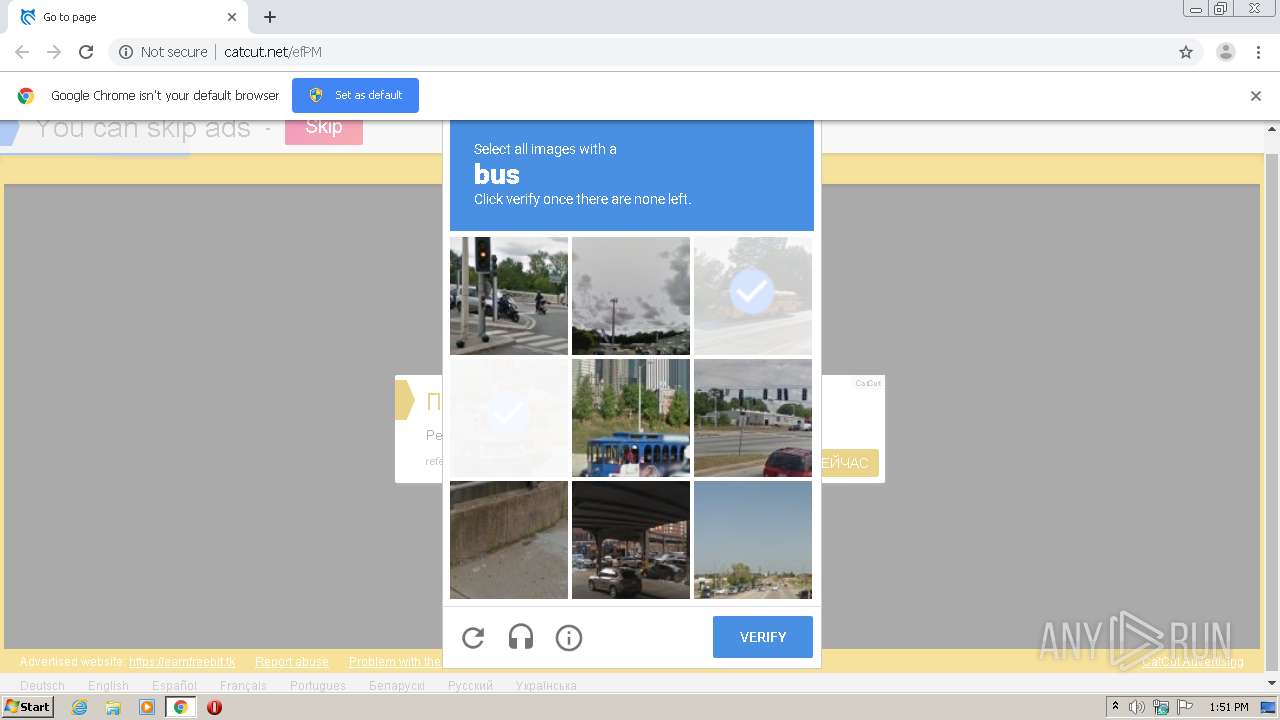
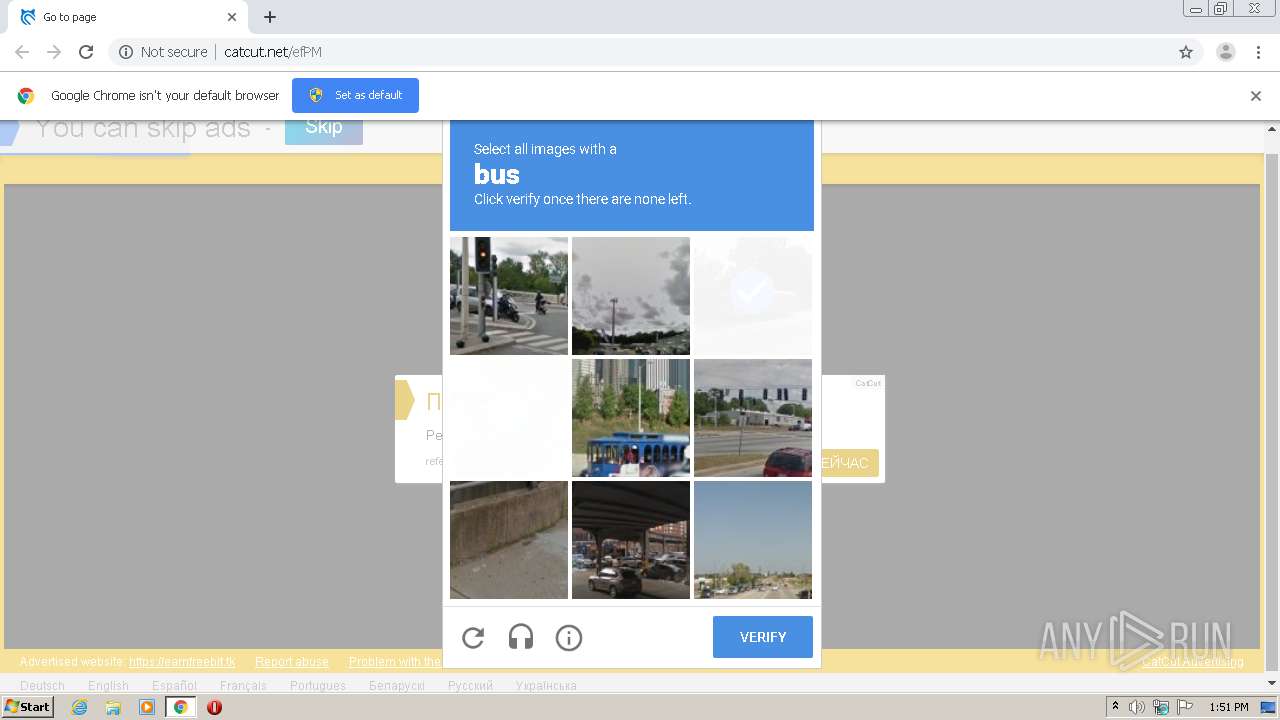
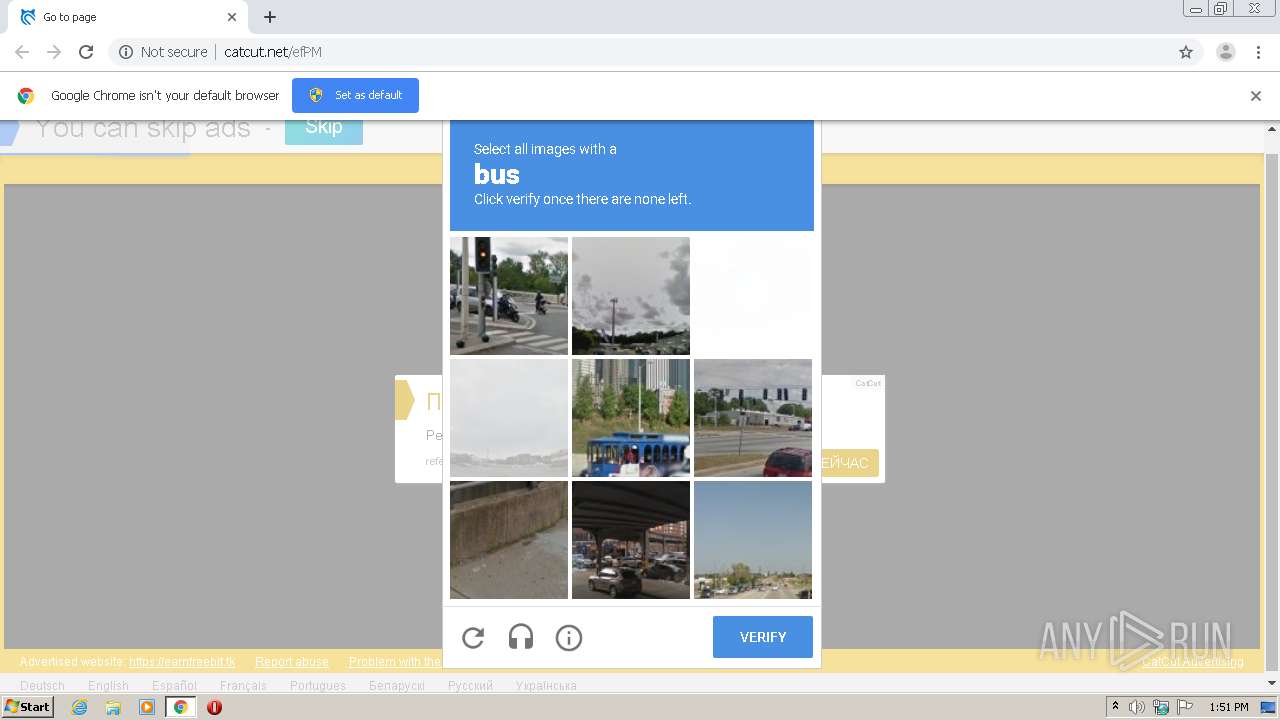
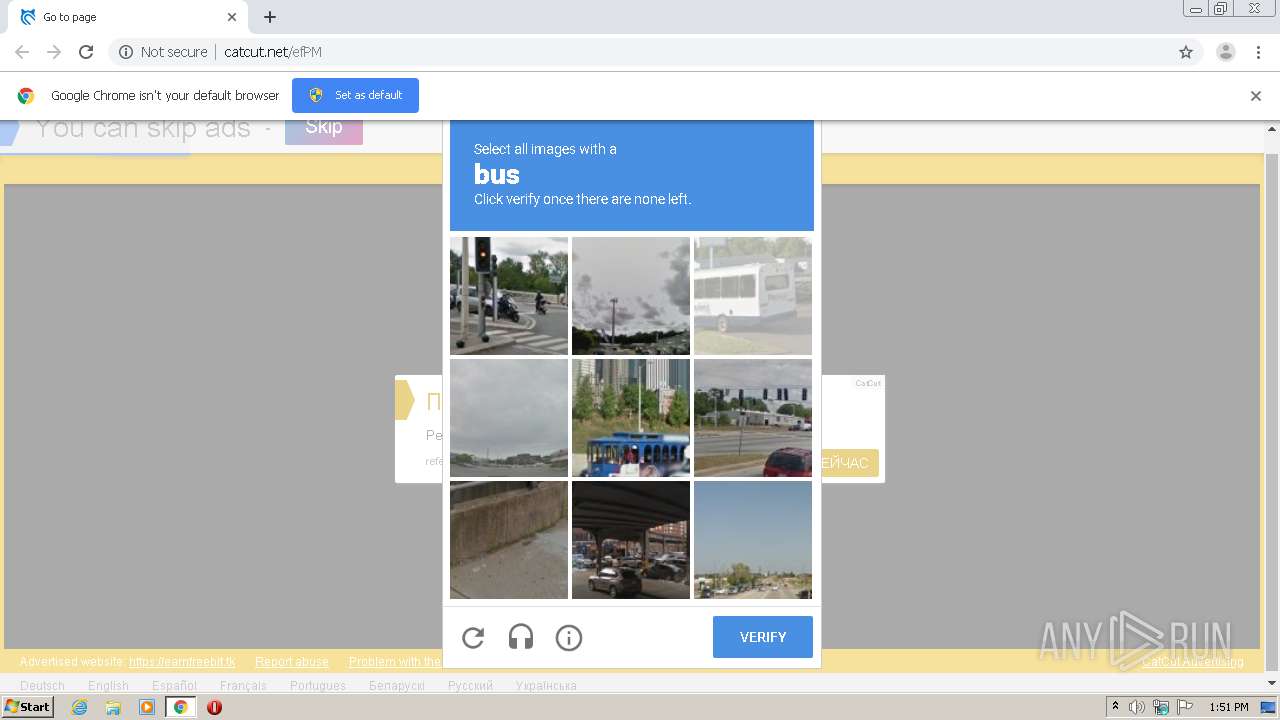
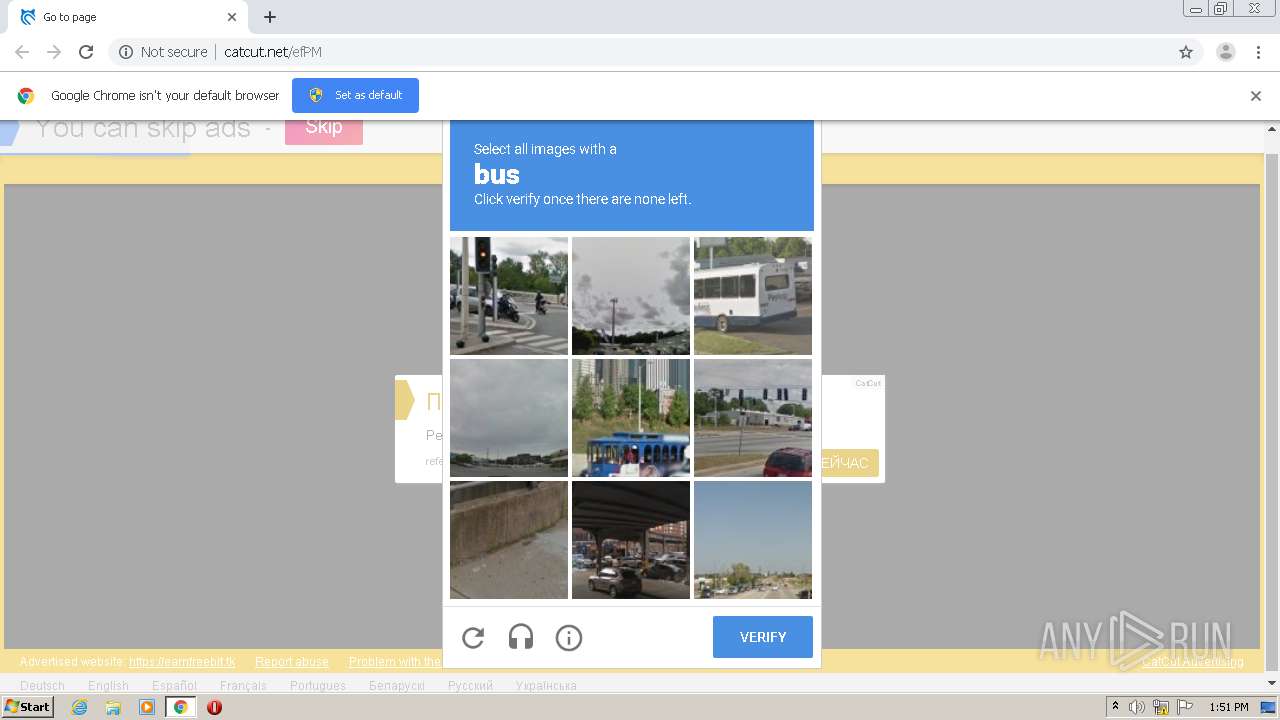
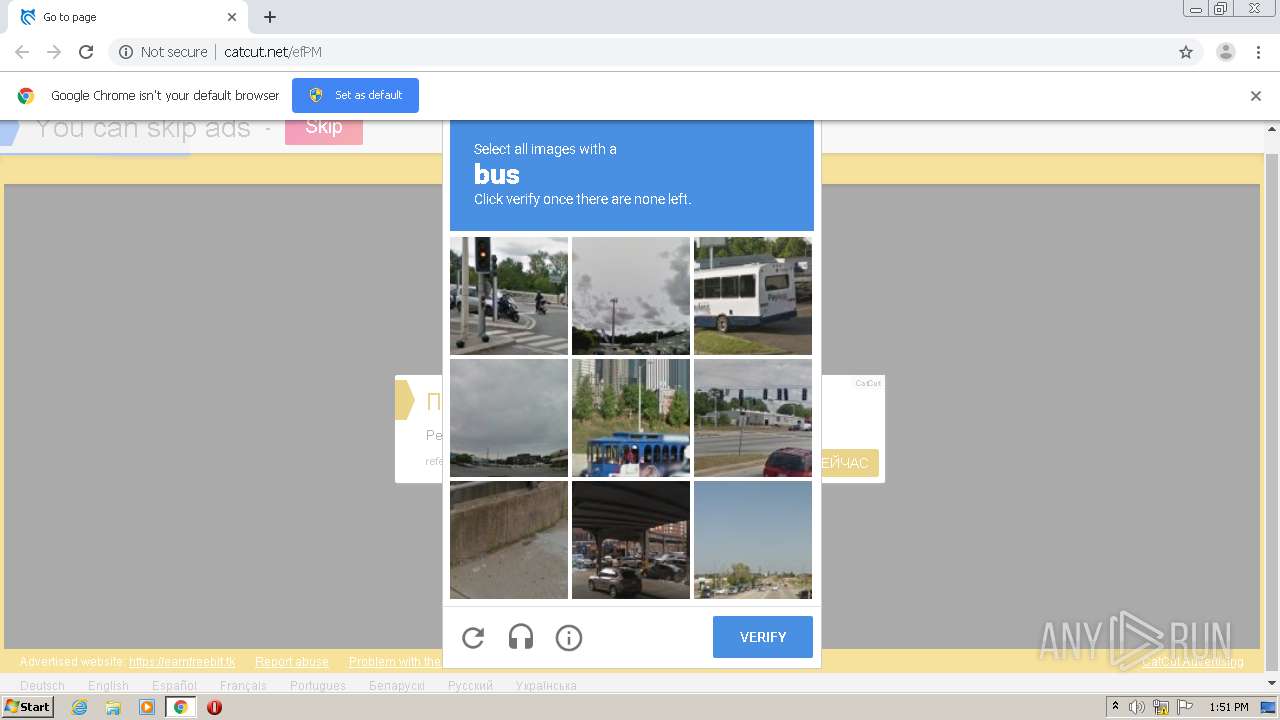
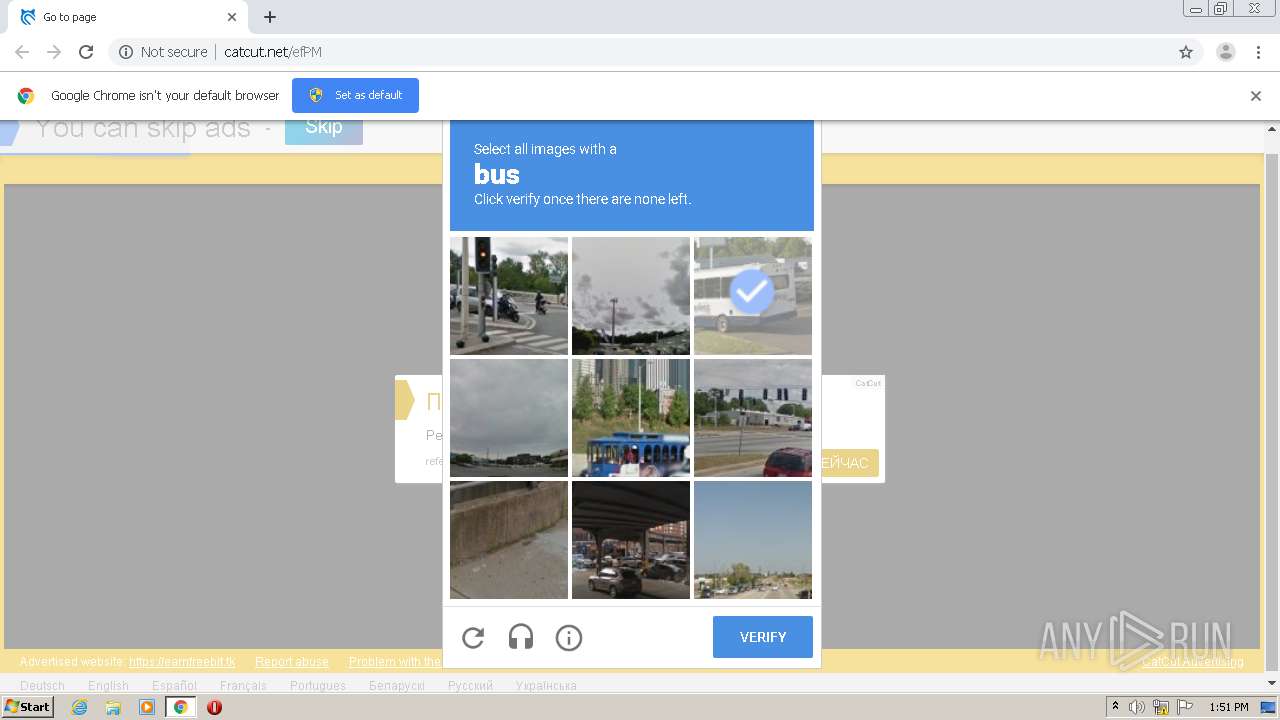
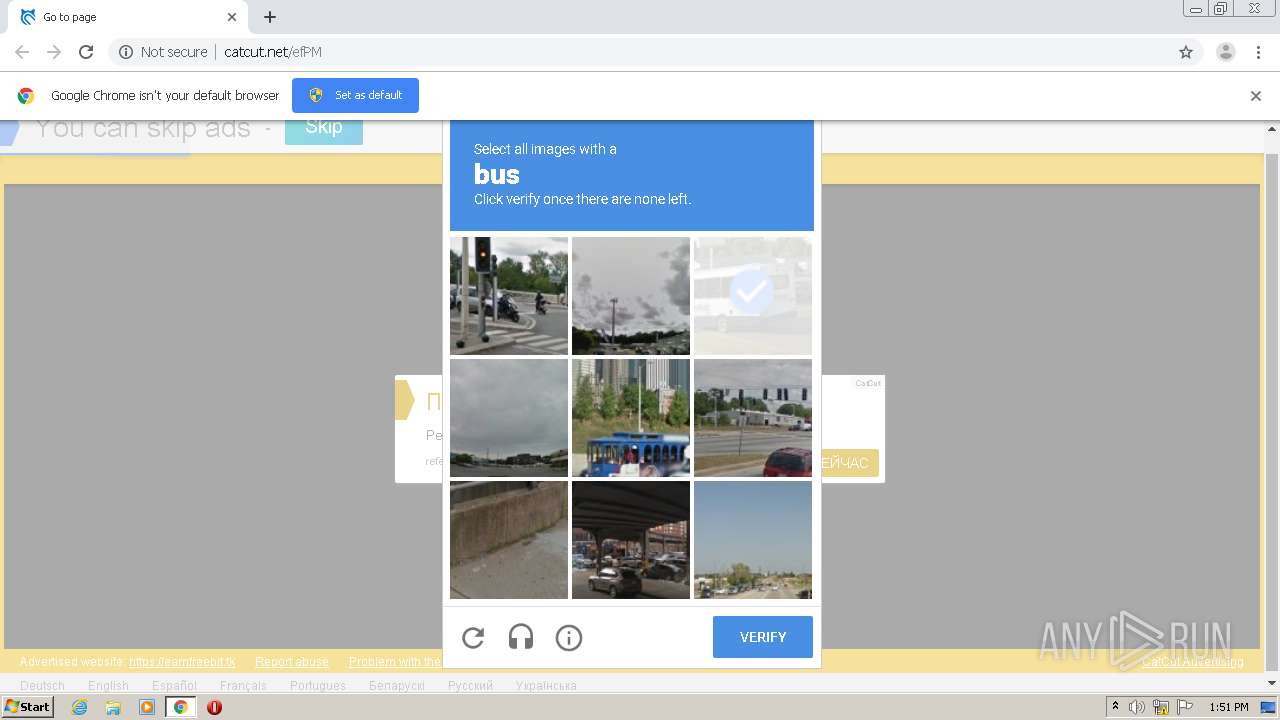
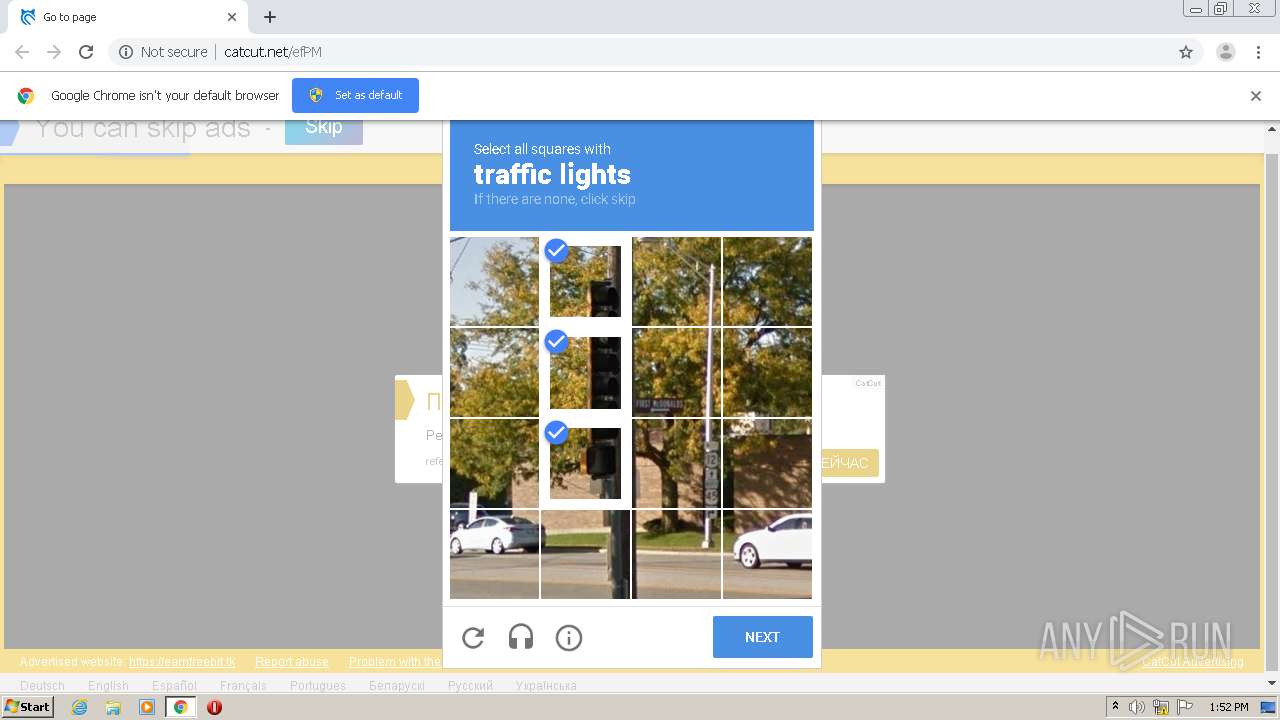
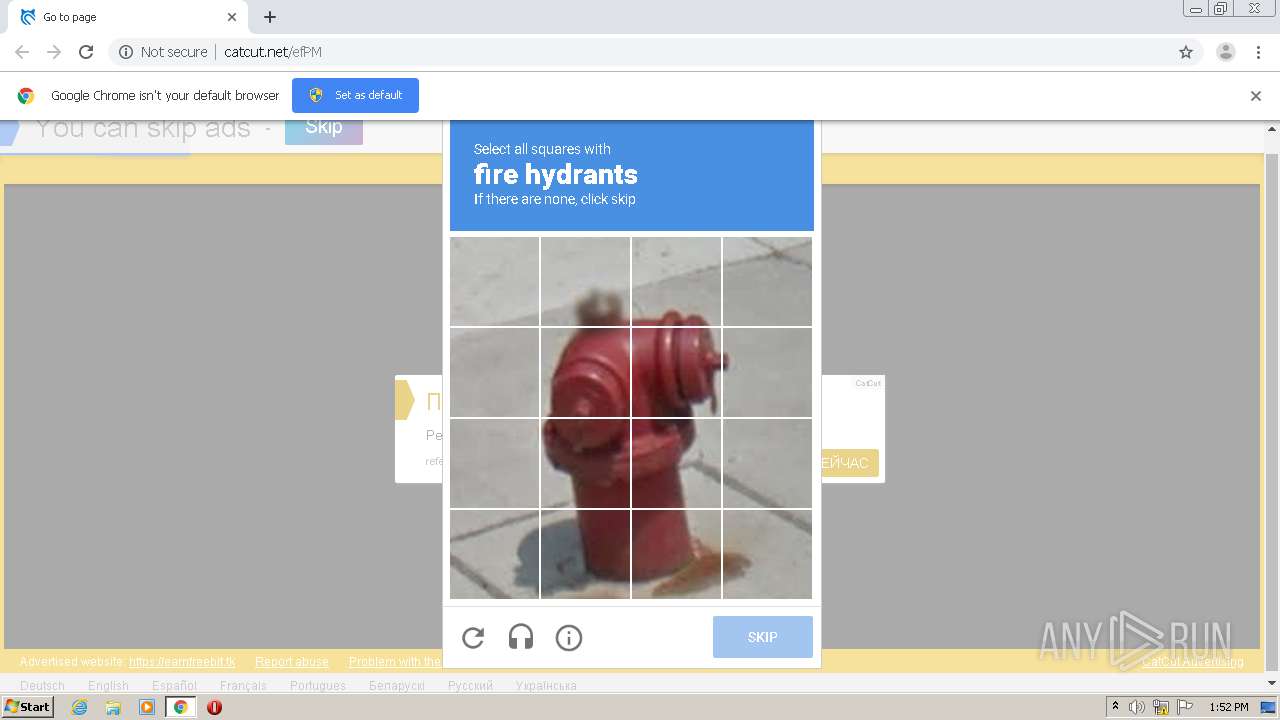
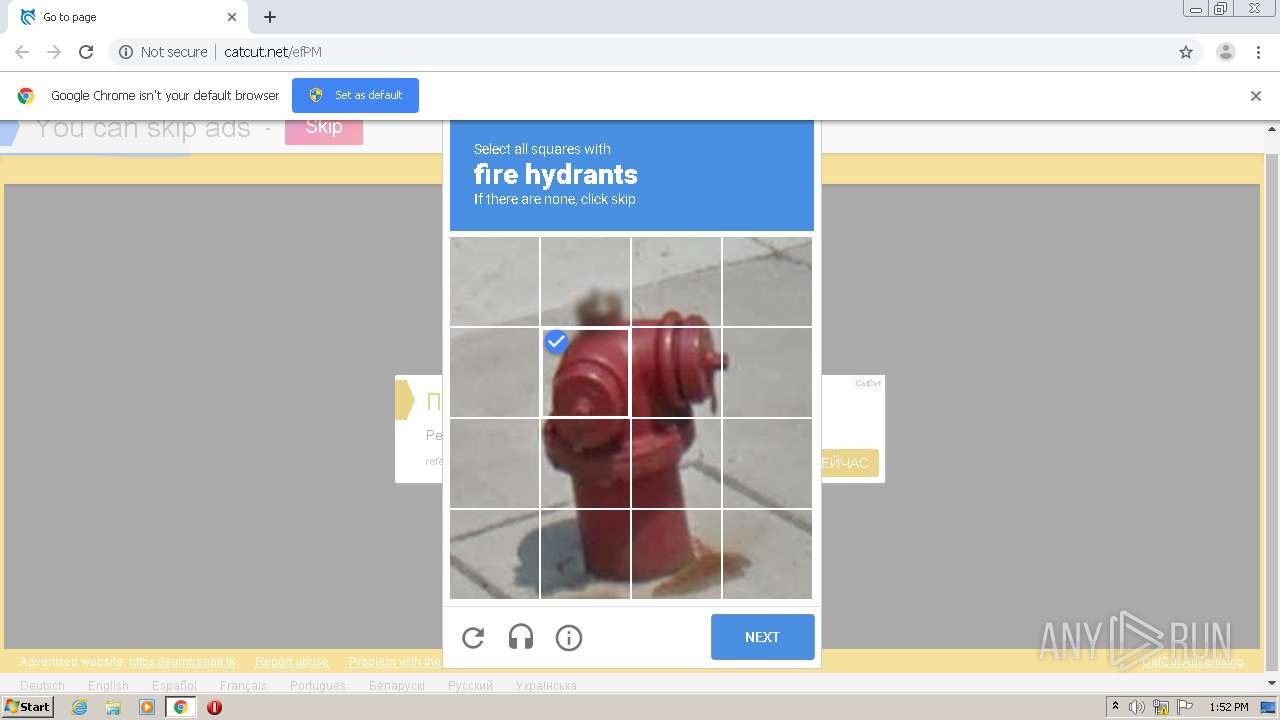
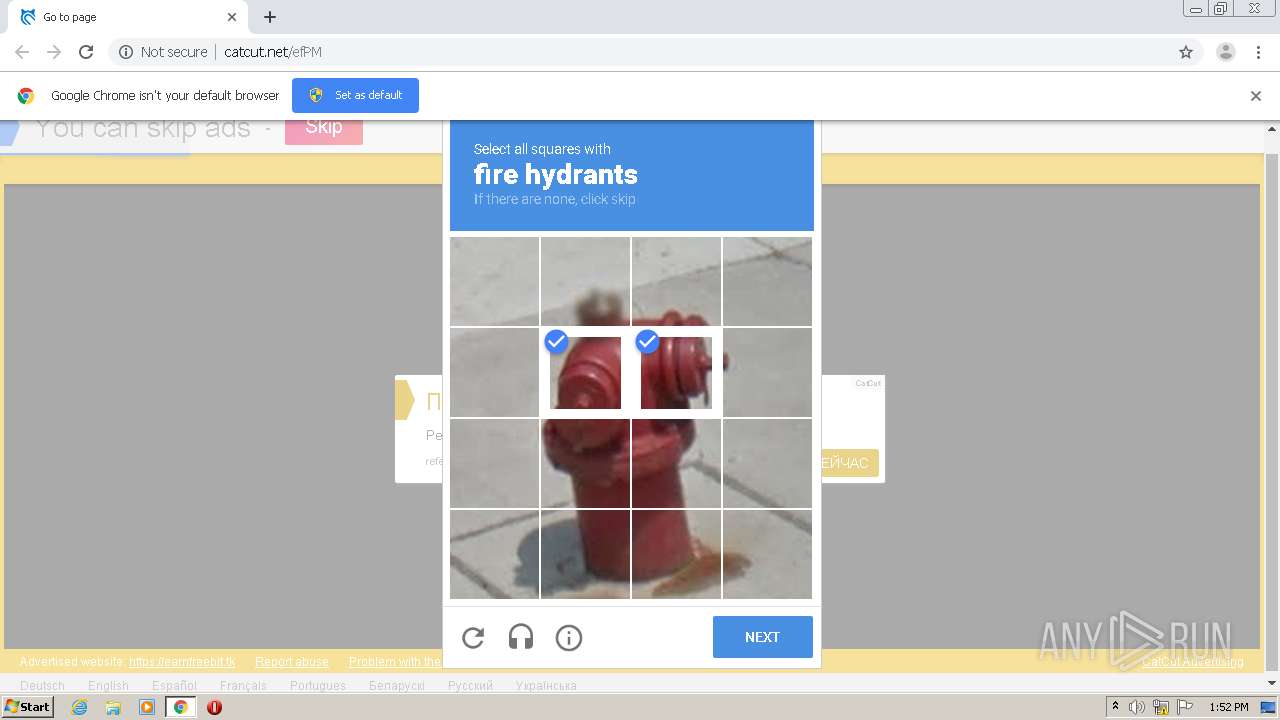
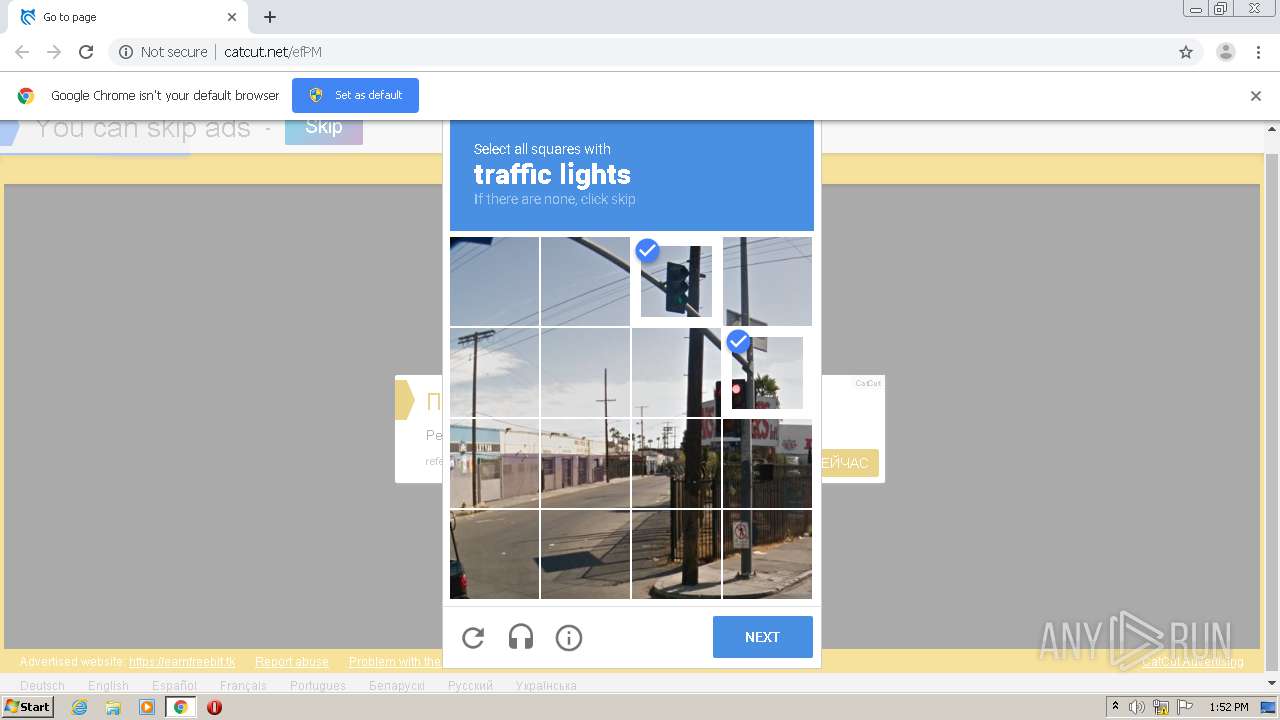
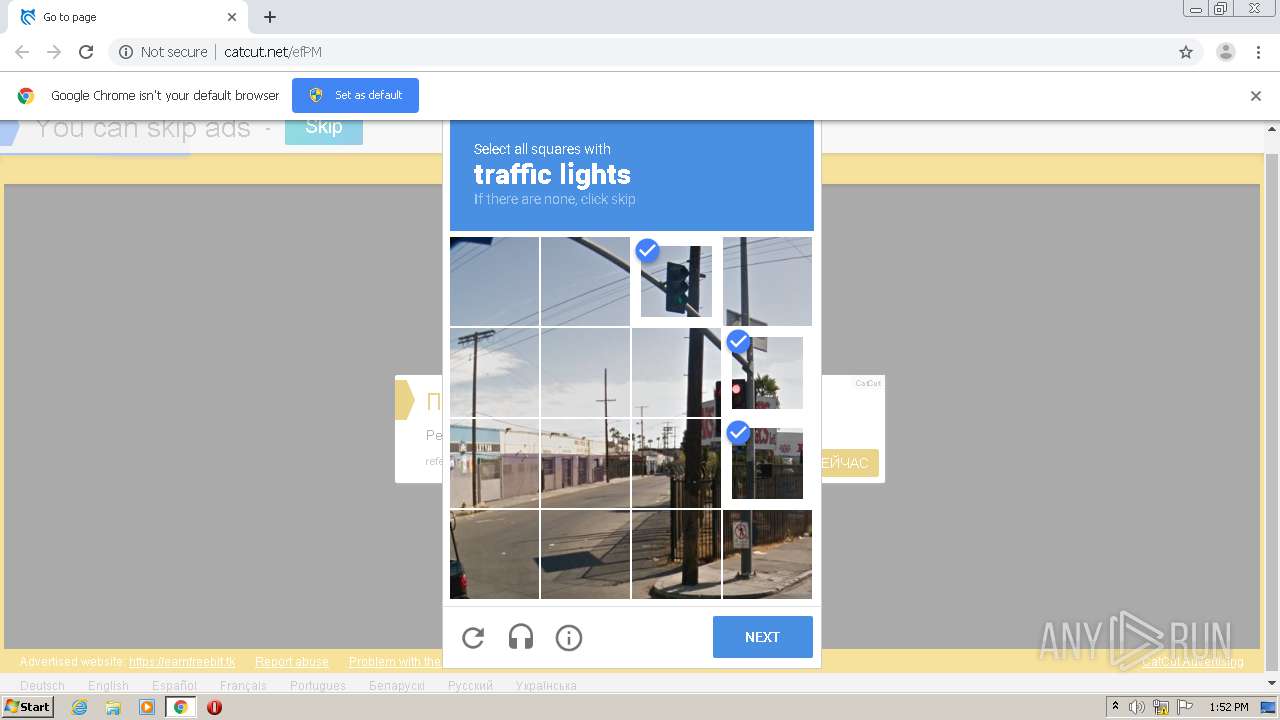
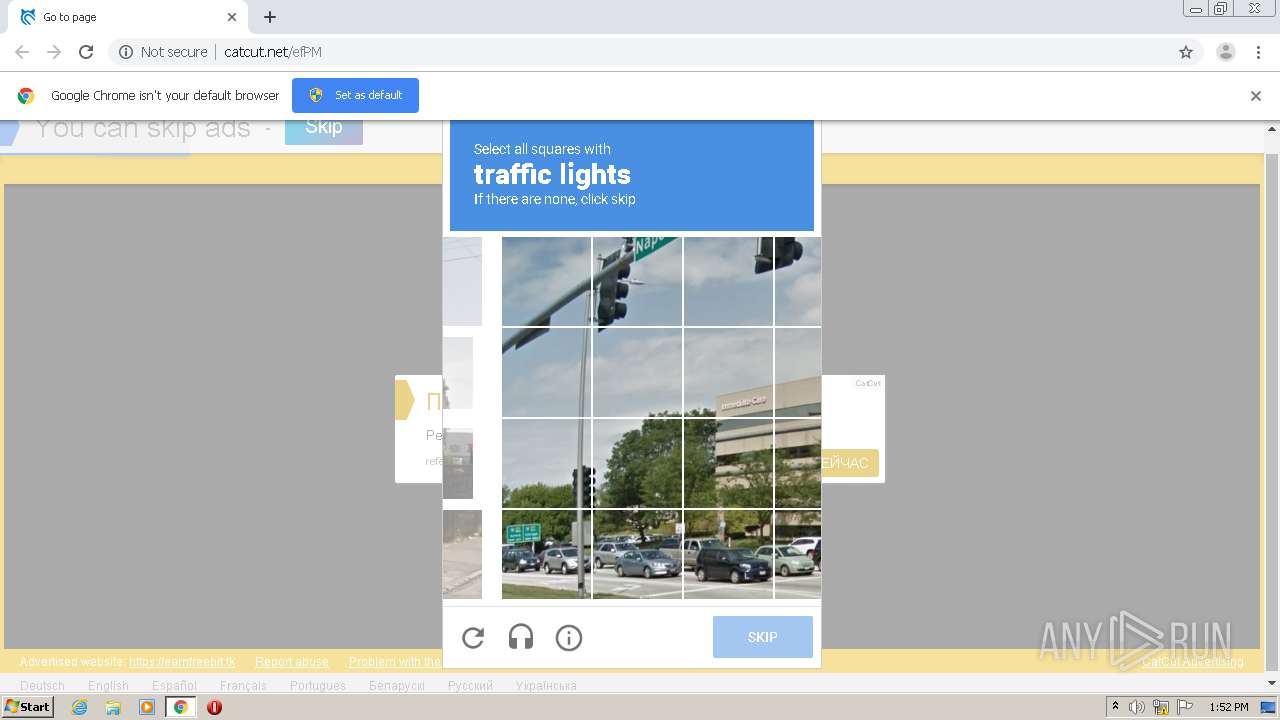
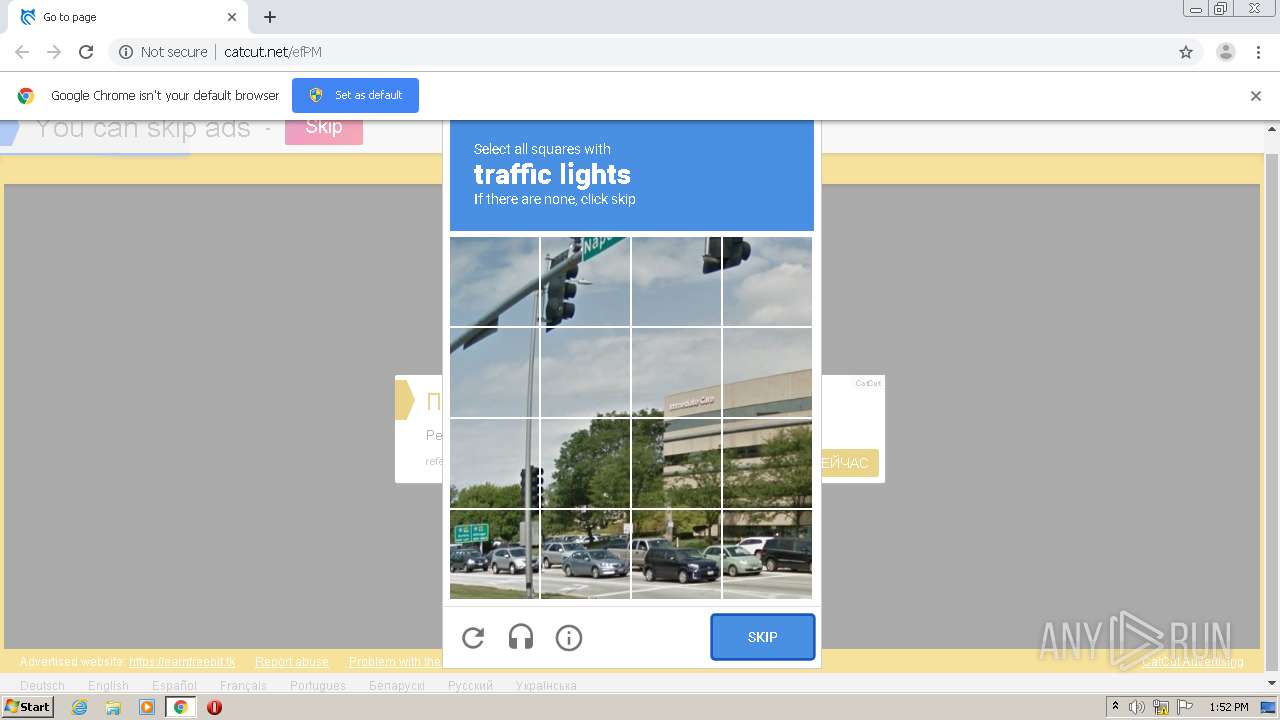
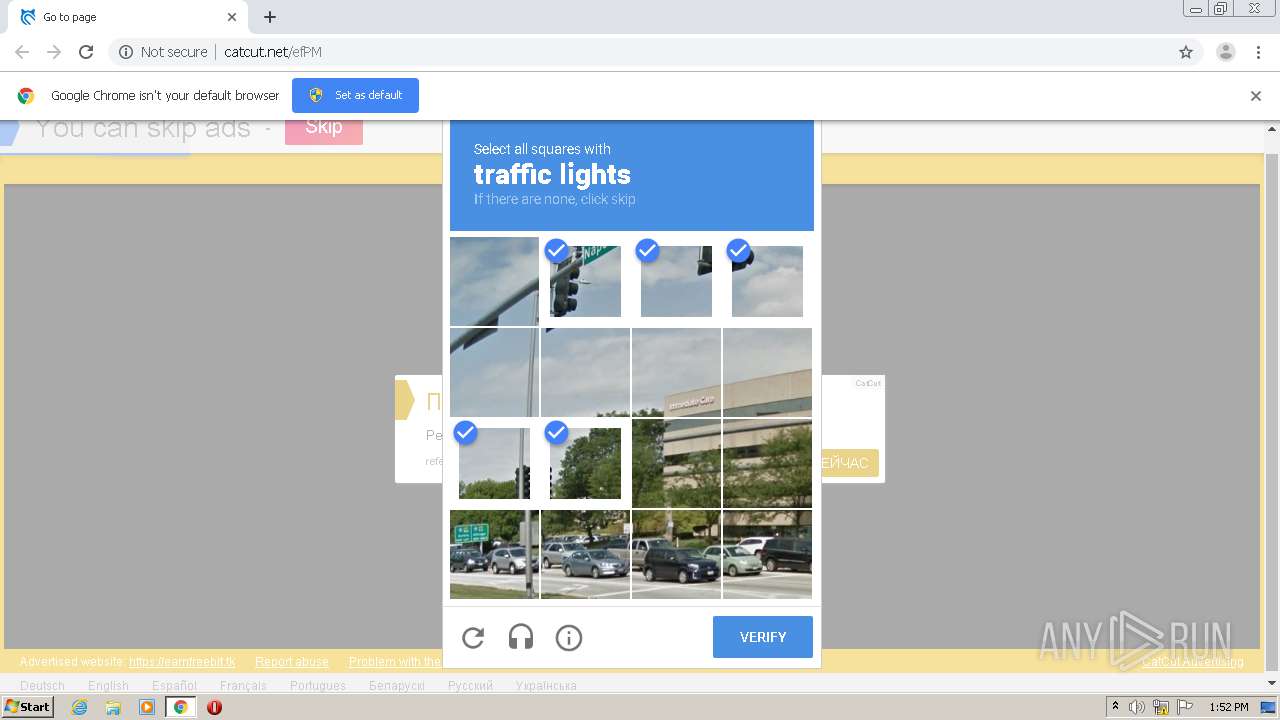
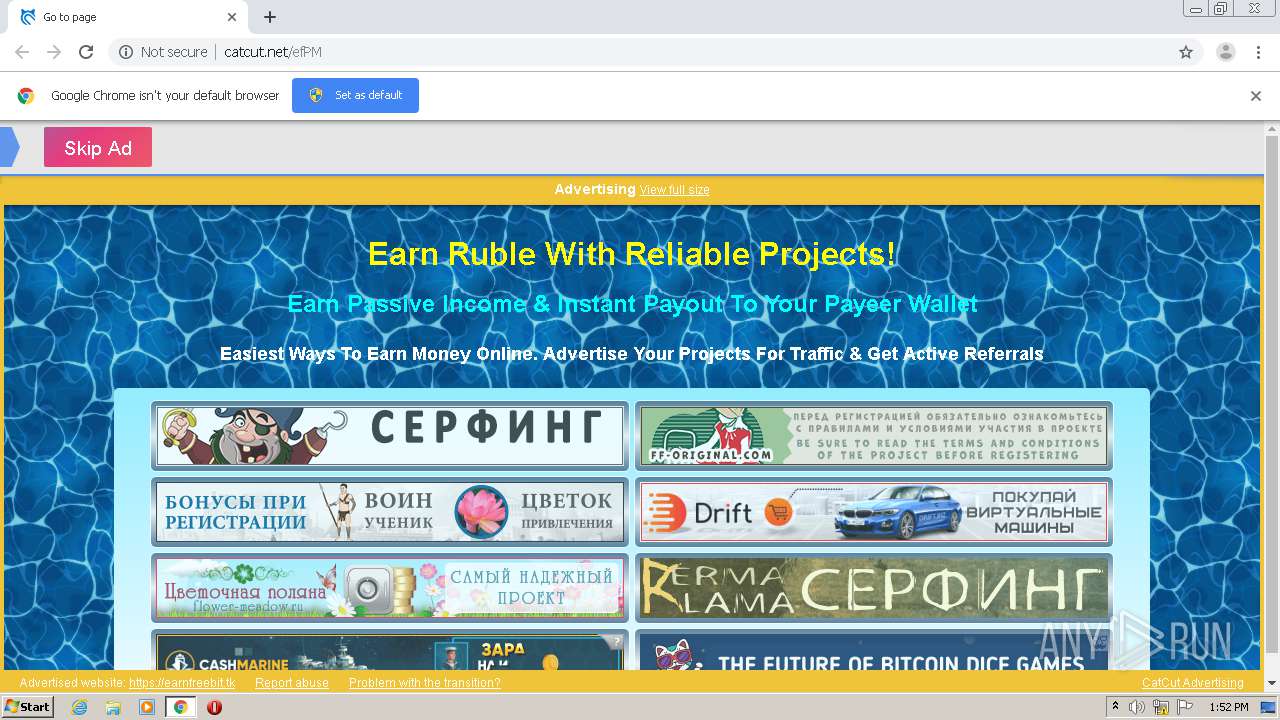
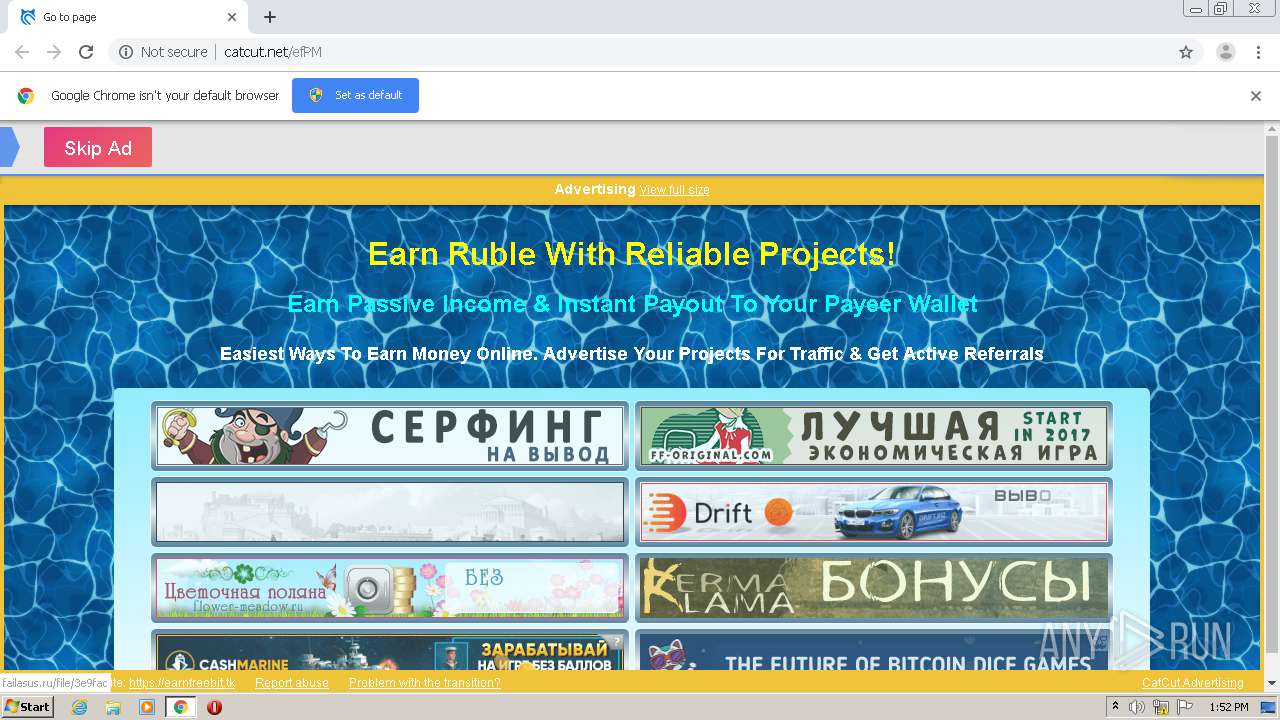
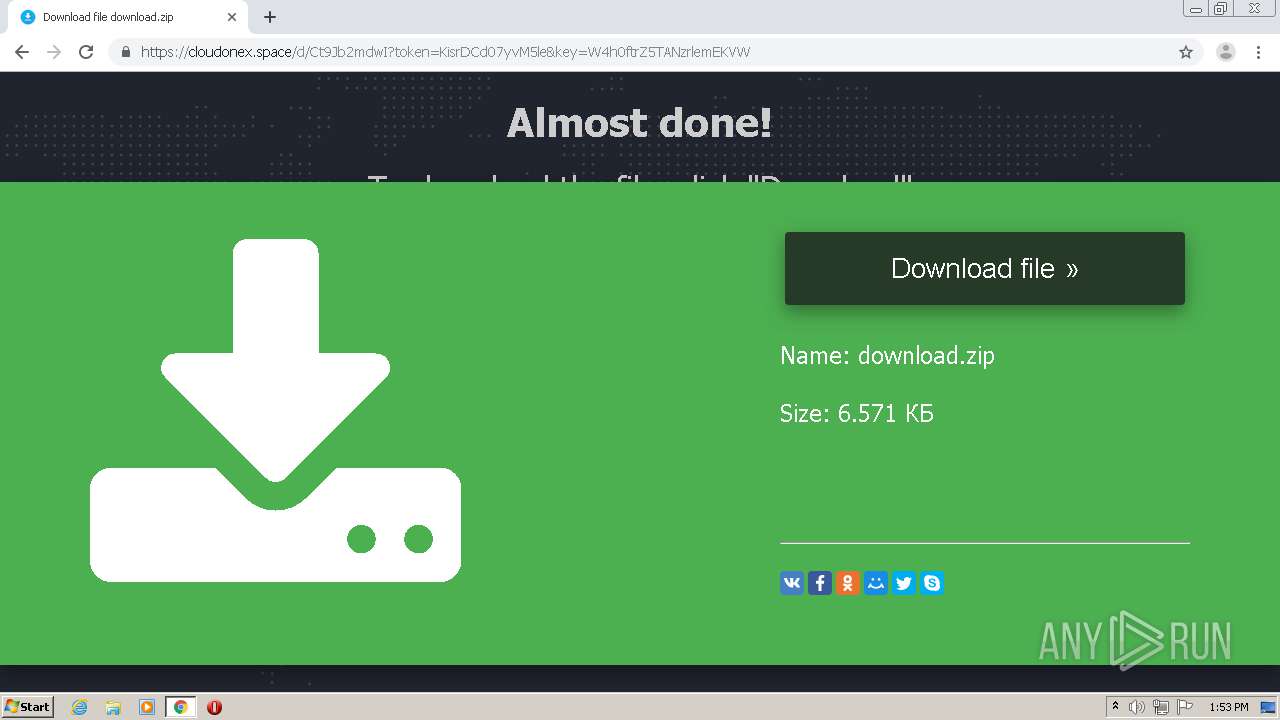
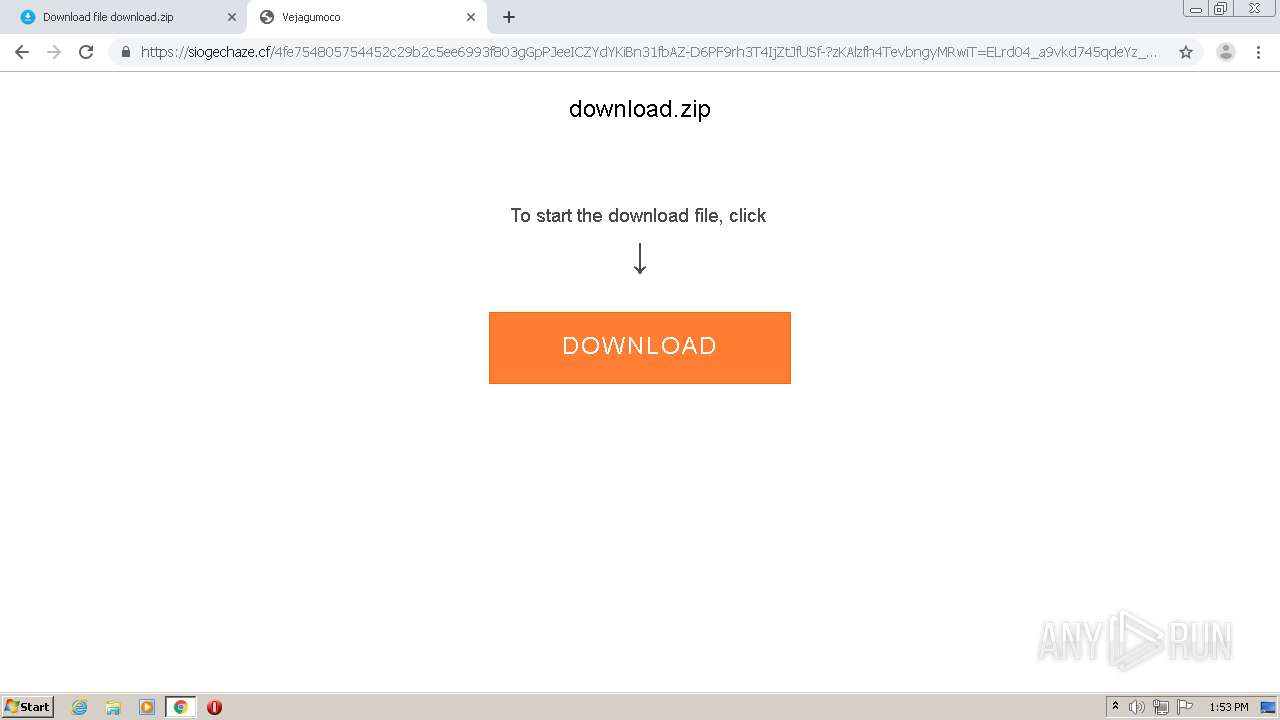
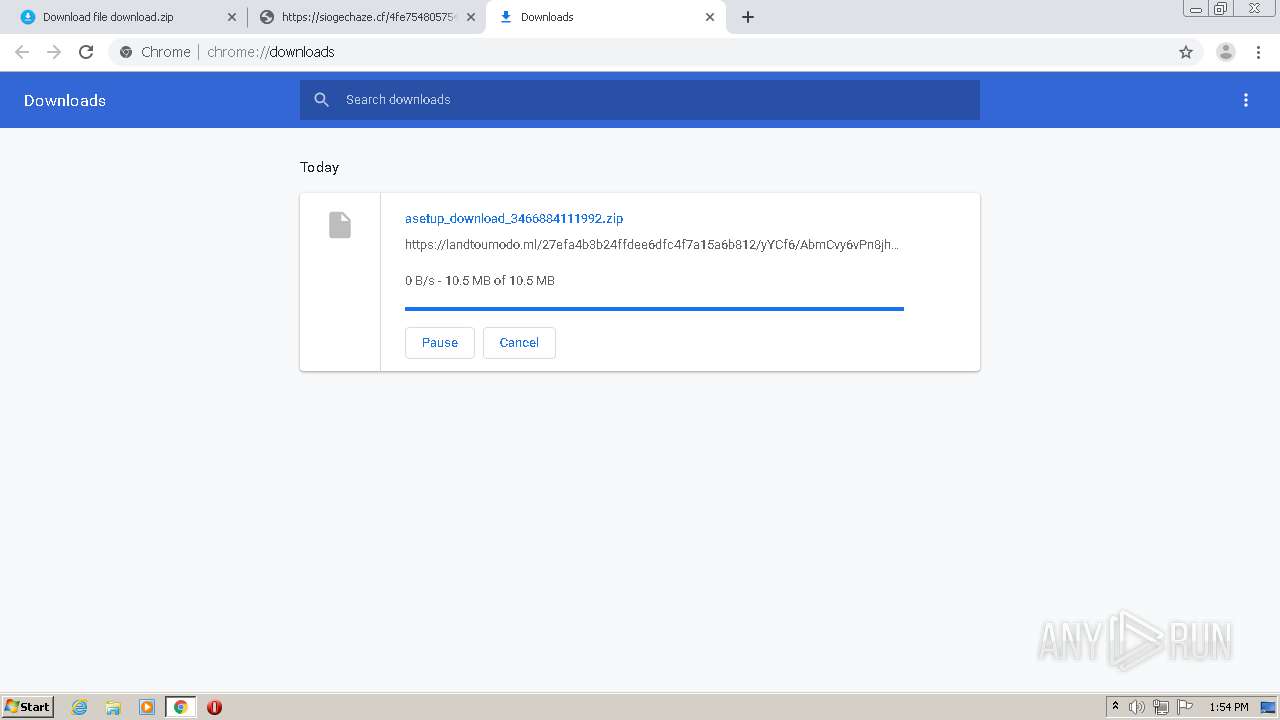
| URL: | http://catcut.net/efPM |
| Full analysis: | https://app.any.run/tasks/f552485c-f701-458e-842e-2640cd2722cd |
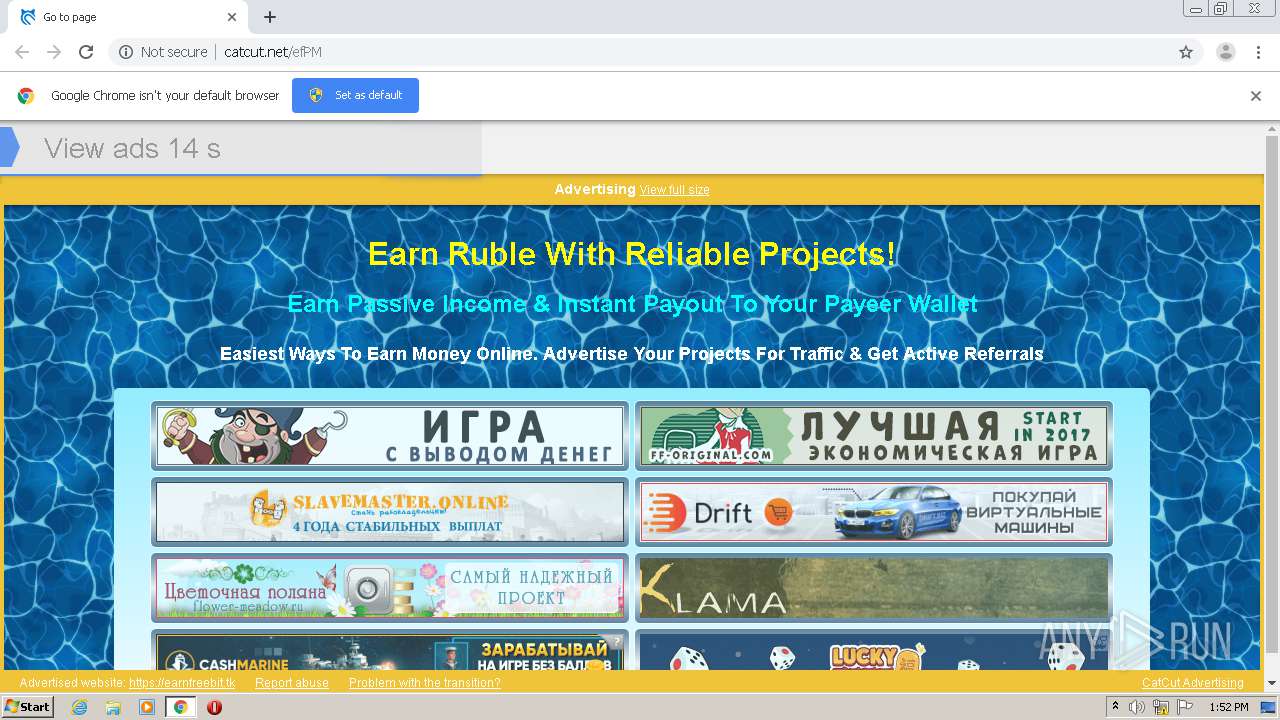
| Verdict: | Malicious activity |
| Analysis date: | August 07, 2020, 12:50:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3D3570DFB5965C8A31B6BD22E10F22B0 |
| SHA1: | AF9488C399CAE90719BBFE993843207710A17D4F |
| SHA256: | FA415B2D4F98ED3C024864FBD4E8860216E23FE6D4968609008529E7D422053B |
| SSDEEP: | 3:N1KdEVRIRin:CGz |
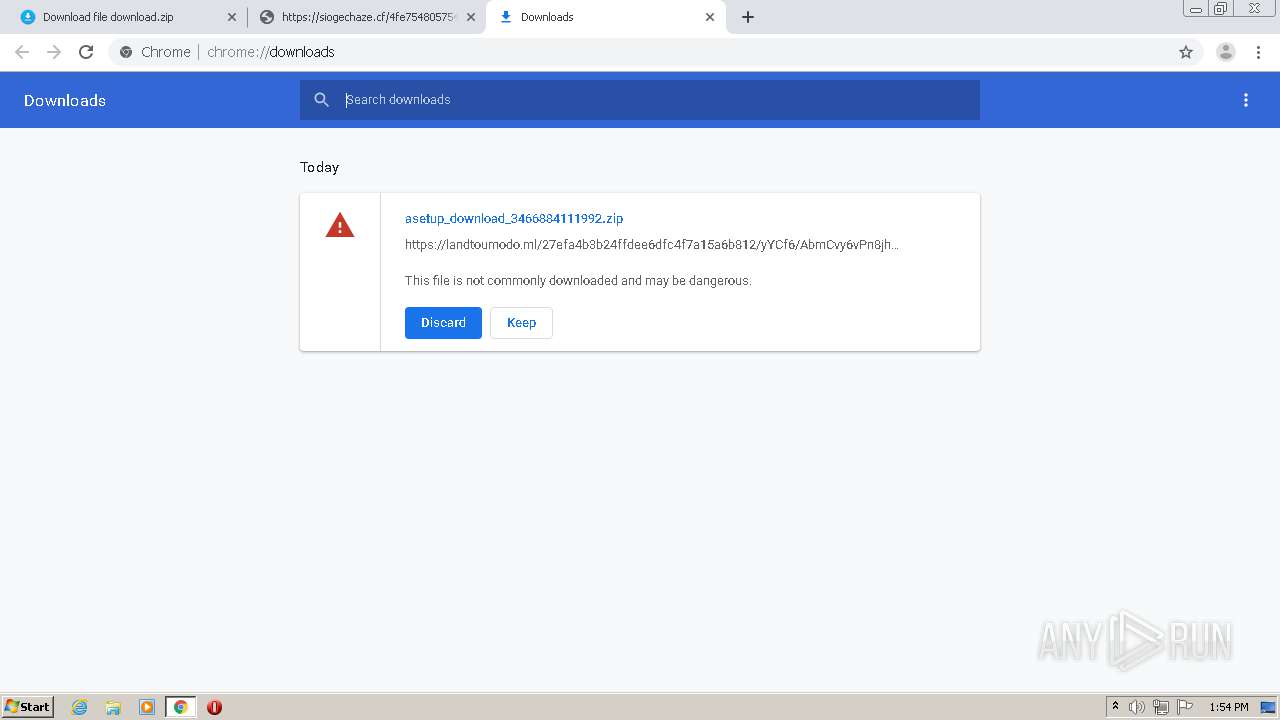
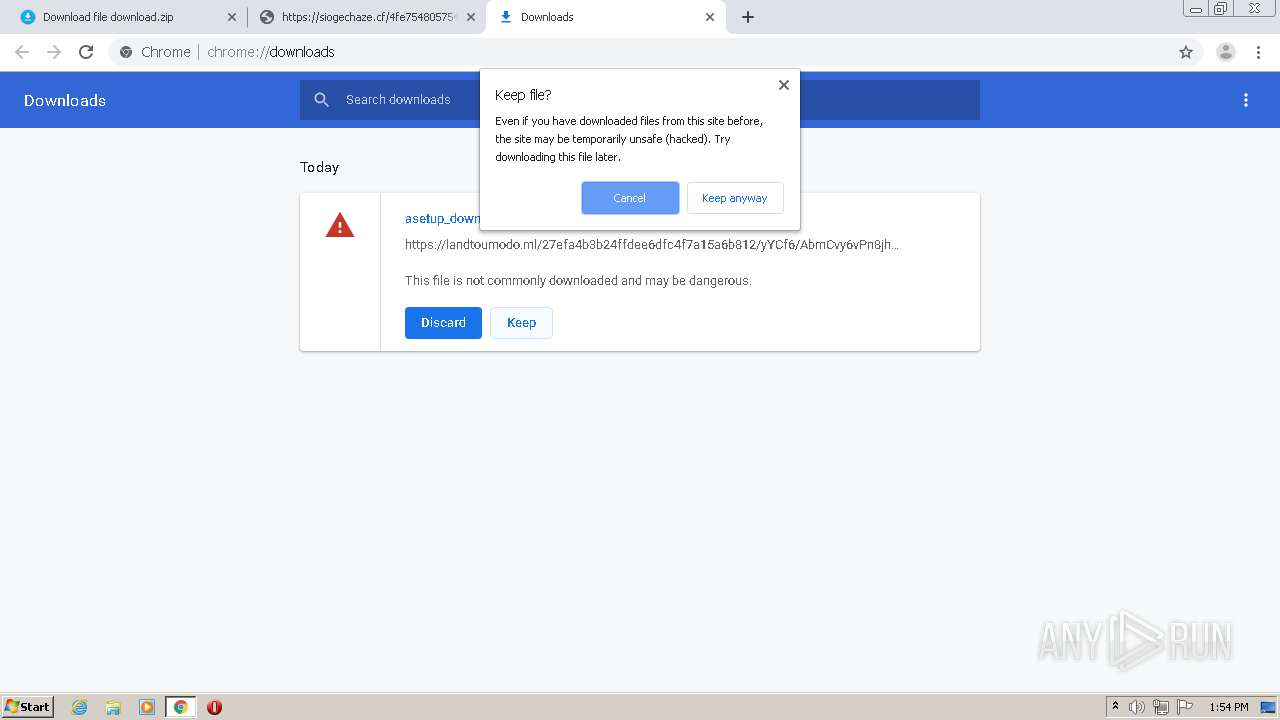
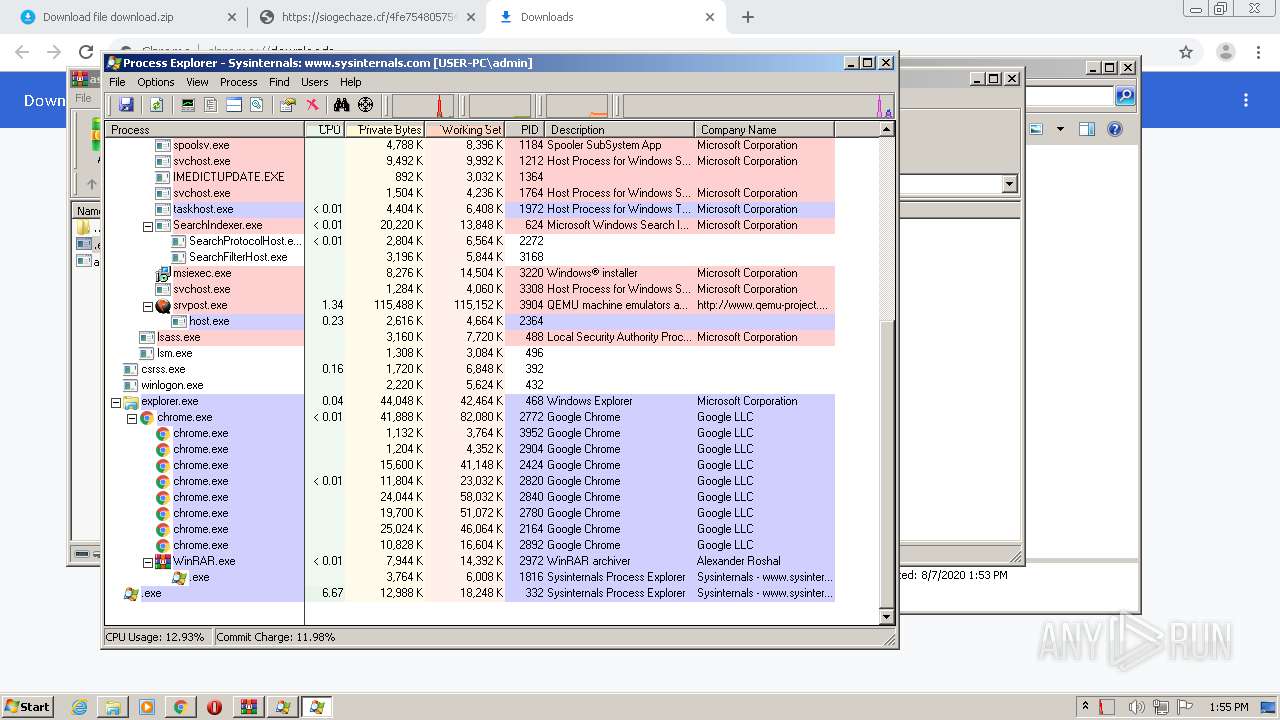
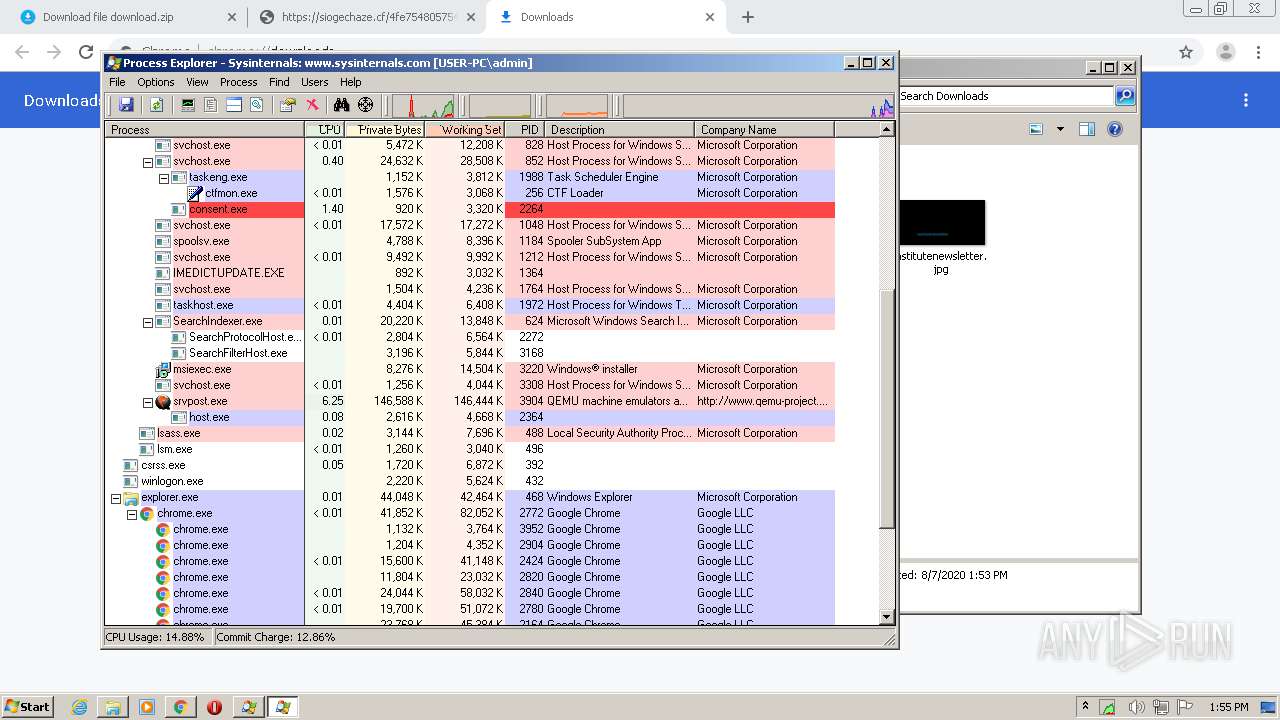
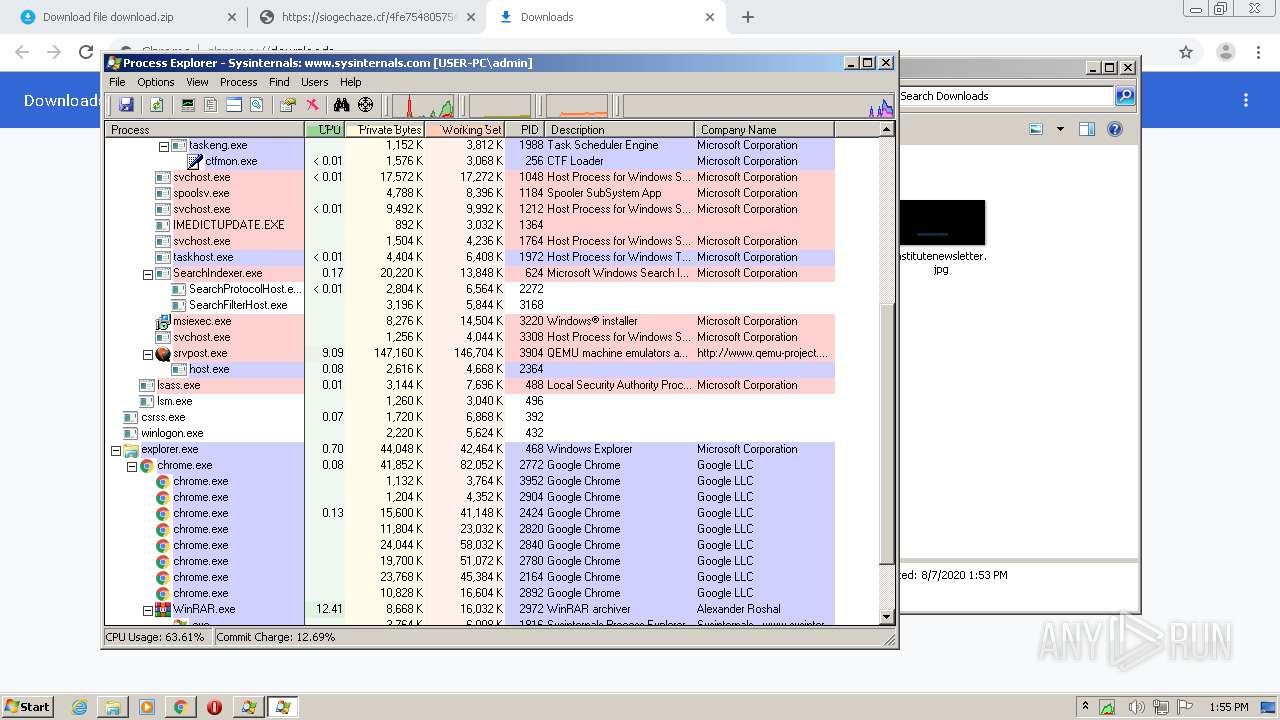
MALICIOUS
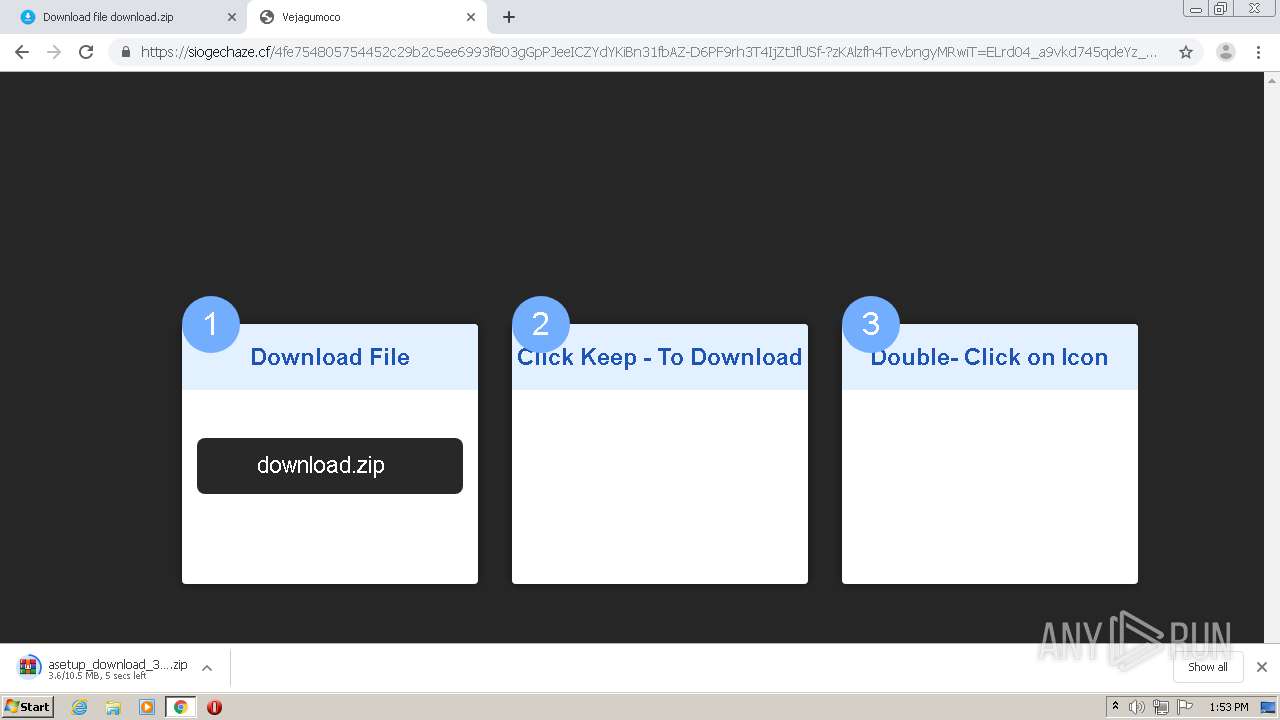
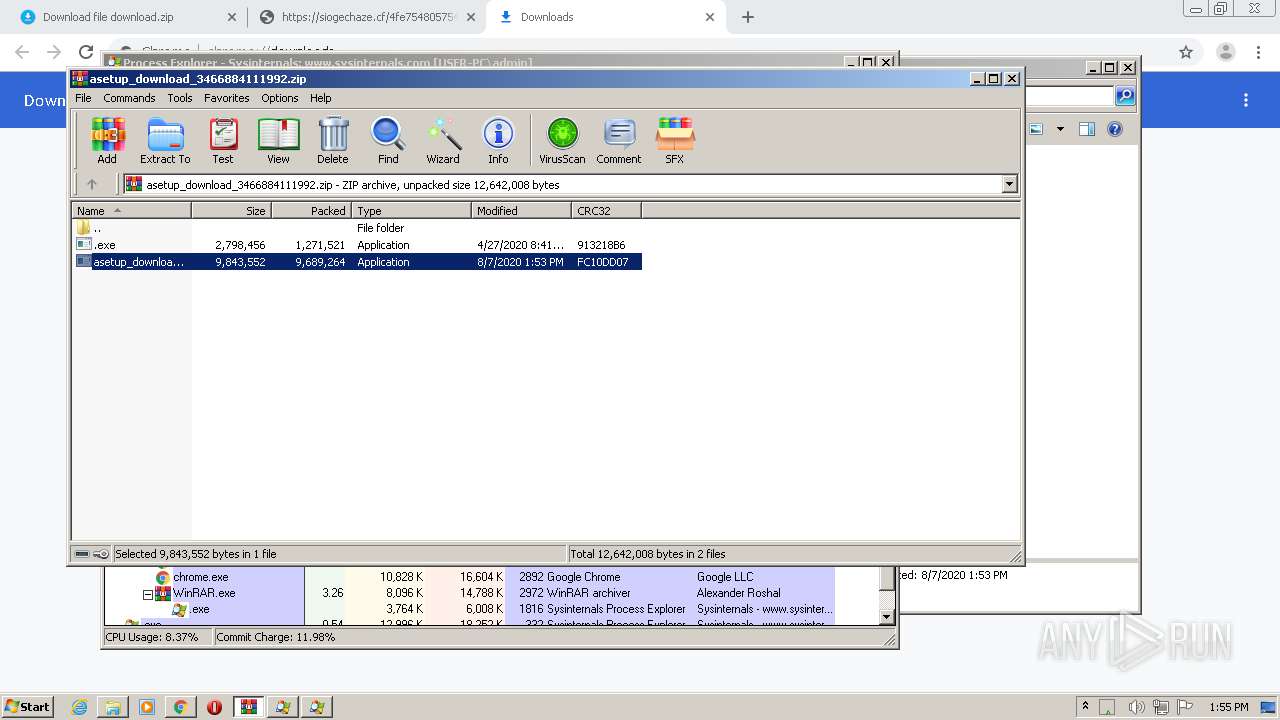
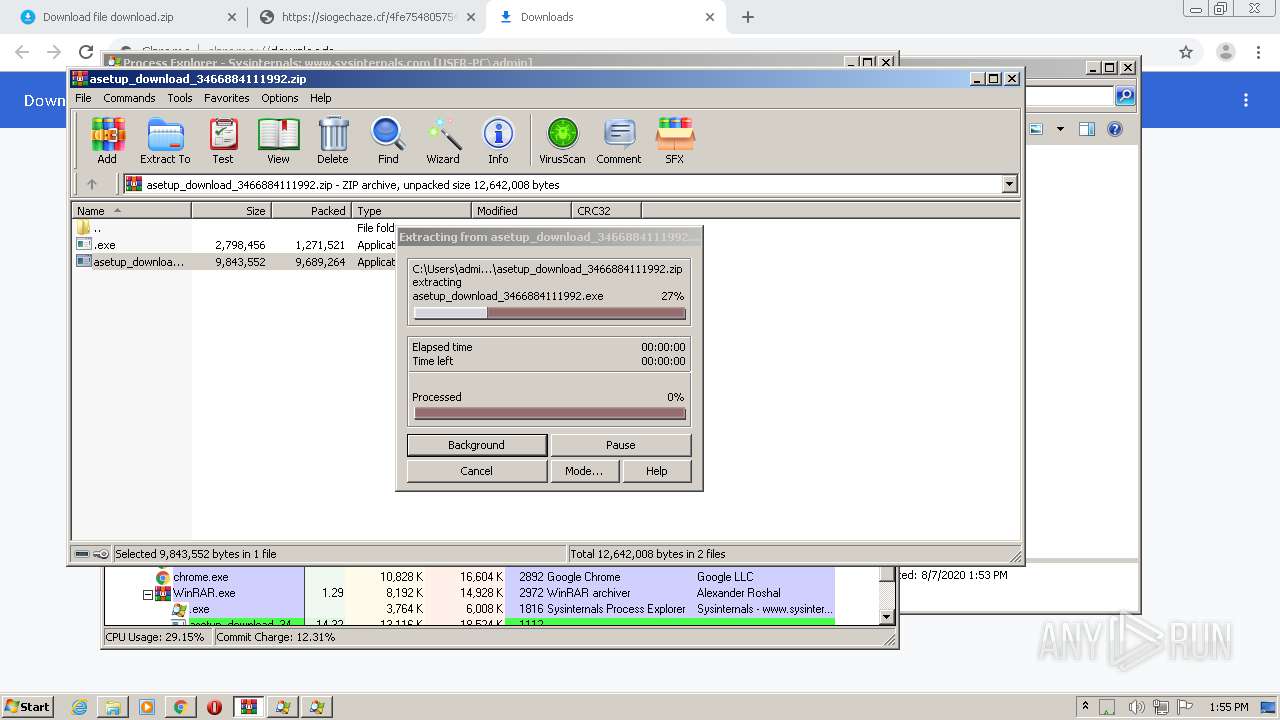
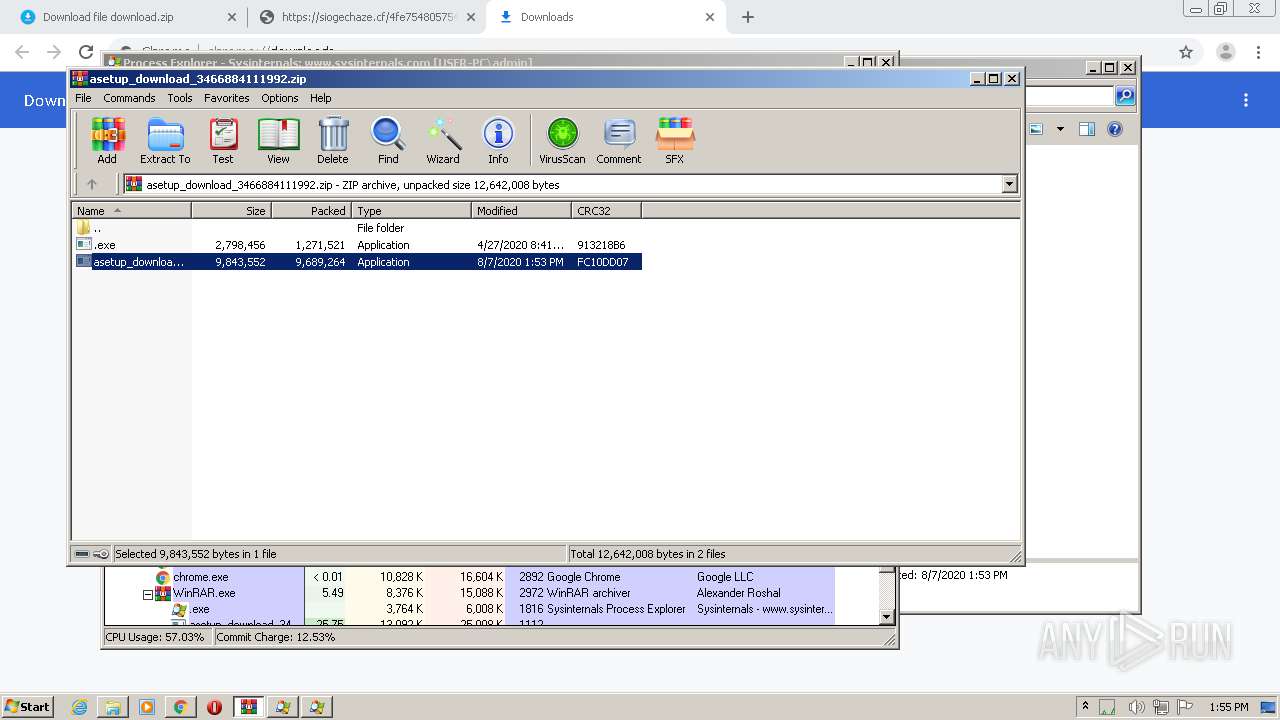
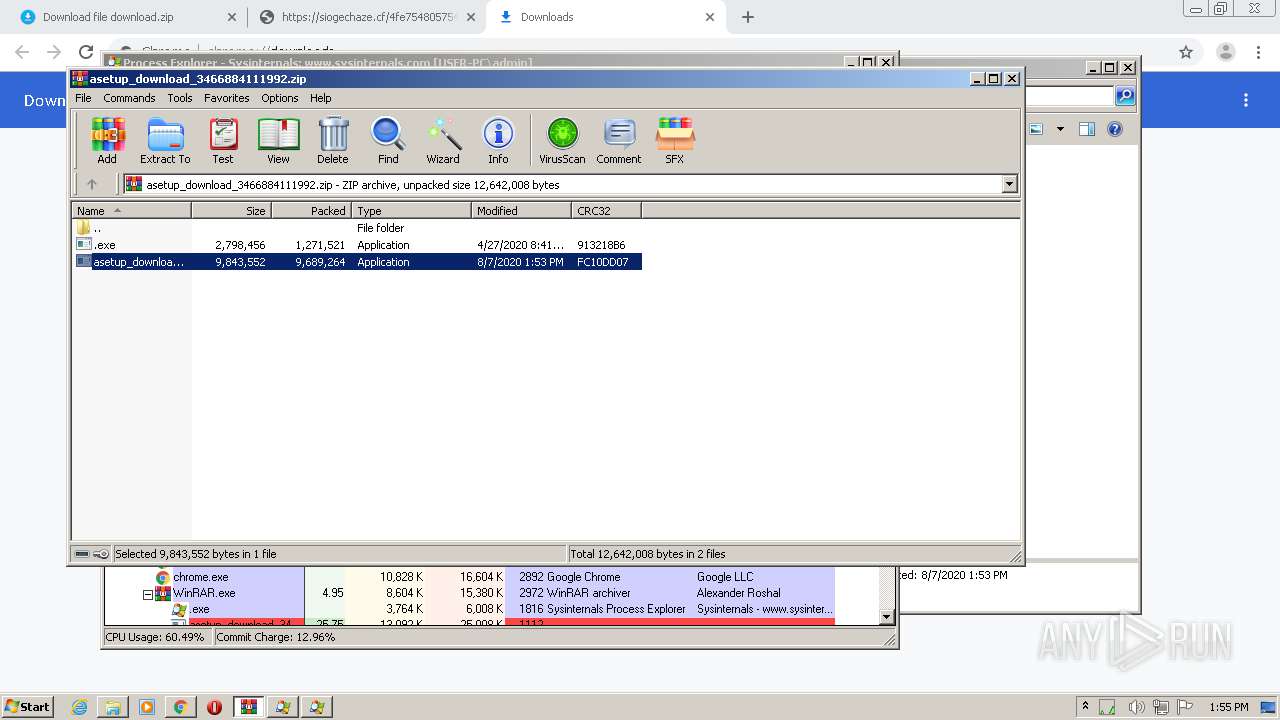
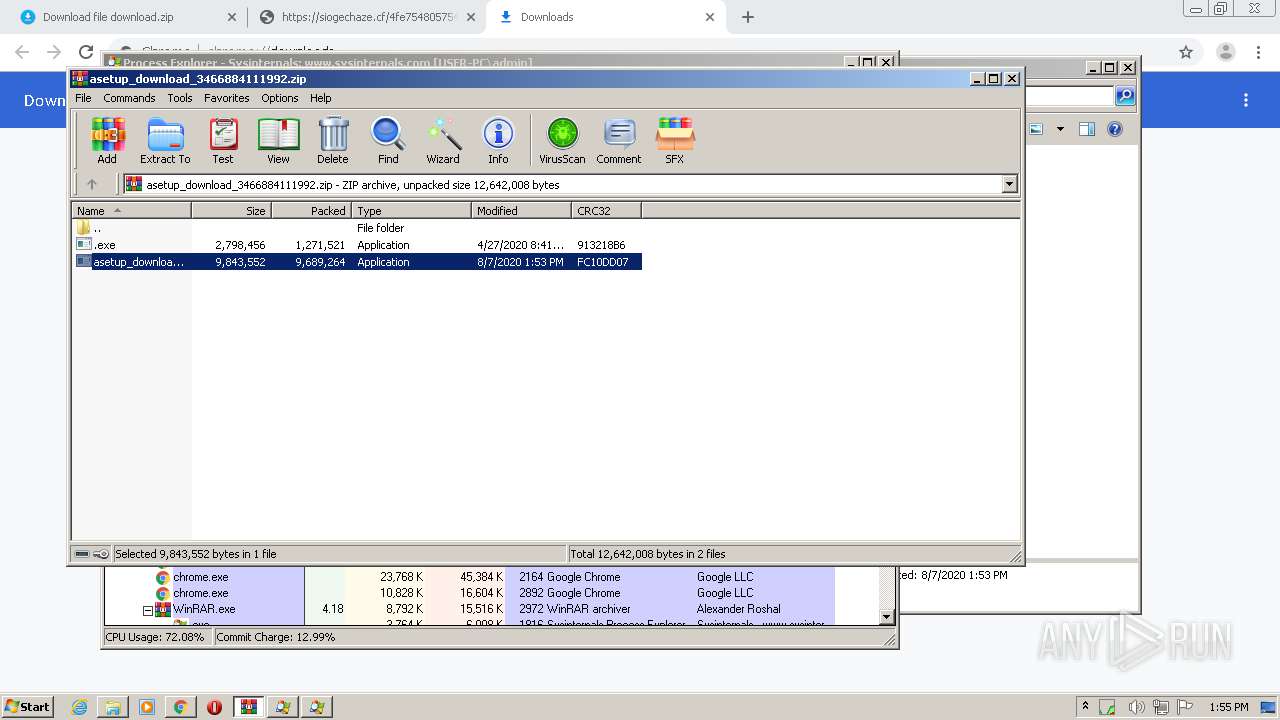
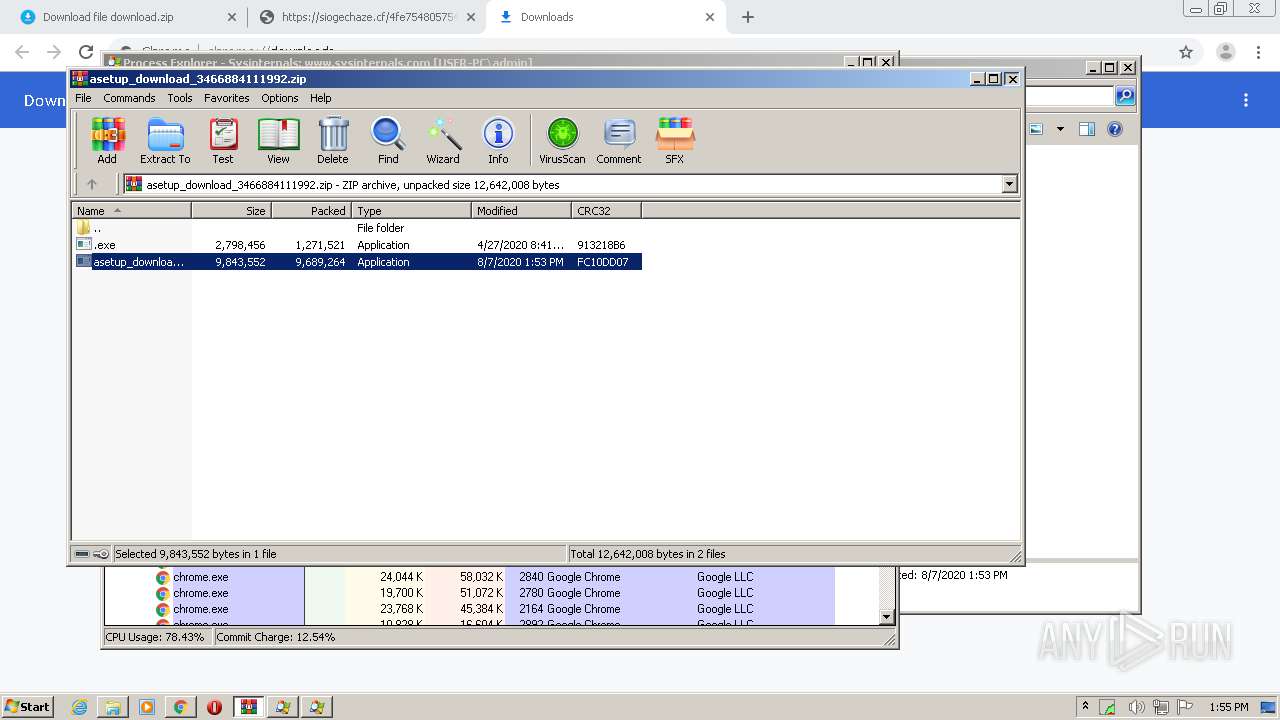
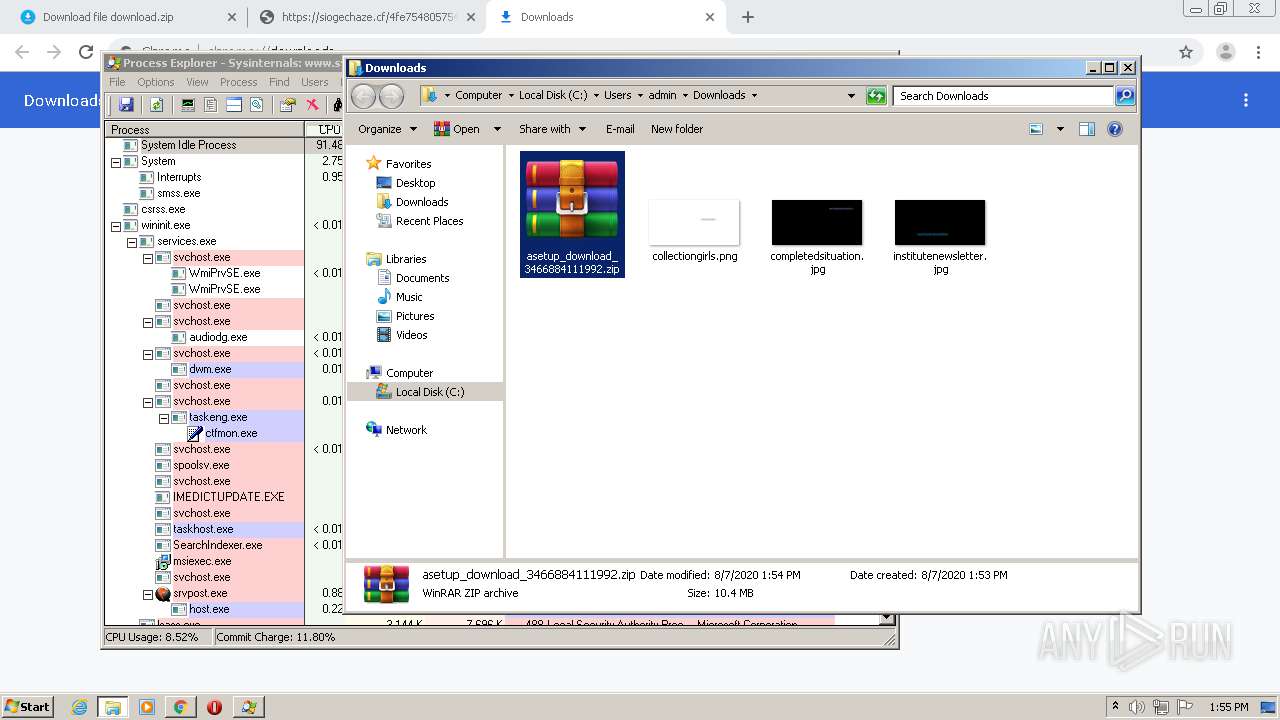
Application was dropped or rewritten from another process
- .exe (PID: 1816)
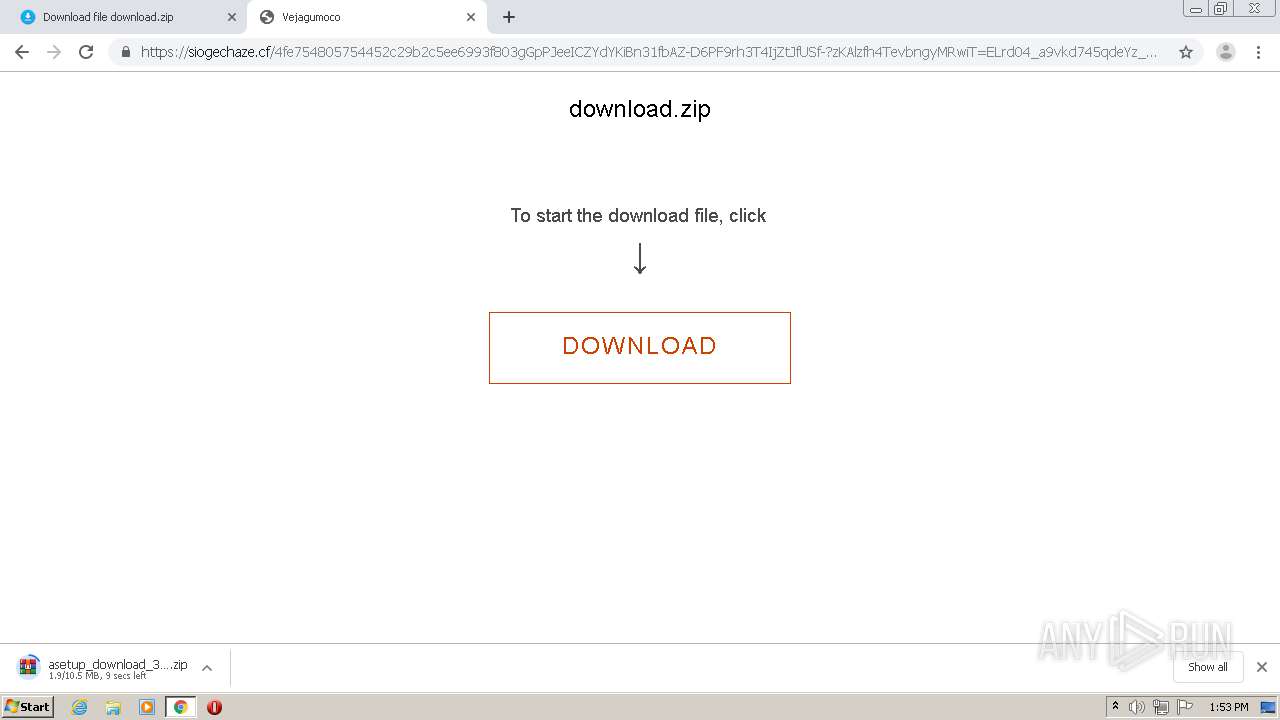
- asetup_download_3466884111992.exe (PID: 2968)
- asetup_download_3466884111992.exe (PID: 1840)
- asetup_download_3466884111992.exe (PID: 1296)
- .exe (PID: 332)
- asetup_download_3466884111992.exe (PID: 1900)
- asetup_download_3466884111992.exe (PID: 2248)
- asetup_download_3466884111992.exe (PID: 2416)
- asetup_download_3466884111992.exe (PID: 3448)
- asetup_download_3466884111992.exe (PID: 1112)
- asetup_download_3466884111992.exe (PID: 3916)
- asetup_download_3466884111992.exe (PID: 2584)
- asetup_download_3466884111992.exe (PID: 3096)
- asetup_download_3466884111992.exe (PID: 3924)
- asetup_download_3466884111992.exe (PID: 180)
- asetup_download_3466884111992.exe (PID: 2140)
- asetup_download_3466884111992.exe (PID: 2288)
- asetup_download_3466884111992.exe (PID: 3392)
- asetup_download_3466884111992.exe (PID: 1068)
- asetup_download_3466884111992.exe (PID: 3252)
- asetup_download_3466884111992.exe (PID: 3012)
- asetup_download_3466884111992.exe (PID: 3608)
Loads the Task Scheduler COM API
- .exe (PID: 332)
- .exe (PID: 1816)
SUSPICIOUS
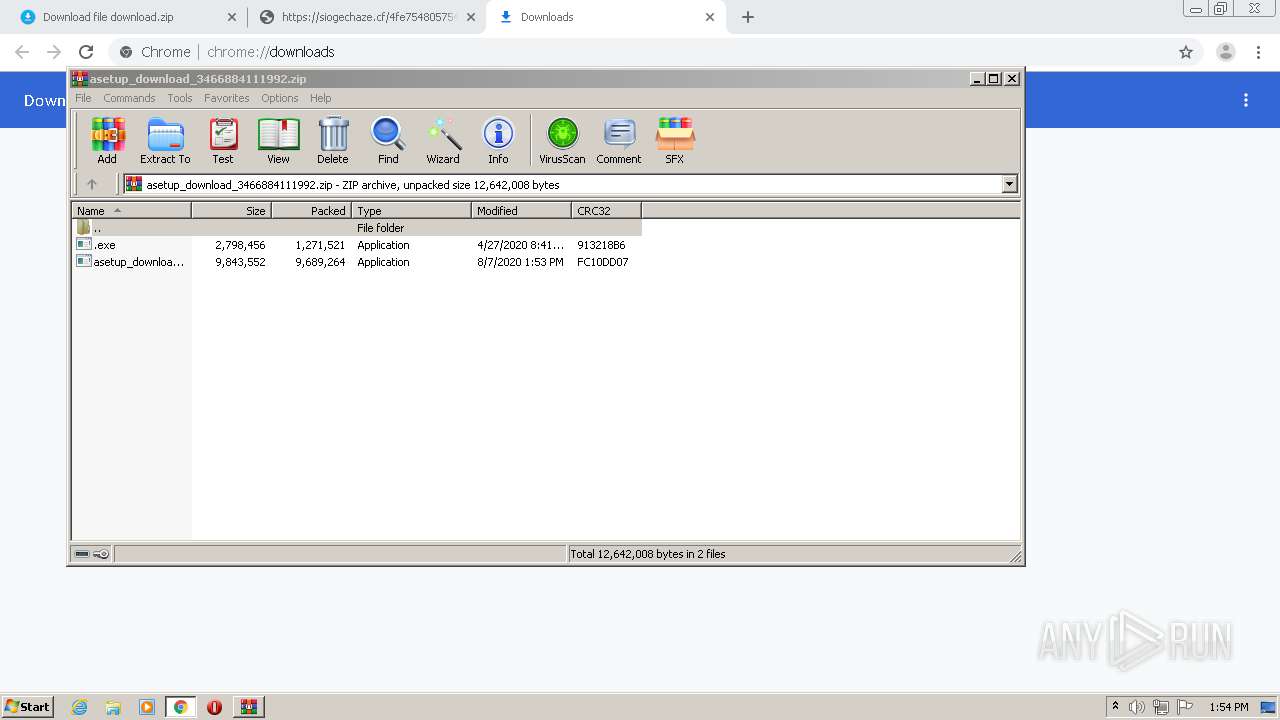
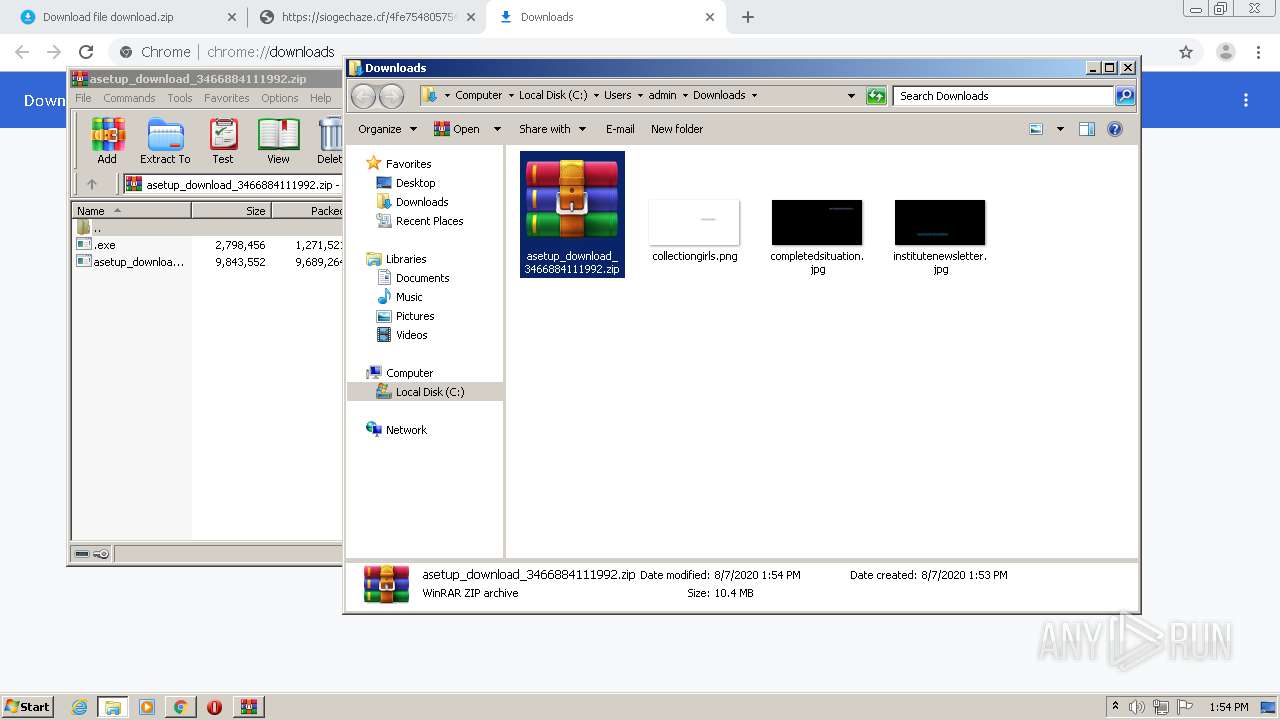
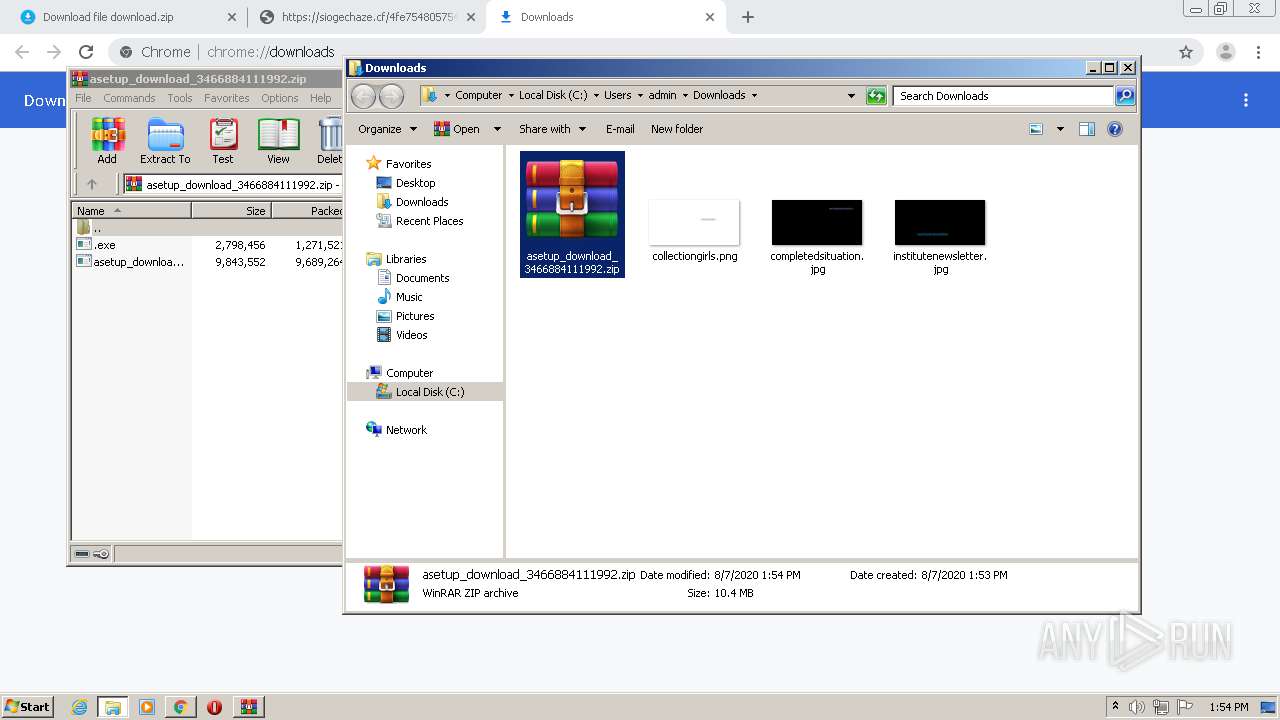
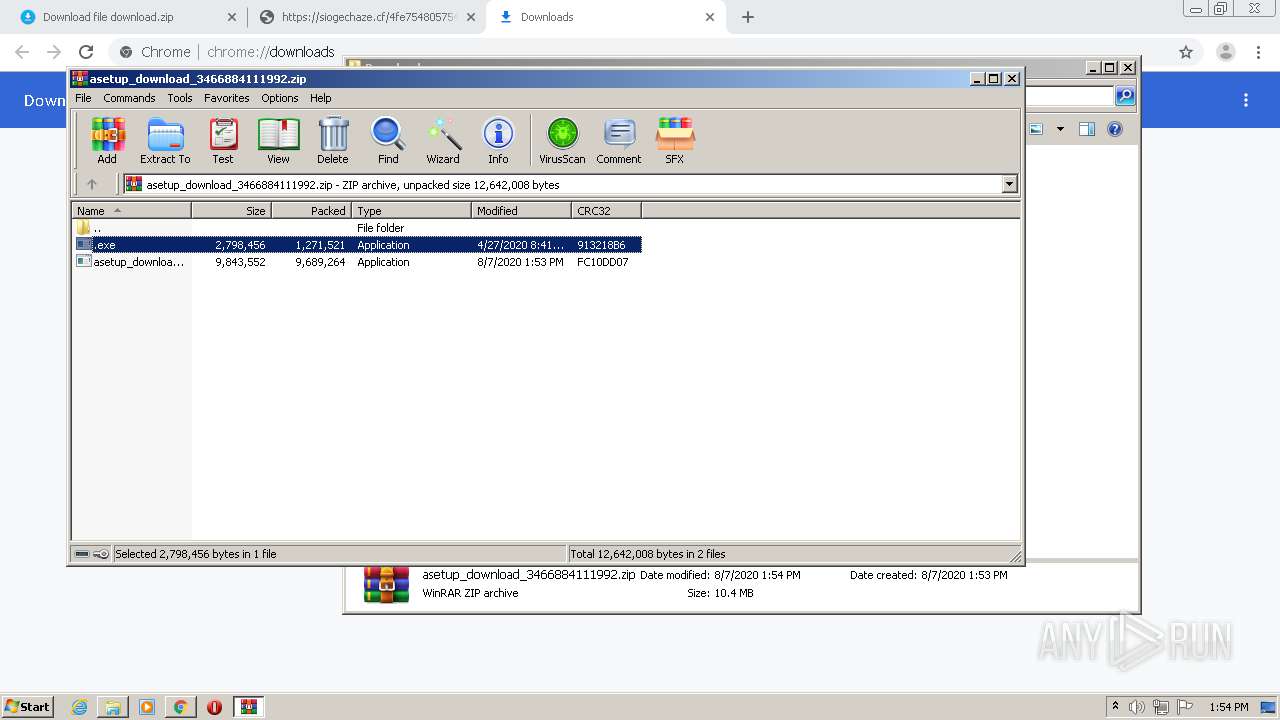
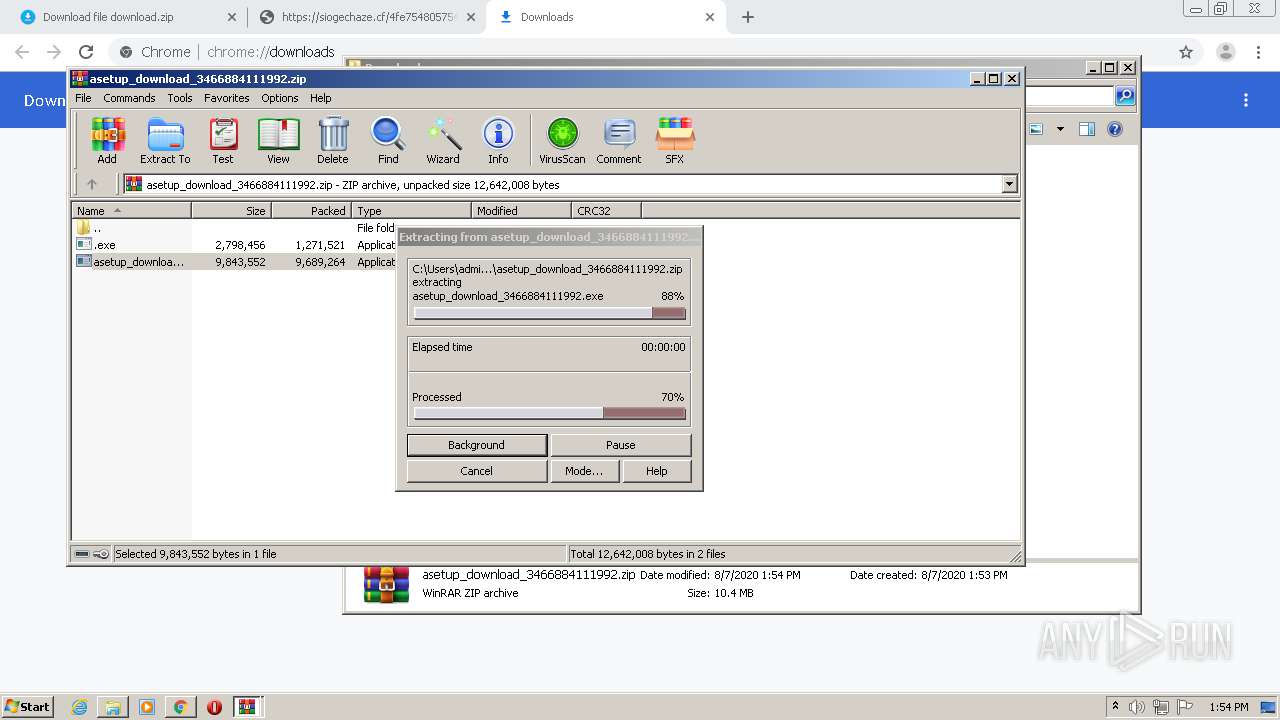
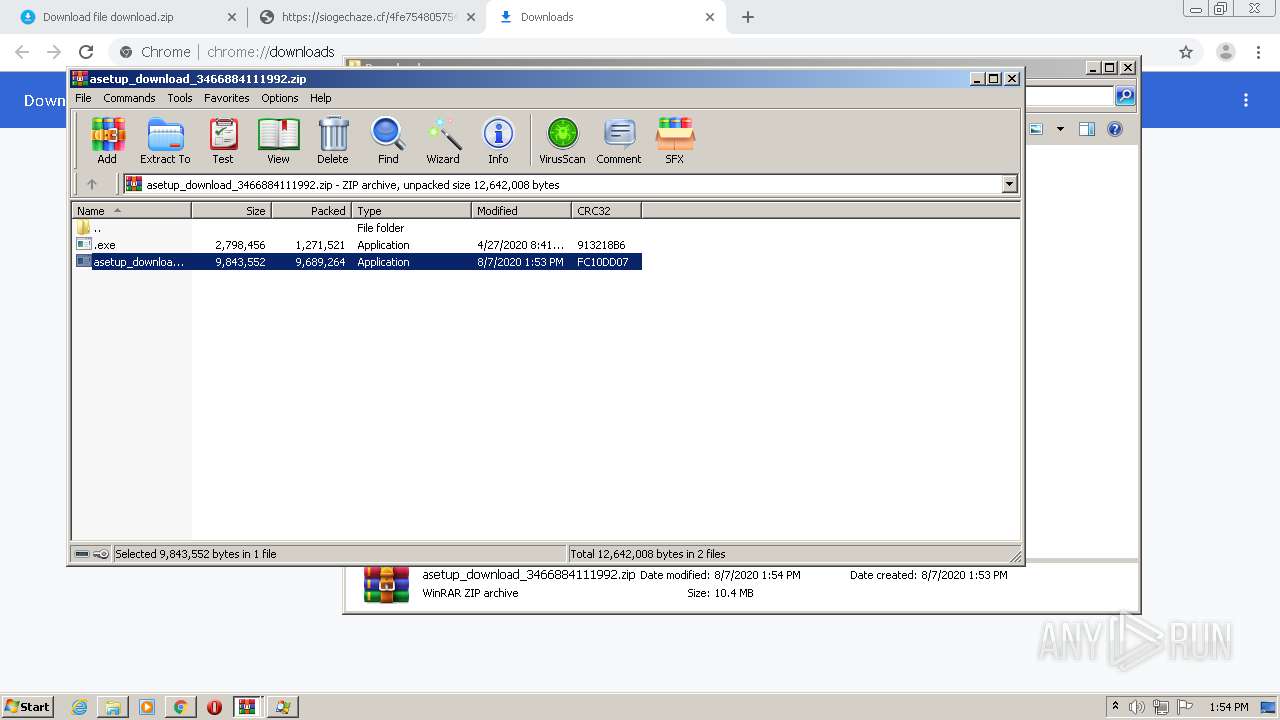
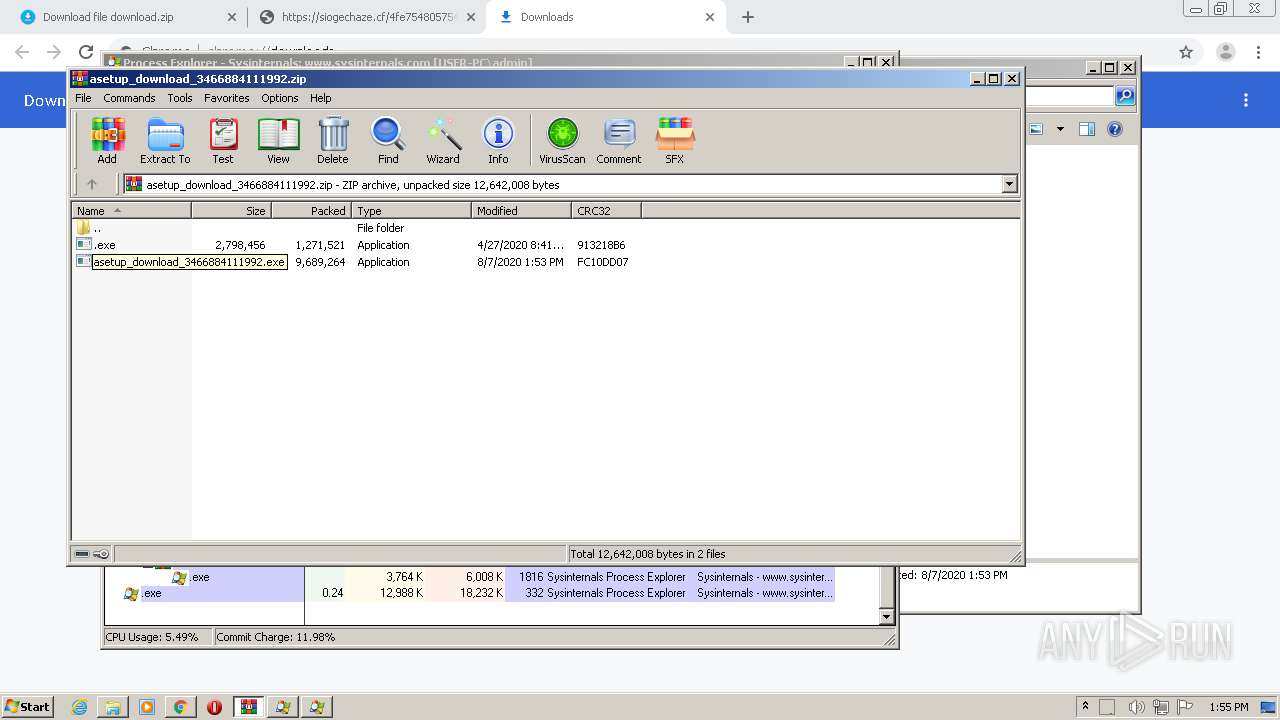
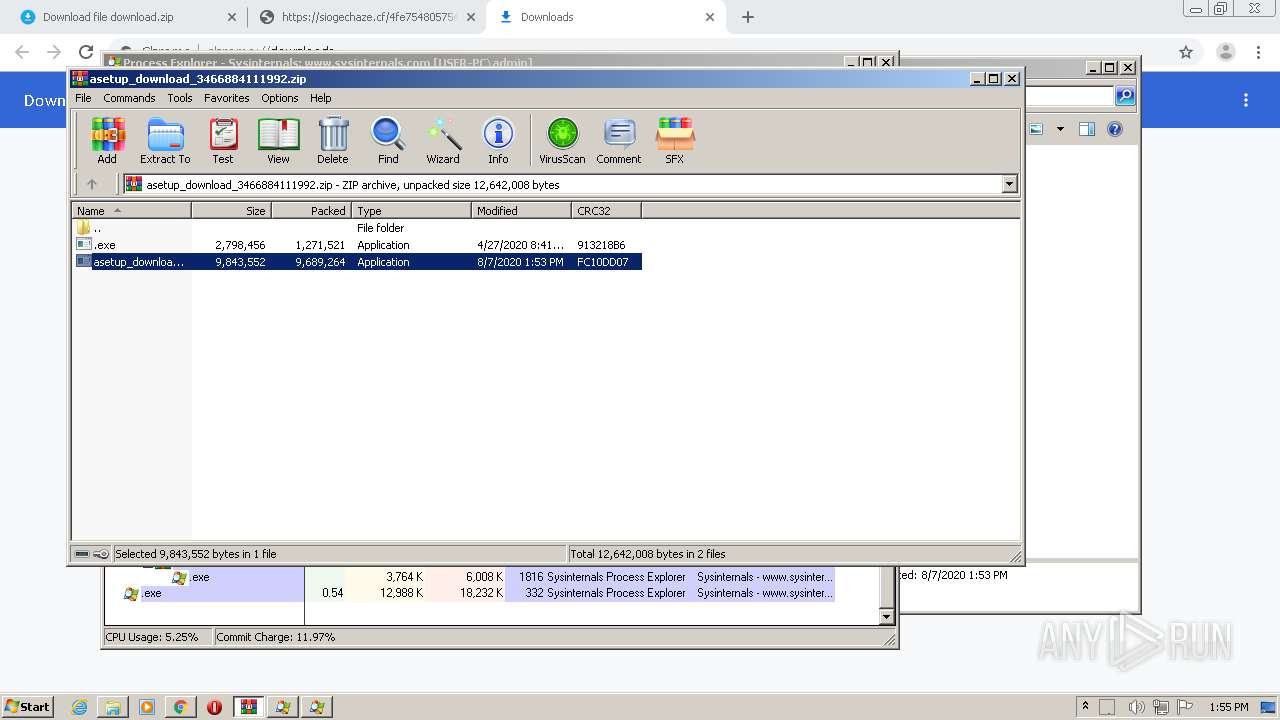
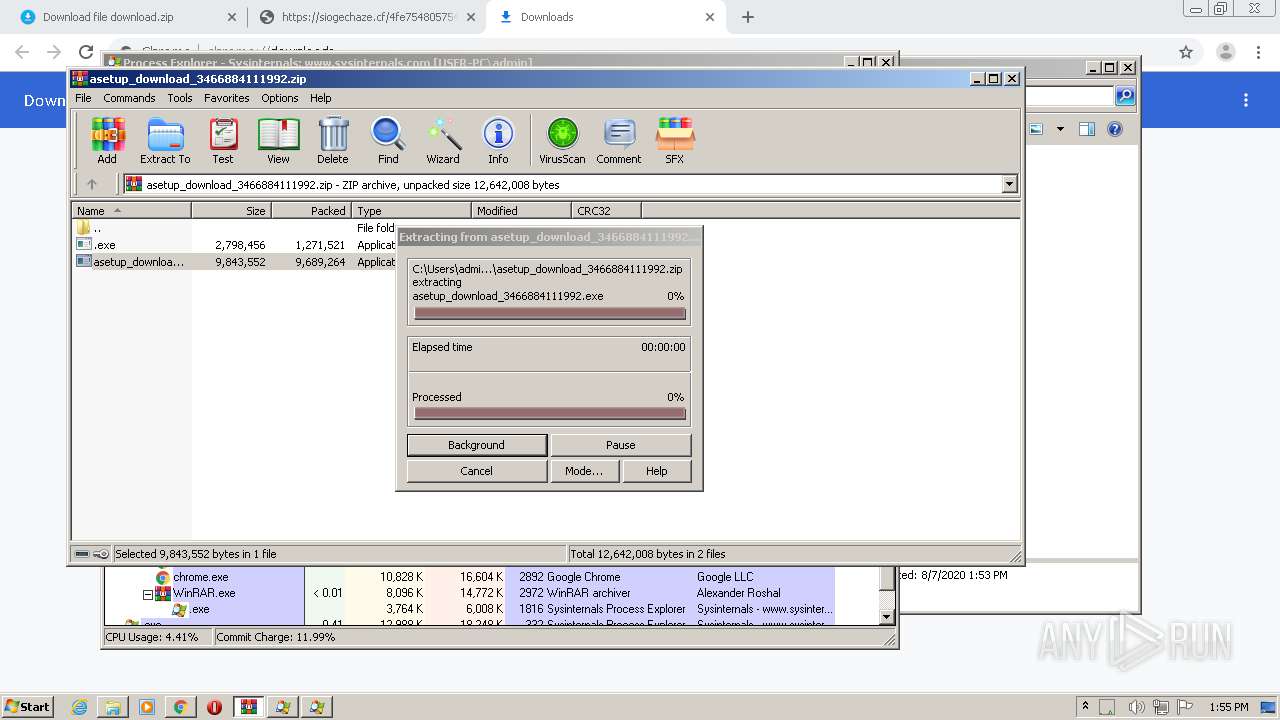
Executable content was dropped or overwritten
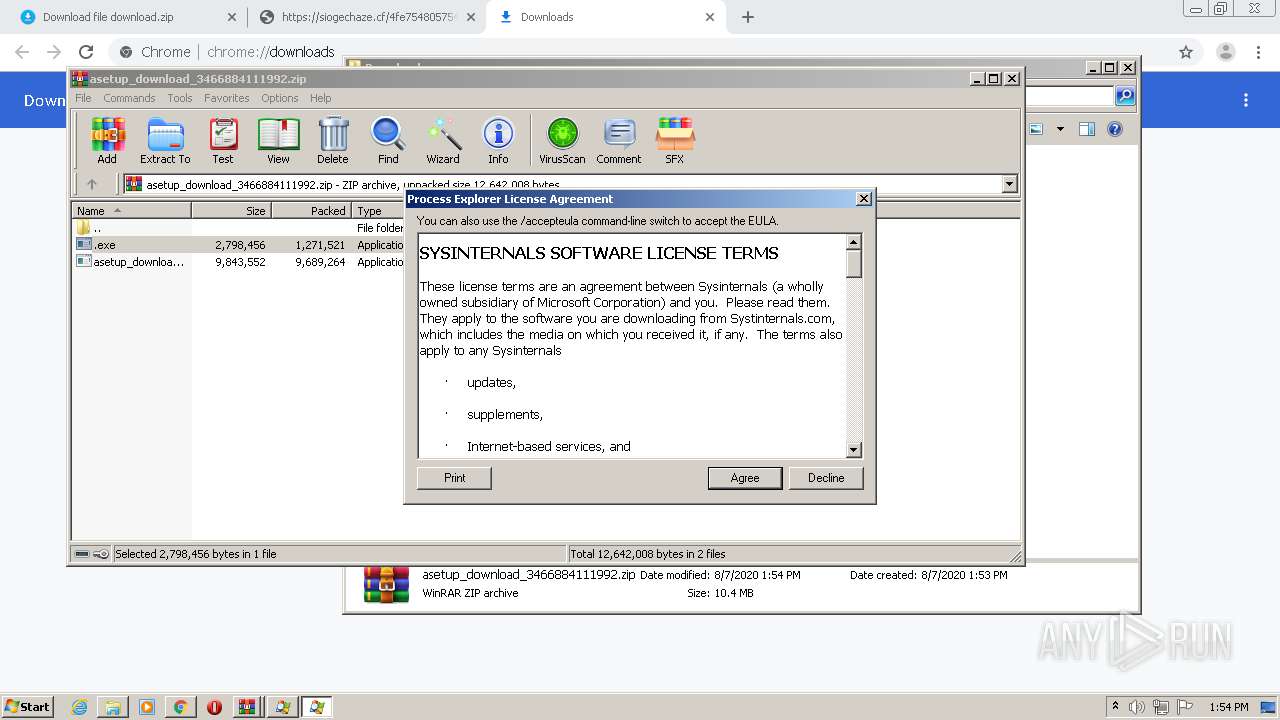
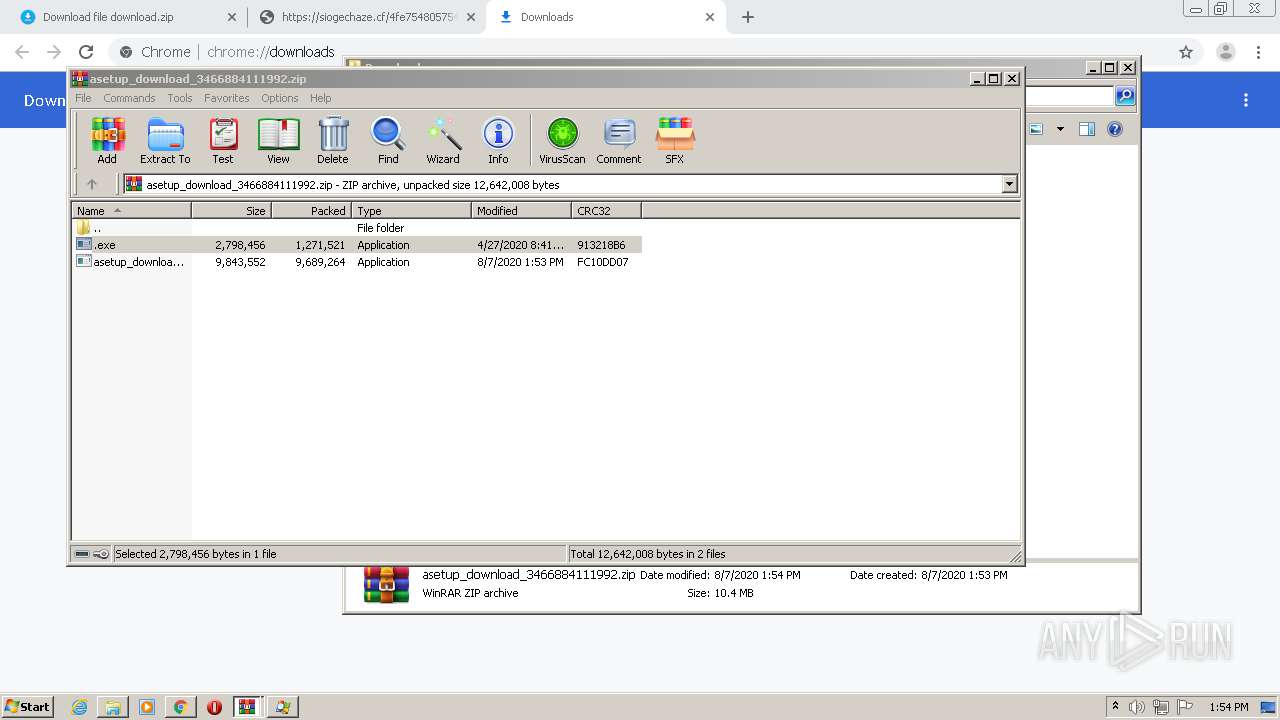
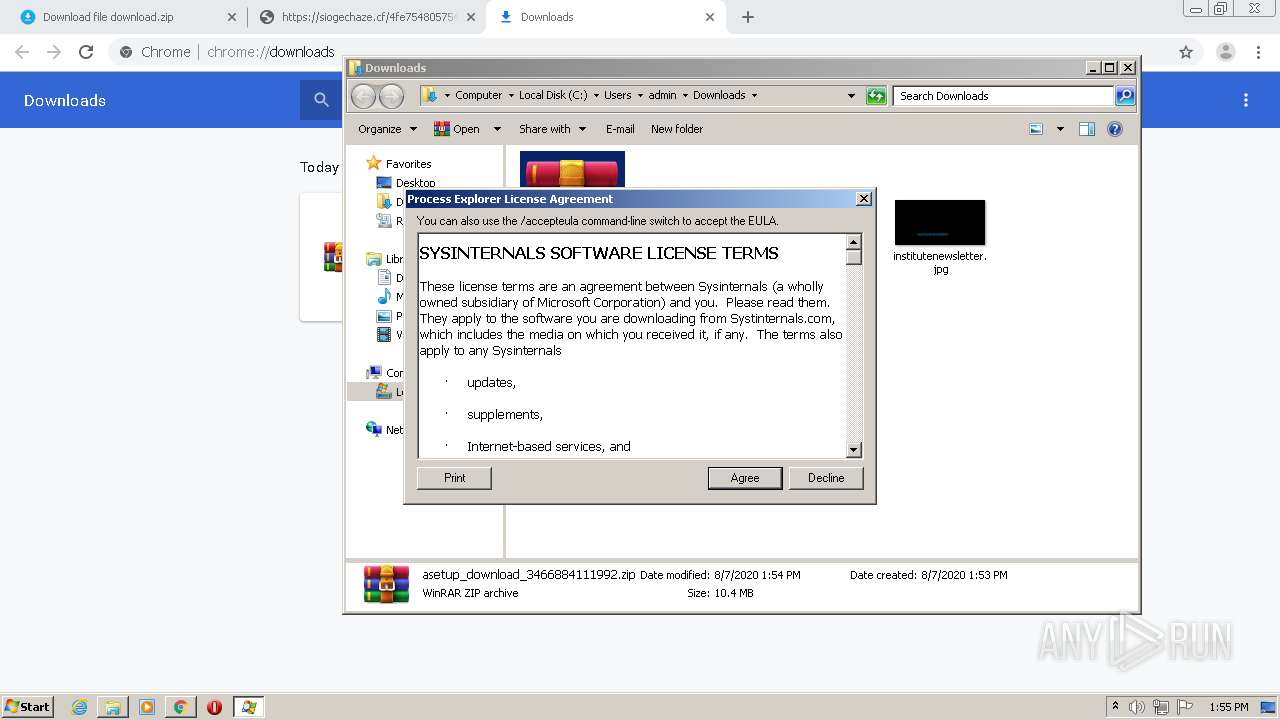
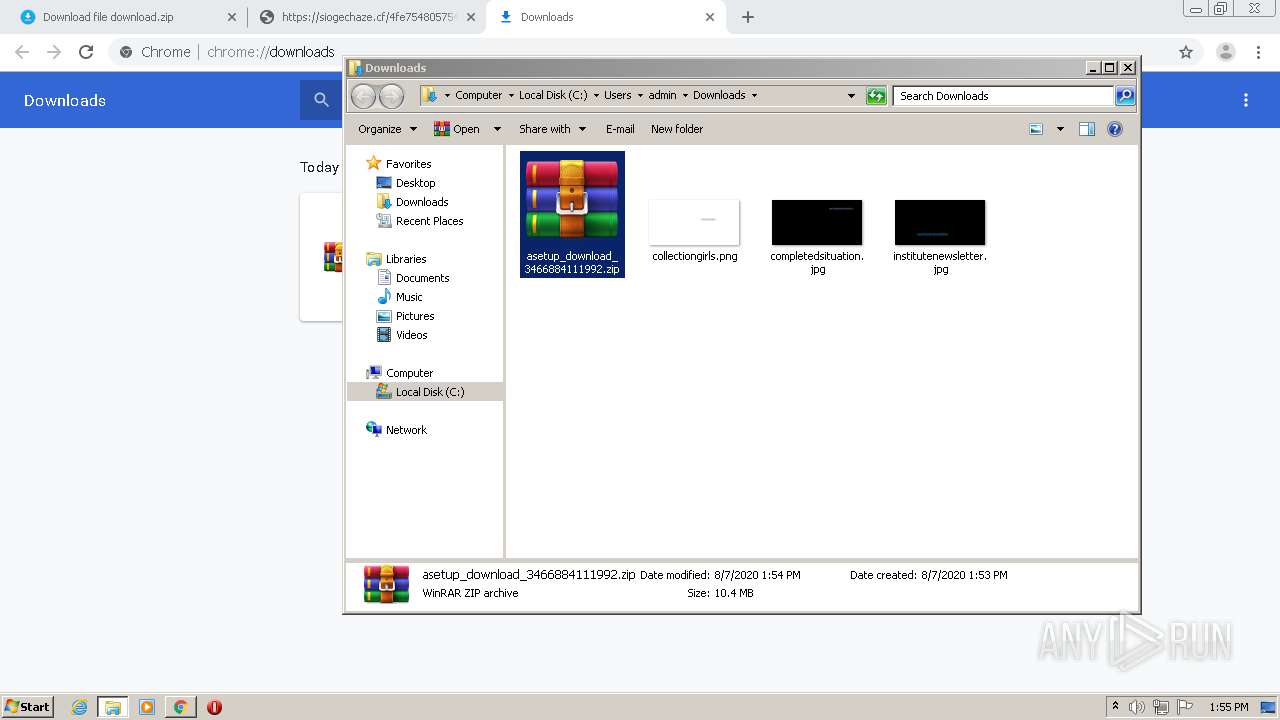
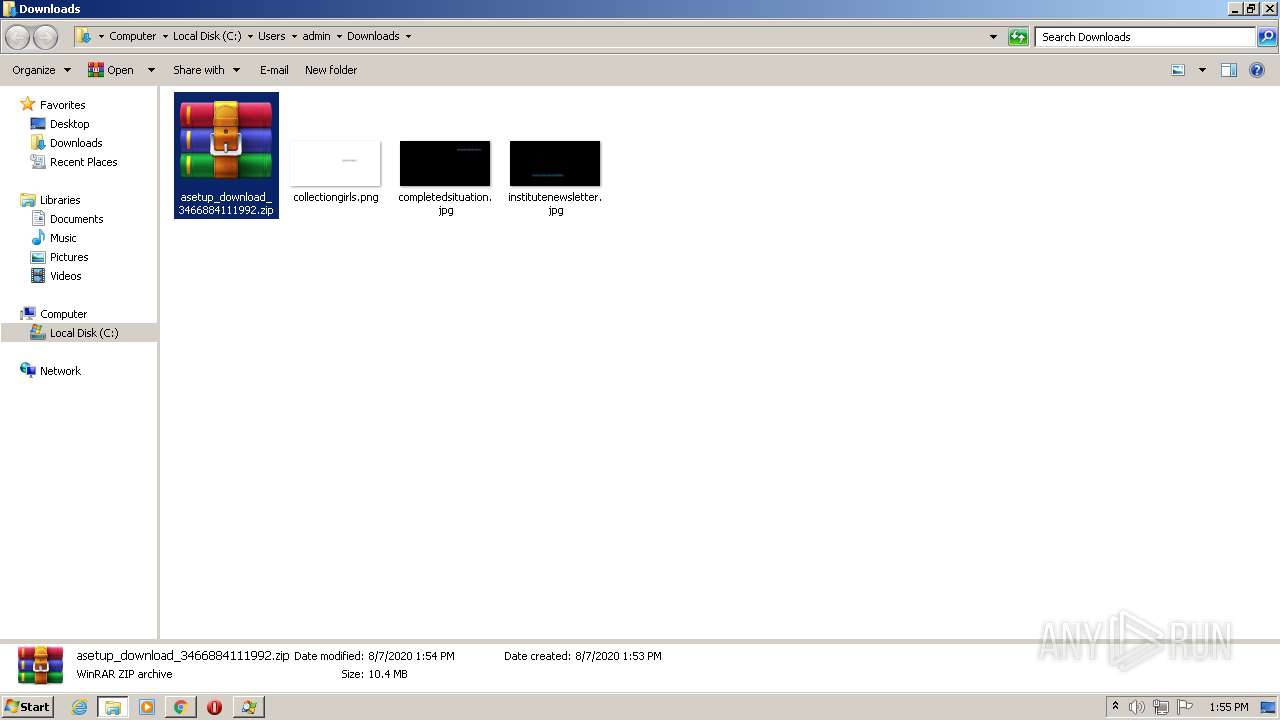
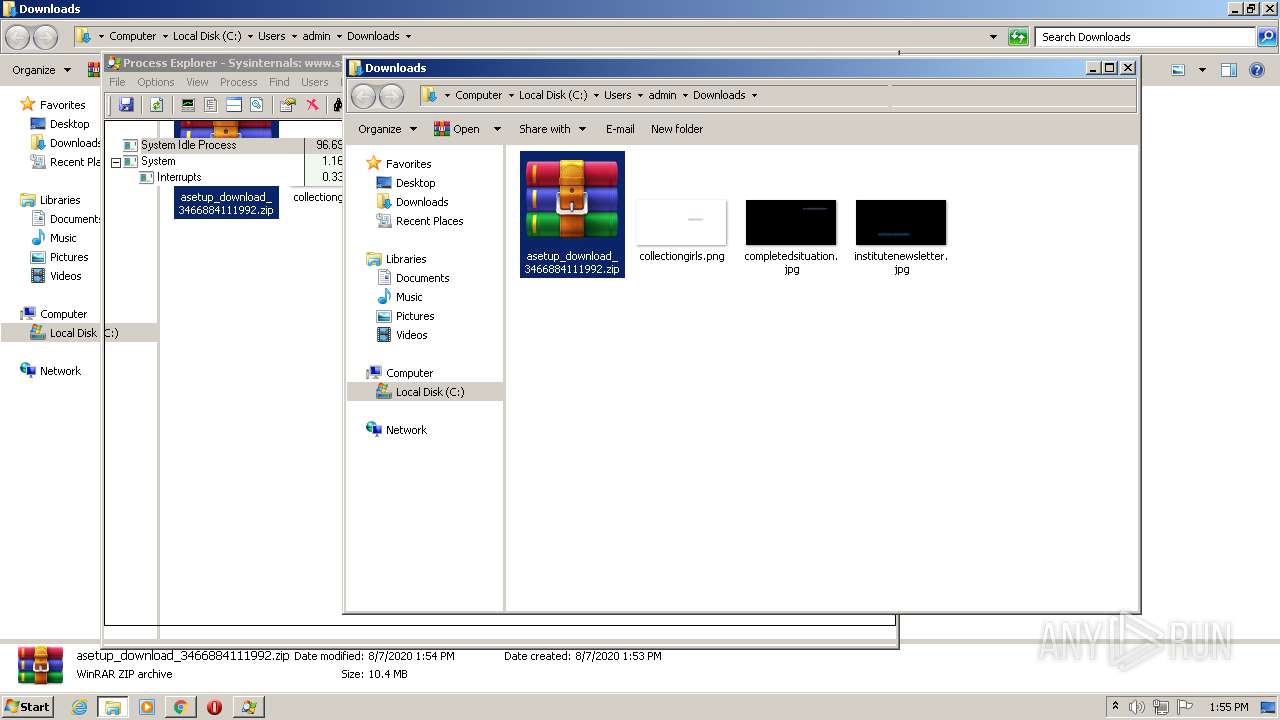
- WinRAR.exe (PID: 2368)
- WinRAR.exe (PID: 2972)
Executed via COM
- DllHost.exe (PID: 380)
INFO
Application launched itself
- chrome.exe (PID: 2772)
Reads the hosts file
- chrome.exe (PID: 2772)
- chrome.exe (PID: 2820)
Reads Internet Cache Settings
- chrome.exe (PID: 2772)
Manual execution by user
- WinRAR.exe (PID: 2368)
Reads settings of System Certificates
- .exe (PID: 1816)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2820)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
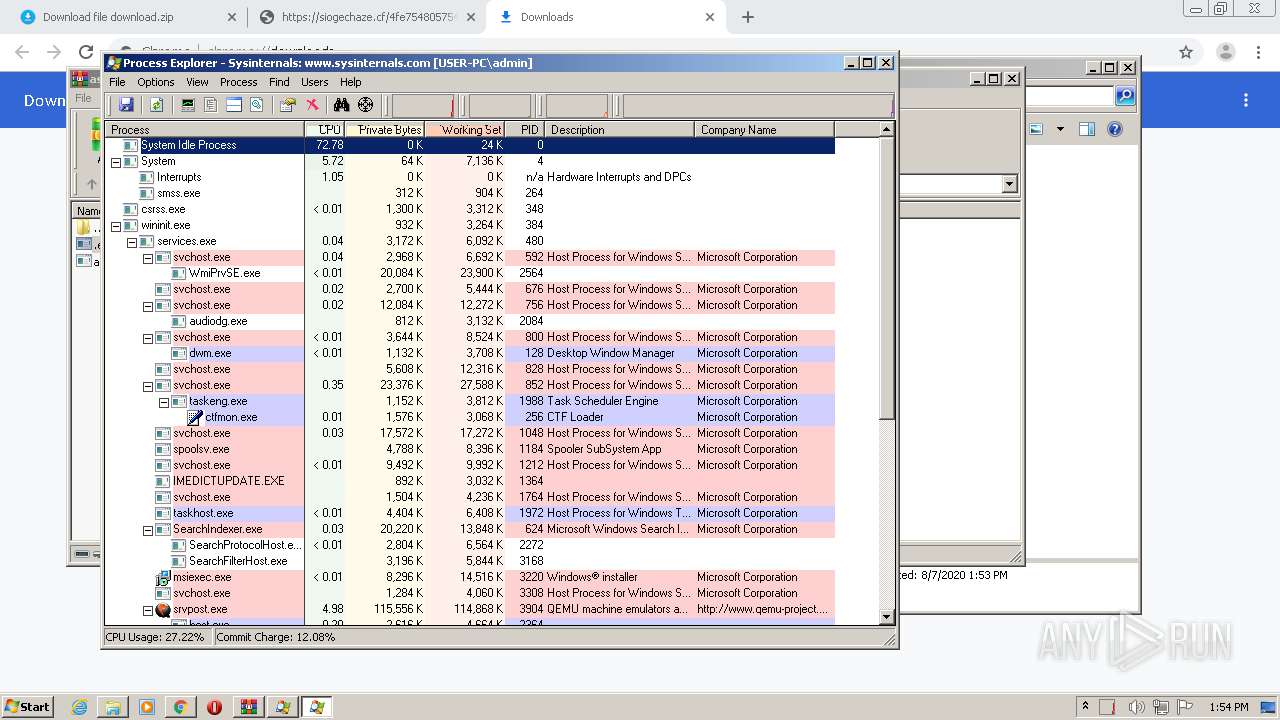
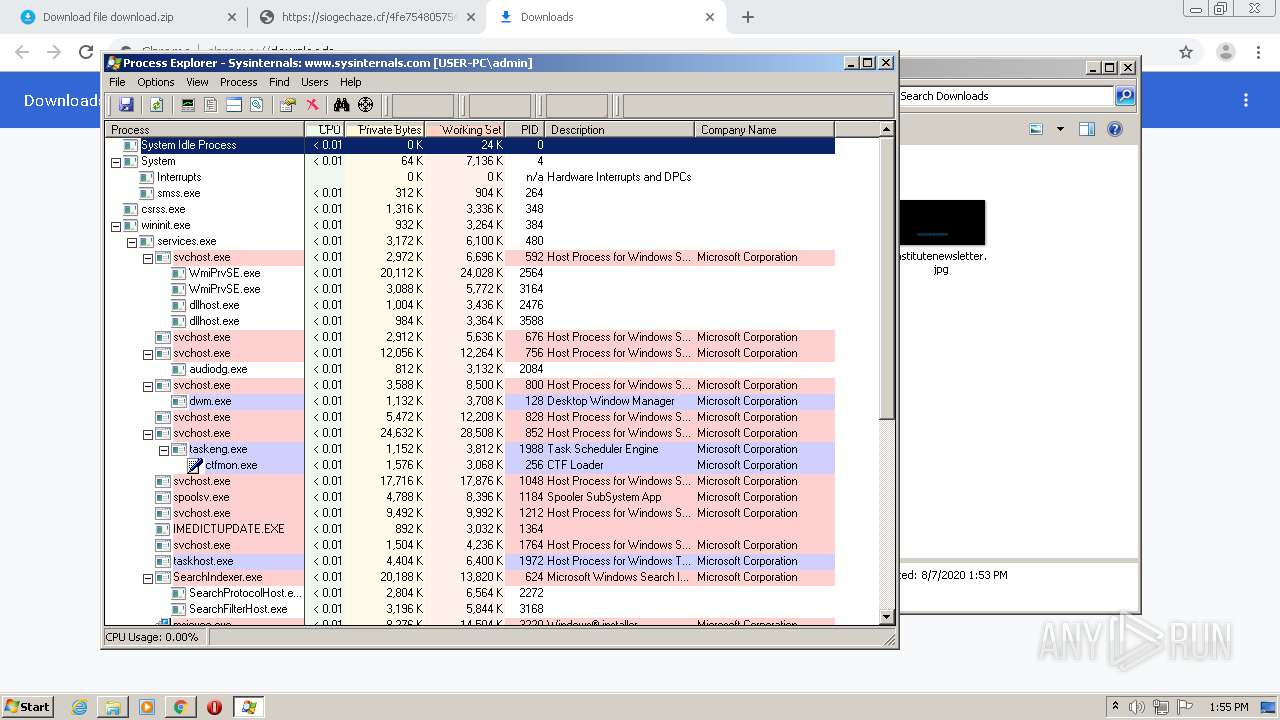
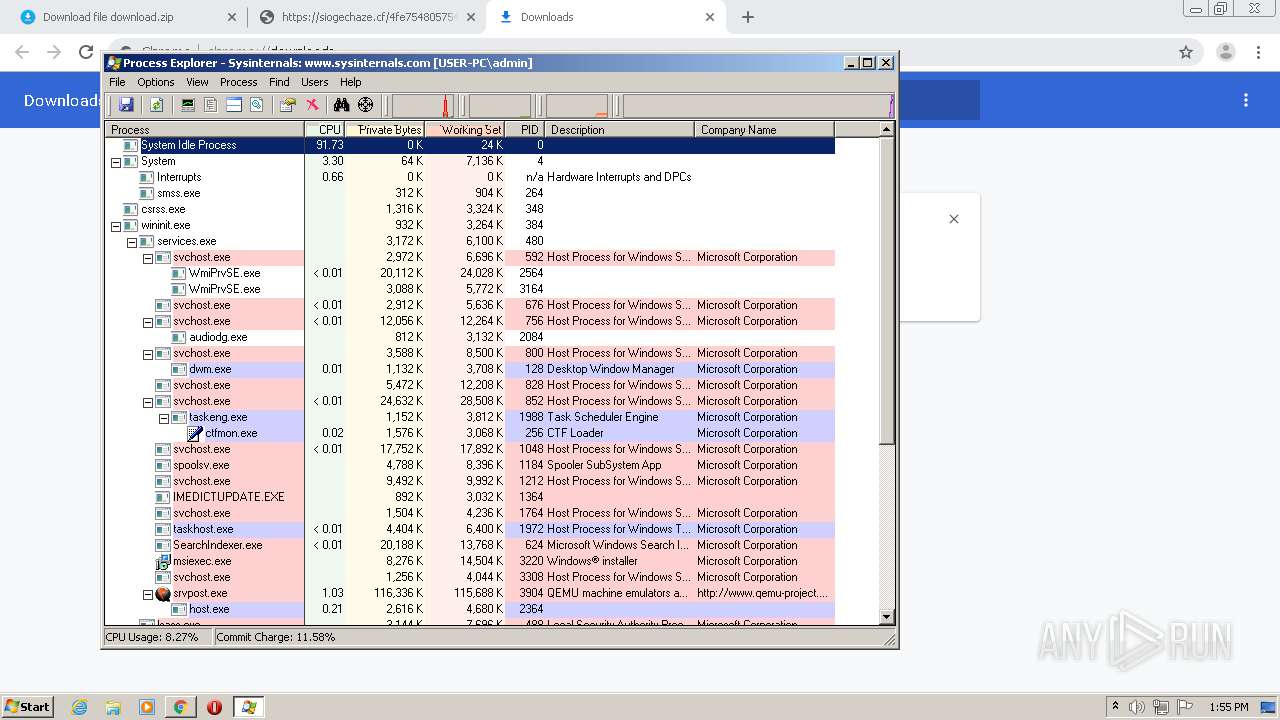
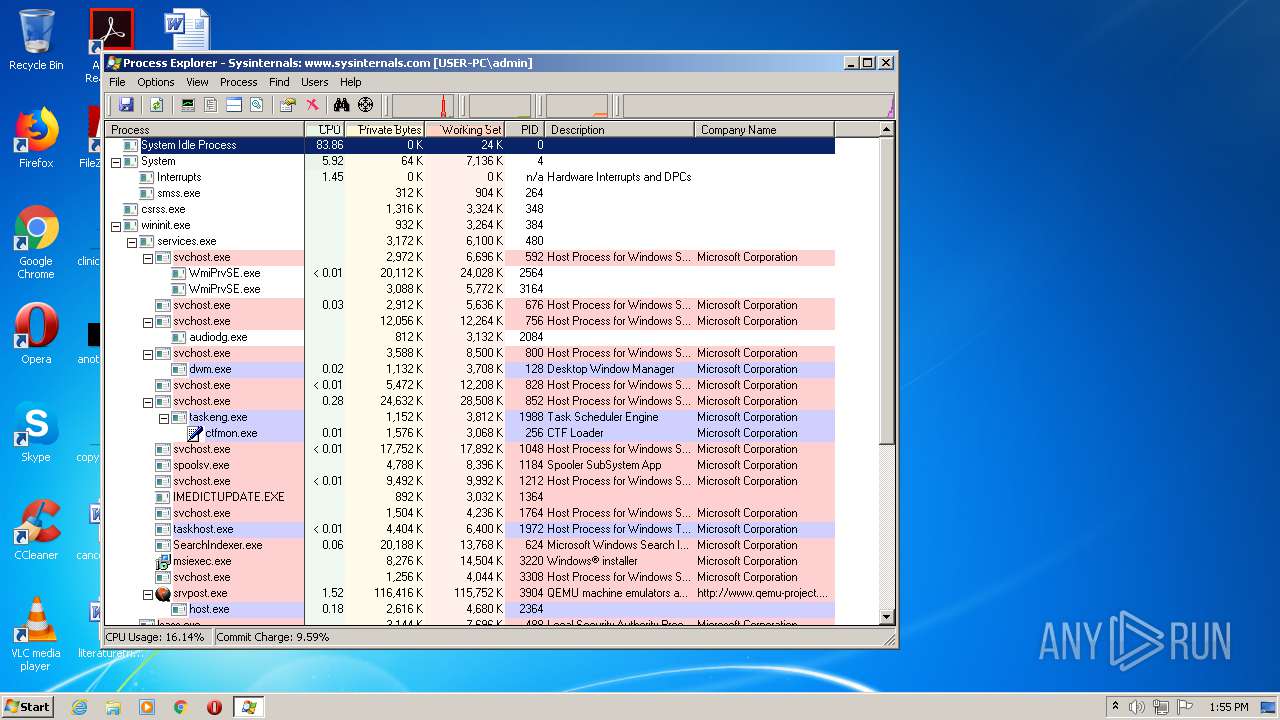
Total processes
121
Monitored processes
59
Malicious processes
8
Suspicious processes
1
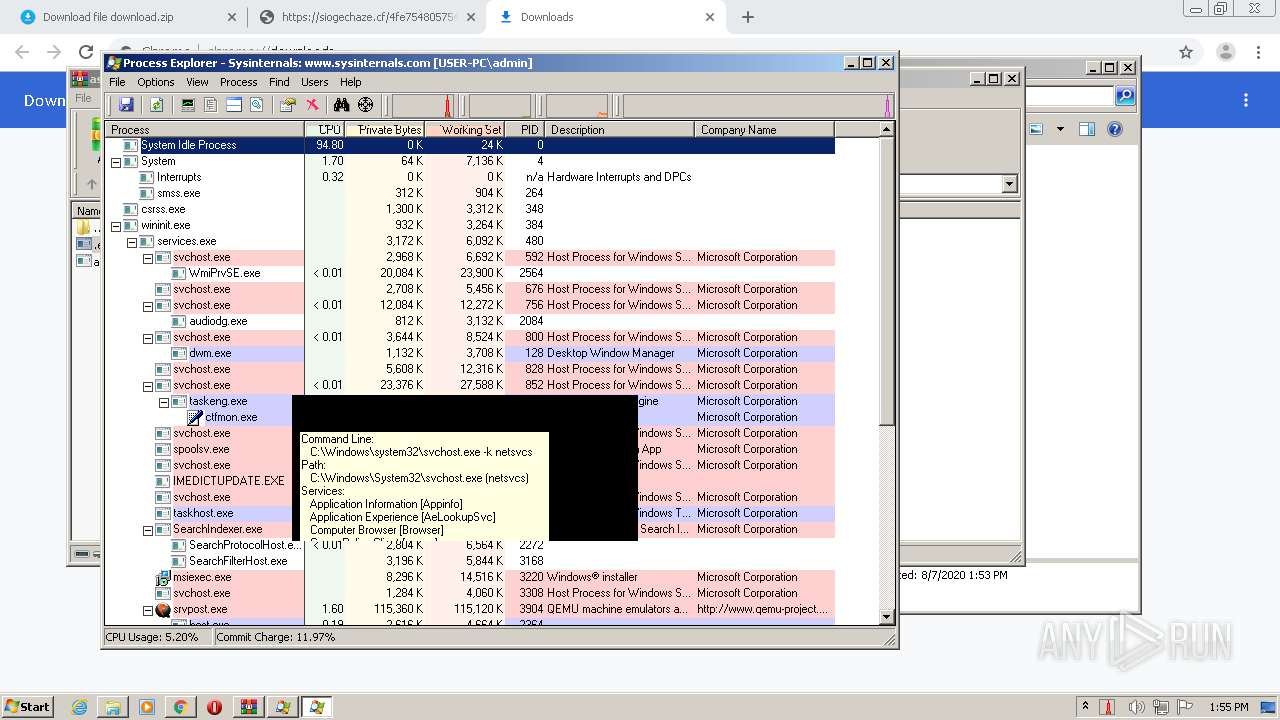
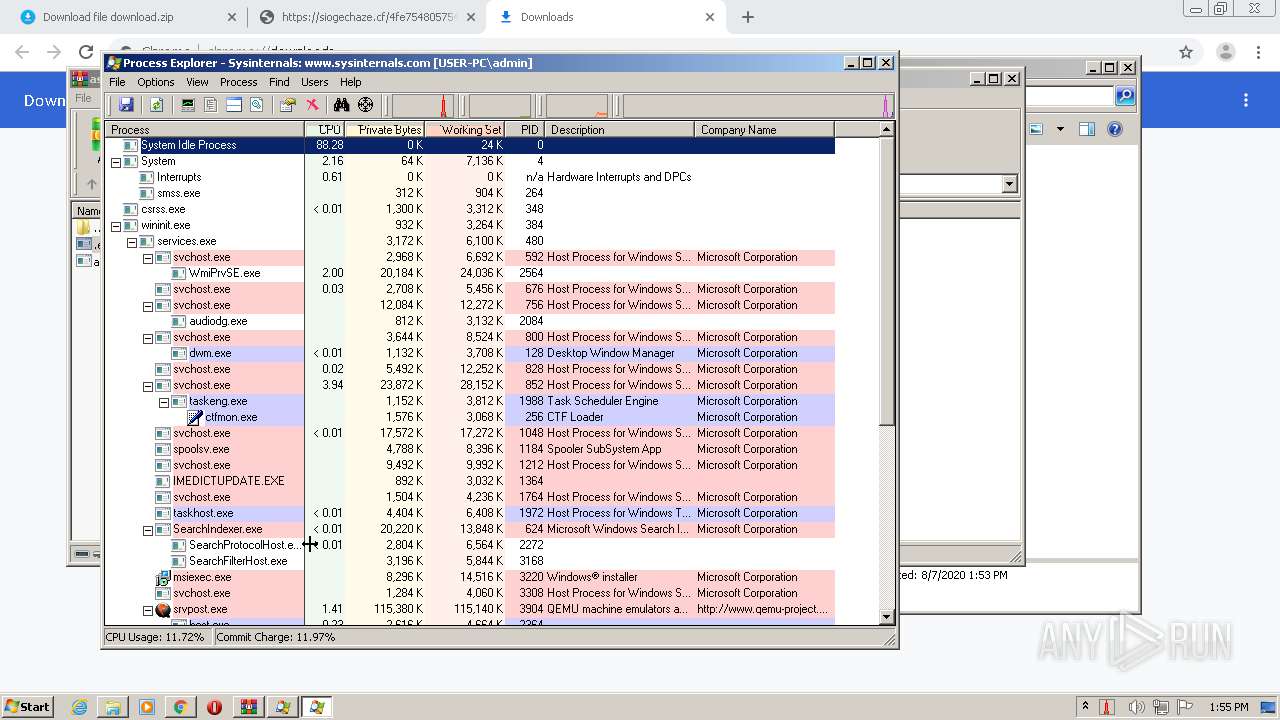
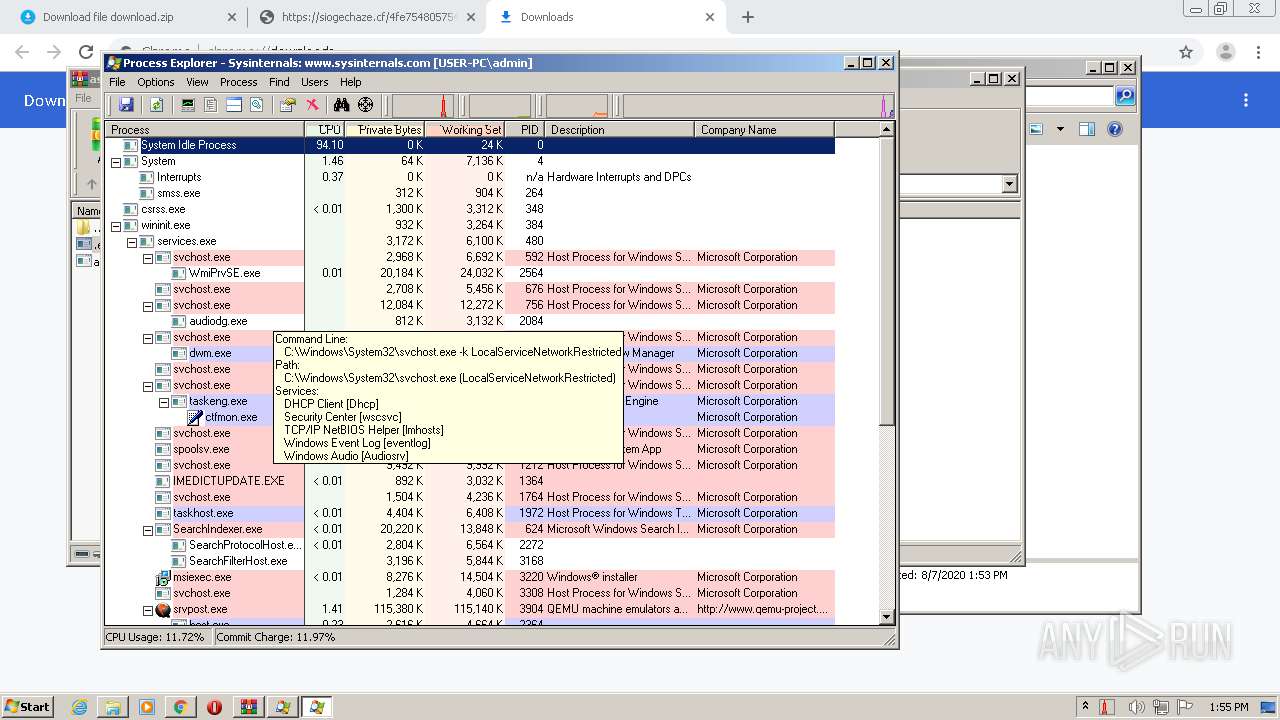
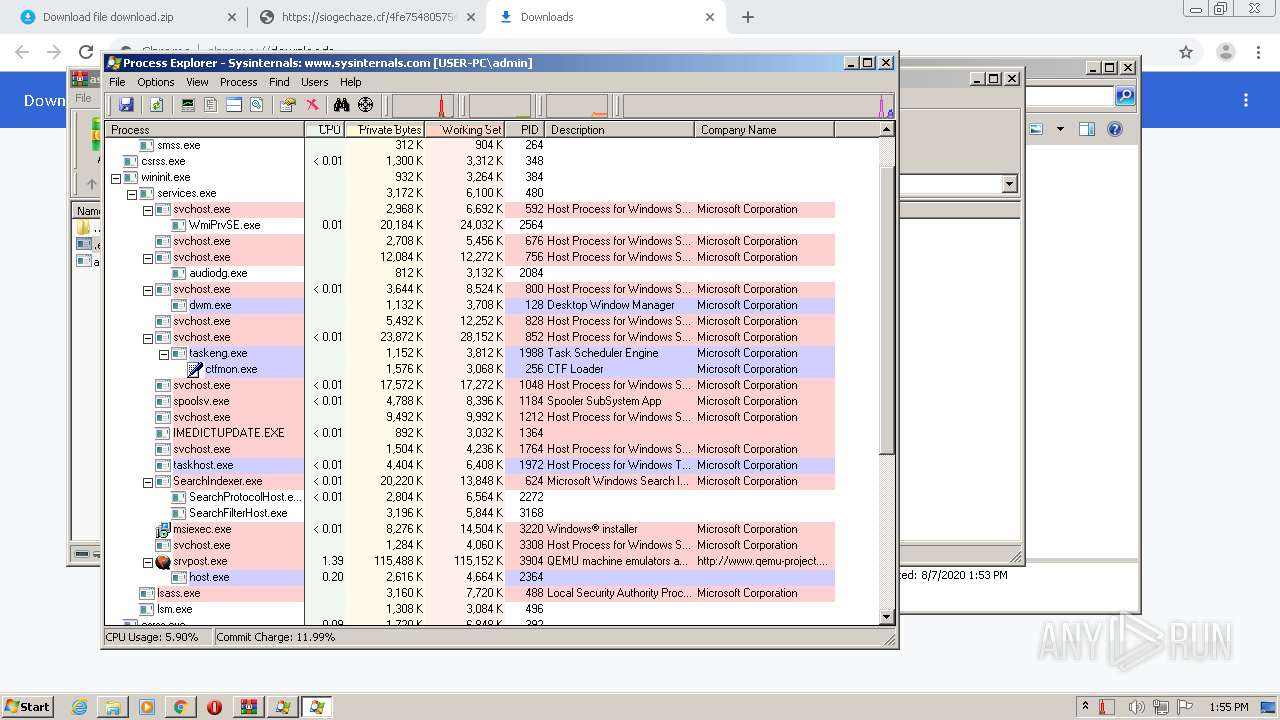
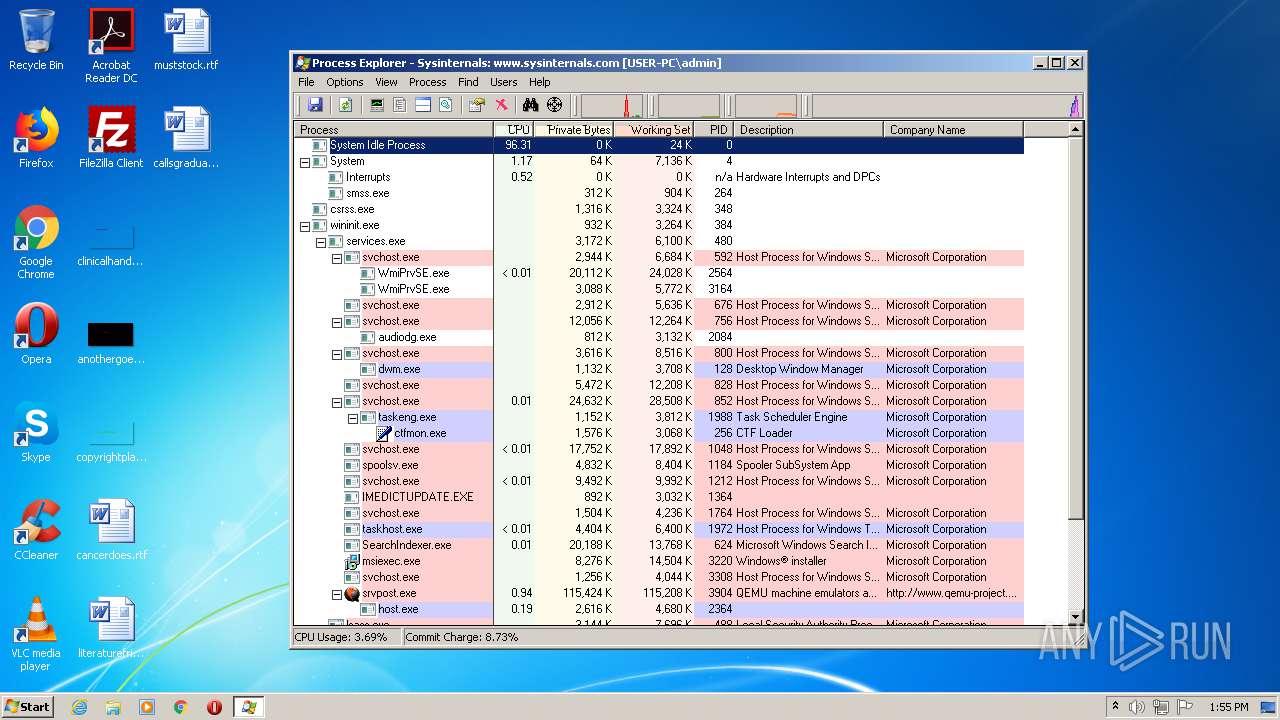
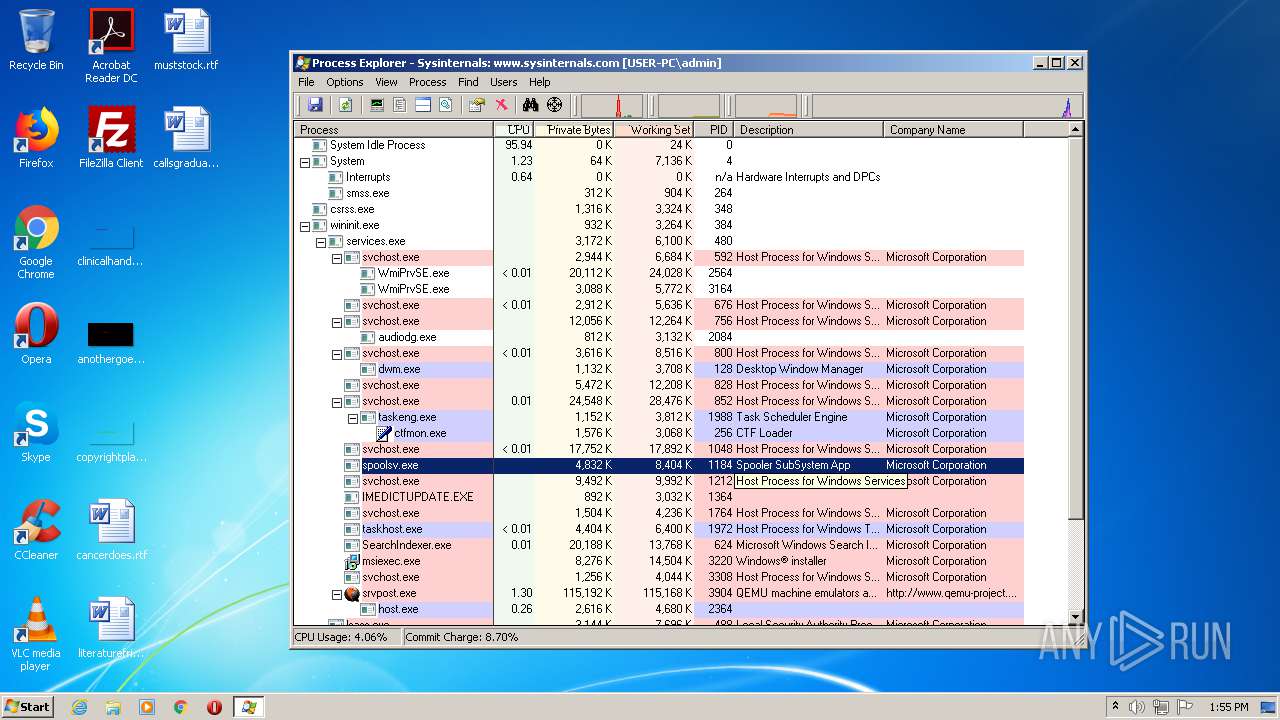
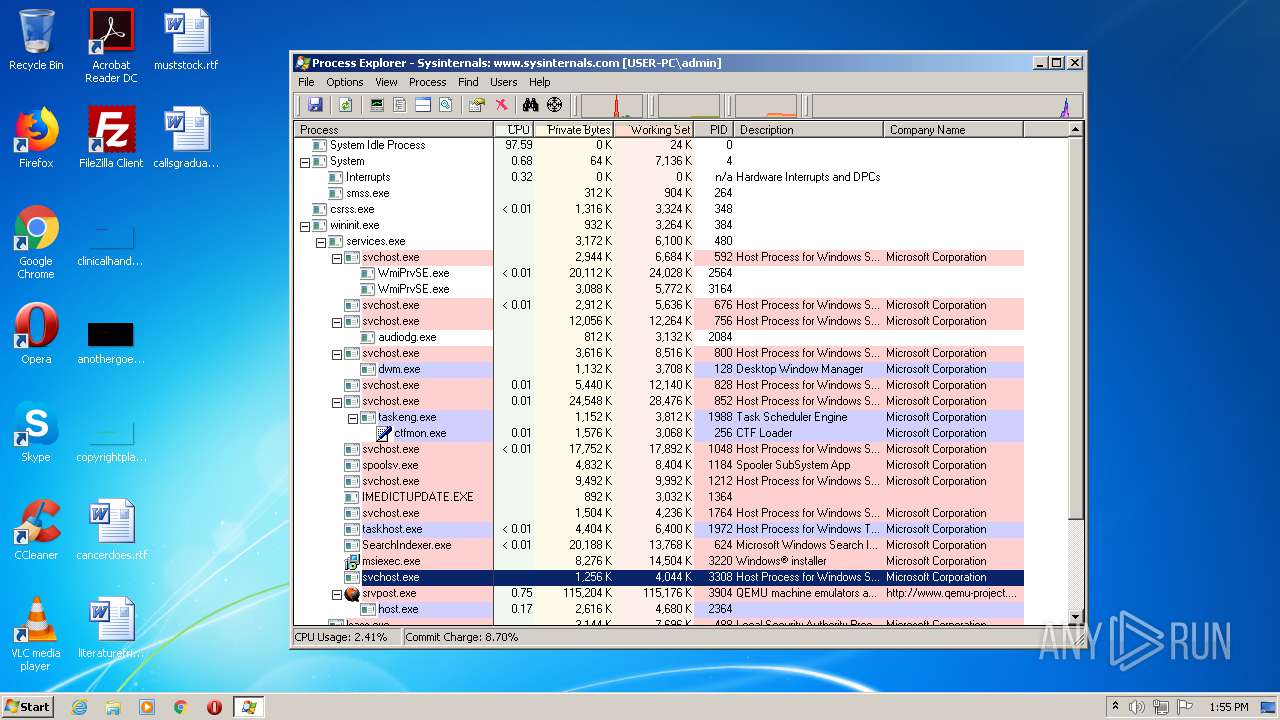
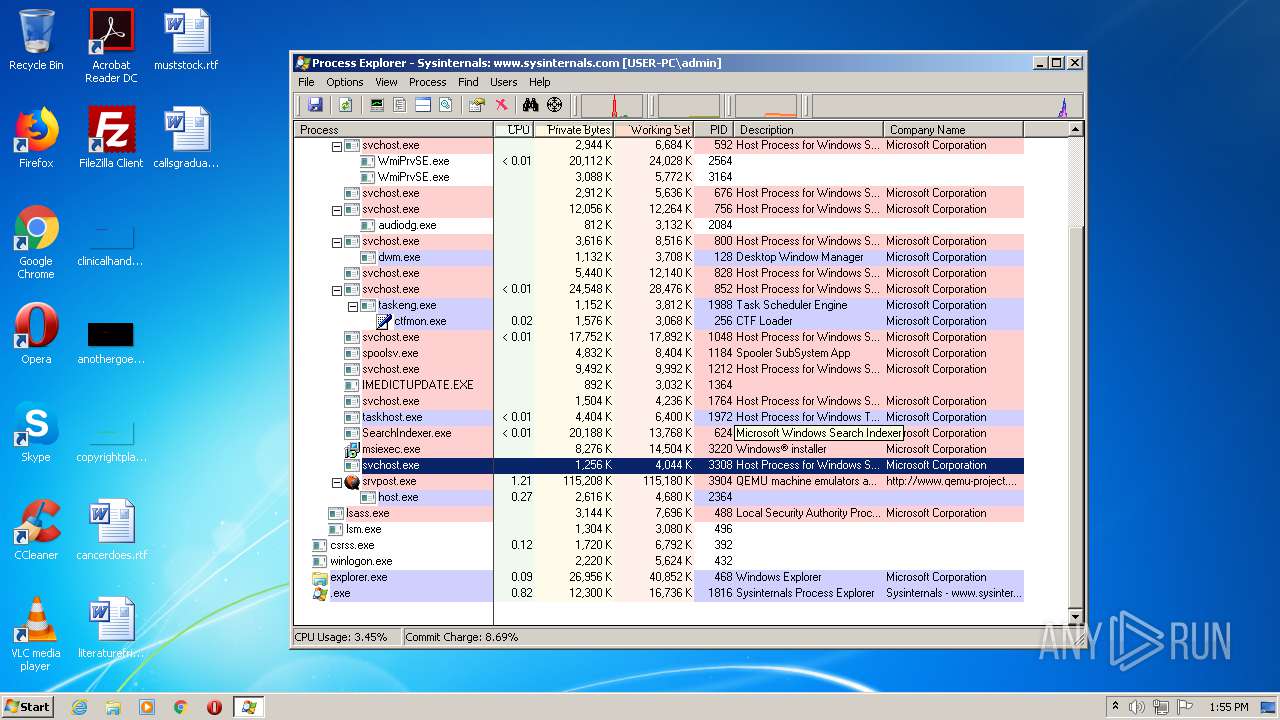
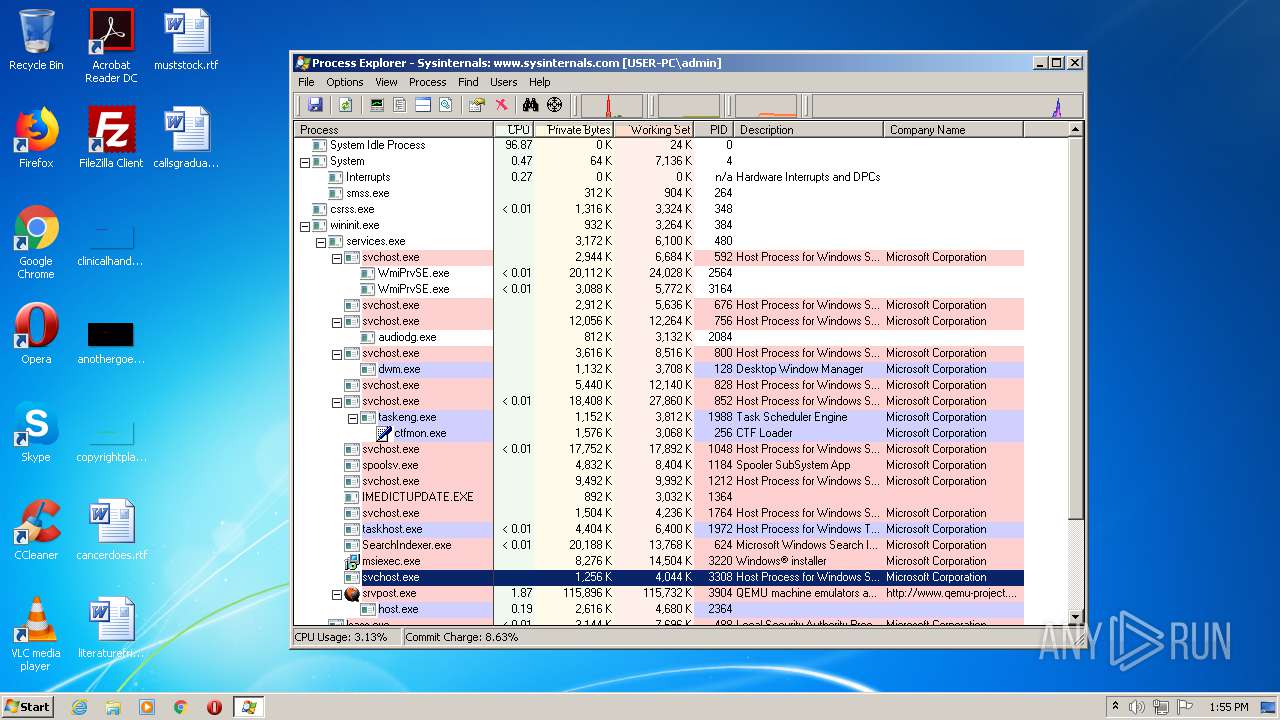
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,17383426814989127752,2669167517411125937,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=11594943308251692666 --mojo-platform-channel-handle=3244 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 180 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2972.24614\asetup_download_3466884111992.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2972.24614\asetup_download_3466884111992.exe | WinRAR.exe | ||||||||||||
User: admin Company: Contaware.com Integrity Level: HIGH Description: Installation Routine of ContaCam Exit code: 3735929054 Version: 9.9.1.0 Modules
| |||||||||||||||
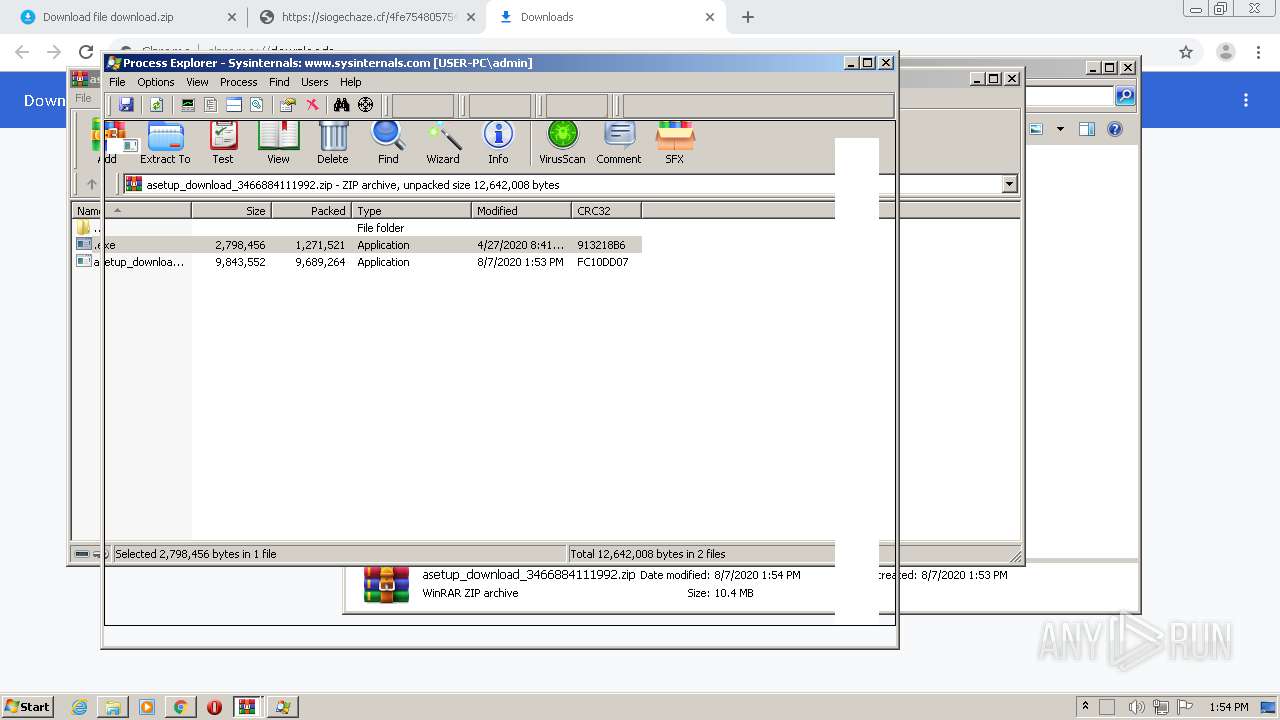
| 332 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2368.22428\.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2368.22428\.exe | WinRAR.exe | ||||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: MEDIUM Description: Sysinternals Process Explorer Exit code: 0 Version: 16.32 Modules
| |||||||||||||||
| 380 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,17383426814989127752,2669167517411125937,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17878187649184390442 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2452 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,17383426814989127752,2669167517411125937,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=14012140765514220848 --mojo-platform-channel-handle=1172 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,17383426814989127752,2669167517411125937,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17445780328071500826 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3424 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1068 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2972.24771\asetup_download_3466884111992.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2972.24771\asetup_download_3466884111992.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Contaware.com Integrity Level: MEDIUM Description: Installation Routine of ContaCam Exit code: 3221226540 Version: 9.9.1.0 Modules
| |||||||||||||||
| 1112 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2972.24416\asetup_download_3466884111992.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2972.24416\asetup_download_3466884111992.exe | WinRAR.exe | ||||||||||||
User: admin Company: Contaware.com Integrity Level: HIGH Description: Installation Routine of ContaCam Exit code: 3735929054 Version: 9.9.1.0 Modules
| |||||||||||||||
| 1288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,17383426814989127752,2669167517411125937,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14224523361185278689 --mojo-platform-channel-handle=500 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 517
Read events
3 183
Write events
329
Delete events
5
Modification events
| (PID) Process: | (2904) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2772-13241278259127375 |
Value: 259 | |||
| (PID) Process: | (2772) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2772) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2772) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2772) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2772) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2772) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2772) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2772) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (2772) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
24
Suspicious files
109
Text files
165
Unknown types
16
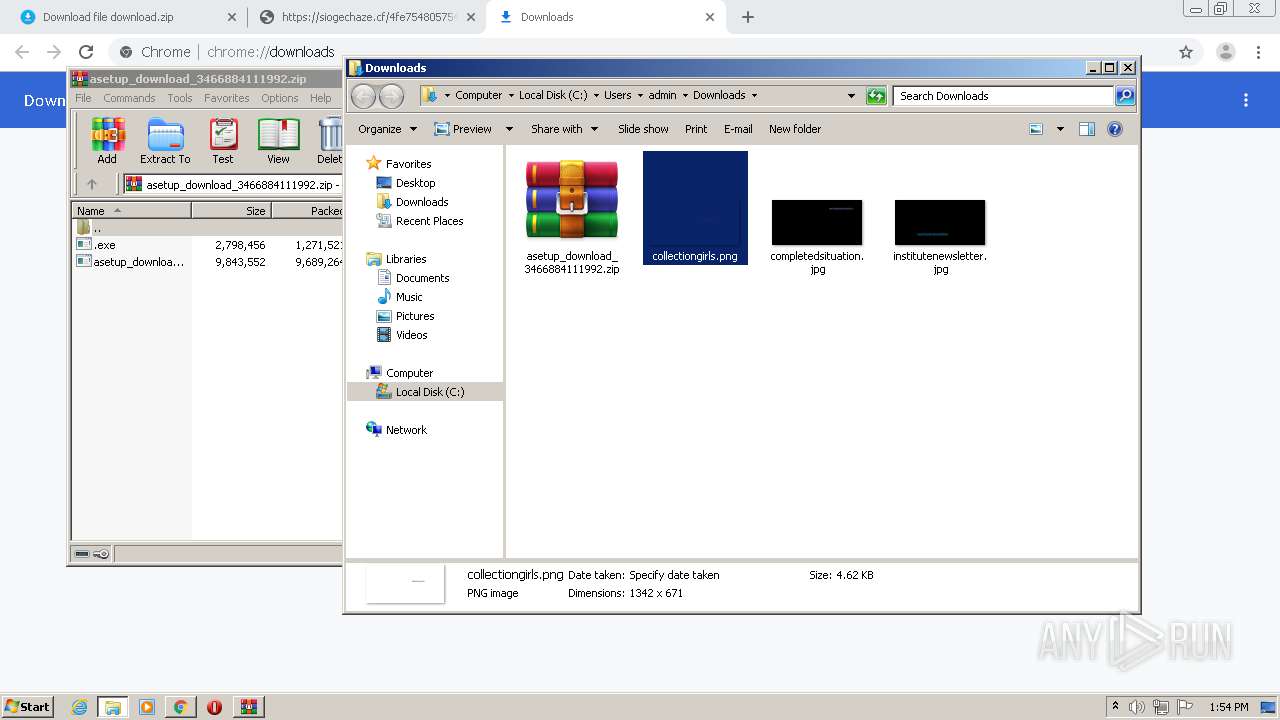
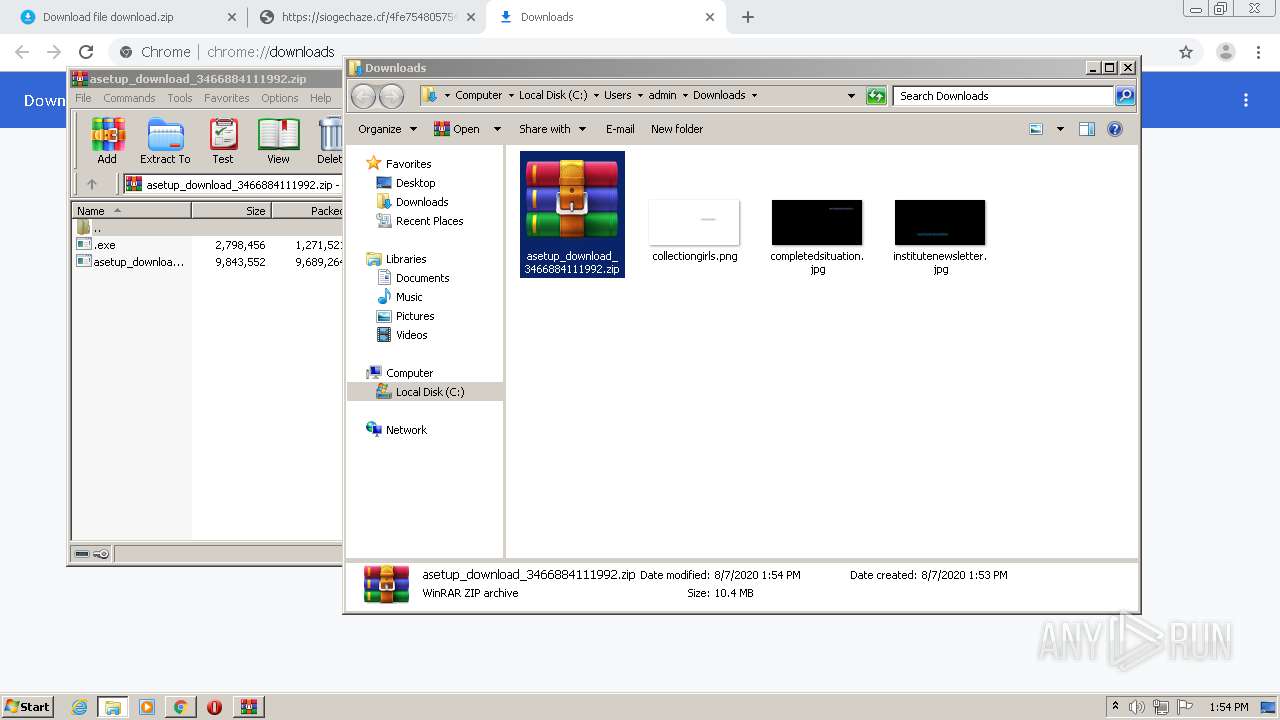
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e2f70f73-0270-41b7-86c4-49aa73aae24d.tmp | — | |
MD5:— | SHA256:— | |||
| 2772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\000001.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFe3004.TMP | text | |
MD5:— | SHA256:— | |||
| 2772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFe3024.TMP | text | |
MD5:— | SHA256:— | |||
| 2772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
70
DNS requests
48
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
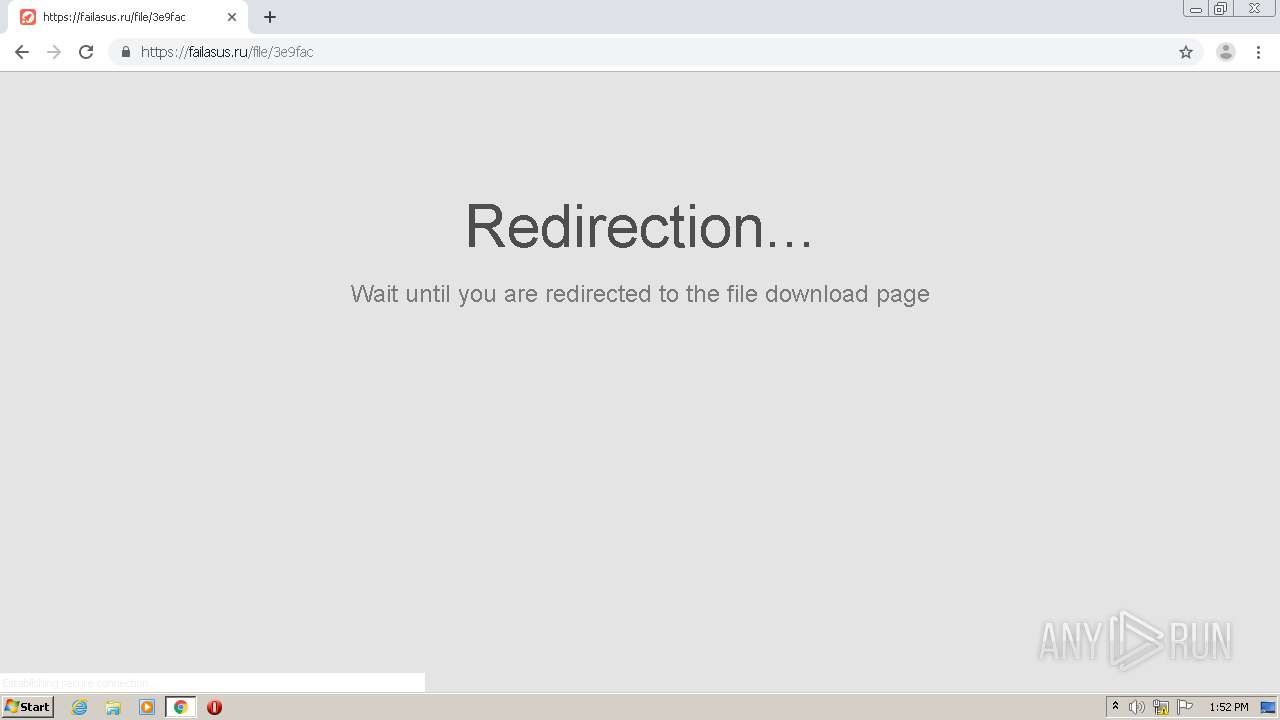
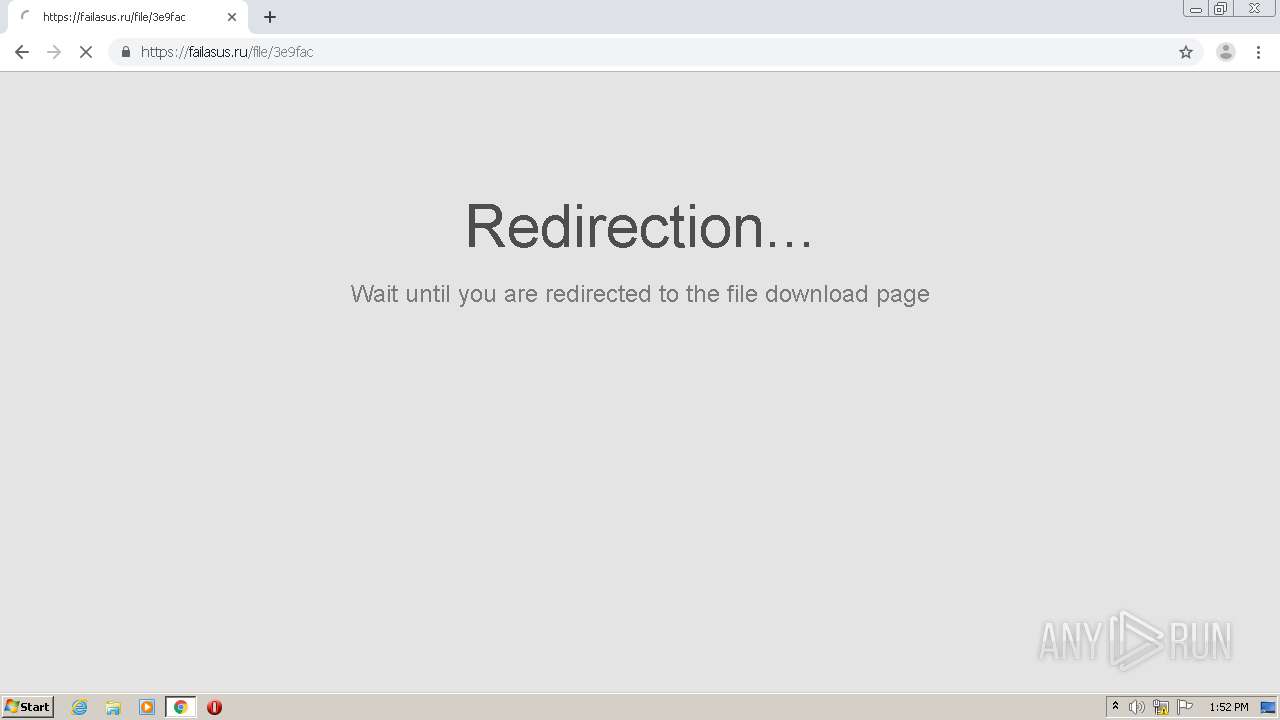
2820 | chrome.exe | GET | 301 | 104.18.56.142:80 | http://failasus.ru/file/3e9fac | US | — | — | malicious |
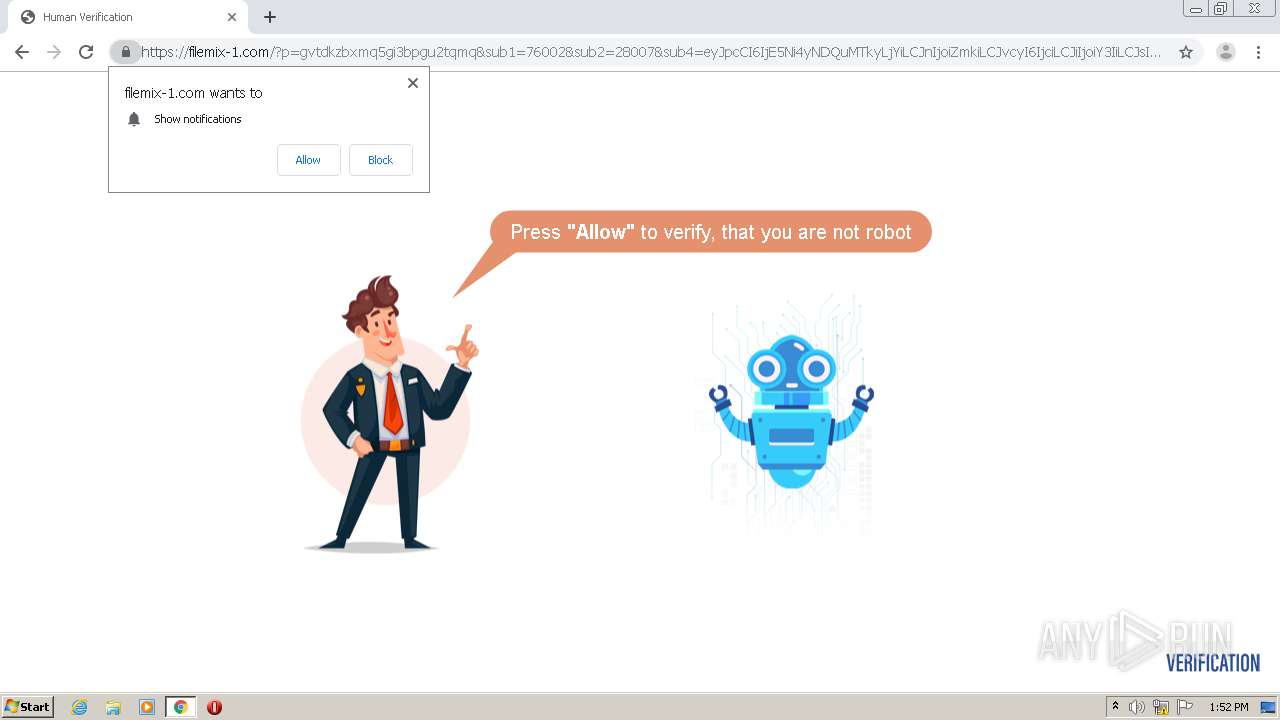
2820 | chrome.exe | GET | 301 | 104.24.122.181:80 | http://failzoma.online/redirect/open | US | — | — | unknown |
2820 | chrome.exe | GET | 301 | 104.24.122.181:80 | http://failzoma.online/redirect/eyJ0eXBlIjozLCJmaWQiOiIxMjhlMiIsImluZm8iOiJleUpwY0NJNklqRTVOaTR5TkRRdU1Ua3lMallpTENKblpXOGlPaUptYVNJc0ltOXpJam9pTnlJc0ltSnliM2R6WlhKeklqb2lZM0lpTENKc1lXNW5Jam9pWlc0dFZWTWlMQ0pwYm1adklqb2lNVGN5T0RVeE9EZzRNeUlzSW5KbFptVnlaWElpT2lKb2RIUndPaTh2WTJGMFkzVjBMbTVsZENJc0ltdGxlU0k2SW1Oak1tRXhNelU0TWpkaFltRmhZemM1WW1Nek4yWmxOVGRsTWpNME1EZ3pJbjA9In0= | US | — | — | unknown |
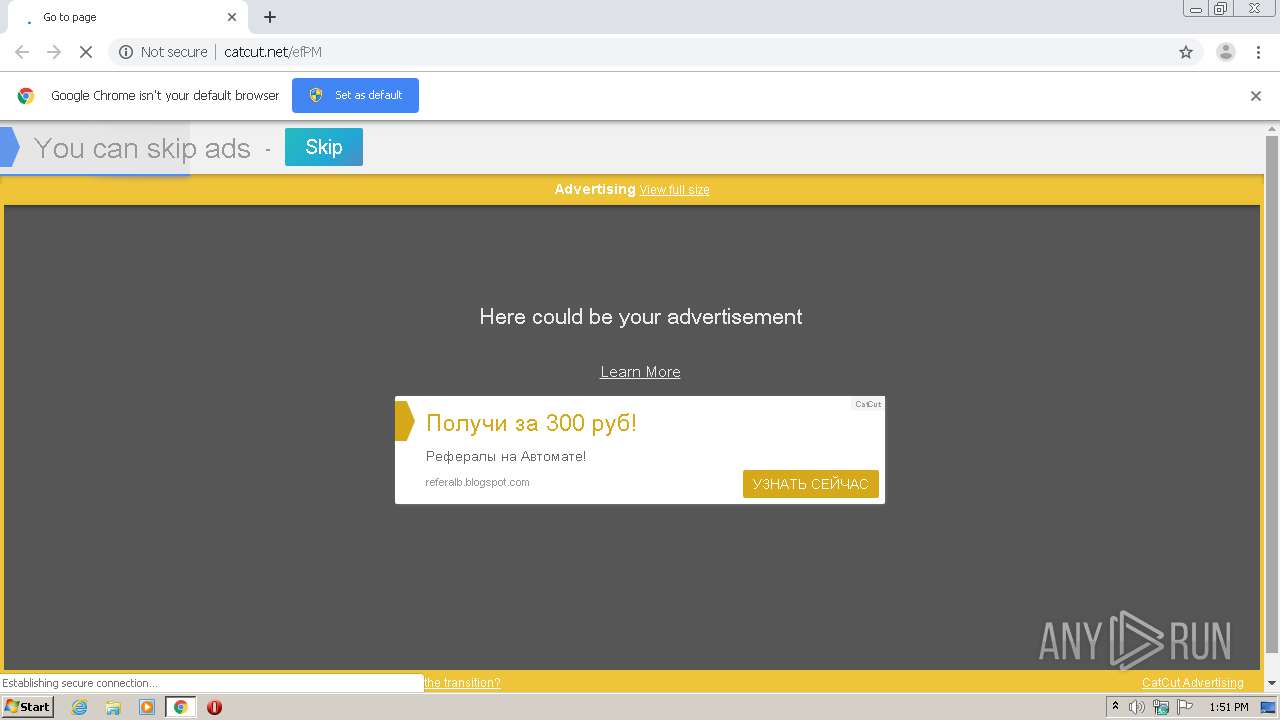
2820 | chrome.exe | GET | 200 | 185.26.97.103:80 | http://catcut.net/adv/public.php?a=18594&b=&c=aHR0cDovL2NhdGN1dC5uZXQvZWZQTQ==&d=c3b0c7c2ade858e6db2c73965468cb69&f=aHR0cDovL2NhdGN1dC5uZXQvZWZQTQ==&g=YXBwbGljYXRpb24vcGRmK3BkZjthcHBsaWNhdGlvbi94LWdvb2dsZS1jaHJvbWUtcGRmK3BkZjthcHBsaWNhdGlvbi94LW5hY2wrO2FwcGxpY2F0aW9uL3gtcG5hY2wrOw==&h=1 | DE | html | 9.06 Kb | suspicious |
2820 | chrome.exe | GET | 200 | 185.26.97.103:80 | http://catcut.net/images/favicon64.ico | DE | image | 2.00 Kb | suspicious |
332 | .exe | GET | 200 | 2.16.186.120:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | unknown | der | 550 b | whitelisted |
2820 | chrome.exe | GET | 200 | 185.26.97.103:80 | http://catcut.net/efPM | DE | html | 21.1 Kb | suspicious |
2820 | chrome.exe | GET | 200 | 185.26.97.103:80 | http://catcut.net/away3.php?&b=1af5cf11fba36841e6ef905b7c08cb6d.67142&c=c1780af3e2fdd993e61d30f8ba7264f8&d=&q=1&r=13&p=0&t=1&s=1&u14=26&v14=65&w7=103&x=03AGdBq27J7zE8P4CKNLNIZlascyksoQlcEhvIiaA--LNHg84Tjg0dUbSy4ZBFevZKEgNZ6gEG1ubDGT12U-QsBXDznjCbvHgRtVvm9LsADZXGv0O1X6-wL1NU3OwukgL_bscmp3DqFjRc31rEB_gS-OSMXD9uAlQ-LmNRc-aA8X0j1pPt5VKdVaBTMMJ7WkNuvZLDJE5KHO4rmvbTx2imrJky_TS7HqwBp2Qkr2TySX1A87Ps29NjQwIkB-3DTBzZVzp31Ag_yDB3k4M3IeMlmvIxYI8dxE_bklbwLQs8Y3A4z406ig-u3wh7Racir_VgmMeOrmBpwQYSEL9RPBHeU0uYuqJUFdtbPlFHyNqm2_dg-g1XVvlmhRikGqj2PFQ-1JMNzT0zLjfC | DE | text | 40 b | suspicious |
2820 | chrome.exe | GET | 200 | 185.26.97.103:80 | http://catcut.net/adv/18594 | DE | text | 1.26 Kb | suspicious |
2820 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAP%2B7xu1tkg0miCVD4vGl1M%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2820 | chrome.exe | 185.26.97.103:80 | catcut.net | First Colo GmbH | DE | unknown |
2820 | chrome.exe | 172.217.23.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2820 | chrome.exe | 172.217.16.164:443 | www.google.com | Google Inc. | US | whitelisted |
2820 | chrome.exe | 172.217.16.174:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
2820 | chrome.exe | 172.217.23.109:443 | accounts.google.com | Google Inc. | US | suspicious |
2820 | chrome.exe | 172.217.21.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2820 | chrome.exe | 173.194.76.154:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
2820 | chrome.exe | 216.58.206.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
2820 | chrome.exe | 172.217.23.131:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2820 | chrome.exe | 104.31.67.143:443 | earnfreebit.tk | Cloudflare Inc | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
catcut.net |
| suspicious |
accounts.google.com |
| shared |
www.google.com |
| malicious |
www.google-analytics.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
stats.g.doubleclick.net |
| whitelisted |
clients1.google.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
earnfreebit.tk |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |
1048 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .ml Domain |
2820 | chrome.exe | Potentially Bad Traffic | ET INFO Suspicious Domain (*.ml) in TLS SNI |
1048 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1048 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
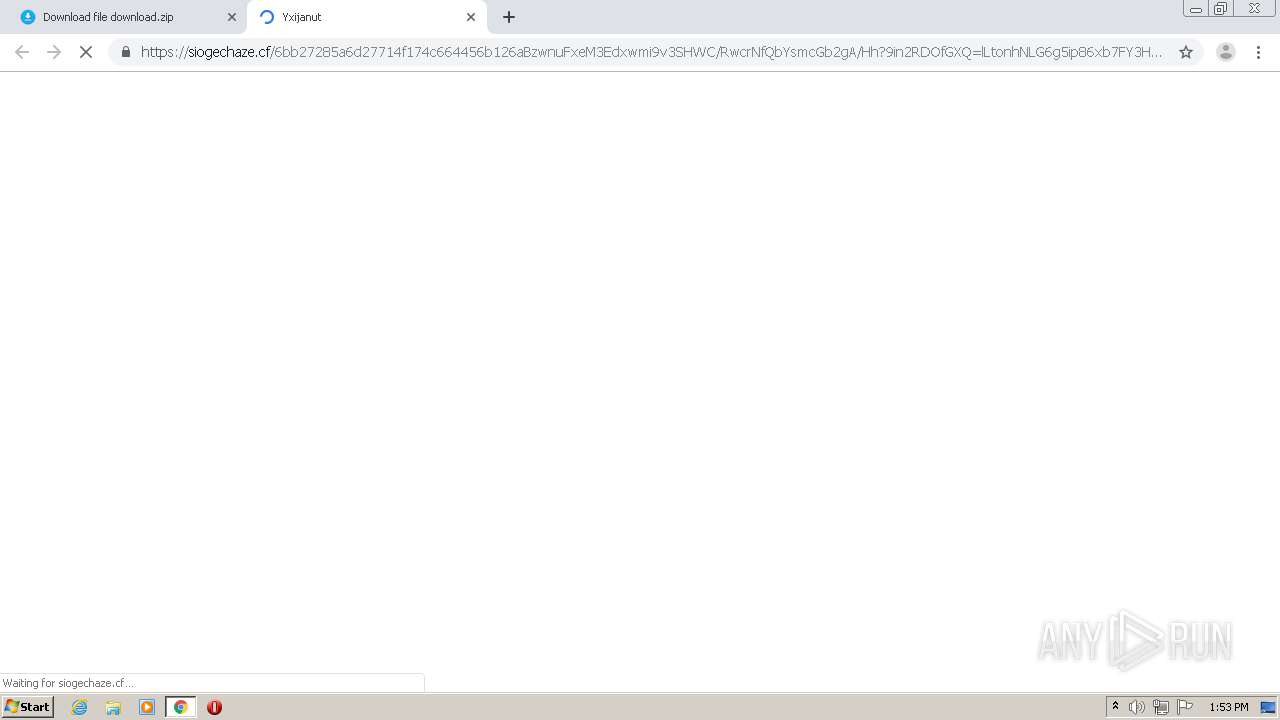
1048 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .cf Domain |
2820 | chrome.exe | Potentially Bad Traffic | ET INFO Suspicious Domain (*.cf) in TLS SNI |
1048 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .ml Domain |
2820 | chrome.exe | Potentially Bad Traffic | ET INFO Suspicious Domain (*.ml) in TLS SNI |