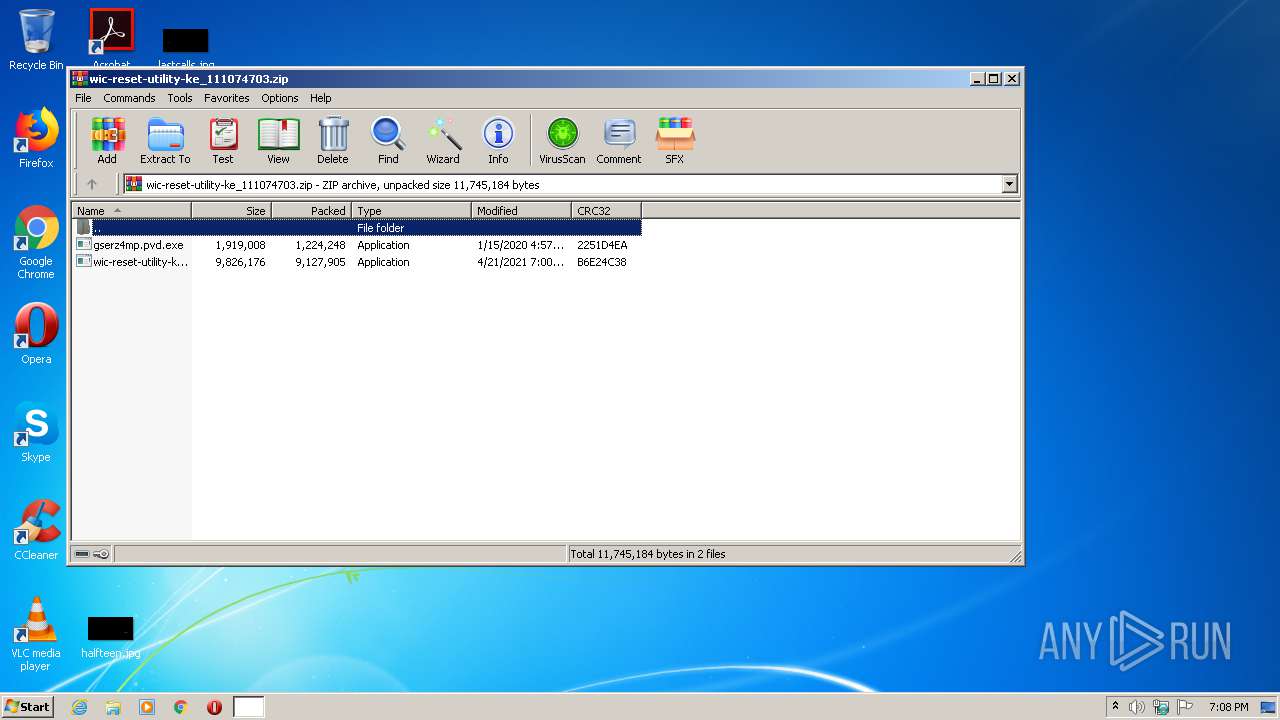
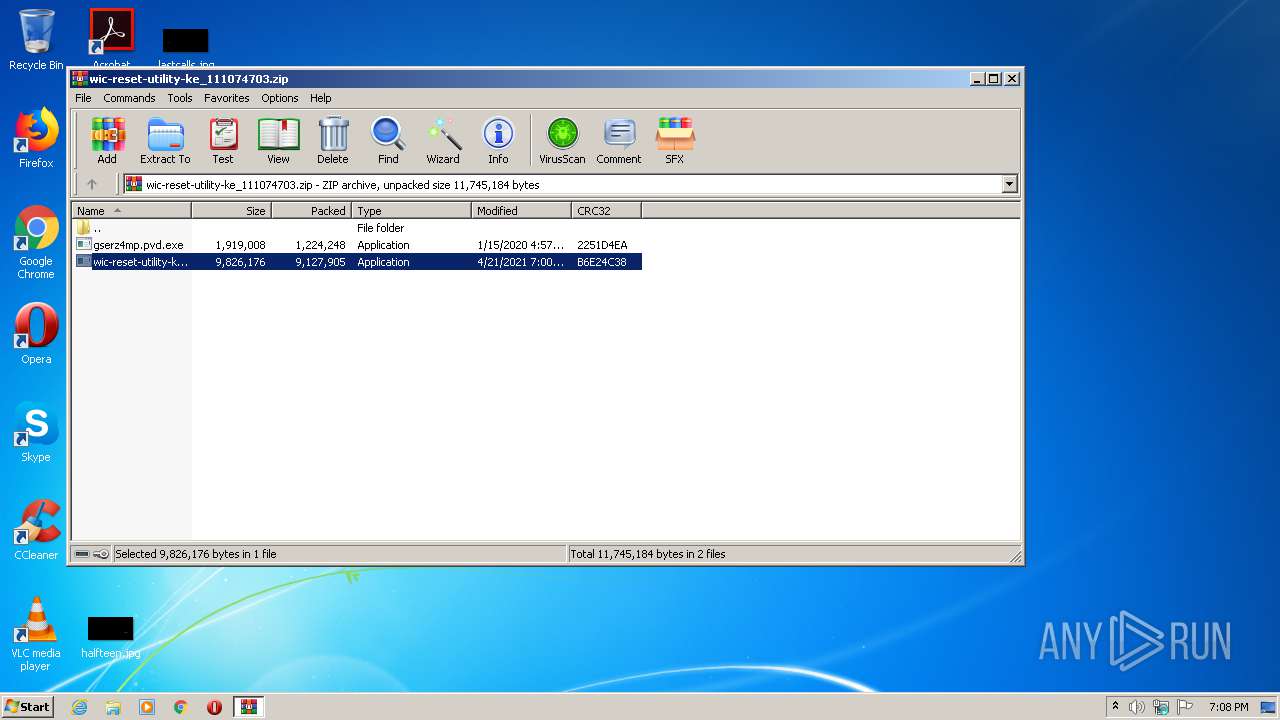
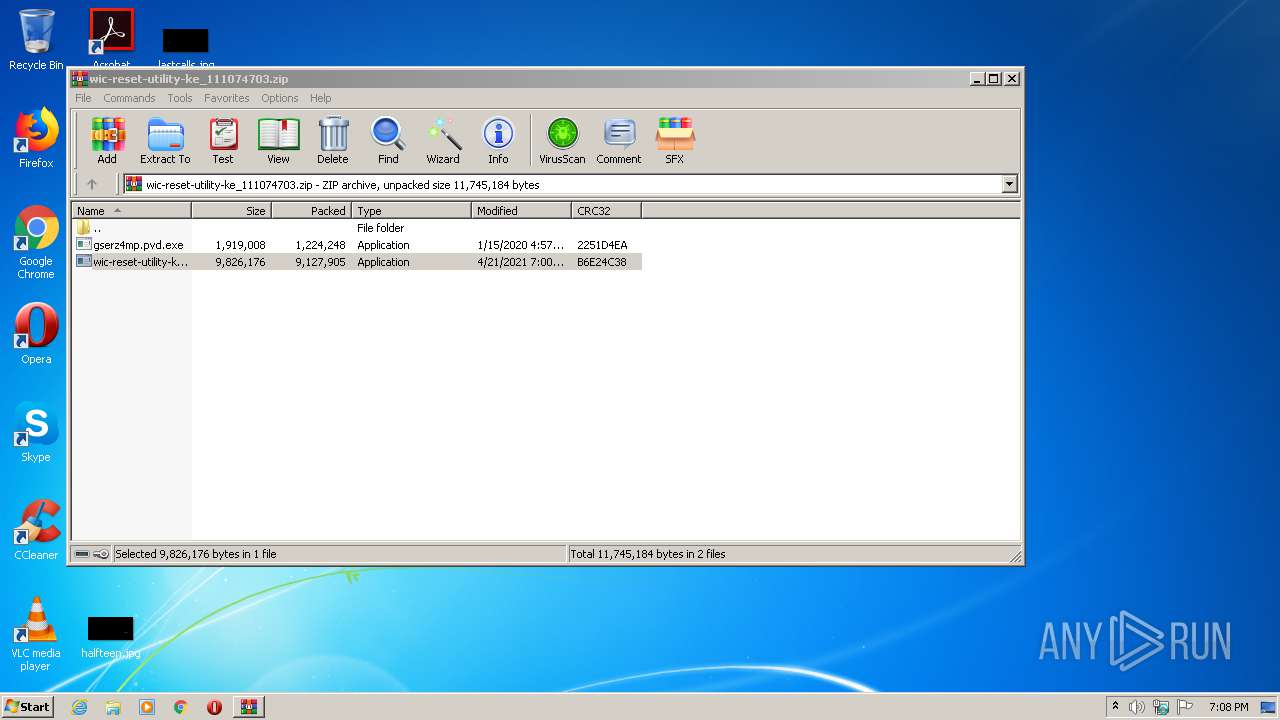
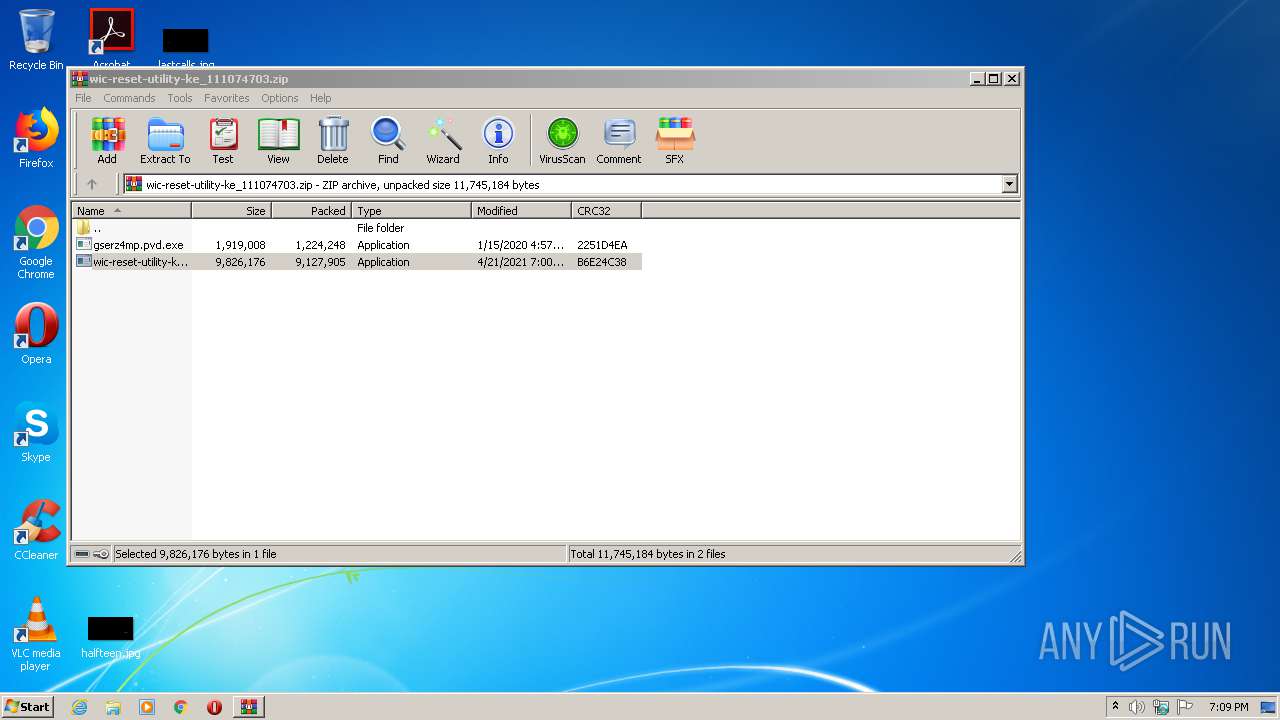
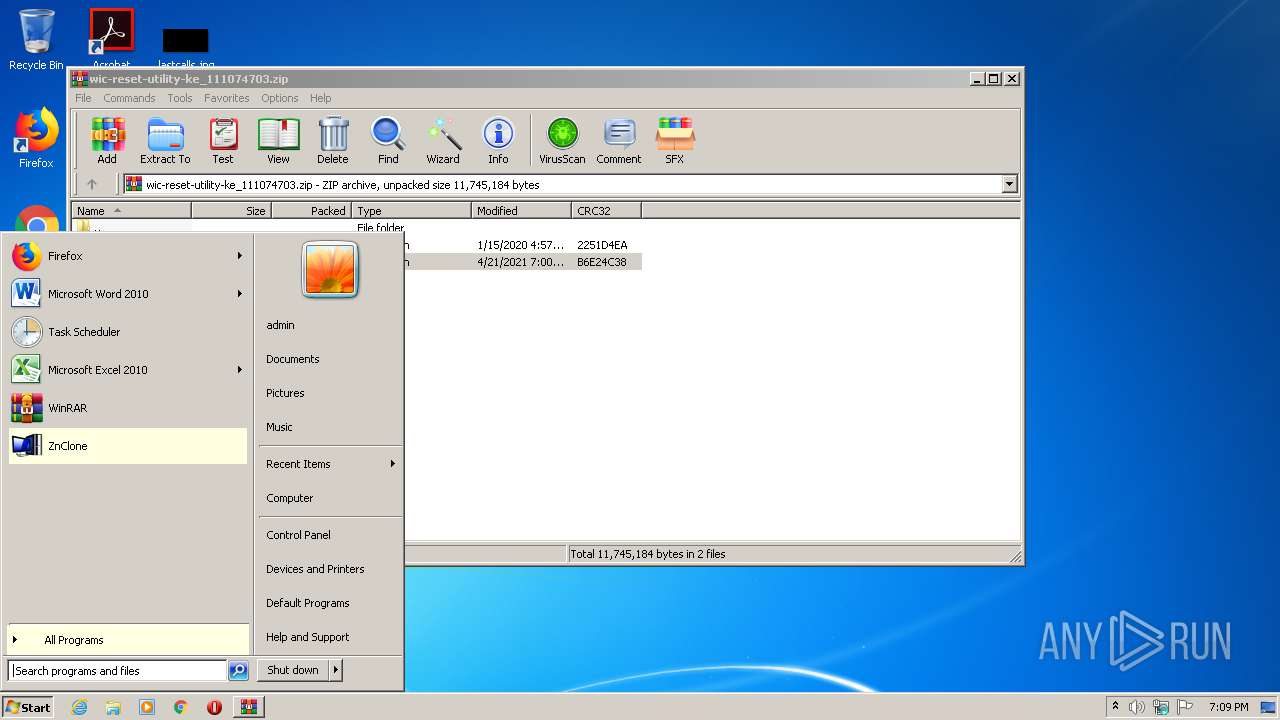
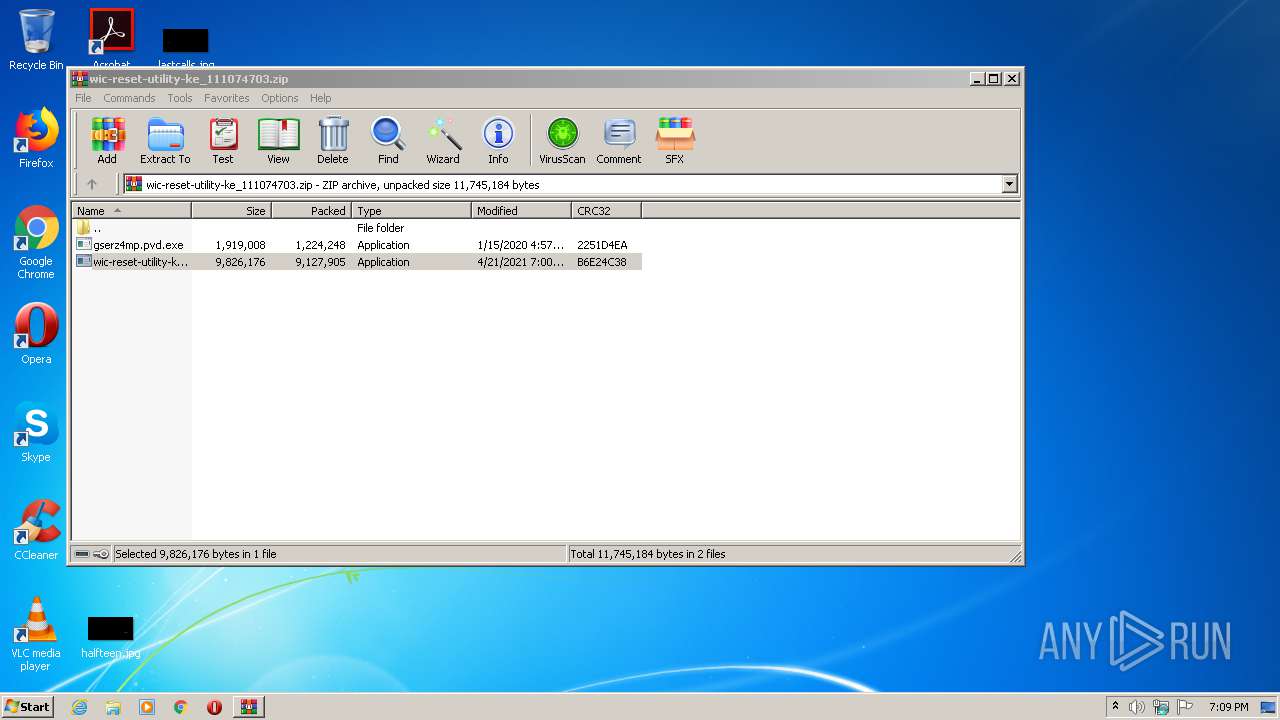
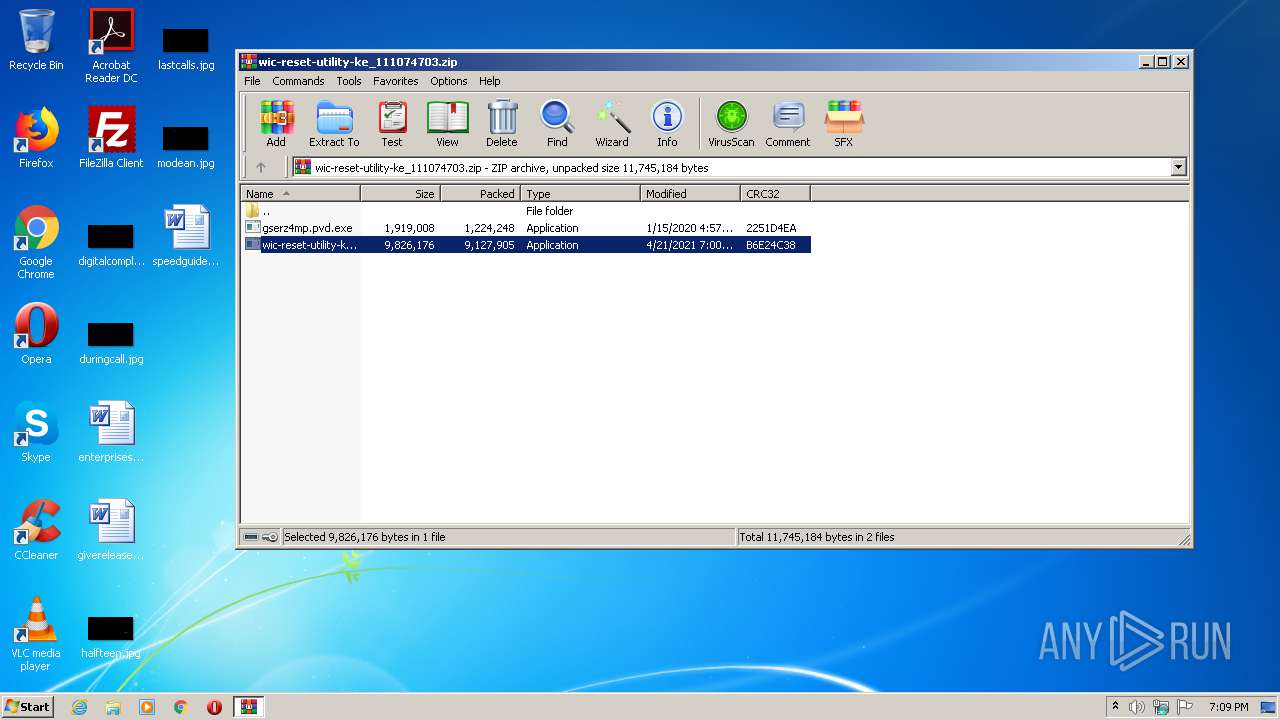
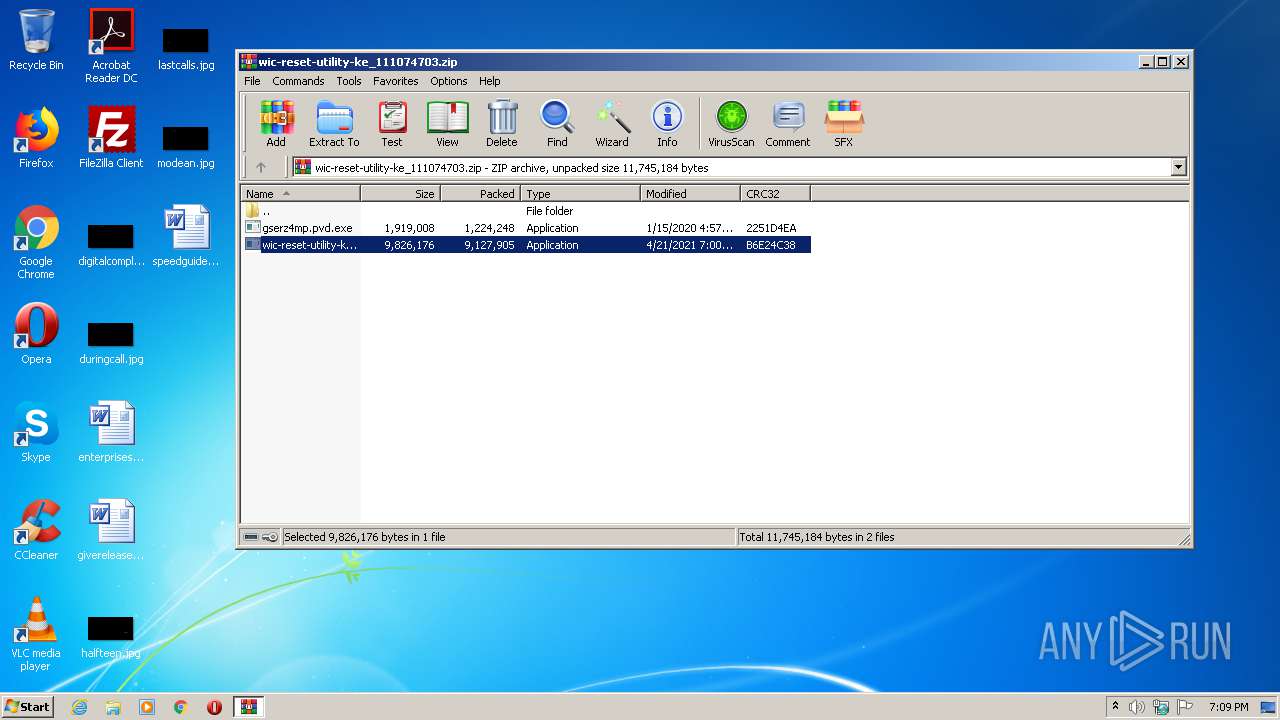
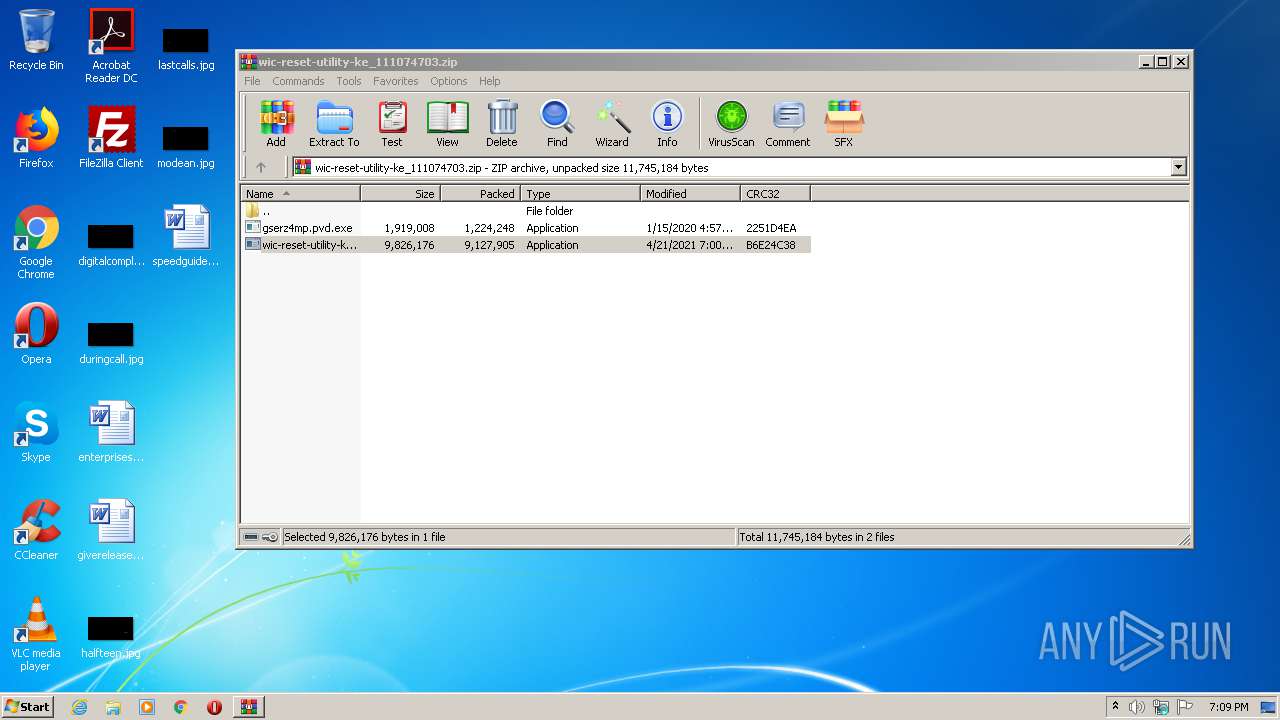
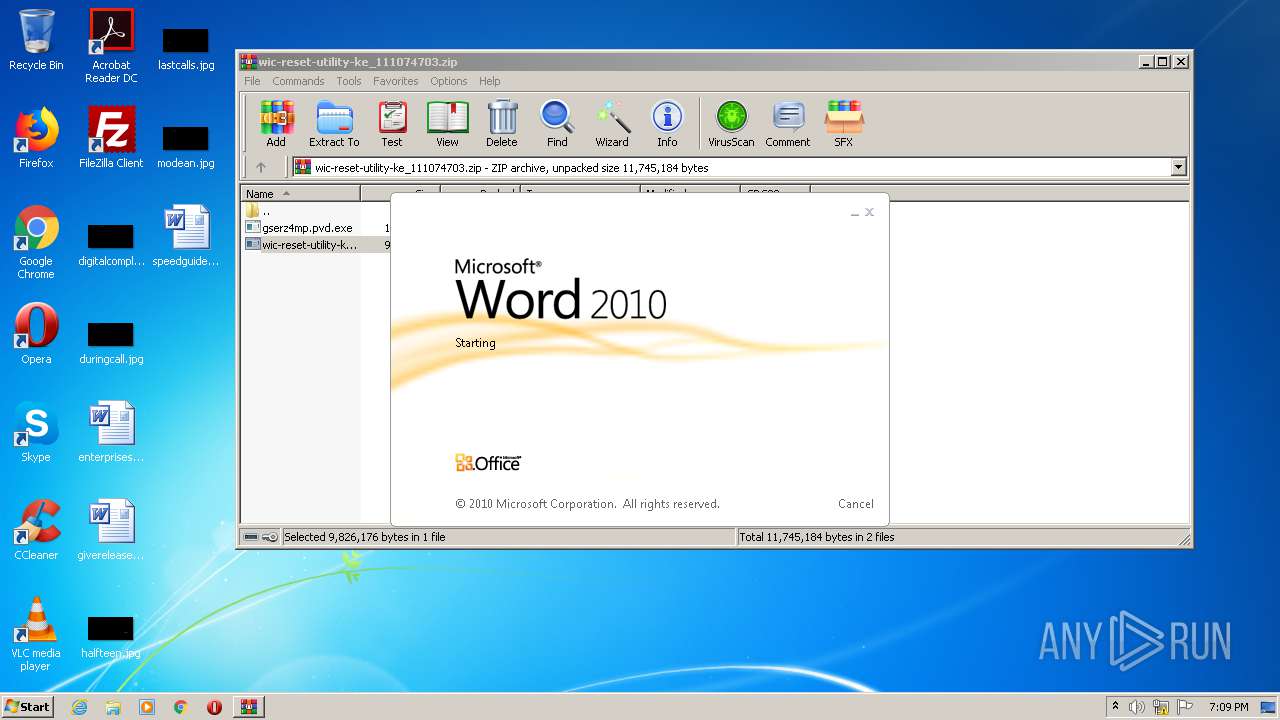
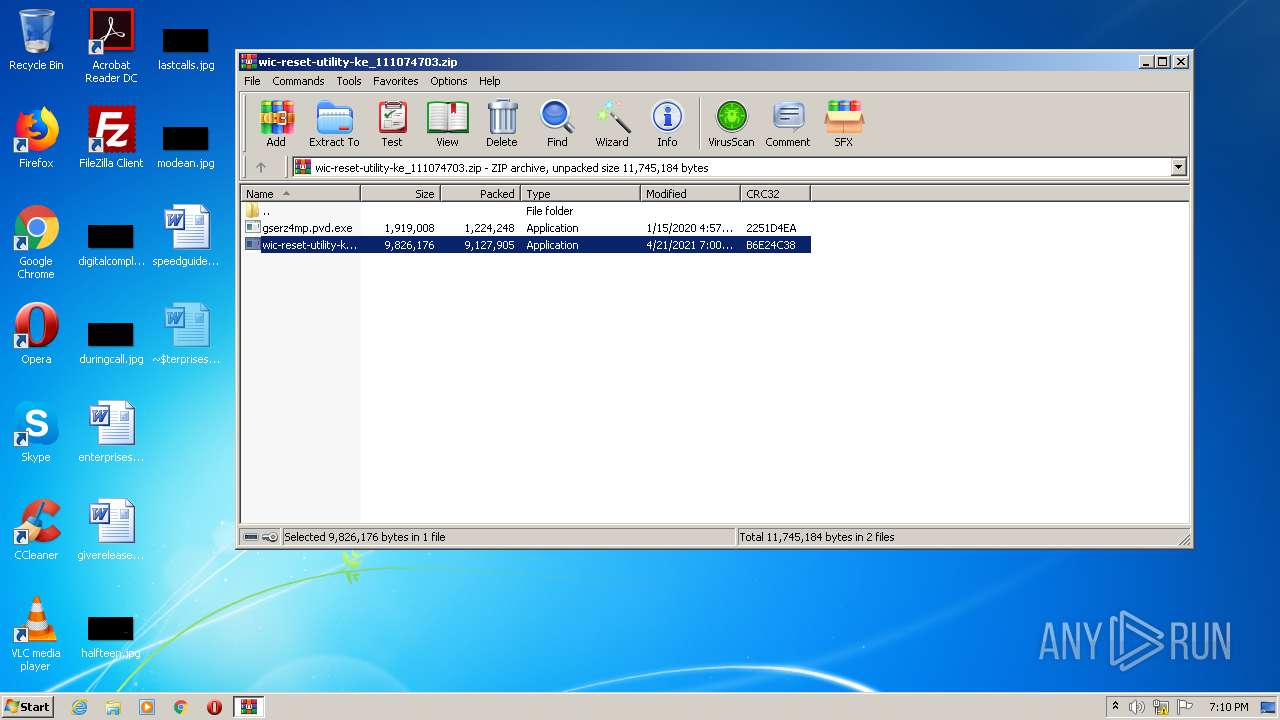
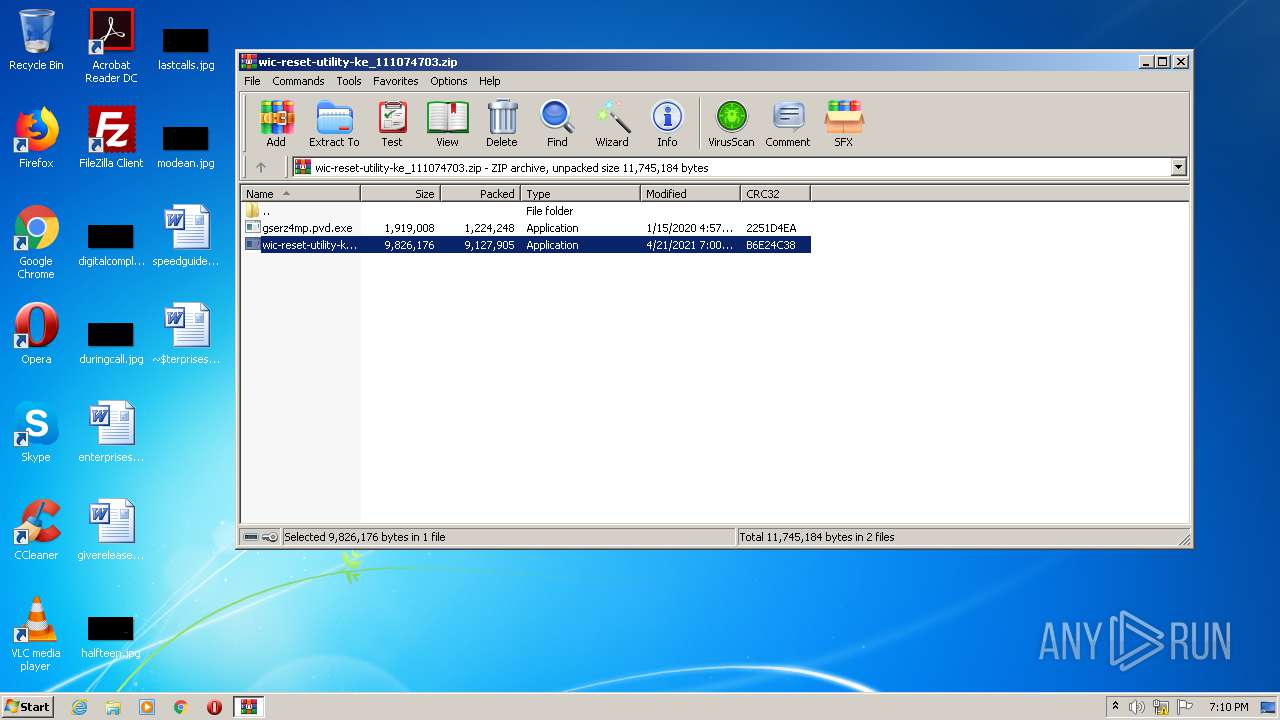
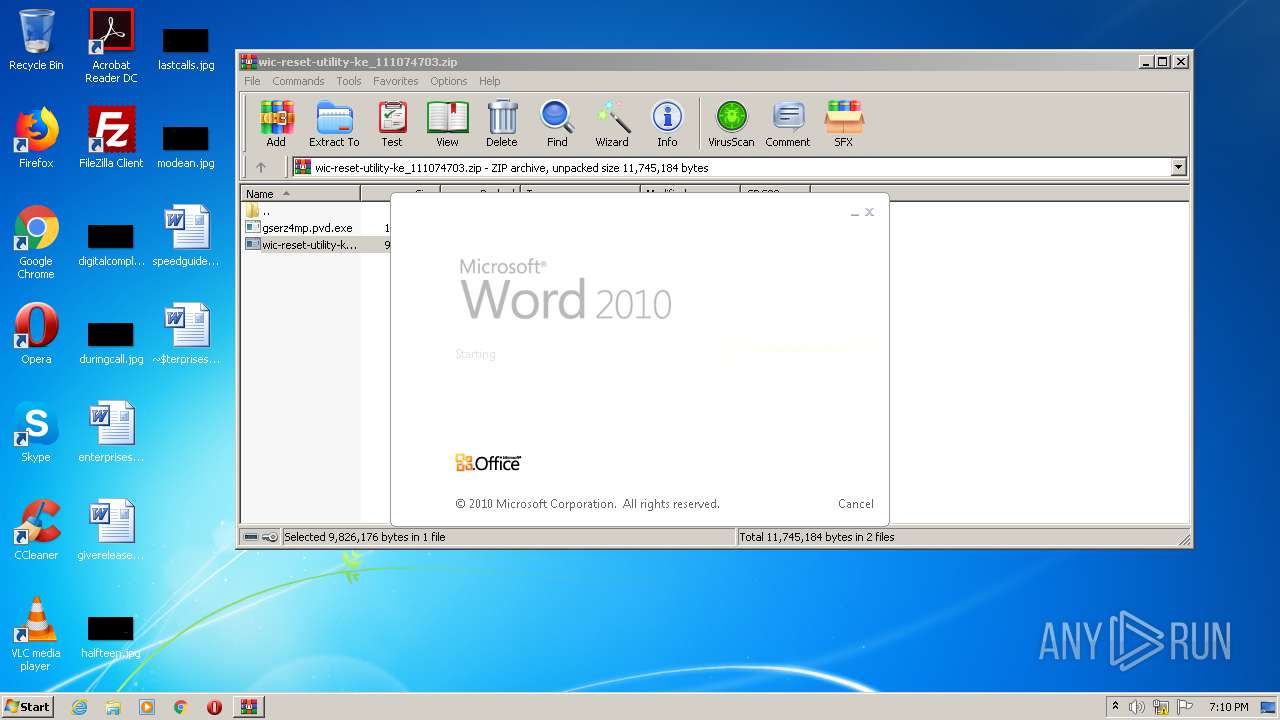
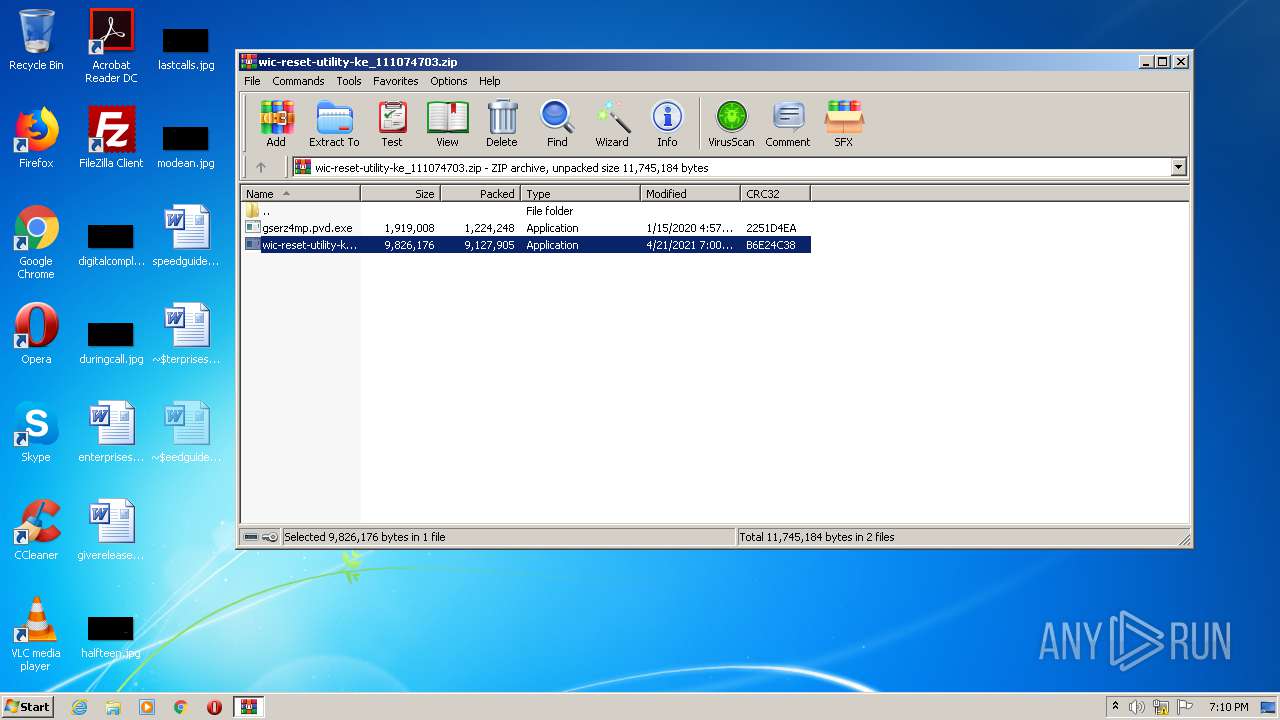
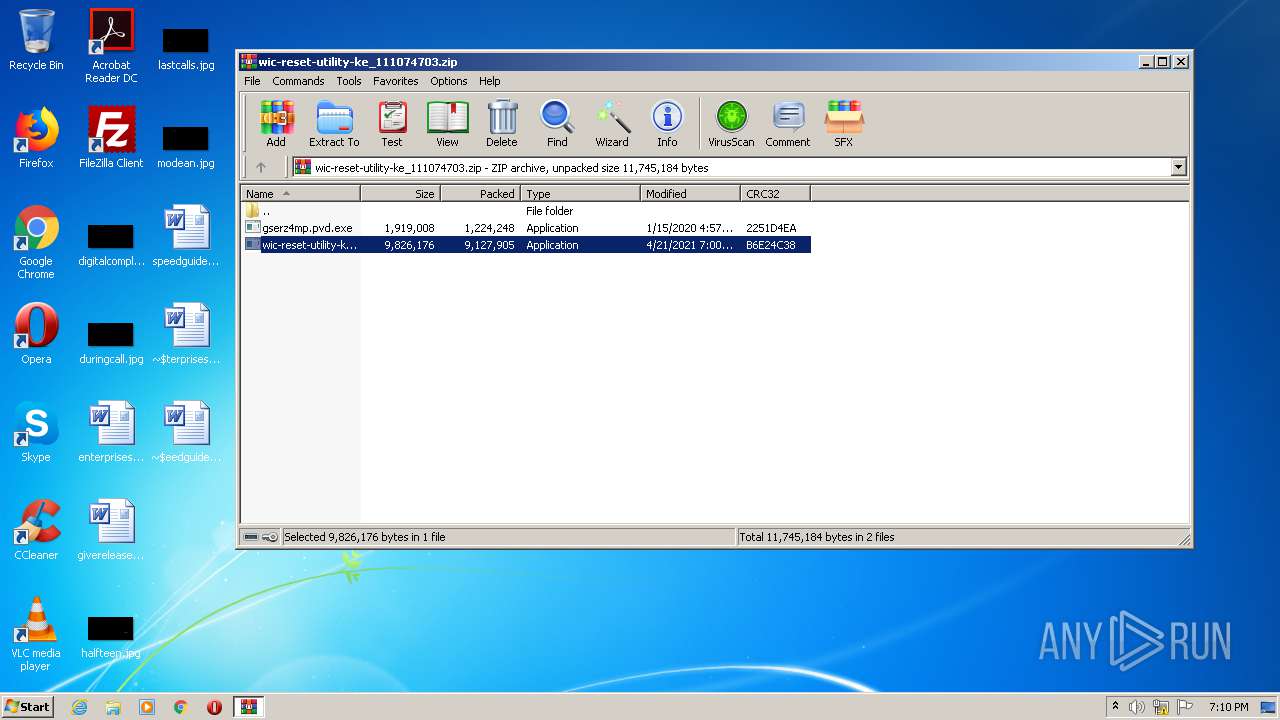
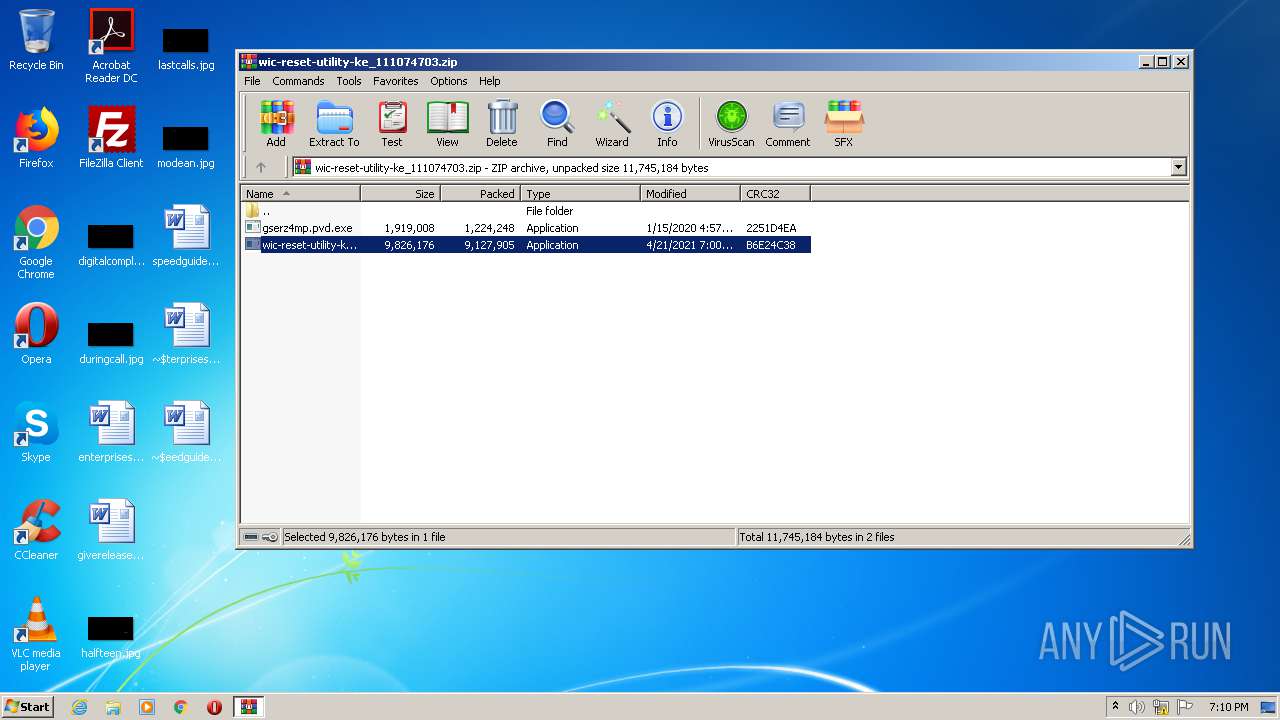
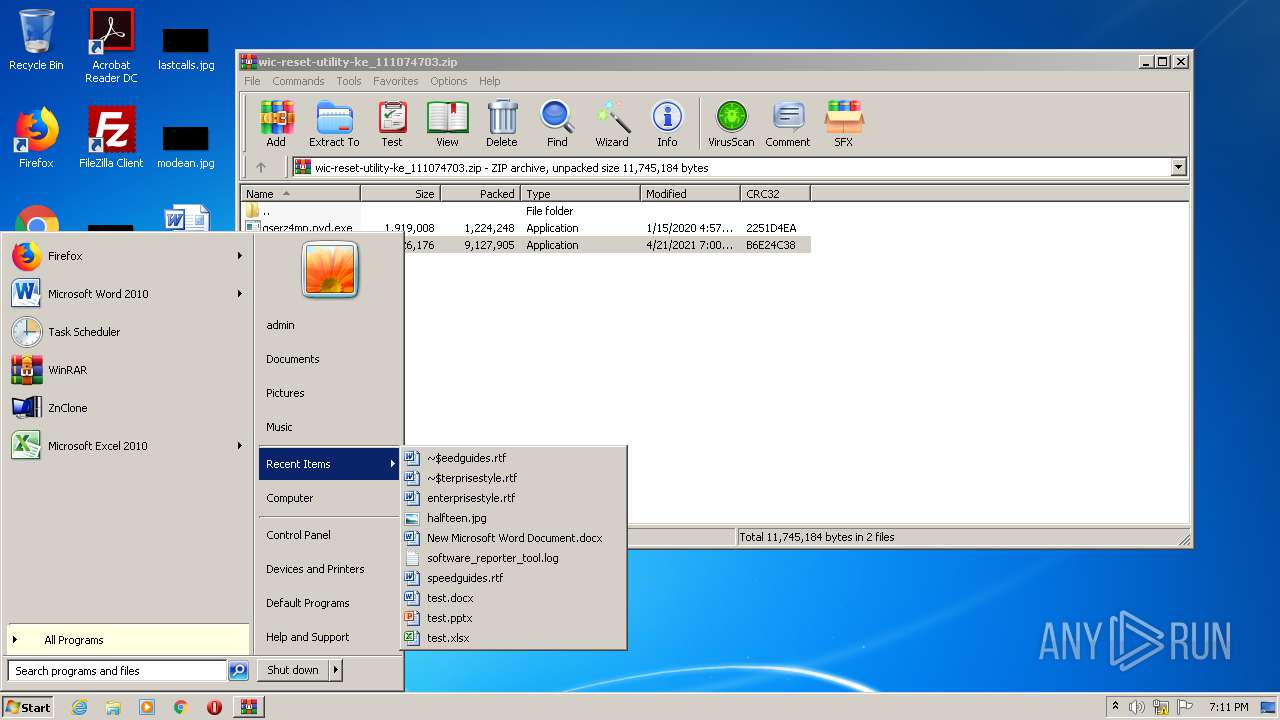
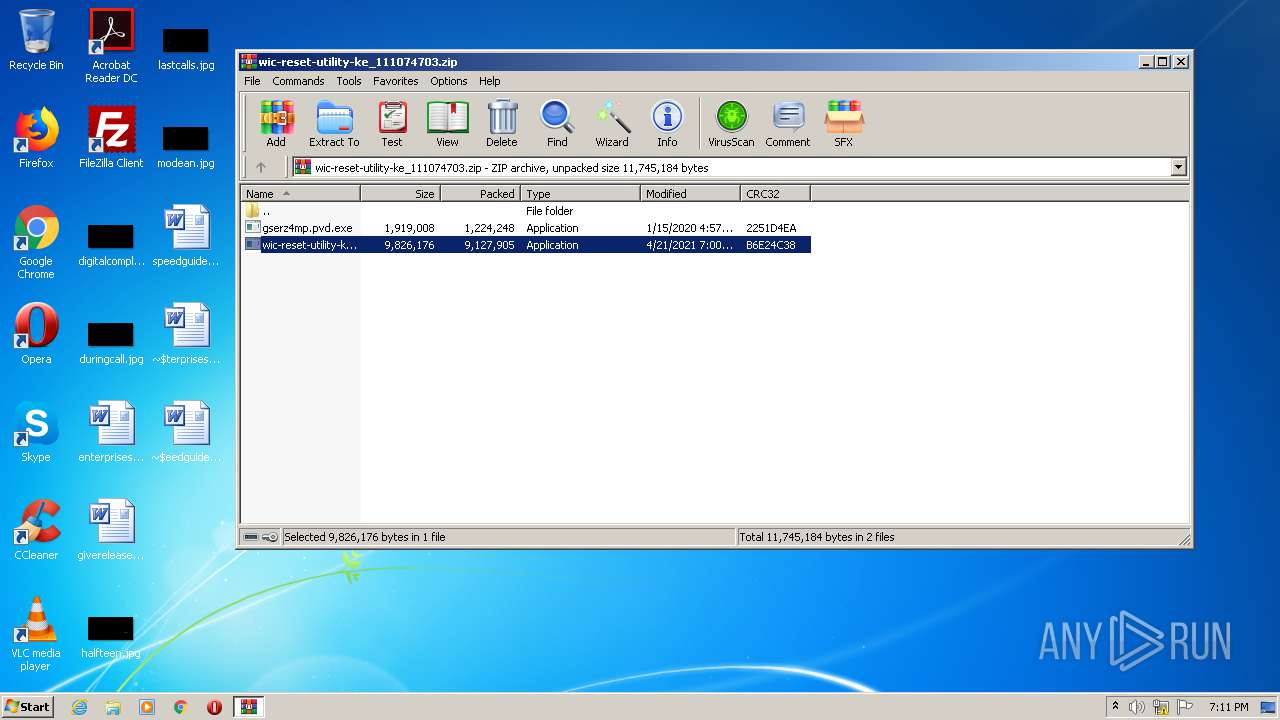
| File name: | wic-reset-utility-ke_111074703.zip |
| Full analysis: | https://app.any.run/tasks/b6c730b9-91de-4dec-9b36-b3dbb902c741 |
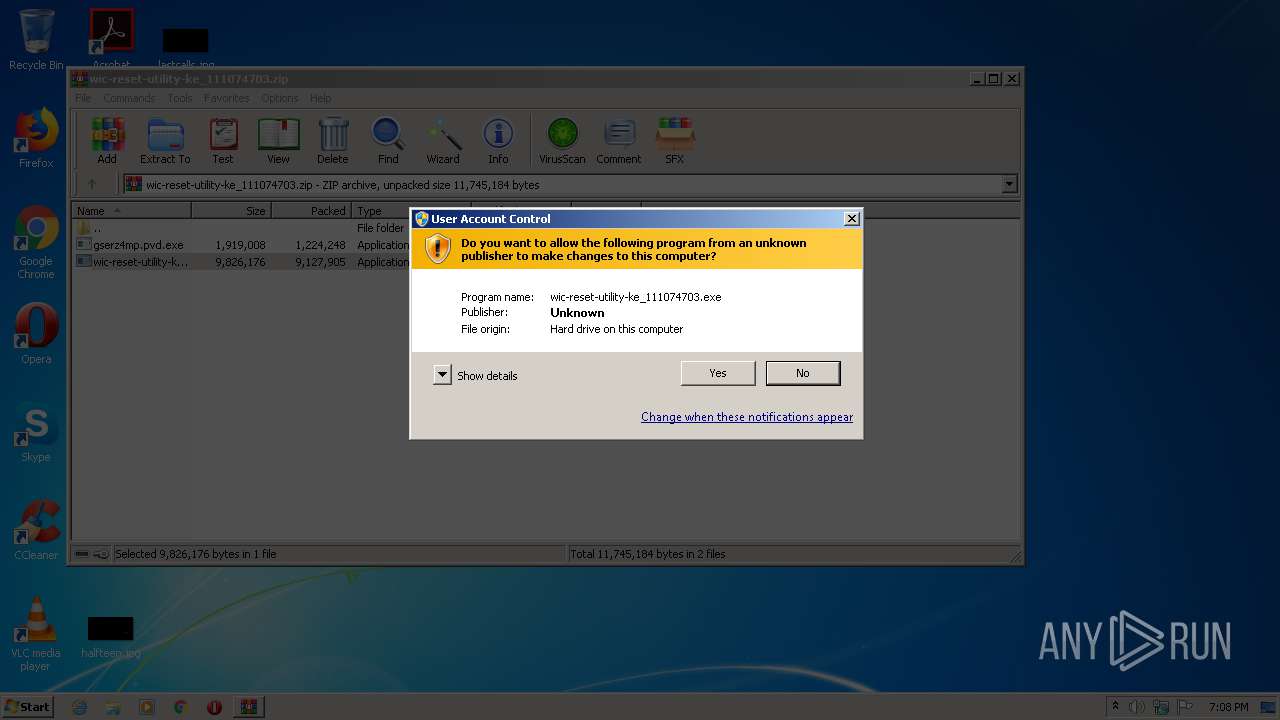
| Verdict: | Malicious activity |
| Analysis date: | April 21, 2021, 18:08:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | E2DB2FD76DA84D45AA6FF93F90FA90B0 |
| SHA1: | 3B826552927C973E994108FE18EC0629A0160DD8 |
| SHA256: | FA279D2331843E6C70157FDA598813E5A904704F1B01B44768D0A8157B47CEC3 |
| SSDEEP: | 196608:InMsuVEFPBL23f68+hjKFhqdgbJlhD4mK977Rzq7IH2r6dKx7pNzyd:IneW1BL23i/hwhqeHhDUy7MdALs |
MALICIOUS
Application was dropped or rewritten from another process
- wic-reset-utility-ke_111074703.exe (PID: 2160)
- wic-reset-utility-ke_111074703.exe (PID: 3712)
- wmfdist.exe (PID: 1912)
- AweClone.exe (PID: 2828)
- AweClone.exe (PID: 756)
- AweClone.exe (PID: 2848)
- AweClone.exe (PID: 1568)
- AweClone.exe (PID: 3428)
Drops executable file immediately after starts
- wic-reset-utility-ke_111074703.exe (PID: 2160)
- wic-reset-utility-ke_111074703.tmp (PID: 2076)
- wic-reset-utility-ke_111074703.exe (PID: 3712)
SUSPICIOUS
Executable content was dropped or overwritten
- wic-reset-utility-ke_111074703.exe (PID: 2160)
- WinRAR.exe (PID: 2132)
- wic-reset-utility-ke_111074703.exe (PID: 3712)
- wic-reset-utility-ke_111074703.tmp (PID: 2076)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 2132)
- wic-reset-utility-ke_111074703.tmp (PID: 2076)
Reads Windows owner or organization settings
- wic-reset-utility-ke_111074703.tmp (PID: 2076)
Reads the Windows organization settings
- wic-reset-utility-ke_111074703.tmp (PID: 2076)
Drops a file with too old compile date
- wic-reset-utility-ke_111074703.tmp (PID: 2076)
Drops a file with a compile date too recent
- wic-reset-utility-ke_111074703.tmp (PID: 2076)
Creates a directory in Program Files
- wic-reset-utility-ke_111074703.tmp (PID: 2076)
Executed via COM
- DllHost.exe (PID: 300)
INFO
Application was dropped or rewritten from another process
- wic-reset-utility-ke_111074703.tmp (PID: 3376)
- wic-reset-utility-ke_111074703.tmp (PID: 2076)
Dropped object may contain Bitcoin addresses
- wic-reset-utility-ke_111074703.tmp (PID: 2076)
Creates files in the program directory
- wic-reset-utility-ke_111074703.tmp (PID: 2076)
Creates a software uninstall entry
- wic-reset-utility-ke_111074703.tmp (PID: 2076)
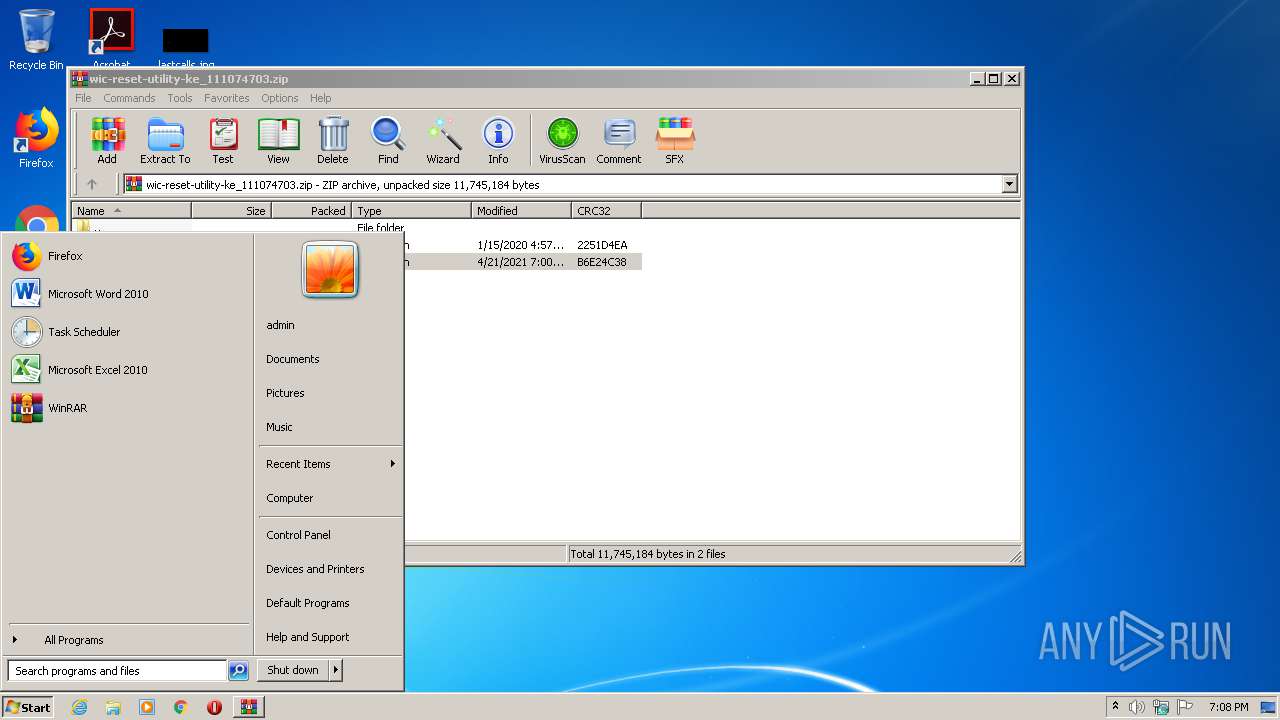
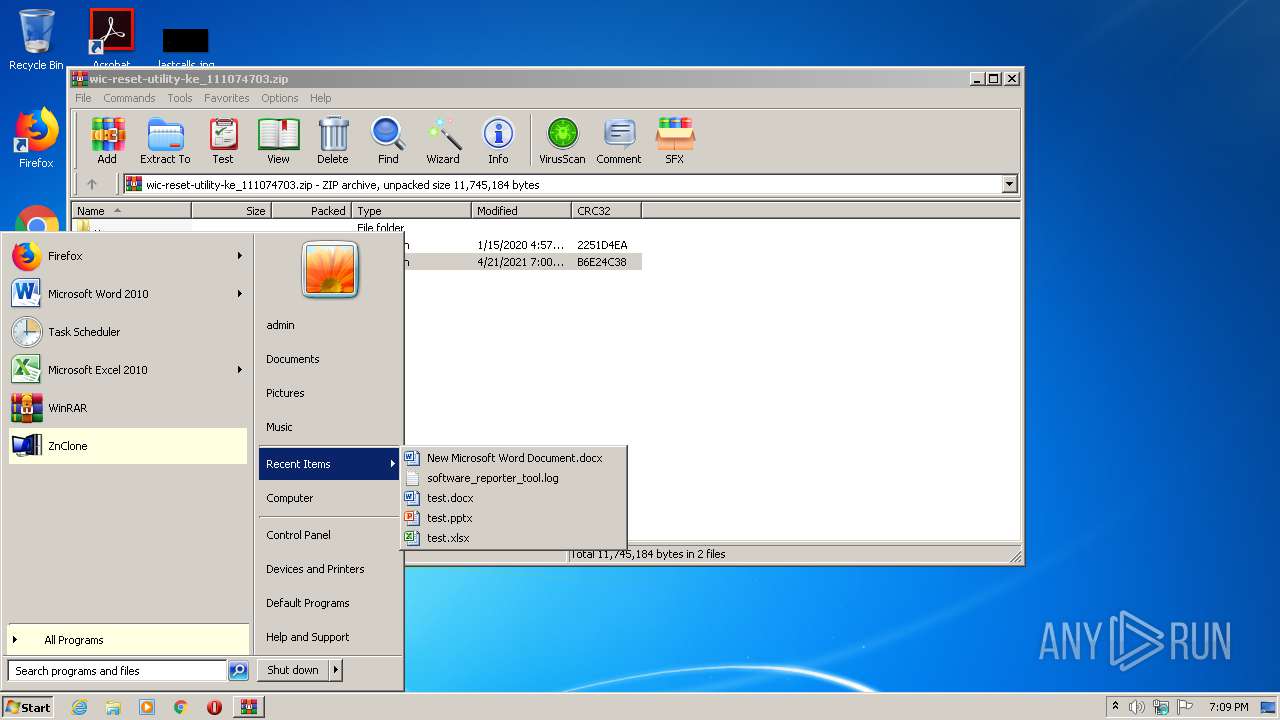
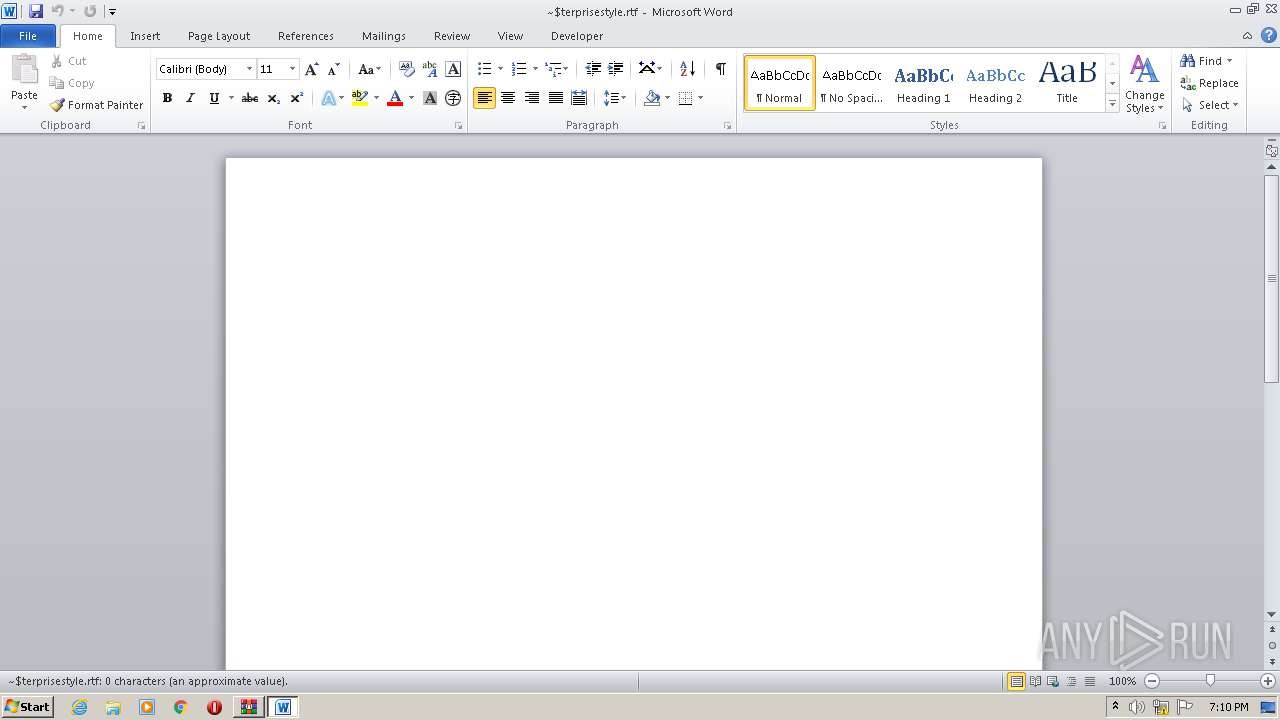
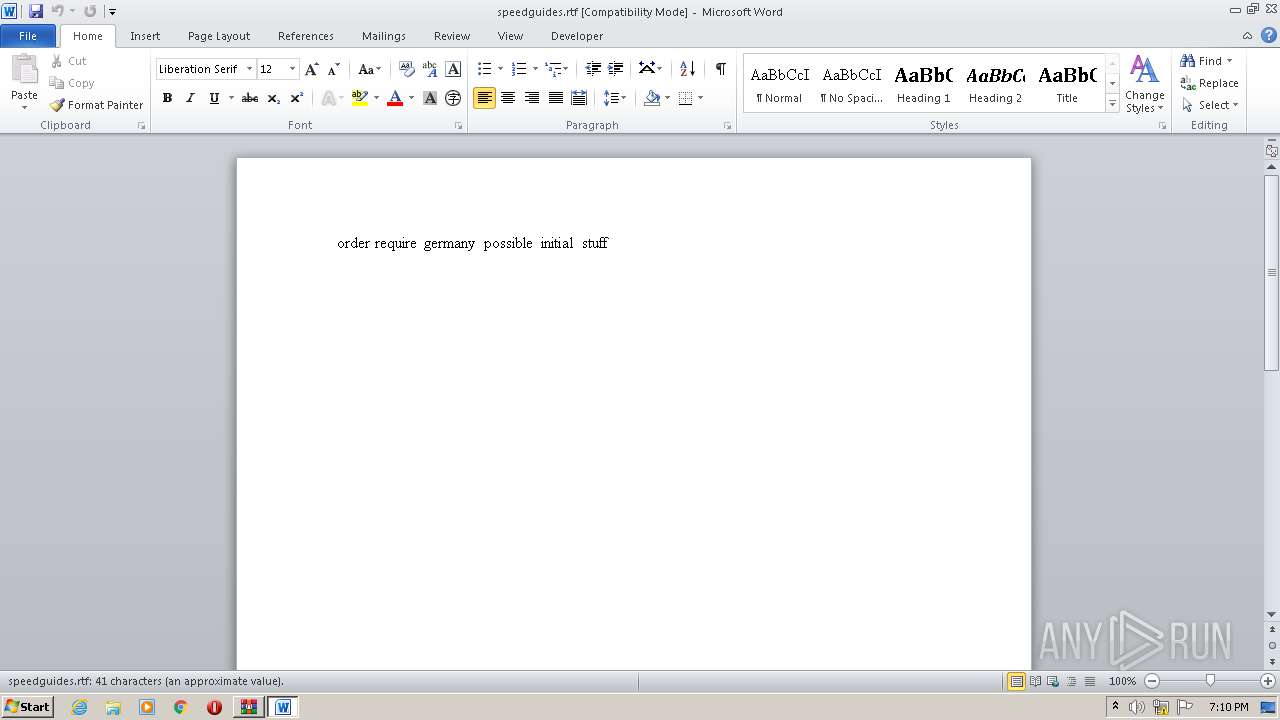
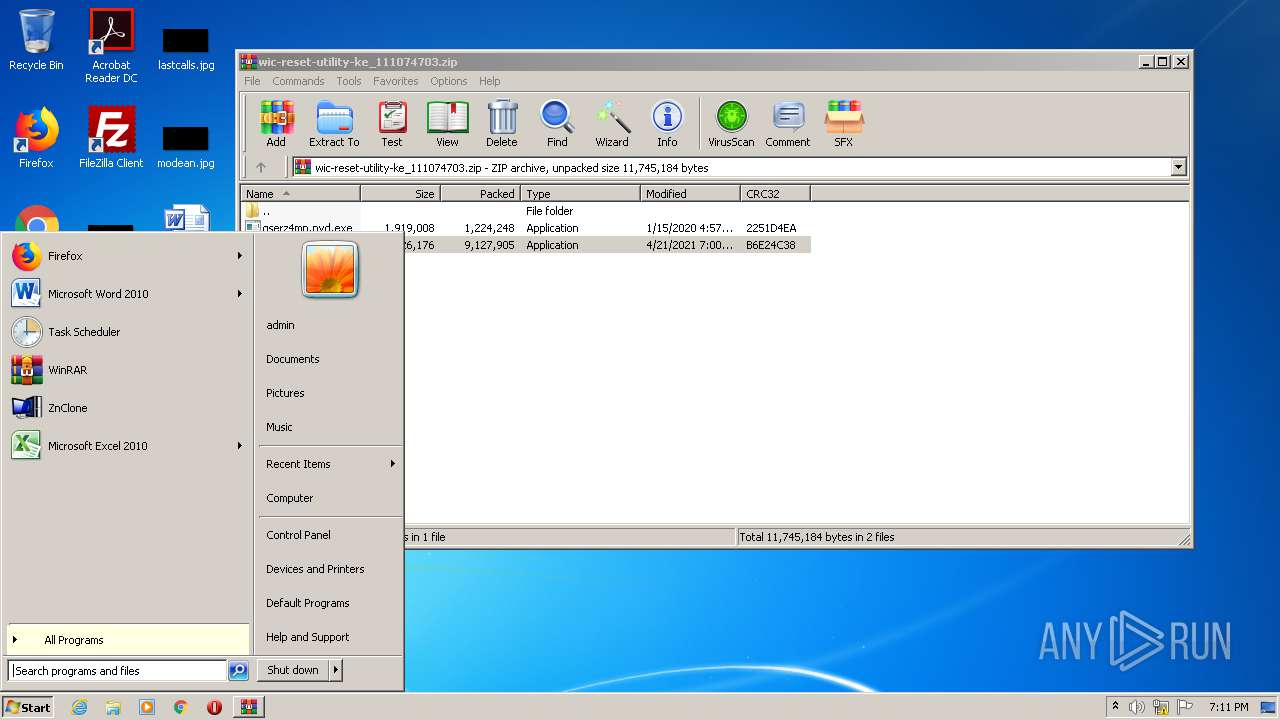
Manual execution by user
- AweClone.exe (PID: 756)
- WINWORD.EXE (PID: 3564)
- AweClone.exe (PID: 2848)
- WINWORD.EXE (PID: 1588)
- WINWORD.EXE (PID: 1820)
- AweClone.exe (PID: 1568)
- WINWORD.EXE (PID: 4084)
- AweClone.exe (PID: 3428)
- WINWORD.EXE (PID: 1388)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3564)
- WINWORD.EXE (PID: 1588)
- WINWORD.EXE (PID: 4084)
- WINWORD.EXE (PID: 1388)
- WINWORD.EXE (PID: 1820)
Creates files in the user directory
- WINWORD.EXE (PID: 3564)
- WINWORD.EXE (PID: 1588)
- WINWORD.EXE (PID: 1388)
- WINWORD.EXE (PID: 4084)
- WINWORD.EXE (PID: 1820)
Loads dropped or rewritten executable
- wic-reset-utility-ke_111074703.tmp (PID: 2076)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
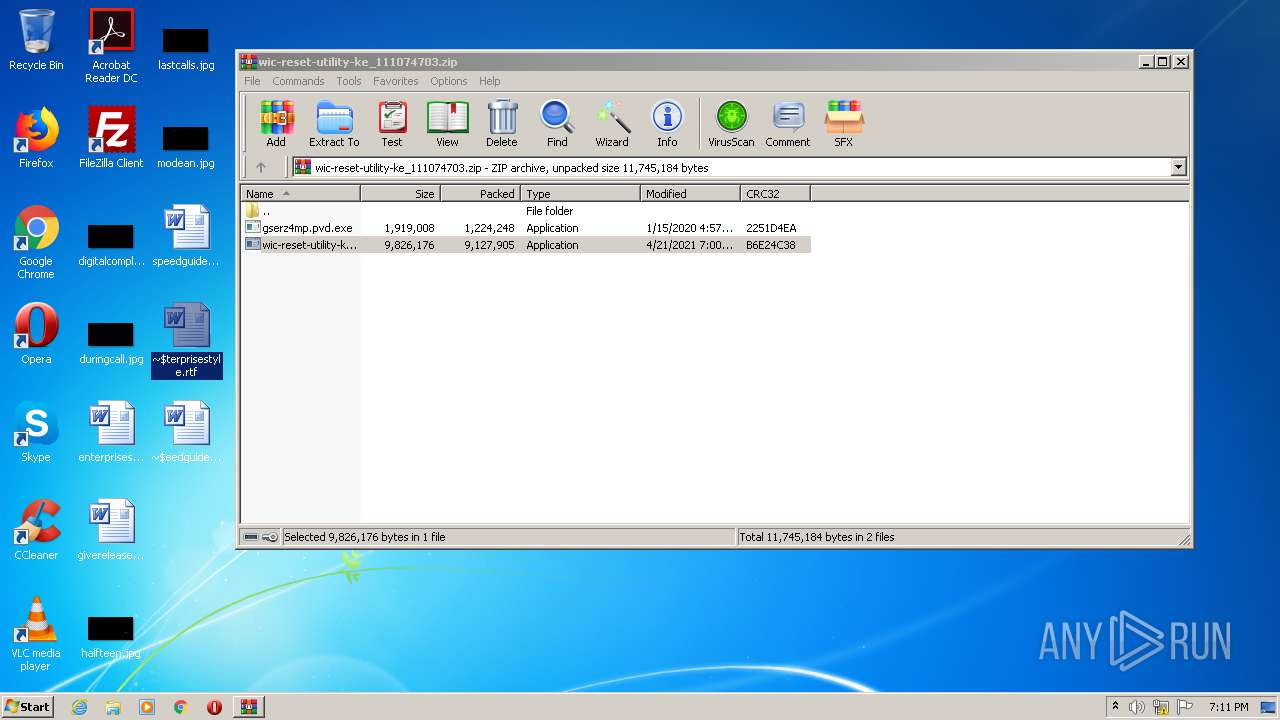
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:01:15 19:57:05 |
| ZipCRC: | 0x2251d4ea |
| ZipCompressedSize: | 1224248 |
| ZipUncompressedSize: | 1919008 |
| ZipFileName: | gserz4mp.pvd.exe |
Total processes
60
Monitored processes
17
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | C:\Windows\system32\DllHost.exe /Processid:{76D0CB12-7604-4048-B83C-1005C7DDC503} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 756 | "C:\Program Files\ZnClone\bin\AweClone.exe" | C:\Program Files\ZnClone\bin\AweClone.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: CloseApplication Exit code: 255 Version: 1.0.0.0 Modules
| |||||||||||||||
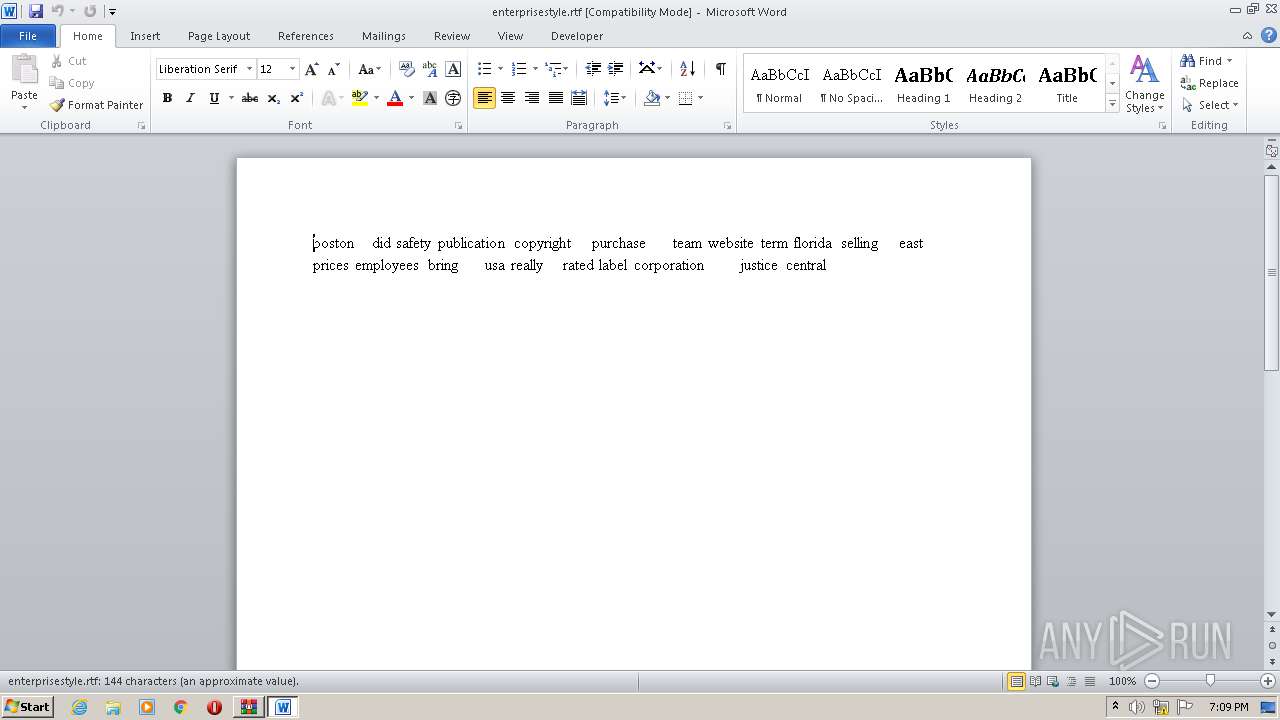
| 1388 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\~$terprisestyle.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1568 | "C:\Program Files\ZnClone\bin\AweClone.exe" | C:\Program Files\ZnClone\bin\AweClone.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: CloseApplication Exit code: 255 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1588 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\~$terprisestyle.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1820 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\speedguides.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1912 | "C:\Program Files\ZnClone\bin\wmfdist.exe" /Q:A /R:N | C:\Program Files\ZnClone\bin\wmfdist.exe | — | wic-reset-utility-ke_111074703.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Media Component Setup Application Exit code: 0 Version: 9.00.00.2926 Modules
| |||||||||||||||
| 2076 | "C:\Users\admin\AppData\Local\Temp\is-VOVRB.tmp\wic-reset-utility-ke_111074703.tmp" /SL5="$30176,9065752,1017344,C:\Users\admin\AppData\Local\Temp\Rar$EXa2132.35962\wic-reset-utility-ke_111074703.exe" /SPAWNWND=$20178 /NOTIFYWND=$3015A | C:\Users\admin\AppData\Local\Temp\is-VOVRB.tmp\wic-reset-utility-ke_111074703.tmp | wic-reset-utility-ke_111074703.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
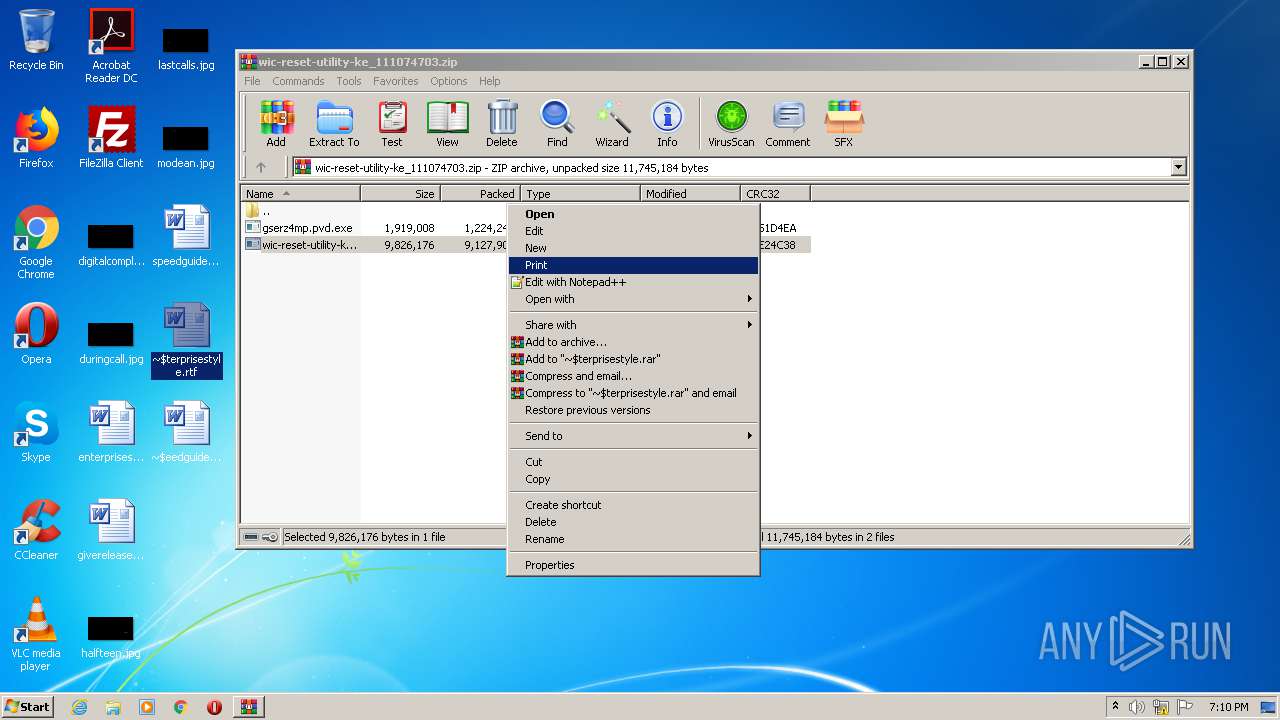
| 2132 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\wic-reset-utility-ke_111074703.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2160 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2132.35962\wic-reset-utility-ke_111074703.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2132.35962\wic-reset-utility-ke_111074703.exe | WinRAR.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: development framework. Exit code: 0 Version: Modules
| |||||||||||||||
Total events
6 794
Read events
4 861
Write events
1 223
Delete events
710
Modification events
| (PID) Process: | (2132) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2132) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2132) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2132) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (2132) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\wic-reset-utility-ke_111074703.zip | |||
| (PID) Process: | (2132) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2132) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2132) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2132) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2132) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
22
Suspicious files
2
Text files
26
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2076 | wic-reset-utility-ke_111074703.tmp | C:\Program Files\ZnClone\is-7E5LR.tmp | — | |
MD5:— | SHA256:— | |||
| 2076 | wic-reset-utility-ke_111074703.tmp | C:\Program Files\ZnClone\bin\is-MQ0RB.tmp | — | |
MD5:— | SHA256:— | |||
| 2076 | wic-reset-utility-ke_111074703.tmp | C:\Program Files\ZnClone\bin\is-1O6O7.tmp | — | |
MD5:— | SHA256:— | |||
| 2076 | wic-reset-utility-ke_111074703.tmp | C:\Program Files\ZnClone\bin\is-272ER.tmp | — | |
MD5:— | SHA256:— | |||
| 2076 | wic-reset-utility-ke_111074703.tmp | C:\Program Files\ZnClone\bin\is-TNBV6.tmp | — | |
MD5:— | SHA256:— | |||
| 2076 | wic-reset-utility-ke_111074703.tmp | C:\Program Files\ZnClone\bin\is-NDUD3.tmp | — | |
MD5:— | SHA256:— | |||
| 2076 | wic-reset-utility-ke_111074703.tmp | C:\Program Files\ZnClone\bin\is-BSGVT.tmp | — | |
MD5:— | SHA256:— | |||
| 2076 | wic-reset-utility-ke_111074703.tmp | C:\Program Files\ZnClone\bin\is-DF606.tmp | — | |
MD5:— | SHA256:— | |||
| 2076 | wic-reset-utility-ke_111074703.tmp | C:\Program Files\ZnClone\bin\is-S7FCR.tmp | — | |
MD5:— | SHA256:— | |||
| 2076 | wic-reset-utility-ke_111074703.tmp | C:\Program Files\ZnClone\bin\is-7R84F.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report