| File name: | dotNetFx40_Full_setup.exe |
| Full analysis: | https://app.any.run/tasks/73b4a454-54b7-41d3-956d-3d19f28d134e |
| Verdict: | Malicious activity |
| Analysis date: | October 22, 2024, 06:19:51 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 53406E9988306CBD4537677C5336ABA4 |
| SHA1: | 06BECADB92A5FCCA2529C0B93687C2A0C6D0D610 |
| SHA256: | FA1AFFF978325F8818CE3A559D67A58297D9154674DE7FD8EB03656D93104425 |
| SSDEEP: | 24576:+tW4x8xAxCdUcyezFSjaBHFaNlsqK5/oh6iZf1LUXw/vxNI:d4x8xqCGexm8FCspg0iZf1LUXD |
MALICIOUS
No malicious indicators.SUSPICIOUS
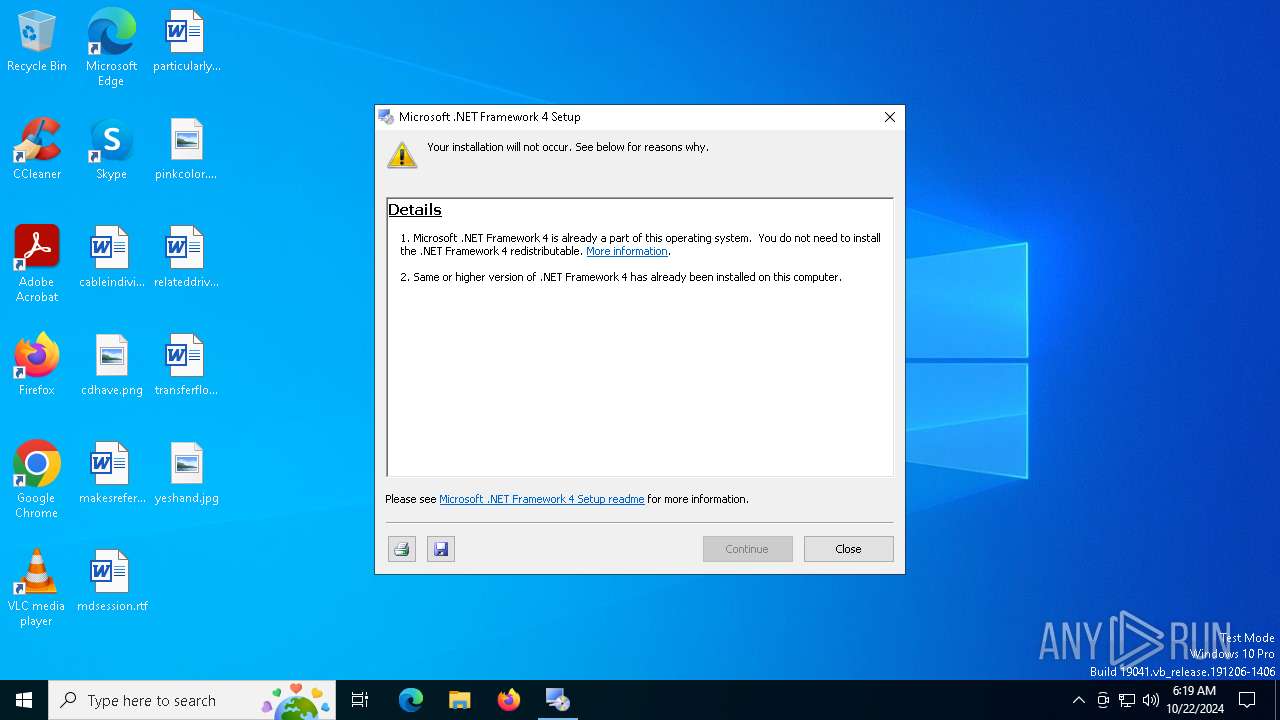
Starts a Microsoft application from unusual location
- dotNetFx40_Full_setup.exe (PID: 1176)
- dotNetFx40_Full_setup.exe (PID: 6456)
Process drops legitimate windows executable
- dotNetFx40_Full_setup.exe (PID: 1176)
Creates file in the systems drive root
- dotNetFx40_Full_setup.exe (PID: 1176)
Executable content was dropped or overwritten
- dotNetFx40_Full_setup.exe (PID: 1176)
INFO
Create files in a temporary directory
- dotNetFx40_Full_setup.exe (PID: 1176)
- Setup.exe (PID: 3128)
Checks supported languages
- dotNetFx40_Full_setup.exe (PID: 1176)
- Setup.exe (PID: 3128)
Reads the machine GUID from the registry
- dotNetFx40_Full_setup.exe (PID: 1176)
Reads the computer name
- Setup.exe (PID: 3128)
- dotNetFx40_Full_setup.exe (PID: 1176)
Reads CPU info
- Setup.exe (PID: 3128)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:10:09 19:27:34+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 165376 |
| InitializedDataSize: | 24064 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x191c6 |
| OSVersion: | 5.1 |
| ImageVersion: | 10 |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.0.30319.1 |
| ProductVersionNumber: | 4.0.30319.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Microsoft .NET Framework 4 Setup |
| FileVersion: | 4.0.30319.01 |
| InternalName: | dotNetFx40_Full_setup.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | dotNetFx40_Full_setup.exe |
| ProductName: | Microsoft .NET Framework 4 |
| ProductVersion: | 4.0.30319.01 |
Total processes
140
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
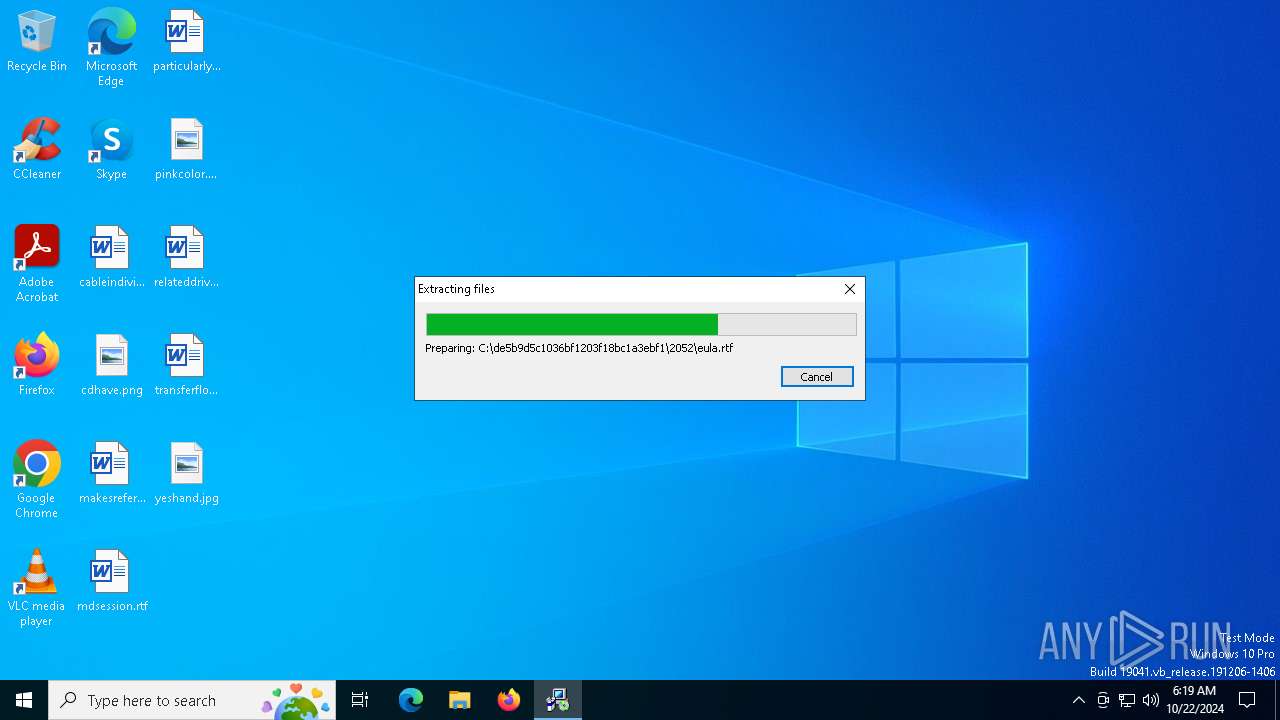
| 1176 | "C:\Users\admin\AppData\Local\Temp\dotNetFx40_Full_setup.exe" | C:\Users\admin\AppData\Local\Temp\dotNetFx40_Full_setup.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Framework 4 Setup Version: 4.0.30319.01 Modules
| |||||||||||||||
| 1712 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3128 | C:\de5b9d5c1036bf1203f18bc1a3ebf1\\Setup.exe /x86 /x64 /ia64 /web | C:\de5b9d5c1036bf1203f18bc1a3ebf1\Setup.exe | — | dotNetFx40_Full_setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Setup Installer Version: 10.0.30319.1 built by: RTMRel Modules
| |||||||||||||||
| 5532 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6456 | "C:\Users\admin\AppData\Local\Temp\dotNetFx40_Full_setup.exe" | C:\Users\admin\AppData\Local\Temp\dotNetFx40_Full_setup.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Framework 4 Setup Exit code: 3221226540 Version: 4.0.30319.01 Modules
| |||||||||||||||
Total events
257
Read events
257
Write events
0
Delete events
0
Modification events
Executable files
30
Suspicious files
0
Text files
81
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1176 | dotNetFx40_Full_setup.exe | C:\de5b9d5c1036bf1203f18bc1a3ebf1\watermark.bmp | image | |
MD5:B0075CEE80173D764C0237E840BA5879 | SHA256:AB18374B3AAB10E5979E080D0410579F9771DB888BA1B80A5D81BA8896E2D33A | |||
| 1176 | dotNetFx40_Full_setup.exe | C:\de5b9d5c1036bf1203f18bc1a3ebf1\SplashScreen.bmp | image | |
MD5:0966FCD5A4AB0DDF71F46C01EFF3CDD5 | SHA256:31C13ECFC0EB27F34036FB65CC0E735CD444EEC75376EEA2642F926AC162DCB3 | |||
| 1176 | dotNetFx40_Full_setup.exe | C:\de5b9d5c1036bf1203f18bc1a3ebf1\header.bmp | image | |
MD5:514BFCD8DA66722A9639EB41ED3988B7 | SHA256:6B8201ED10CE18FFADE072B77C6D1FCACCF1D29ACB47D86F553D9BEEBD991290 | |||
| 1176 | dotNetFx40_Full_setup.exe | C:\de5b9d5c1036bf1203f18bc1a3ebf1\Graphics\Rotate4.ico | image | |
MD5:BB55B5086A9DA3097FB216C065D15709 | SHA256:8D82FF7970C9A67DA8134686560FE3A6C986A160CED9D1CC1392F2BA75C698AB | |||
| 1176 | dotNetFx40_Full_setup.exe | C:\de5b9d5c1036bf1203f18bc1a3ebf1\Graphics\Save.ico | image | |
MD5:7D62E82D960A938C98DA02B1D5201BD5 | SHA256:AE041C8764F56FD89277B34982145D16FC59A4754D261C861B19371C3271C6E5 | |||
| 1176 | dotNetFx40_Full_setup.exe | C:\de5b9d5c1036bf1203f18bc1a3ebf1\Graphics\Setup.ico | image | |
MD5:3D25D679E0FF0B8C94273DCD8B07049D | SHA256:288E9AD8F0201E45BC187839F15ACA79D6B9F76A7D3C9274C80F5D4A4C219C0F | |||
| 1176 | dotNetFx40_Full_setup.exe | C:\de5b9d5c1036bf1203f18bc1a3ebf1\Graphics\SysReqNotMet.ico | image | |
MD5:EE2C05CC9D14C29F586D40EB90C610A9 | SHA256:3C9C71950857DDB82BAAB83ED70C496DEE8F20F3BC3216583DC1DDDA68AEFC73 | |||
| 1176 | dotNetFx40_Full_setup.exe | C:\de5b9d5c1036bf1203f18bc1a3ebf1\Graphics\stop.ico | image | |
MD5:5DFA8D3ABCF4962D9EC41CFC7C0F75E3 | SHA256:B499E1B21091B539D4906E45B6FDF490D5445256B72871AECE2F5B2562C11793 | |||
| 1176 | dotNetFx40_Full_setup.exe | C:\de5b9d5c1036bf1203f18bc1a3ebf1\Graphics\Rotate5.ico | image | |
MD5:3B4861F93B465D724C60670B64FCCFCF | SHA256:7237051D9AF5DB972A1FECF0B35CD8E9021471740782B0DBF60D3801DC9F5F75 | |||
| 1176 | dotNetFx40_Full_setup.exe | C:\de5b9d5c1036bf1203f18bc1a3ebf1\Graphics\Rotate2.ico | image | |
MD5:8419CAA81F2377E09B7F2F6218E505AE | SHA256:DB89D8A45C369303C04988322B2774D2C7888DA5250B4DAB2846DEEF58A7DE22 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
52
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6944 | svchost.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6384 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3952 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7144 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
3952 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7060 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6944 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6944 | svchost.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6944 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4360 | SearchApp.exe | 104.126.37.139:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |