| File name: | update.exe |
| Full analysis: | https://app.any.run/tasks/317c34fc-c549-4284-8e6b-7966e6a5a6b6 |
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2019, 16:25:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 470B4F5BC84DB74AB1935186A3B5219F |
| SHA1: | 522DA30DADF030861E51DA3EFAF25EA0E0619206 |
| SHA256: | FA0978B3D14458524BB235D6095358A27AF9F2E9281BE7CD0EB1A4D2123A8330 |
| SSDEEP: | 196608:eAqjTpnhXlmyWCZNulPKQ8hY/Bkr/fOIT/+VdlBFKaz:kfauN/HYOSIT/EVF9 |
MALICIOUS
Loads dropped or rewritten executable
- update.exe (PID: 1012)
- WMIC.exe (PID: 3760)
Starts NET.EXE to view/change users group
- cmd.exe (PID: 2900)
- cmd.exe (PID: 1824)
SUSPICIOUS
Application launched itself
- update.exe (PID: 2196)
Executable content was dropped or overwritten
- update.exe (PID: 2196)
Loads Python modules
- update.exe (PID: 1012)
Starts CMD.EXE for commands execution
- update.exe (PID: 1012)
Executes PowerShell scripts
- update.exe (PID: 1012)
Creates files in the user directory
- powershell.exe (PID: 1628)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:09:04 16:42:13+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 128000 |
| InitializedDataSize: | 172032 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x779a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 04-Sep-2018 14:42:13 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 04-Sep-2018 14:42:13 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001F224 | 0x0001F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.65269 |
.rdata | 0x00021000 | 0x0000B0EC | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.10091 |
.data | 0x0002D000 | 0x0000E680 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.94098 |
.gfids | 0x0003C000 | 0x000000B8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.89006 |
.rsrc | 0x0003D000 | 0x0000EA38 | 0x0000EC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.29706 |
.reloc | 0x0004C000 | 0x000017B8 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.65088 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.58652 | 3752 | UNKNOWN | UNKNOWN | RT_ICON |
2 | 6.05629 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 5.5741 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 7.95079 | 37019 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 5.29119 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 5.43869 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 5.89356 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
101 | 2.71858 | 104 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
KERNEL32.dll |
WS2_32.dll |
Total processes
45
Monitored processes
12
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
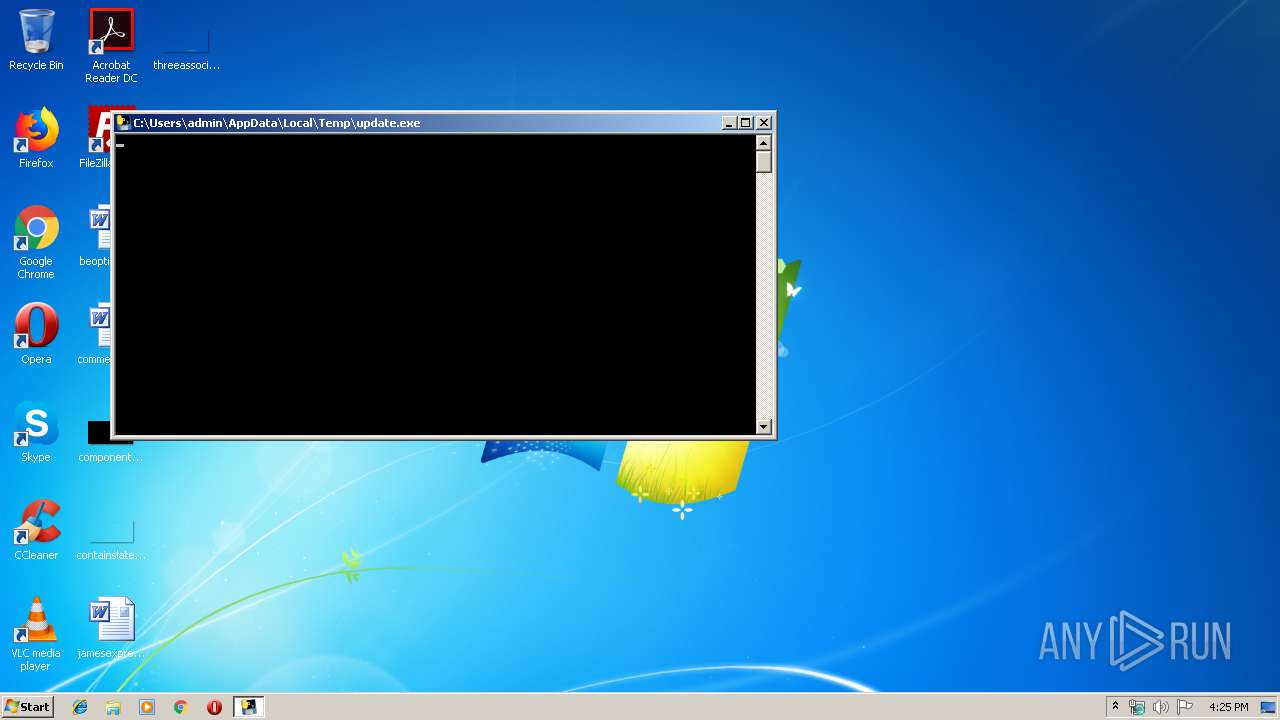
| 292 | "C:\Users\admin\AppData\Local\Temp\update.exe" | C:\Users\admin\AppData\Local\Temp\update.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1012 | "C:\Users\admin\AppData\Local\Temp\update.exe" | C:\Users\admin\AppData\Local\Temp\update.exe | — | update.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1628 | powershell.exe -exec bypass "import-module C:\Users\admin\AppData\Local\Temp\m2.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | update.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
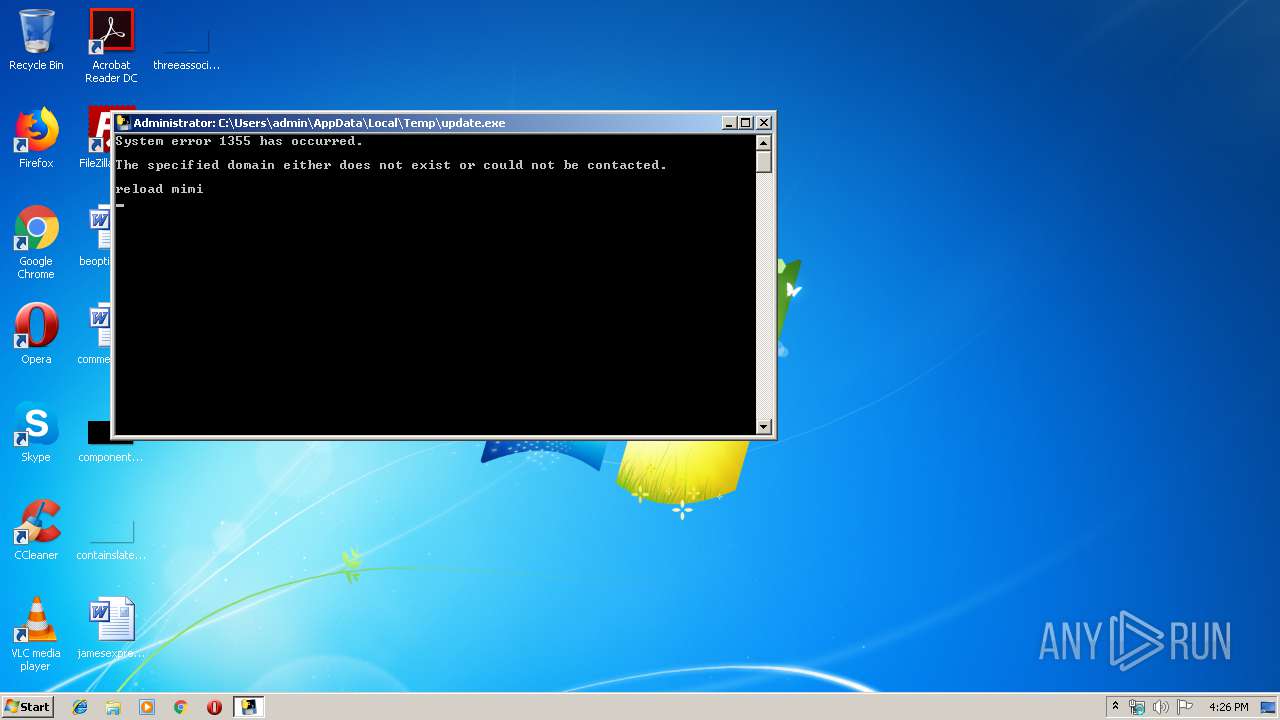
| 1824 | cmd /c net group "domain admins" /domain | C:\Windows\system32\cmd.exe | — | update.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2196 | "C:\Users\admin\AppData\Local\Temp\update.exe" | C:\Users\admin\AppData\Local\Temp\update.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2652 | net group "domain admins" /domain | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2776 | C:\Windows\system32\net1 group "domain admins" /domain | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2900 | cmd /c net localgroup administrators | C:\Windows\system32\cmd.exe | — | update.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3252 | net localgroup administrators | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3256 | cmd /c wmic ntdomain get domainname | C:\Windows\system32\cmd.exe | — | update.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
225
Read events
170
Write events
55
Delete events
0
Modification events
| (PID) Process: | (1628) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
28
Suspicious files
2
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2196 | update.exe | C:\Users\admin\AppData\Local\Temp\_MEI21962\Crypto.Cipher._ARC4.pyd | executable | |
MD5:8D85DBF6C981BFF4E8A1BEA86A0AC5E9 | SHA256:356623219B8C098435D511C0055C061018641D8B700EB089FC6FF87D233260E1 | |||
| 2196 | update.exe | C:\Users\admin\AppData\Local\Temp\_MEI21962\Crypto.Random.OSRNG.winrandom.pyd | executable | |
MD5:731A6B82B8475E383DAC97B20AEAB7F7 | SHA256:D710B5A398DD0DC128129F3B035D459D6860B5C45CCC8EE2066069202B9D1F30 | |||
| 2196 | update.exe | C:\Users\admin\AppData\Local\Temp\_MEI21962\Microsoft.VC90.CRT.manifest | xml | |
MD5:BFB93876892CCA8E2AD0021585C34C8B | SHA256:0D060ED7C25159B7B75F16D449963BFD639C15B3C5280BC7897403268C2B9F35 | |||
| 2196 | update.exe | C:\Users\admin\AppData\Local\Temp\_MEI21962\Crypto.Cipher._AES.pyd | executable | |
MD5:9FD78D7D6AB69AF5A14E0F29AFFD7EF4 | SHA256:87C920ED2C1AFCF295729563B4DEF671DC9E36EF8B3E183D4836571300180E74 | |||
| 2196 | update.exe | C:\Users\admin\AppData\Local\Temp\_MEI21962\_hashlib.pyd | executable | |
MD5:22071845DAF8C1F6E87F006673EED4FD | SHA256:51C47389782BC2DE8E401D231233E2E7F1A4B3AFCE7DF4DDF4AD533184DAD407 | |||
| 2196 | update.exe | C:\Users\admin\AppData\Local\Temp\_MEI21962\_socket.pyd | executable | |
MD5:B7C3E334648A6CBB03B550B842818409 | SHA256:F0781A1B879584F494D984E31869EAB13F0535825F68862E6597B1639DF708BD | |||
| 2196 | update.exe | C:\Users\admin\AppData\Local\Temp\_MEI21962\_ctypes.pyd | executable | |
MD5:98638A1BFDECDCECF4D7D47B521AC903 | SHA256:11C739D28227773D70C3941D2E979B9D4CEE12F1D53CC94DAF77B62A4D3A0327 | |||
| 2196 | update.exe | C:\Users\admin\AppData\Local\Temp\_MEI21962\Crypto.Cipher._DES.pyd | executable | |
MD5:4B7B86B41280DFD1E1D29A7F626393EF | SHA256:8B0F41FD5A3D78E7C4990B1DF3414C4FA221624444F318BB0A29F92F02B1A15E | |||
| 2196 | update.exe | C:\Users\admin\AppData\Local\Temp\_MEI21962\bz2.pyd | executable | |
MD5:0B1688C02640EC14D85E1CC3C93F7276 | SHA256:753EA279675EEB34FE58908F10CB15886955C865B49C01B533A5930E6B326038 | |||
| 2196 | update.exe | C:\Users\admin\AppData\Local\Temp\_MEI21962\ii.exe.manifest | xml | |
MD5:08458035409AF6BAEF39D93956F86E74 | SHA256:82517610333E631B6DF2D74E19F217D87824B0DFD39F9CDDDECB416F1EE66808 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report