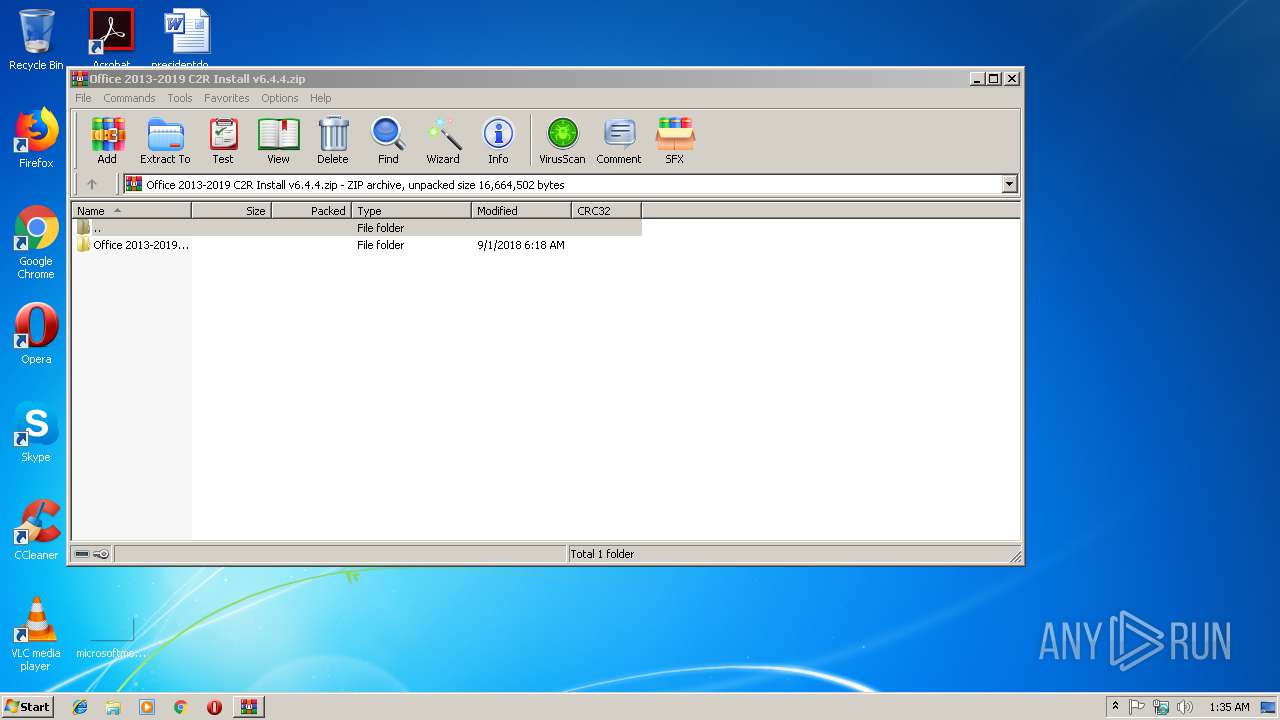
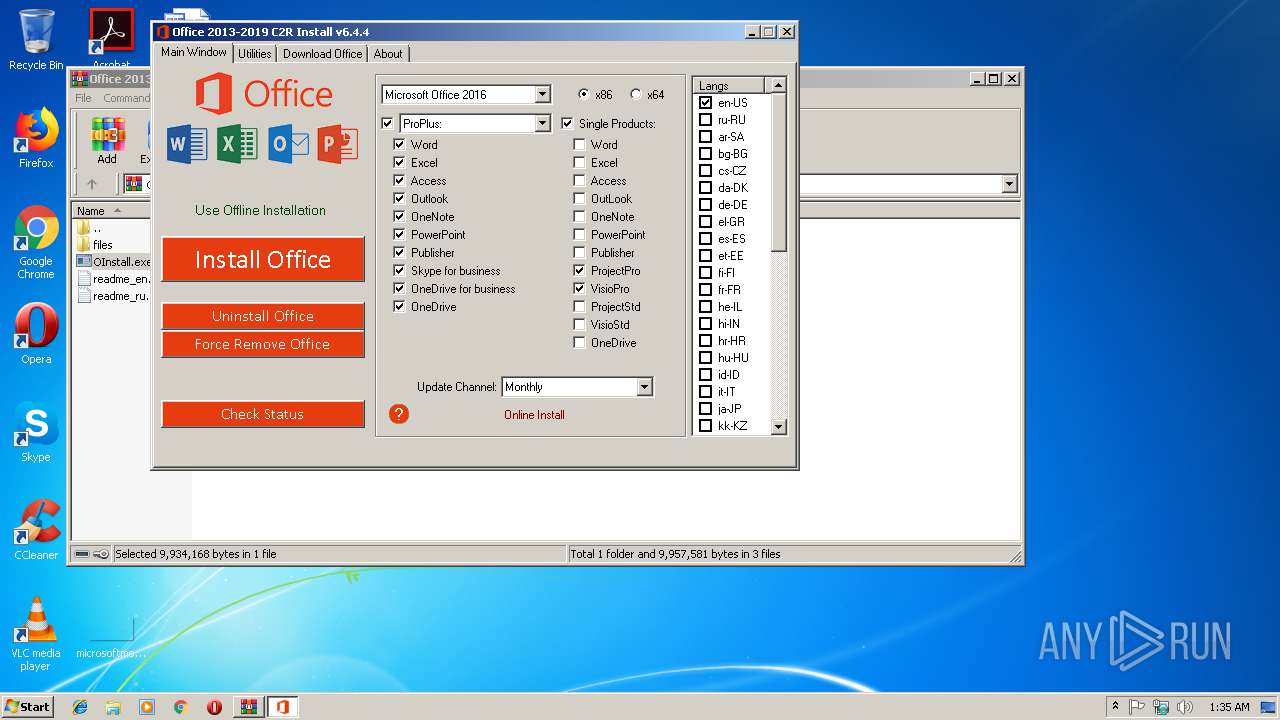
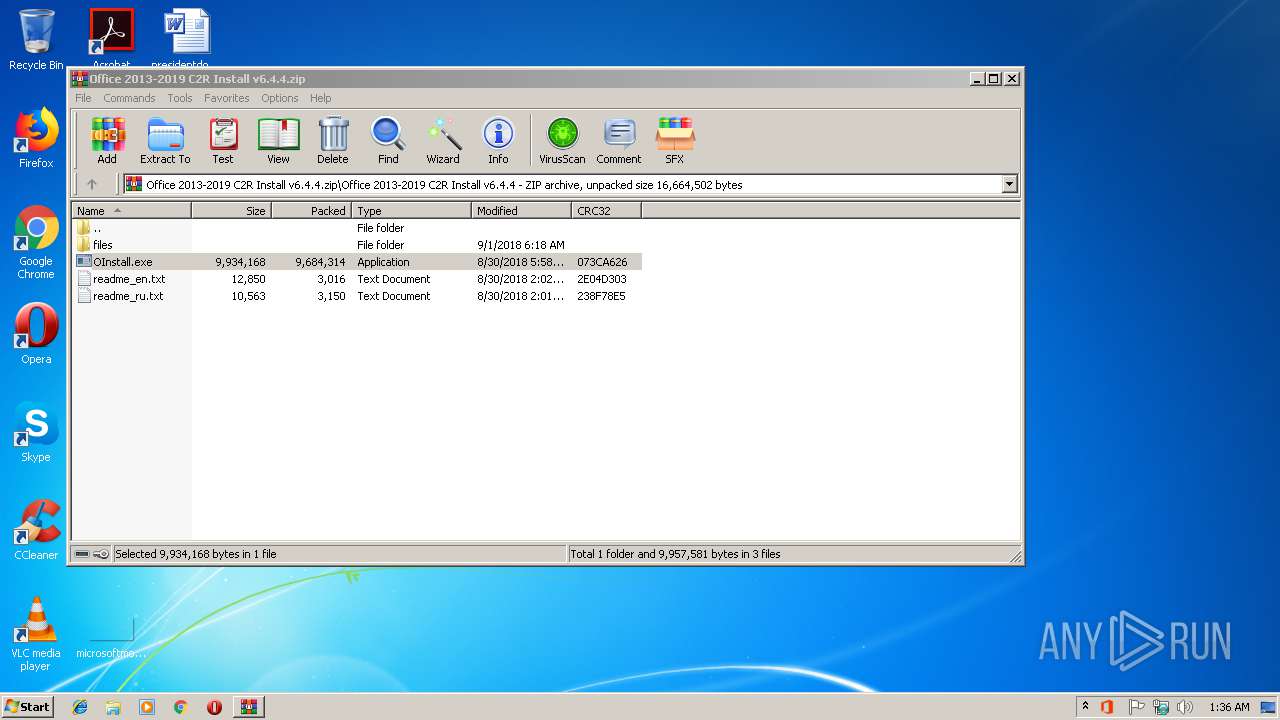
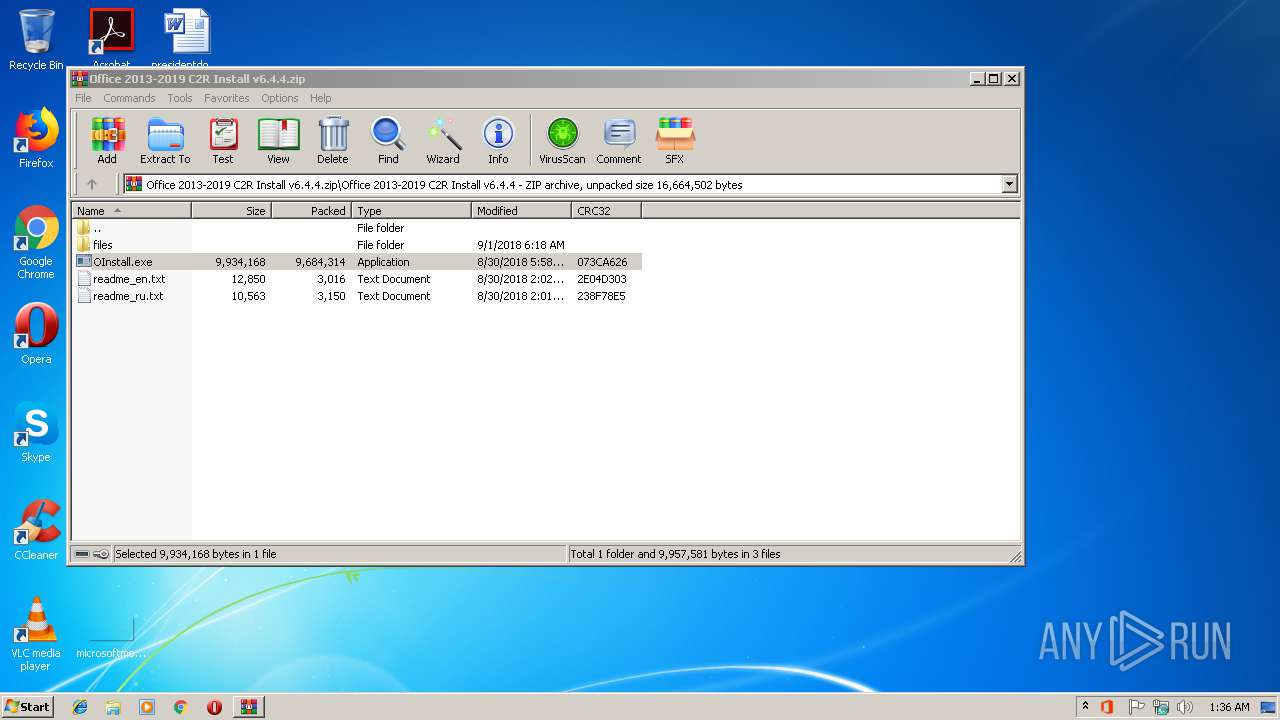
| File name: | Office 2013-2019 C2R Install v6.4.4.zip |
| Full analysis: | https://app.any.run/tasks/3b50f8fd-6f81-4ad6-9c4d-d02a243f73ca |
| Verdict: | Malicious activity |
| Analysis date: | February 08, 2019, 01:35:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 39BD4961FFFEED4556602628D858D2F9 |
| SHA1: | 5D2CA234D2D05017FB37379B7F003853A3428C3A |
| SHA256: | FA07CB20796000B002B1B4018BD21C7C664DD1E67B2C927811FB9F11158D9145 |
| SSDEEP: | 196608:Fi0DPHn+vZk0S7qBWTLGl1igWuzKf6Nof3iF0Le0Uos3jHOktmbl9oP8payOXDy1:nHn+hkgBWTLc195i6NnCXwz8pab+y8L |
MALICIOUS
Application was dropped or rewritten from another process
- OInstall.exe (PID: 2428)
- OInstall.exe (PID: 3412)
- setup.exe (PID: 3976)
- OfficeClickToRun.exe (PID: 1520)
- OfficeClickToRun.exe (PID: 3156)
Changes settings of System certificates
- setup.exe (PID: 3976)
- OfficeClickToRun.exe (PID: 3156)
Loads dropped or rewritten executable
- OfficeClickToRun.exe (PID: 1520)
- OfficeClickToRun.exe (PID: 3156)
SUSPICIOUS
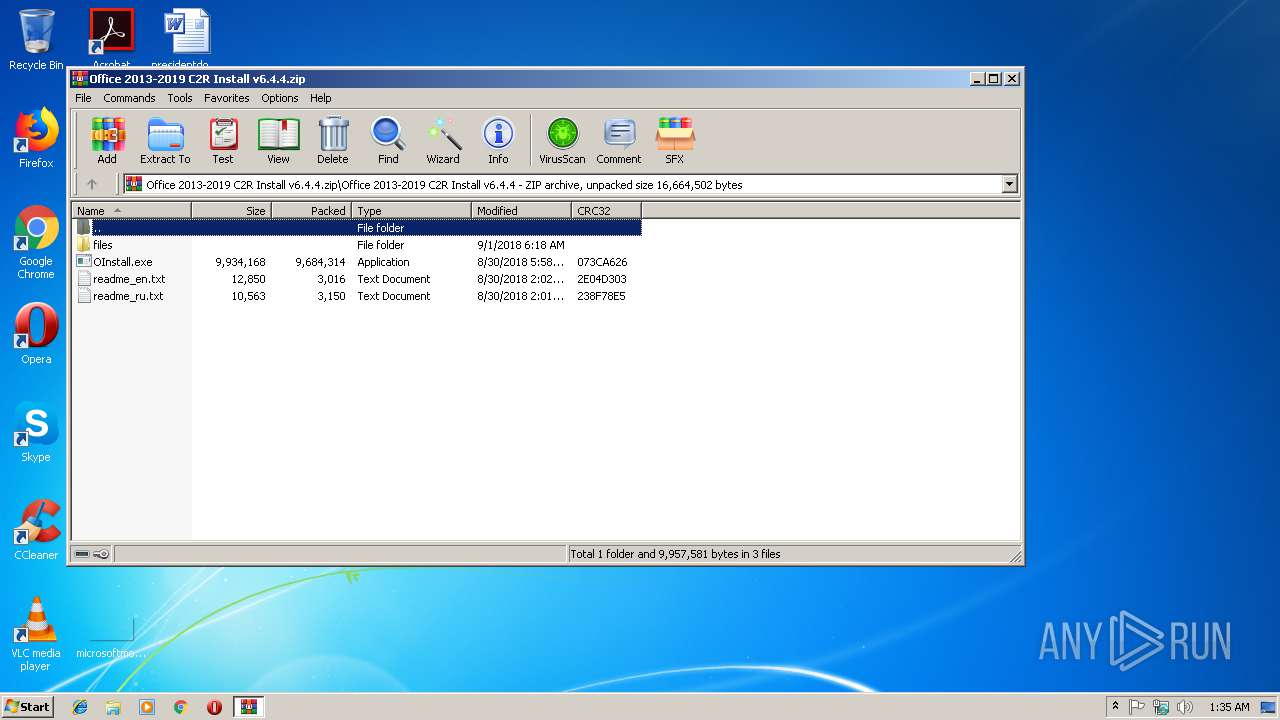
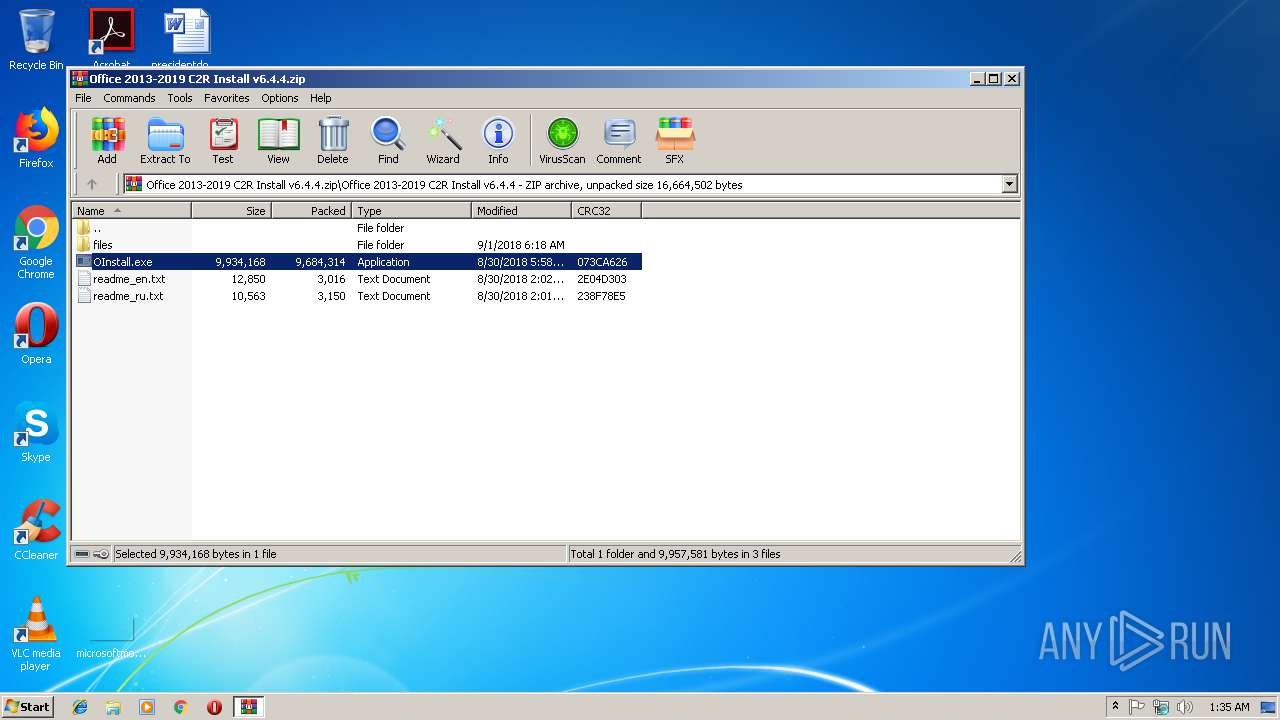
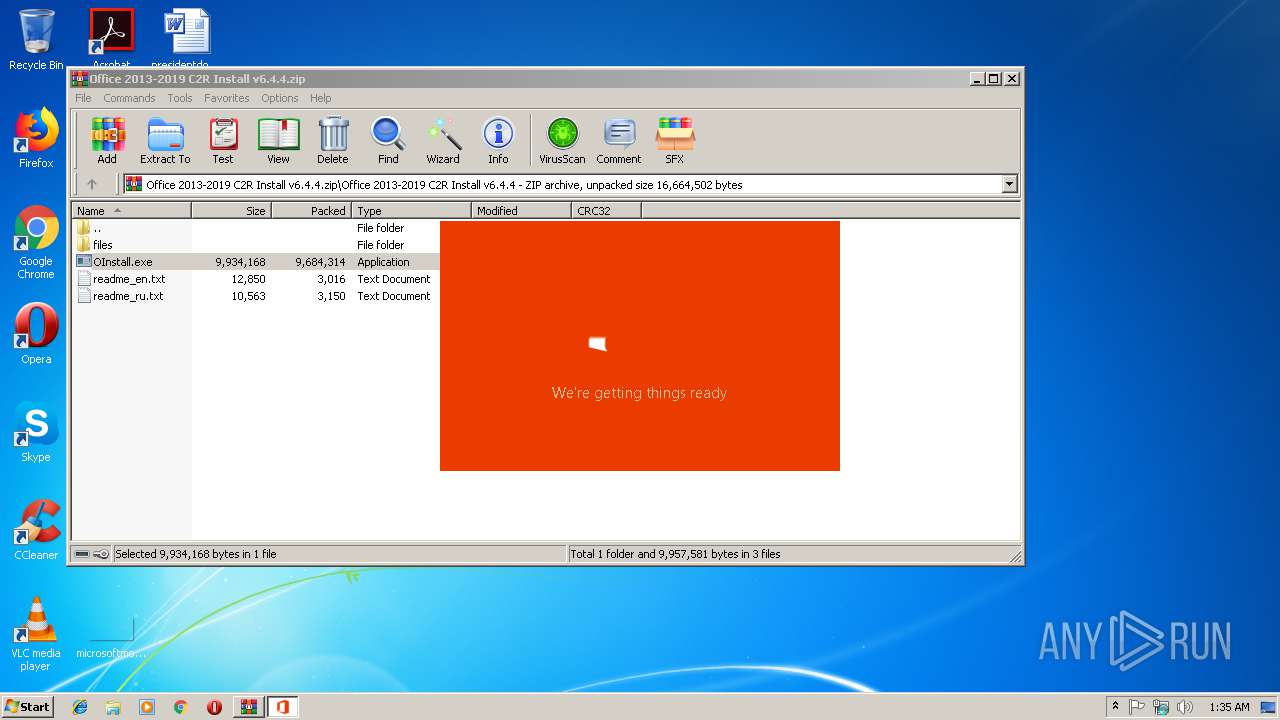
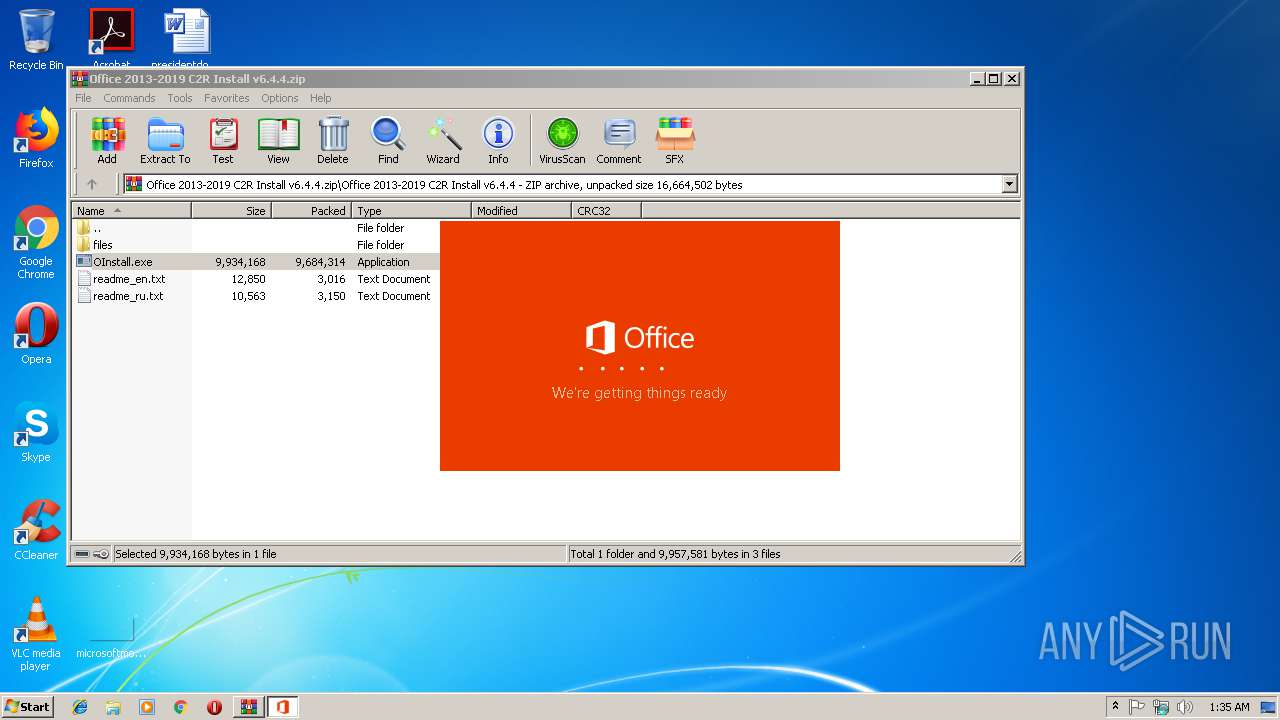
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3284)
- OInstall.exe (PID: 2428)
- OfficeClickToRun.exe (PID: 3156)
- setup.exe (PID: 3976)
Starts CMD.EXE for commands execution
- OInstall.exe (PID: 2428)
Searches for installed software
- setup.exe (PID: 3976)
Executes PowerShell scripts
- setup.exe (PID: 3976)
Reads Internet Cache Settings
- setup.exe (PID: 3976)
- OfficeClickToRun.exe (PID: 1520)
Adds / modifies Windows certificates
- setup.exe (PID: 3976)
- OfficeClickToRun.exe (PID: 3156)
Creates files in the user directory
- powershell.exe (PID: 1472)
Creates files in the Windows directory
- OfficeClickToRun.exe (PID: 3156)
Creates files in the program directory
- OfficeClickToRun.exe (PID: 3156)
- setup.exe (PID: 3976)
Removes files from Windows directory
- OfficeClickToRun.exe (PID: 3156)
INFO
Reads settings of System Certificates
- setup.exe (PID: 3976)
- OfficeClickToRun.exe (PID: 1520)
- OfficeClickToRun.exe (PID: 3156)
- chrome.exe (PID: 2252)
Reads Microsoft Office registry keys
- OfficeClickToRun.exe (PID: 3156)
- OfficeClickToRun.exe (PID: 1520)
Application launched itself
- chrome.exe (PID: 2252)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xpi | | | Mozilla Firefox browser extension (66.6) |
|---|---|---|
| .zip | | | ZIP compressed archive (33.3) |
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2018:09:01 08:18:10 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Office 2013-2019 C2R Install v6.4.4/ |
Total processes
52
Monitored processes
16
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1472 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -NonInteractive -WindowStyle Hidden -Command "& { $isOfficeInstalled = Get-AppxPackage Microsoft.Office.Desktop -allusers; if ($isOfficeInstalled -eq $null) { Out-File -FilePath 'C:\Users\admin\AppData\Local\Temp\Centennial.Detection.IsCentennialOfficeInstalled.scratch' -InputObject '0' -Encoding ascii; } else { Out-File -FilePath 'C:\Users\admin\AppData\Local\Temp\Centennial.Detection.IsCentennialOfficeInstalled.scratch' -InputObject '1' -Encoding ascii } }" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1520 | deliverymechanism=492350f6-3a01-4f97-b9c0-c7c6ddf67d60 platform=x86 productreleaseid=none forcecentcheck= culture=en-us defaultplatform=False storeid= lcid=1033 b= totalclientcabsize=19396517 productstoadd=ProjectProRetail.16_en-us_x-none|ProplusRetail.16_en-us_x-none|VisioProRetail.16_en-us_x-none scenariosubtype=ODT scenario=unknown updatesenabled.16=True acceptalleulas.16=True cdnbaseurl.16=http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60 version.16=16.0.11231.20130 mediatype.16=CDN visioproretail.excludedapps.16=onedrive baseurl.16=http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60 projectproretail.excludedapps.16=onedrive sourcetype.16=CDN flt.useexptransportinplacepl=unknown flt.useaddons=unknown flt.useofficehelperaddon=unknown flt.useonedriveclientaddon=unknown flt.useoutlookshareaddon=unknown | C:\Program Files\Common Files\Microsoft Shared\ClickToRun\OfficeClickToRun.exe | setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Office Click-to-Run (SxS) Exit code: 0 Version: 16.0.11231.20122 Modules
| |||||||||||||||
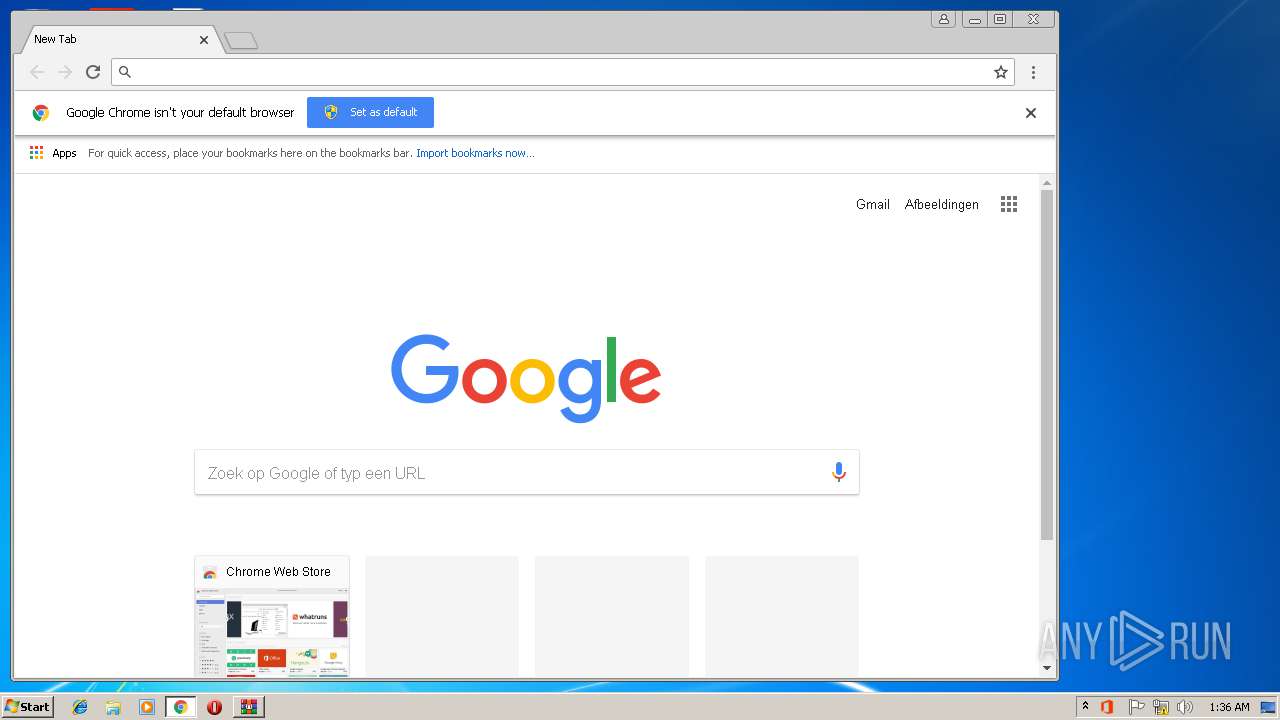
| 2252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=188,8795939425079610089,13429053483518042225,131072 --enable-features=PasswordImport --service-pipe-token=9574E388FE3CAF2479D0018580AC976D --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9574E388FE3CAF2479D0018580AC976D --renderer-client-id=5 --mojo-platform-channel-handle=996 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2428 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3284.24930\Office 2013-2019 C2R Install v6.4.4\OInstall.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3284.24930\Office 2013-2019 C2R Install v6.4.4\OInstall.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Office 2013-2016 C2R Install Exit code: 0 Modules
| |||||||||||||||
| 2452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=188,8795939425079610089,13429053483518042225,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=E8C7ECB034CC1C60AD83F91BCBD32C5E --mojo-platform-channel-handle=1020 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2292 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=188,8795939425079610089,13429053483518042225,131072 --enable-features=PasswordImport --service-pipe-token=E3FC6576797BAA20EA6BDA961114F007 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=E3FC6576797BAA20EA6BDA961114F007 --renderer-client-id=3 --mojo-platform-channel-handle=2084 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3156 | "C:\Program Files\Common Files\Microsoft Shared\ClickToRun\OfficeClickToRun.exe" /service | C:\Program Files\Common Files\Microsoft Shared\ClickToRun\OfficeClickToRun.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Office Click-to-Run (SxS) Exit code: 0 Version: 16.0.11231.20122 Modules
| |||||||||||||||
| 3188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=188,8795939425079610089,13429053483518042225,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=A08D961A9B33C237D61D0A698C15729E --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=A08D961A9B33C237D61D0A698C15729E --renderer-client-id=6 --mojo-platform-channel-handle=3592 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
1 541
Read events
1 147
Write events
363
Delete events
31
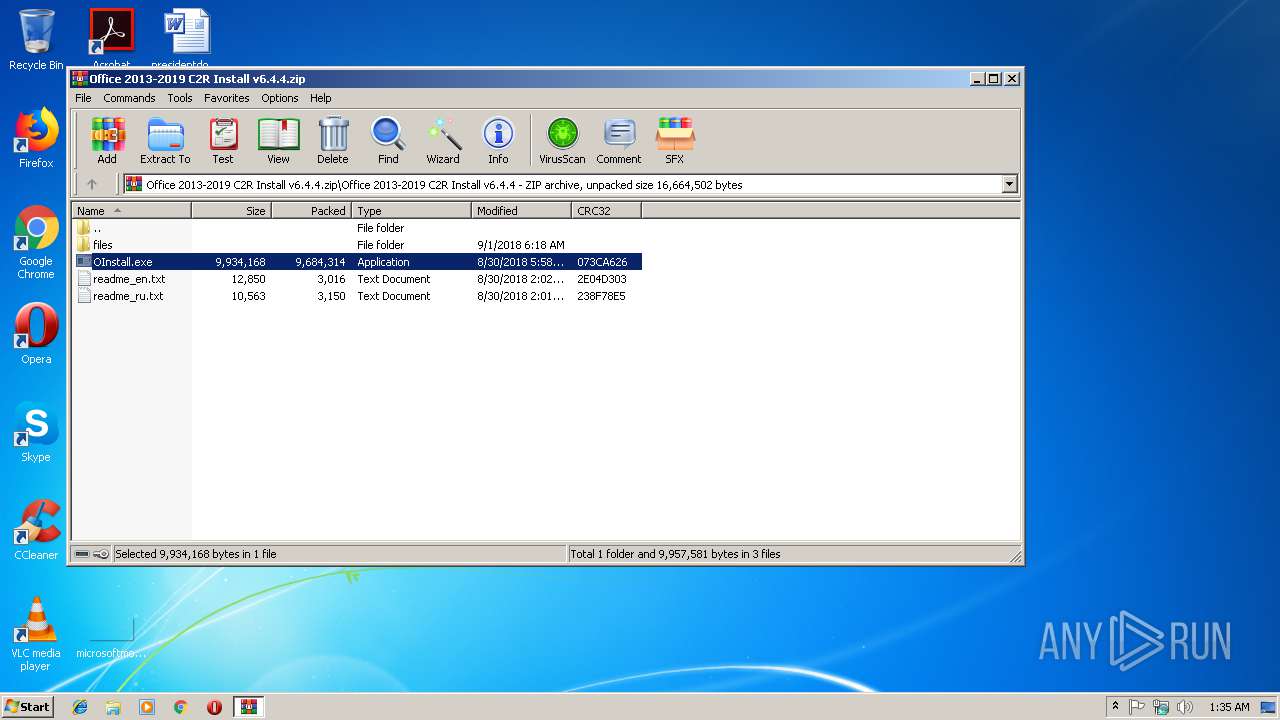
Modification events
| (PID) Process: | (3284) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3284) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3284) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3284) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Office 2013-2019 C2R Install v6.4.4.zip | |||
| (PID) Process: | (3284) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3284) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3284) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3284) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3284) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3284) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
195
Suspicious files
38
Text files
65
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3976 | setup.exe | C:\Users\admin\AppData\Local\Temp\CabBFD6.tmp | — | |
MD5:— | SHA256:— | |||
| 3976 | setup.exe | C:\Users\admin\AppData\Local\Temp\TarBFD7.tmp | — | |
MD5:— | SHA256:— | |||
| 3976 | setup.exe | C:\Users\admin\AppData\Local\Temp\OfficeC2R2DE8CE02-D524-487D-A061-08049F00B07FOfficeC2R7FA6A500-785D-4431-92BB-A507A238399D\v32.hash | — | |
MD5:— | SHA256:— | |||
| 3976 | setup.exe | C:\Users\admin\AppData\Local\Temp\OfficeC2R2DE8CE02-D524-487D-A061-08049F00B07FOfficeC2R7FA6A500-785D-4431-92BB-A507A238399D\VersionDescriptor.xml | — | |
MD5:— | SHA256:— | |||
| 3976 | setup.exe | C:\Users\admin\AppData\Local\Temp\OfficeC2R2DE8CE02-D524-487D-A061-08049F00B07F\v32.hash | — | |
MD5:— | SHA256:— | |||
| 3976 | setup.exe | C:\Users\admin\AppData\Local\Temp\OfficeC2R2DE8CE02-D524-487D-A061-08049F00B07F\VersionDescriptor.xml | — | |
MD5:— | SHA256:— | |||
| 1472 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\VTSG8S70XKU50LB3KRCX.temp | — | |
MD5:— | SHA256:— | |||
| 3976 | setup.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7396C420A8E1BC1DA97F1AF0D10BAD21 | der | |
MD5:— | SHA256:— | |||
| 3976 | setup.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7396C420A8E1BC1DA97F1AF0D10BAD21 | binary | |
MD5:— | SHA256:— | |||
| 3976 | setup.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\696F3DE637E6DE85B458996D49D759AD | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
27
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3976 | setup.exe | HEAD | 301 | 2.18.232.120:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v32_16.0.11231.20130.cab | unknown | — | — | whitelisted |
3976 | setup.exe | HEAD | 200 | 2.16.186.90:80 | http://officecdn.microsoft.com.edgesuite.net/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v32_16.0.11231.20130.cab | unknown | — | — | whitelisted |
3976 | setup.exe | GET | 301 | 2.18.232.120:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v32_16.0.11231.20130.cab | unknown | — | — | whitelisted |
3976 | setup.exe | HEAD | 301 | 2.18.232.120:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/16.0.11231.20130/i320.cab | unknown | — | — | whitelisted |
3976 | setup.exe | HEAD | 200 | 2.16.186.90:80 | http://officecdn.microsoft.com.edgesuite.net/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v32_16.0.11231.20130.cab | unknown | — | — | whitelisted |
3976 | setup.exe | HEAD | 301 | 2.18.232.120:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/16.0.11231.20130/i321033.cab | unknown | — | — | whitelisted |
3976 | setup.exe | GET | 301 | 2.18.232.120:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/16.0.11231.20130/i320.cab | unknown | — | — | whitelisted |
3976 | setup.exe | GET | — | 2.16.186.90:80 | http://officecdn.microsoft.com.edgesuite.net/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/16.0.11231.20130/i320.cab | unknown | — | — | whitelisted |
3976 | setup.exe | HEAD | 301 | 2.18.232.120:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v32_16.0.11231.20130.cab | unknown | — | — | whitelisted |
3976 | setup.exe | GET | 200 | 2.16.186.90:80 | http://officecdn.microsoft.com.edgesuite.net/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v32_16.0.11231.20130.cab | unknown | compressed | 17.0 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2252 | chrome.exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
2252 | chrome.exe | 172.217.21.206:443 | apis.google.com | Google Inc. | US | whitelisted |
3156 | OfficeClickToRun.exe | 2.18.232.120:80 | officecdn.microsoft.com | Akamai International B.V. | — | whitelisted |
3976 | setup.exe | 13.107.3.128:443 | config.edge.skype.com | Microsoft Corporation | US | whitelisted |
3976 | setup.exe | 52.232.69.150:443 | client-office365-tas.msedge.net | Microsoft Corporation | NL | whitelisted |
3976 | setup.exe | 52.109.88.44:443 | mrodevicemgr.officeapps.live.com | Microsoft Corporation | NL | whitelisted |
3976 | setup.exe | 2.18.232.120:80 | officecdn.microsoft.com | Akamai International B.V. | — | whitelisted |
3976 | setup.exe | 2.16.186.74:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
3976 | setup.exe | 2.16.186.90:80 | officecdn.microsoft.com.edgesuite.net | Akamai International B.V. | — | whitelisted |
1520 | OfficeClickToRun.exe | 52.232.69.150:443 | client-office365-tas.msedge.net | Microsoft Corporation | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.edge.skype.com |
| malicious |
client-office365-tas.msedge.net |
| whitelisted |
mrodevicemgr.officeapps.live.com |
| whitelisted |
officecdn.microsoft.com |
| whitelisted |
officecdn.microsoft.com.edgesuite.net |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.google.de |
| whitelisted |
www.gstatic.com |
| whitelisted |