| File name: | quacker.bat |
| Full analysis: | https://app.any.run/tasks/e644e3ad-96f2-455d-a4e7-39415ce9758a |
| Verdict: | Malicious activity |
| Analysis date: | March 01, 2025, 11:46:16 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with CRLF line terminators |
| MD5: | 58E9F84DAE81811FDDDC367A1BFA765E |
| SHA1: | 1AB15B70848E6E693E8ECFE2C4818C40B8F19FD4 |
| SHA256: | F9F90E6F485B135A55569A5C5943FEB541DD2FA3ECAF7CFE5F06B12F87113E3D |
| SSDEEP: | 12:wNHJowyeJC98JGk2vFB/f3meP8JGkdMGEFEb0Qn:w/S/f3mGWMGBz |
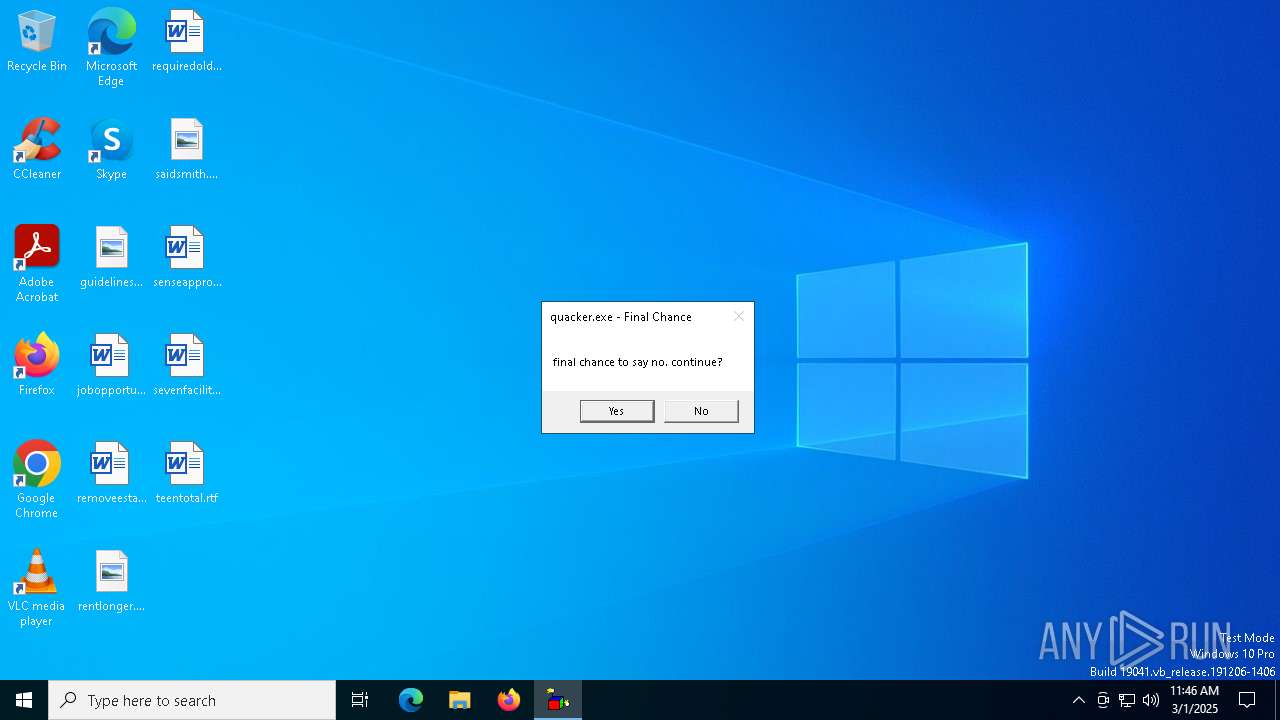
MALICIOUS
Starts NET.EXE to view/add/change user profiles
- cmd.exe (PID: 8084)
- cmd.exe (PID: 8028)
- cmd.exe (PID: 7984)
- cmd.exe (PID: 8124)
- net.exe (PID: 7376)
- cmd.exe (PID: 3192)
- net.exe (PID: 6708)
- net.exe (PID: 7492)
- net.exe (PID: 5256)
- net.exe (PID: 7640)
- net.exe (PID: 7484)
- cmd.exe (PID: 7292)
- cmd.exe (PID: 7300)
- net.exe (PID: 7468)
- net.exe (PID: 7756)
- cmd.exe (PID: 8180)
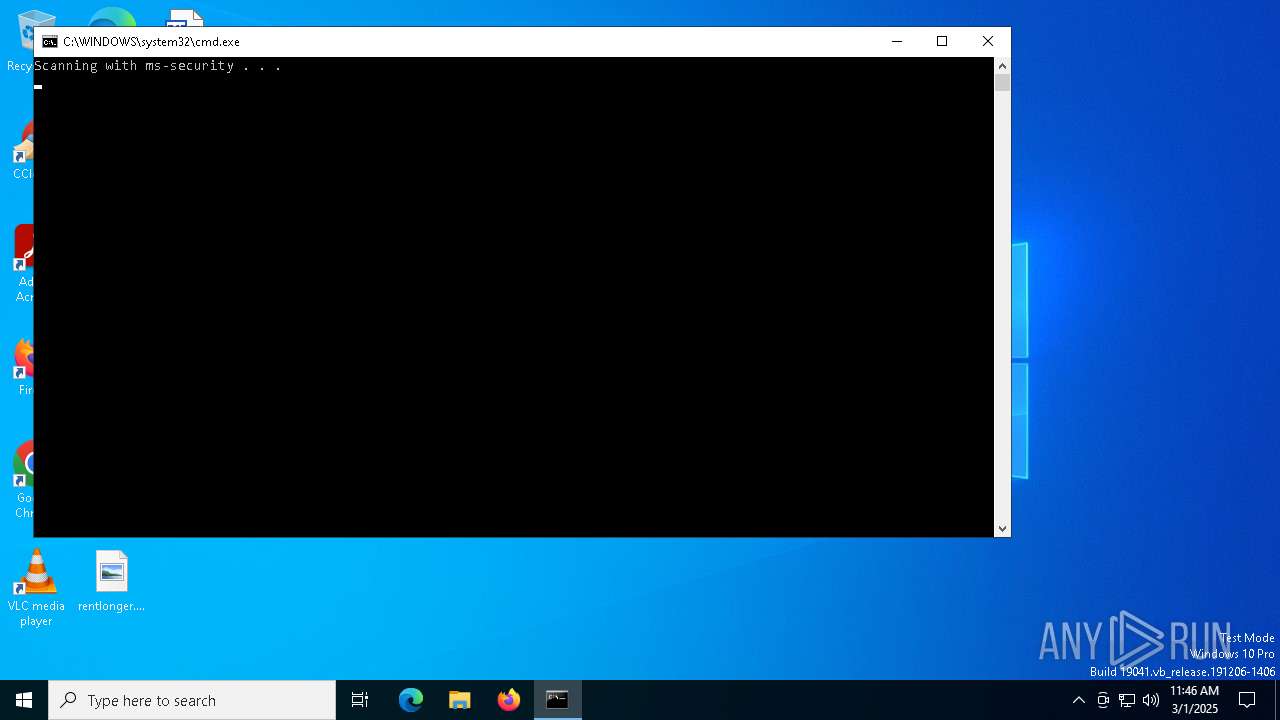
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 5864)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 1300)
- cmd.exe (PID: 7192)
The process executes VB scripts
- cmd.exe (PID: 1300)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7788)
- cmd.exe (PID: 7928)
- cmd.exe (PID: 7836)
- cmd.exe (PID: 7884)
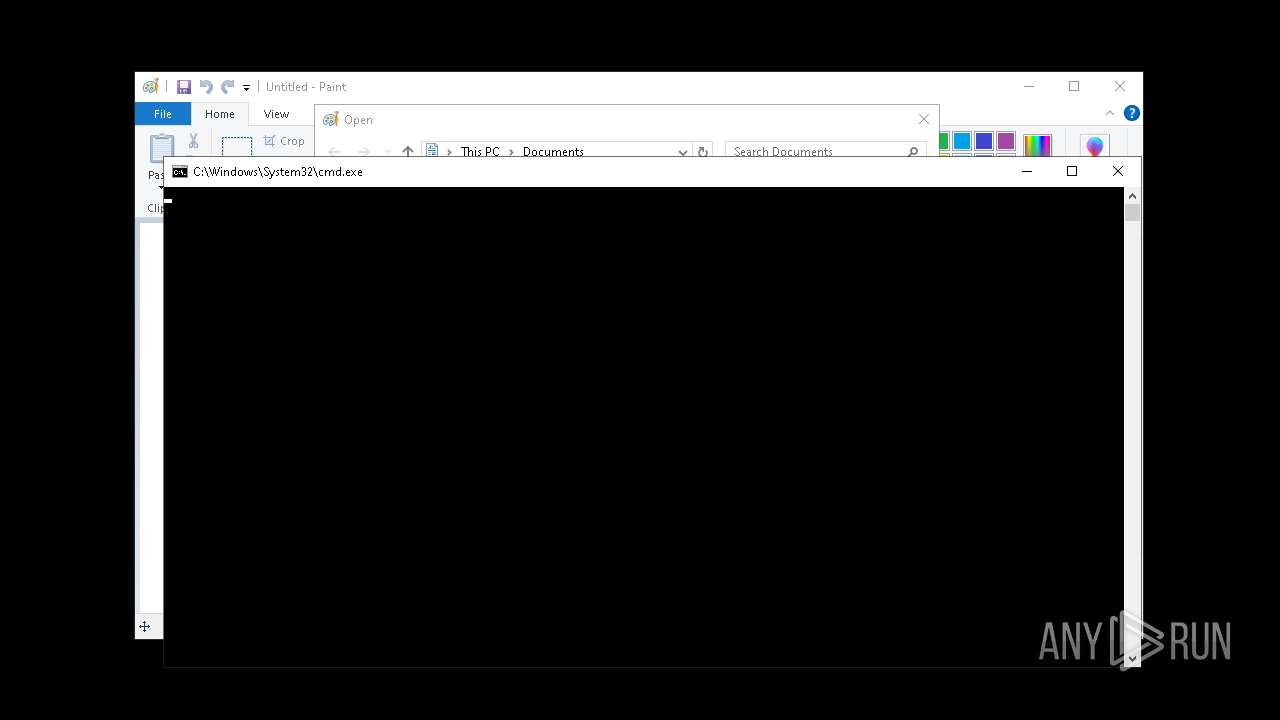
Starts CMD.EXE for commands execution
- wscript.exe (PID: 5864)
Runs shell command (SCRIPT)
- wscript.exe (PID: 5864)
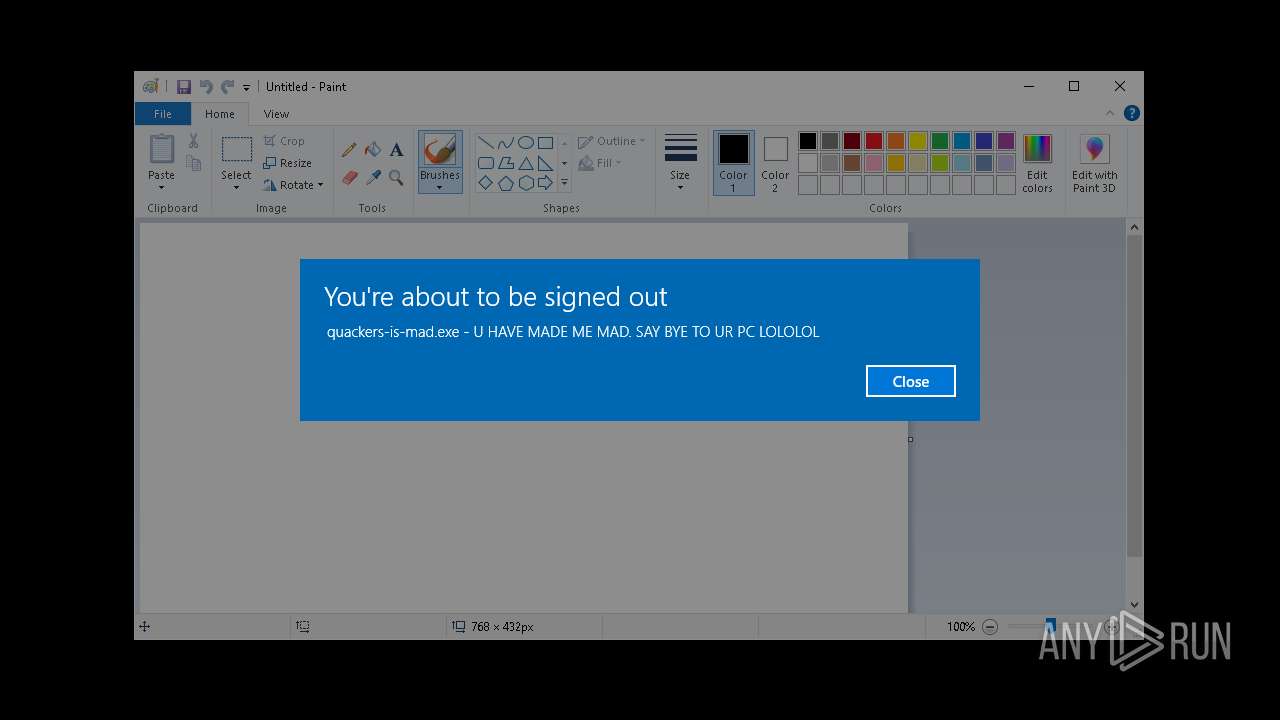
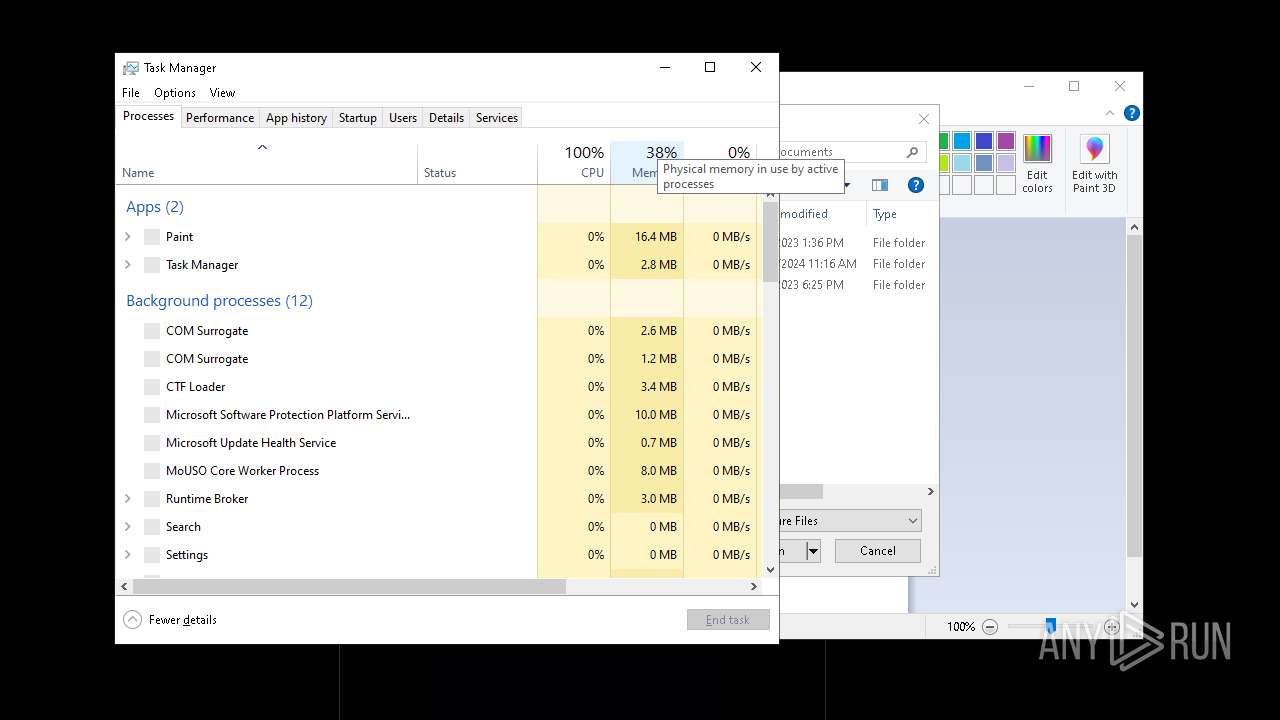
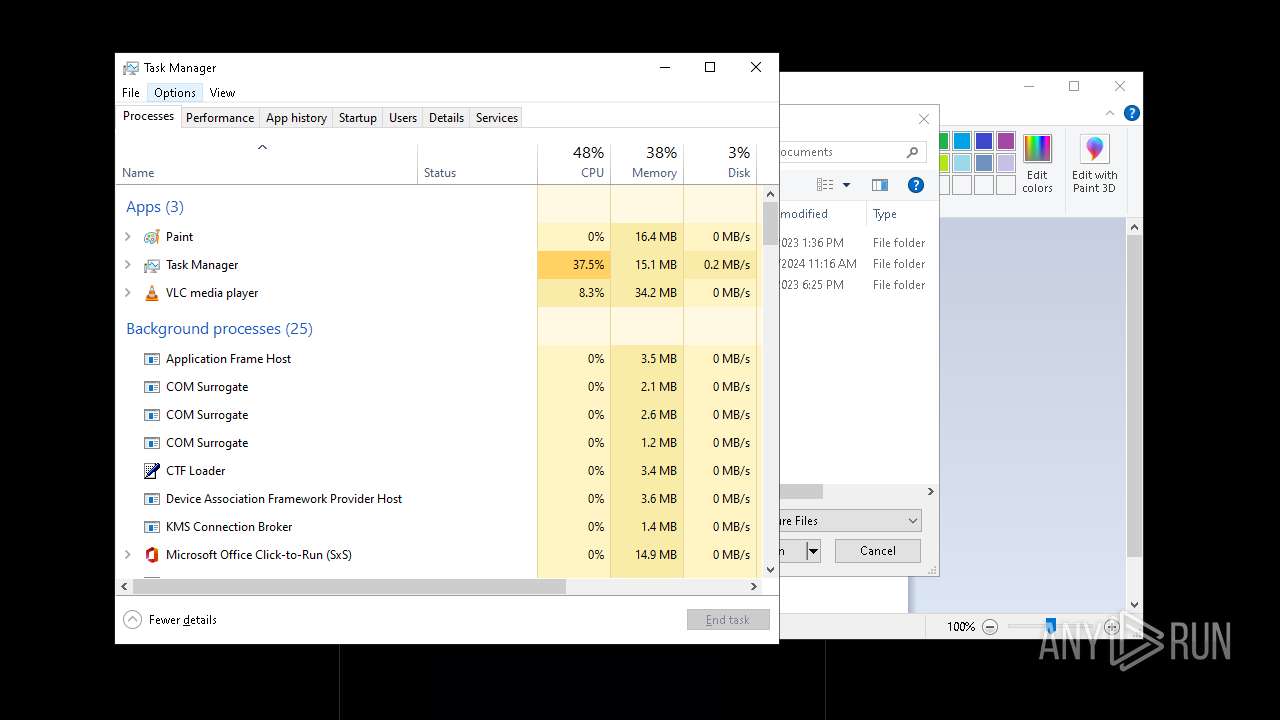
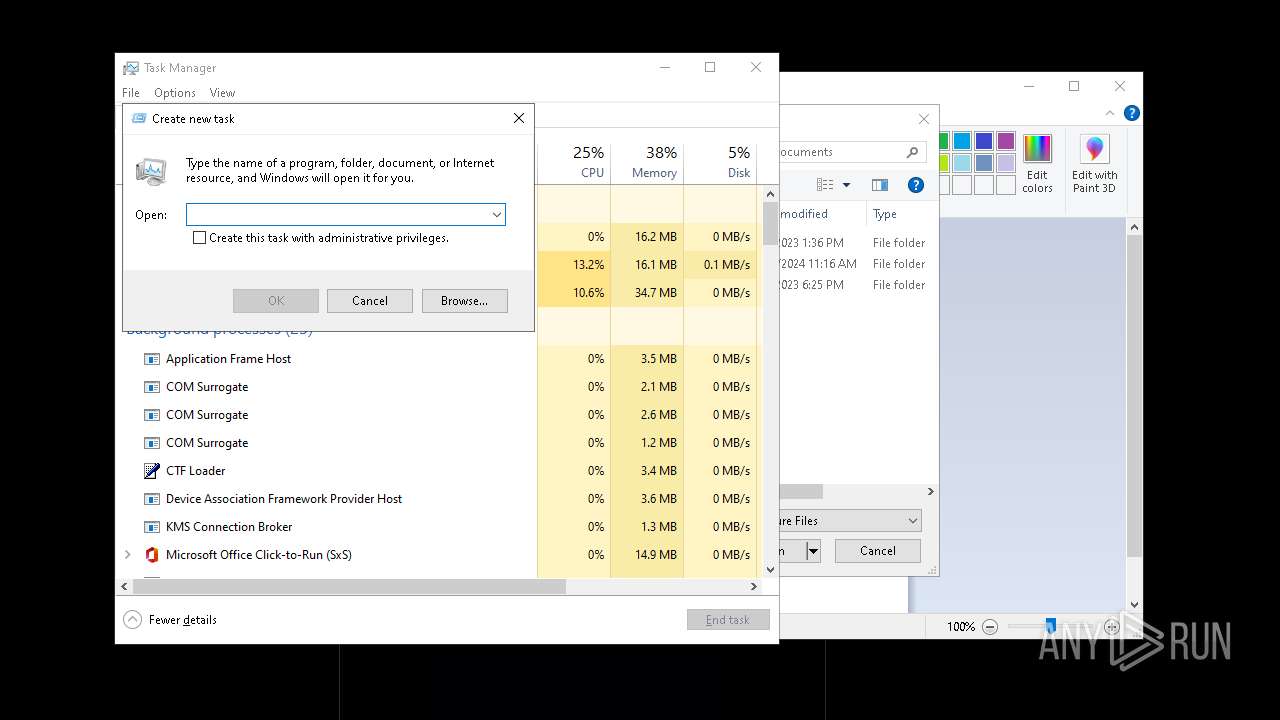
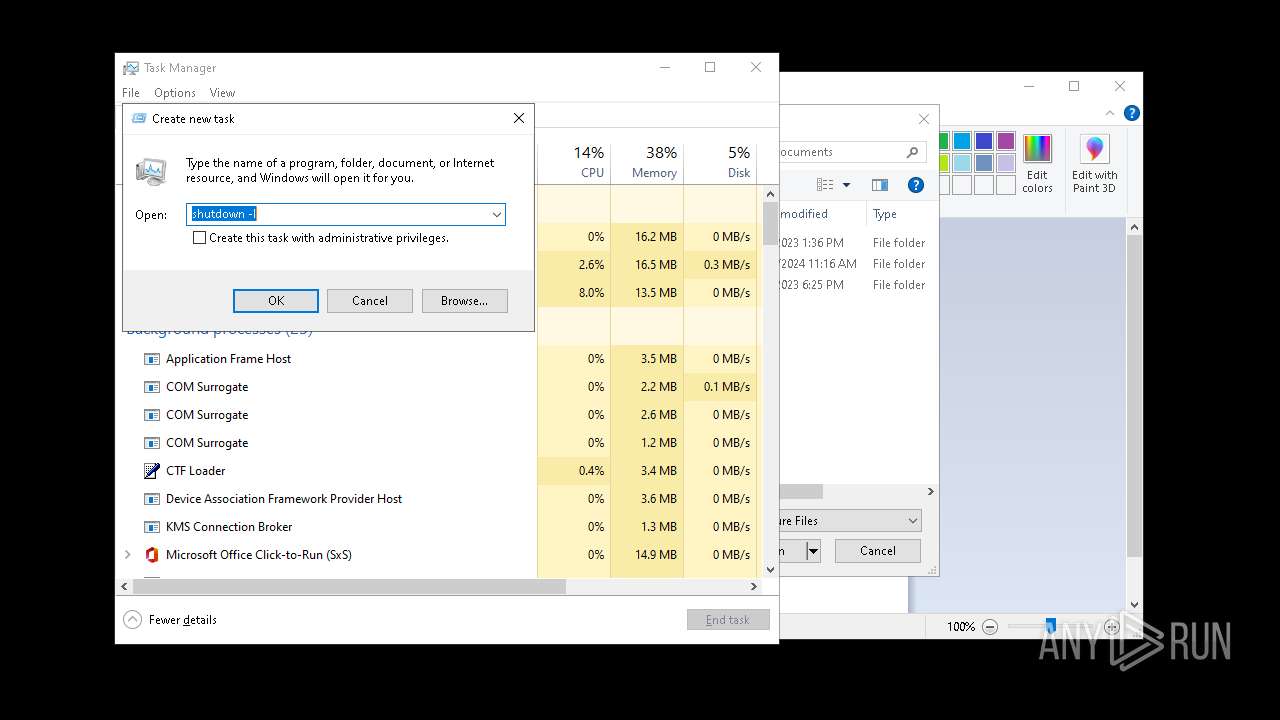
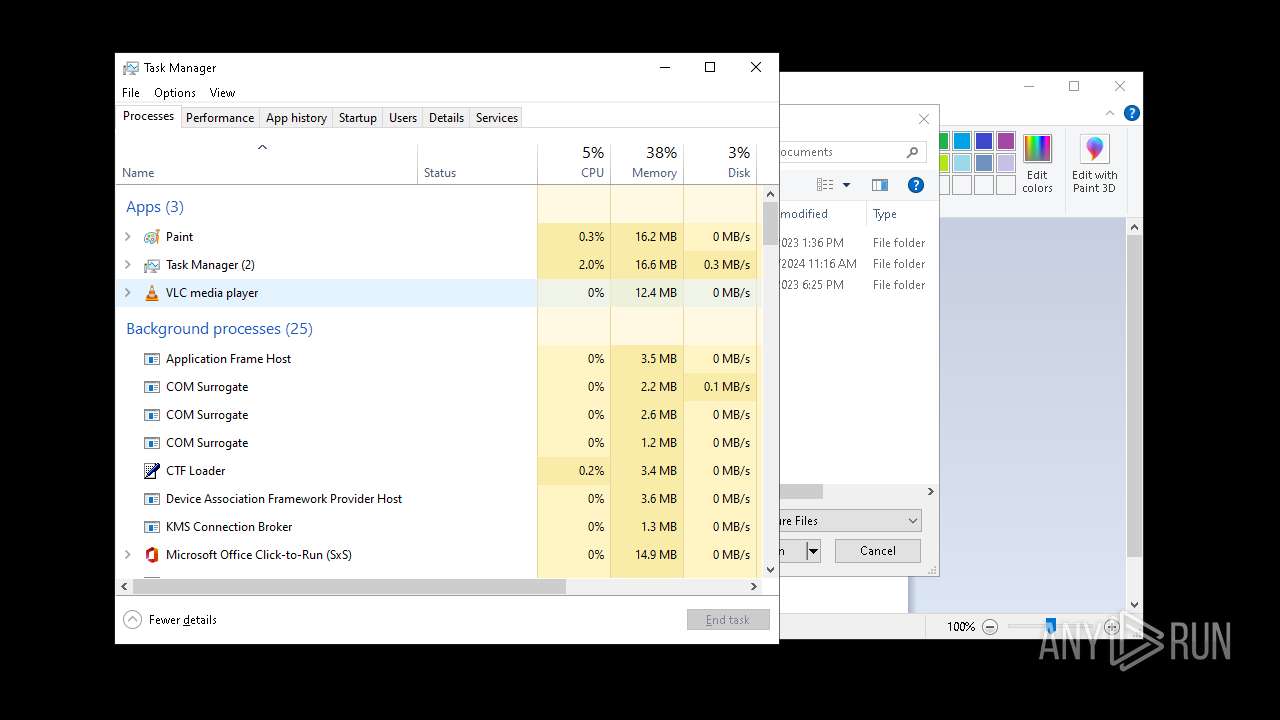
The system shut down or reboot
- cmd.exe (PID: 7220)
- Taskmgr.exe (PID: 4980)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 5528)
Downloads file from URI via Powershell
- powershell.exe (PID: 7288)
INFO
Disables trace logs
- powershell.exe (PID: 7036)
- powershell.exe (PID: 5048)
- powershell.exe (PID: 7288)
Checks proxy server information
- powershell.exe (PID: 5048)
- BackgroundTransferHost.exe (PID: 7700)
- powershell.exe (PID: 7036)
- powershell.exe (PID: 7288)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 7700)
- BackgroundTransferHost.exe (PID: 7416)
- BackgroundTransferHost.exe (PID: 7532)
- BackgroundTransferHost.exe (PID: 728)
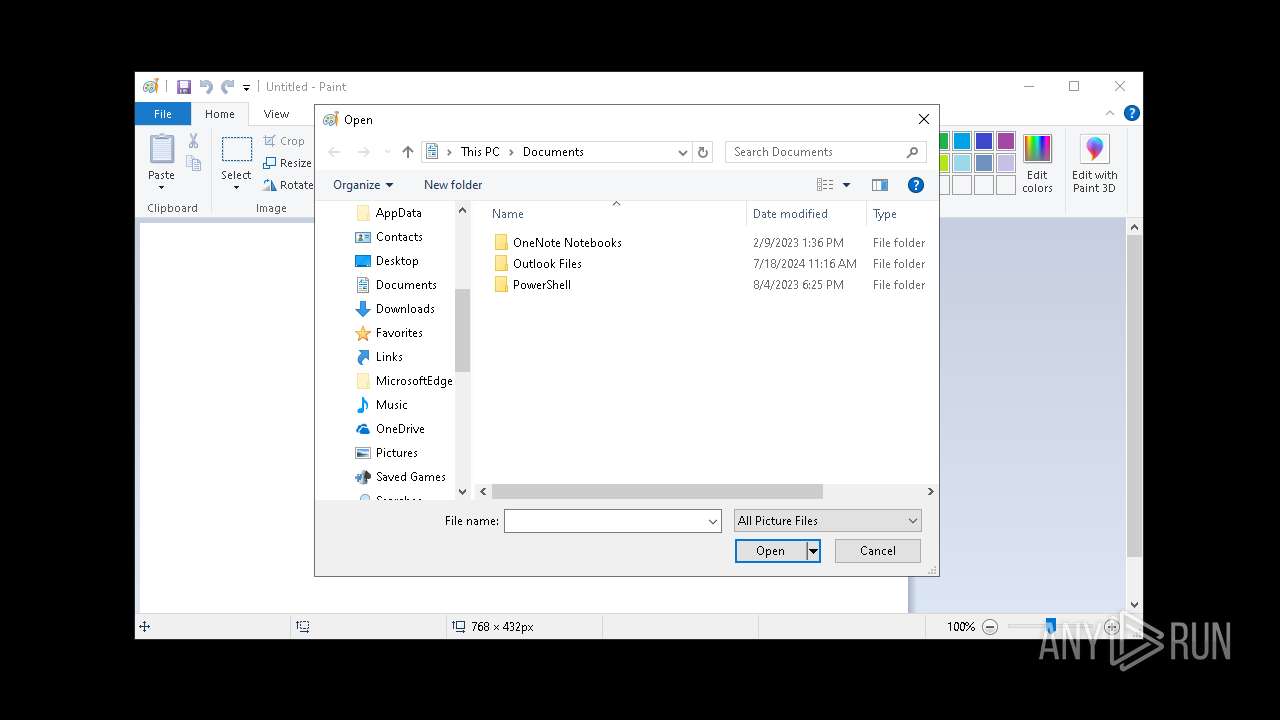
- mspaint.exe (PID: 7316)
- Taskmgr.exe (PID: 4980)
- BackgroundTransferHost.exe (PID: 7952)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 7700)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 7700)
Checks supported languages
- vlc.exe (PID: 4752)
Reads the computer name
- vlc.exe (PID: 4752)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
211
Monitored processes
76
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 496 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 672 | REG ADD HKCU\Software\Policies\Microsoft\Windows\System /v DisableCMD /t REG_DWORD /d 2 | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 720 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1300 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\quacker.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | "C:\WINDOWS\system32\shutdown.exe" -l | C:\Windows\System32\shutdown.exe | — | Taskmgr.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Shutdown and Annotation Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3192 | "C:\Windows\System32\cmd.exe" /C net user isdestroying quack /add | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4164 | "C:\Windows\System32\cmd.exe" /C start mspaint | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4180 | "C:\Windows\System32\Taskmgr.exe" | C:\Windows\System32\Taskmgr.exe | — | mspaint.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Manager Exit code: 3221226540 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4560 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
28 061
Read events
28 019
Write events
41
Delete events
1
Modification events
| (PID) Process: | (1300) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.vbs\OpenWithProgids |
| Operation: | write | Name: | VBSFile |
Value: | |||
| (PID) Process: | (7416) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7416) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7416) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7700) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7700) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7700) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7532) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7532) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7532) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
2
Suspicious files
7
Text files
10
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7700 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\df558295-918d-429d-9cc0-352e826ae6d3.down_data | — | |
MD5:— | SHA256:— | |||
| 5048 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_nje4zaql.bos.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5048 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:DE082B20FF2DA83DB486A350F1295C13 | SHA256:1DDFF36A3A6CC335D8C34B41A830FC849B01B6DB11B66138A26B4C9F8B259FD4 | |||
| 5048 | powershell.exe | C:\Users\admin\AppData\Local\Temp\WindowsDefenderLogs\continue.vbs | text | |
MD5:D5F6F777C2C68194D29058F25B8CEAF4 | SHA256:8FC26D94FE04DC679C33D98478BF532FDCEF6B448EAC49696EE023C663D1CD31 | |||
| 4752 | vlc.exe | C:\Users\admin\AppData\Roaming\vlc\vlc-qt-interface.ini.lock | text | |
MD5:DFE195DBB460D03A1B539955E7A05D71 | SHA256:B5560CC4DB631F5A29E5952D9C3D402379079CAF188C5D45CDA097324E53E34C | |||
| 7700 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\d9b26814-a21f-4cb3-8f89-05c8b4adacea.0debf880-3b38-4d29-96ac-dafce86ffd24.down_meta | binary | |
MD5:B719A5D3304E34192E8DD1F46291F3D0 | SHA256:5EBBDE4D8D9292BCD988B99316B19F2F239DDC39C107033E94D57688A4313F6A | |||
| 4752 | vlc.exe | C:\Users\admin\AppData\Roaming\vlc\vlc-qt-interface.ini | text | |
MD5:D9400E24F7ACECF219499ED766F7589B | SHA256:021A85DF037725AD60AD77DEFD0B979D01C28553FB3DC147577FC92E8E88EFD2 | |||
| 7700 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\d9b26814-a21f-4cb3-8f89-05c8b4adacea.up_meta_secure | binary | |
MD5:0412EF173D93ACCCE9D0507DDE66BE20 | SHA256:2B1C13619F88AFB44990D6B9671AD726161D20BC8603618DD6342CB20B2C03AF | |||
| 4980 | Taskmgr.exe | C:\Users\admin\AppData\Local\D3DSCache\ecbf0d5a3a180bb\F4EB2D6C-ED2B-4BDD-AD9D-F913287E6768.lock | text | |
MD5:F49655F856ACB8884CC0ACE29216F511 | SHA256:7852FCE59C67DDF1D6B8B997EAA1ADFAC004A9F3A91C37295DE9223674011FBA | |||
| 7288 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_oquteqr4.dgd.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
30
DNS requests
18
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7700 | BackgroundTransferHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2604 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2604 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5048 | powershell.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
5048 | powershell.exe | 185.199.109.133:443 | raw.githubusercontent.com | FASTLY | US | whitelisted |
6544 | svchost.exe | 20.190.160.22:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3008 | backgroundTaskHost.exe | 92.123.104.32:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
2112 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
github.com |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.bing.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |