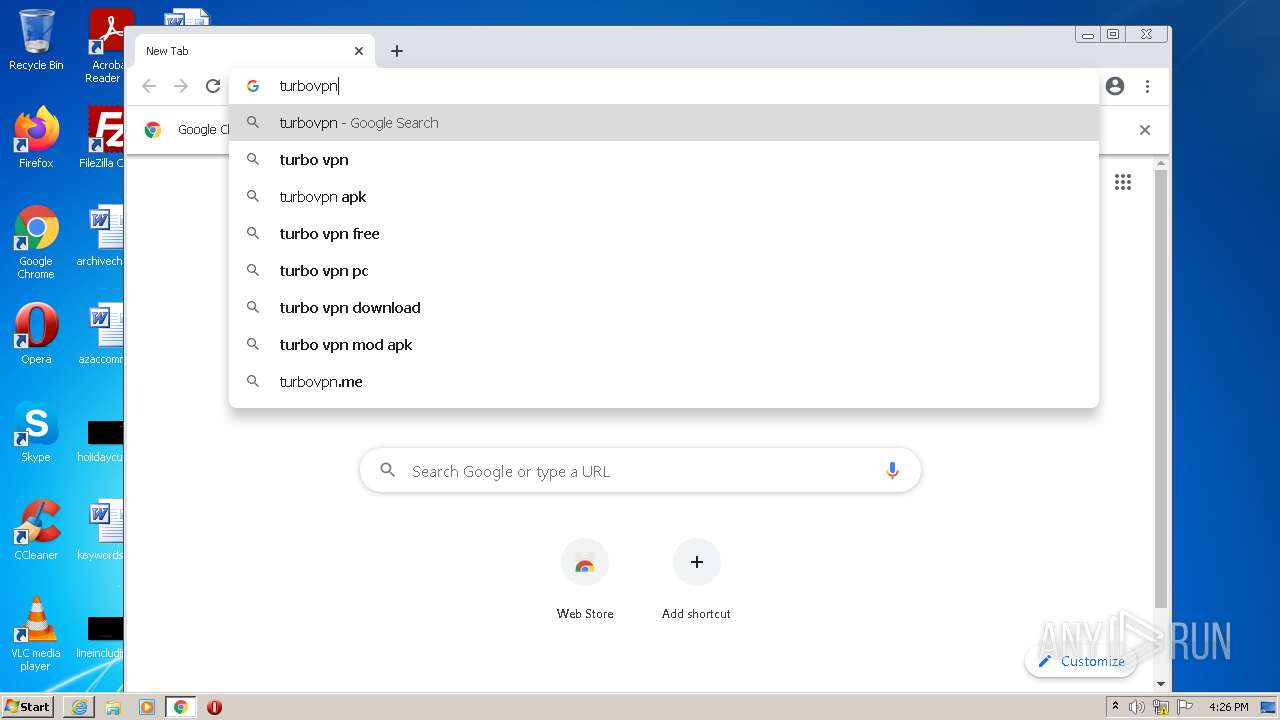
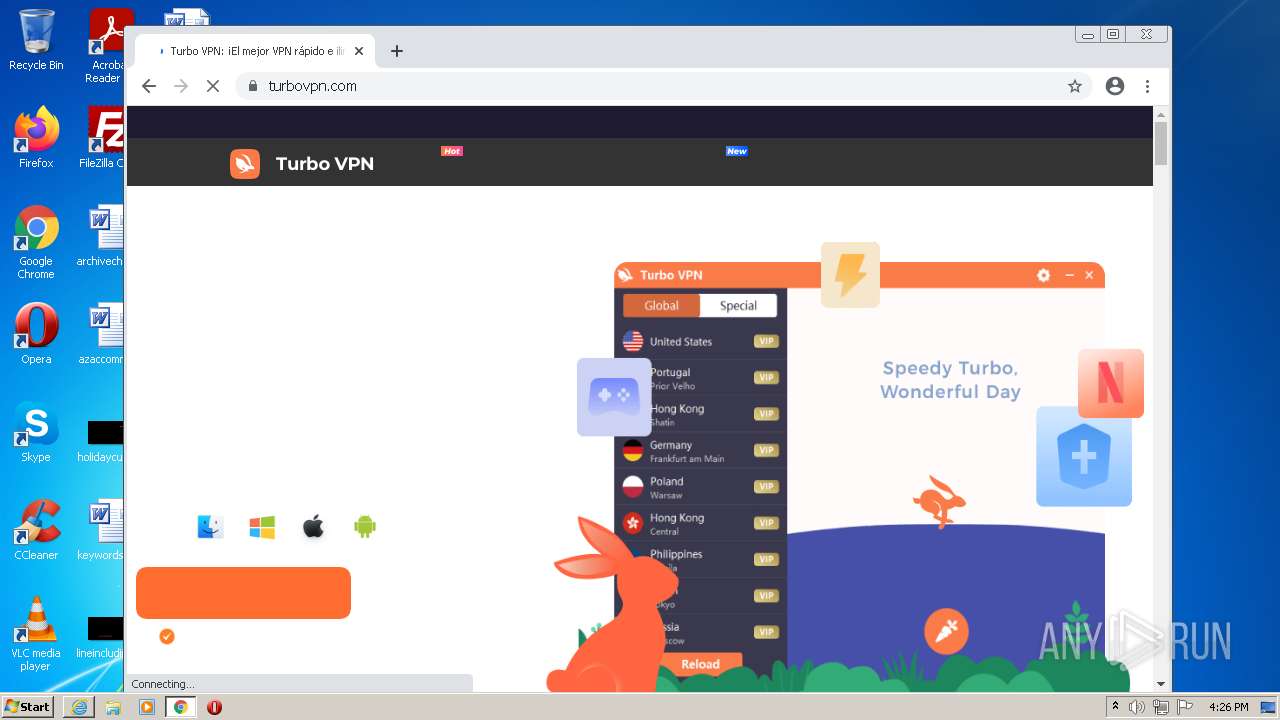
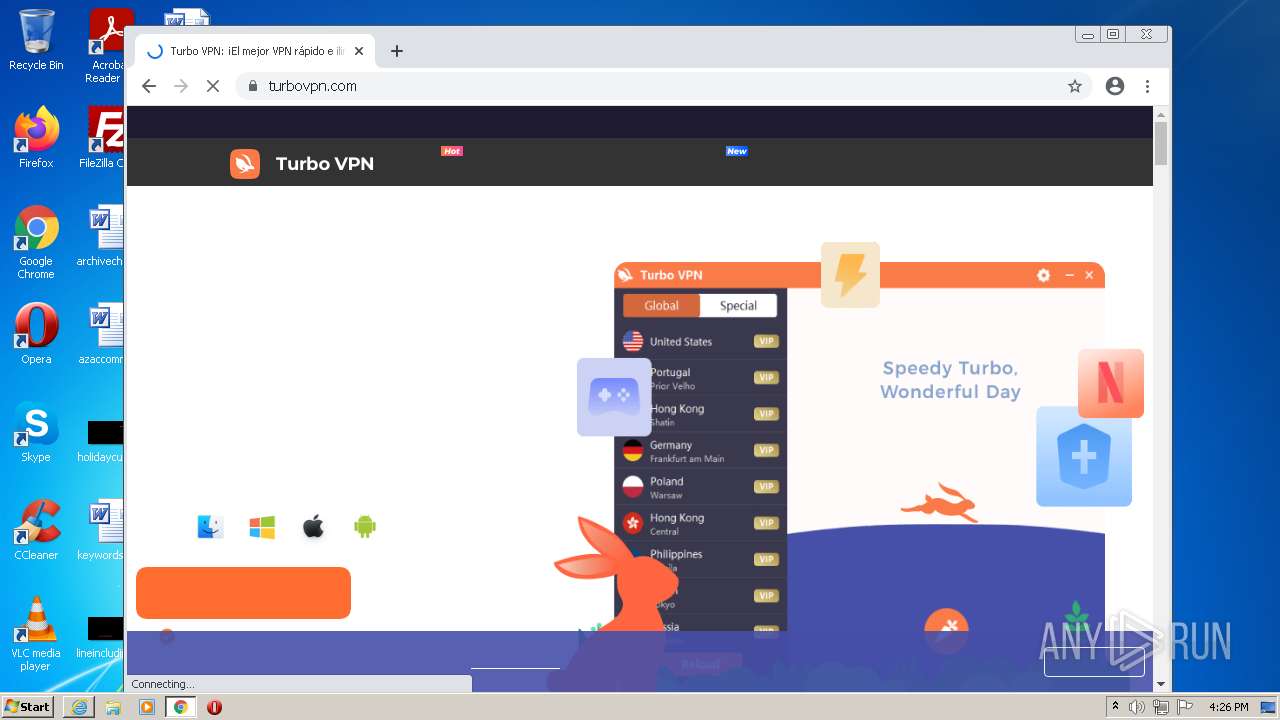
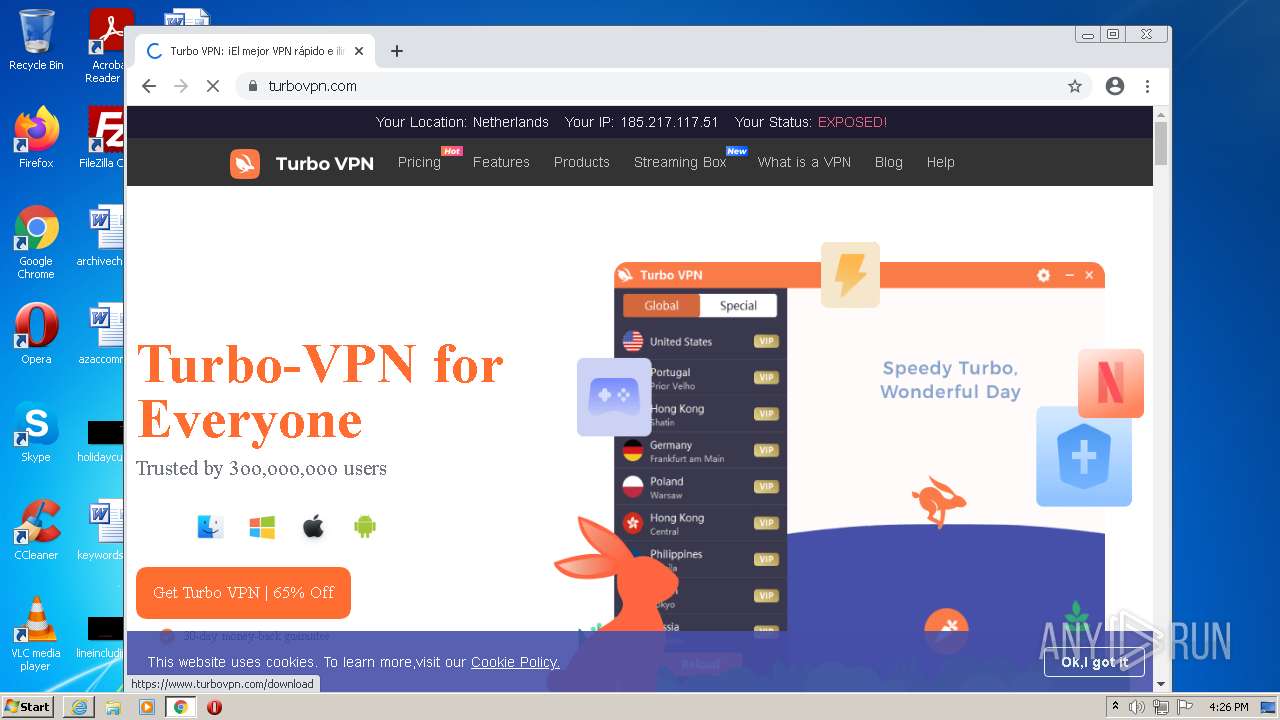
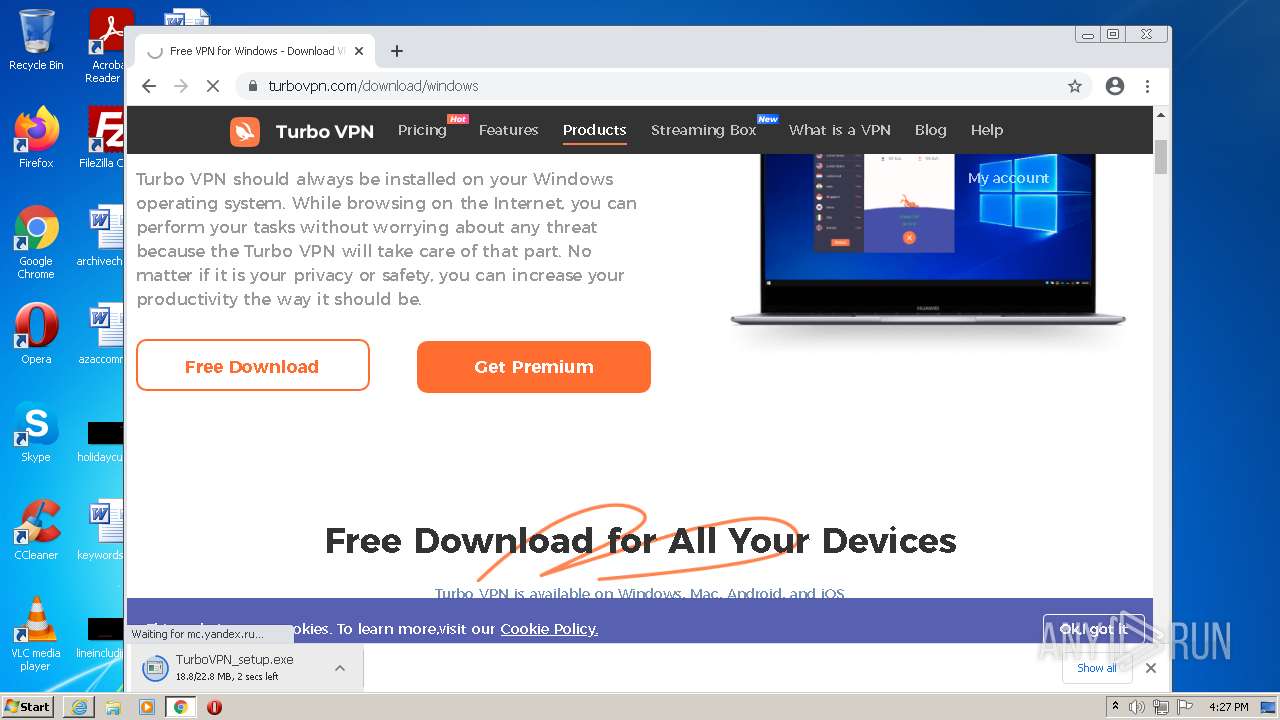
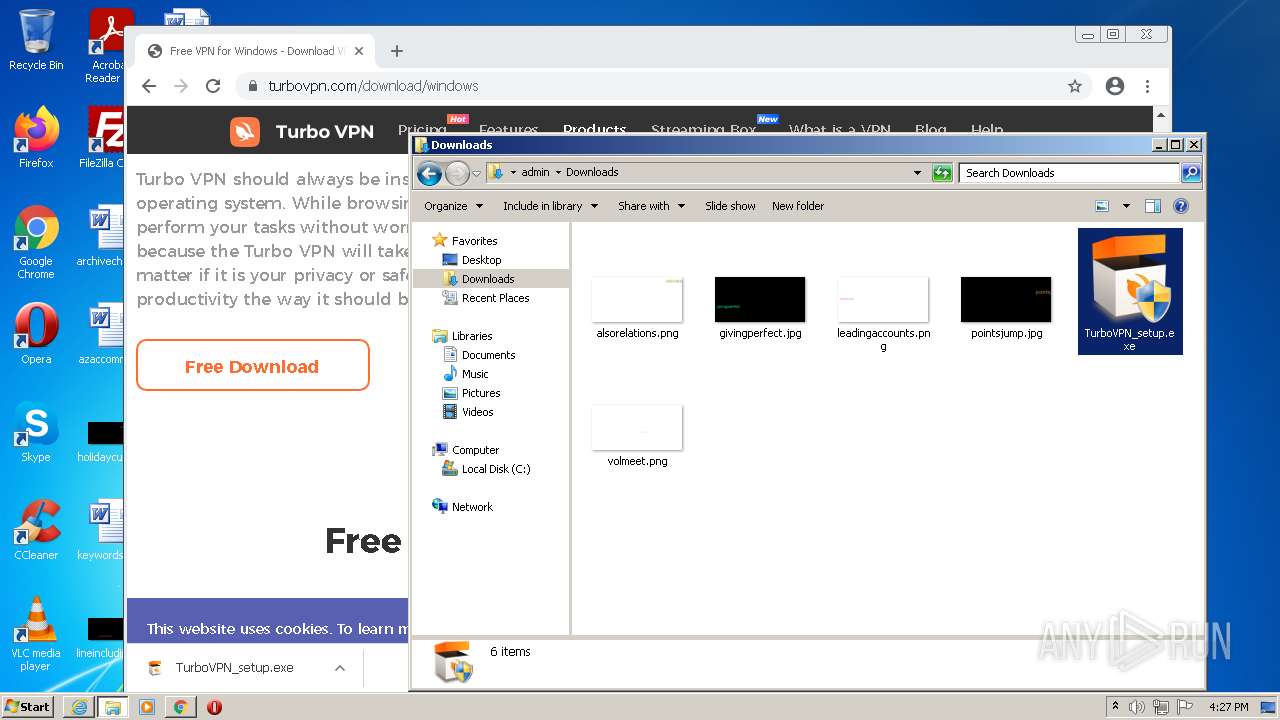
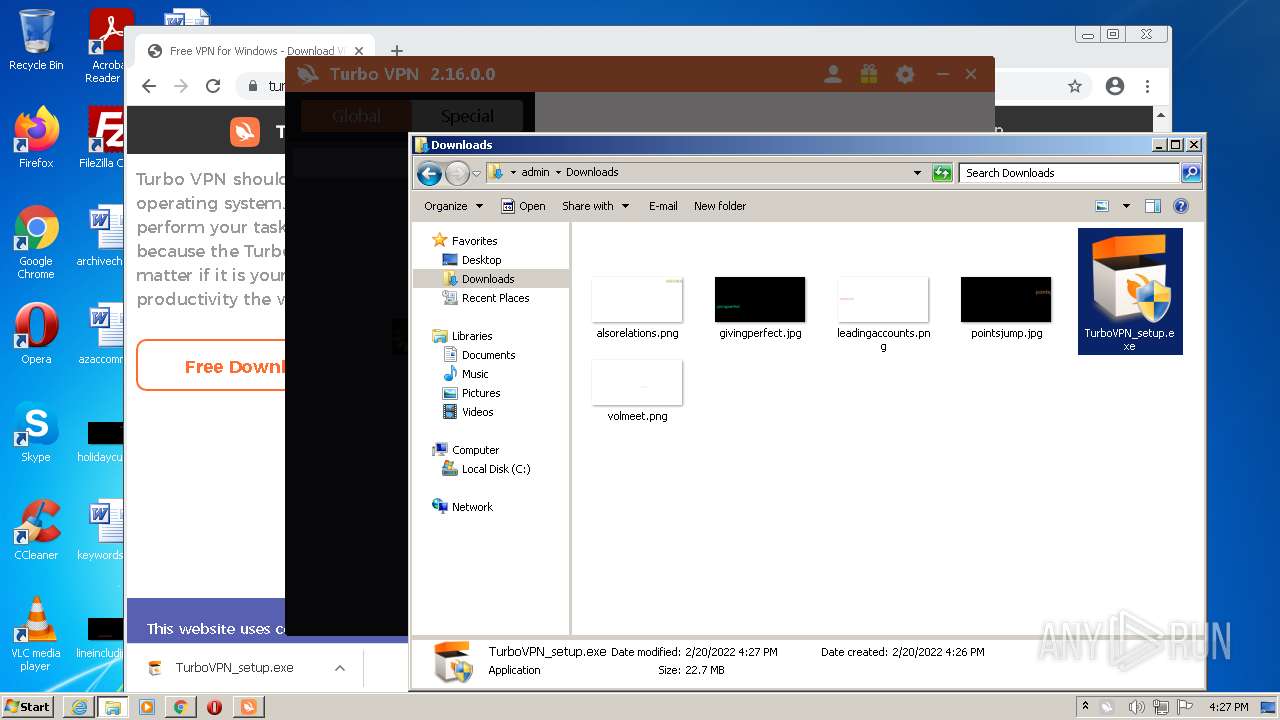
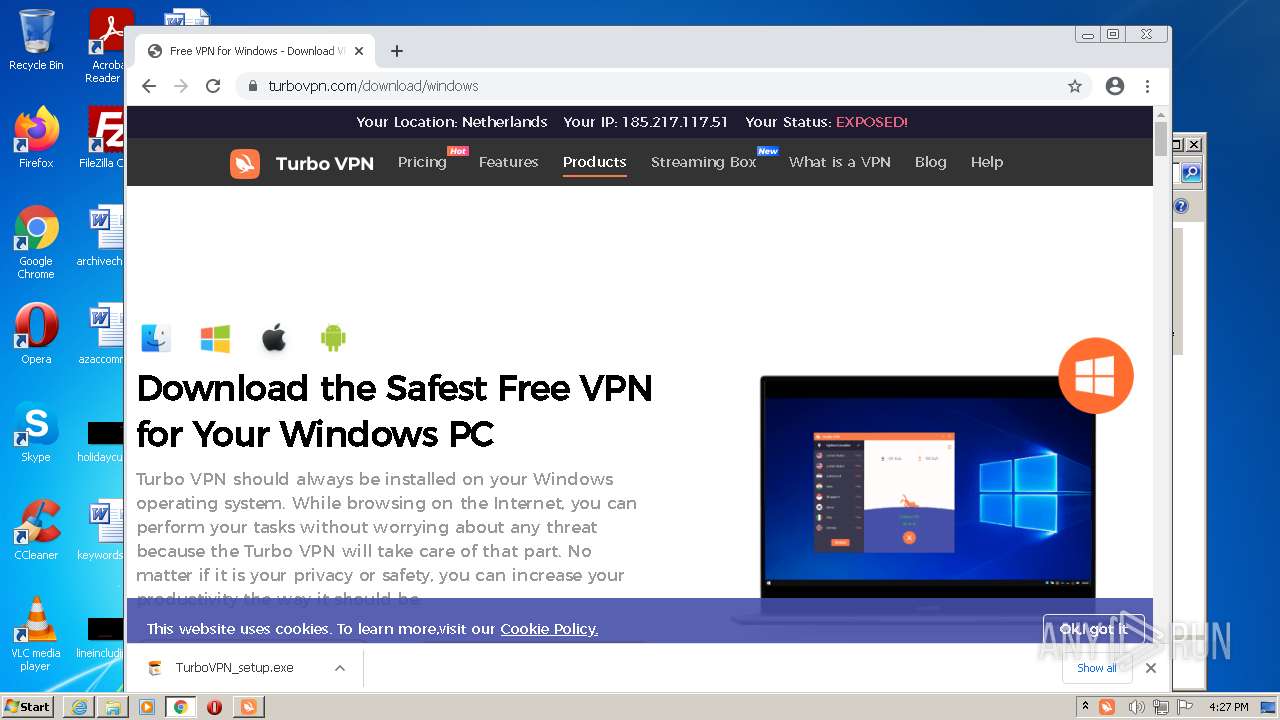
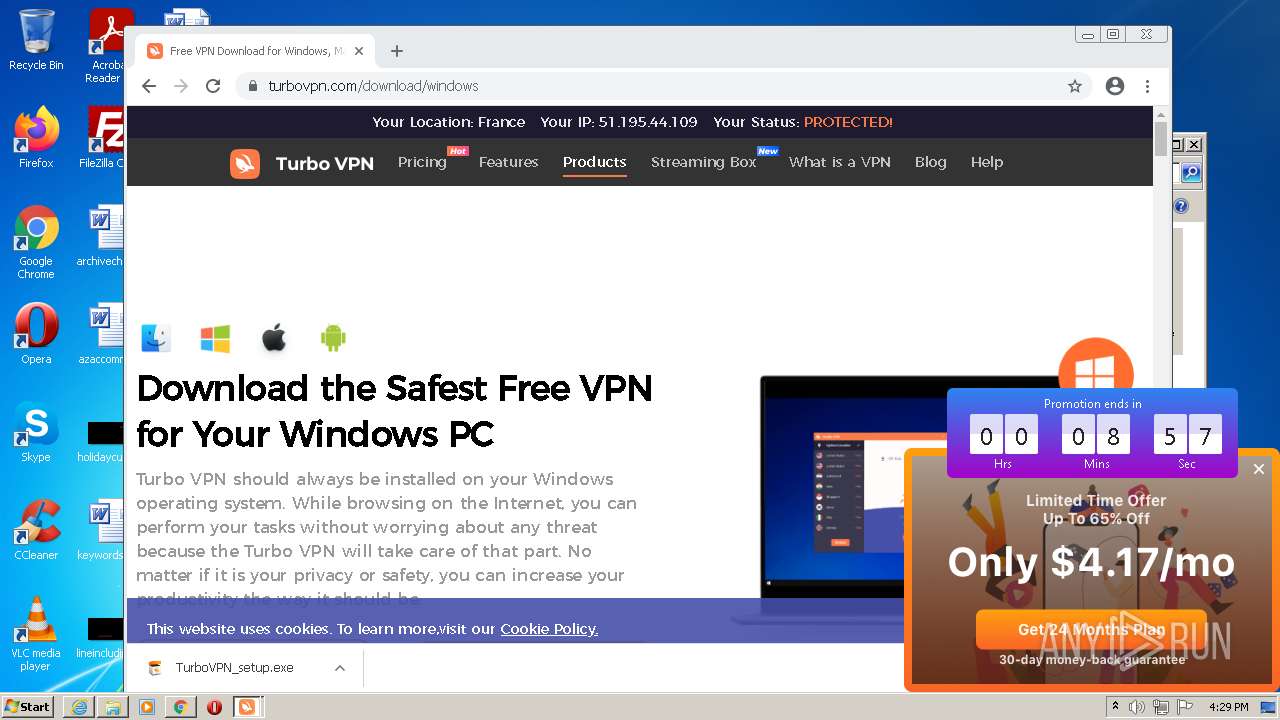
| URL: | https://turbovpn.com/download/windows |
| Full analysis: | https://app.any.run/tasks/ba1e264f-a51e-4209-86ca-eeecdd515230 |
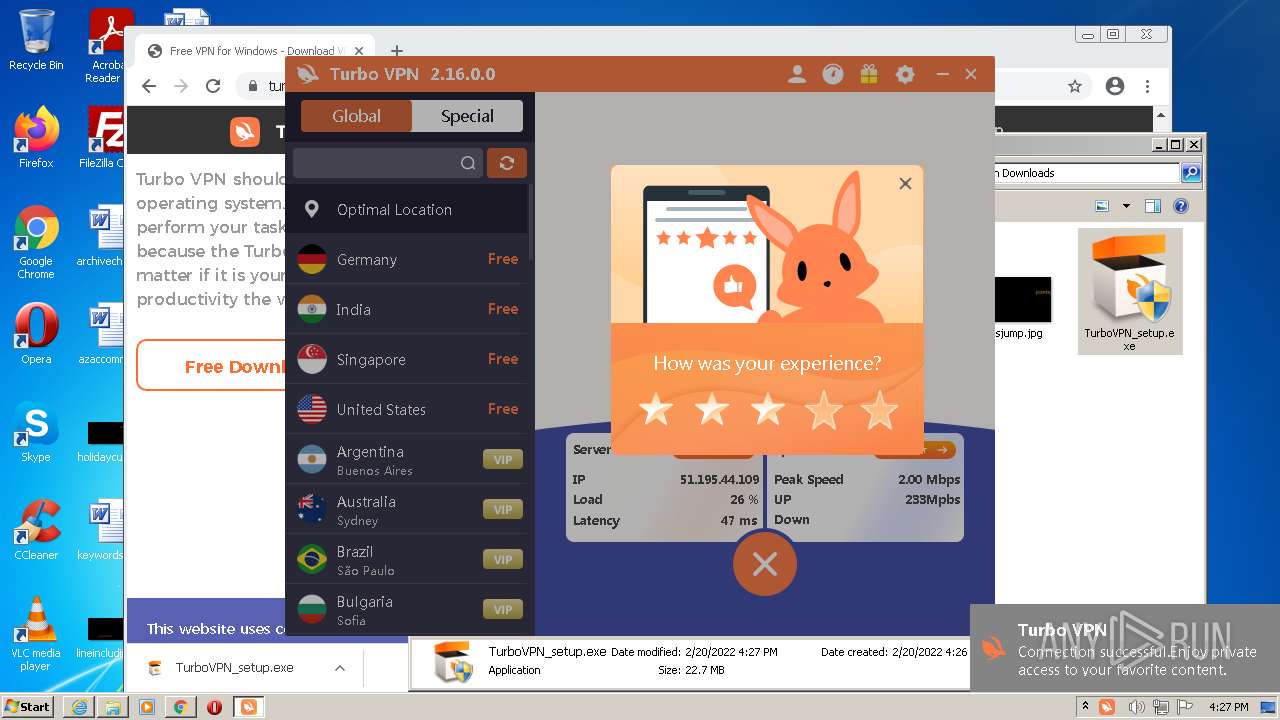
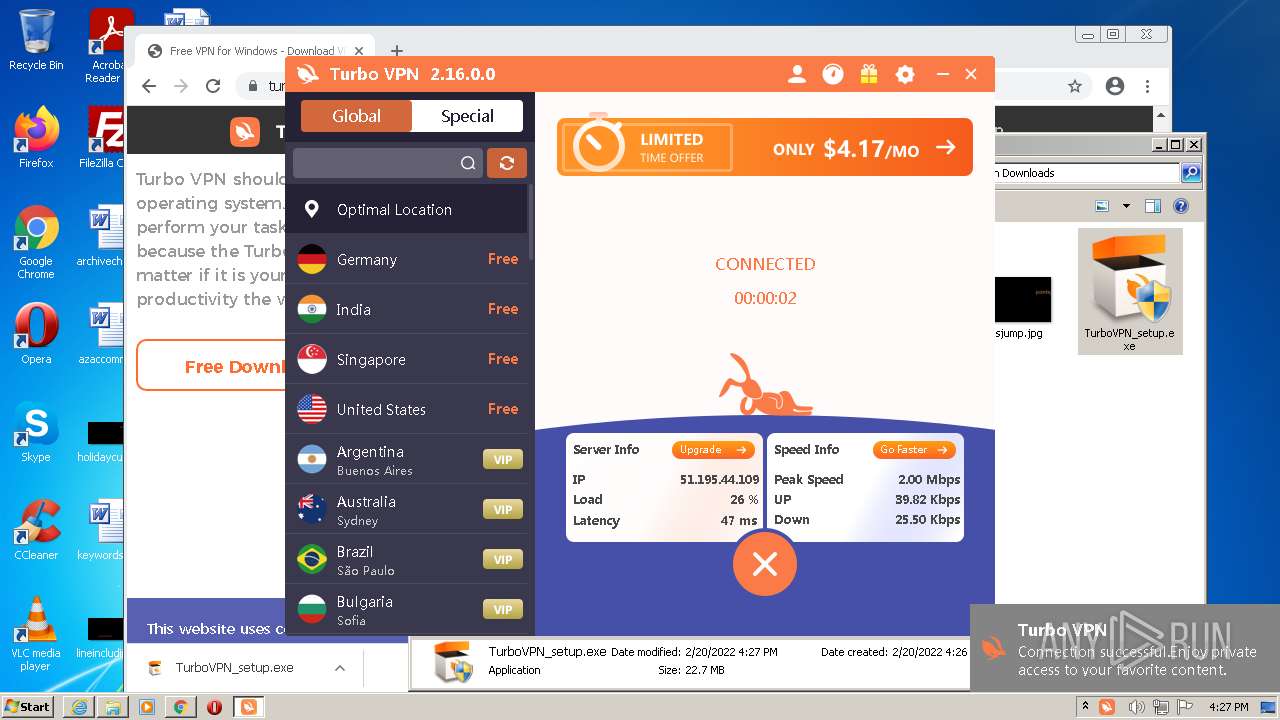
| Verdict: | Malicious activity |
| Analysis date: | February 20, 2022, 16:26:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D18FE300FB5B000B8D985186FE79E3FA |
| SHA1: | FC766F4858BF755033F6E604A90C6A946D8725A6 |
| SHA256: | F9EB07D20EAC11210FE4ABCD12C27FC5E0DC447C9291833CF26699C178D85CB4 |
| SSDEEP: | 3:N8YY0aKLdY:2YY45Y |
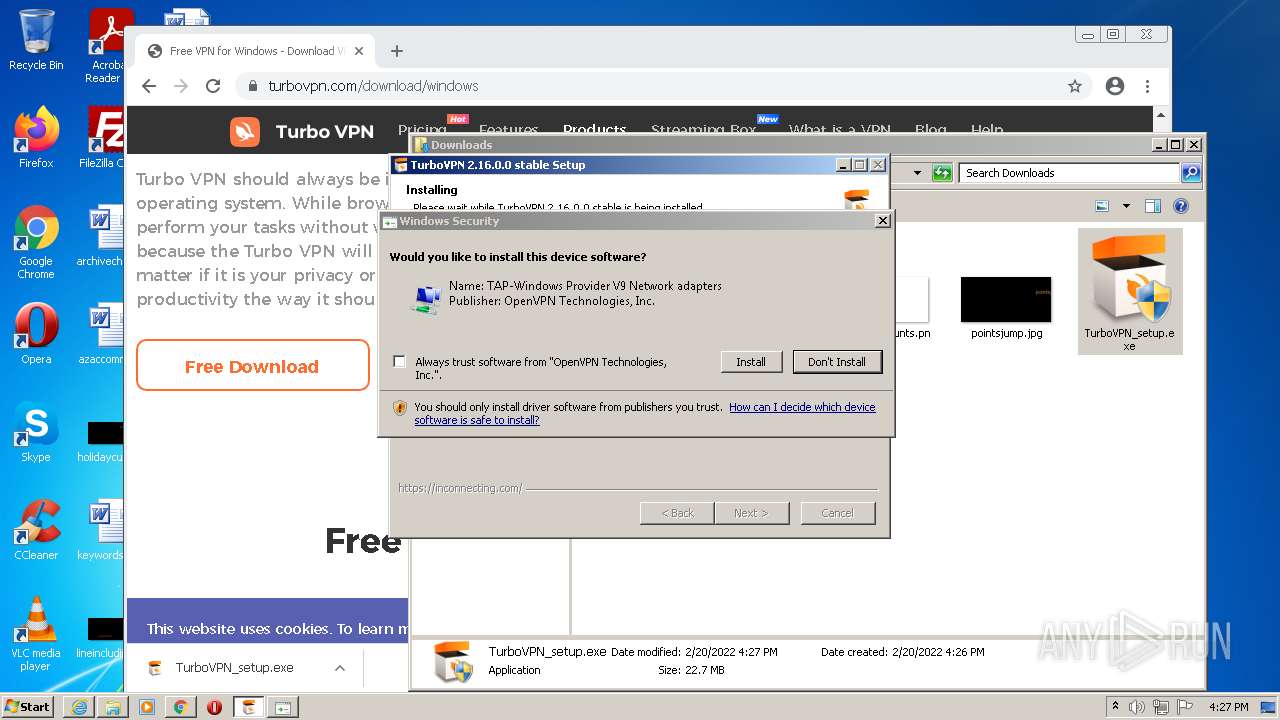
MALICIOUS
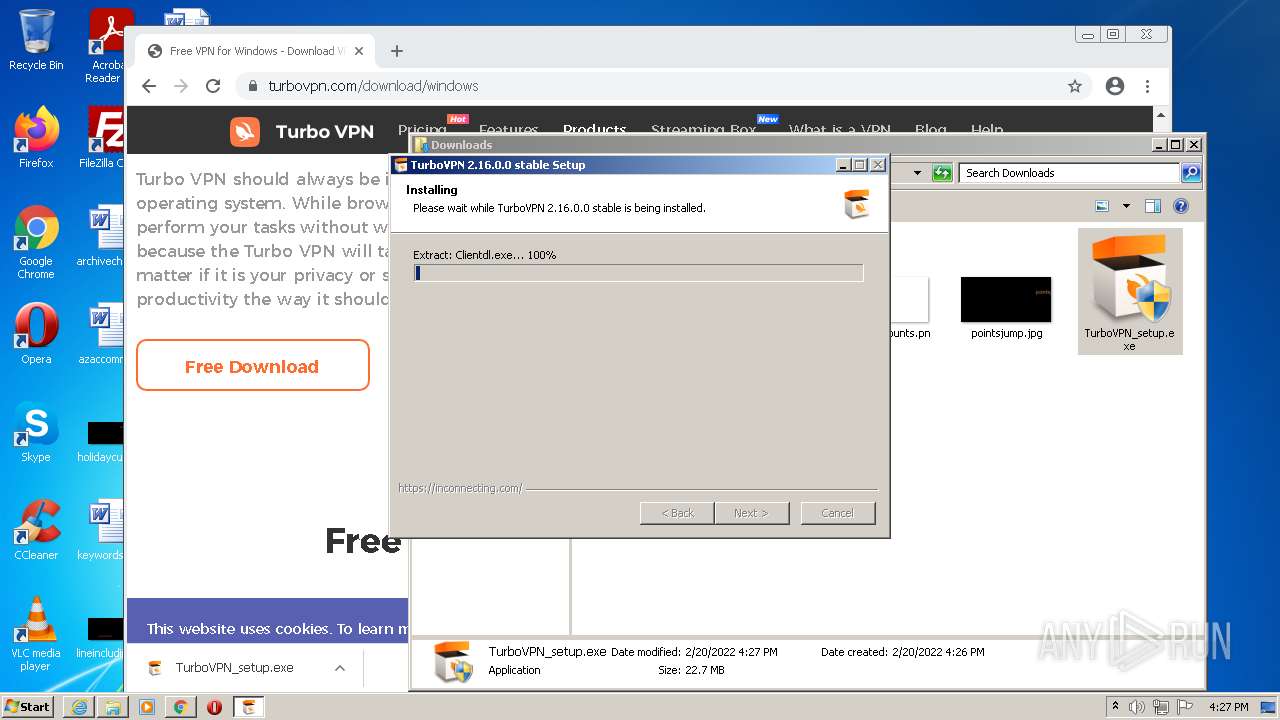
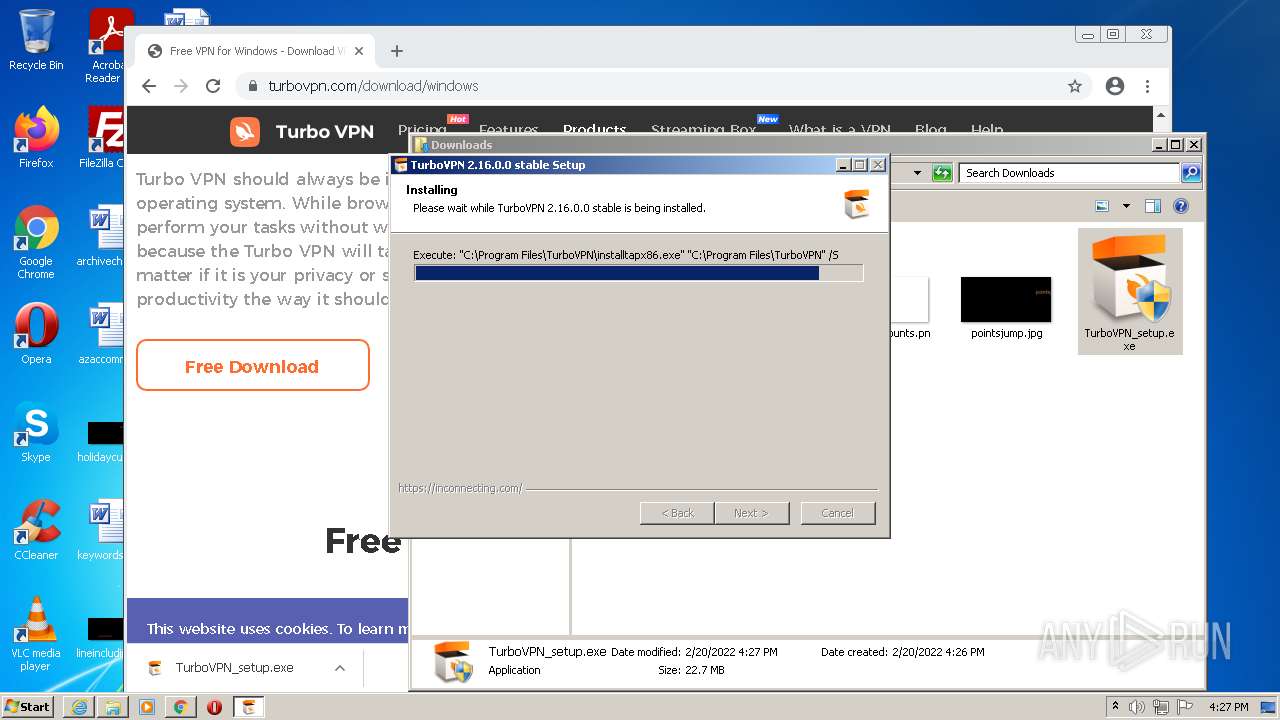
Application was dropped or rewritten from another process
- TurboVPN_setup.exe (PID: 464)
- TurboVPN_setup.exe (PID: 2328)
- installtapx86.exe (PID: 3152)
- turbo_vpn-service.exe (PID: 2644)
- turbo_vpn-service.exe (PID: 3488)
- turbo_vpn-service.exe (PID: 1988)
- TurboVPNLauncher.exe (PID: 328)
- TurboVPN.exe (PID: 1536)
- tun2socks.exe (PID: 2332)
Drops executable file immediately after starts
- TurboVPN_setup.exe (PID: 2328)
- DrvInst.exe (PID: 2492)
- DrvInst.exe (PID: 1212)
- chrome.exe (PID: 3788)
Loads dropped or rewritten executable
- TurboVPN_setup.exe (PID: 2328)
- turbo_vpn-service.exe (PID: 2644)
- turbo_vpn-service.exe (PID: 3488)
- turbo_vpn-service.exe (PID: 1988)
- TurboVPN.exe (PID: 1536)
Changes the autorun value in the registry
- DrvInst.exe (PID: 1212)
- TurboVPN_setup.exe (PID: 2328)
Changes settings of System certificates
- TurboVPN.exe (PID: 1536)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3988)
- iexplore.exe (PID: 2328)
Modifies files in Chrome extension folder
- chrome.exe (PID: 4016)
Executable content was dropped or overwritten
- chrome.exe (PID: 4016)
- chrome.exe (PID: 2424)
- TurboVPN_setup.exe (PID: 2328)
- installtapx86.exe (PID: 3152)
- DrvInst.exe (PID: 2492)
- DrvInst.exe (PID: 1212)
- chrome.exe (PID: 3788)
Reads the computer name
- TurboVPN_setup.exe (PID: 2328)
- installtapx86.exe (PID: 3152)
- DrvInst.exe (PID: 2492)
- DrvInst.exe (PID: 1212)
- turbo_vpn-service.exe (PID: 3488)
- turbo_vpn-service.exe (PID: 2644)
- turbo_vpn-service.exe (PID: 1988)
- TurboVPNLauncher.exe (PID: 328)
- TurboVPN.exe (PID: 1536)
- tun2socks.exe (PID: 2332)
Checks supported languages
- TurboVPN_setup.exe (PID: 2328)
- installtapx86.exe (PID: 3152)
- DrvInst.exe (PID: 2492)
- DrvInst.exe (PID: 1212)
- turbo_vpn-service.exe (PID: 2644)
- turbo_vpn-service.exe (PID: 1988)
- turbo_vpn-service.exe (PID: 3488)
- TurboVPNLauncher.exe (PID: 328)
- tun2socks.exe (PID: 2332)
- TurboVPN.exe (PID: 1536)
Drops a file that was compiled in debug mode
- TurboVPN_setup.exe (PID: 2328)
- installtapx86.exe (PID: 3152)
- DrvInst.exe (PID: 2492)
- DrvInst.exe (PID: 1212)
- chrome.exe (PID: 3788)
Checks for external IP
- TurboVPN_setup.exe (PID: 2328)
- TurboVPN.exe (PID: 1536)
Drops a file with too old compile date
- TurboVPN_setup.exe (PID: 2328)
Creates files in the program directory
- TurboVPN_setup.exe (PID: 2328)
- turbo_vpn-service.exe (PID: 2644)
- TurboVPNLauncher.exe (PID: 328)
- TurboVPN.exe (PID: 1536)
- turbo_vpn-service.exe (PID: 3488)
Creates a directory in Program Files
- TurboVPN_setup.exe (PID: 2328)
- TurboVPN.exe (PID: 1536)
Drops a file with a compile date too recent
- TurboVPN_setup.exe (PID: 2328)
Executed via COM
- DrvInst.exe (PID: 2492)
- DrvInst.exe (PID: 1212)
Creates files in the Windows directory
- DrvInst.exe (PID: 2492)
- DrvInst.exe (PID: 1212)
Uses RUNDLL32.EXE to load library
- DrvInst.exe (PID: 2492)
Removes files from Windows directory
- DrvInst.exe (PID: 2492)
- DrvInst.exe (PID: 1212)
Creates files in the driver directory
- DrvInst.exe (PID: 2492)
- DrvInst.exe (PID: 1212)
Executed as Windows Service
- vssvc.exe (PID: 2928)
- turbo_vpn-service.exe (PID: 1988)
Reads Environment values
- vssvc.exe (PID: 2928)
- DrvInst.exe (PID: 1212)
- netsh.exe (PID: 2672)
- netsh.exe (PID: 3436)
Creates files in the user directory
- TurboVPN_setup.exe (PID: 2328)
Creates a software uninstall entry
- TurboVPN_setup.exe (PID: 2328)
Creates or modifies windows services
- TurboVPN.exe (PID: 1536)
Uses NETSH.EXE for network configuration
- tun2socks.exe (PID: 2332)
Uses IPCONFIG.EXE to discover IP address
- TurboVPN.exe (PID: 1536)
INFO
Checks supported languages
- iexplore.exe (PID: 2284)
- iexplore.exe (PID: 3988)
- chrome.exe (PID: 4016)
- chrome.exe (PID: 2168)
- chrome.exe (PID: 1108)
- chrome.exe (PID: 2424)
- chrome.exe (PID: 3048)
- chrome.exe (PID: 3432)
- chrome.exe (PID: 2980)
- chrome.exe (PID: 1140)
- chrome.exe (PID: 3652)
- chrome.exe (PID: 3260)
- chrome.exe (PID: 3188)
- chrome.exe (PID: 3596)
- chrome.exe (PID: 1876)
- chrome.exe (PID: 3888)
- chrome.exe (PID: 3160)
- chrome.exe (PID: 2700)
- chrome.exe (PID: 3456)
- chrome.exe (PID: 336)
- chrome.exe (PID: 3288)
- chrome.exe (PID: 2844)
- chrome.exe (PID: 3328)
- chrome.exe (PID: 3484)
- chrome.exe (PID: 3332)
- chrome.exe (PID: 1084)
- chrome.exe (PID: 2728)
- chrome.exe (PID: 3556)
- chrome.exe (PID: 3180)
- chrome.exe (PID: 3796)
- chrome.exe (PID: 2824)
- chrome.exe (PID: 3264)
- chrome.exe (PID: 3012)
- chrome.exe (PID: 1940)
- chrome.exe (PID: 3624)
- chrome.exe (PID: 2328)
- chrome.exe (PID: 2508)
- chrome.exe (PID: 2196)
- explorer.exe (PID: 2480)
- chrome.exe (PID: 412)
- chrome.exe (PID: 2208)
- chrome.exe (PID: 3428)
- chrome.exe (PID: 1328)
- chrome.exe (PID: 412)
- rundll32.exe (PID: 2480)
- vssvc.exe (PID: 2928)
- chrome.exe (PID: 548)
- chrome.exe (PID: 2784)
- route.exe (PID: 2784)
- netsh.exe (PID: 2672)
- netsh.exe (PID: 3436)
- ipconfig.exe (PID: 2556)
- chrome.exe (PID: 3224)
- chrome.exe (PID: 3148)
- chrome.exe (PID: 3788)
- iexplore.exe (PID: 2328)
- chrome.exe (PID: 2368)
- chrome.exe (PID: 4072)
- chrome.exe (PID: 2820)
- chrome.exe (PID: 1584)
- chrome.exe (PID: 3084)
- chrome.exe (PID: 864)
- chrome.exe (PID: 3796)
- chrome.exe (PID: 3068)
- chrome.exe (PID: 3148)
Reads the computer name
- iexplore.exe (PID: 2284)
- iexplore.exe (PID: 3988)
- chrome.exe (PID: 4016)
- chrome.exe (PID: 1108)
- chrome.exe (PID: 2424)
- chrome.exe (PID: 3652)
- chrome.exe (PID: 3012)
- explorer.exe (PID: 2480)
- chrome.exe (PID: 2196)
- chrome.exe (PID: 2208)
- chrome.exe (PID: 1328)
- chrome.exe (PID: 412)
- rundll32.exe (PID: 2480)
- vssvc.exe (PID: 2928)
- chrome.exe (PID: 2784)
- netsh.exe (PID: 3436)
- ipconfig.exe (PID: 2556)
- iexplore.exe (PID: 2328)
- netsh.exe (PID: 2672)
Changes internet zones settings
- iexplore.exe (PID: 2284)
Application launched itself
- iexplore.exe (PID: 2284)
- chrome.exe (PID: 4016)
Reads settings of System Certificates
- iexplore.exe (PID: 2284)
- chrome.exe (PID: 2424)
- iexplore.exe (PID: 3988)
- chrome.exe (PID: 4016)
- installtapx86.exe (PID: 3152)
- DrvInst.exe (PID: 2492)
- rundll32.exe (PID: 2480)
- DrvInst.exe (PID: 1212)
- TurboVPN.exe (PID: 1536)
- iexplore.exe (PID: 2328)
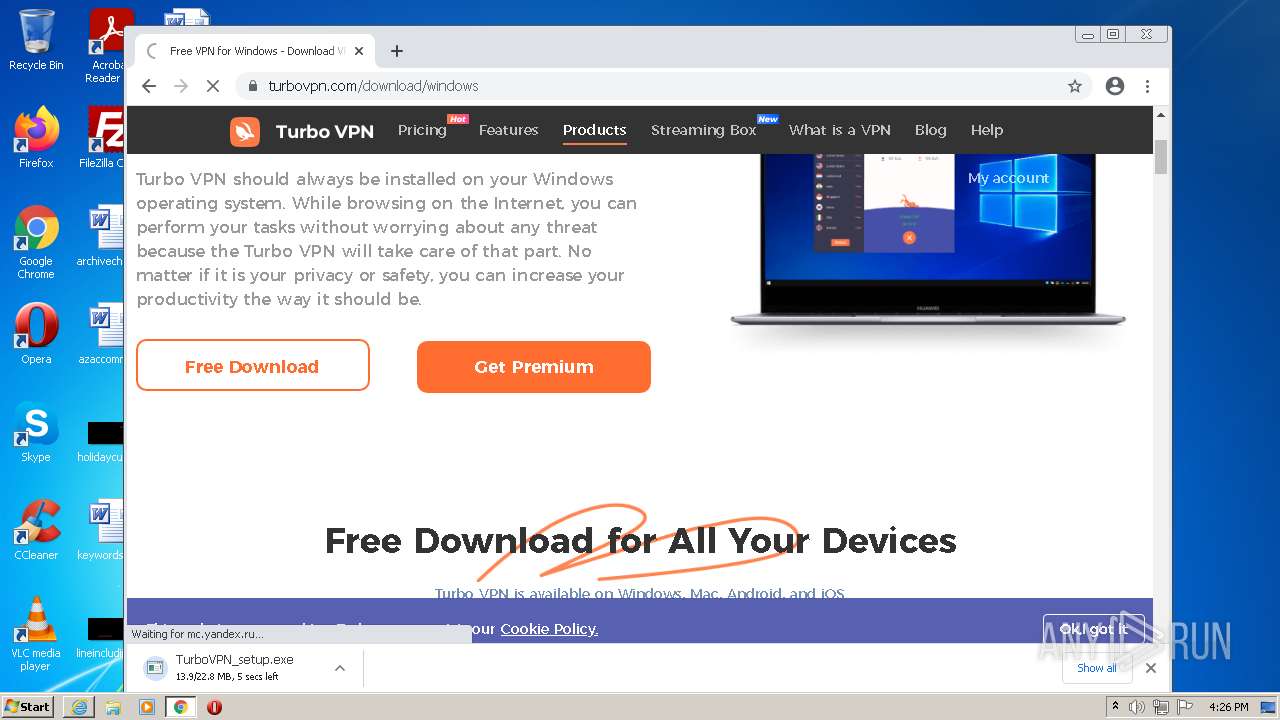
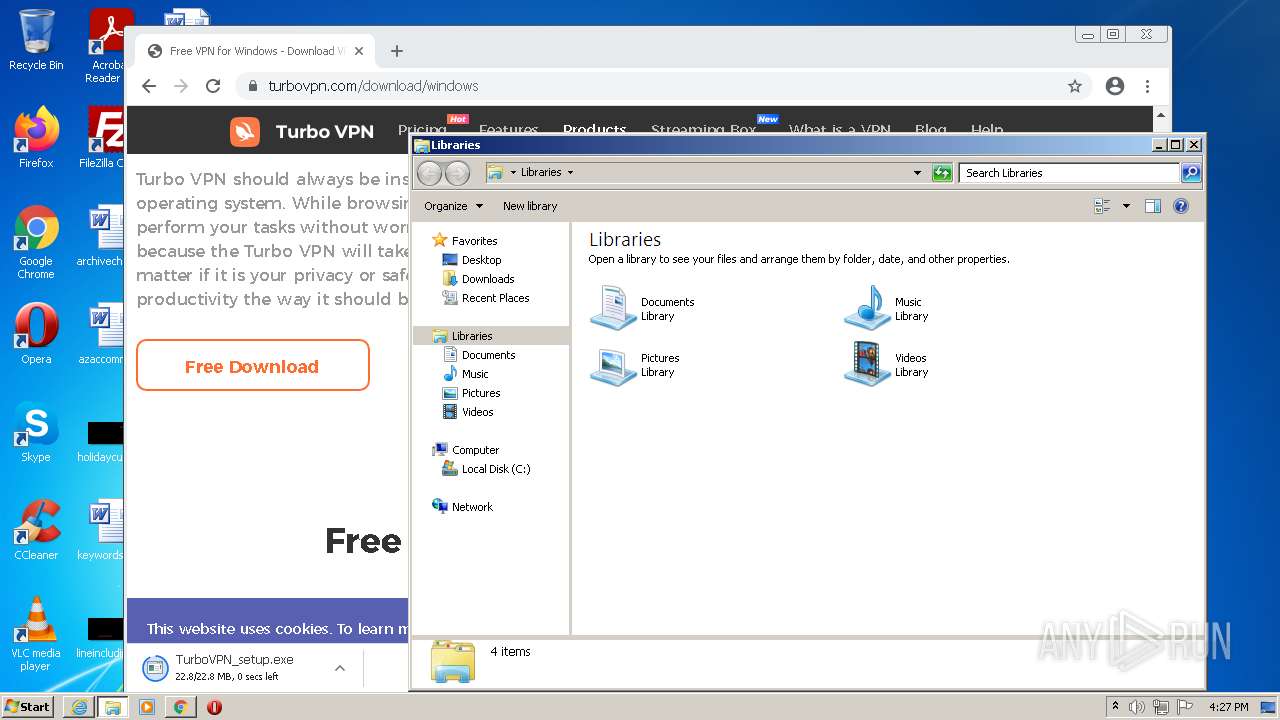
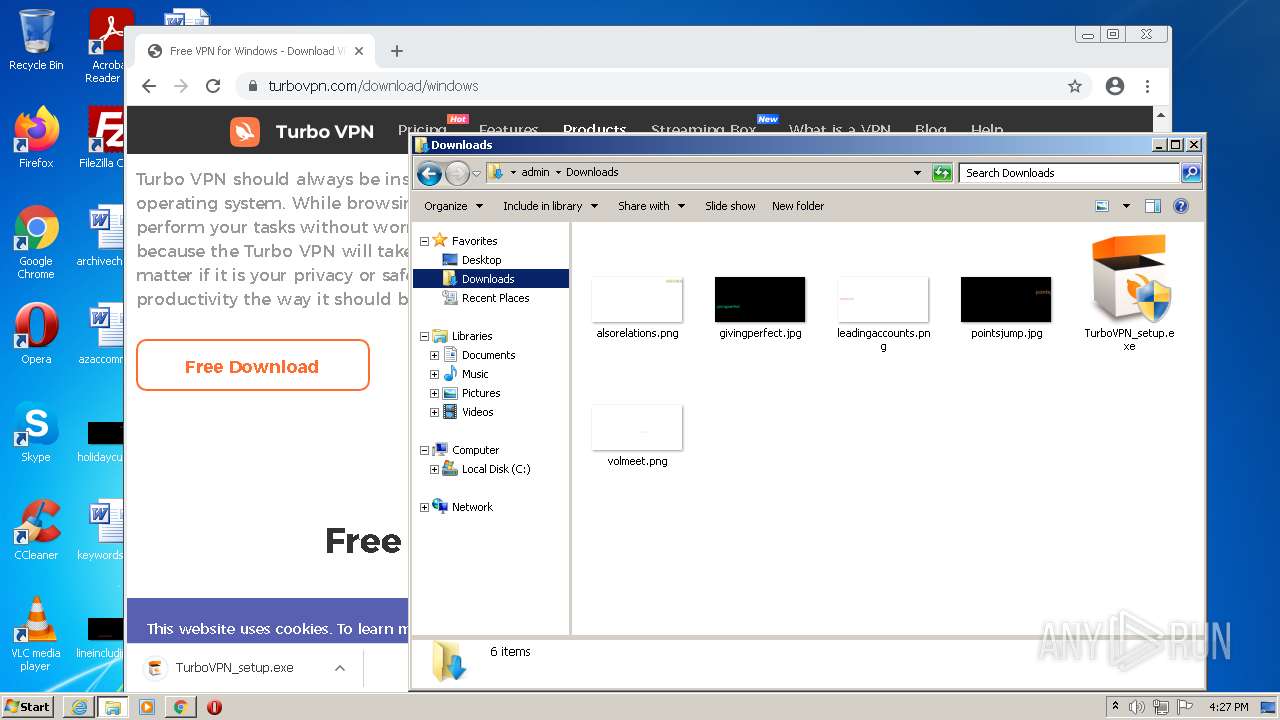
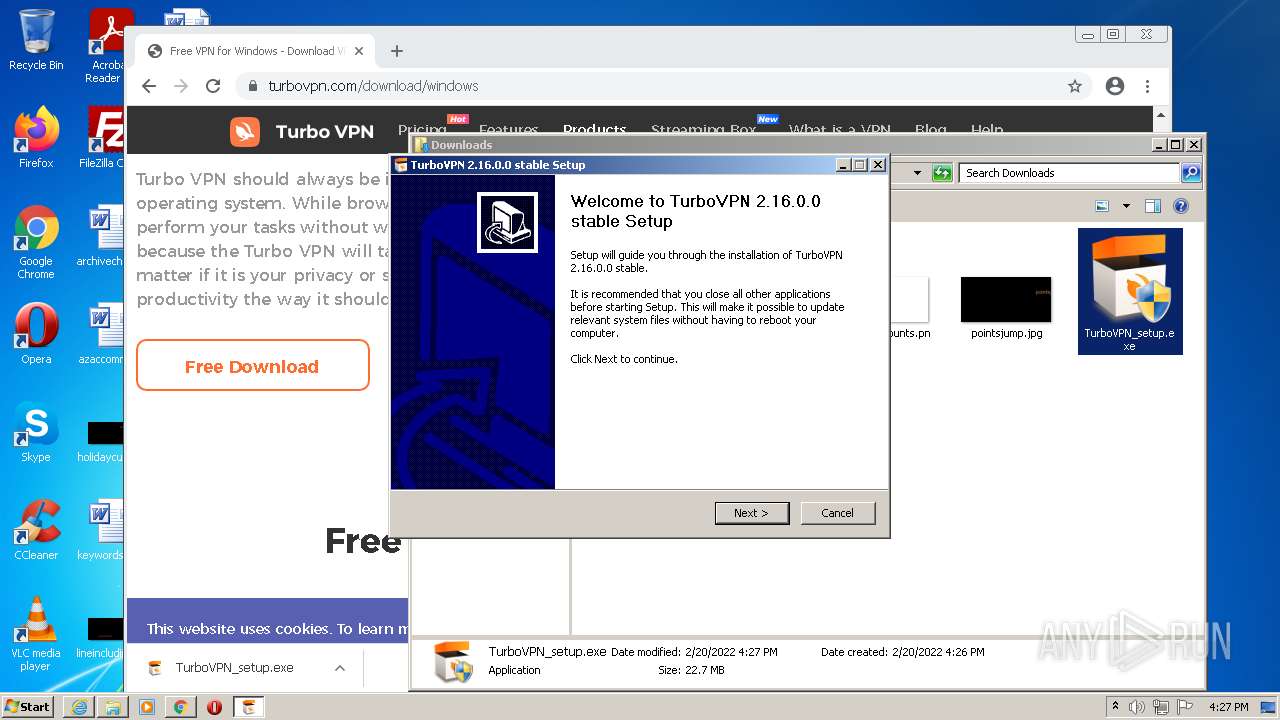
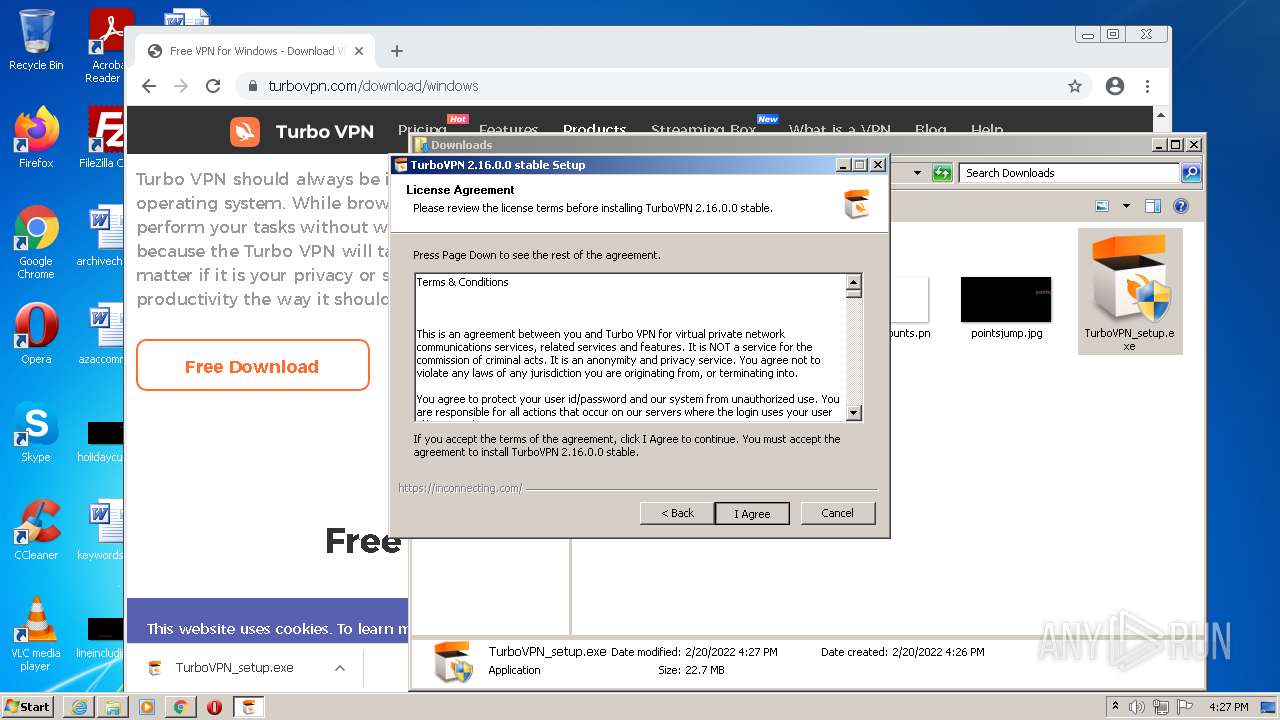
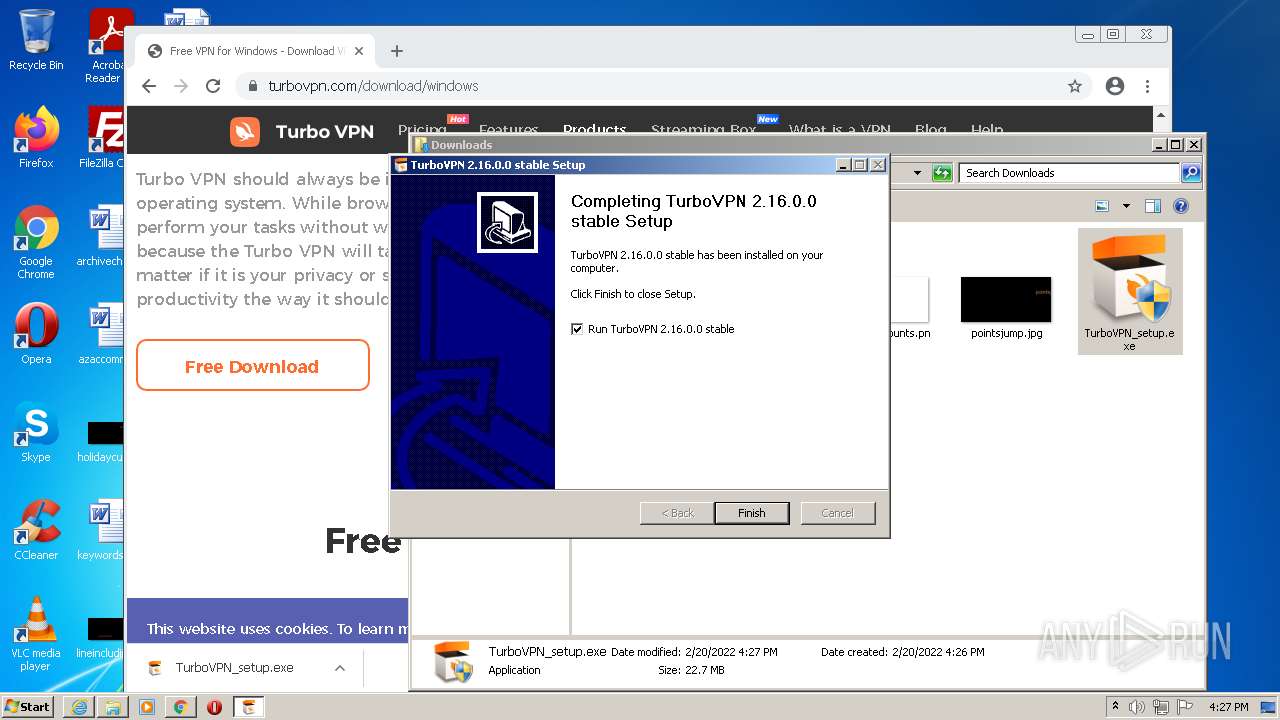
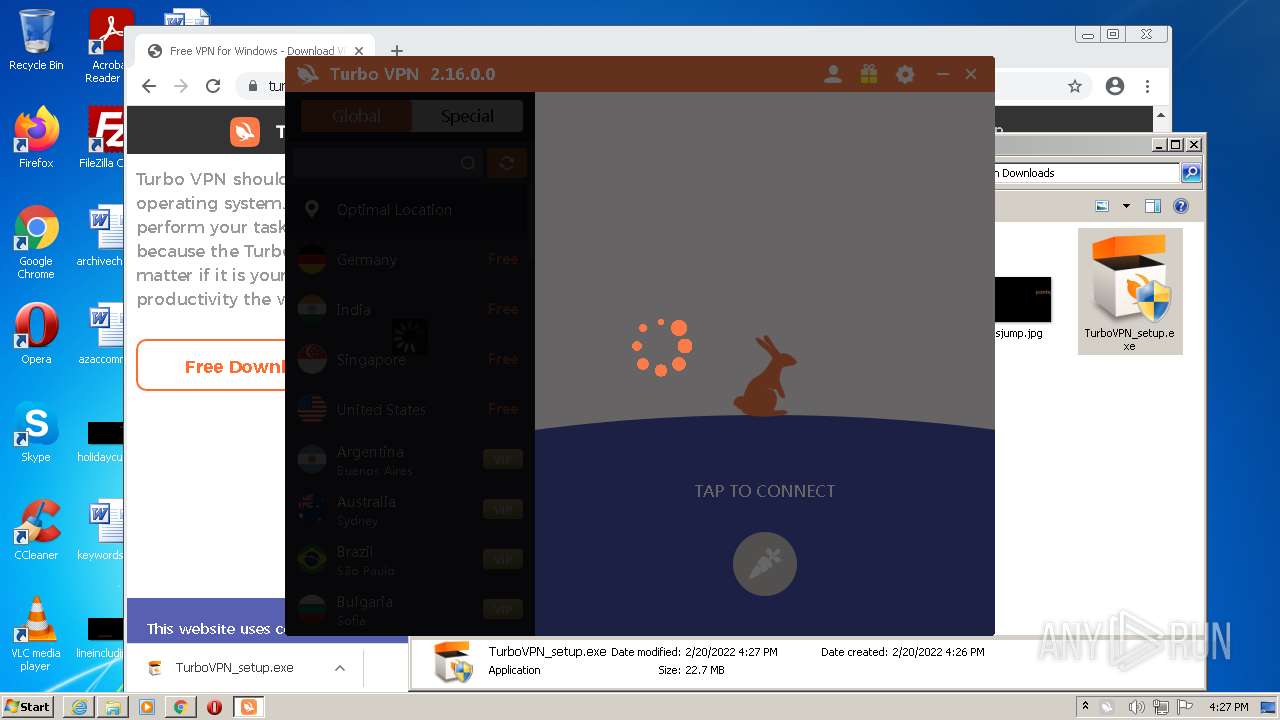
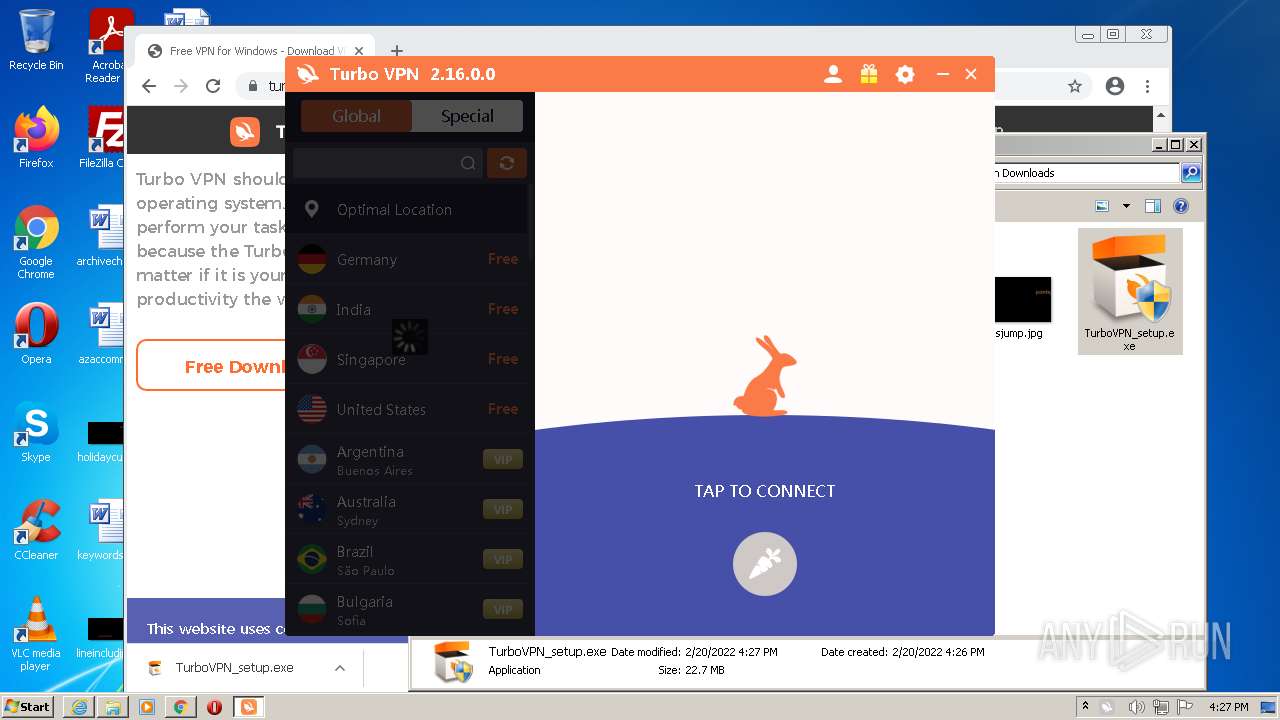
Manual execution by user
- chrome.exe (PID: 4016)
- explorer.exe (PID: 2480)
- TurboVPN_setup.exe (PID: 464)
- TurboVPN_setup.exe (PID: 2328)
Checks Windows Trust Settings
- iexplore.exe (PID: 2284)
- iexplore.exe (PID: 3988)
- chrome.exe (PID: 4016)
- installtapx86.exe (PID: 3152)
- DrvInst.exe (PID: 2492)
- rundll32.exe (PID: 2480)
- DrvInst.exe (PID: 1212)
- TurboVPN.exe (PID: 1536)
- iexplore.exe (PID: 2328)
Reads the hosts file
- chrome.exe (PID: 4016)
- chrome.exe (PID: 2424)
- TurboVPN.exe (PID: 1536)
Reads internet explorer settings
- iexplore.exe (PID: 3988)
- iexplore.exe (PID: 2328)
Creates files in the user directory
- iexplore.exe (PID: 3988)
- iexplore.exe (PID: 2284)
- iexplore.exe (PID: 2328)
Dropped object may contain Bitcoin addresses
- TurboVPN_setup.exe (PID: 2328)
Reads the date of Windows installation
- chrome.exe (PID: 412)
Changes settings of System certificates
- iexplore.exe (PID: 2284)
- DrvInst.exe (PID: 2492)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2284)
Searches for installed software
- DrvInst.exe (PID: 2492)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
130
Monitored processes
76
Malicious processes
6
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 328 | "C:\Program Files\TurboVPN\TurboVPNLauncher.exe" | C:\Program Files\TurboVPN\TurboVPNLauncher.exe | — | TurboVPN_setup.exe | |||||||||||
User: admin Company: Innovative Connecting Integrity Level: HIGH Description: Startup Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1056,15682893856489199033,12771587244817023452,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3468 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1056,15682893856489199033,12771587244817023452,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=4312 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1056,15682893856489199033,12771587244817023452,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=972 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 464 | "C:\Users\admin\Downloads\TurboVPN_setup.exe" | C:\Users\admin\Downloads\TurboVPN_setup.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Innovative Connecting Integrity Level: MEDIUM Description: TurboVPN Exit code: 3221226540 Version: 2.16.0.0 Modules
| |||||||||||||||
| 548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1056,15682893856489199033,12771587244817023452,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=536 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1056,15682893856489199033,12771587244817023452,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2432 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1084 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1056,15682893856489199033,12771587244817023452,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=4132 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1056,15682893856489199033,12771587244817023452,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1064 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1056,15682893856489199033,12771587244817023452,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2960 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
74 089
Read events
72 909
Write events
1 118
Delete events
62
Modification events
| (PID) Process: | (2284) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2284) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2284) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30942838 | |||
| (PID) Process: | (2284) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2284) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30942838 | |||
| (PID) Process: | (2284) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2284) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2284) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2284) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2284) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
42
Suspicious files
278
Text files
347
Unknown types
56
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62126BB5-FB0.pma | — | |
MD5:— | SHA256:— | |||
| 2284 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2284 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 4016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 4016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 4016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 2168 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 4016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4cee9078-6d2e-43a5-ae54-dbc9b9a947ba.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 4016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 4016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b097df0f-51d1-433e-86fd-dc60825d4639.tmp | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
73
TCP/UDP connections
478
DNS requests
94
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2284 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.68 Kb | whitelisted |
3988 | iexplore.exe | GET | 200 | 99.86.1.190:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
3988 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
3988 | iexplore.exe | GET | 200 | 143.204.214.40:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
3988 | iexplore.exe | GET | 200 | 99.86.1.190:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
3988 | iexplore.exe | GET | 200 | 142.250.181.227:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3988 | iexplore.exe | GET | 200 | 143.204.214.169:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEAoyW5lNAX05D0gn%2BE1SJ%2BQ%3D | US | der | 471 b | whitelisted |
2284 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3988 | iexplore.exe | GET | 200 | 143.204.214.169:80 | http://ocsp.sca1b.amazontrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQz9arGHWbnBV0DFzpNHz4YcTiFDQQUWaRmBlKge5WSPKOUByeWdFv5PdACEAFmHKQG%2FMSndoNDmtt9NKg%3D | US | der | 471 b | whitelisted |
3988 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2284 | iexplore.exe | 67.27.159.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | malicious |
2424 | chrome.exe | 142.250.185.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3988 | iexplore.exe | 143.204.98.57:443 | turbovpn.com | — | US | unknown |
2284 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2284 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2284 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
2424 | chrome.exe | 142.250.185.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
2424 | chrome.exe | 142.250.181.228:443 | www.google.com | Google Inc. | US | whitelisted |
2424 | chrome.exe | 142.250.184.237:443 | accounts.google.com | Google Inc. | US | suspicious |
2424 | chrome.exe | 142.250.185.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
turbovpn.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
www.google.com |
| malicious |
accounts.google.com |
| shared |
crl3.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2328 | TurboVPN_setup.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
2328 | TurboVPN_setup.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
2328 | TurboVPN_setup.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
2328 | TurboVPN_setup.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
2328 | TurboVPN_setup.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
2328 | TurboVPN_setup.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
2328 | TurboVPN_setup.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
2328 | TurboVPN_setup.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
1536 | TurboVPN.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
1536 | TurboVPN.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
Process | Message |
|---|---|
TurboVPN_setup.exe | {}
|
installtapx86.exe | 3 |
installtapx86.exe | C:\Program Files\TurboVPN\installtapx86.exe |
installtapx86.exe | C:\Program Files\TurboVPN |
installtapx86.exe | /S |
installtapx86.exe | C:\Program Files\TurboVPN\installtapx86.exe C:\Program Files\TurboVPN /S |
installtapx86.exe | C:\Program Files\TurboVPN |
installtapx86.exe | C:\Program Files\TurboVPN\installtapx86.exe |
installtapx86.exe | strCmdType |
installtapx86.exe | |