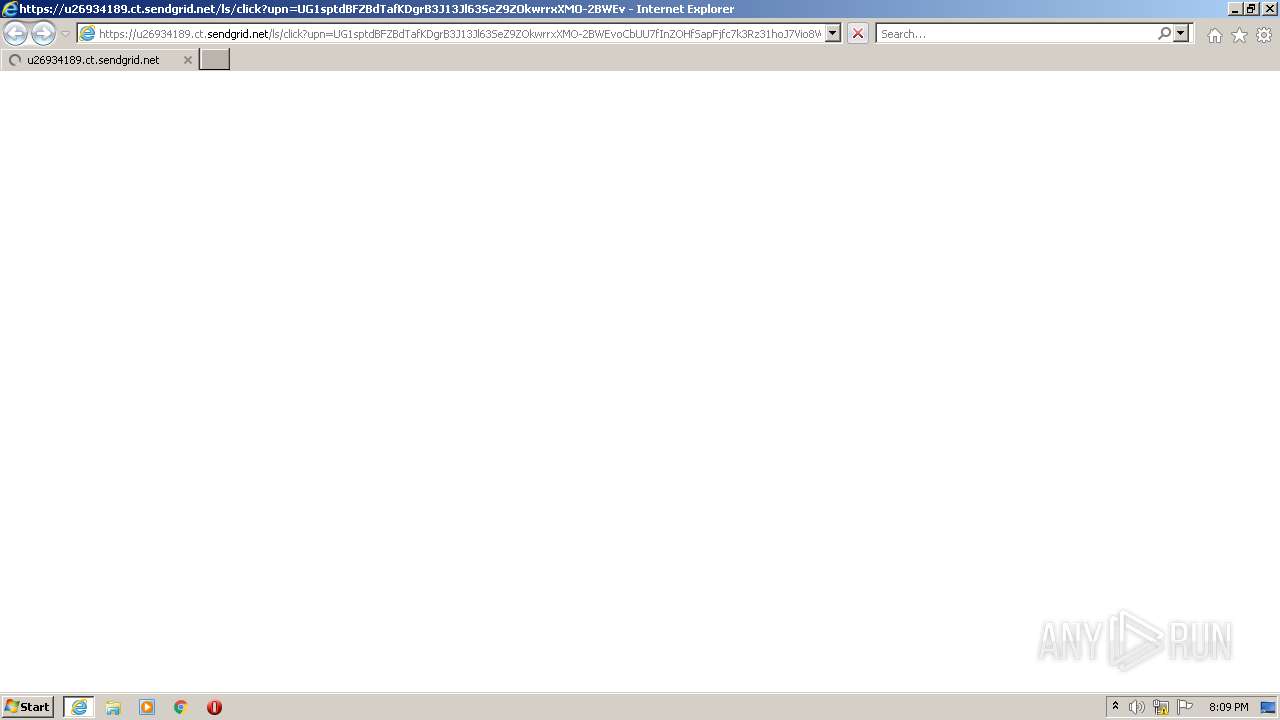
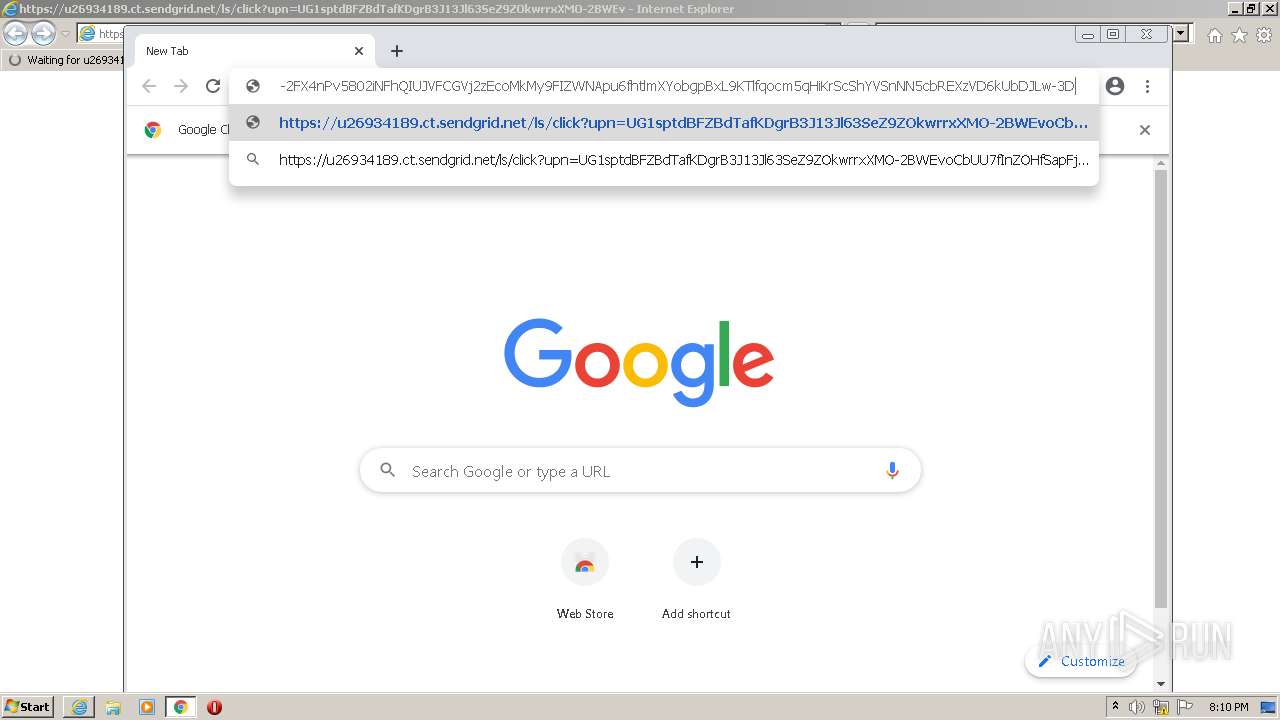
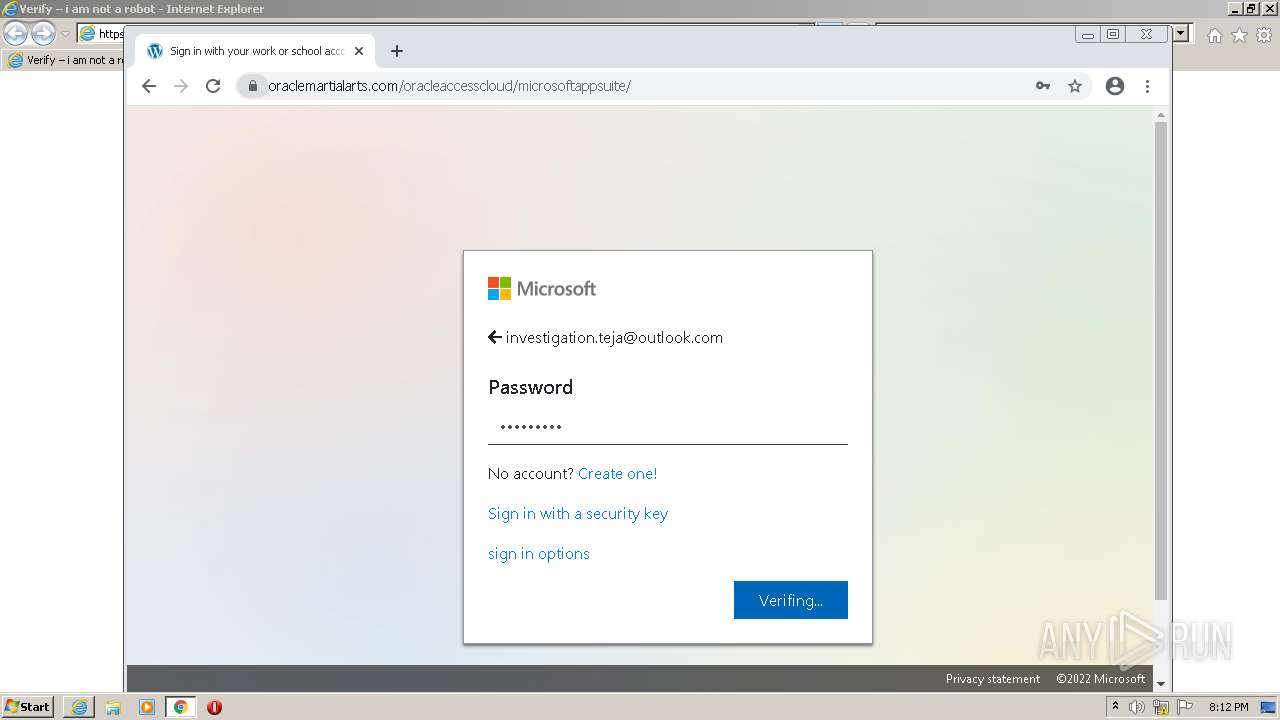
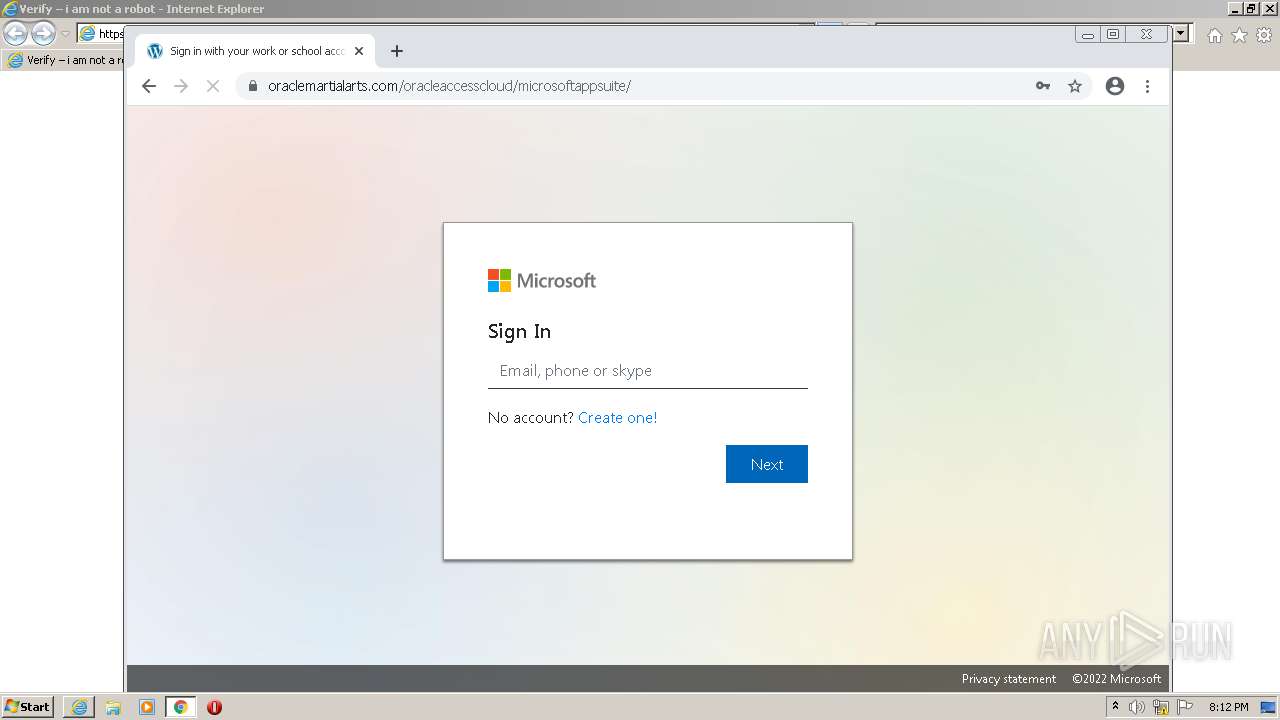
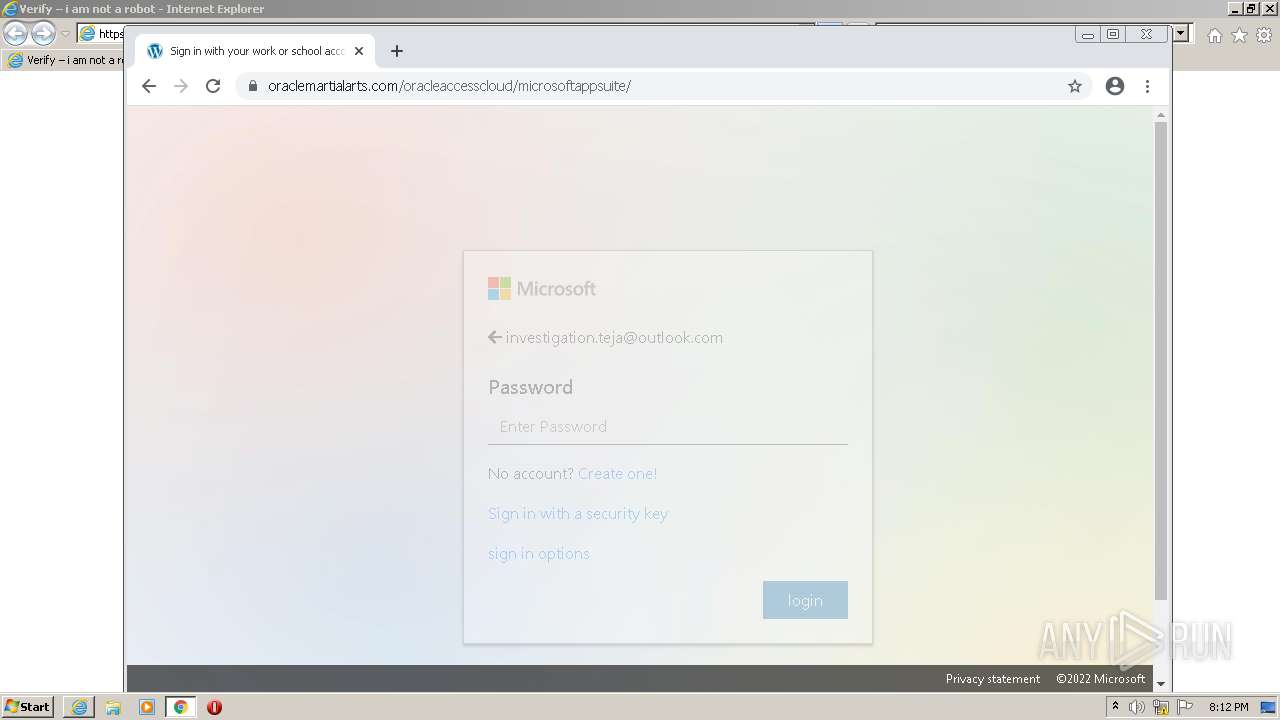
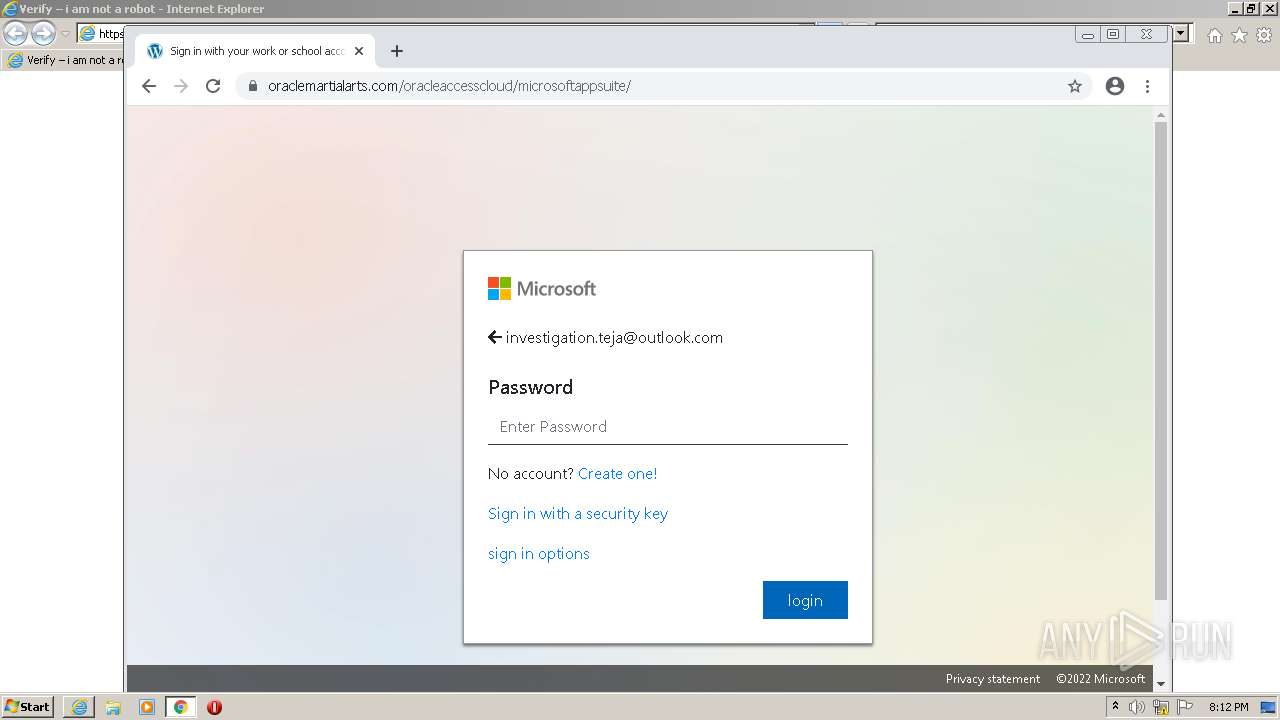
| URL: | https://u26934189.ct.sendgrid.net/ls/click?upn=UG1sptdBFZBdTafKDgrB3J13Jl63SeZ9ZOkwrrxXMO-2BWEvoCbUU7fInZOHfSapFjfc7k3Rz31hoJ7Vio8Wm7Pw-3D-3DIRyk_QzYfKuVeYTHRVjziq4uwJdnFyoggSW4hlimJdGWUGo9xOWlX-2BWR2aaAghpuAGStbUZRAU3uNIj0jizkY8zEyy2gAANp-2FYAM-2FtOyFzff1i3-2BtBuT4ba7IWbZrXbiLMHLtodS6dmsEO3GP0NmNPyHy6w9o-2FqDoJDkrJofbLgvLr8cMXKnTYeDT-2FeT2-2FiewAUIeiFbw6HhbJ3GL2715LMAYpdzh-2BGnT89jn7Z-2FRkW-2Fxn4S29ThcD1FEvCZSSTI2NiqvnWb5qdsO3-2BOEKSmHzirH2-2FukvxGERDcGr5tPjZu63K5UEz4RUY2hQ-2BEmJNaUcrZuS6nUqJGoCQ-2F-2B7UnLRXHO64AWkN4yunMlJqqyqVgoC2AEzl4ZW-2BwFQ9BTUbNH4WrA8AChHqqC0BpsiDB2GEeM8LGOz6aAczi37eWN3ldGrQre4gi9wlceNQI3DLy3yR-2F1YrafGfQUdL0FAwCS2bvLxHHKV5jtBWhV8a3XMIPDFK9KsmiJ3RPChUTNlpiCg1HlVjBOnIq5sB1Zk6-2FEN0iLsjm1XdvzrlTneV3HAo05t-2BG2kxNXUojWUB6n0Pgv7gwbdKQxMSnroWLpChy0QXCjZ0DxDK-2FmfYIv3sGyIdVLv0W6b2VKL2SoGSI-2FweHs78nuALv8OZ2tkcyCPeAwHBjoYNiUp-2F3lxvabGRj1nUOApkzeLWDiaodbguq05AiwE8us7fBtyEw-2FTa-2Fwd9UsHOaI0nkQv1f2LiHFDK2QGTgnKDKDHRmMv-2Fh1Ko9NtFsyHbltVDGWovsk-2FX4nPv5802iNFhQIUJVFCGVj2zEcoMkMy9FIZWNApu6fhtlmXYobgpBxL9KTlfqocm5qHiKrScShYVSnNN5cbREXzVD6kUbDJLw-3D |
| Full analysis: | https://app.any.run/tasks/c35d2bf7-37e5-4e8f-bdbc-f15868acd2f1 |
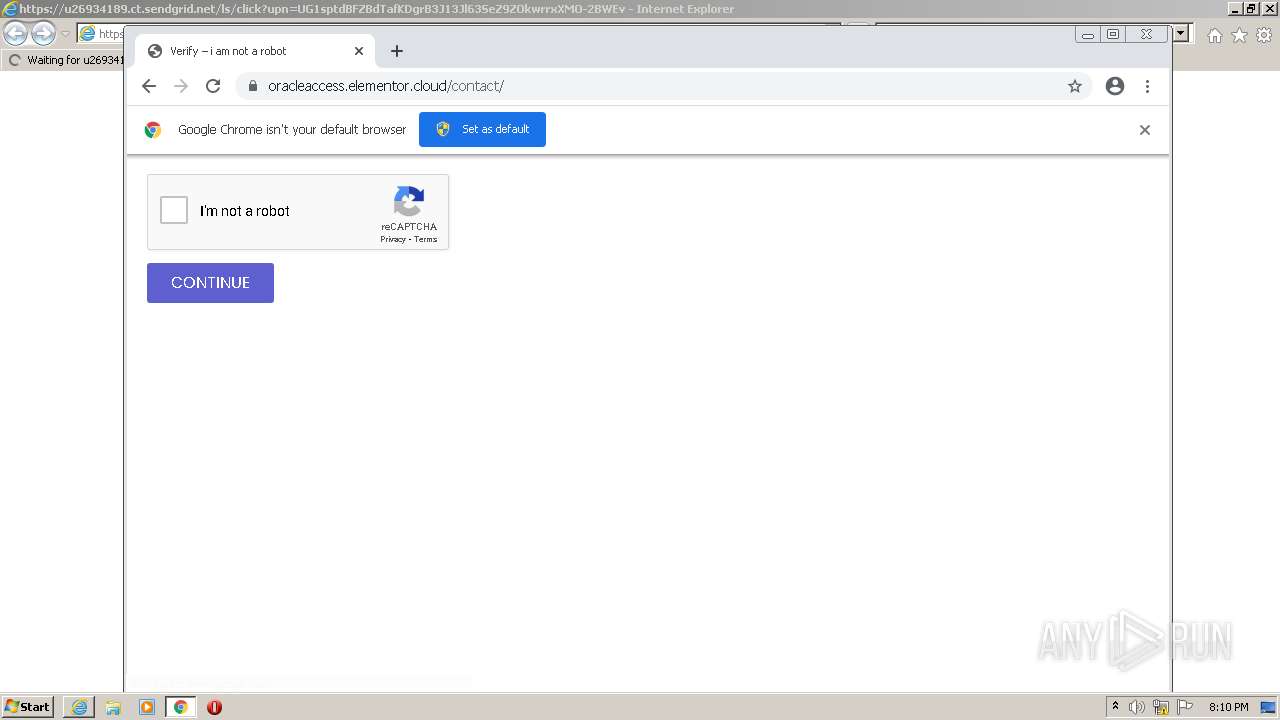
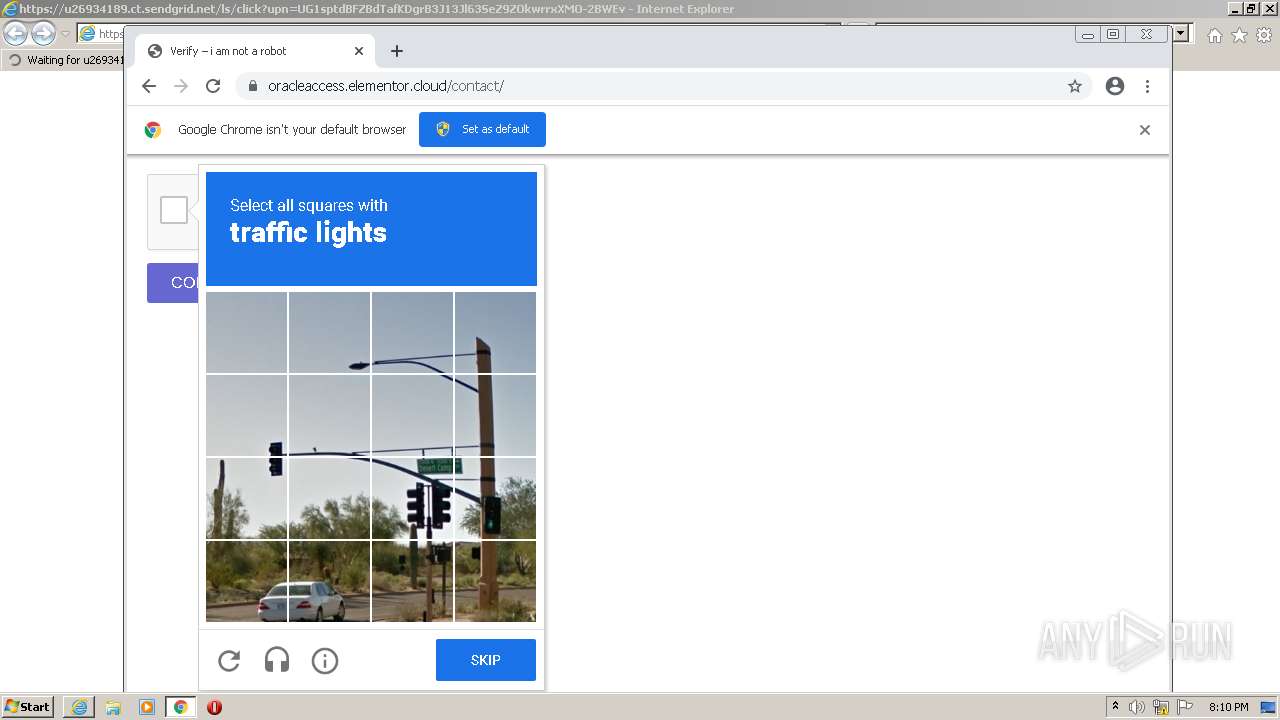
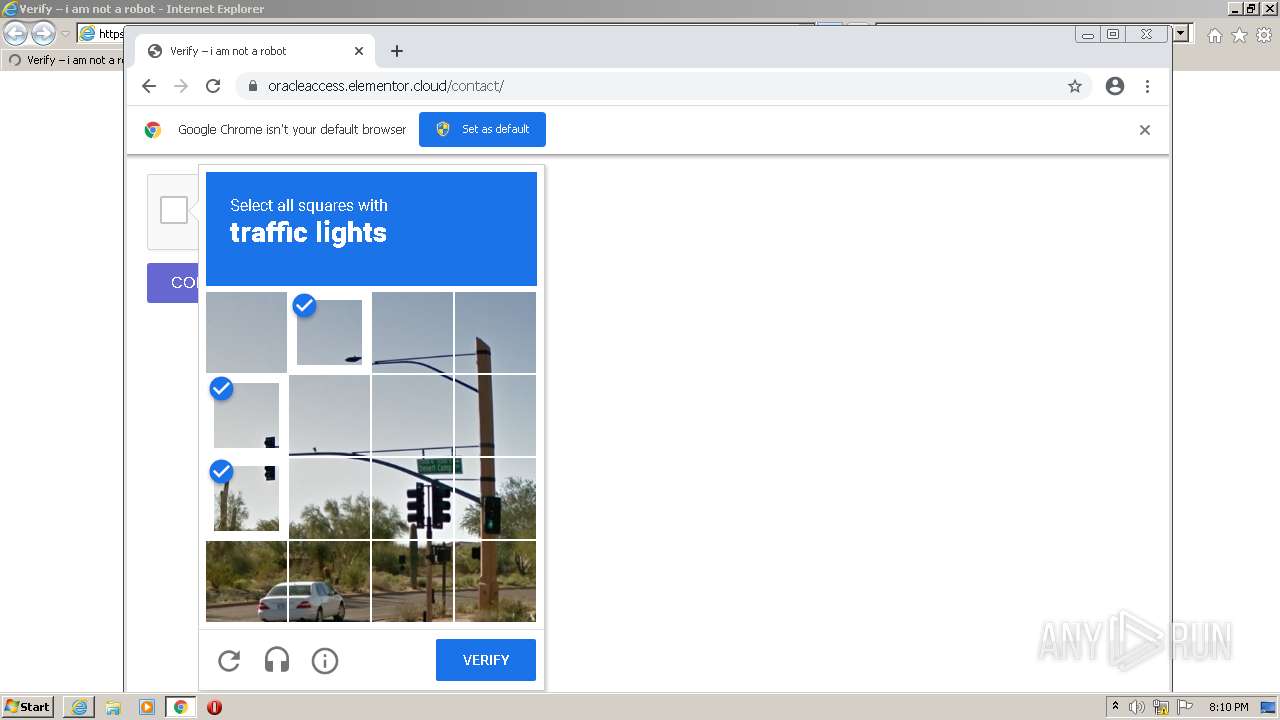
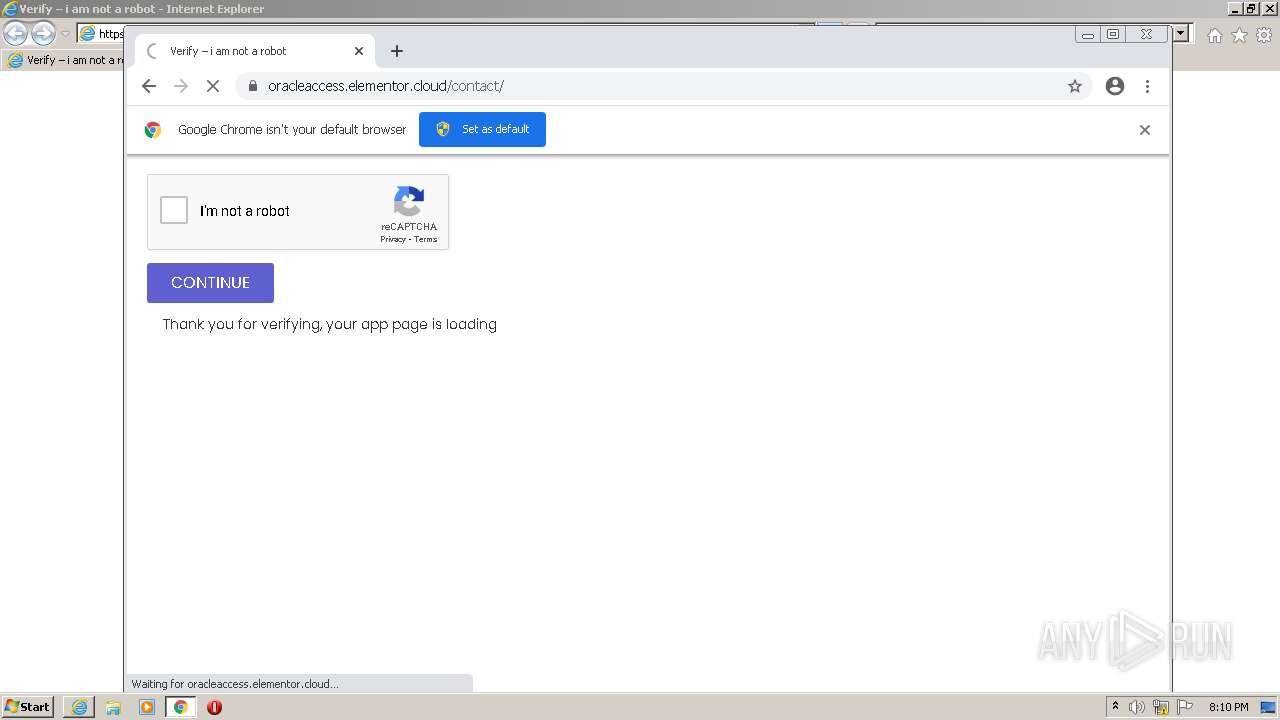
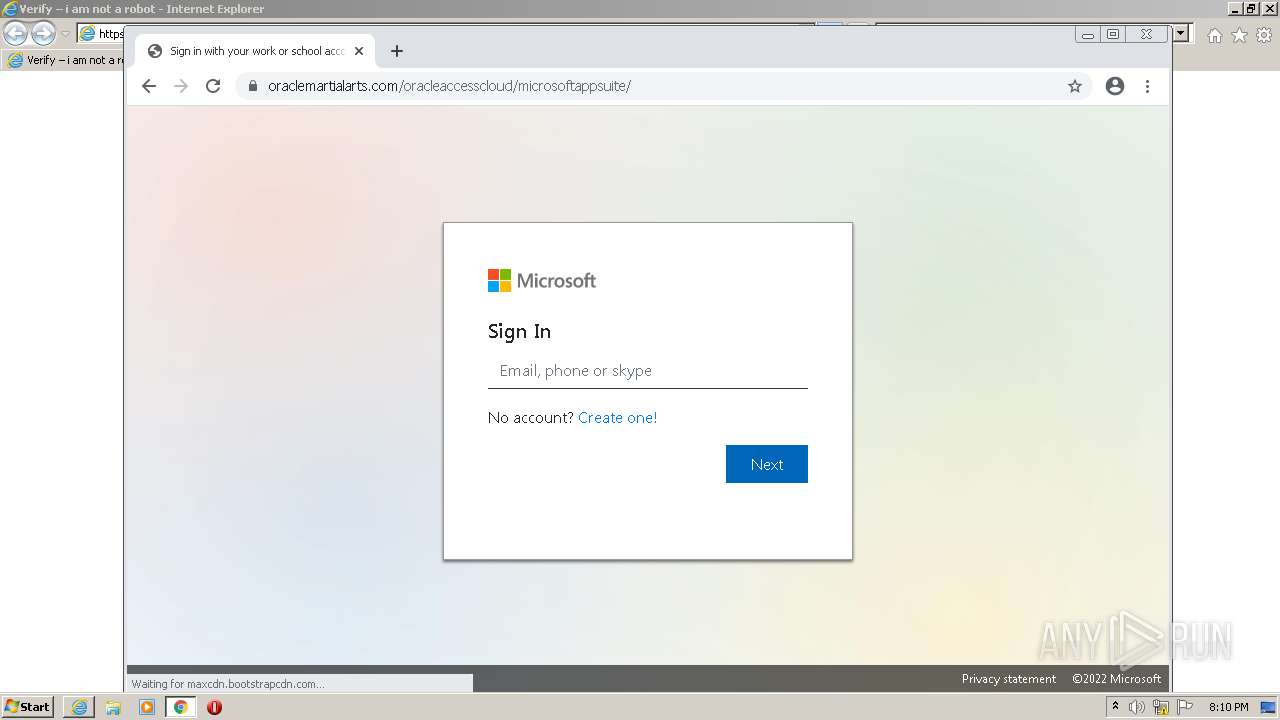
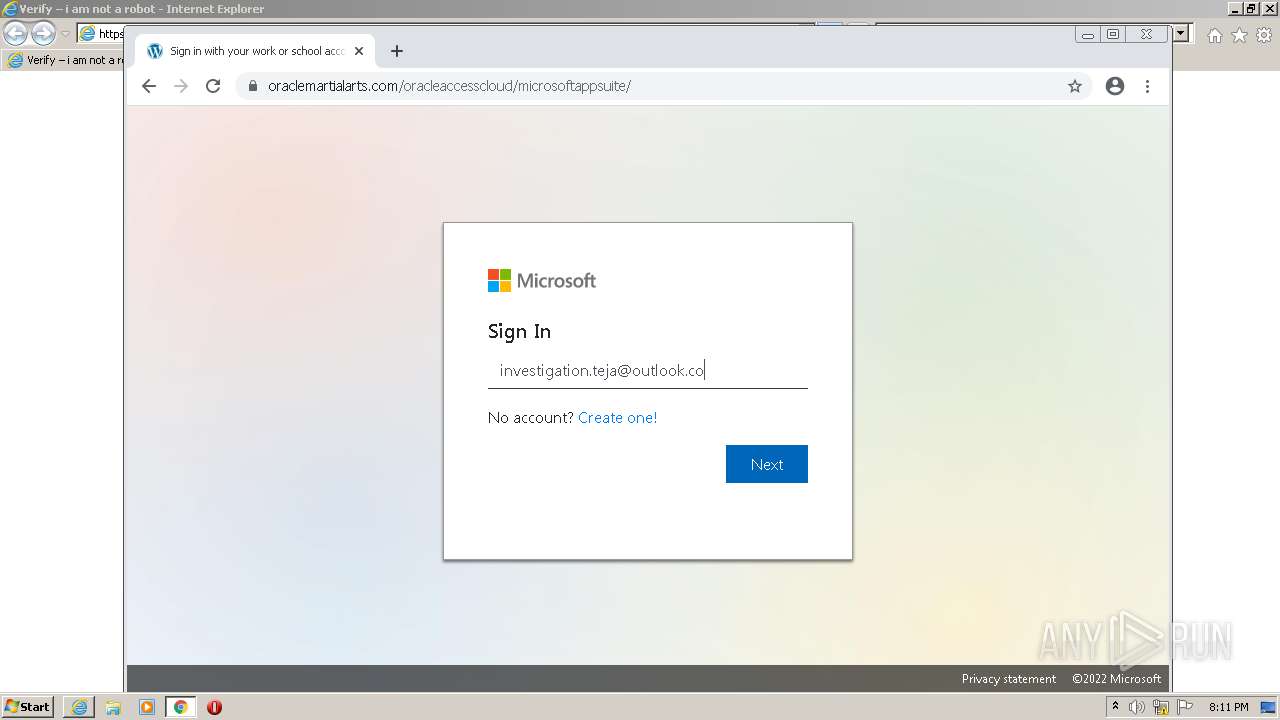
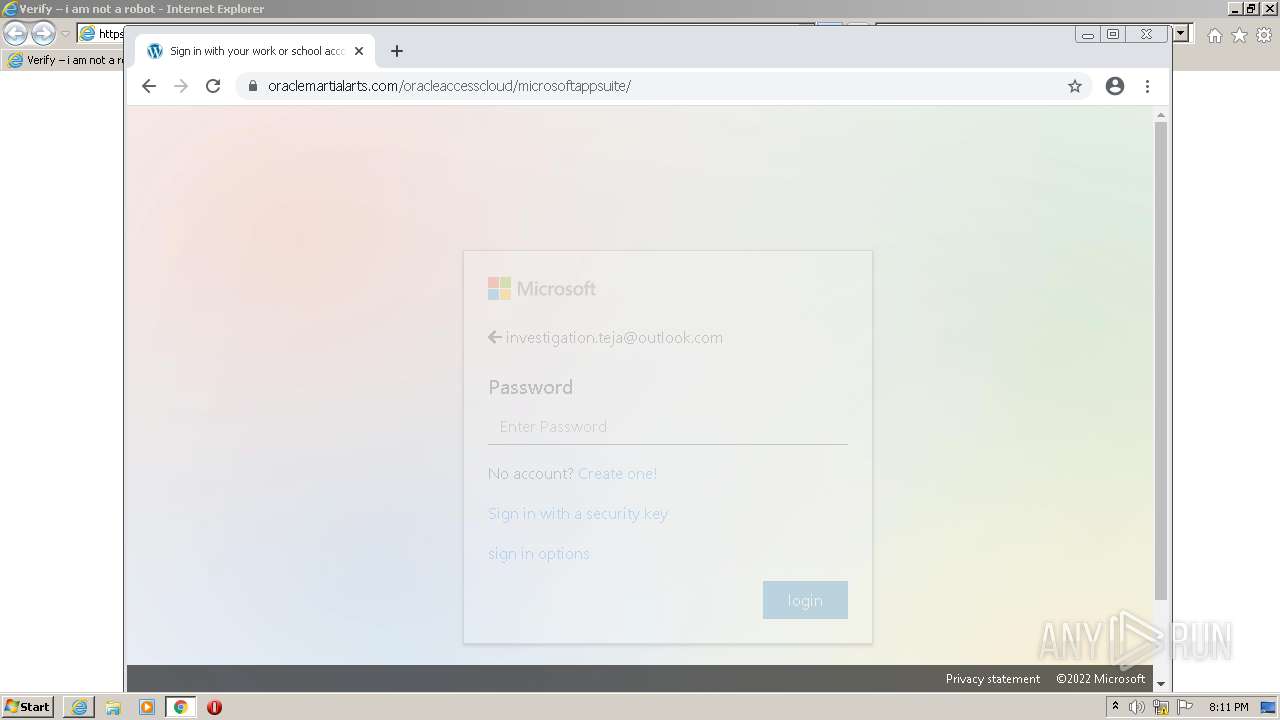
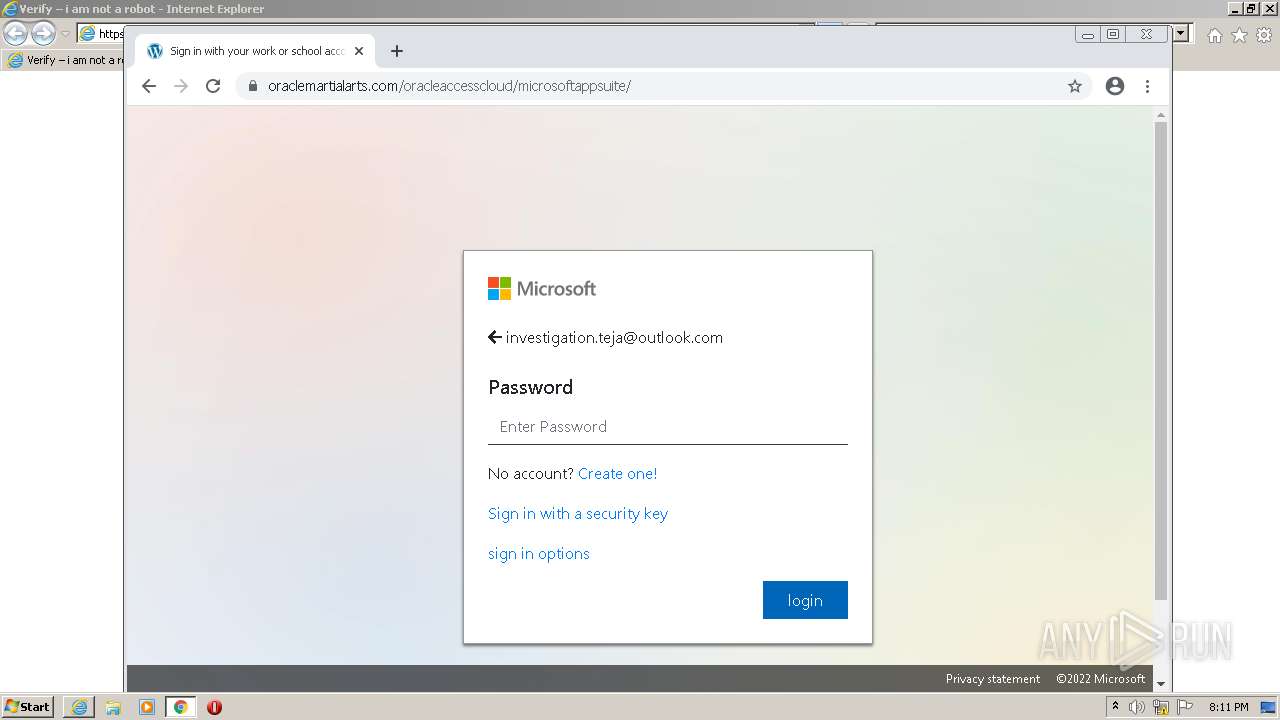
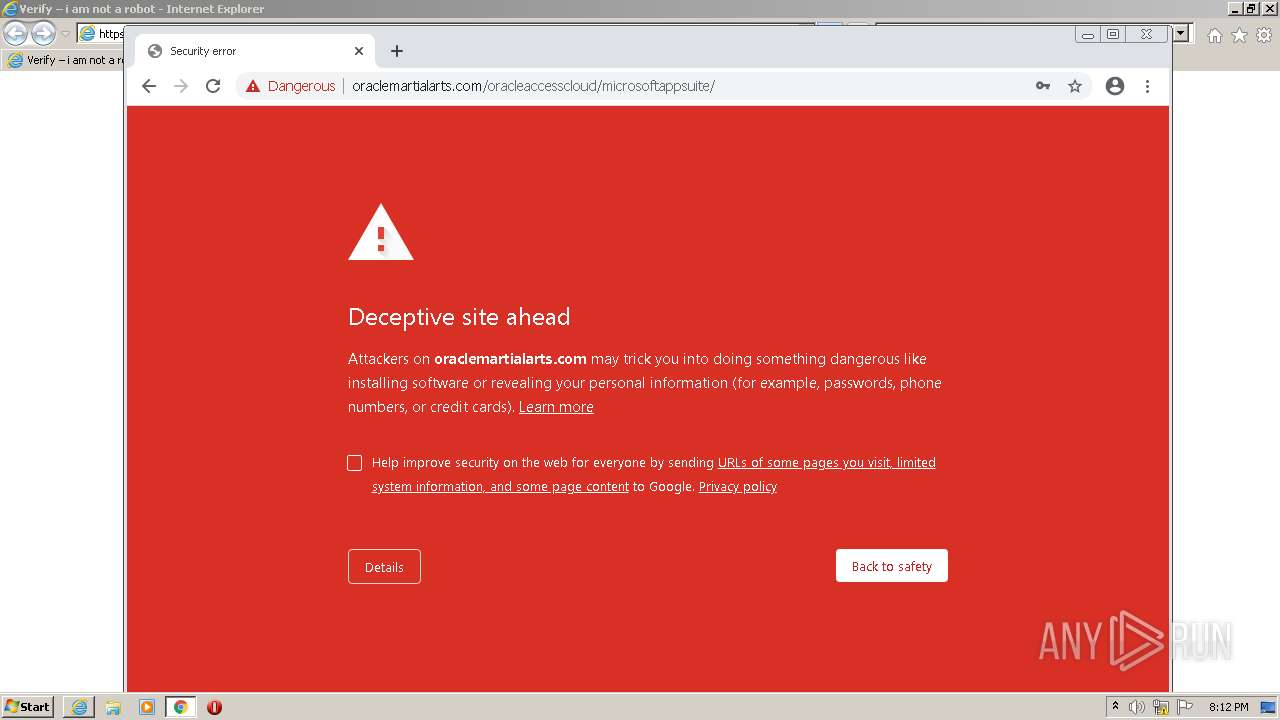
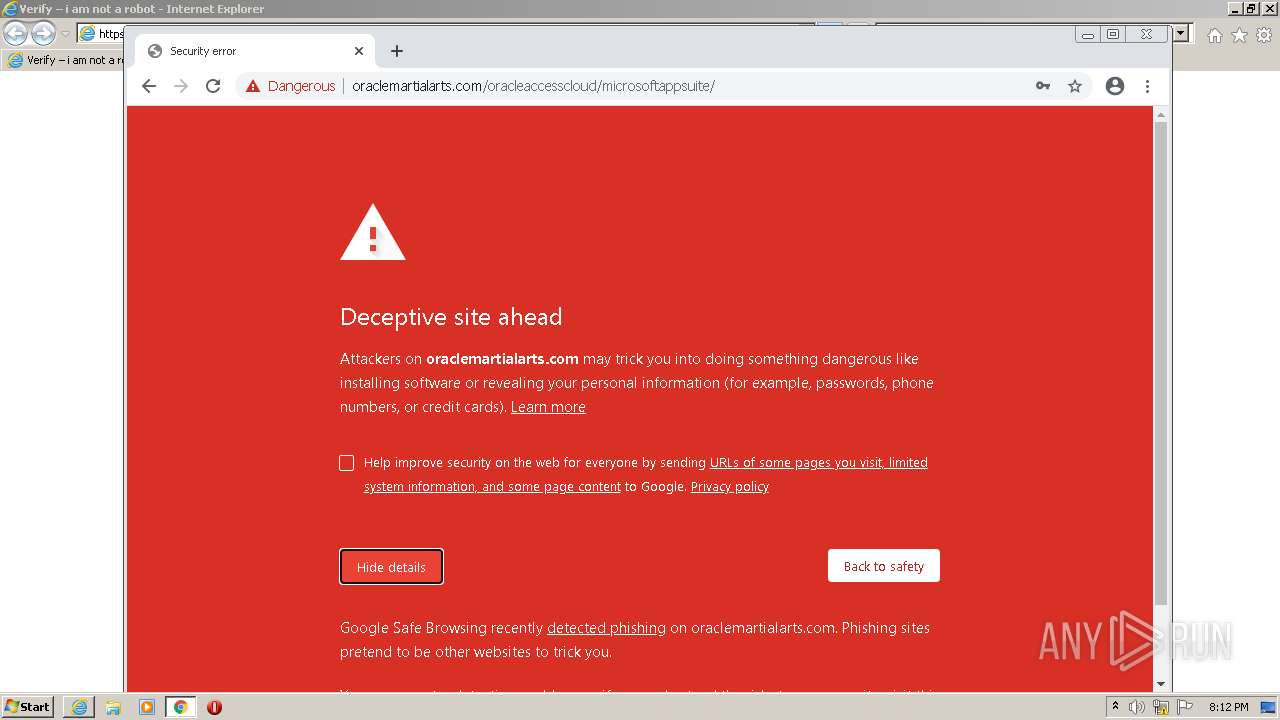
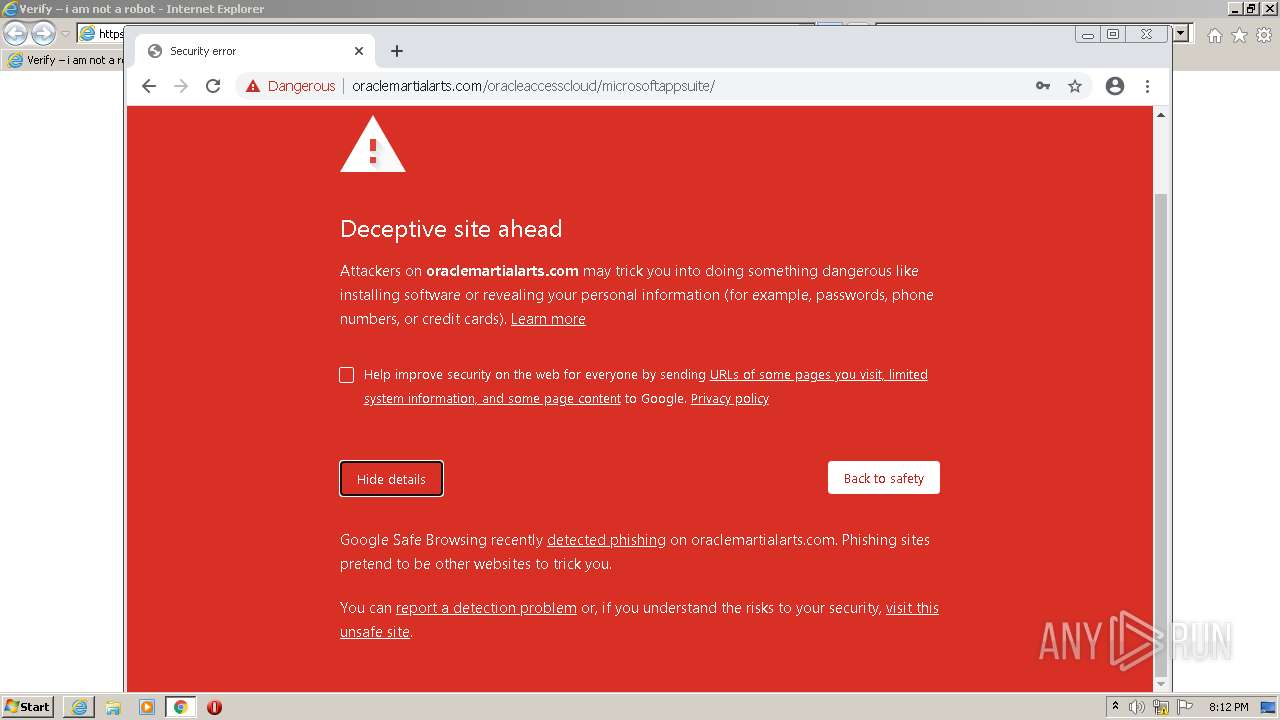
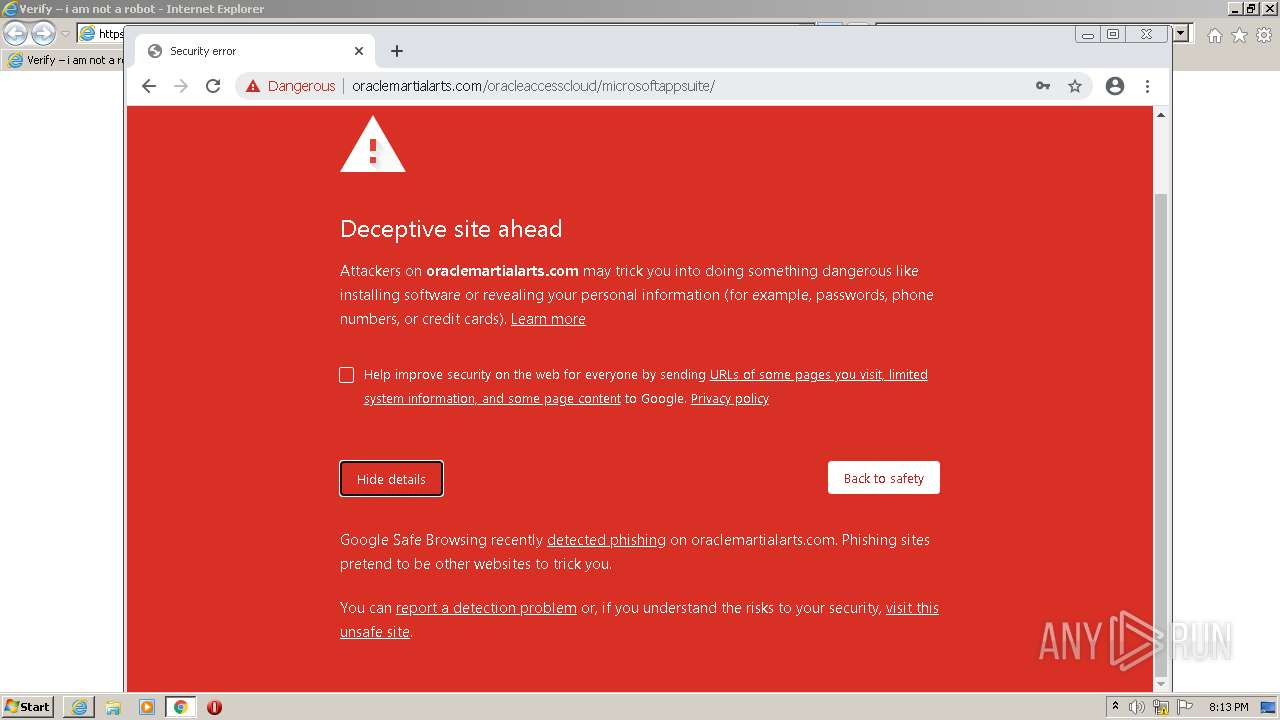
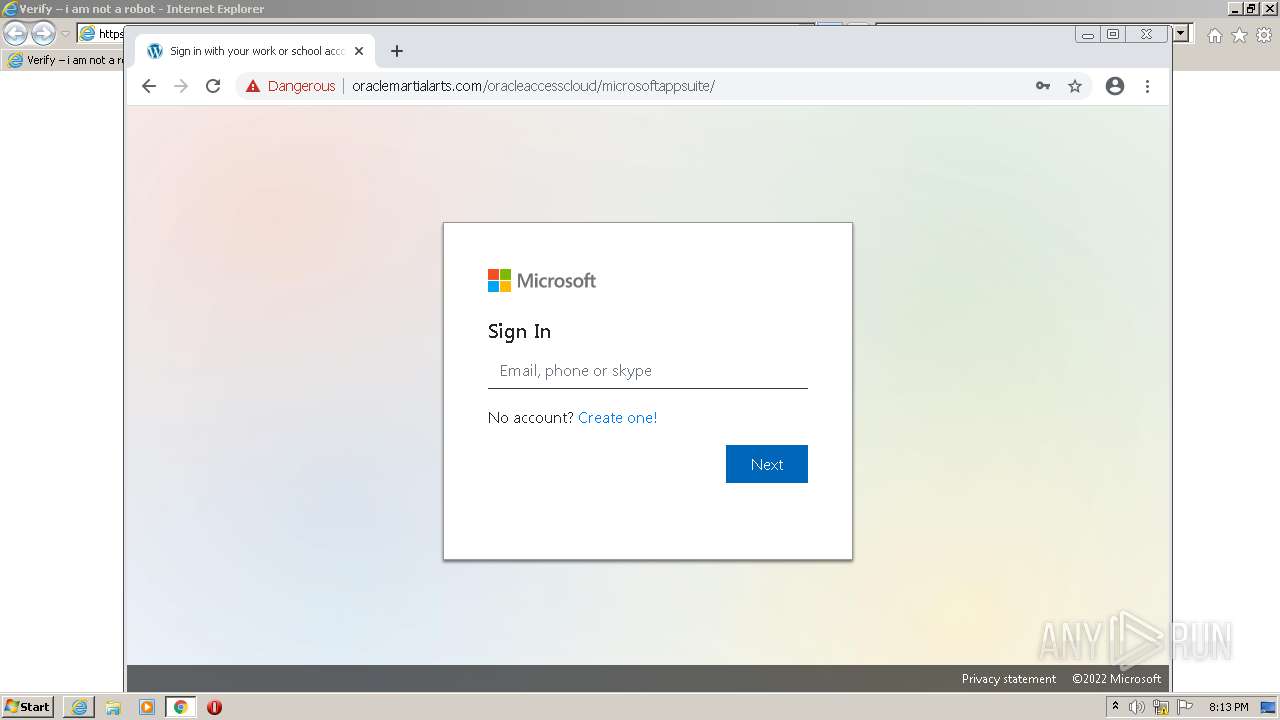
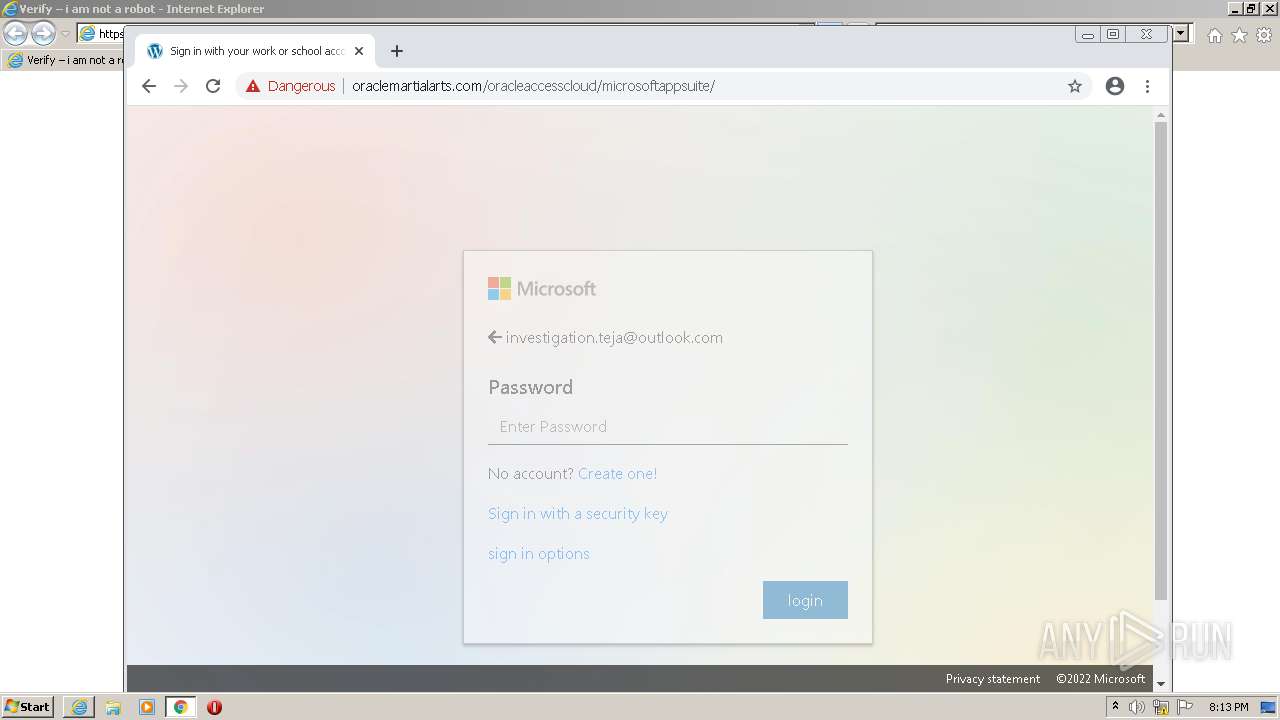
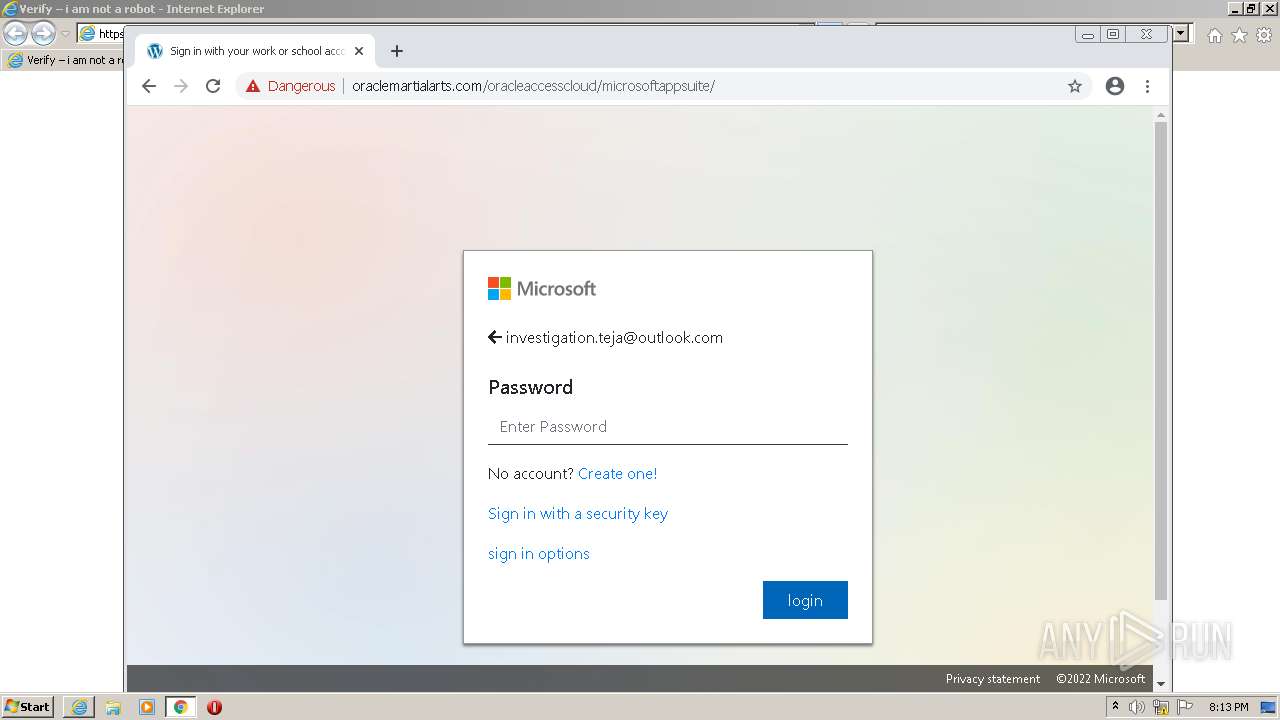
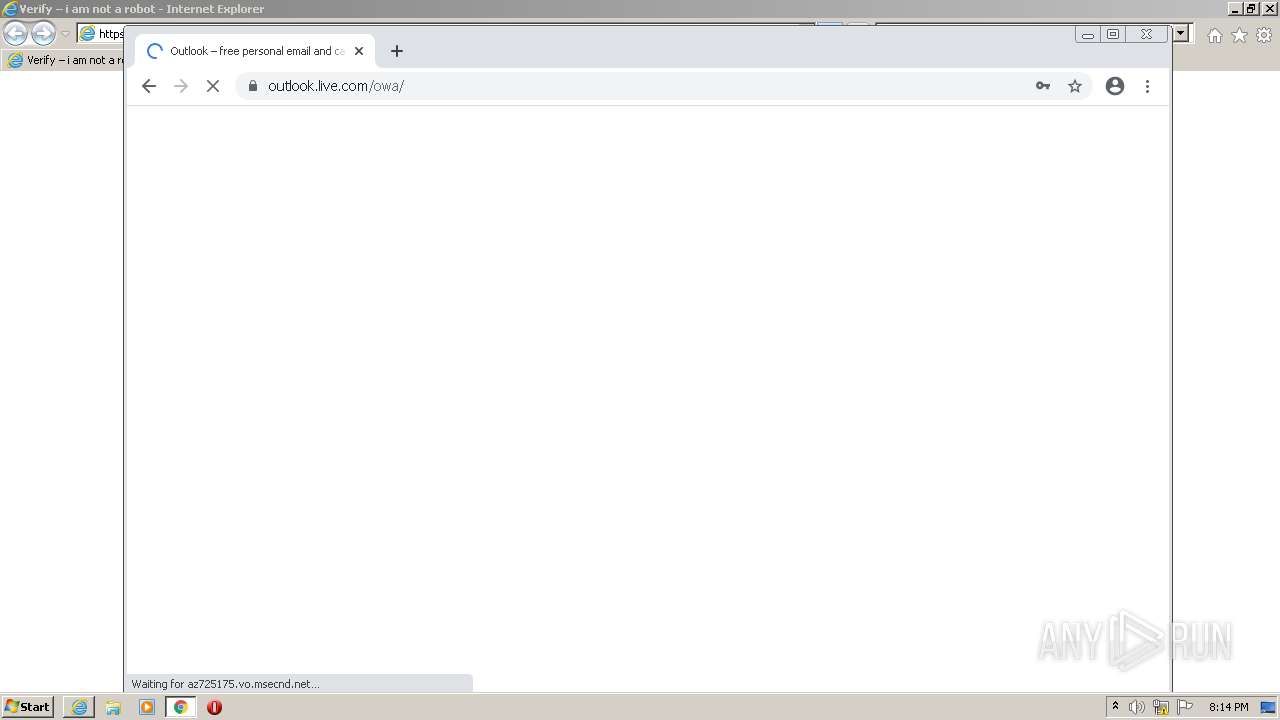
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2022, 19:09:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | C4FDF72B7F979BD5A9FBEE64EEF96FD3 |
| SHA1: | 0BE4CB03FE130FC8669A564976EB4ADF1B3BF35A |
| SHA256: | F9D17818DEE4181DB7855979F2D8C085D474B8D3C3D178702985CBB024B17D6D |
| SSDEEP: | 24:26HJCJzidY5D570mKjQgMXtzVWXQgMDU1ot1vU:OziA53yxM9VWAgMI1ons |
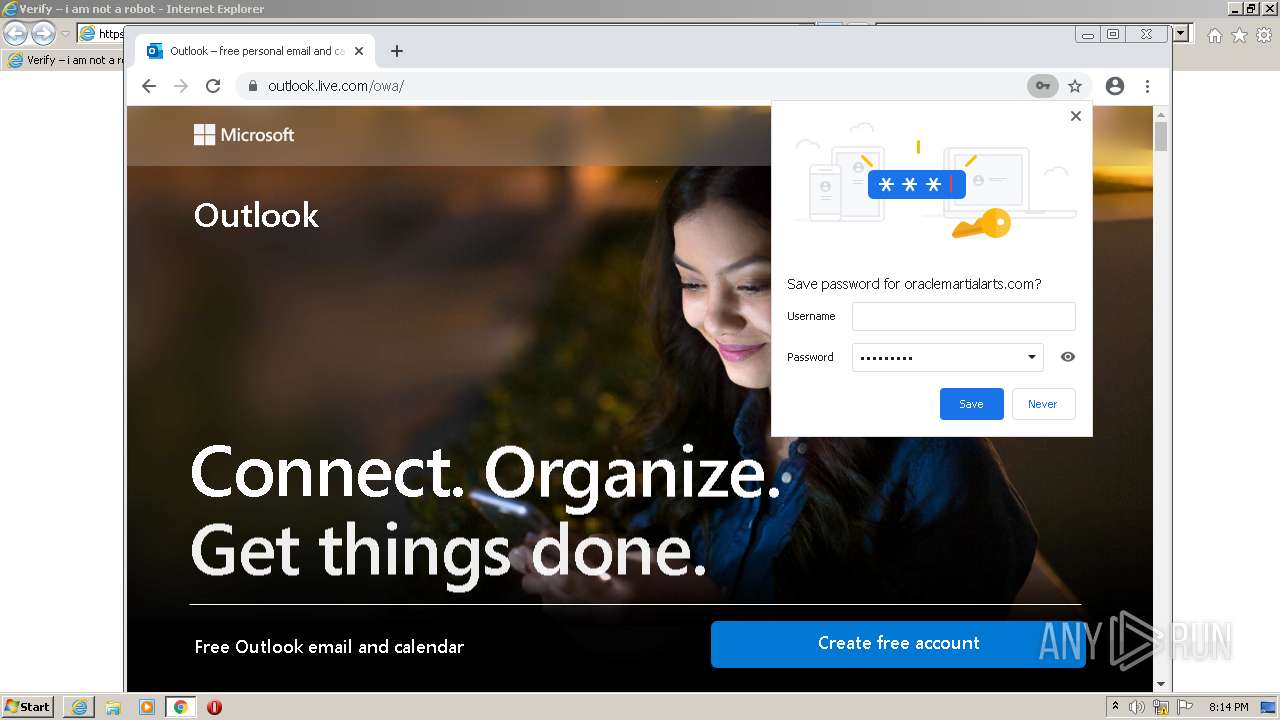
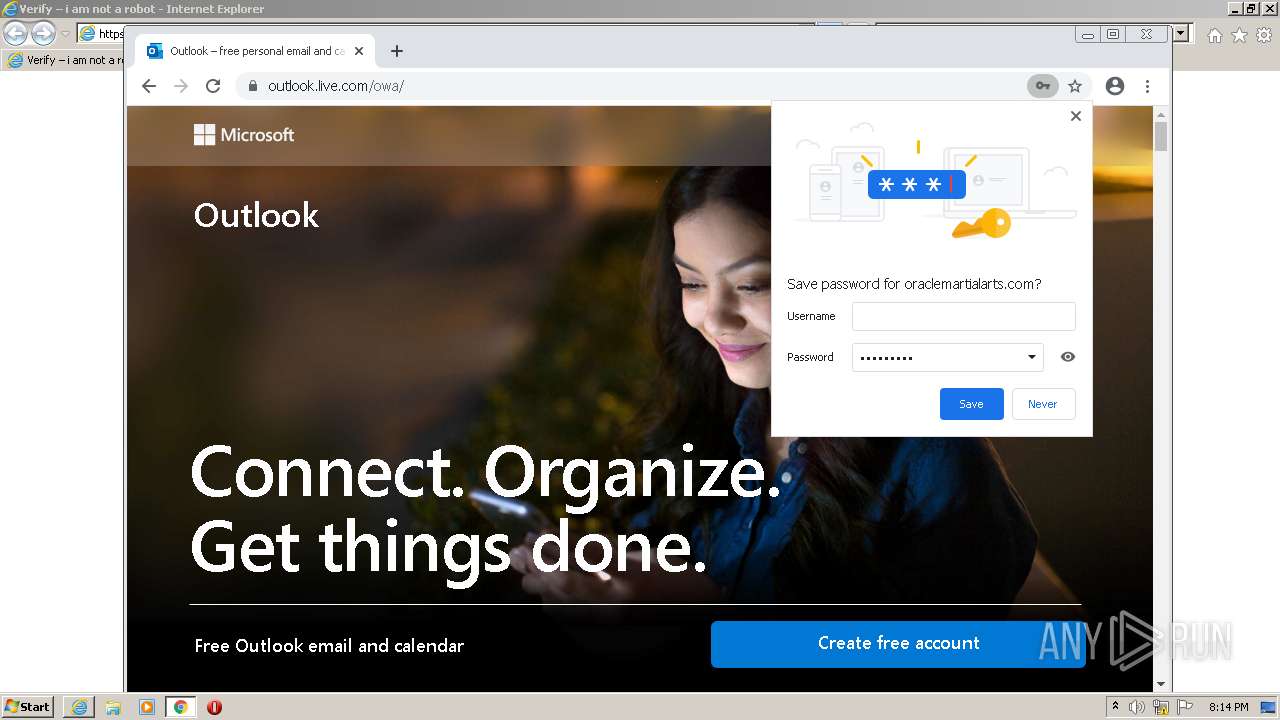
MALICIOUS
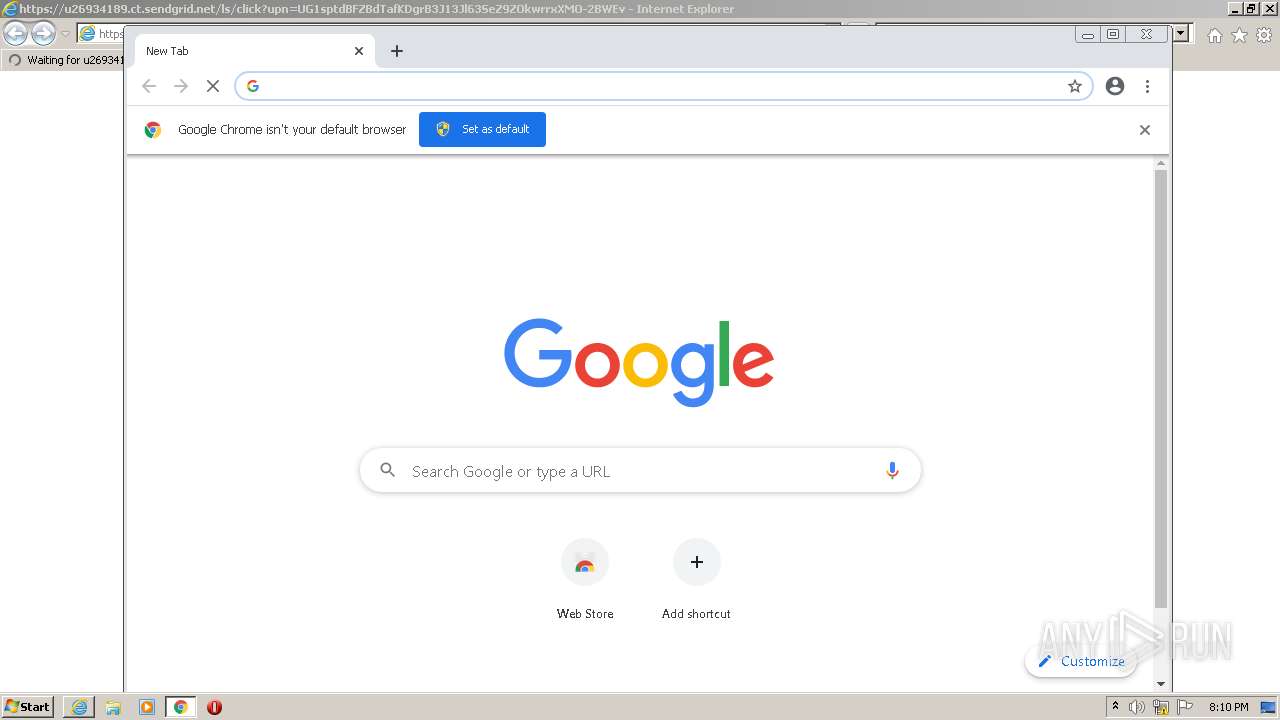
Drops executable file immediately after starts
- chrome.exe (PID: 2664)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3336)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2664)
Drops a file with a compile date too recent
- chrome.exe (PID: 2664)
INFO
Checks supported languages
- iexplore.exe (PID: 2532)
- iexplore.exe (PID: 3336)
- chrome.exe (PID: 2664)
- chrome.exe (PID: 3328)
- chrome.exe (PID: 3944)
- chrome.exe (PID: 2964)
- chrome.exe (PID: 1104)
- chrome.exe (PID: 1444)
- chrome.exe (PID: 3984)
- chrome.exe (PID: 824)
- chrome.exe (PID: 752)
- chrome.exe (PID: 2384)
- chrome.exe (PID: 3260)
- chrome.exe (PID: 2556)
- chrome.exe (PID: 3428)
- chrome.exe (PID: 3024)
- chrome.exe (PID: 3908)
- chrome.exe (PID: 2860)
- chrome.exe (PID: 2908)
- chrome.exe (PID: 2816)
- chrome.exe (PID: 988)
- chrome.exe (PID: 2744)
- chrome.exe (PID: 2268)
- chrome.exe (PID: 3176)
- chrome.exe (PID: 2136)
- chrome.exe (PID: 3260)
- chrome.exe (PID: 2584)
- chrome.exe (PID: 1940)
- chrome.exe (PID: 3224)
- chrome.exe (PID: 2556)
- chrome.exe (PID: 3096)
- chrome.exe (PID: 3304)
Application launched itself
- iexplore.exe (PID: 2532)
- chrome.exe (PID: 2664)
Reads the computer name
- iexplore.exe (PID: 3336)
- chrome.exe (PID: 2664)
- iexplore.exe (PID: 2532)
- chrome.exe (PID: 3328)
- chrome.exe (PID: 2964)
- chrome.exe (PID: 2384)
- chrome.exe (PID: 752)
- chrome.exe (PID: 2816)
- chrome.exe (PID: 2744)
- chrome.exe (PID: 2136)
- chrome.exe (PID: 1940)
Manual execution by user
- chrome.exe (PID: 2664)
Changes internet zones settings
- iexplore.exe (PID: 2532)
Reads the hosts file
- chrome.exe (PID: 2664)
- chrome.exe (PID: 3328)
Reads settings of System Certificates
- chrome.exe (PID: 3328)
- iexplore.exe (PID: 3336)
- iexplore.exe (PID: 2532)
Checks Windows Trust Settings
- iexplore.exe (PID: 2532)
- iexplore.exe (PID: 3336)
Reads internet explorer settings
- iexplore.exe (PID: 3336)
Reads the date of Windows installation
- chrome.exe (PID: 2744)
Changes settings of System certificates
- iexplore.exe (PID: 2532)
Creates files in the user directory
- iexplore.exe (PID: 2532)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2532)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
68
Monitored processes
32
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1124,6498083054526090497,7101670774798434757,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2612 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 824 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1124,6498083054526090497,7101670774798434757,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2272 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 988 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1124,6498083054526090497,7101670774798434757,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2344 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1124,6498083054526090497,7101670774798434757,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2240 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6eccd988,0x6eccd998,0x6eccd9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1124,6498083054526090497,7101670774798434757,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=964 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2136 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1124,6498083054526090497,7101670774798434757,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=964 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2268 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1124,6498083054526090497,7101670774798434757,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=536 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1124,6498083054526090497,7101670774798434757,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1112 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2532 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://u26934189.ct.sendgrid.net/ls/click?upn=UG1sptdBFZBdTafKDgrB3J13Jl63SeZ9ZOkwrrxXMO-2BWEvoCbUU7fInZOHfSapFjfc7k3Rz31hoJ7Vio8Wm7Pw-3D-3DIRyk_QzYfKuVeYTHRVjziq4uwJdnFyoggSW4hlimJdGWUGo9xOWlX-2BWR2aaAghpuAGStbUZRAU3uNIj0jizkY8zEyy2gAANp-2FYAM-2FtOyFzff1i3-2BtBuT4ba7IWbZrXbiLMHLtodS6dmsEO3GP0NmNPyHy6w9o-2FqDoJDkrJofbLgvLr8cMXKnTYeDT-2FeT2-2FiewAUIeiFbw6HhbJ3GL2715LMAYpdzh-2BGnT89jn7Z-2FRkW-2Fxn4S29ThcD1FEvCZSSTI2NiqvnWb5qdsO3-2BOEKSmHzirH2-2FukvxGERDcGr5tPjZu63K5UEz4RUY2hQ-2BEmJNaUcrZuS6nUqJGoCQ-2F-2B7UnLRXHO64AWkN4yunMlJqqyqVgoC2AEzl4ZW-2BwFQ9BTUbNH4WrA8AChHqqC0BpsiDB2GEeM8LGOz6aAczi37eWN3ldGrQre4gi9wlceNQI3DLy3yR-2F1YrafGfQUdL0FAwCS2bvLxHHKV5jtBWhV8a3XMIPDFK9KsmiJ3RPChUTNlpiCg1HlVjBOnIq5sB1Zk6-2FEN0iLsjm1XdvzrlTneV3HAo05t-2BG2kxNXUojWUB6n0Pgv7gwbdKQxMSnroWLpChy0QXCjZ0DxDK-2FmfYIv3sGyIdVLv0W6b2VKL2SoGSI-2FweHs78nuALv8OZ2tkcyCPeAwHBjoYNiUp-2F3lxvabGRj1nUOApkzeLWDiaodbguq05AiwE8us7fBtyEw-2FTa-2Fwd9UsHOaI0nkQv1f2LiHFDK2QGTgnKDKDHRmMv-2Fh1Ko9NtFsyHbltVDGWovsk-2FX4nPv5802iNFhQIUJVFCGVj2zEcoMkMy9FIZWNApu6fhtlmXYobgpBxL9KTlfqocm5qHiKrScShYVSnNN5cbREXzVD6kUbDJLw-3D" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
25 552
Read events
25 284
Write events
258
Delete events
10
Modification events
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 846068560 | |||
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30960765 | |||
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30960765 | |||
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2532) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
226
Text files
217
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6287E791-A68.pma | — | |
MD5:— | SHA256:— | |||
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\2a4e1ec1-b3e7-45f0-b553-40f2ac0bbbae.tmp | text | |
MD5:— | SHA256:— | |||
| 3328 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\index | binary | |
MD5:— | SHA256:— | |||
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 3328 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\data_0 | vxd | |
MD5:CF89D16BB9107C631DAABF0C0EE58EFB | SHA256:D6A5FE39CD672781B256E0E3102F7022635F1D4BB7CFCC90A80FFFE4D0F3877E | |||
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF10758f.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 2664 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences~RF1077d2.TMP | text | |
MD5:8304B8F42465198890090F52D3F80A4C | SHA256:80C32AC2585E7E81200104B1630F19560A156C4ABF51B5888B0FBF07323FAB34 | |||
| 3328 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\data_1 | vxd | |
MD5:259E7ED5FB3C6C90533B963DA5B2FC1B | SHA256:35BB2F189C643DCF52ECF037603D104035ECDC490BF059B7736E58EF7D821A09 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
130
DNS requests
59
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODJiQUFYYVJaZ0k5di1hUFlXS1prX2xDZw/1.0.0.13_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | — | — | whitelisted |
3336 | iexplore.exe | GET | 200 | 192.124.249.41:80 | http://ocsp.godaddy.com//MEowSDBGMEQwQjAJBgUrDgMCGgUABBS2CA1fbGt26xPkOKX4ZguoUjM0TgQUQMK9J47MNIMwojPX%2B2yz8LQsgM4CCQCbtonfHJ3EDA%3D%3D | US | der | 1.74 Kb | whitelisted |
3336 | iexplore.exe | GET | 200 | 192.124.249.41:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
2532 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
2532 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3336 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEG3aTvFLTYzNCmxS2fUJutw%3D | US | der | 471 b | whitelisted |
3336 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEFsL8ccV6MRJElibH7RYju4%3D | US | der | 471 b | whitelisted |
3336 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3336 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3336 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2532 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3328 | chrome.exe | 142.250.185.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
3328 | chrome.exe | 142.251.37.100:443 | www.google.com | Google Inc. | US | malicious |
3328 | chrome.exe | 142.250.185.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3328 | chrome.exe | 142.250.186.77:443 | accounts.google.com | Google Inc. | US | suspicious |
3328 | chrome.exe | 172.217.23.97:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
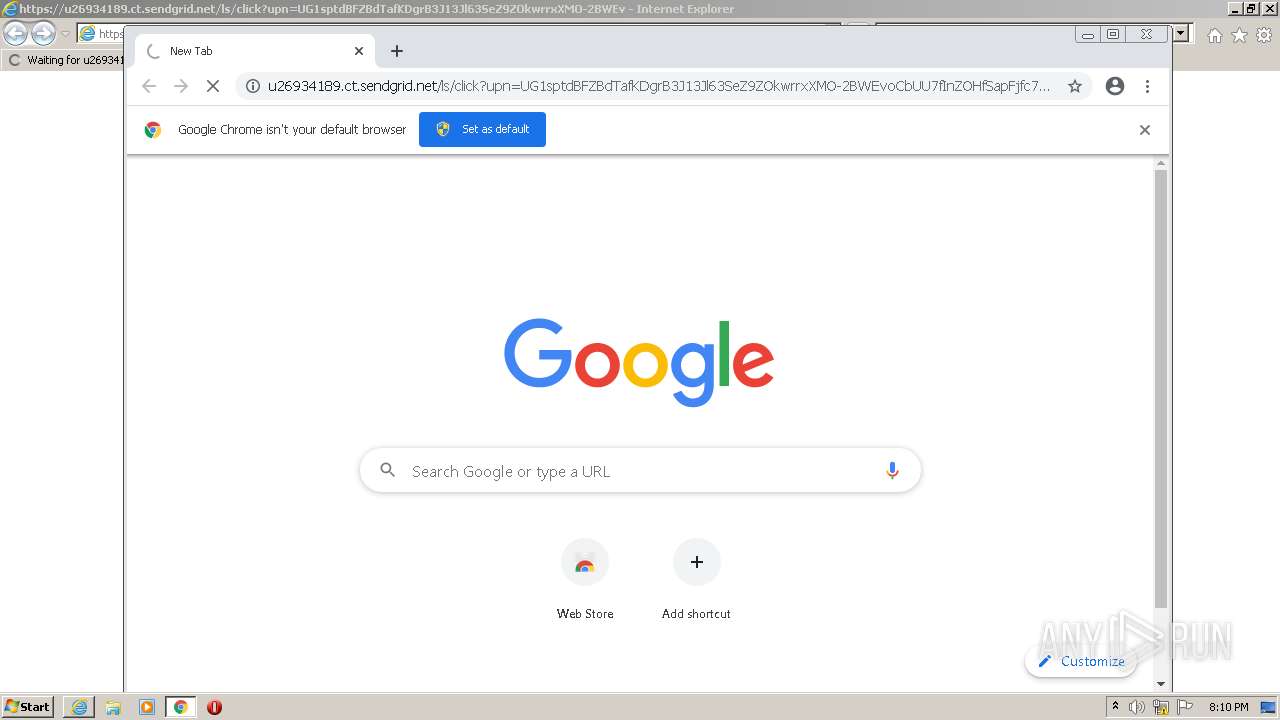
3328 | chrome.exe | 167.89.118.35:443 | u26934189.ct.sendgrid.net | SendGrid, Inc. | US | suspicious |
3336 | iexplore.exe | 167.89.123.16:443 | u26934189.ct.sendgrid.net | SendGrid, Inc. | US | malicious |
3328 | chrome.exe | 142.250.74.195:443 | update.googleapis.com | Google Inc. | US | whitelisted |
3328 | chrome.exe | 142.250.74.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
u26934189.ct.sendgrid.net |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
www.google.com |
| malicious |
clients2.googleusercontent.com |
| whitelisted |
oracleaccess.elementor.cloud |
| suspicious |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |