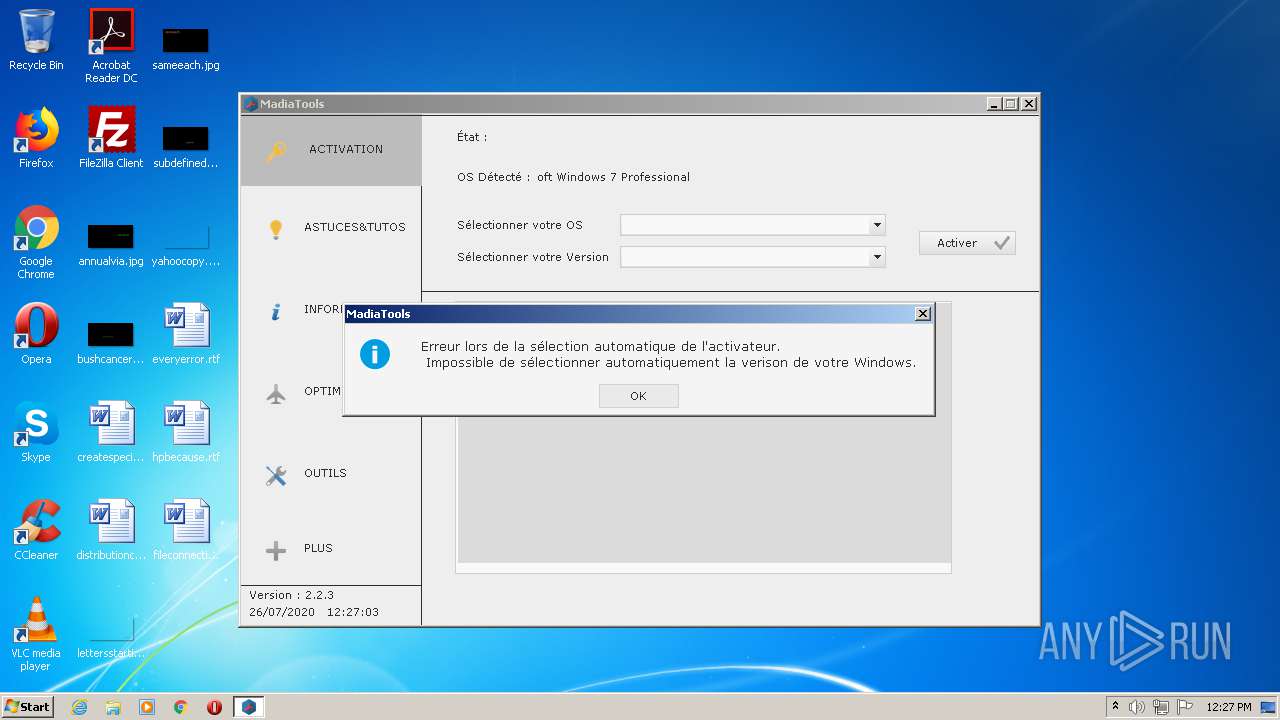
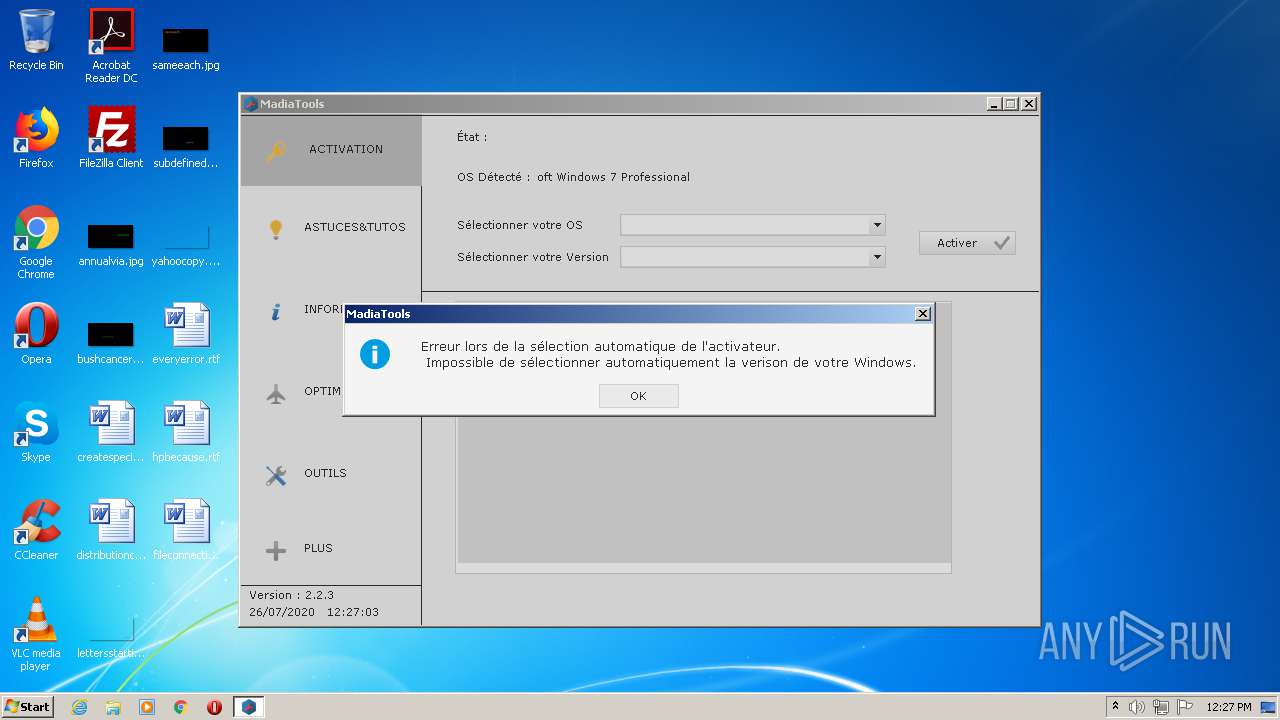
| File name: | MadiaTools 2.2.3.exe |
| Full analysis: | https://app.any.run/tasks/8ca55bee-8082-4f02-8a06-d70e4c9bb9ad |
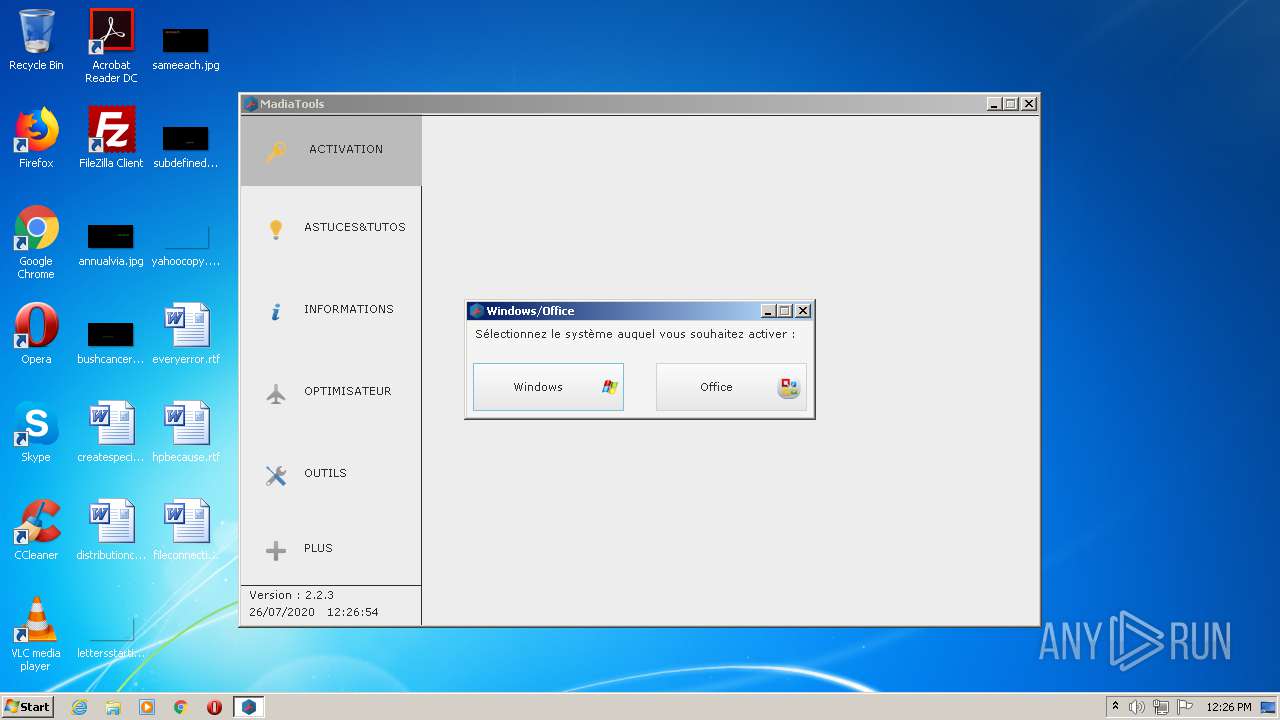
| Verdict: | Malicious activity |
| Analysis date: | July 26, 2020, 11:25:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 73C4966E013D1527E0E89ECEAA8C34E8 |
| SHA1: | B28D8F125D0618A60D06D094F92145F155677144 |
| SHA256: | F9CF5C1156F8CC666EB73C24418AA4501B101AEE1A7F1BA8CF75836C290E89D8 |
| SSDEEP: | 98304:m32s1Brfvon3+O06PYwE/2ImoPfTukCKCSj:tsXon3M6PYwQ2ImoqkCKC |
MALICIOUS
Loads dropped or rewritten executable
- MadiaTools 2.2.3.exe (PID: 2724)
SUSPICIOUS
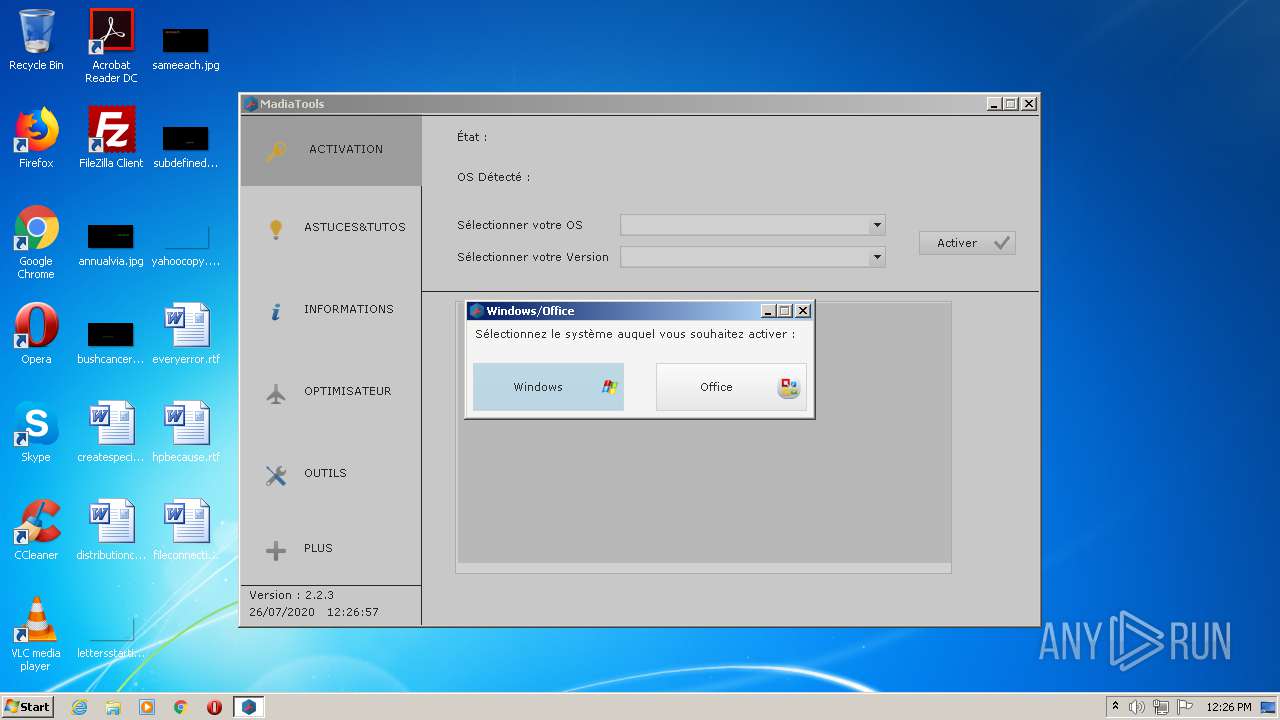
Uses SYSTEMINFO.EXE to read environment
- MadiaTools 2.2.3.exe (PID: 2724)
Reads Internet Cache Settings
- MadiaTools 2.2.3.exe (PID: 2724)
Executes scripts
- MadiaTools 2.2.3.exe (PID: 2724)
Application launched itself
- InstallFramework.exe (PID: 2560)
Executable content was dropped or overwritten
- InstallFramework.exe (PID: 3676)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:09:10 12:13:56+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 194560 |
| InitializedDataSize: | 3843072 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1879e |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.2.65534.65522 |
| ProductVersionNumber: | 24.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | French |
| CharacterSet: | Unicode |
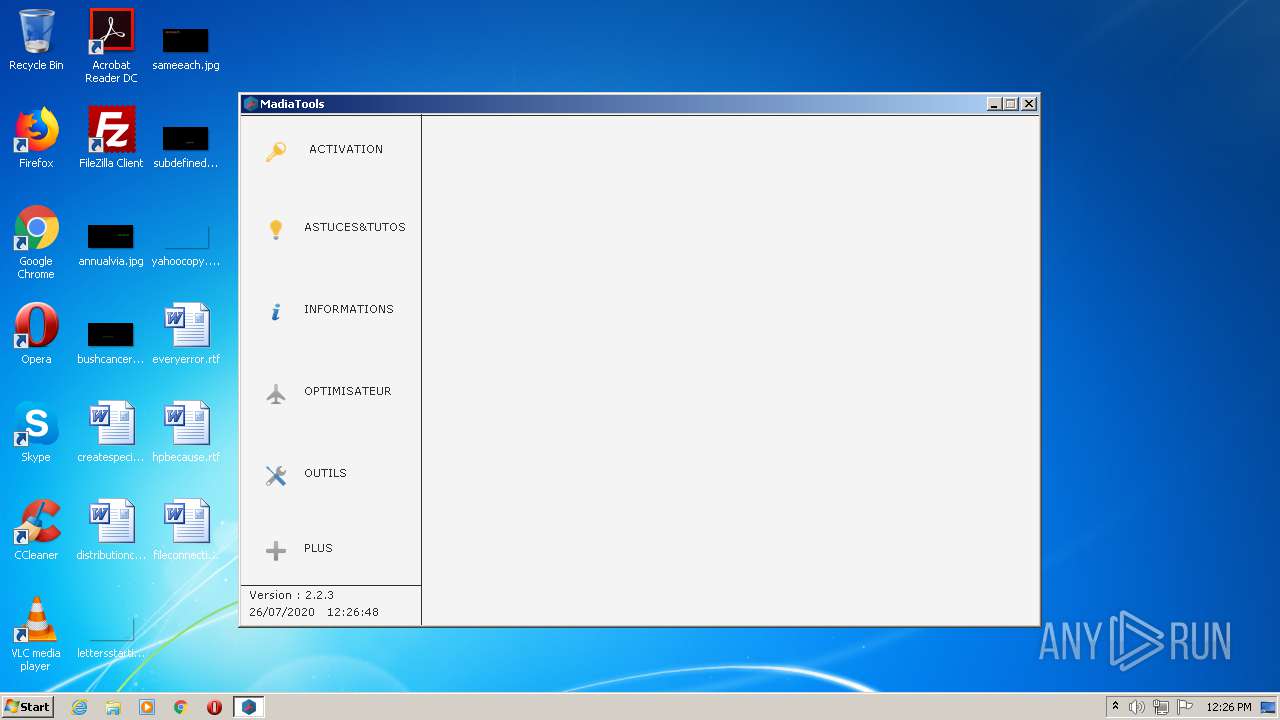
| CompanyName: | Madia972 |
| FileDescription: | - |
| FileVersion: | 2.2.3 |
| Version: | 2.2.3 |
| LegalCopyright: | Copyright © Madia972 @2020 |
| WDVersion: | 24 |
| ProductName: | MadiaTools 2.2.3 |
| ProductVersion: | 2.2.3 |
Total processes
50
Monitored processes
7
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | "C:\Users\admin\AppData\Local\Temp\MadiaTools 2.2.3.exe" | C:\Users\admin\AppData\Local\Temp\MadiaTools 2.2.3.exe | — | explorer.exe | |||||||||||
User: admin Company: Madia972 Integrity Level: MEDIUM Exit code: 0 Version: 2.2.3 | |||||||||||||||
| 928 | systeminfo | C:\Windows\system32\systeminfo.exe | — | MadiaTools 2.2.3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Displays system information Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1616 | cscript C:\Windows\system32\slmgr.vbs /dli | C:\Windows\system32\cscript.exe | — | MadiaTools 2.2.3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 | |||||||||||||||
| 2560 | "C:\Users\admin\AppData\Local\Temp\InstallFramework.exe" /REP="C:\Users\admin\AppData\Local\Temp\" /SILENT | C:\Users\admin\AppData\Local\Temp\InstallFramework.exe | — | MadiaTools 2.2.3.exe | |||||||||||
User: admin Company: PC SOFT Integrity Level: HIGH Description: WDAutoEx.EXE (Executable auto-extractible) - Win32 Exit code: 0 Version: 22.0.2.0 Modules
| |||||||||||||||
| 2724 | "C:\Users\admin\AppData\Local\Temp\MadiaTools 2.2.3.exe" | C:\Users\admin\AppData\Local\Temp\MadiaTools 2.2.3.exe | explorer.exe | ||||||||||||
User: admin Company: Madia972 Integrity Level: HIGH Exit code: 0 Version: 2.2.3 Modules
| |||||||||||||||
| 2832 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\MadiaTools\Temp\OS.vbs" | C:\Windows\System32\WScript.exe | — | MadiaTools 2.2.3.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3676 | "C:\Users\admin\AppData\Local\Temp\InstallFramework.exe" /REP="C:\Users\admin\AppData\Local\Temp\" /SILENT /RELANCE | C:\Users\admin\AppData\Local\Temp\InstallFramework.exe | InstallFramework.exe | ||||||||||||
User: admin Company: PC SOFT Integrity Level: HIGH Description: WDAutoEx.EXE (Executable auto-extractible) - Win32 Exit code: 0 Version: 22.0.2.0 Modules
| |||||||||||||||
Total events
747
Read events
730
Write events
17
Delete events
0
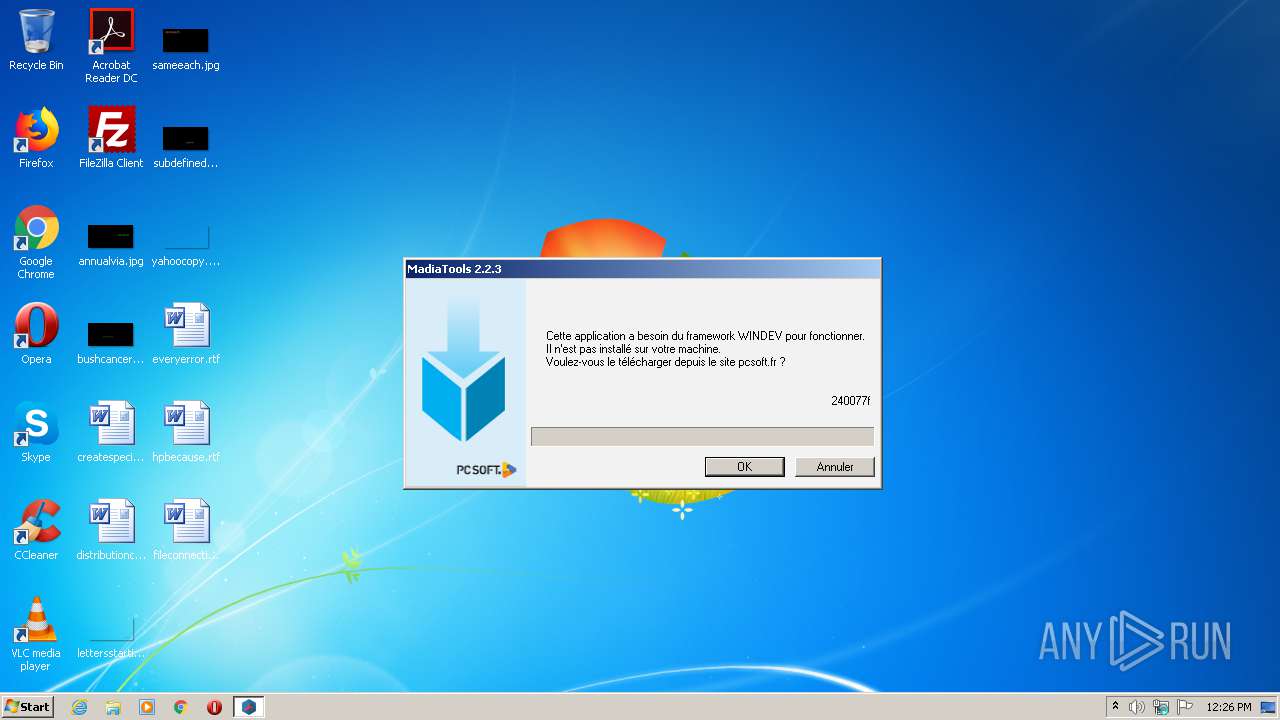
Modification events
| (PID) Process: | (2724) MadiaTools 2.2.3.exe | Key: | HKEY_CURRENT_USER\Software\PC SOFT\WINDEV\24.0\APPLI\MadiaTools 2.2.3 |
| Operation: | write | Name: | LAST_FRAMEWORK |
Value: 240077f | |||
| (PID) Process: | (2724) MadiaTools 2.2.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2724) MadiaTools 2.2.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2724) MadiaTools 2.2.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2724) MadiaTools 2.2.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2724) MadiaTools 2.2.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2560) InstallFramework.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2560) InstallFramework.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2724) MadiaTools 2.2.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2724) MadiaTools 2.2.3.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
51
Suspicious files
1
Text files
2
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2724 | MadiaTools 2.2.3.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\InstallFramework_240077f[1].exe | — | |
MD5:— | SHA256:— | |||
| 2724 | MadiaTools 2.2.3.exe | C:\Users\admin\AppData\Local\Temp\InstallFramework.exe | — | |
MD5:— | SHA256:— | |||
| 3676 | InstallFramework.exe | C:\Users\admin\AppData\Local\Temp\wd240awws.dll | executable | |
MD5:2E483998FABE1D0A94AC6971A2C9B85B | SHA256:96A727BB1A4BB6E164EE4B0BFD7661DEB42BAA904FC73F0FAFA1F007A8AF12C3 | |||
| 3676 | InstallFramework.exe | C:\Users\admin\AppData\Local\Temp\wd240com.dll | executable | |
MD5:BDC244D6D6E1ED864D8460F0A0B7D67E | SHA256:2AA844C3BD5B83A391ADED35C82ACC9A8DCECA239EAE6EC8487B3FFE299742ED | |||
| 3676 | InstallFramework.exe | C:\Users\admin\AppData\Local\Temp\wd240action.dll | executable | |
MD5:964CE598969E9C6C919BEC4E6CF1229D | SHA256:336B378F51E0930FEEE48F781E8BFB073B26EB8A66935F04845BC73CA1C0CA89 | |||
| 3676 | InstallFramework.exe | C:\Users\admin\AppData\Local\Temp\wd240big.dll | executable | |
MD5:DAFA4E78C35797D7AFDCB12F2A7CF4B4 | SHA256:E342908AD84FCD4885468B290A5AE680DA0690A4813254F9487F89E76C0AB435 | |||
| 3676 | InstallFramework.exe | C:\Users\admin\AppData\Local\Temp\wd240barc.dll | executable | |
MD5:3D08C1D82B7990AAC874BF882D6EEDA5 | SHA256:BF934B42EA79012A16D7FAEACEBFD1461D48A9AECC6AD80139987D25E8BCB028 | |||
| 3676 | InstallFramework.exe | C:\Users\admin\AppData\Local\Temp\wd240hf.dll | executable | |
MD5:9015DA80E17790A132E5820E14566C40 | SHA256:CDB4FD53703A21511F8A2E2C85B012A58D36660C2B345A274B6DDB891DEEA8C0 | |||
| 3676 | InstallFramework.exe | C:\Users\admin\AppData\Local\Temp\wd240ijv.dll | executable | |
MD5:EBA57EE9F8E811A08F96477F687C6257 | SHA256:F223503609CD8A31549932D1578ACB500170F4858ED671B8C871B7E2BB3D955D | |||
| 3676 | InstallFramework.exe | C:\Users\admin\AppData\Local\Temp\wd240fc.dll | executable | |
MD5:4FBE197E5BA4ECFB09171714B2D0EDB1 | SHA256:6F67A929FA41E88E0774D5BCDFC52455CF35C06F9AC2C84A7DDF60B803569D9D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
2
Threats
3
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2724 | MadiaTools 2.2.3.exe | 149.202.161.200:21 | framework.pcsoft.fr | OVH SAS | FR | suspicious |
2724 | MadiaTools 2.2.3.exe | 149.202.161.200:11877 | framework.pcsoft.fr | OVH SAS | FR | suspicious |
2724 | MadiaTools 2.2.3.exe | 149.202.161.200:10913 | framework.pcsoft.fr | OVH SAS | FR | suspicious |
2724 | MadiaTools 2.2.3.exe | 79.82.239.182:2000 | Madia972.ddns.net | SFR | FR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
framework.pcsoft.fr |
| suspicious |
Madia972.ddns.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2724 | MadiaTools 2.2.3.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2724 | MadiaTools 2.2.3.exe | Potential Corporate Privacy Violation | ET INFO .exe File requested over FTP |
1052 | svchost.exe | Potentially Bad Traffic | ET POLICY DNS Query to DynDNS Domain *.ddns .net |