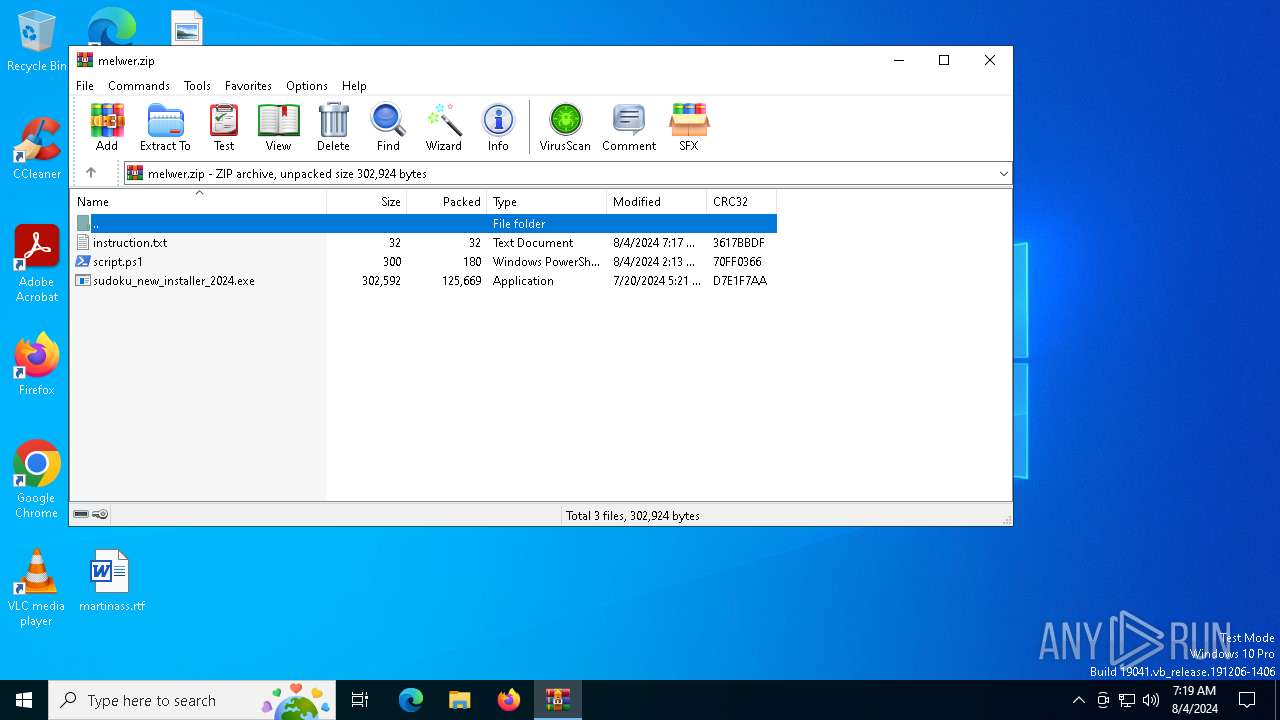
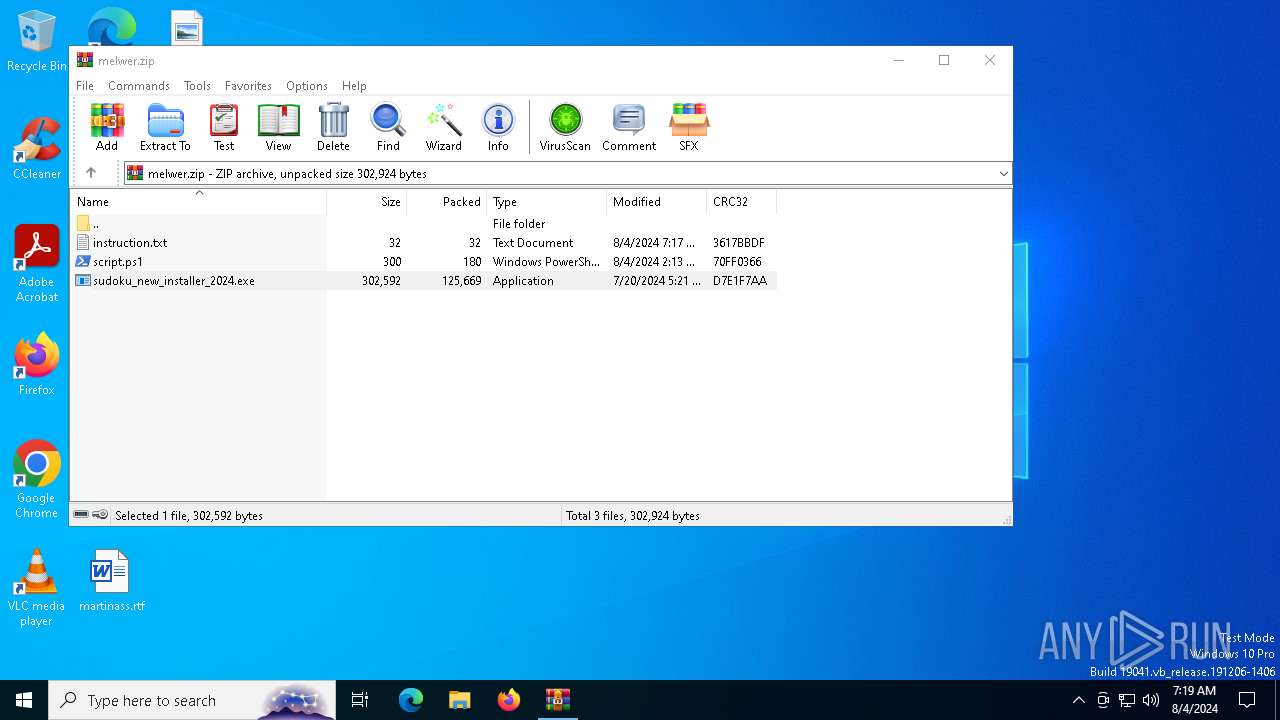
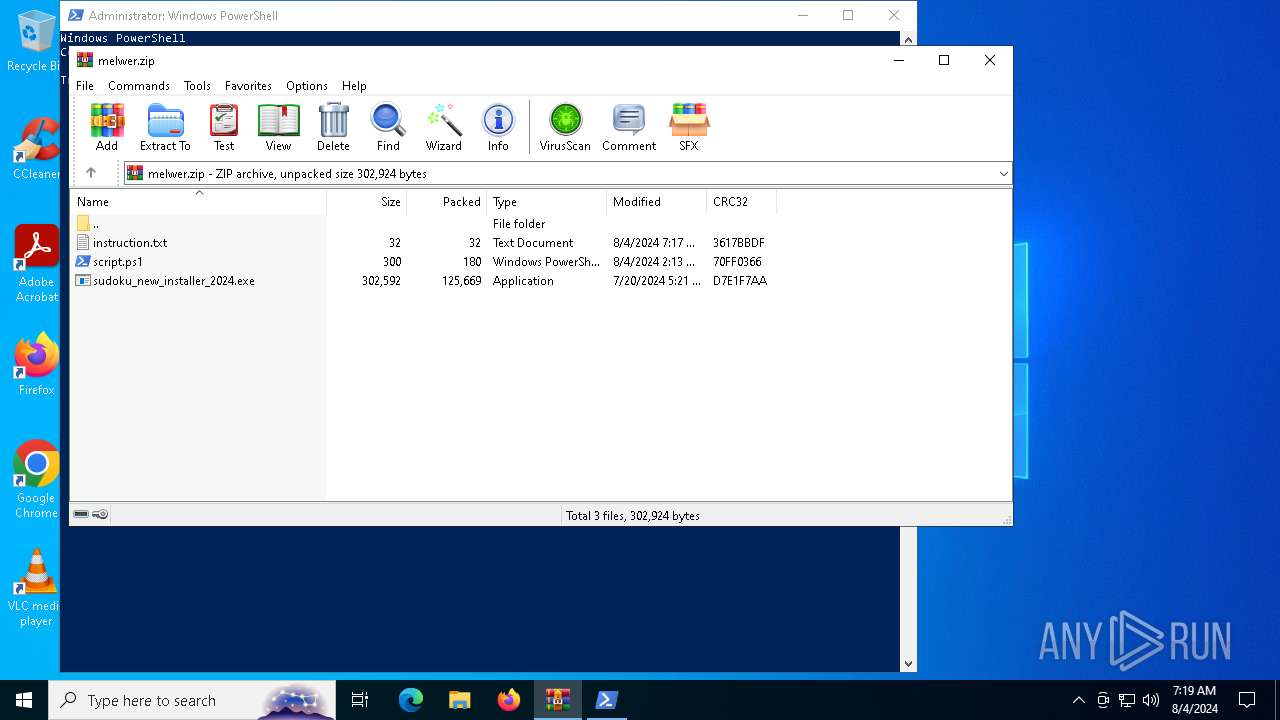
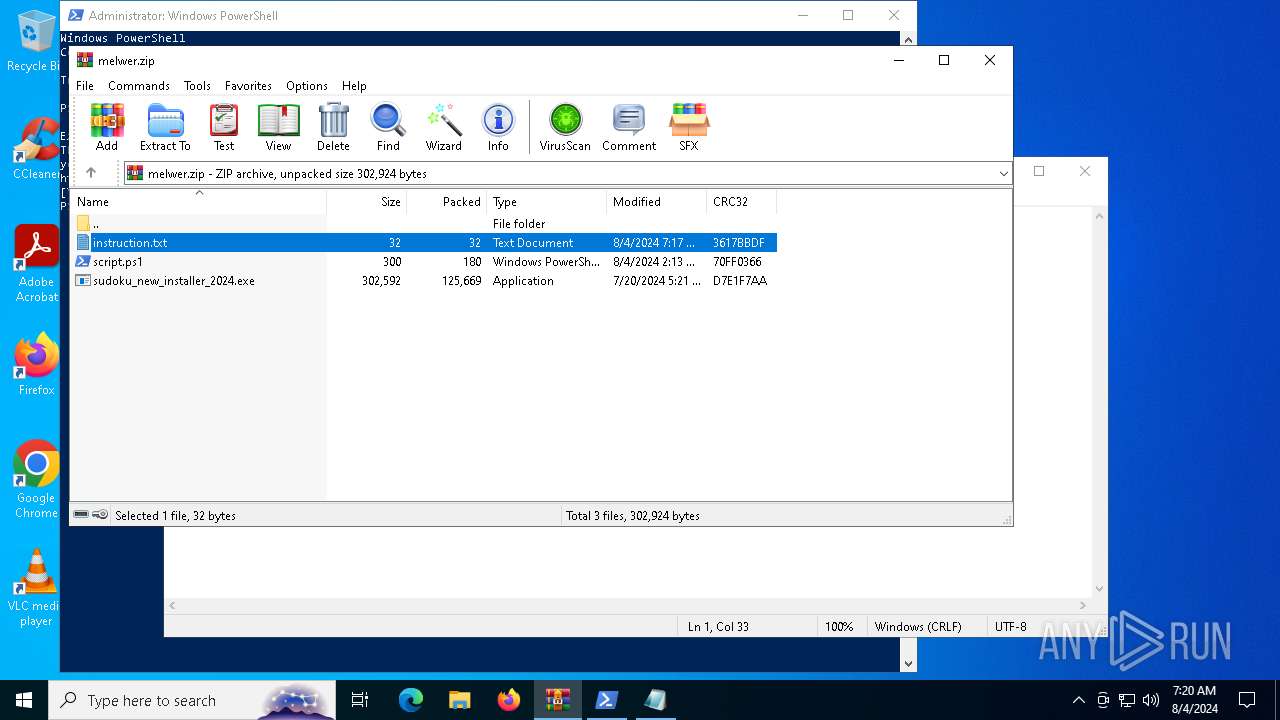
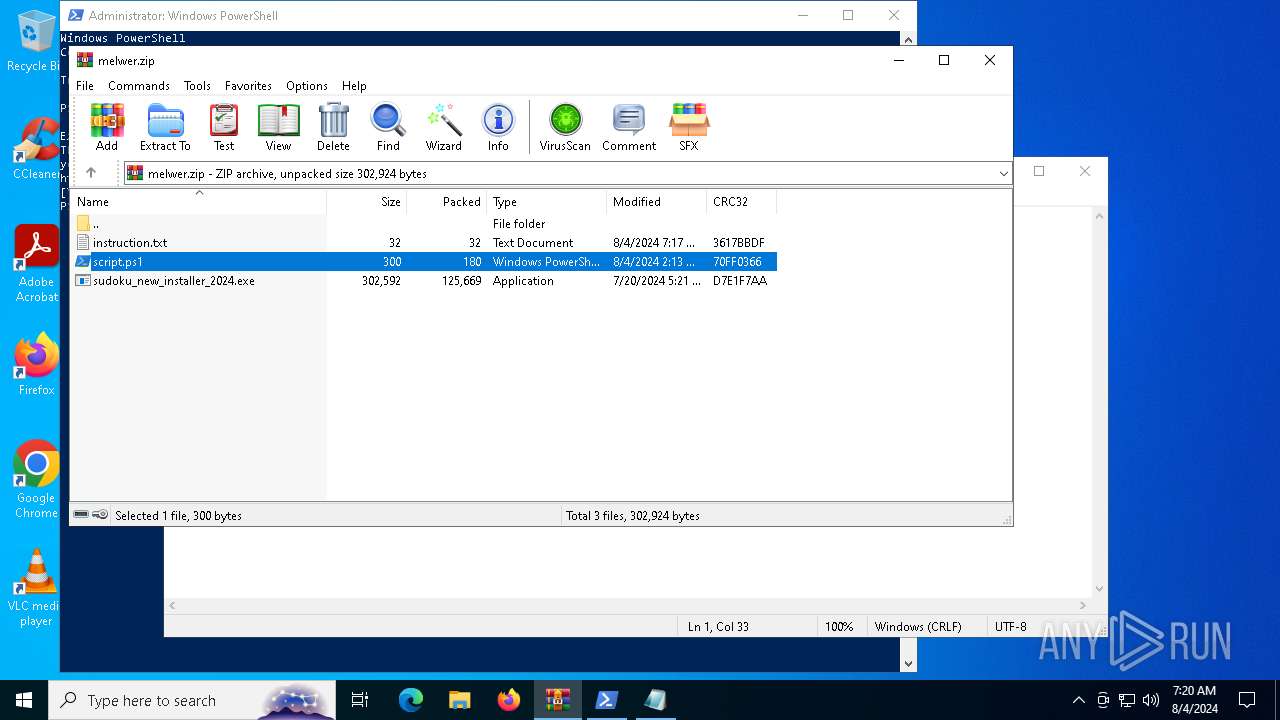
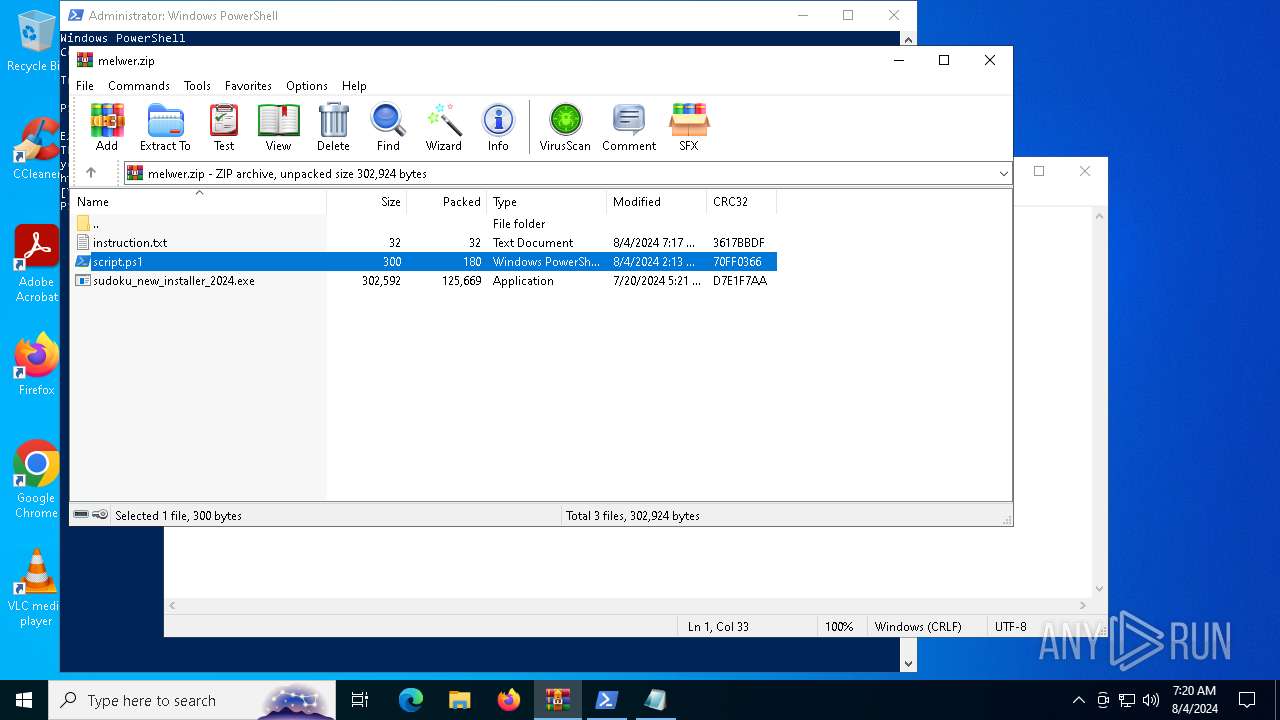
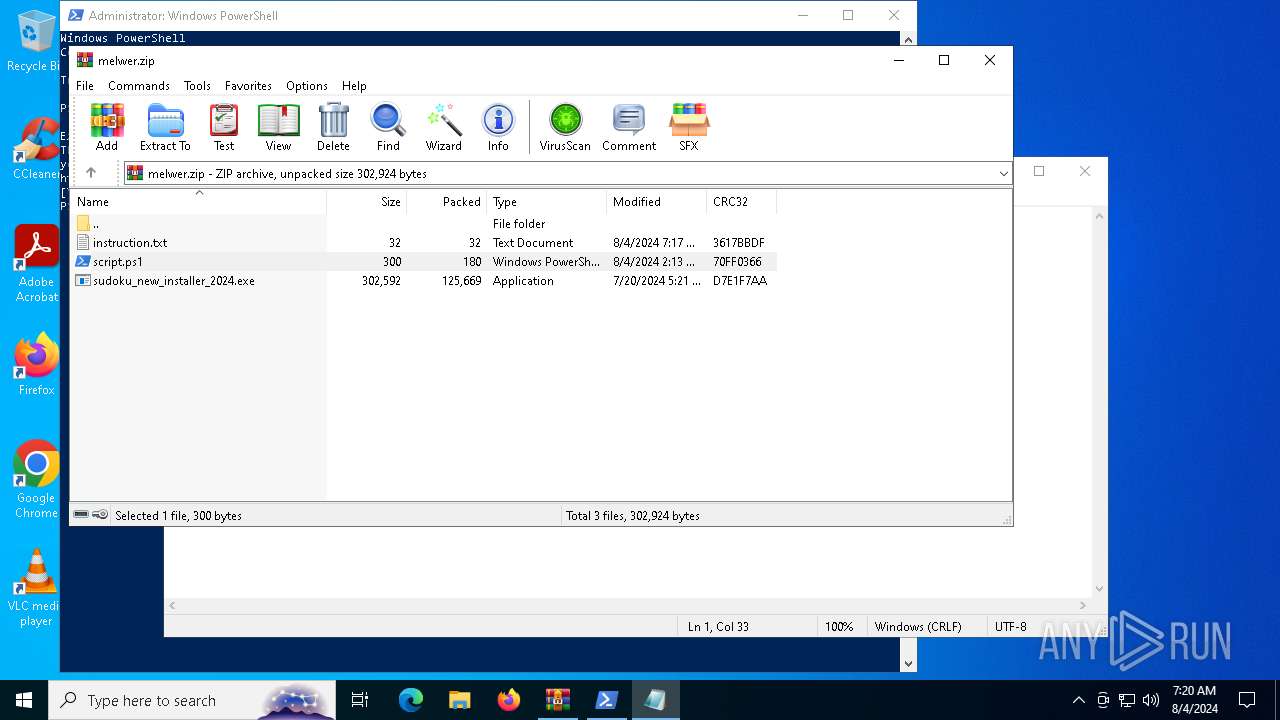
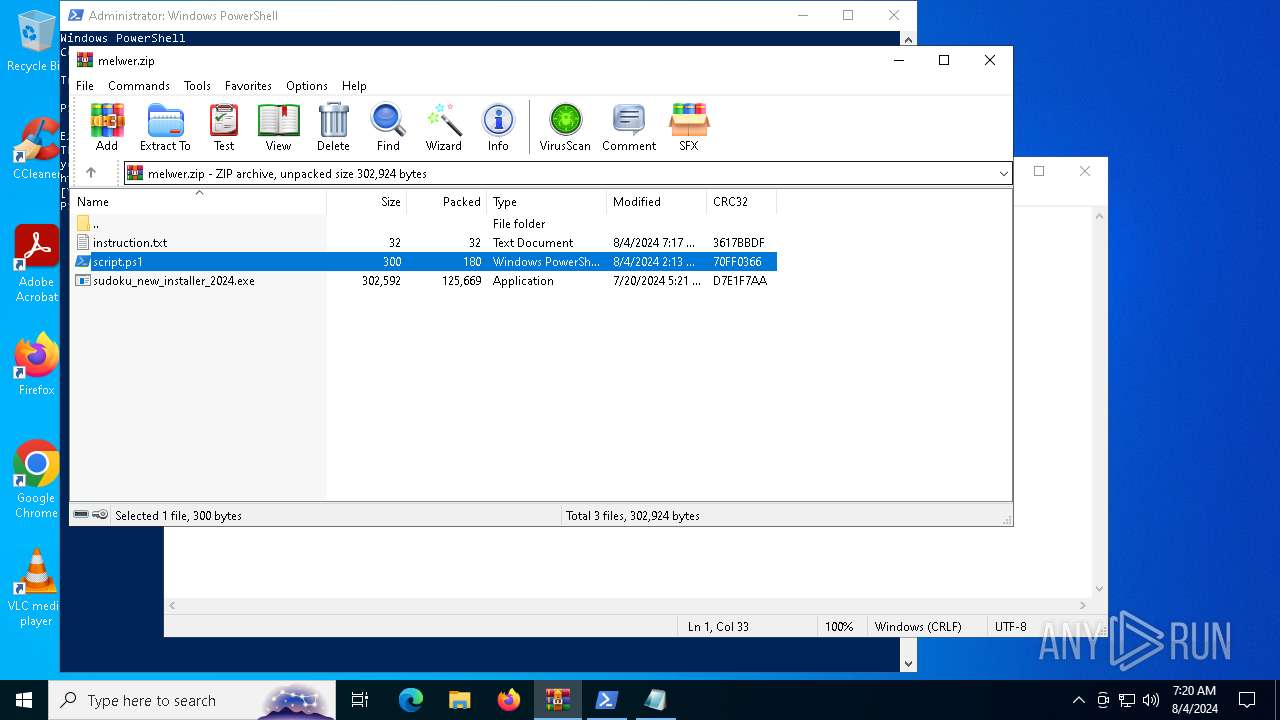
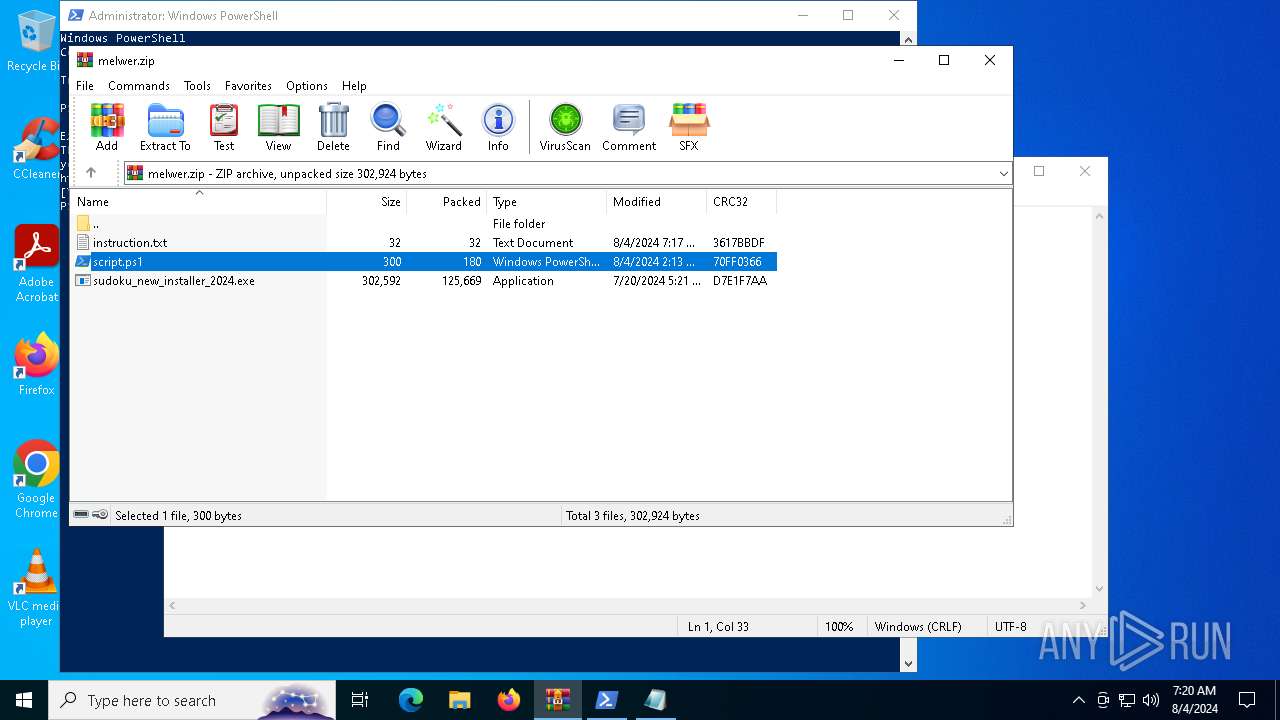
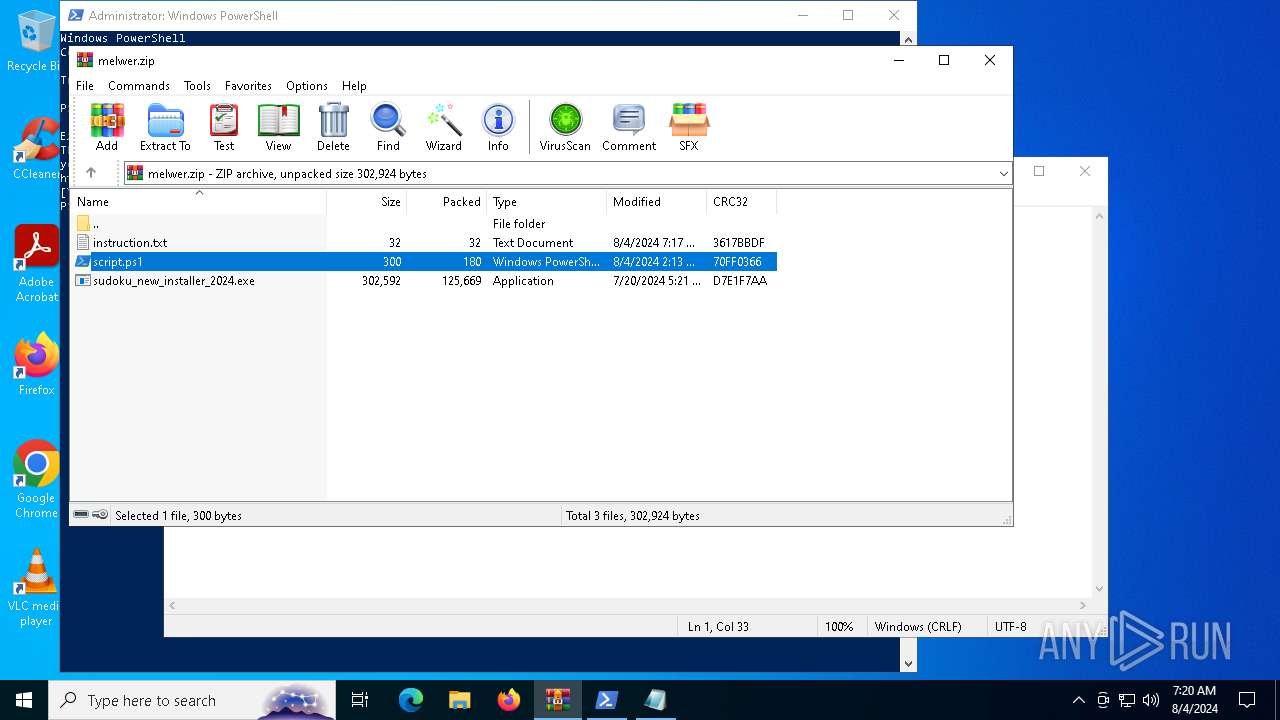
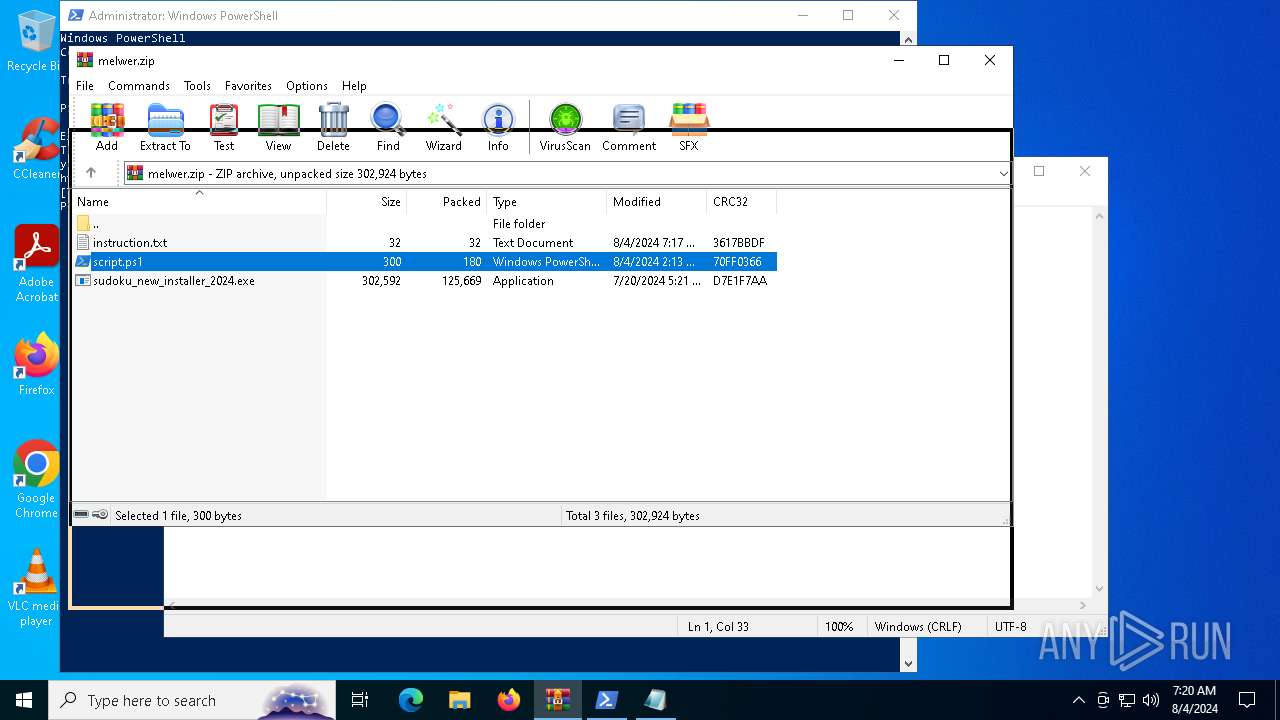
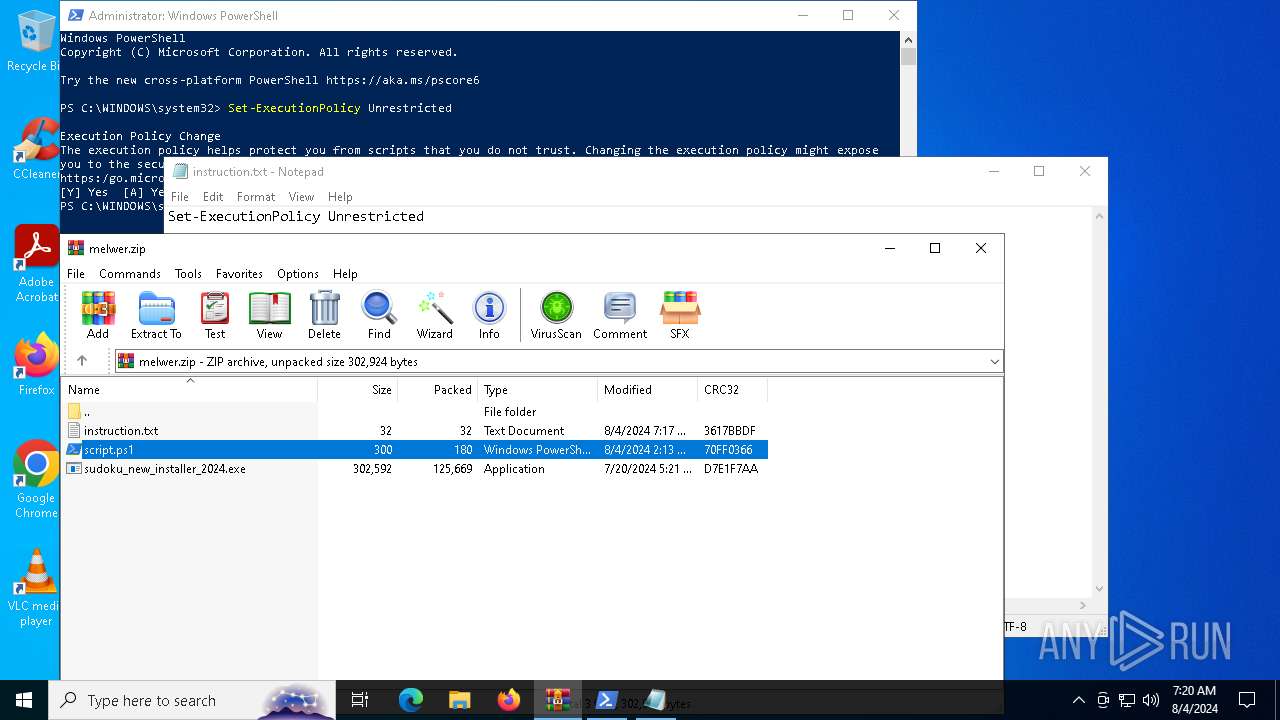
| File name: | melwer.zip |
| Full analysis: | https://app.any.run/tasks/1d467ce8-9087-4bd8-92c2-22b688b07690 |
| Verdict: | Malicious activity |
| Analysis date: | August 04, 2024, 07:19:34 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 6A9C2B2A0C318C34069726B87719AAB6 |
| SHA1: | 6807914DB40865DC5FCC7868134C2077E8D3FC3E |
| SHA256: | F9977F36ECFBB1DF4305E528D07802638BFCDC06E58E4969BAA2540F406E0B0F |
| SSDEEP: | 3072:eN6ECwdz3wi72RsgrPEqsnQXuKqu/Gn3FC6Aqyi1ePZD:eMGgXKCPrsnQXu5u/G3FljyOmZD |
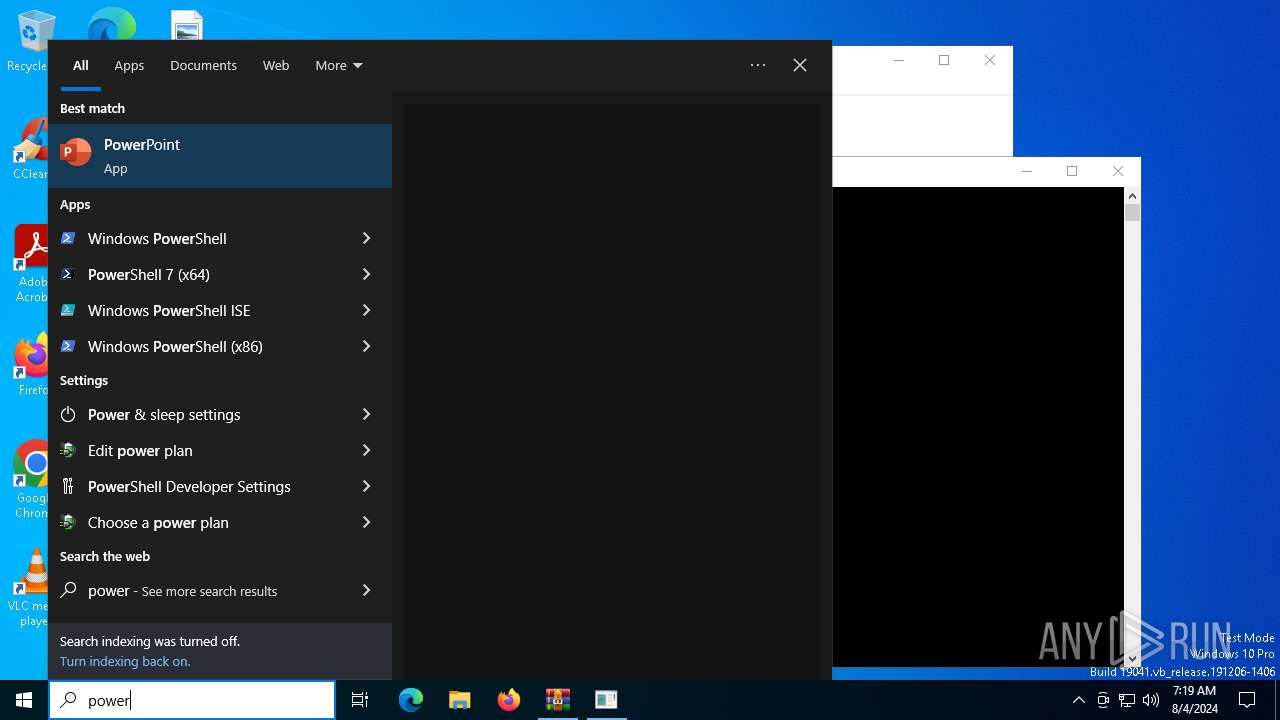
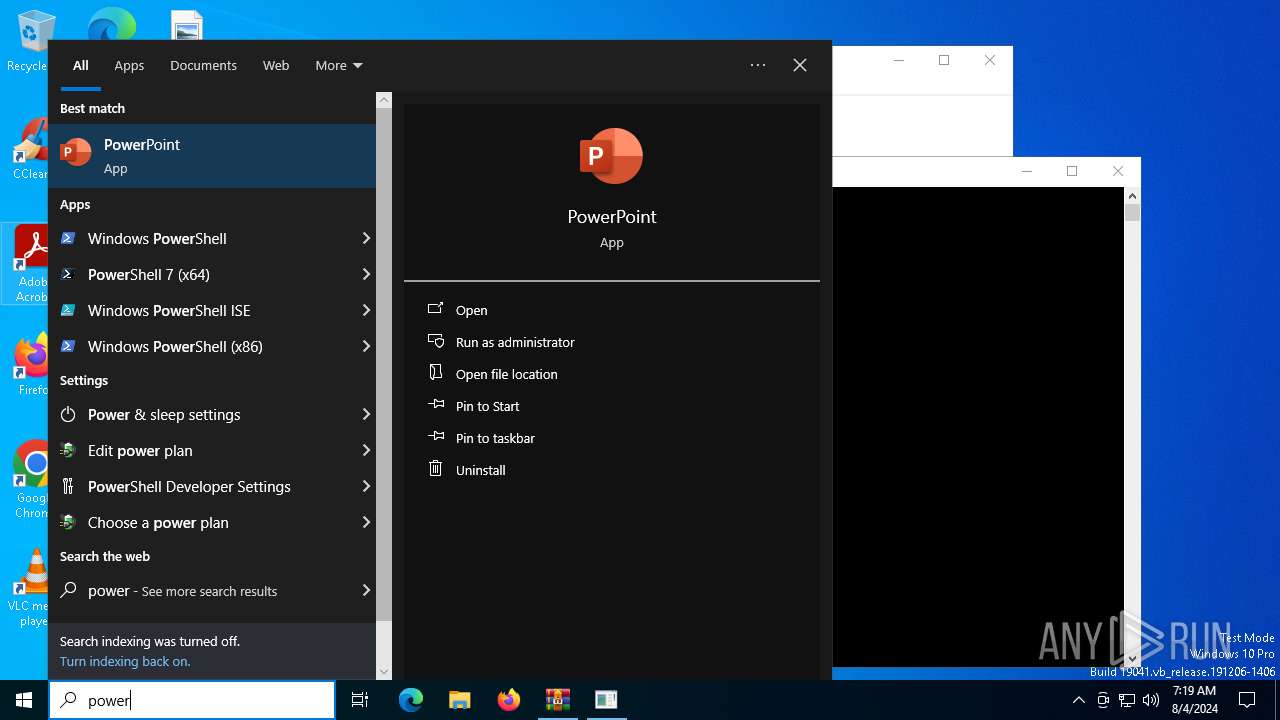
MALICIOUS
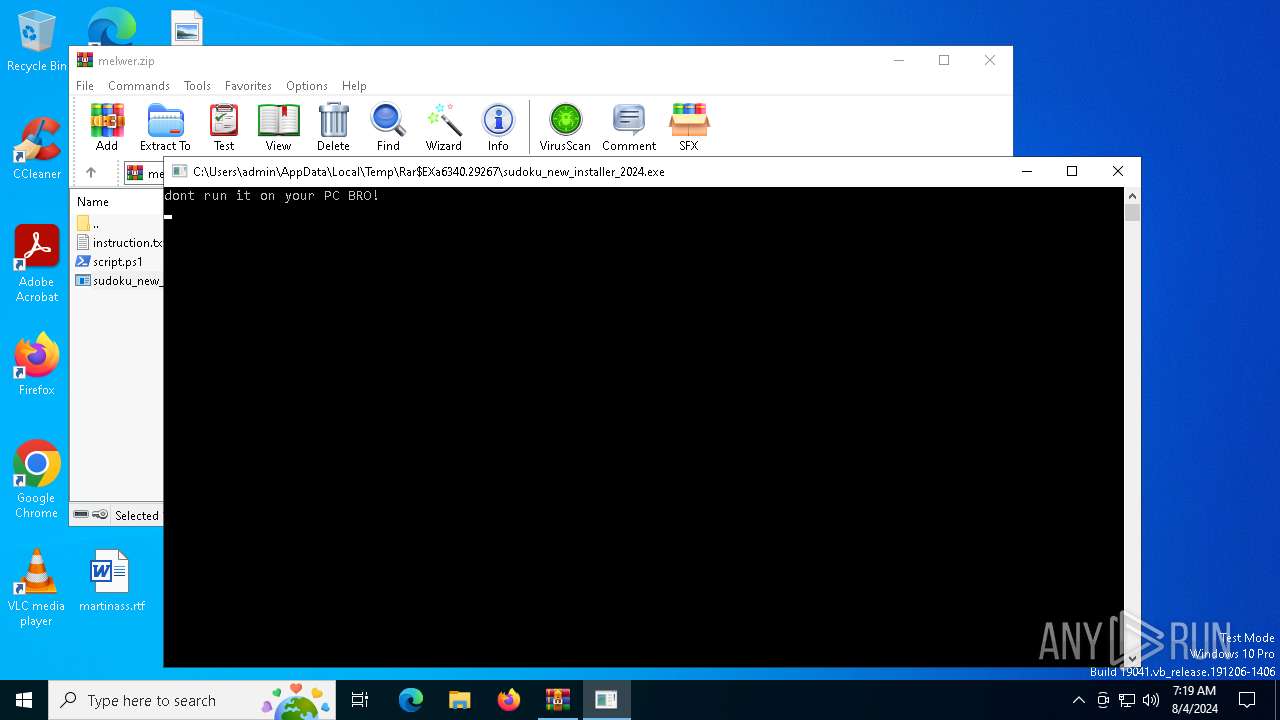
Drops the executable file immediately after the start
- WinRAR.exe (PID: 6340)
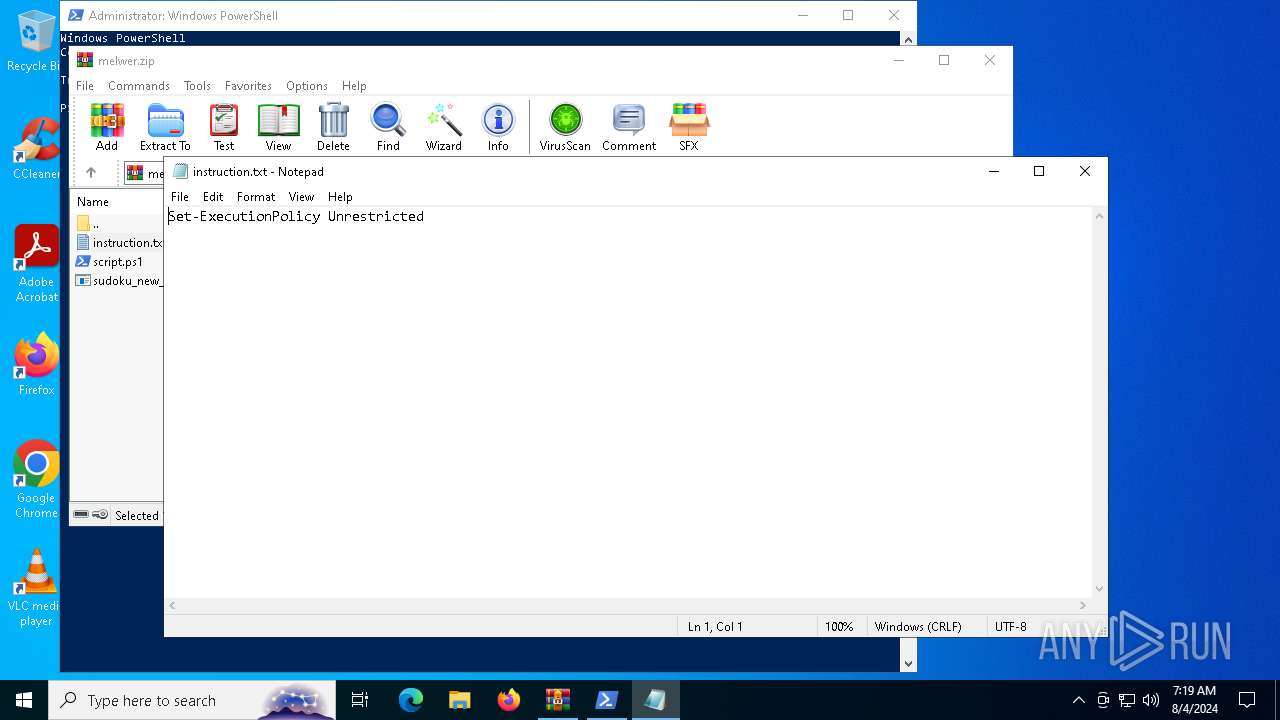
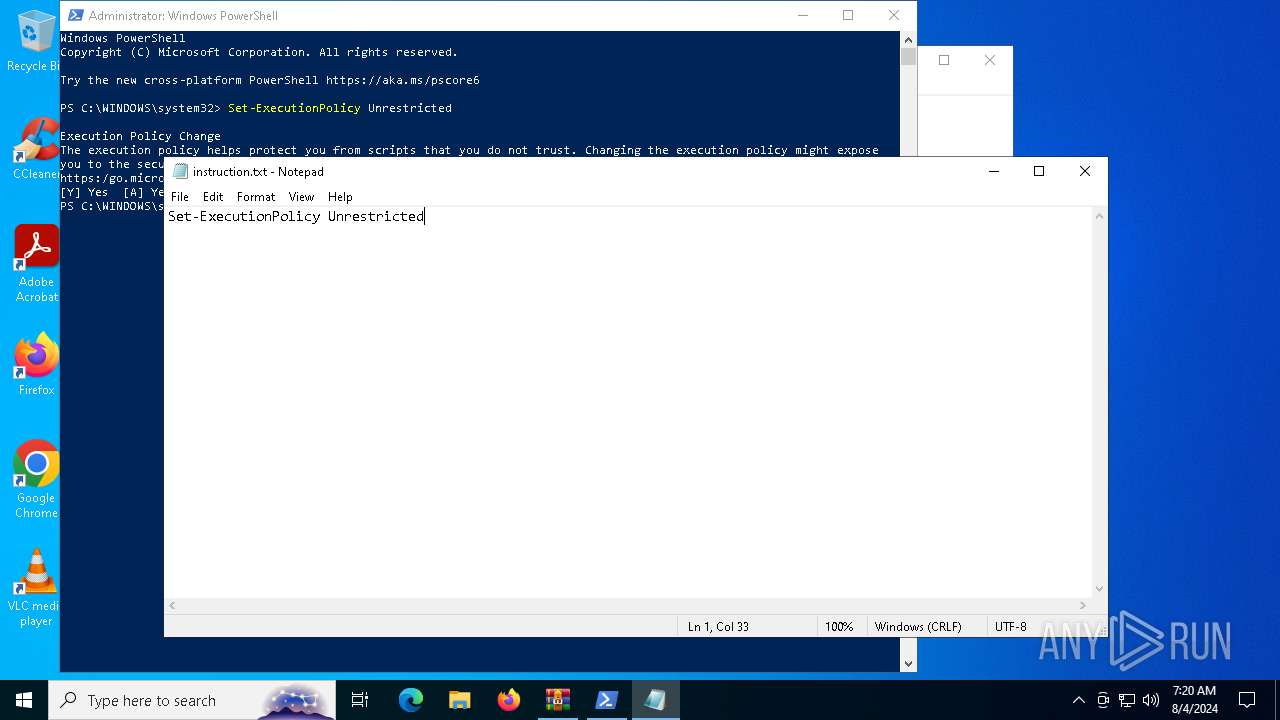
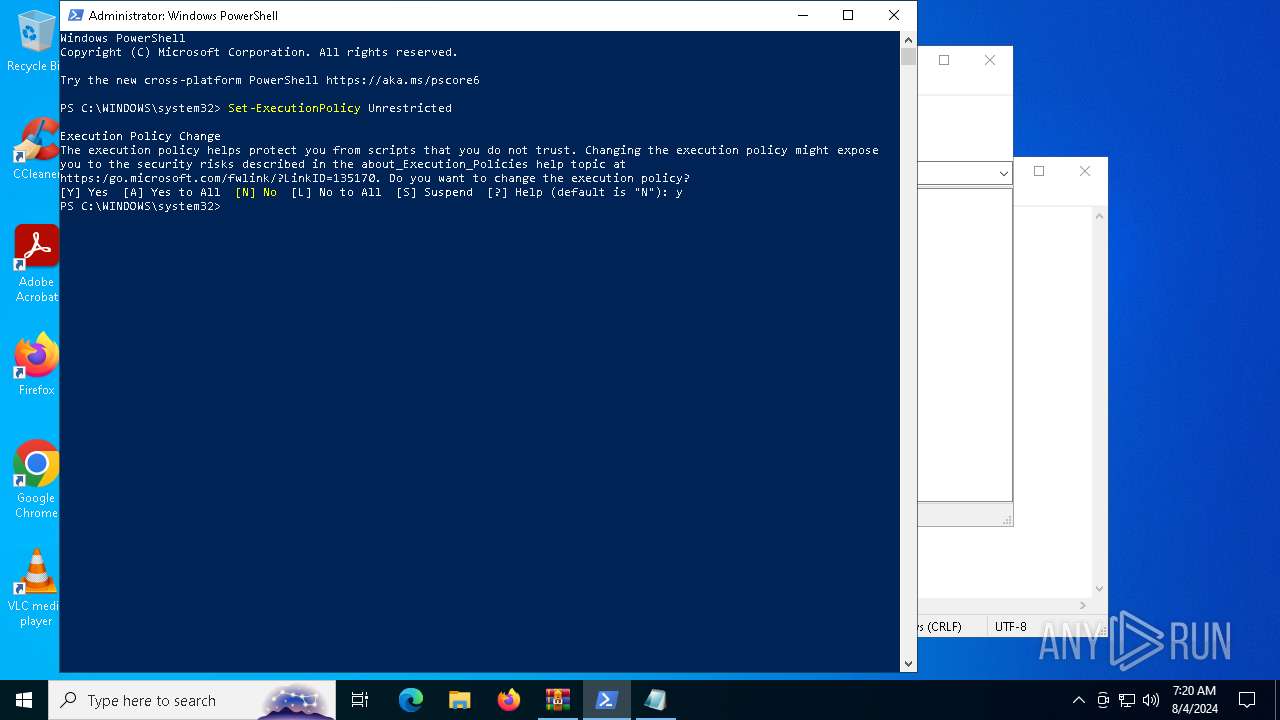
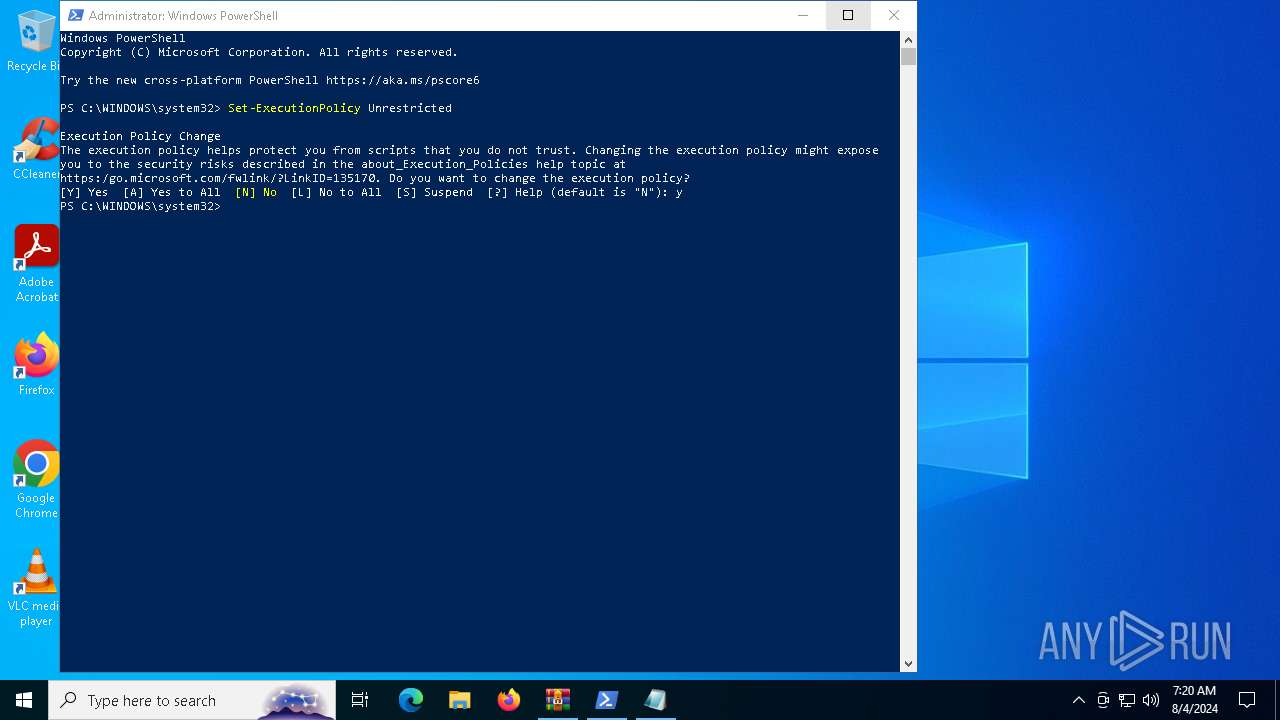
Changes powershell execution policy (Bypass)
- WinRAR.exe (PID: 6340)
Bypass execution policy to execute commands
- powershell.exe (PID: 7776)
- powershell.exe (PID: 8052)
- powershell.exe (PID: 236)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6340)
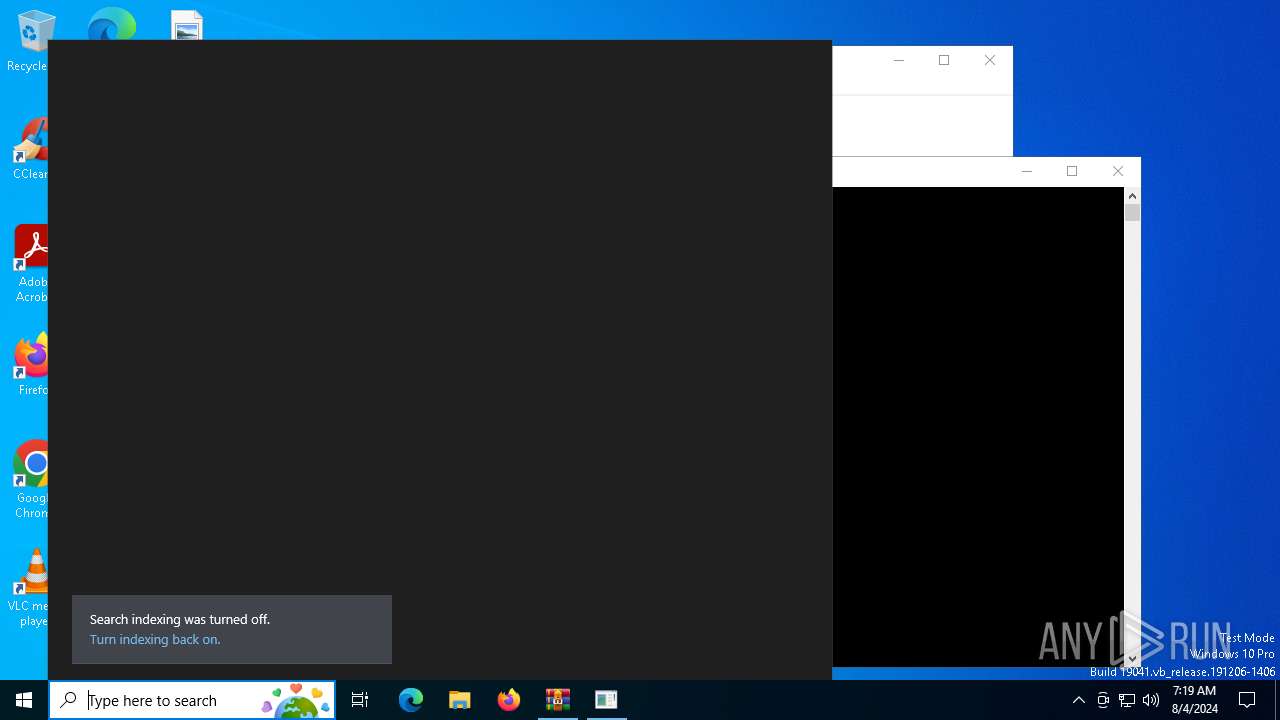
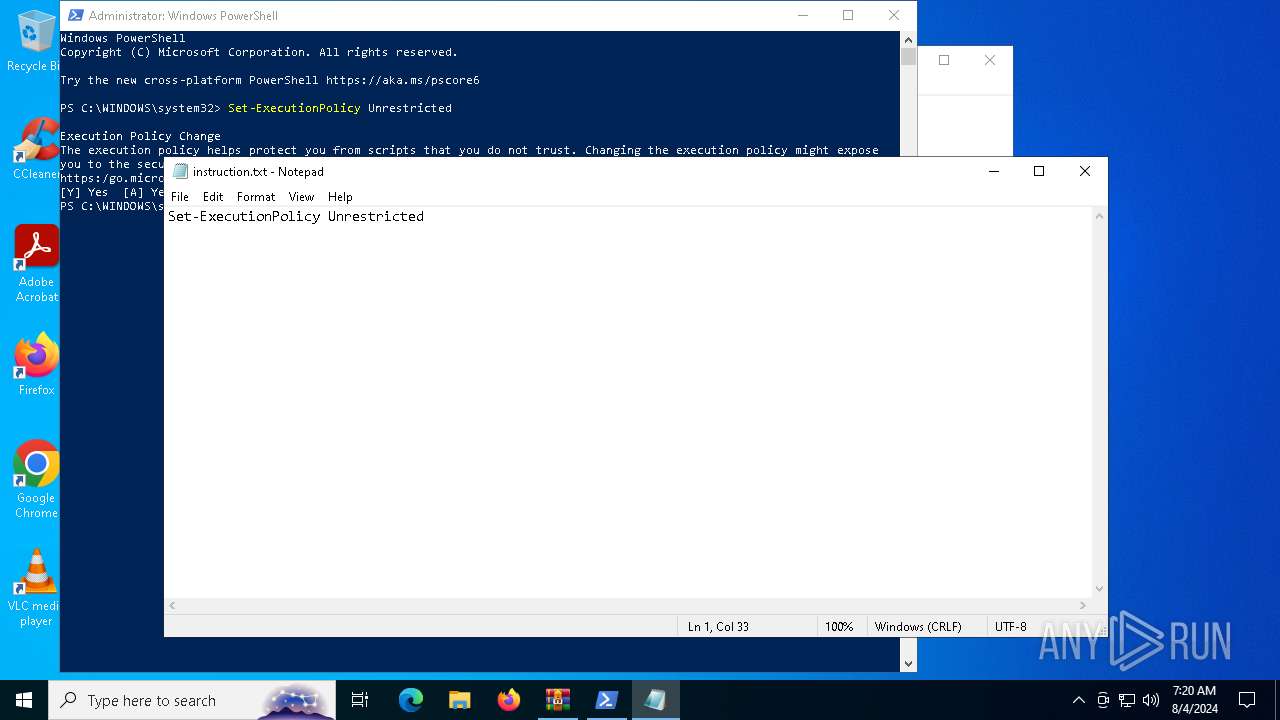
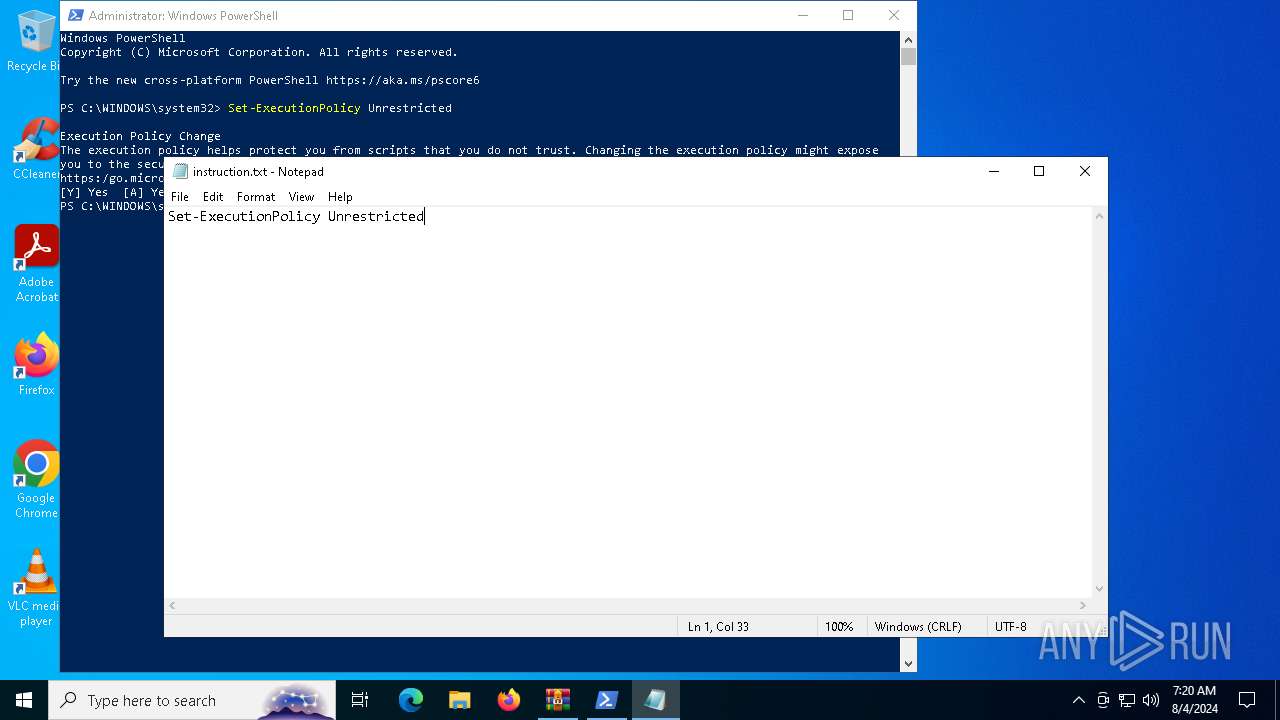
Start notepad (likely ransomware note)
- WinRAR.exe (PID: 6340)
The process executes Powershell scripts
- WinRAR.exe (PID: 6340)
Starts POWERSHELL.EXE for commands execution
- WinRAR.exe (PID: 6340)
INFO
Checks supported languages
- sudoku_new_installer_2024.exe (PID: 6620)
- TextInputHost.exe (PID: 6784)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6340)
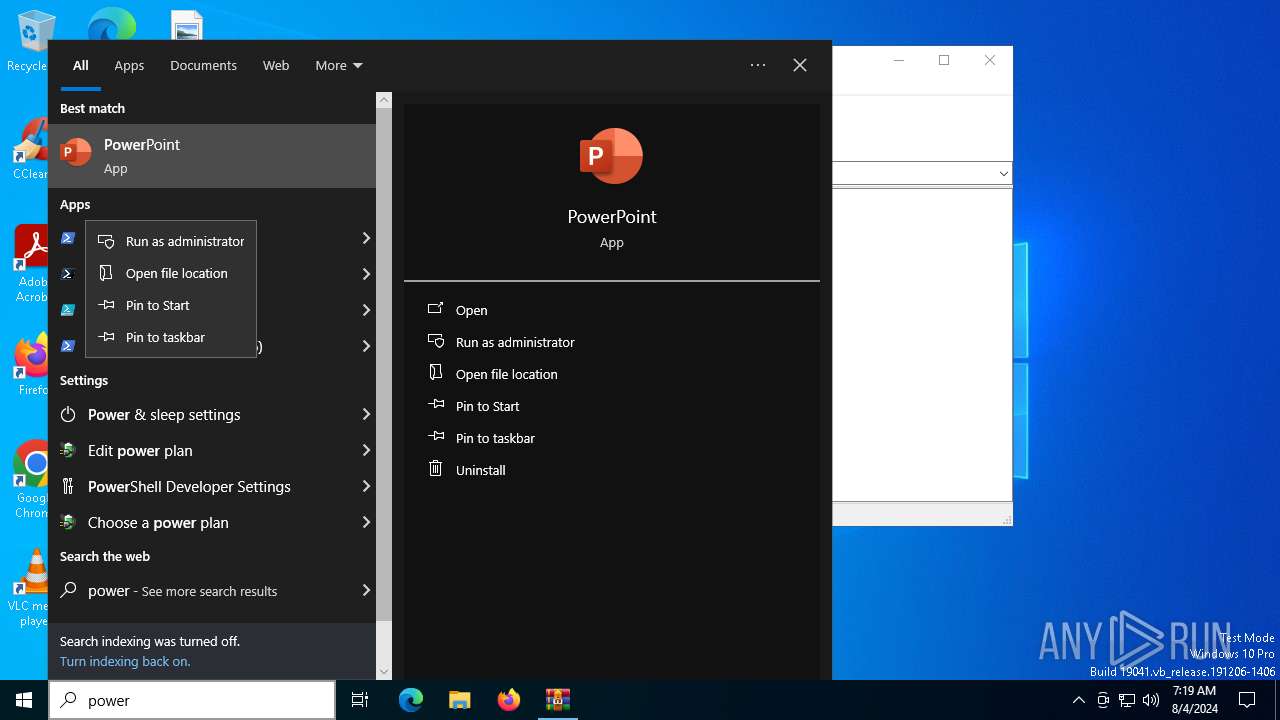
Manual execution by a user
- powershell.exe (PID: 6516)
Reads the computer name
- TextInputHost.exe (PID: 6784)
Reads security settings of Internet Explorer
- notepad.exe (PID: 7320)
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 6340)
Checks current location (POWERSHELL)
- powershell.exe (PID: 6516)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7776)
- powershell.exe (PID: 8052)
- powershell.exe (PID: 236)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:08:04 14:13:12 |
| ZipCRC: | 0x70ff0366 |
| ZipCompressedSize: | 180 |
| ZipUncompressedSize: | 300 |
| ZipFileName: | script.ps1 |
Total processes
149
Monitored processes
13
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass "C:\Users\admin\AppData\Local\Temp\Rar$DIa6340.33118\script.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6340 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\melwer.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 6516 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6584 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6620 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa6340.29267\sudoku_new_installer_2024.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa6340.29267\sudoku_new_installer_2024.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 6628 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sudoku_new_installer_2024.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6784 | "C:\WINDOWS\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe" -ServerName:InputApp.AppXjd5de1g66v206tj52m9d0dtpppx4cgpn.mca | C:\Windows\SystemApps\MicrosoftWindows.Client.CBS_cw5n1h2txyewy\TextInputHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Version: 123.26505.0.0 Modules
| |||||||||||||||
| 6820 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7320 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Rar$DIa6340.30464\instruction.txt | C:\Windows\System32\notepad.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7776 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass "C:\Users\admin\AppData\Local\Temp\Rar$DIa6340.31540\script.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
43 886
Read events
43 856
Write events
30
Delete events
0
Modification events
| (PID) Process: | (6340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (6340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (6340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\melwer.zip | |||
| (PID) Process: | (6340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6340) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | @"C:\WINDOWS\system32\windowspowershell\v1.0\powershell.exe",-107 |
Value: Windows PowerShell Console File | |||
| (PID) Process: | (6340) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
1
Suspicious files
14
Text files
15
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6340 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6340.29267\sudoku_new_installer_2024.exe | executable | |
MD5:13E2DE1EB5B07021E858E3812845B7FF | SHA256:116DD8938D94D0EC546E561F17C1AF5D272178ABE7165EB1851484E22C4A2931 | |||
| 6340 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa6340.30464\instruction.txt | text | |
MD5:30B84903A08D9F812E495B6ED005C703 | SHA256:C5C949850D4DE9D8034EC72C2277130A0DE54AD89FCDAF15ED848EFFE5DC2B6D | |||
| 6516 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RFe8076.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 6516 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\F3L1VNYCHD1NAVYWDYKY.temp | binary | |
MD5:6DD68610BE30AC8BD2CF35C7B7E115AD | SHA256:3E6620A08BAEF69A5F2BE8858343C10E0978163831B406267C75D1995CBA5217 | |||
| 6516 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:6DD68610BE30AC8BD2CF35C7B7E115AD | SHA256:3E6620A08BAEF69A5F2BE8858343C10E0978163831B406267C75D1995CBA5217 | |||
| 7776 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\VATWT3CA57JB6PM8O98K.temp | binary | |
MD5:AF7A148DFD35A2B4F7B214EF75DA3808 | SHA256:6019C5901885E3A40B01F8466A77658AF427679081C6736C51C60D1832D266D4 | |||
| 6516 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_h323azep.5t0.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7776 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RFeba43.TMP | binary | |
MD5:6DD68610BE30AC8BD2CF35C7B7E115AD | SHA256:3E6620A08BAEF69A5F2BE8858343C10E0978163831B406267C75D1995CBA5217 | |||
| 6340 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa6340.29267\instruction.txt | text | |
MD5:30B84903A08D9F812E495B6ED005C703 | SHA256:C5C949850D4DE9D8034EC72C2277130A0DE54AD89FCDAF15ED848EFFE5DC2B6D | |||
| 7776 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:AF7A148DFD35A2B4F7B214EF75DA3808 | SHA256:6019C5901885E3A40B01F8466A77658AF427679081C6736C51C60D1832D266D4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
40
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
2132 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5484 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2080 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4788 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4088 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5336 | SearchApp.exe | 2.16.110.195:443 | www.bing.com | Akamai International B.V. | DE | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
5336 | SearchApp.exe | 2.16.110.171:443 | www.bing.com | Akamai International B.V. | DE | unknown |
5336 | SearchApp.exe | 2.16.110.168:443 | www.bing.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
r.bing.com |
| whitelisted |
th.bing.com |
| whitelisted |
browser.pipe.aria.microsoft.com |
| whitelisted |
fp.msedge.net |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |