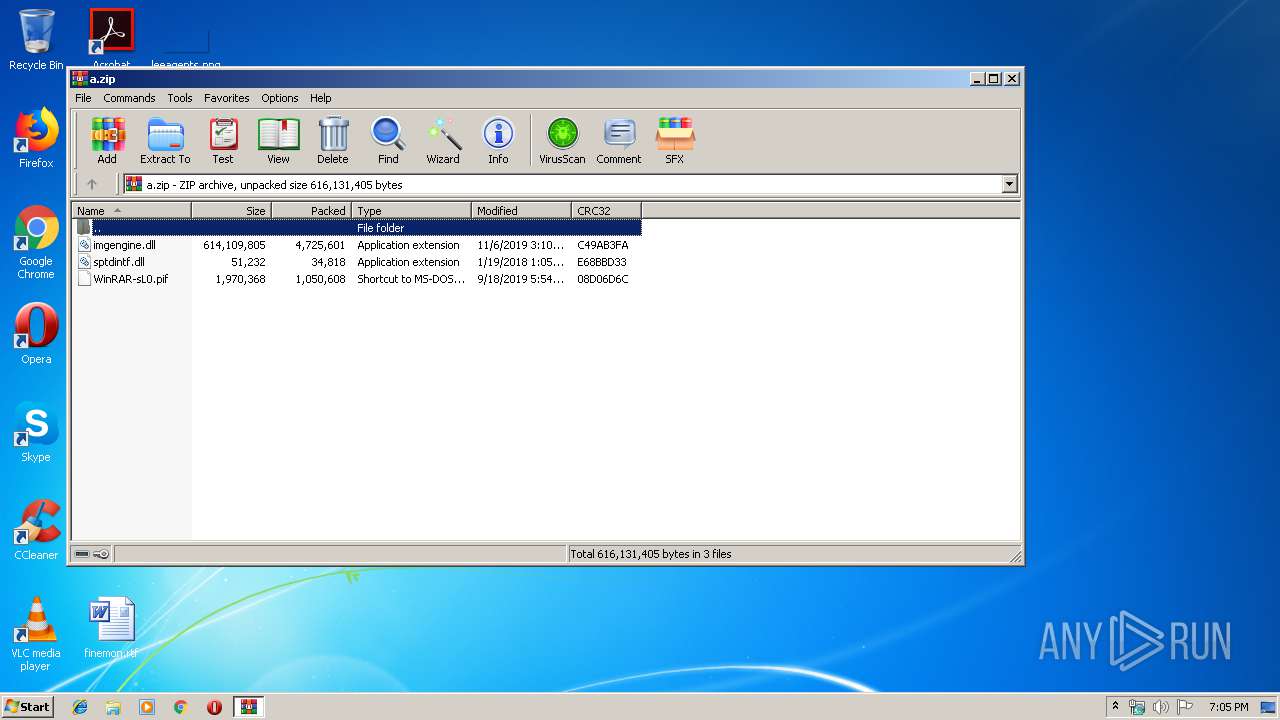
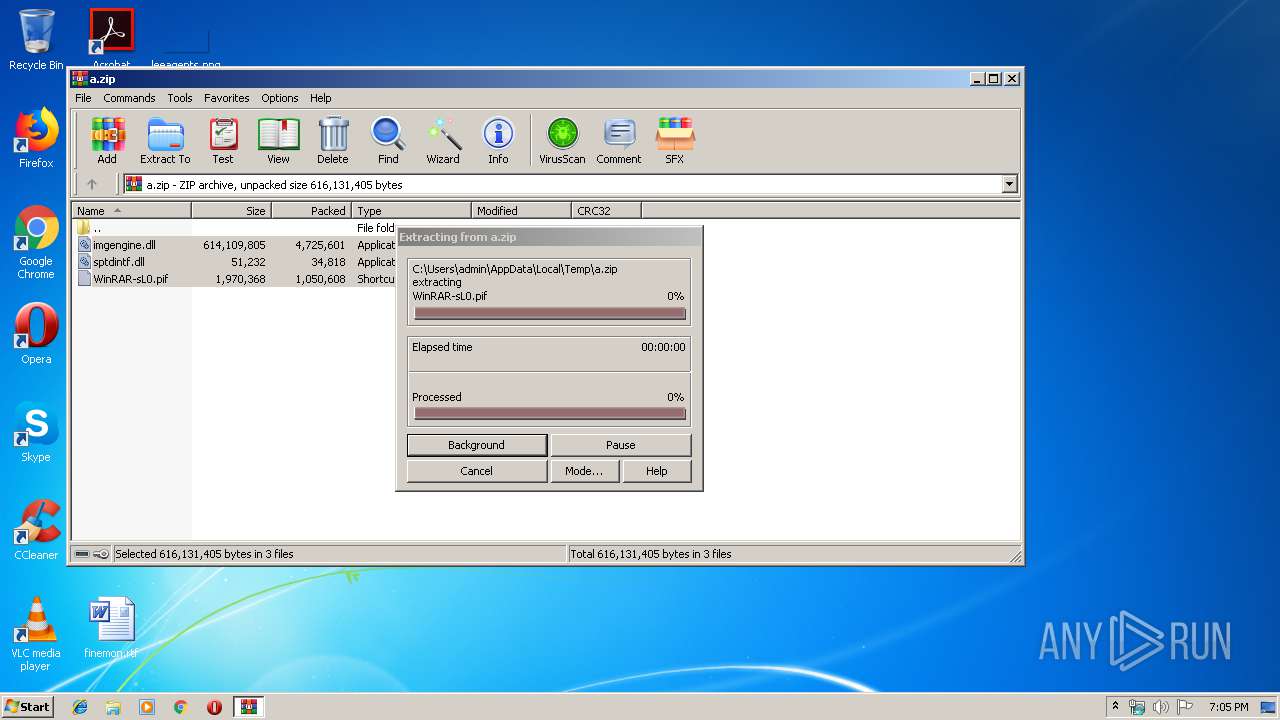
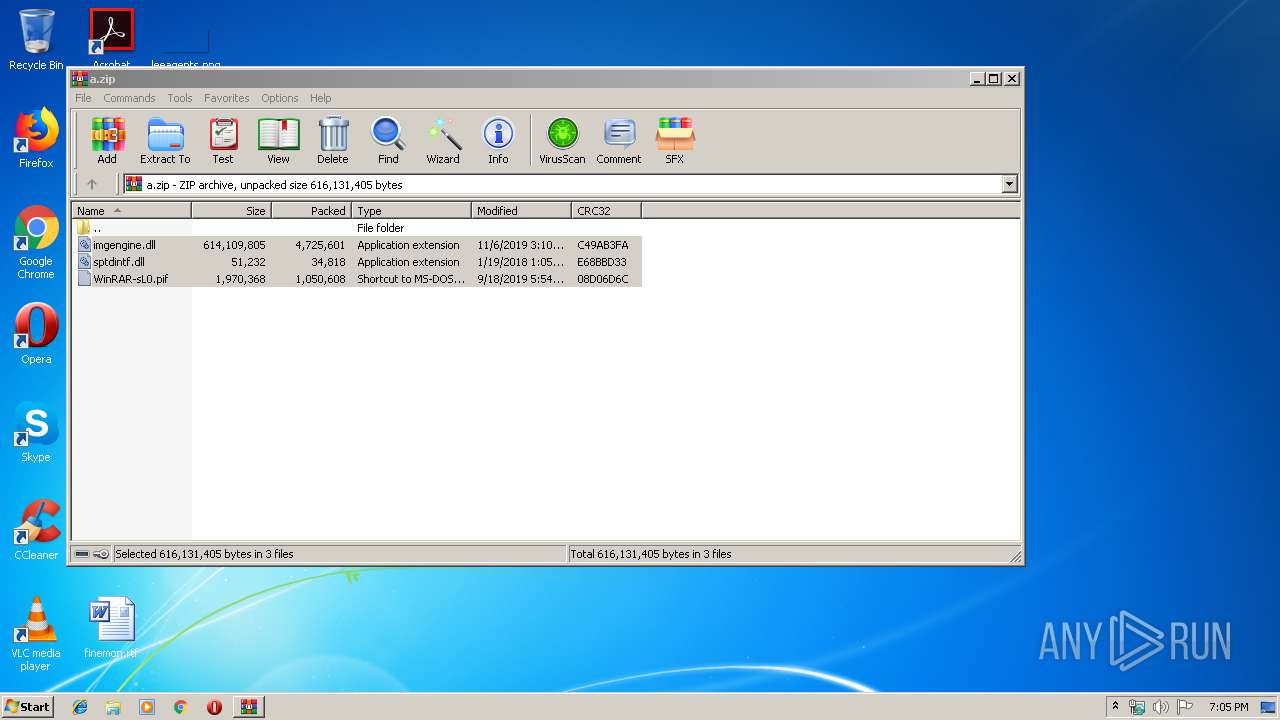
| File name: | a.zip |
| Full analysis: | https://app.any.run/tasks/00c7d3a7-9df2-49a8-a9f2-8d2d99a1cbe3 |
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2020, 19:05:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | C5F9CDE19E62E38F75D4FCDAB704590B |
| SHA1: | 7D42B7FC041FDC259391BC748067DAB049D972D9 |
| SHA256: | F99425F8A7CA8A716C6ABA1D39C9487CB9AE92676E370D2C5894B1C03D486B80 |
| SSDEEP: | 98304:2p/6+uueP7vl8wBikq3ujkTs8qeAYPwLnZXYyfV3CSGTvIkrzh:2/6oerl8wB0gOs83gnZXYyfcSGckR |
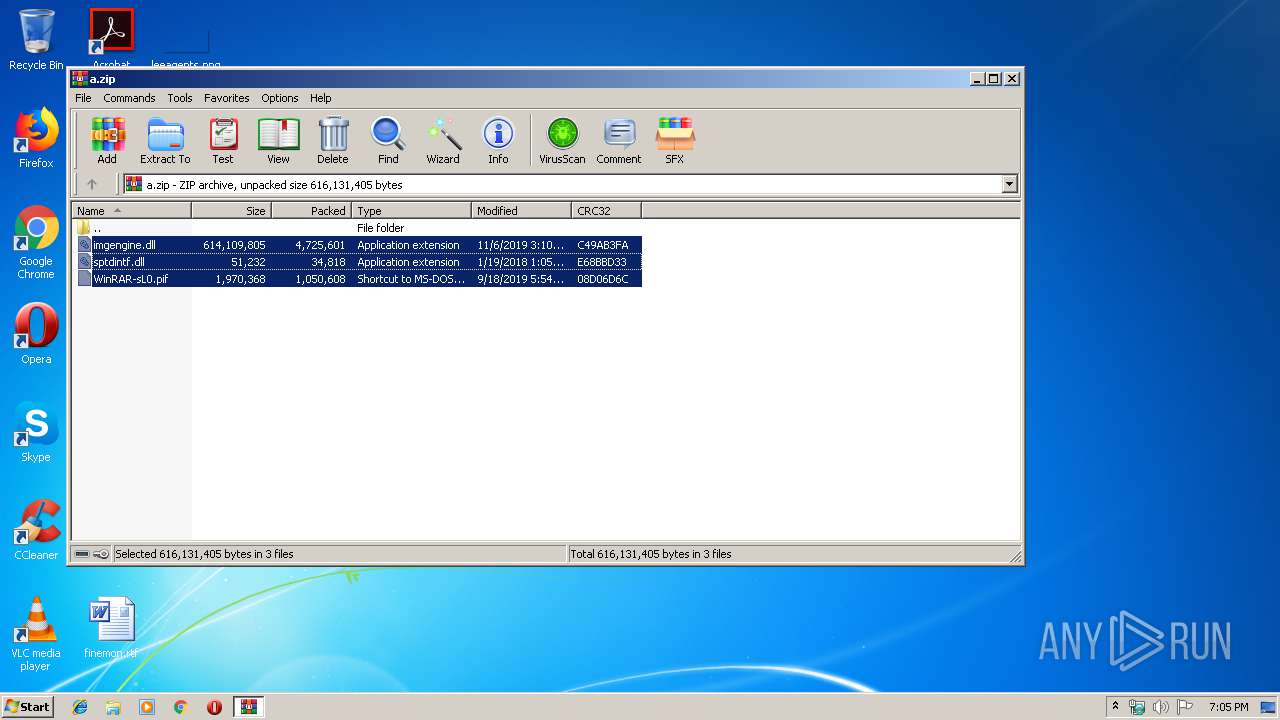
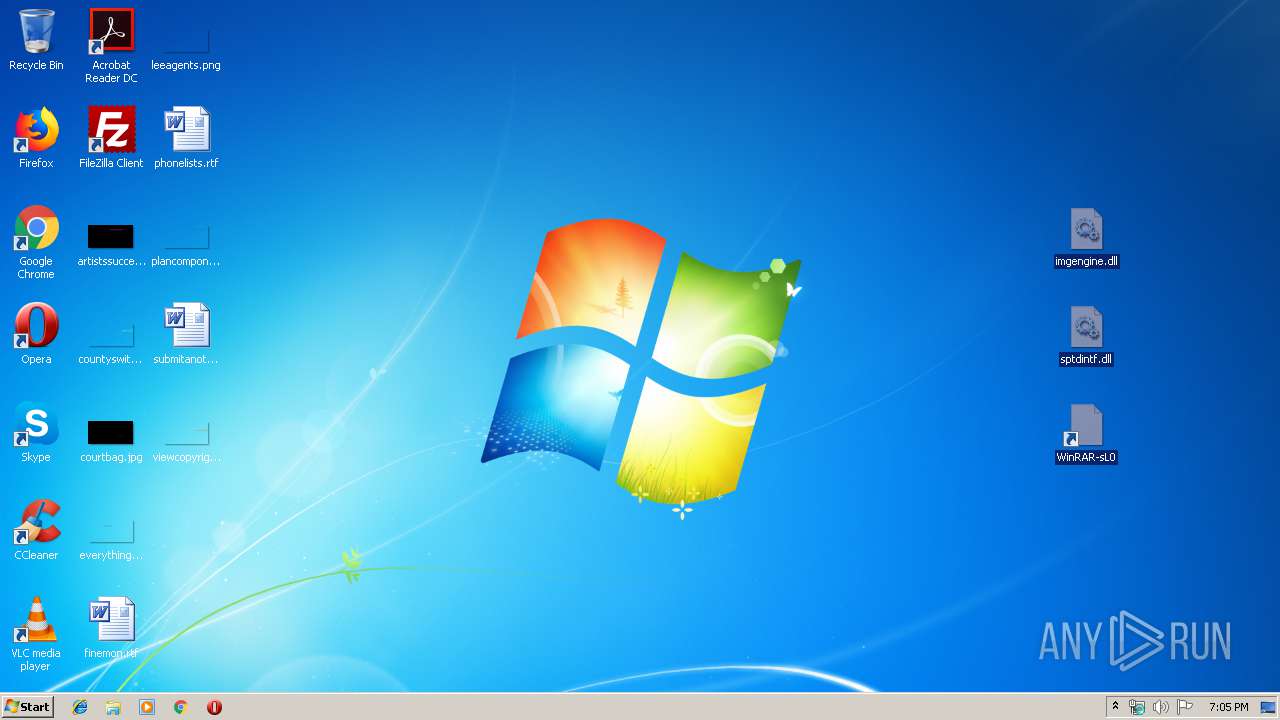
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3484)
- WinRAR-sL0.pif (PID: 2912)
Application was dropped or rewritten from another process
- WinRAR-sL0.pif (PID: 2912)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 932)
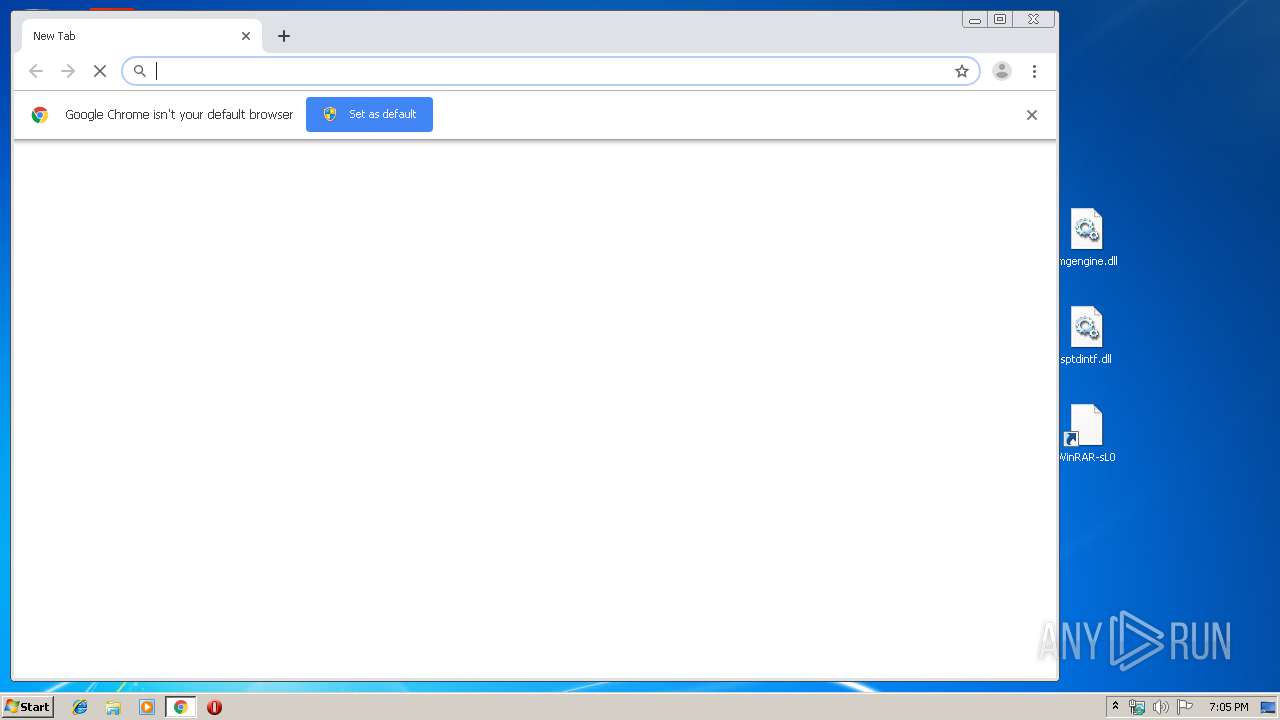
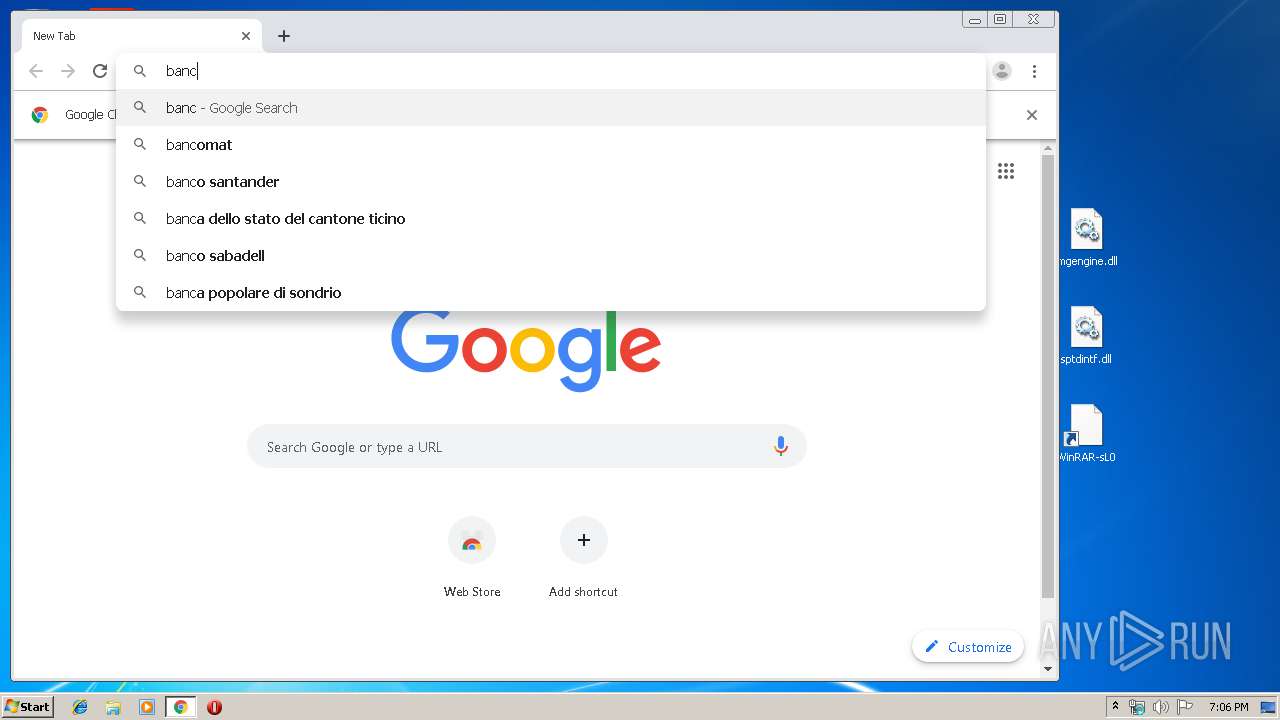
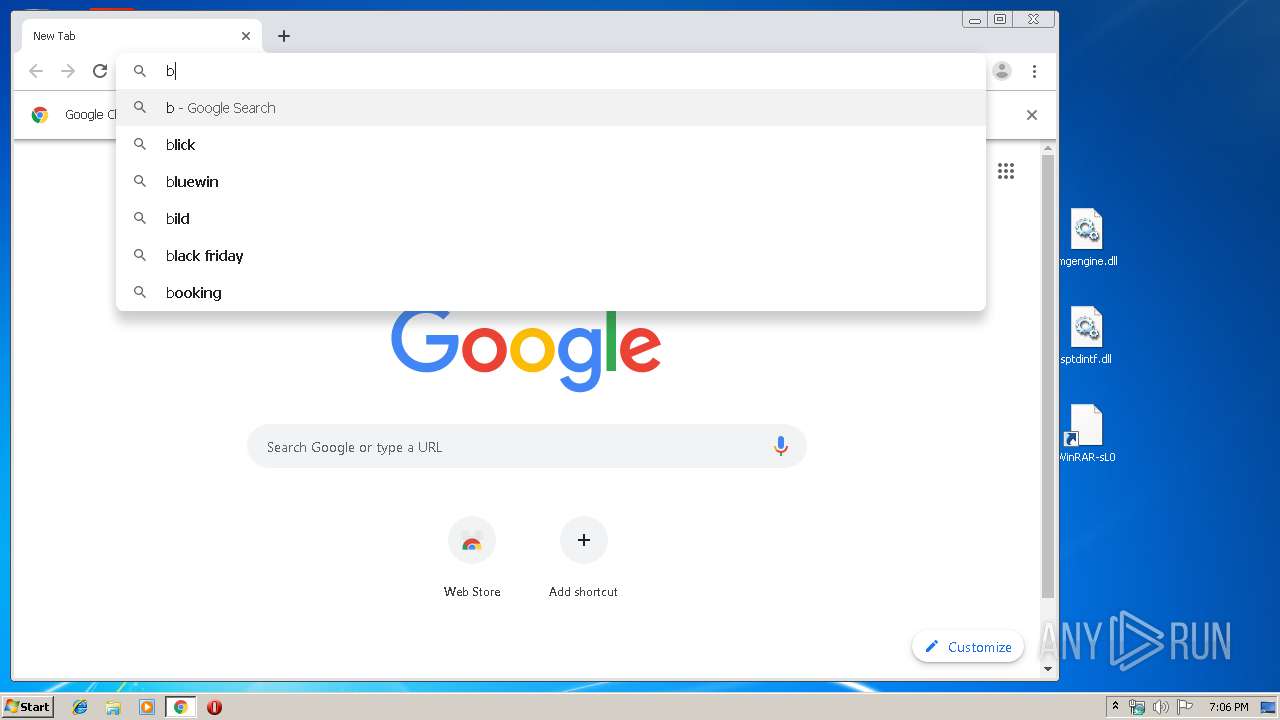
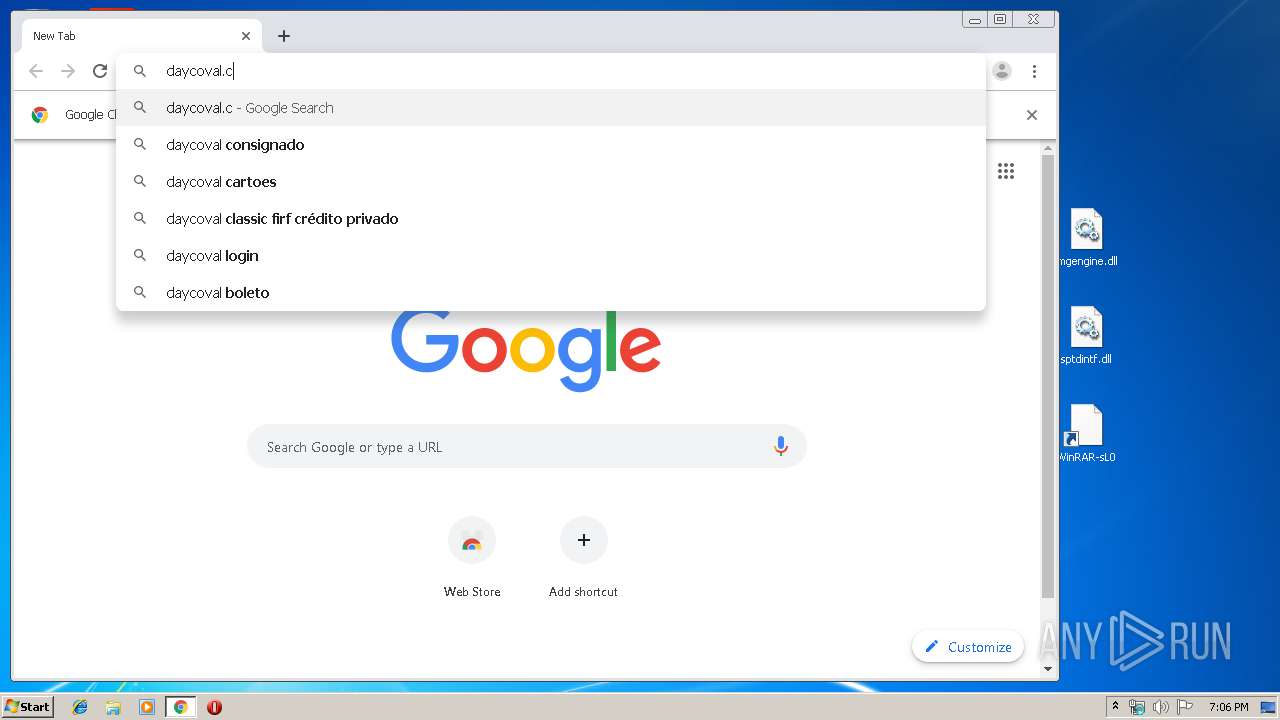
Modifies files in Chrome extension folder
- chrome.exe (PID: 4040)
Checks for external IP
- WinRAR-sL0.pif (PID: 2912)
Reads Environment values
- WinRAR-sL0.pif (PID: 2912)
INFO
Reads the hosts file
- chrome.exe (PID: 4040)
- chrome.exe (PID: 3388)
Application launched itself
- chrome.exe (PID: 4040)
Changes settings of System certificates
- chrome.exe (PID: 3388)
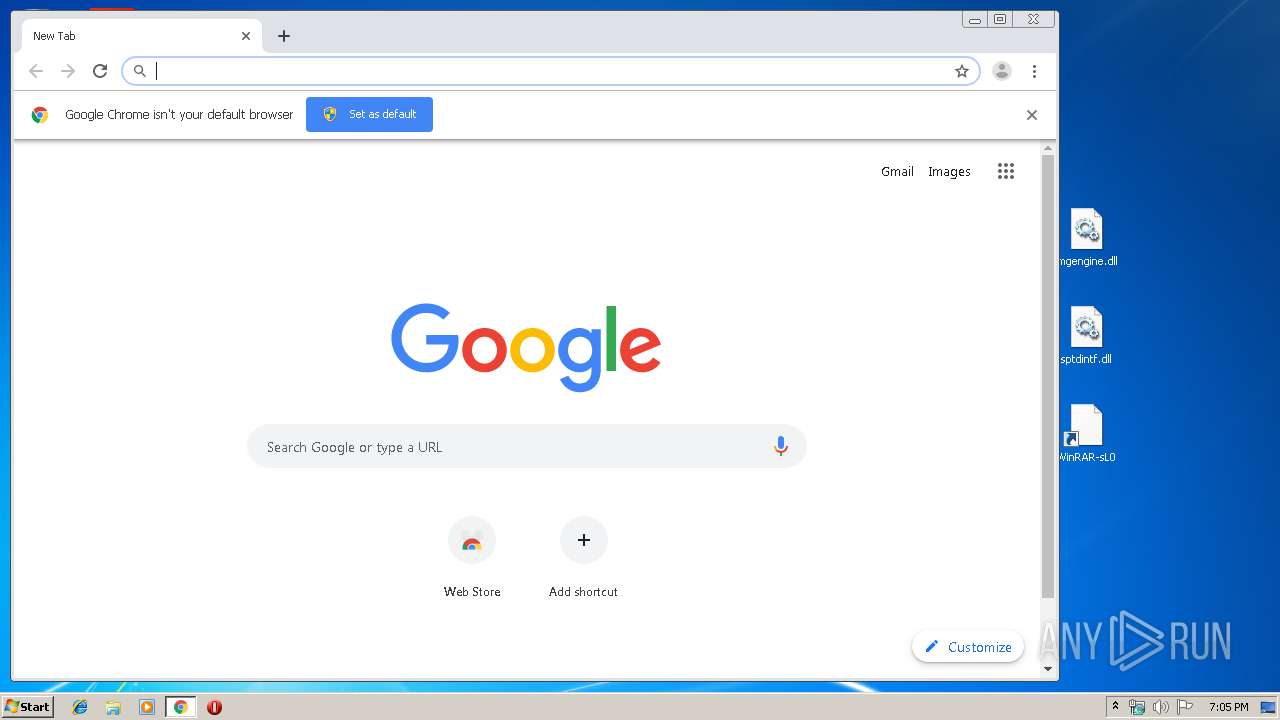
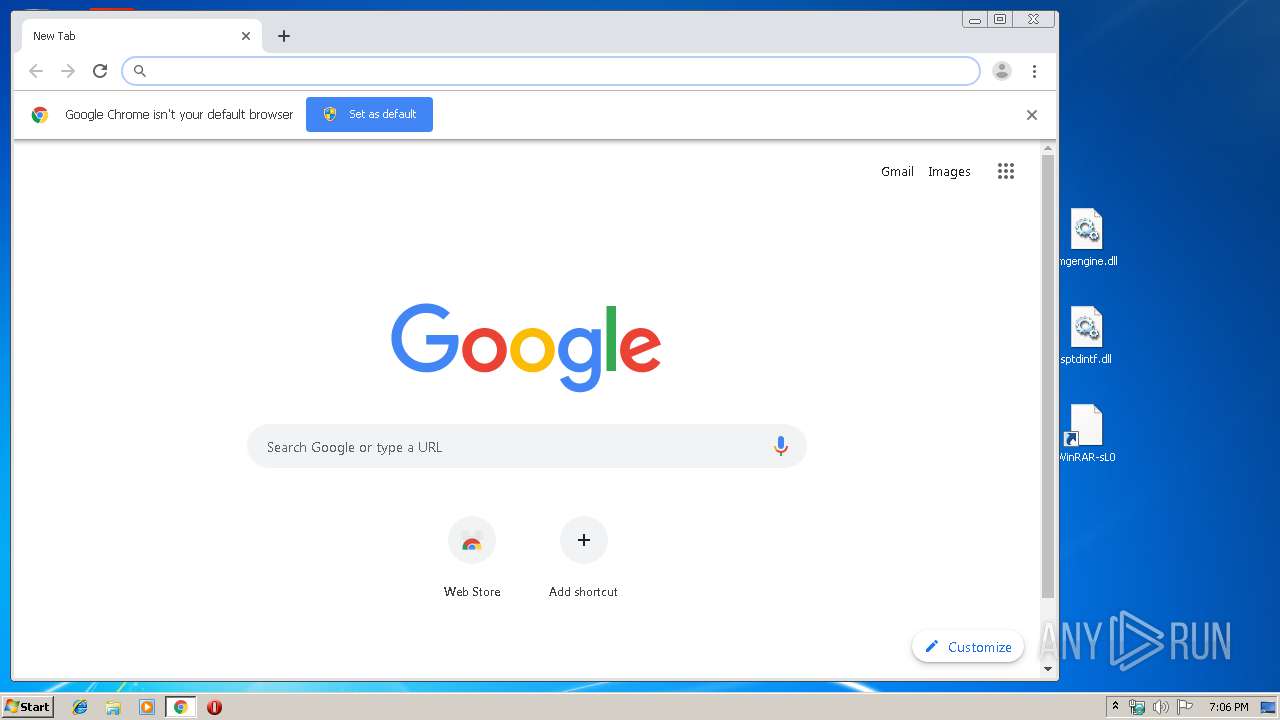
Manual execution by user
- WinRAR-sL0.pif (PID: 2912)
- chrome.exe (PID: 4040)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2018:01:19 11:05:16 |
| ZipCRC: | 0xe68bbd33 |
| ZipCompressedSize: | 34818 |
| ZipUncompressedSize: | 51232 |
| ZipFileName: | sptdintf.dll |
Total processes
75
Monitored processes
40
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,11279261617469905726,12074060155636944417,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1152960761694043866 --mojo-platform-channel-handle=4116 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 252 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,11279261617469905726,12074060155636944417,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15491233256070836977 --renderer-client-id=35 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4388 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=4028 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 932 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\a.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 940 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6d6aa9d0,0x6d6aa9e0,0x6d6aa9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,11279261617469905726,12074060155636944417,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=481344100568903191 --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4304 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,11279261617469905726,12074060155636944417,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12185773567625599782 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4316 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,11279261617469905726,12074060155636944417,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5306716277514706588 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3340 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,11279261617469905726,12074060155636944417,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14077619091963331959 --mojo-platform-channel-handle=4300 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,11279261617469905726,12074060155636944417,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8418892258152554461 --mojo-platform-channel-handle=3456 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
726
Read events
620
Write events
102
Delete events
4
Modification events
| (PID) Process: | (932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (932) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\a.zip | |||
| (PID) Process: | (932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (932) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\acppage.dll,-6005 |
Value: Shortcut to MS-DOS Program | |||
| (PID) Process: | (932) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
2
Suspicious files
57
Text files
309
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 932 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa932.44554\imgengine.dll | — | |
MD5:— | SHA256:— | |||
| 4040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b1f1337f-be89-4aa2-8441-cc99fa7dcfb7.tmp | — | |
MD5:— | SHA256:— | |||
| 4040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 4040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 4040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 4040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:— | SHA256:— | |||
| 4040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 932 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa932.44554\sptdintf.dll | executable | |
MD5:3862C98F3676F3FD8BF4759DB17CF273 | SHA256:1C7D5E42FF3BC5E1A0ECD01FA68633DC67515B3A06E660FCD2D22D6EA436A6F1 | |||
| 4040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
59
DNS requests
44
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3388 | chrome.exe | GET | 302 | 216.58.206.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 510 b | whitelisted |
2912 | WinRAR-sL0.pif | GET | 200 | 191.239.248.130:80 | http://191.239.248.130:80/$p | BR | text | 14 b | unknown |
3388 | chrome.exe | GET | 200 | 91.199.212.52:80 | http://crt.usertrust.com/USERTrustRSAAddTrustCA.crt | GB | der | 1.37 Kb | whitelisted |
3388 | chrome.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEAWL0TfE8bgW4DN6lA4xNpM%3D | US | der | 471 b | whitelisted |
3388 | chrome.exe | GET | 200 | 173.194.160.74:80 | http://r5---sn-1gi7znes.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.212.170.89&mm=28&mn=sn-1gi7znes&ms=nvh&mt=1579287863&mv=m&mvi=4&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
2912 | WinRAR-sL0.pif | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/ | unknown | text | 264 b | malicious |
3388 | chrome.exe | GET | 200 | 173.194.160.72:80 | http://r3---sn-1gi7znes.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=185.212.170.89&mm=28&mn=sn-1gi7znes&ms=nvh&mt=1579287920&mv=m&mvi=2&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
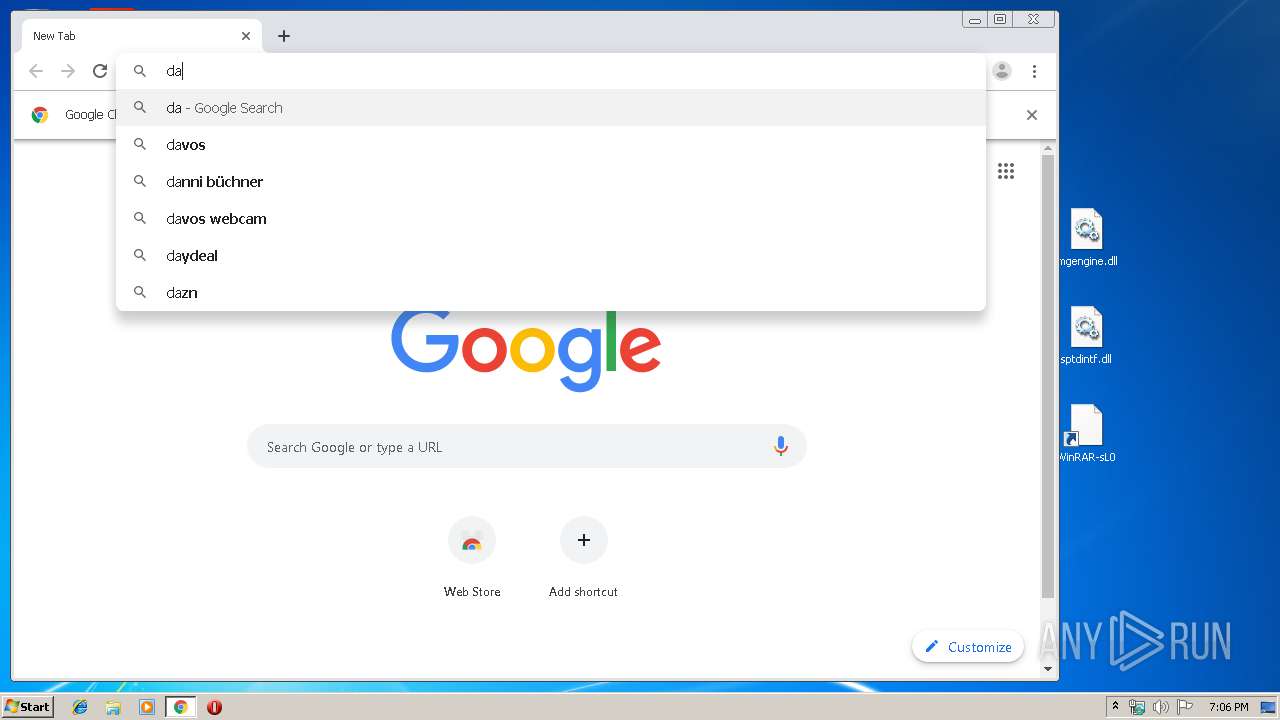
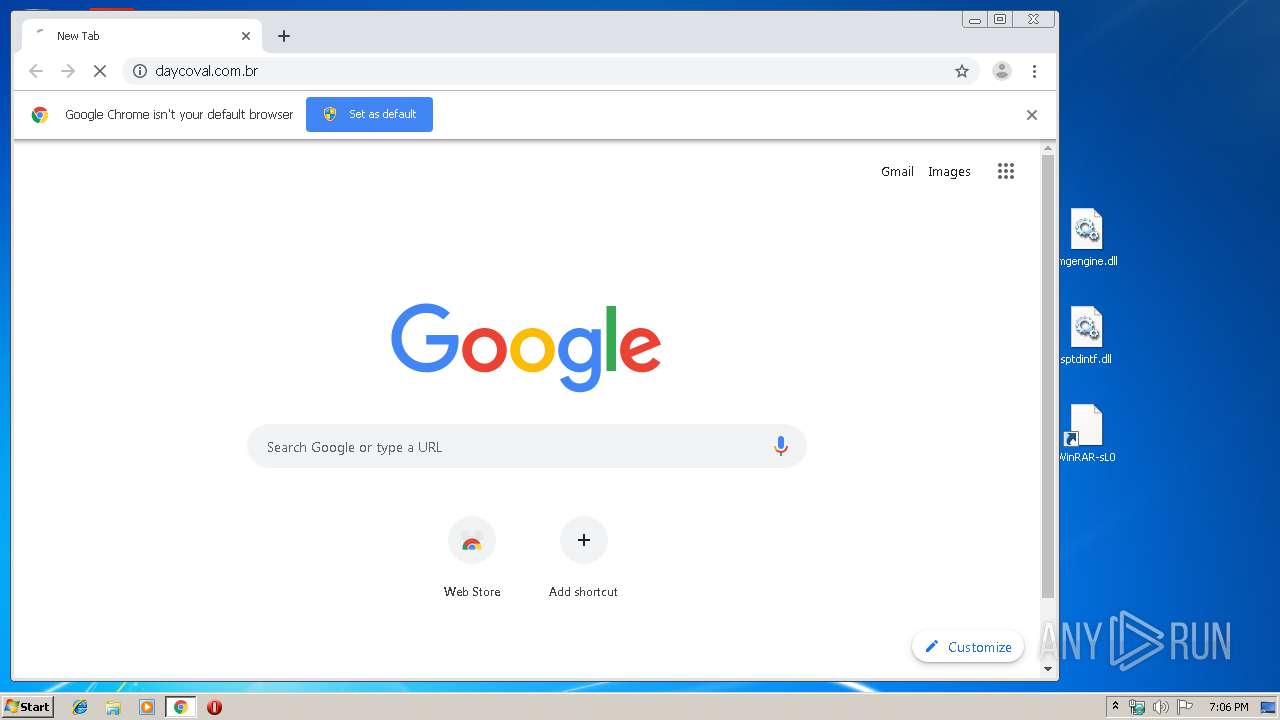
3388 | chrome.exe | GET | 302 | 177.69.70.197:80 | http://daycoval.com.br/ | BR | html | 151 b | whitelisted |
3388 | chrome.exe | GET | 302 | 216.58.206.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
3388 | chrome.exe | GET | 200 | 72.21.91.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEArL3r5GW2bXOQUdsjjYAyg%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3388 | chrome.exe | 216.58.210.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3388 | chrome.exe | 216.58.207.74:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3388 | chrome.exe | 216.58.208.46:443 | ogs.google.com | Google Inc. | US | whitelisted |
3388 | chrome.exe | 216.58.206.4:443 | www.google.com | Google Inc. | US | whitelisted |
3388 | chrome.exe | 172.217.18.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
3388 | chrome.exe | 216.58.206.14:443 | apis.google.com | Google Inc. | US | whitelisted |
3388 | chrome.exe | 172.217.21.227:443 | www.google.ch | Google Inc. | US | whitelisted |
3388 | chrome.exe | 216.58.210.1:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3388 | chrome.exe | 173.194.160.74:80 | r5---sn-1gi7znes.gvt1.com | Google Inc. | US | whitelisted |
3388 | chrome.exe | 172.217.16.206:443 | docs.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
www.google.com |
| malicious |
www.google.ch |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2912 | WinRAR-sL0.pif | Generic Protocol Command Decode | SURICATA HTTP missing Host header |
2912 | WinRAR-sL0.pif | Generic Protocol Command Decode | SURICATA HTTP missing Host header |
2912 | WinRAR-sL0.pif | Generic Protocol Command Decode | SURICATA HTTP missing Host header |
2912 | WinRAR-sL0.pif | Generic Protocol Command Decode | SURICATA HTTP missing Host header |
2912 | WinRAR-sL0.pif | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
2912 | WinRAR-sL0.pif | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |