| URL: | http://www.msn.com |
| Full analysis: | https://app.any.run/tasks/7e33822e-b6a6-460e-a66a-910f0ec7ef27 |
| Verdict: | Malicious activity |
| Analysis date: | March 30, 2020, 10:45:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | FAEF515D875BD88076771963FC4DD672 |
| SHA1: | 53B140634551CFAC508A70649BB22242DB209613 |
| SHA256: | F99205789B2C74BD87F5D96159DB3C2E12A64C26D97BC0E5FF1025948362D0E7 |
| SSDEEP: | 3:N1KJS4fZI:Cc4hI |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
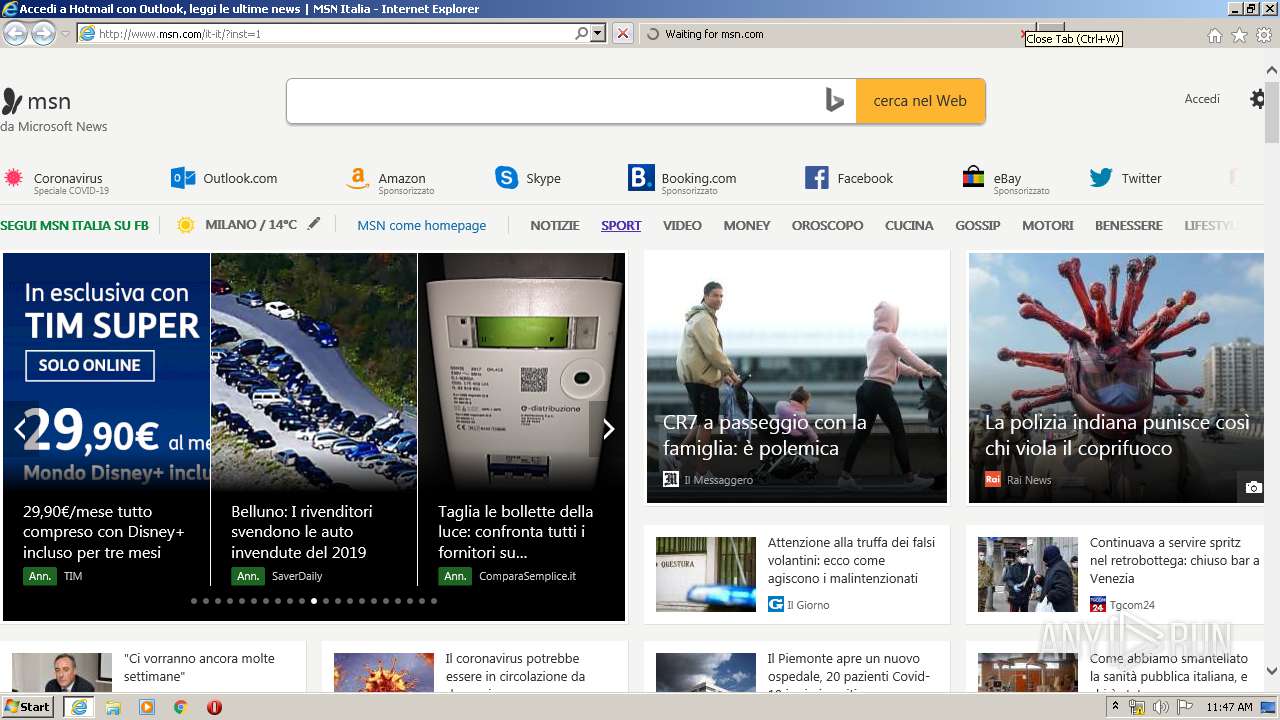
Application launched itself
- iexplore.exe (PID: 1756)
Reads Internet Cache Settings
- iexplore.exe (PID: 1756)
- iexplore.exe (PID: 3276)
- iexplore.exe (PID: 820)
- iexplore.exe (PID: 4076)
Changes internet zones settings
- iexplore.exe (PID: 1756)
Reads internet explorer settings
- iexplore.exe (PID: 3276)
- iexplore.exe (PID: 4076)
- iexplore.exe (PID: 820)
Creates files in the user directory
- iexplore.exe (PID: 820)
- iexplore.exe (PID: 3276)
Dropped object may contain TOR URL's
- iexplore.exe (PID: 820)
Drops Coronavirus (possible) decoy
- iexplore.exe (PID: 3276)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3276)
Reads settings of System Certificates
- iexplore.exe (PID: 820)
- iexplore.exe (PID: 1756)
- iexplore.exe (PID: 3276)
Changes settings of System certificates
- iexplore.exe (PID: 1756)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1756)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
42
Monitored processes
4
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 820 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1756 CREDAT:857455 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1756 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://www.msn.com" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3276 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1756 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 4076 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1756 CREDAT:922957 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
8 596
Read events
2 089
Write events
4 419
Delete events
2 088
Modification events
| (PID) Process: | (3276) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3276) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3276) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1756) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 1702257386 | |||
| (PID) Process: | (1756) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30803584 | |||
| (PID) Process: | (1756) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1756) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1756) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1756) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1756) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
Executable files
0
Suspicious files
246
Text files
523
Unknown types
116
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3276 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\HWYJH8NS.txt | — | |
MD5:— | SHA256:— | |||
| 3276 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\PANGYP2Q.txt | — | |
MD5:— | SHA256:— | |||
| 3276 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\it-it[1].htm | html | |
MD5:— | SHA256:— | |||
| 3276 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\a0-2fafeb-185735b[1].css | text | |
MD5:— | SHA256:— | |||
| 3276 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\optanon[1].css | text | |
MD5:— | SHA256:— | |||
| 3276 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\AAGpOUO[1].png | image | |
MD5:— | SHA256:— | |||
| 3276 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\4B41T6SL.txt | text | |
MD5:— | SHA256:— | |||
| 3276 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\BB11p0rL[1].png | image | |
MD5:— | SHA256:— | |||
| 3276 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\85-0f8009-68ddb2ab[1].js | text | |
MD5:— | SHA256:— | |||
| 3276 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\BBih5H[1].png | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
390
TCP/UDP connections
330
DNS requests
130
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3276 | iexplore.exe | GET | 302 | 204.79.197.203:80 | http://www.msn.com/ | US | html | 142 b | whitelisted |
3276 | iexplore.exe | GET | 200 | 204.79.197.203:80 | http://www.msn.com/it-it/ | US | html | 70.5 Kb | whitelisted |
3276 | iexplore.exe | GET | 200 | 23.55.161.132:80 | http://static-global-s-msn-com.akamaized.net/img-resizer/tenant/amp/entityid/BB11p0rL.img?h=27&w=27&m=6&q=60&u=t&o=t&l=f&f=png | US | image | 853 b | whitelisted |
3276 | iexplore.exe | GET | 200 | 23.55.161.132:80 | http://static-global-s-msn-com.akamaized.net/hp-neu/it-it/homepage/_sc/js/f60532dd-742bd05a/direction=ltr.locales=it-it.themes=start.dpi=resolution1x/97-9a8c47-68ddb2ab/f7-2496d1-74404b1e/a0-65444a-df7f4b68/e4-0588d3-68ddb2ab/4f-f5fbb9-fdcdb750/7e-a2fde3-e76dbcc3/9e-a7a255-68ddb2ab/a9-ac9b58-68ddb2ab/f1-d0c6aa-cae48929/c7-47822a-c5a8ebc8/1e-8f3fd7-3a62facd/ba-d94f83-68ddb2ab/fe-718b87-243aa040/ab-6050f7-19bd582/e4-cdb5df-67c9bea1/9e-639daf-68ddb2ab/85-0f8009-68ddb2ab?ver=20200325_22362463&fdhead=msnallexpusers,muidflt12cf,muidflt47cf,muidflt50cf,muidflt258cf,mmxandroid1cf,platagyedge2cf,moneyedge1cf,moneyedge3cf,rtbhptaba,bingcollabhz1cf,onetrustpoplive,jslltelemetry,1s-feed-next-v1,1s-bing-news,ie11topsites-c&csopd=20200324194617&csopdb=20200323033615 | US | text | 123 Kb | whitelisted |
3276 | iexplore.exe | GET | 200 | 23.55.161.132:80 | http://static-global-s-msn-com.akamaized.net/img-resizer/tenant/amp/entityid/AAGpOUO.img?h=27&w=27&m=6&q=60&u=t&o=t&l=f&f=png | US | image | 347 b | whitelisted |
3276 | iexplore.exe | GET | 200 | 23.55.161.132:80 | http://static-global-s-msn-com.akamaized.net/hp-neu/_h/a1438951/webcore/externalscripts/oneTrust/skins/default_flat_top_two_button_black/v2/css/optanon.css | US | text | 5.40 Kb | whitelisted |
3276 | iexplore.exe | GET | 200 | 23.55.161.132:80 | http://static-global-s-msn-com.akamaized.net/img-resizer/tenant/amp/entityid/BBih5H.img?m=6&o=true&u=true&n=true&w=30&h=30 | US | image | 930 b | whitelisted |
3276 | iexplore.exe | GET | 200 | 23.55.161.132:80 | http://static-global-s-msn-com.akamaized.net/img-resizer/tenant/amp/entityid/BB11TKAF.img?h=333&w=311&m=6&q=60&u=t&o=t&l=f&f=jpg&x=819&y=1048 | US | image | 10.8 Kb | whitelisted |
3276 | iexplore.exe | GET | 200 | 23.55.161.132:80 | http://static-global-s-msn-com.akamaized.net/img-resizer/tenant/amp/entityid/BB11TcYE.img?h=166&w=310&m=6&q=60&u=t&o=t&l=f&f=jpg&x=2161&y=1441 | US | image | 8.56 Kb | whitelisted |
3276 | iexplore.exe | GET | 200 | 23.55.161.132:80 | http://static-global-s-msn-com.akamaized.net/hp-neu/_h/b71c72b5/webcore/externalscripts/oneTrust/it-it/onetrustConsent.js | US | text | 48.4 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3276 | iexplore.exe | 40.77.226.250:443 | web.vortex.data.msn.com | Microsoft Corporation | IE | whitelisted |
3276 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1756 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3276 | iexplore.exe | 23.55.161.132:80 | static-global-s-msn-com.akamaized.net | Akamai International B.V. | US | whitelisted |
3276 | iexplore.exe | 204.79.197.203:443 | www.msn.com | Microsoft Corporation | US | malicious |
3276 | iexplore.exe | 87.248.118.22:443 | s.yimg.com | Yahoo! UK Services Limited | GB | shared |
3276 | iexplore.exe | 152.199.19.160:80 | mscrl.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3276 | iexplore.exe | 216.58.210.3:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3276 | iexplore.exe | 104.18.21.226:80 | ocsp.globalsign.com | Cloudflare Inc | US | shared |
3276 | iexplore.exe | 23.55.161.135:80 | static-global-s-msn-com.akamaized.net | Akamai International B.V. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
static-global-s-msn-com.akamaized.net |
| whitelisted |
linkmaker.itunes.apple.com |
| whitelisted |
play.google.com |
| whitelisted |
web.vortex.data.msn.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ocsp.msocsp.com |
| whitelisted |
api.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3276 | iexplore.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
1756 | iexplore.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
3276 | iexplore.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |