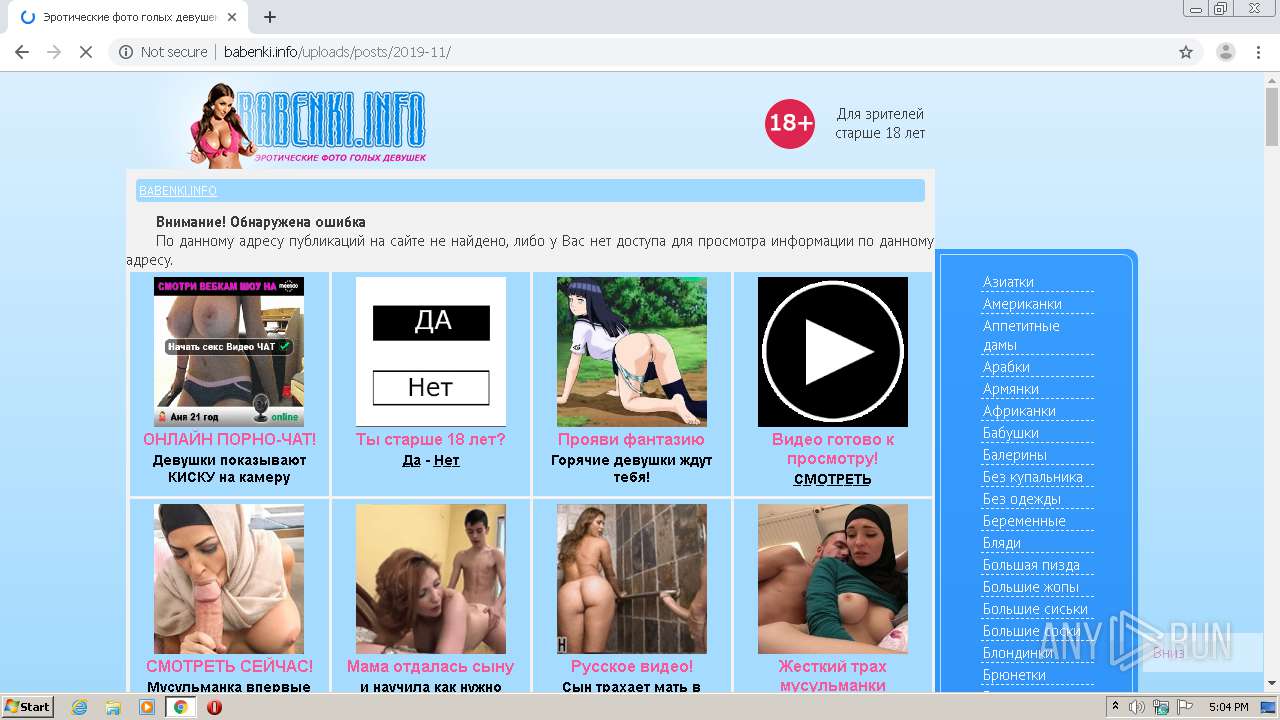
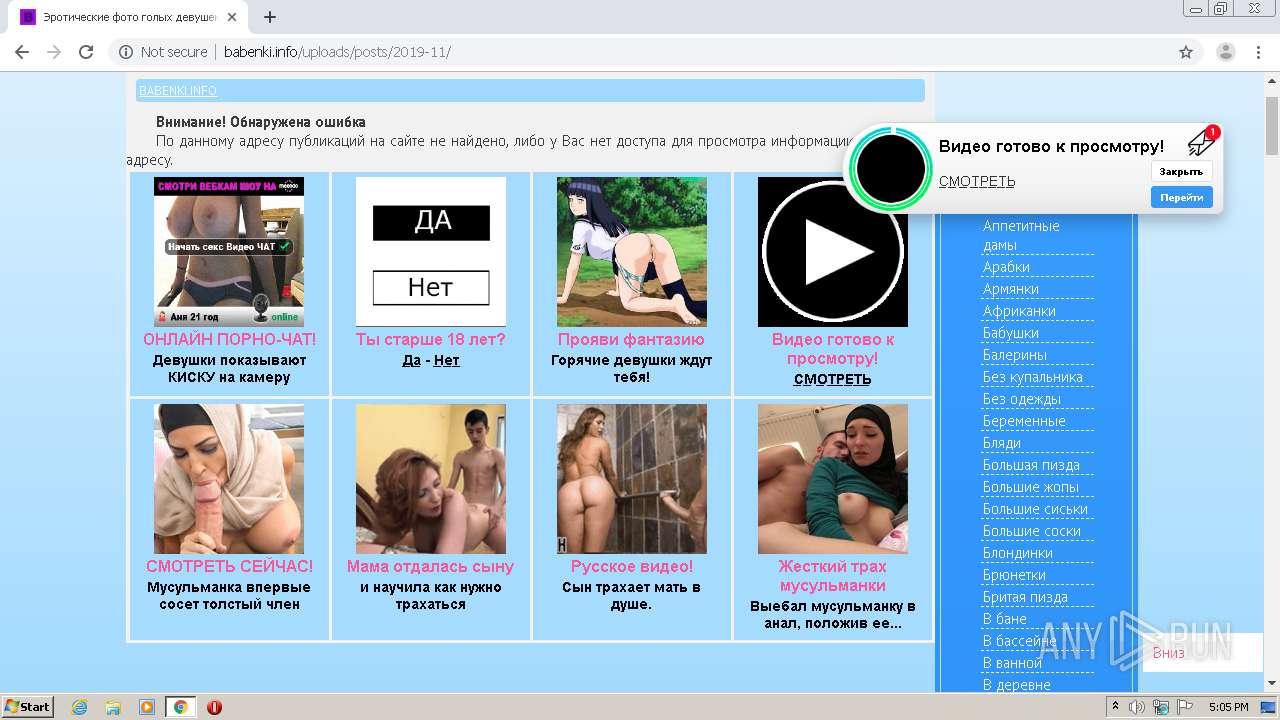
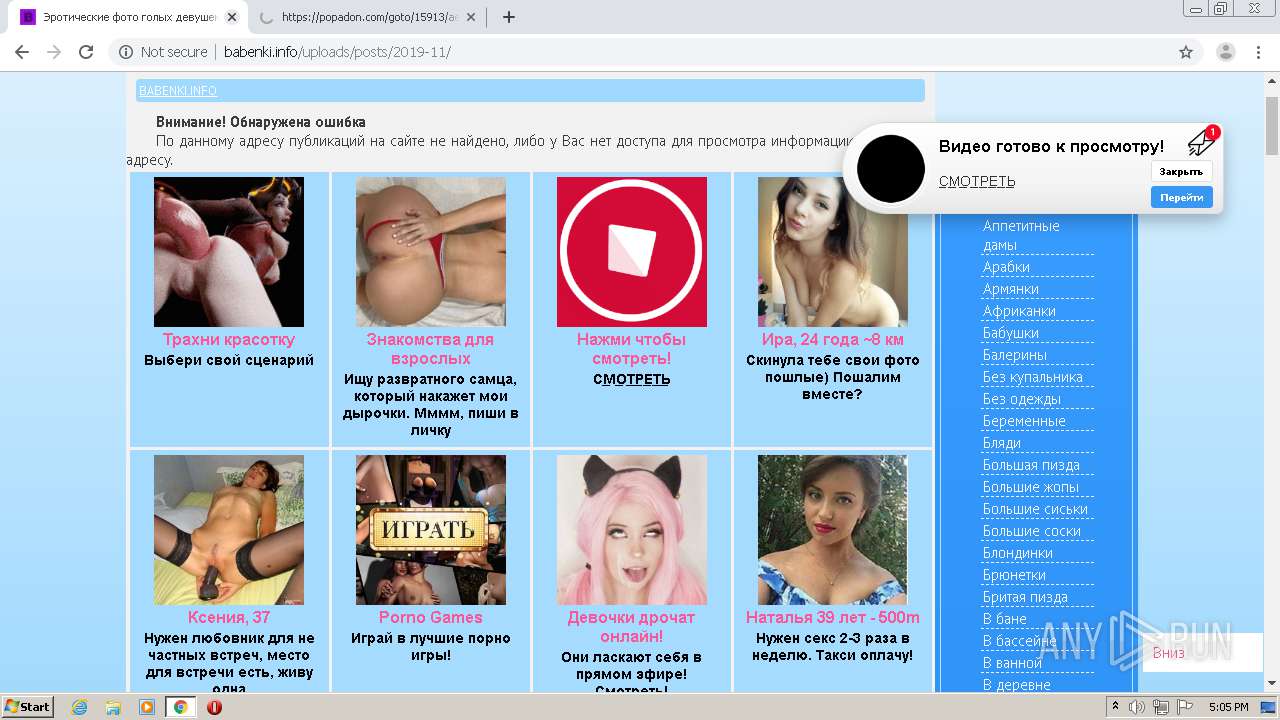
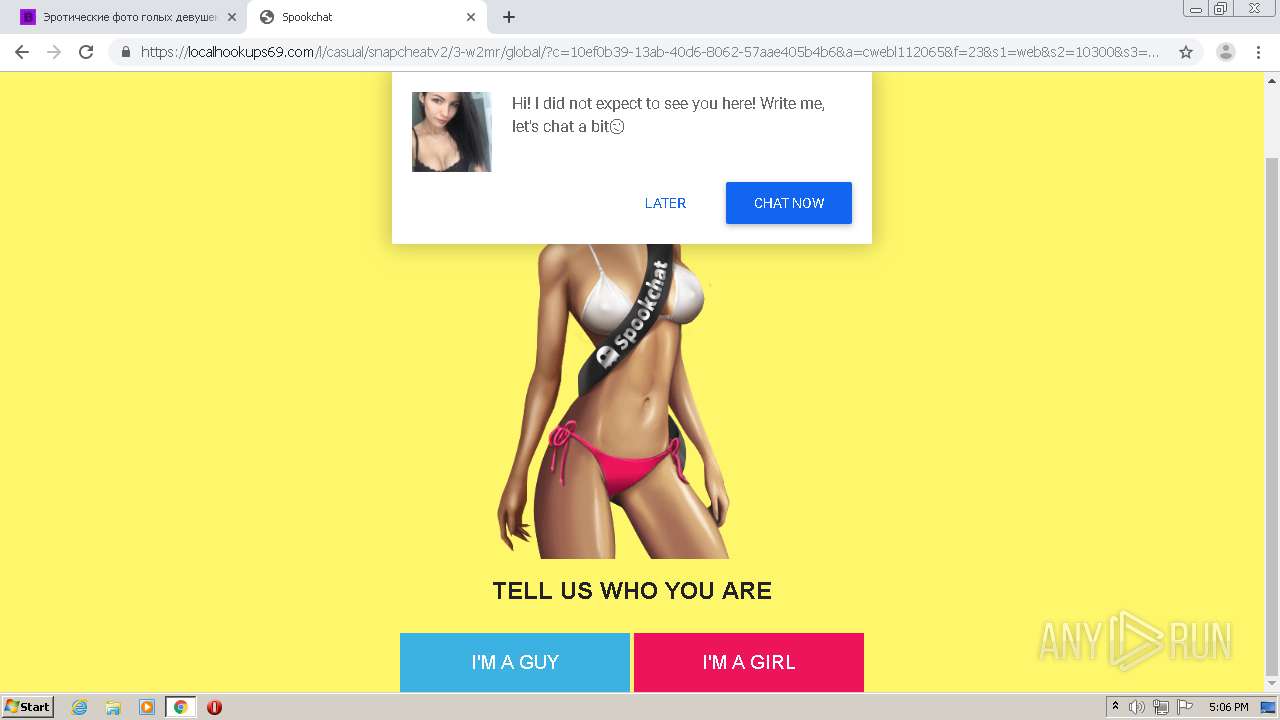
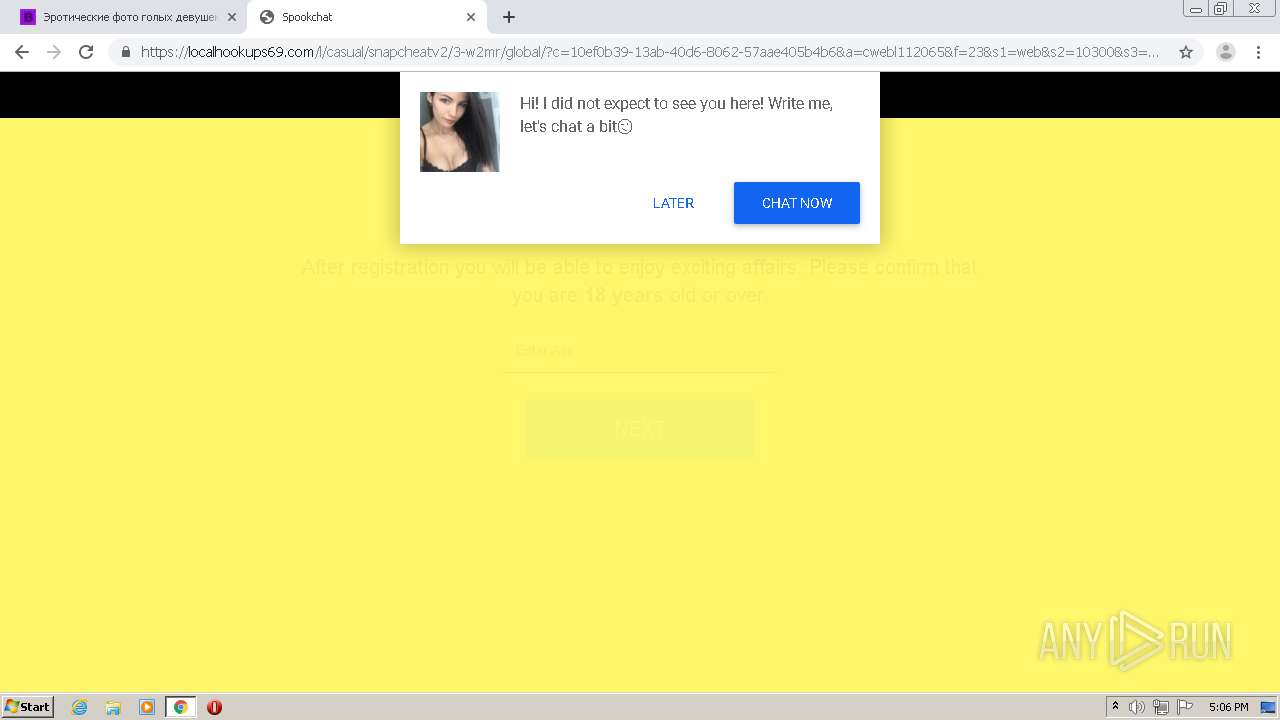
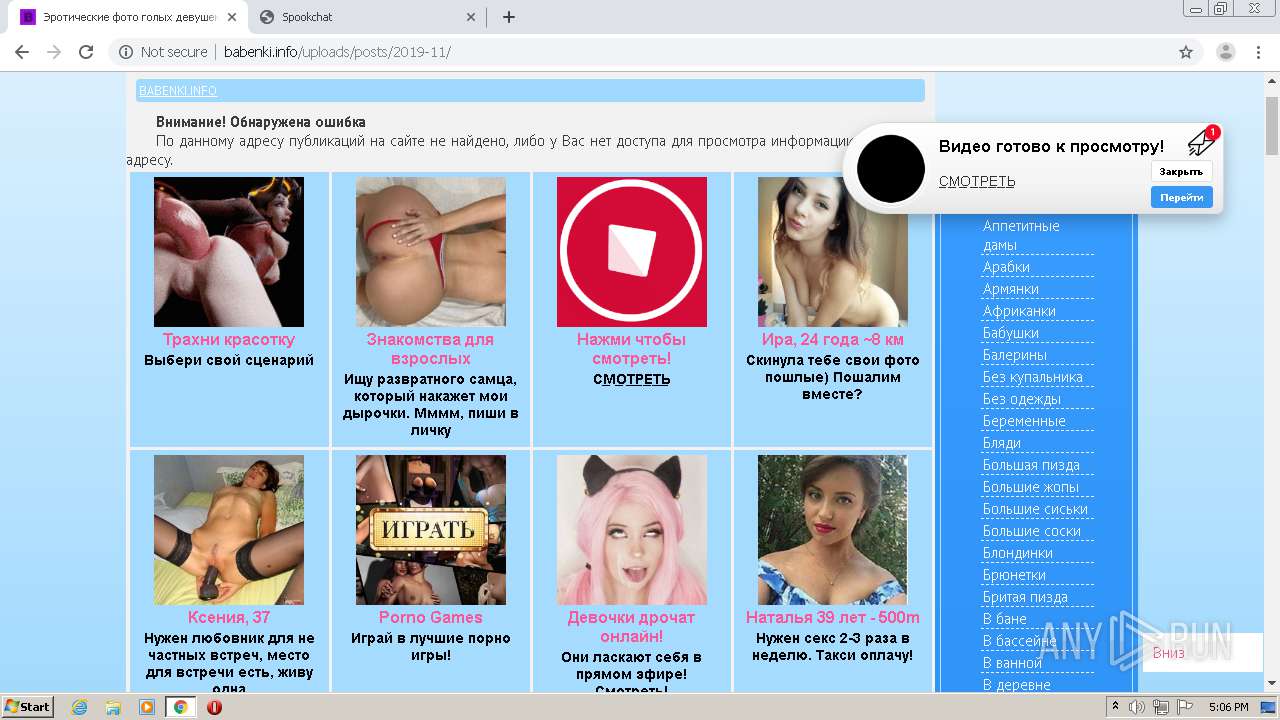
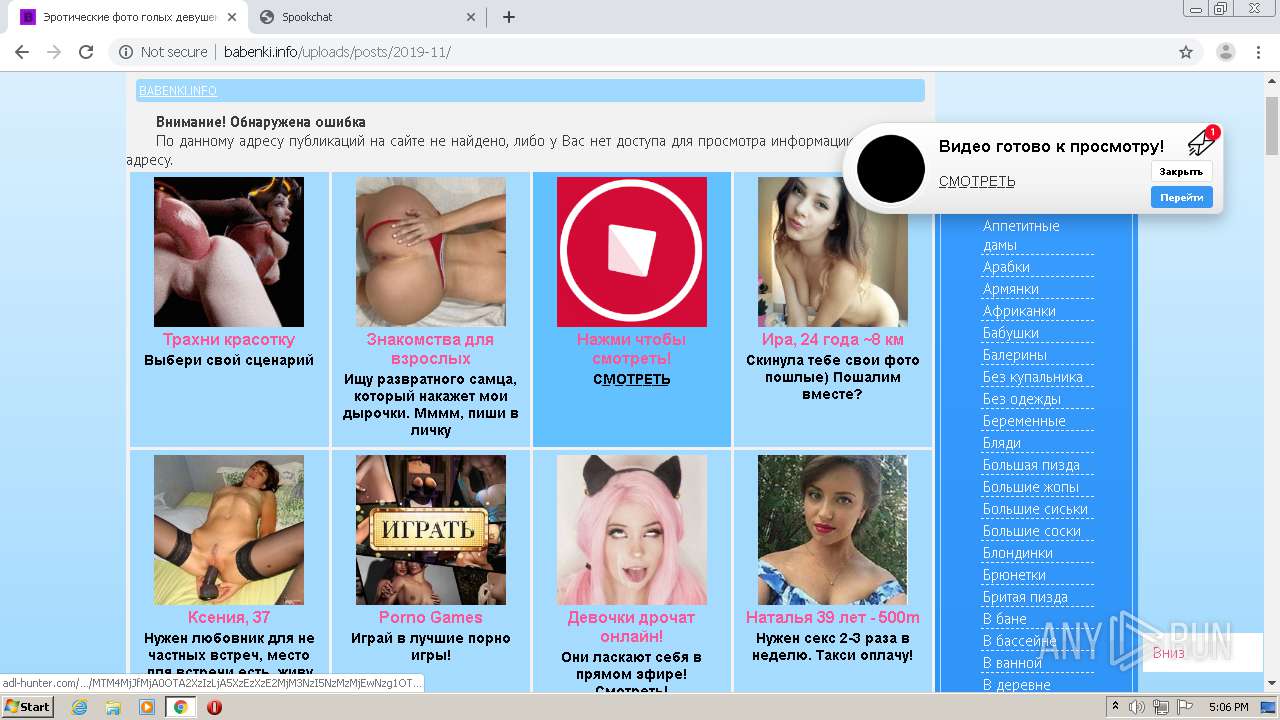
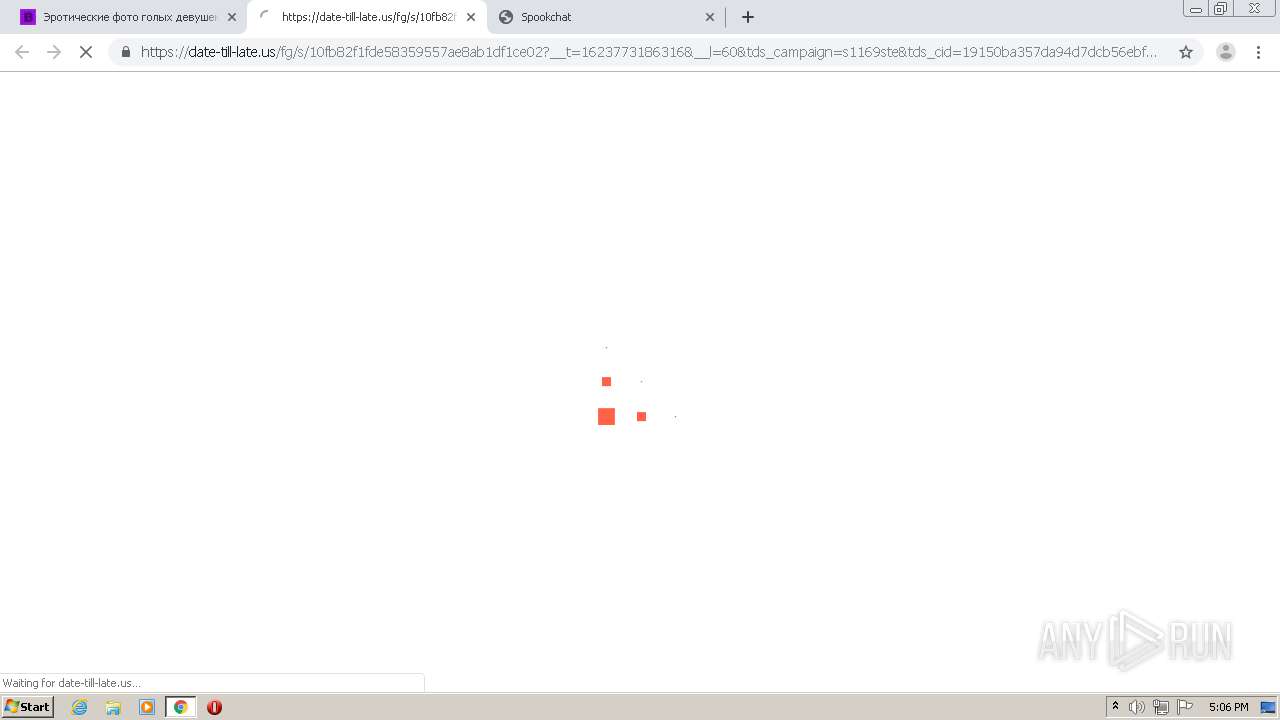
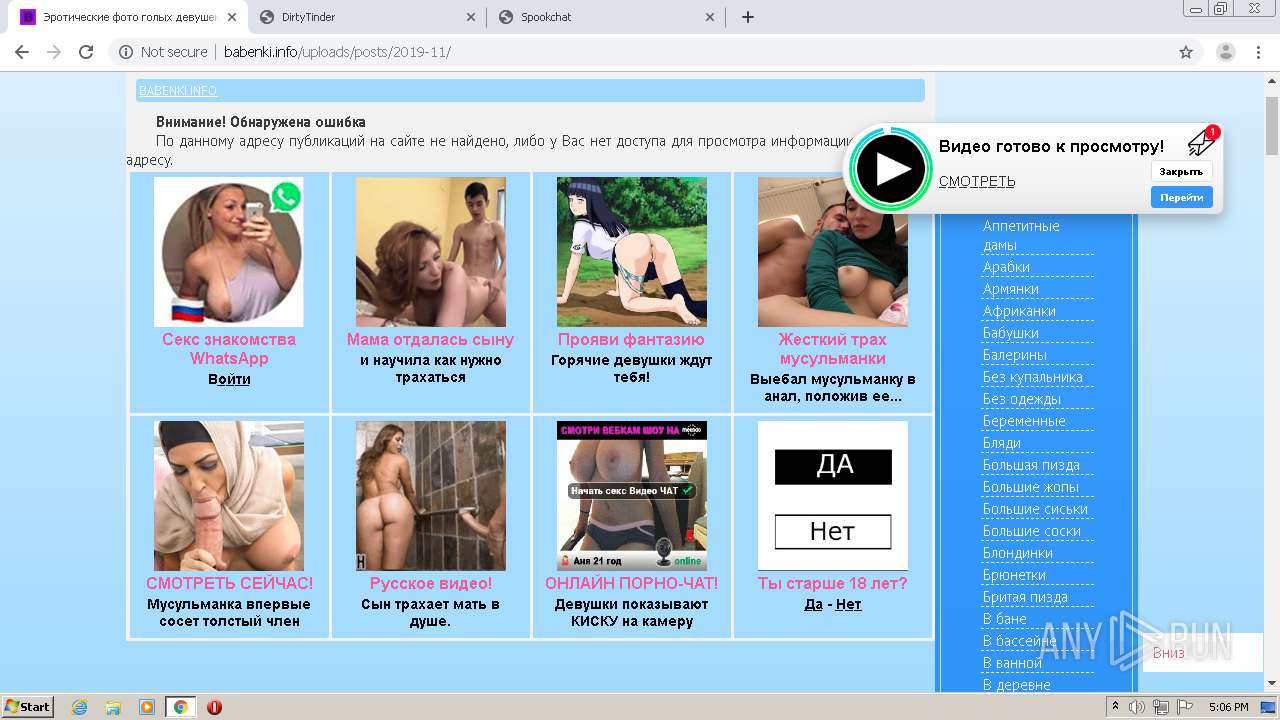
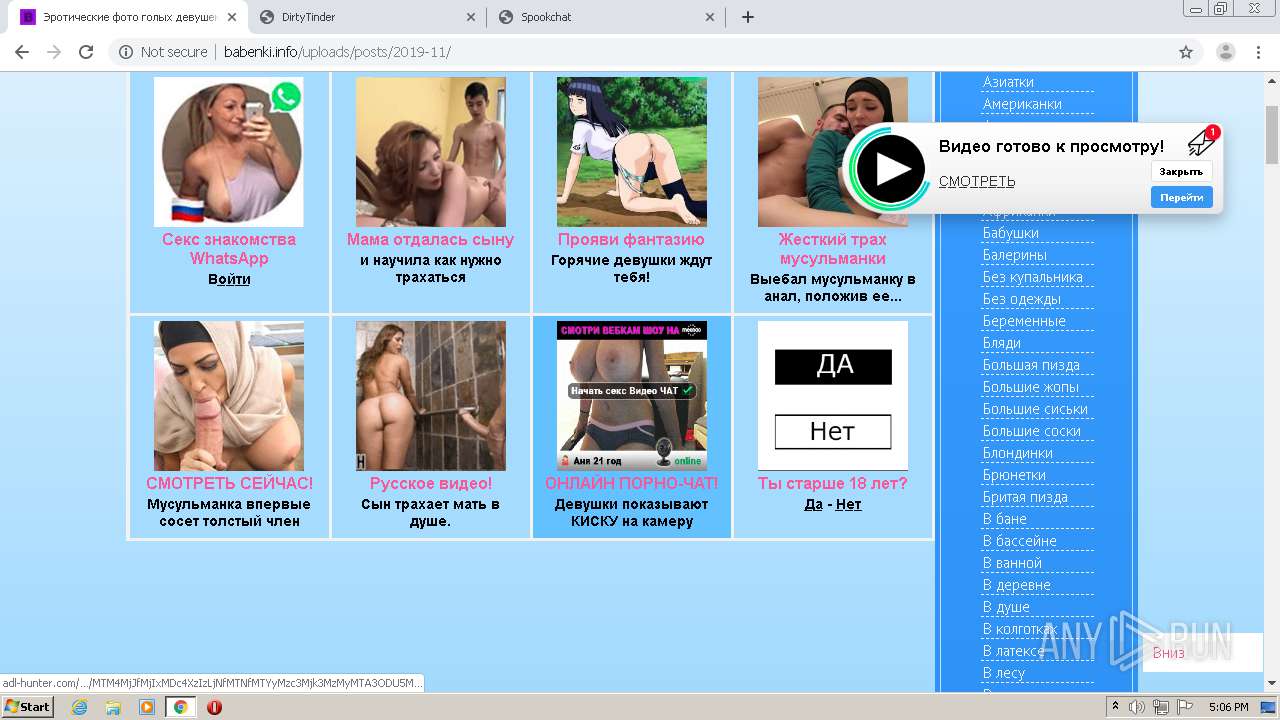
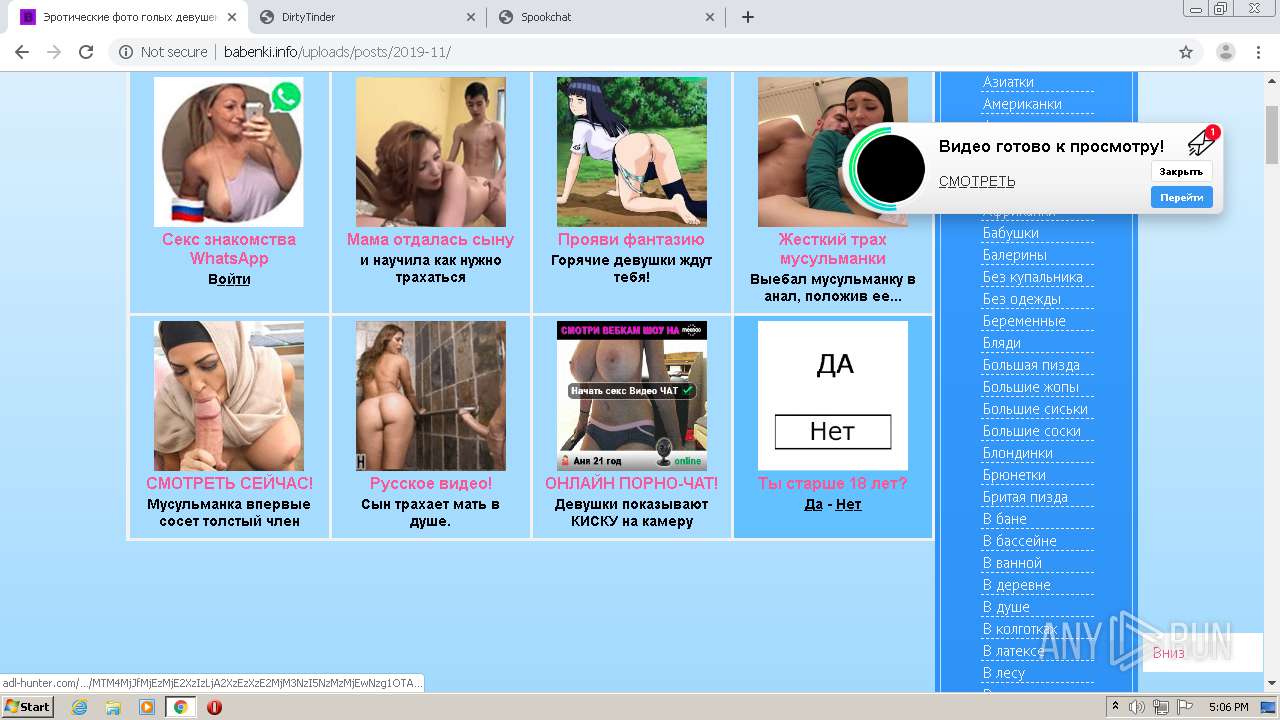
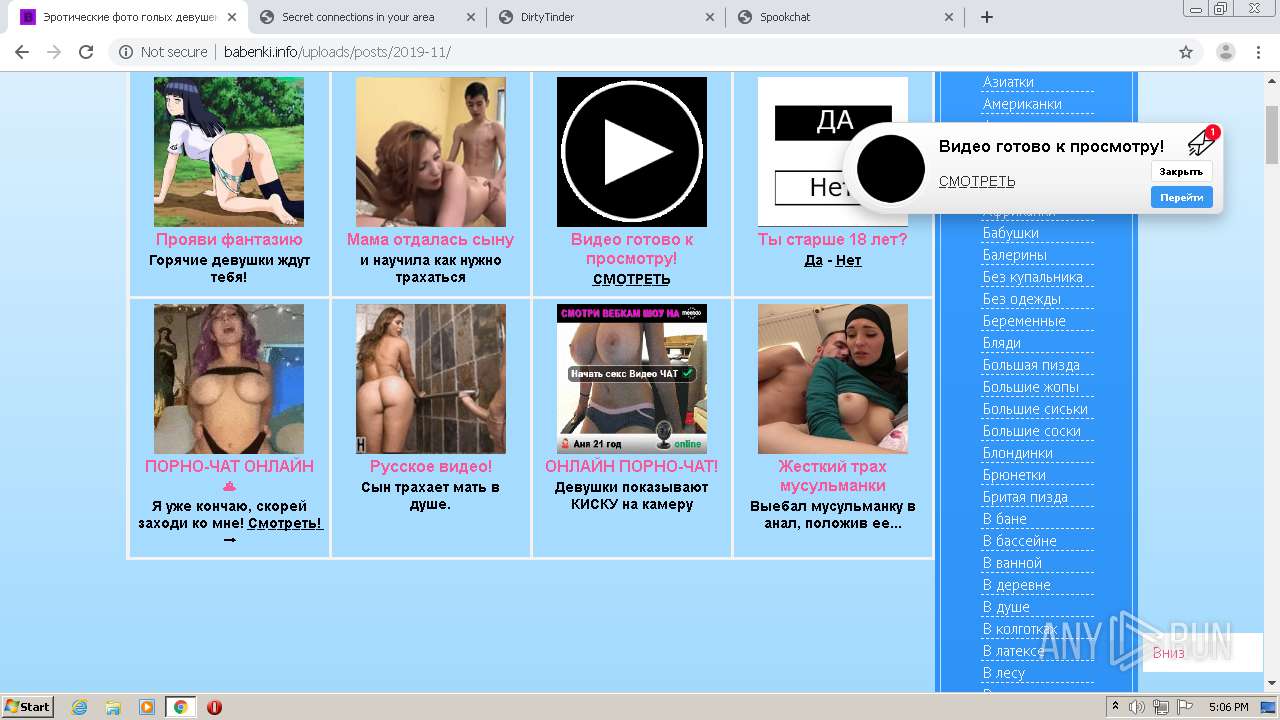
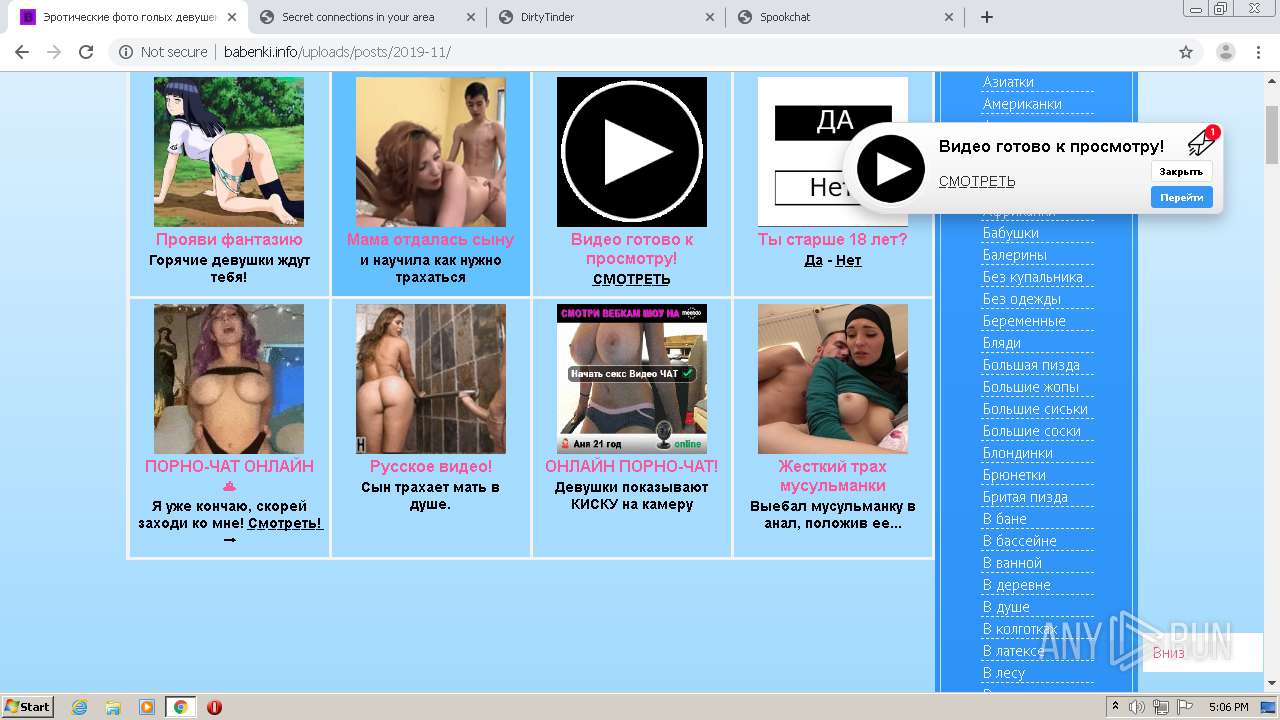
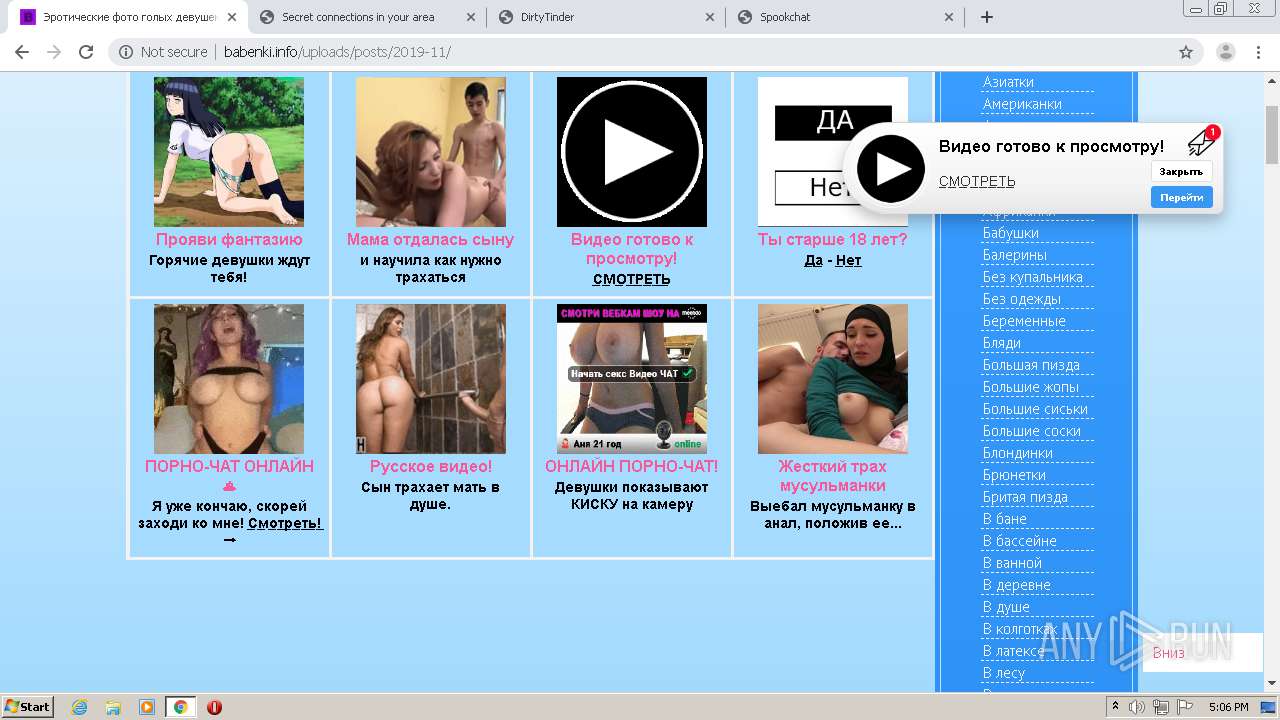
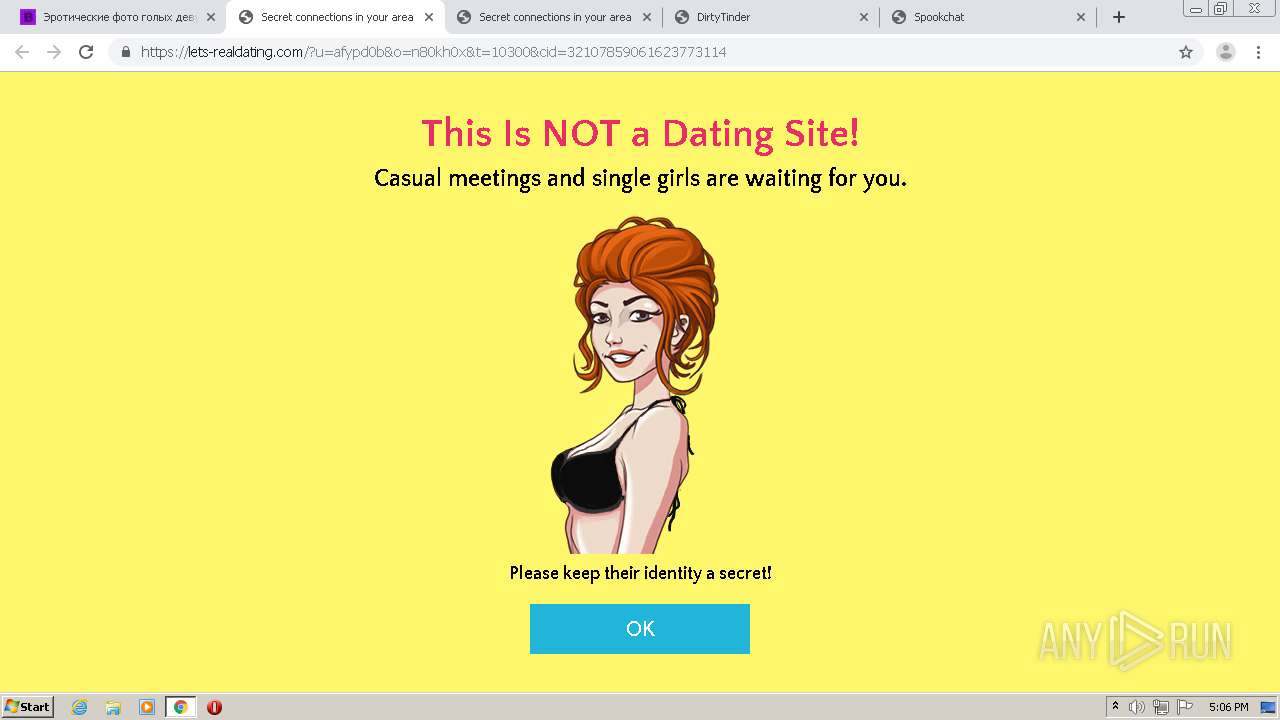
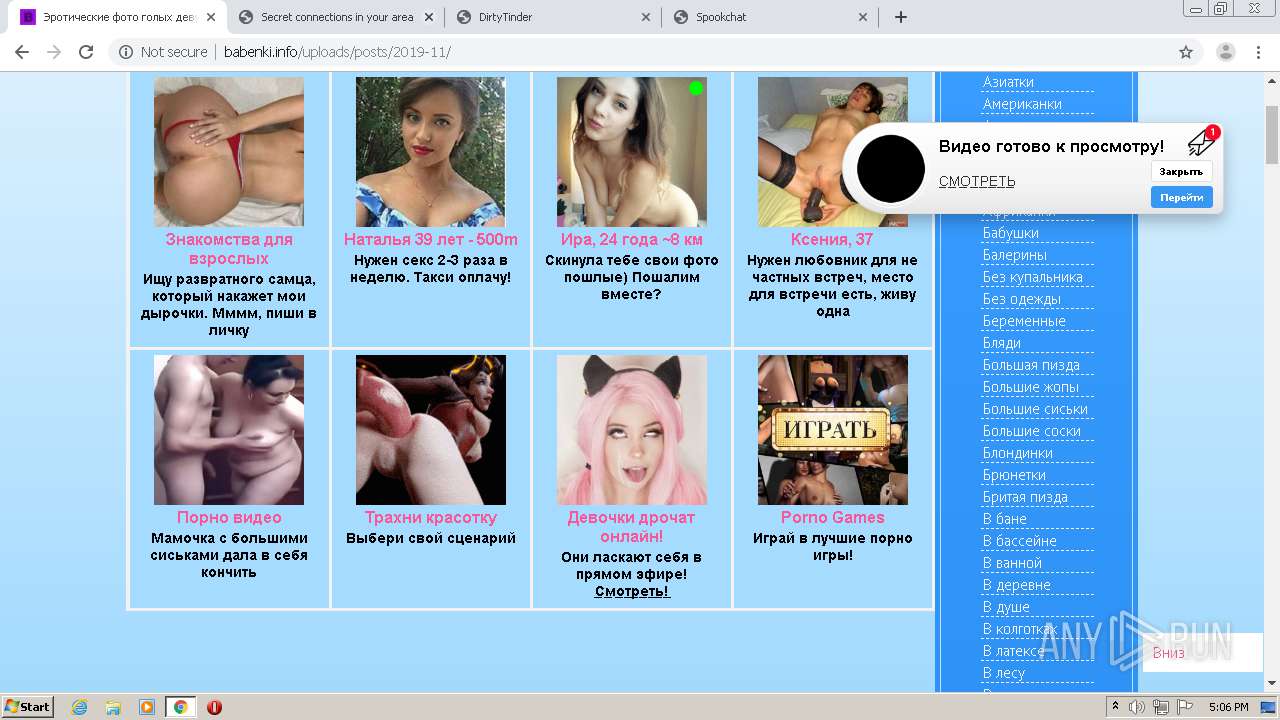
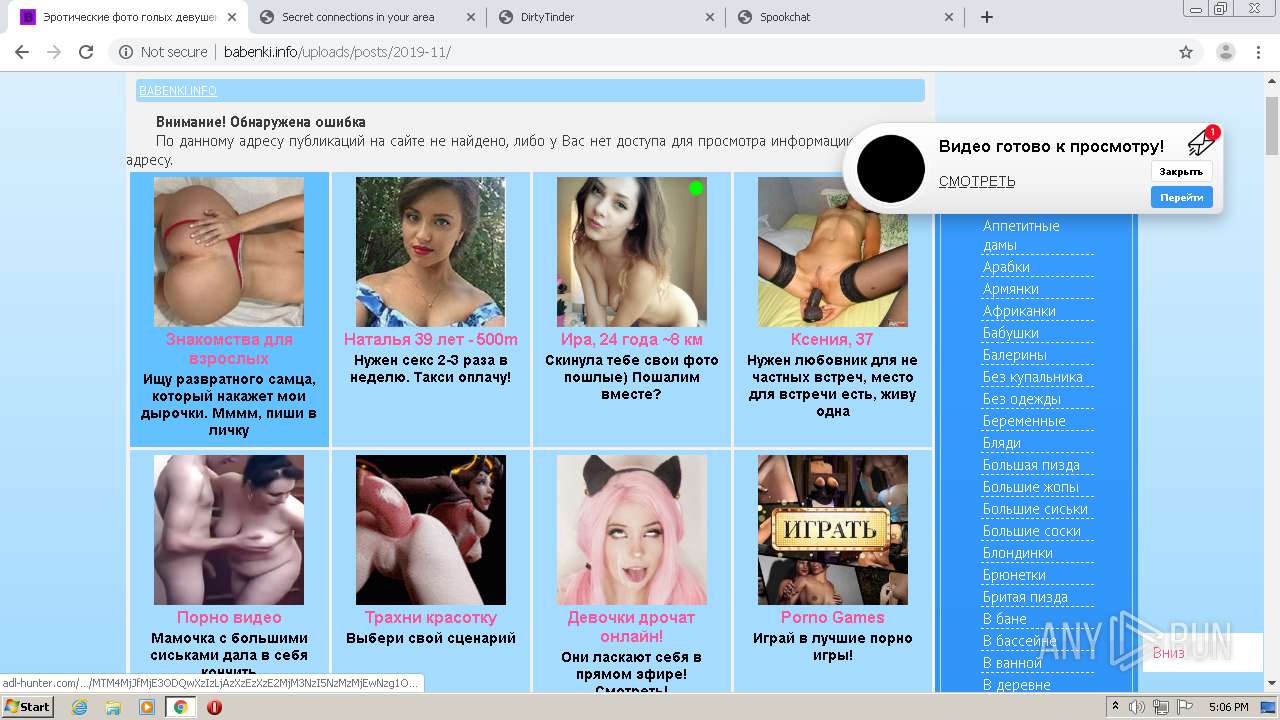
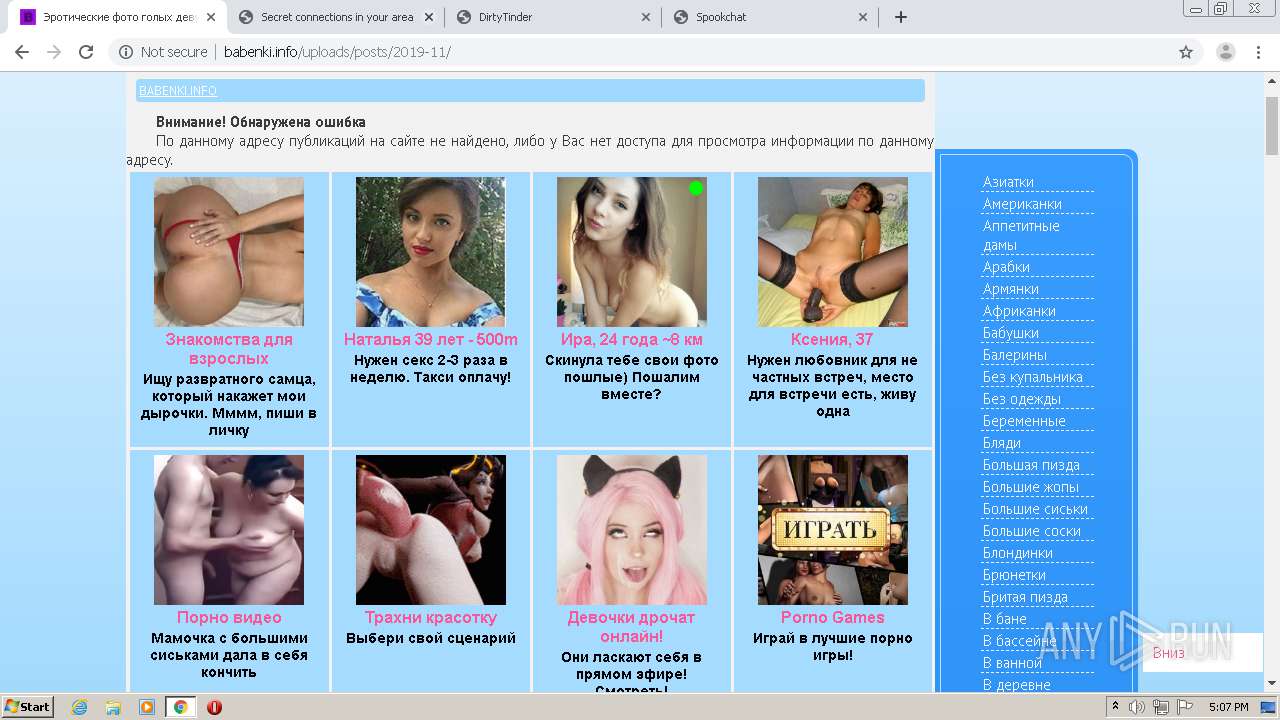
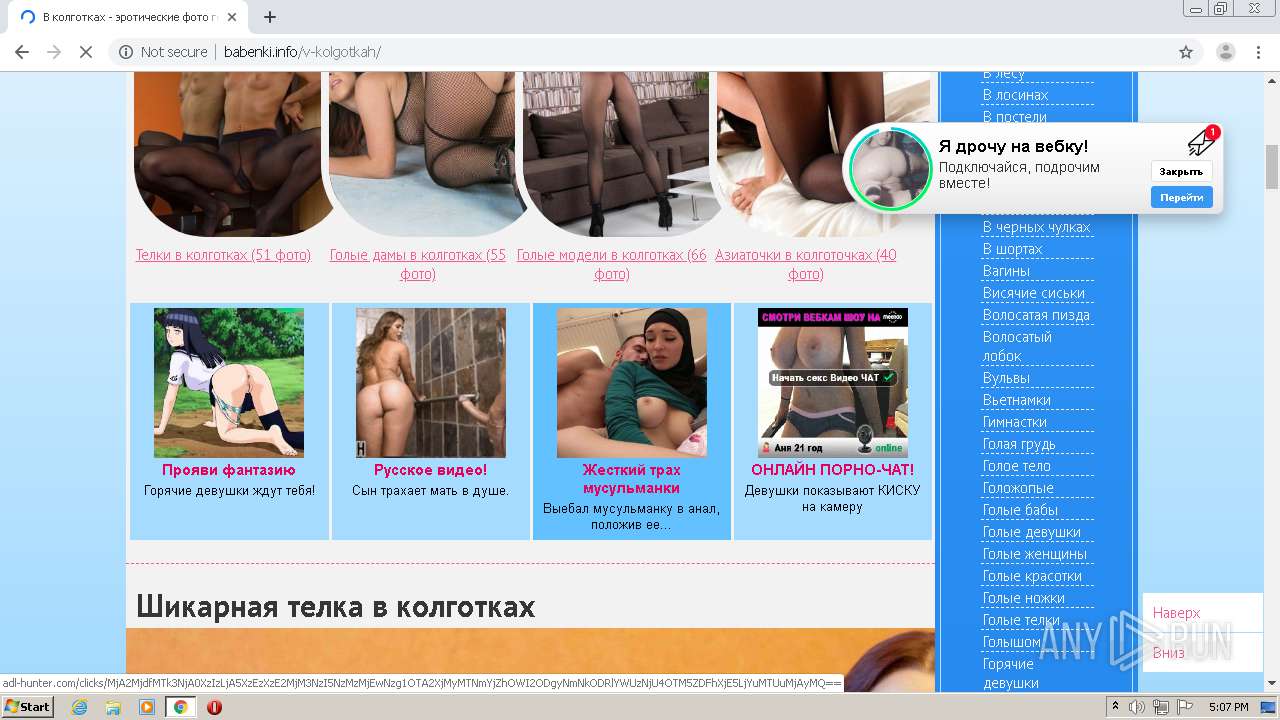
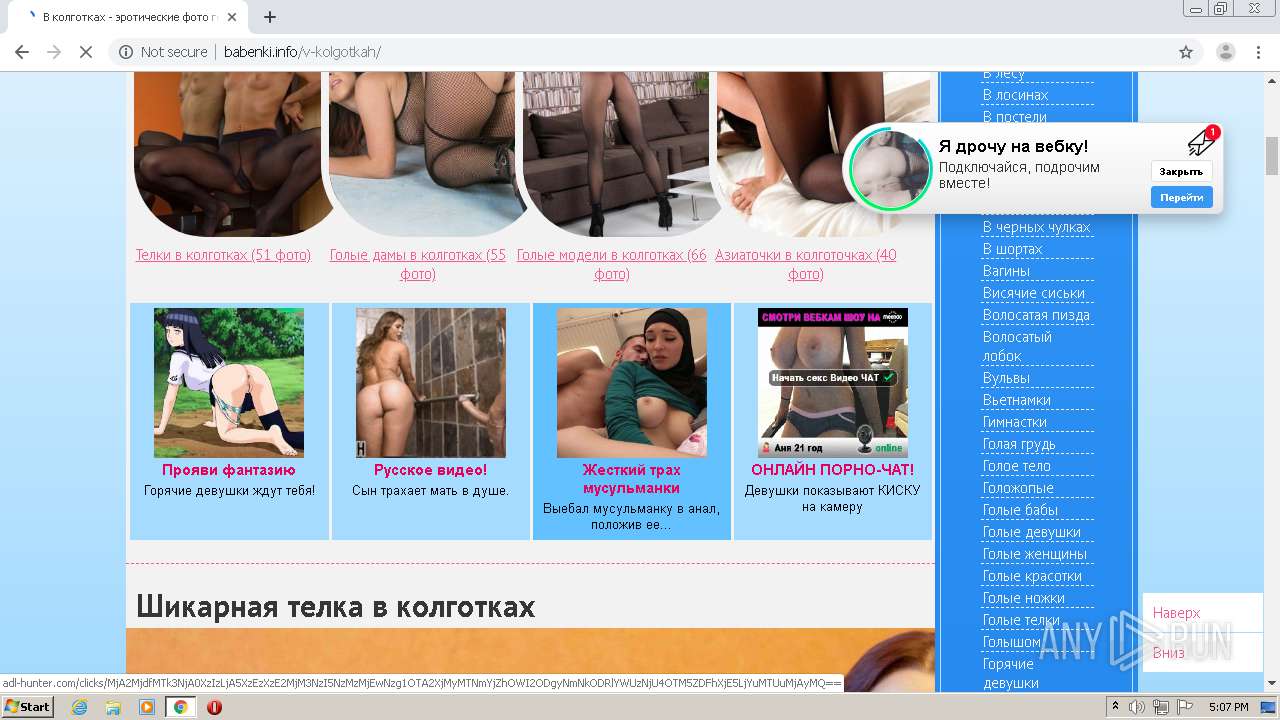
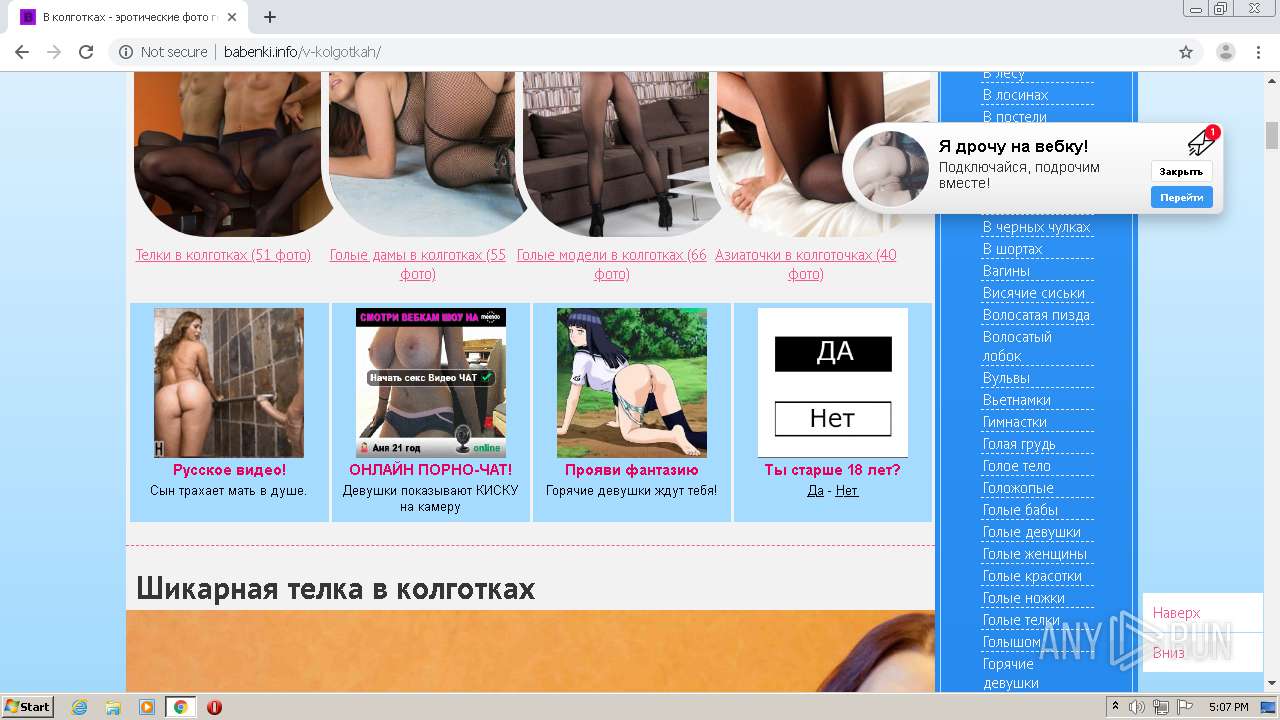
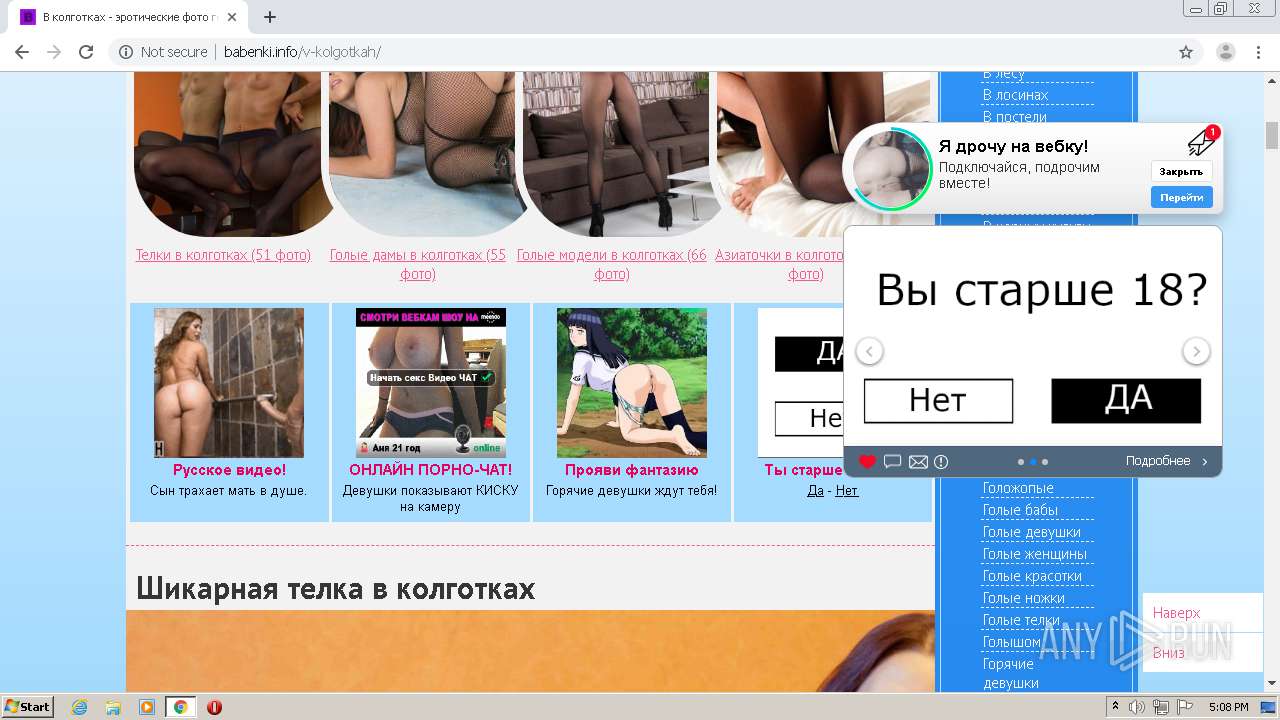
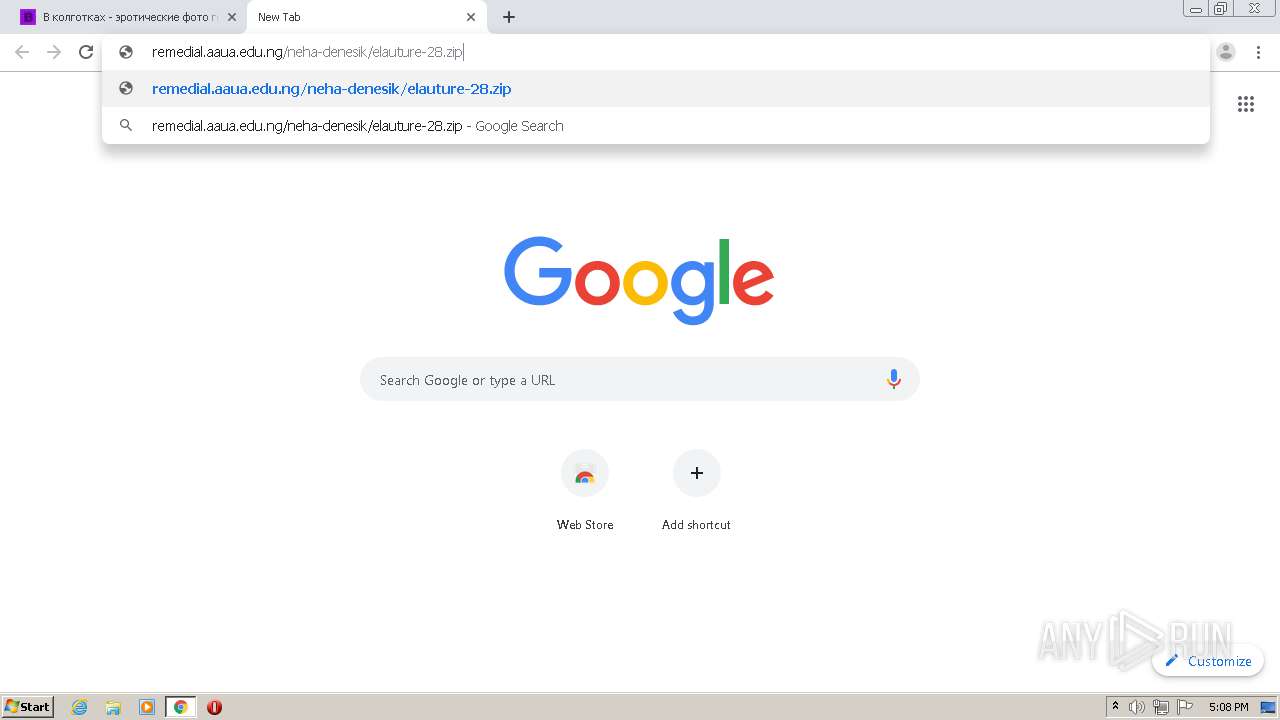
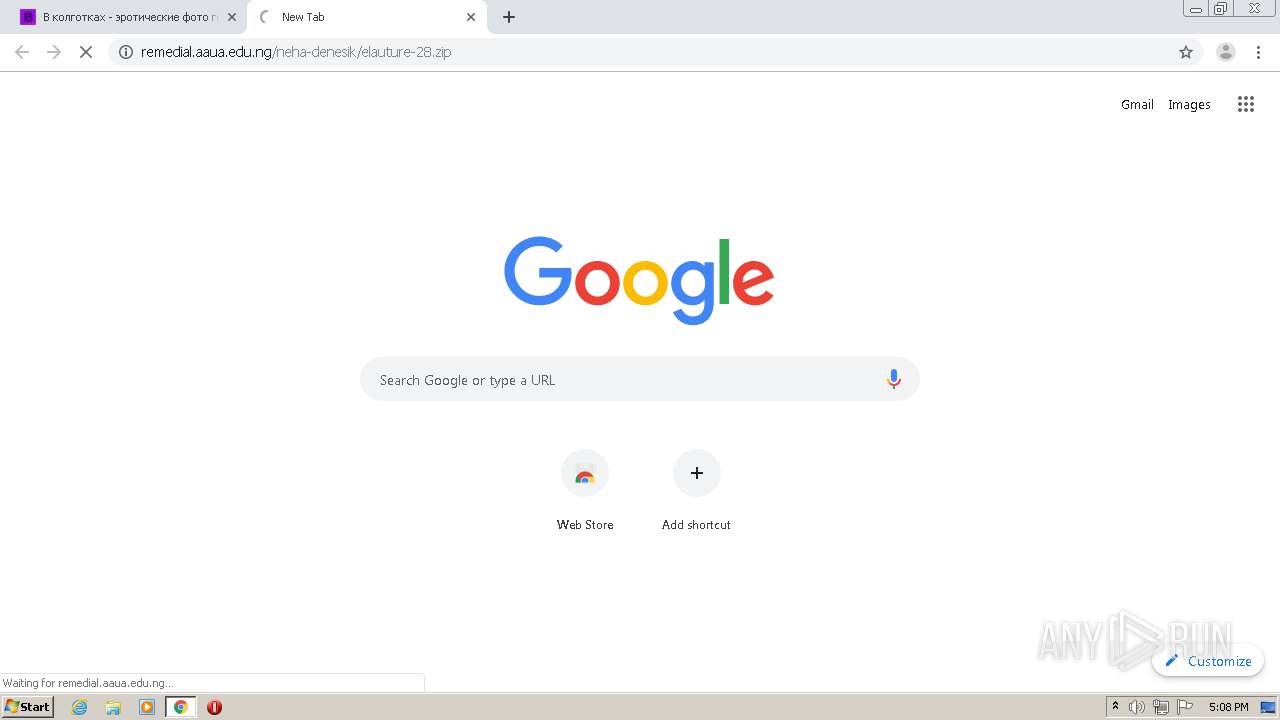
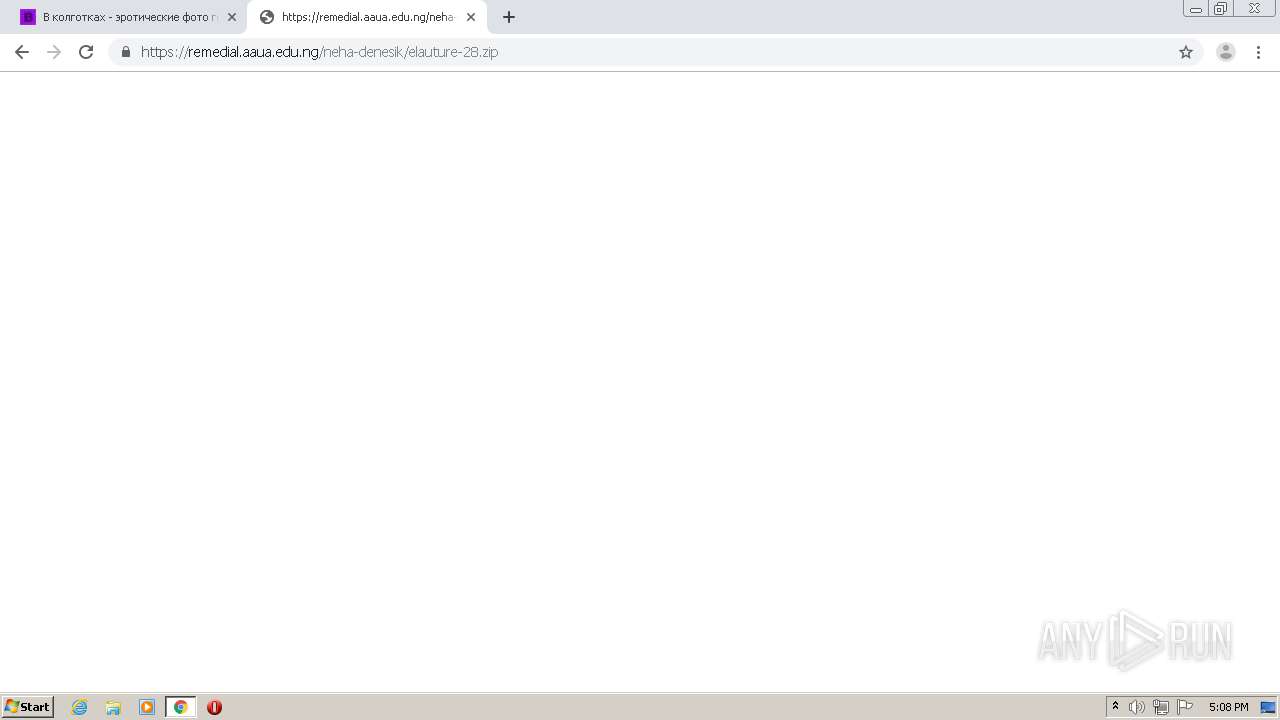
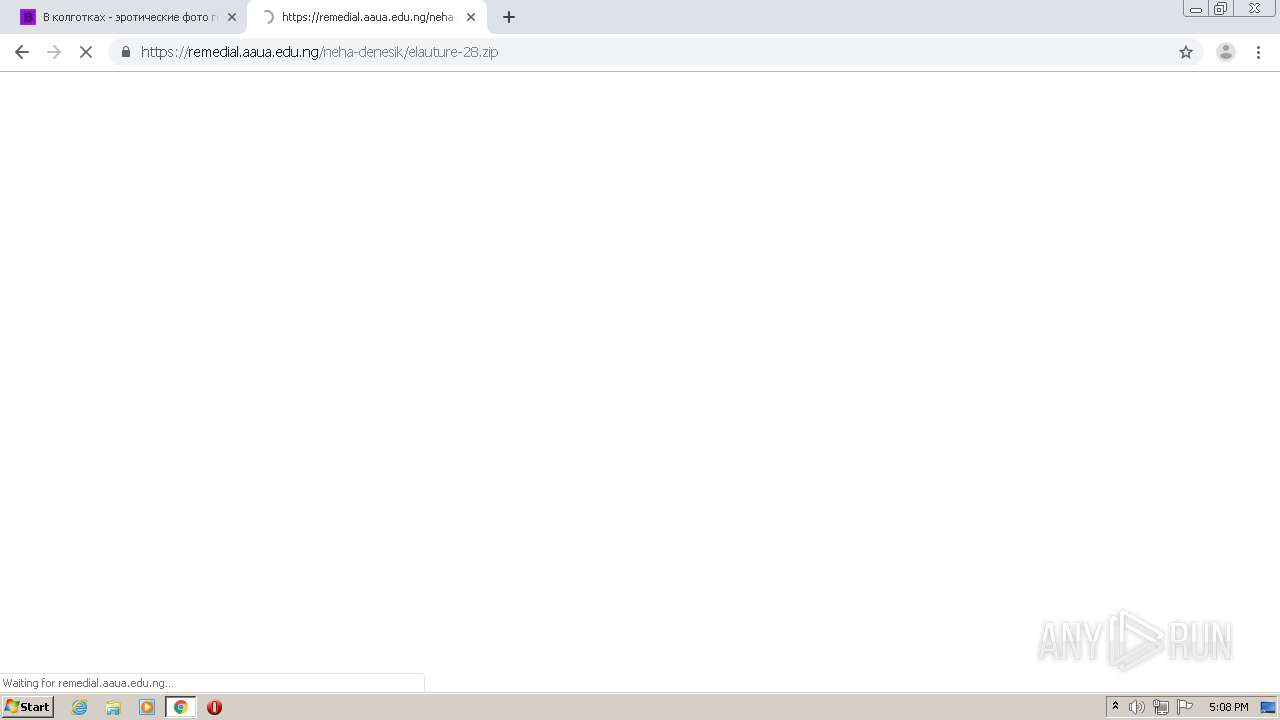
| URL: | http://babenki.info/uploads/posts/2019-11/1574851101_selfi-golyh-devushek-erotika-penthous-21.jpg |
| Full analysis: | https://app.any.run/tasks/878ddce4-c9e5-4901-a1a7-a341b9fc69c2 |
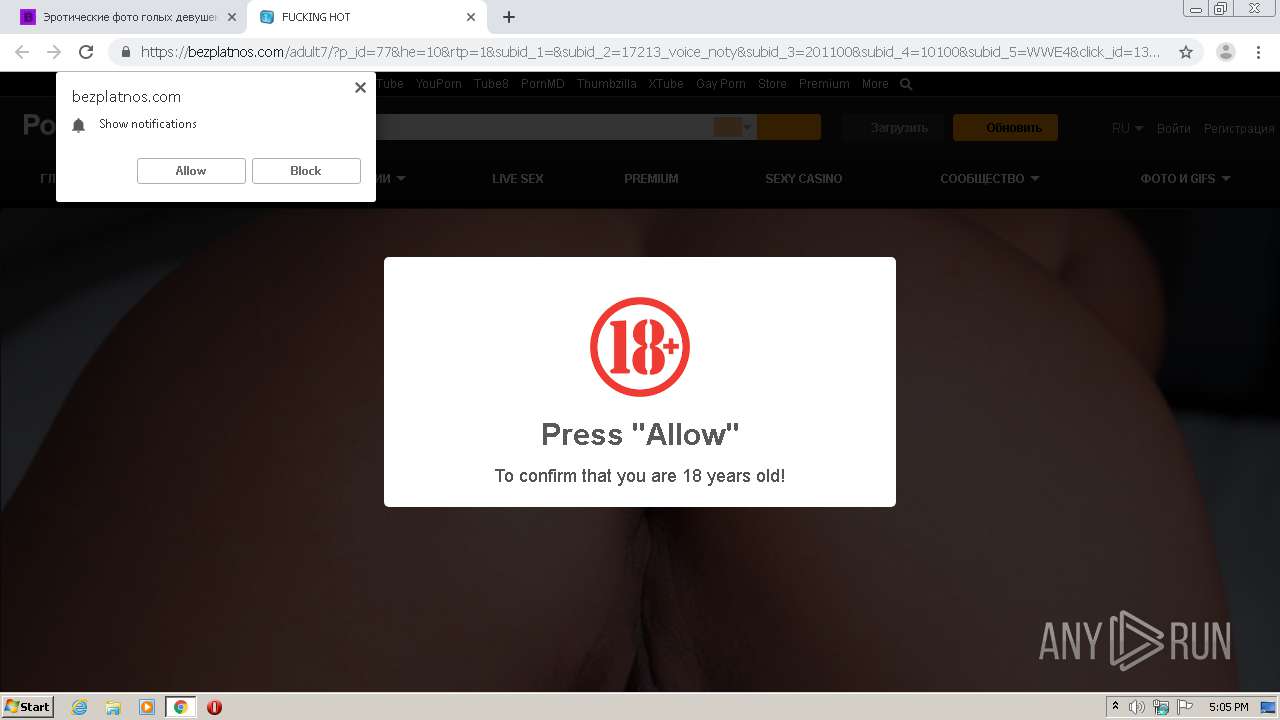
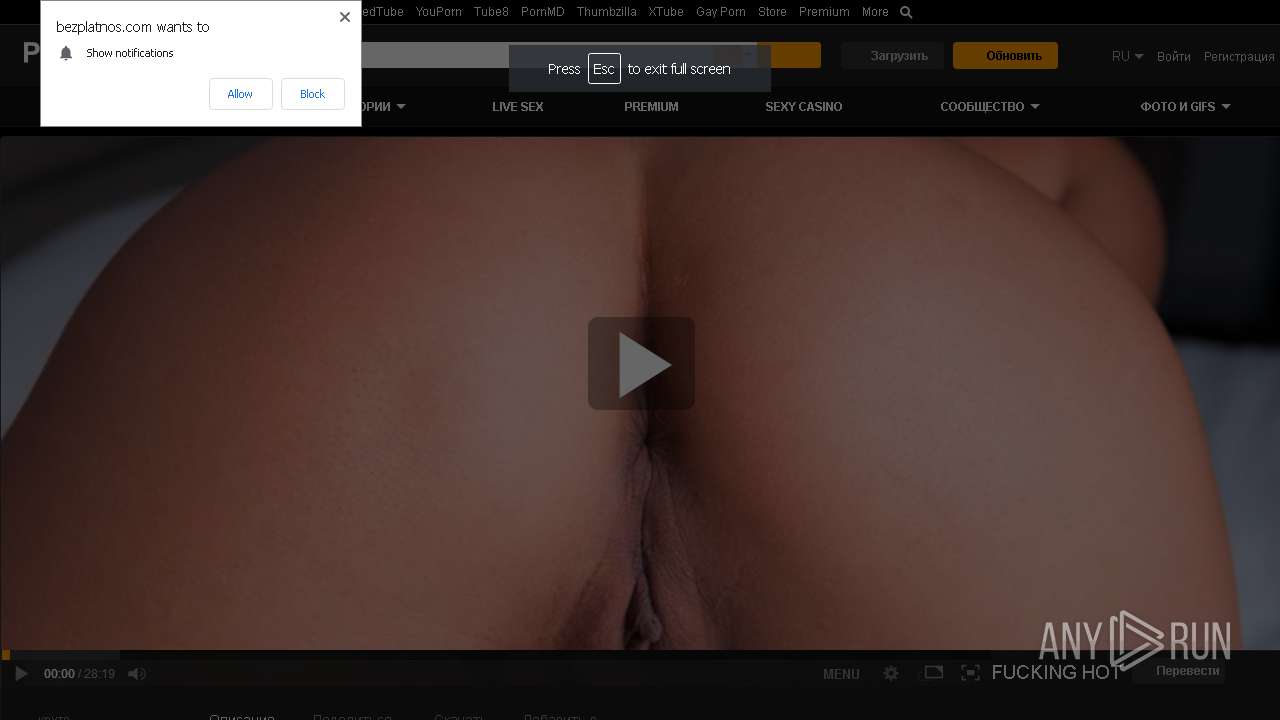
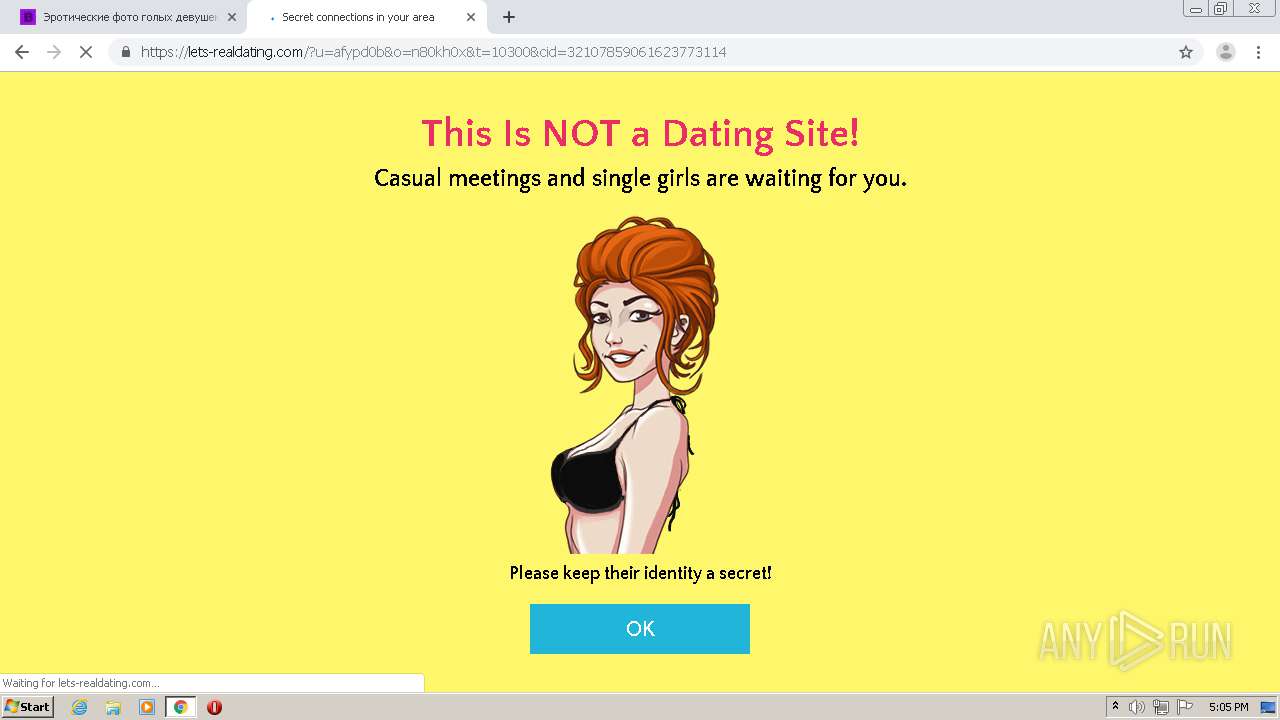
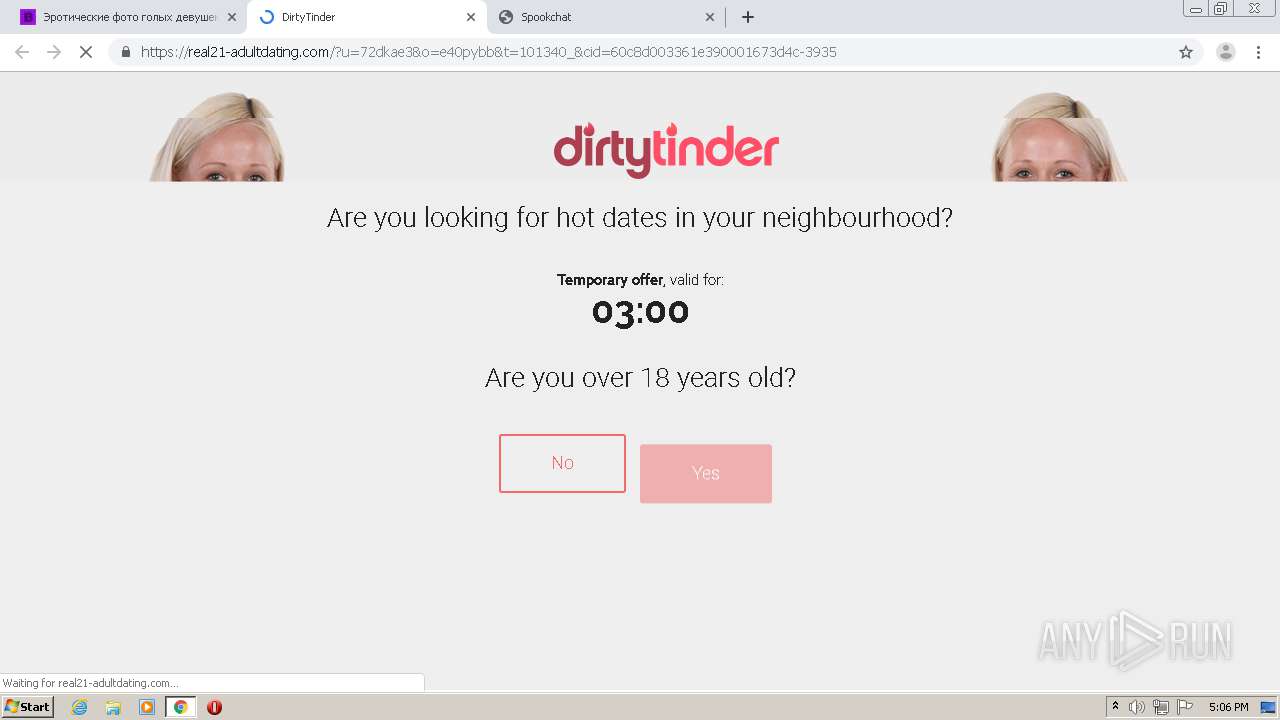
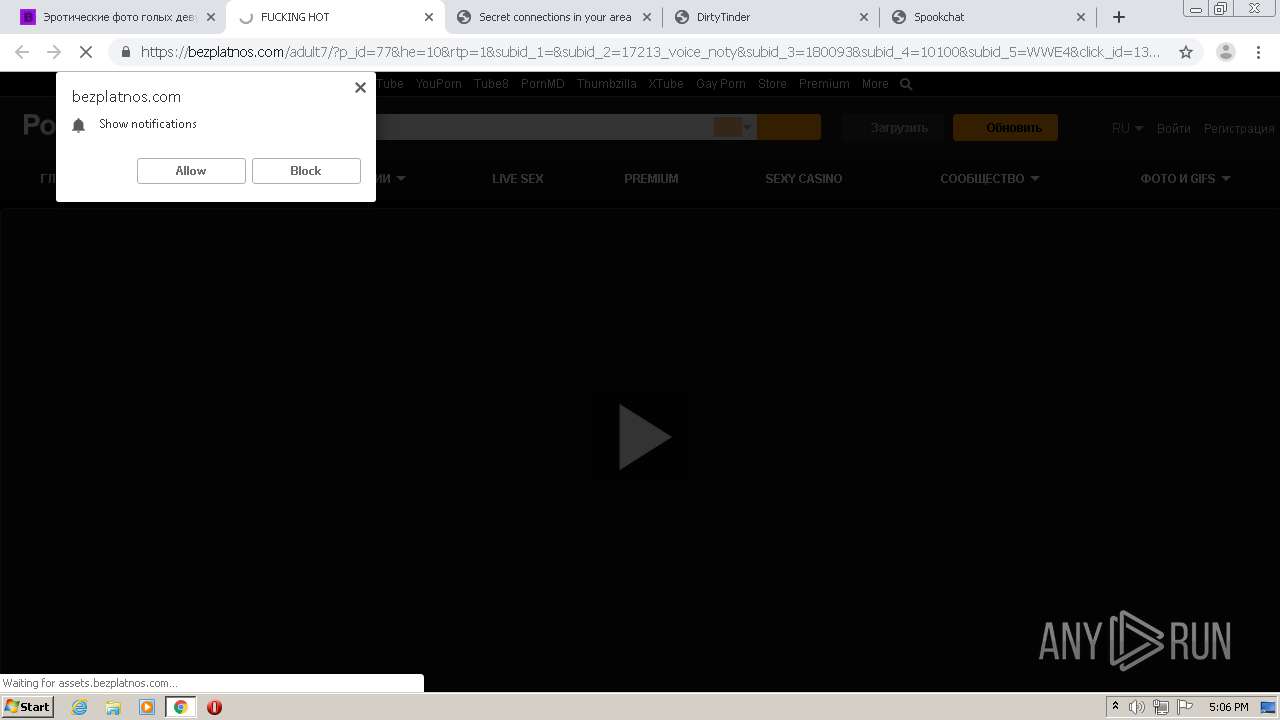
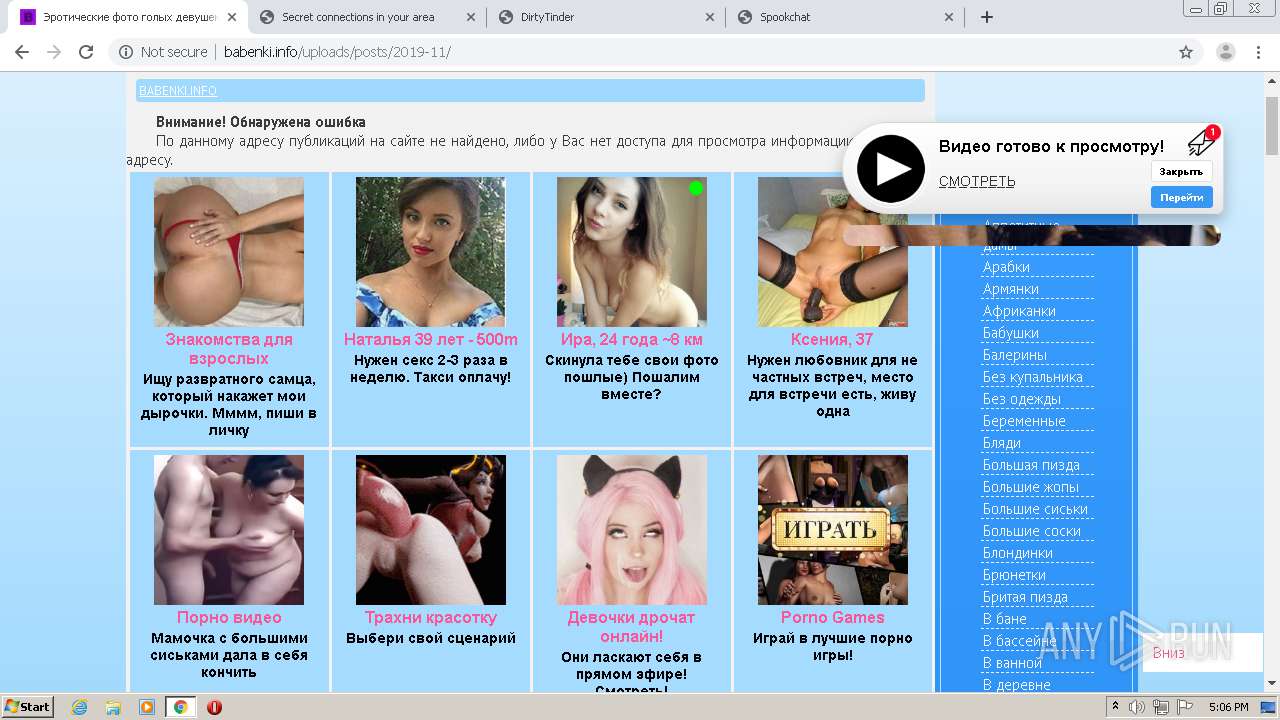
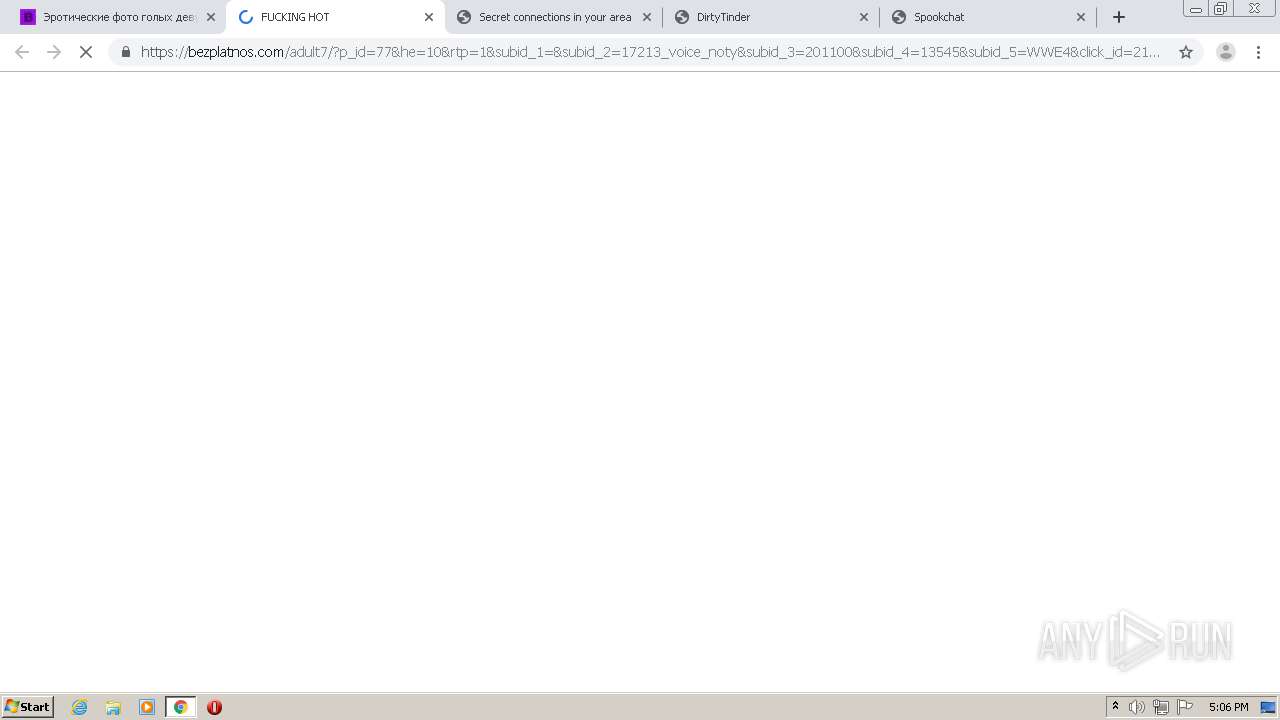
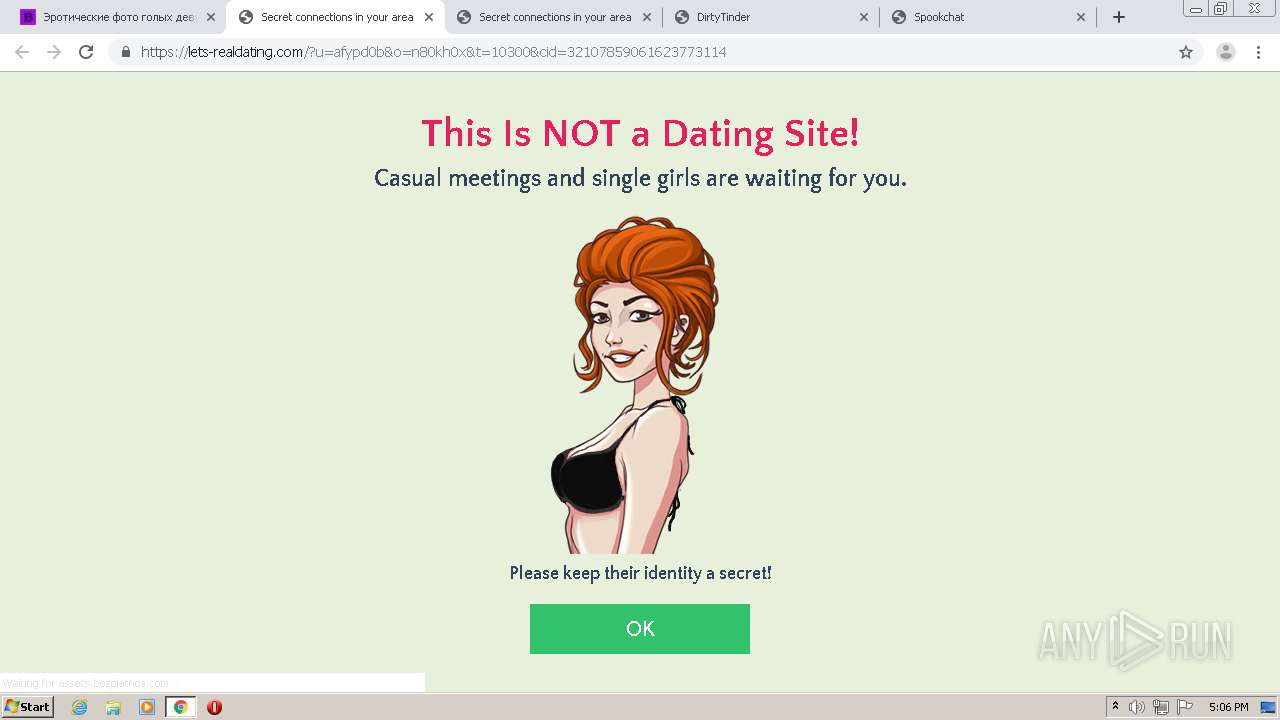
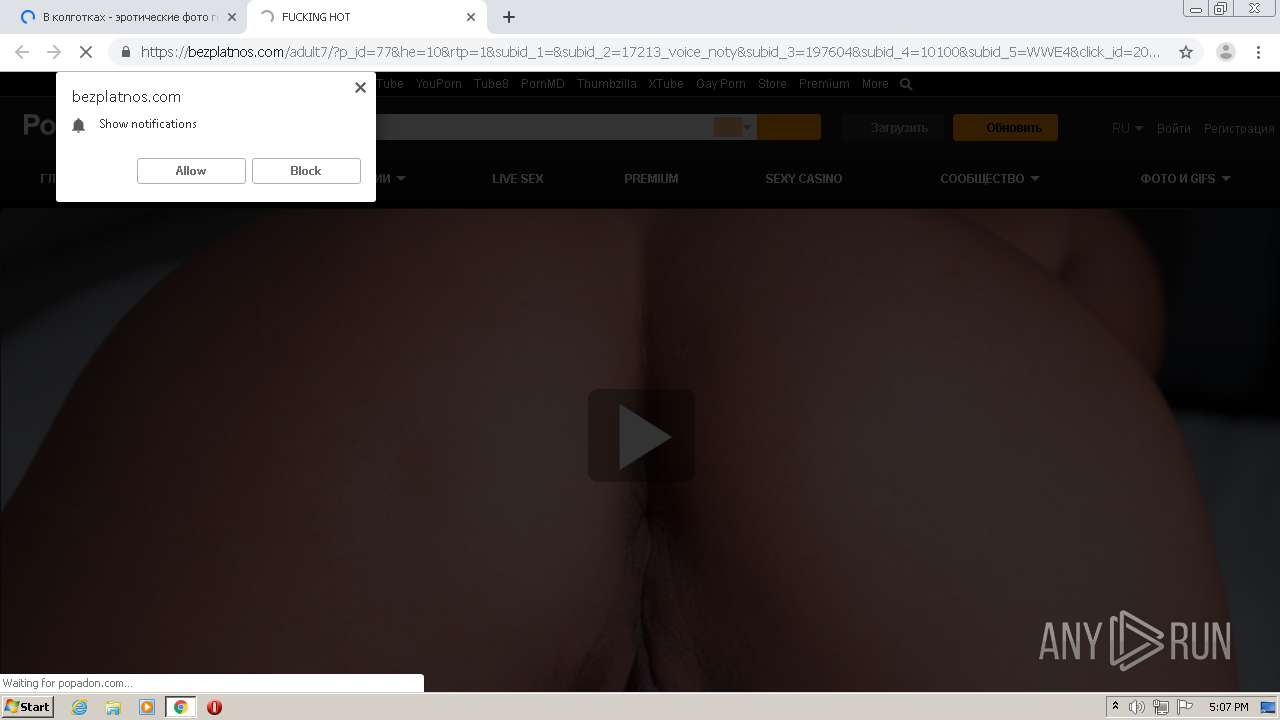
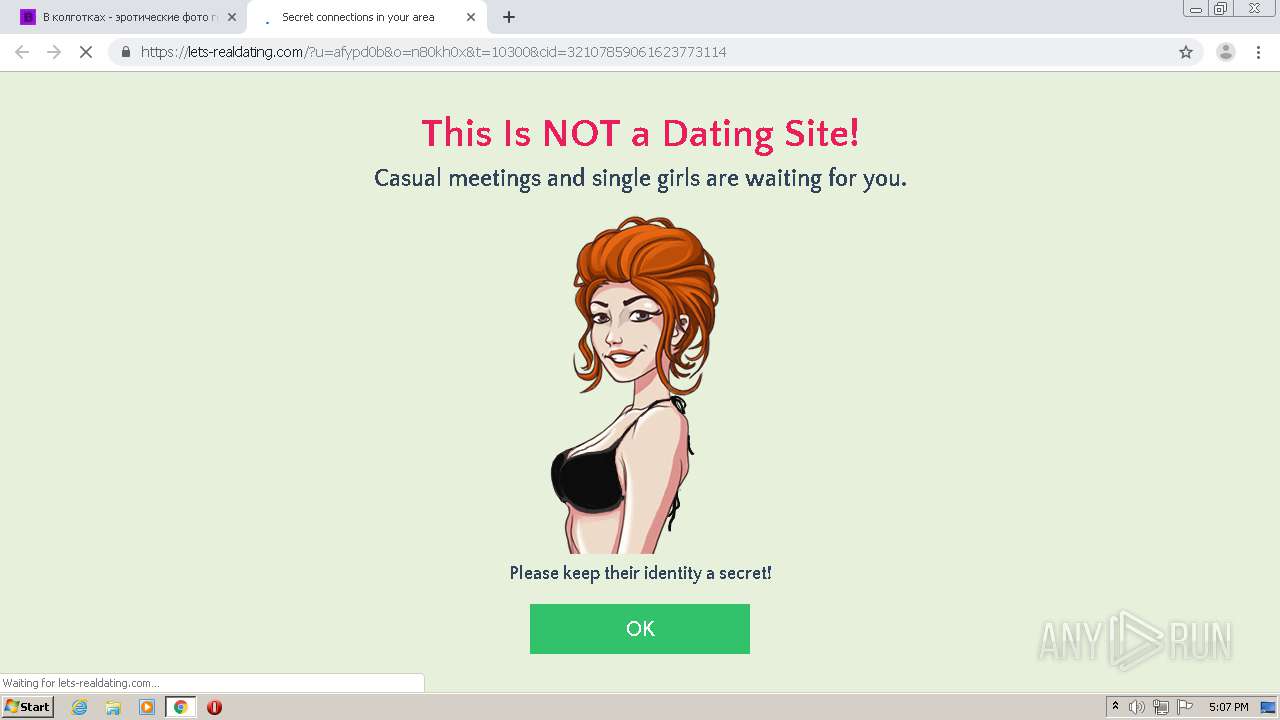
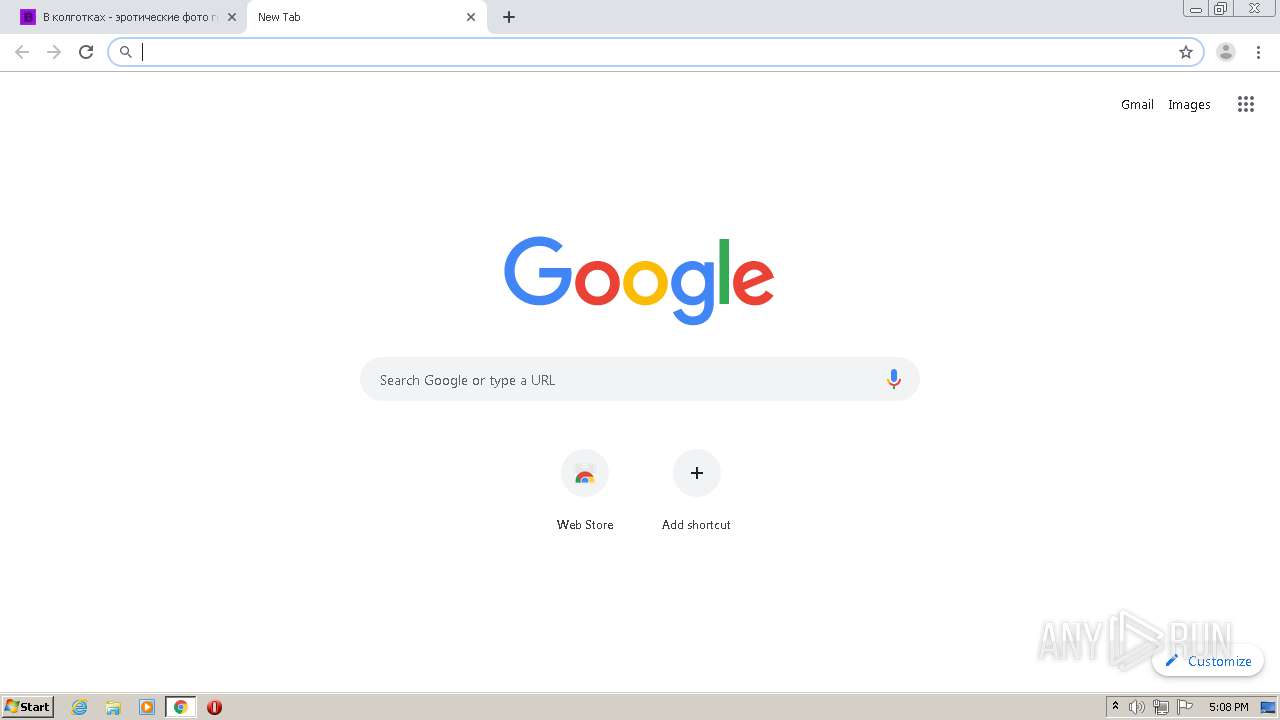
| Verdict: | Malicious activity |
| Analysis date: | June 15, 2021, 16:04:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 262371813AB7F5BA15EE0E37CA1DE760 |
| SHA1: | 25374C9F8CF3C00D65389F5D0F035417E0461851 |
| SHA256: | F98C38D47D1953EABFA449A1B2CAACD809263487ECC8A8E0F6841EF0E3BF541D |
| SSDEEP: | 3:N1KcuAnUKPgWNTINKUHCqAJQCJcNaWqAuhVALRYOSwn:CcMKPgsTINlvCSNazsLRYPwn |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads the hosts file
- chrome.exe (PID: 2204)
- chrome.exe (PID: 1748)
Creates files in the user directory
- chrome.exe (PID: 2204)
Application launched itself
- chrome.exe (PID: 2204)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
105
Monitored processes
66
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,17826103777556478158,13239659113393691858,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5906252616482117339 --renderer-client-id=14 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1948 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,17826103777556478158,13239659113393691858,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11302365871533344410 --renderer-client-id=34 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3868 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,17826103777556478158,13239659113393691858,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5988604556731039715 --renderer-client-id=57 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4056 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,17826103777556478158,13239659113393691858,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9062524547068672806 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2356 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 764 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,17826103777556478158,13239659113393691858,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1564211837979284819 --renderer-client-id=23 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1012 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,17826103777556478158,13239659113393691858,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=15519398399175088108 --mojo-platform-channel-handle=1000 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,17826103777556478158,13239659113393691858,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7784996677520717893 --renderer-client-id=43 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4152 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,17826103777556478158,13239659113393691858,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9442373880745150347 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2172 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,17826103777556478158,13239659113393691858,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8724113597643404503 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3088 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,17826103777556478158,13239659113393691858,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7653301040688810144 --renderer-client-id=59 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
681
Read events
569
Write events
109
Delete events
3
Modification events
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2228) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2204-13268246672148750 |
Value: 259 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
110
Text files
163
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-60C8CF90-89C.pma | — | |
MD5:— | SHA256:— | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\11327c3a-09ed-42c1-9756-a8f8dd89a681.tmp | — | |
MD5:— | SHA256:— | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF13f521.TMP | — | |
MD5:— | SHA256:— | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF13f494.TMP | text | |
MD5:— | SHA256:— | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF13f688.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
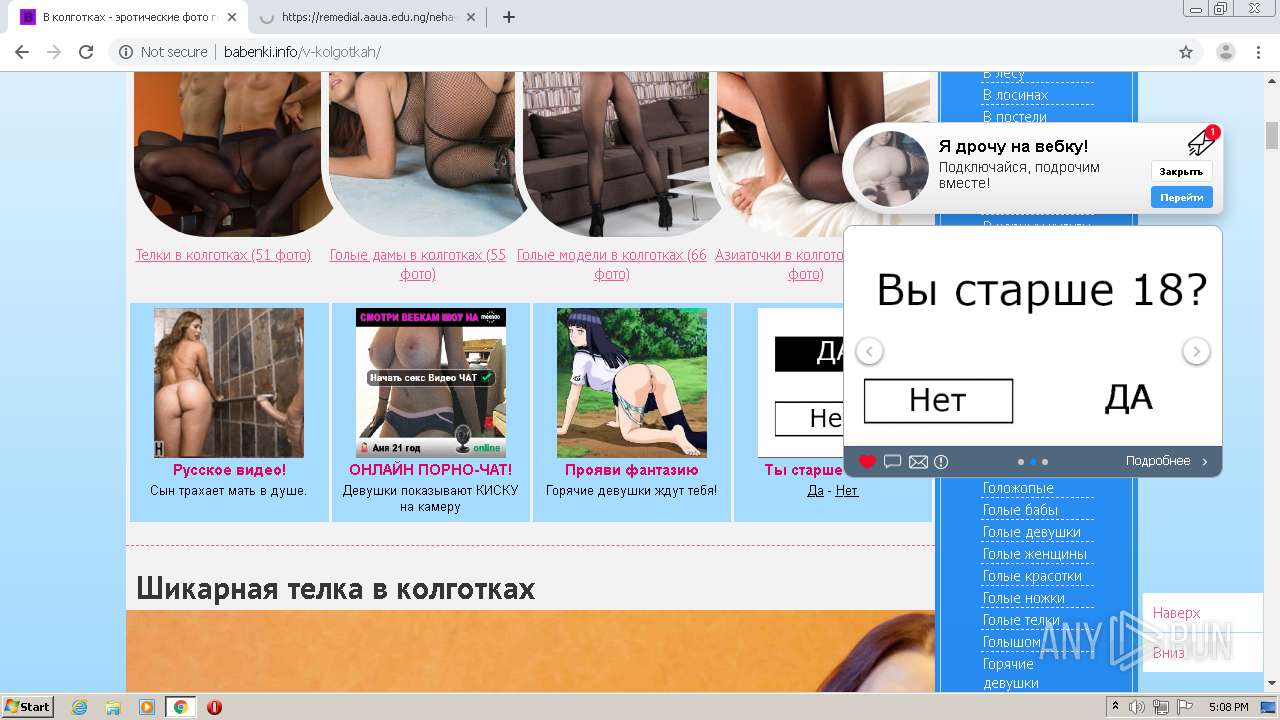
HTTP(S) requests
255
TCP/UDP connections
306
DNS requests
55
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1748 | chrome.exe | GET | 200 | 51.77.36.8:80 | http://babenki.info/templates/babenki/style/engine.css | GB | text | 21.7 Kb | whitelisted |
1748 | chrome.exe | GET | 200 | 193.200.65.11:80 | http://cs09.adl-hunter.com/content/56381/3255427.jpg | NL | image | 124 Kb | unknown |
1748 | chrome.exe | GET | 200 | 193.200.65.12:80 | http://cs10.adl-hunter.com/content/56381/3185005.jpg | NL | image | 9.99 Kb | suspicious |
1748 | chrome.exe | GET | 200 | 193.200.65.11:80 | http://cs09.adl-hunter.com/content/56381/3132463.jpeg | NL | image | 19.8 Kb | unknown |
1748 | chrome.exe | GET | 200 | 193.200.65.13:80 | http://cs11.adl-hunter.com/content/56381/3195493.jpg | NL | image | 19.0 Kb | suspicious |
1748 | chrome.exe | GET | 200 | 193.200.65.13:80 | http://cs11.adl-hunter.com/content/56381/3132472.jpg | NL | image | 87.4 Kb | suspicious |
1748 | chrome.exe | GET | 200 | 193.200.65.11:80 | http://cs09.adl-hunter.com/content/56381/3255427.gif | NL | image | 94.0 Kb | unknown |
1748 | chrome.exe | GET | 200 | 193.200.65.11:80 | http://cs09.adl-hunter.com/content/56381/3249010.jpg | NL | image | 14.5 Kb | unknown |
1748 | chrome.exe | GET | 200 | 193.200.65.13:80 | http://cs11.adl-hunter.com/content/56381/3231841.jpg | NL | image | 14.3 Kb | suspicious |
1748 | chrome.exe | GET | 200 | 193.200.65.11:80 | http://cs09.adl-hunter.com/content/56381/3132466.jpg | NL | image | 83.3 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
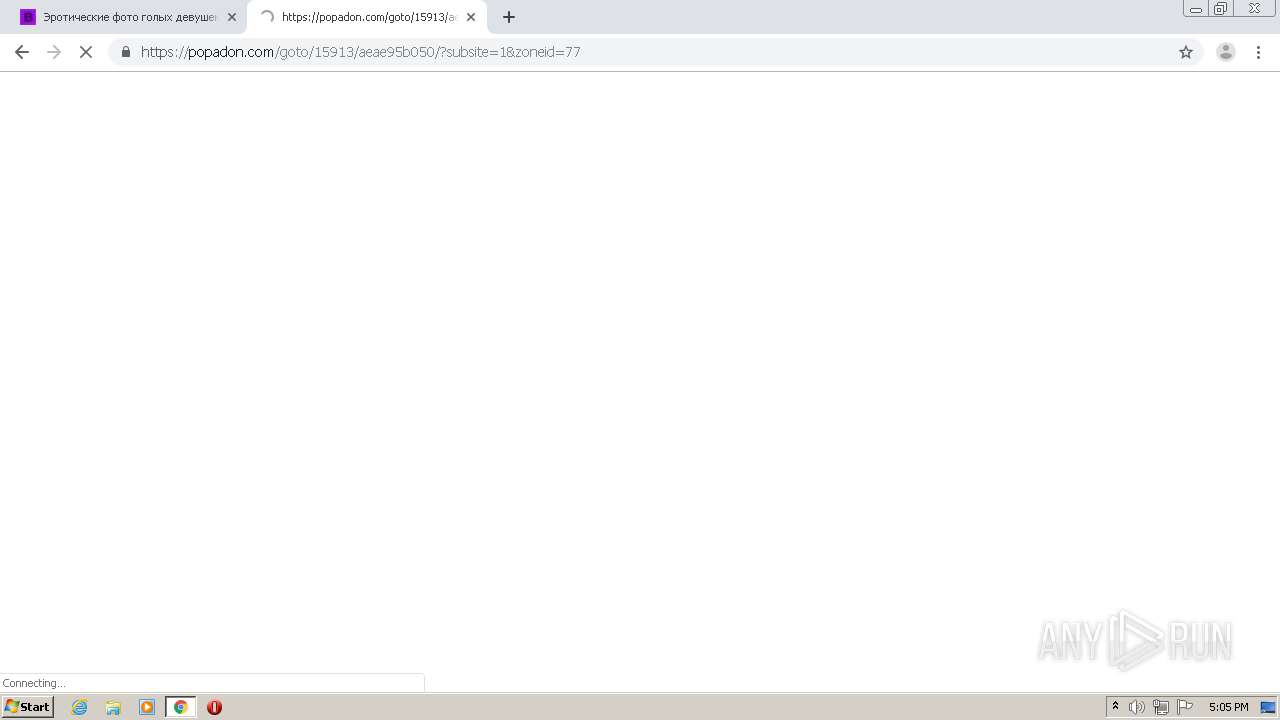
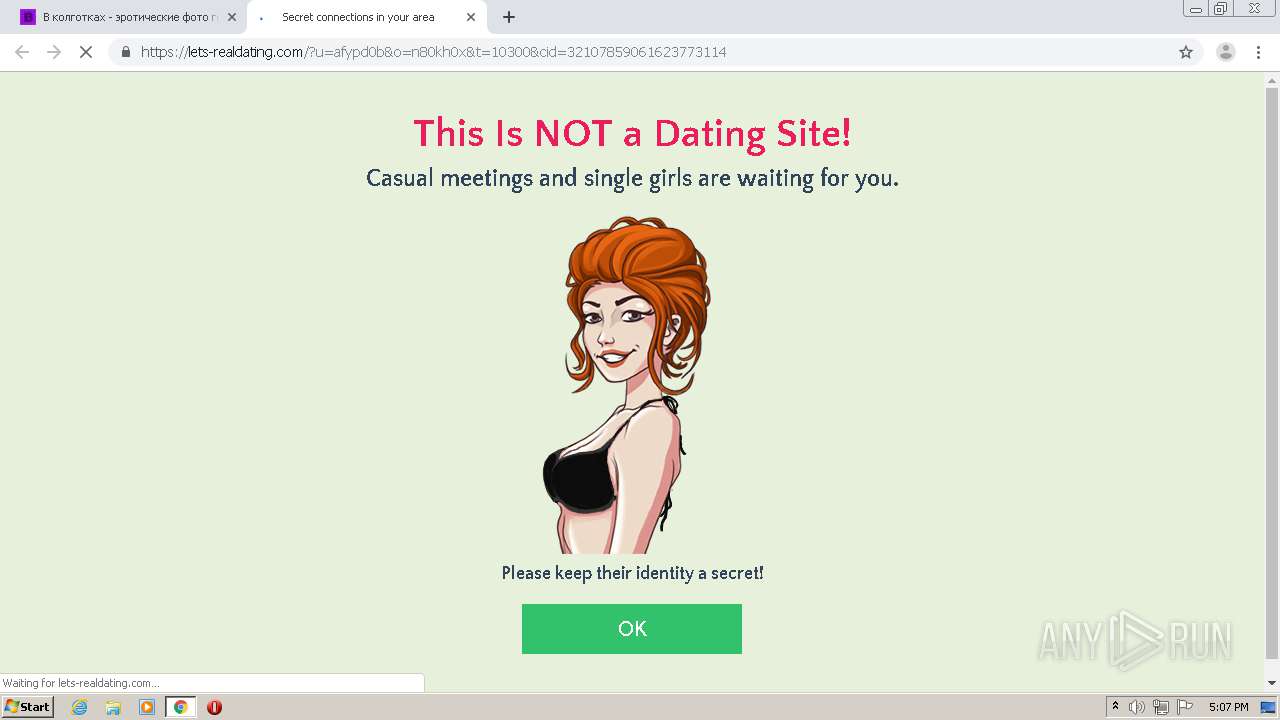
1748 | chrome.exe | 193.200.65.13:80 | cs11.adl-hunter.com | HZ Hosting Ltd | NL | suspicious |
1748 | chrome.exe | 193.200.65.11:80 | cs09.adl-hunter.com | HZ Hosting Ltd | NL | unknown |
1748 | chrome.exe | 87.250.251.119:443 | mc.yandex.ru | YANDEX LLC | RU | whitelisted |
1748 | chrome.exe | 193.200.65.12:80 | cs10.adl-hunter.com | HZ Hosting Ltd | NL | suspicious |
1748 | chrome.exe | 80.239.201.78:443 | mc.webvisor.org | Telia Company AB | — | unknown |
1748 | chrome.exe | 193.200.64.185:443 | budvawshes.ru | HZ Hosting Ltd | NL | suspicious |
1748 | chrome.exe | 193.200.64.20:80 | adl-hunter.com | HZ Hosting Ltd | NL | suspicious |
1748 | chrome.exe | 51.77.36.8:80 | babenki.info | — | GB | unknown |
1748 | chrome.exe | 142.250.186.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
1748 | chrome.exe | 142.250.185.67:443 | www.google.com.ua | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
babenki.info |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
adl-hunter.com |
| suspicious |
counter.yadro.ru |
| whitelisted |
cdn.jsdelivr.net |
| whitelisted |
themes.googleusercontent.com |
| whitelisted |
www.liveinternet.ru |
| whitelisted |
cs09.adl-hunter.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
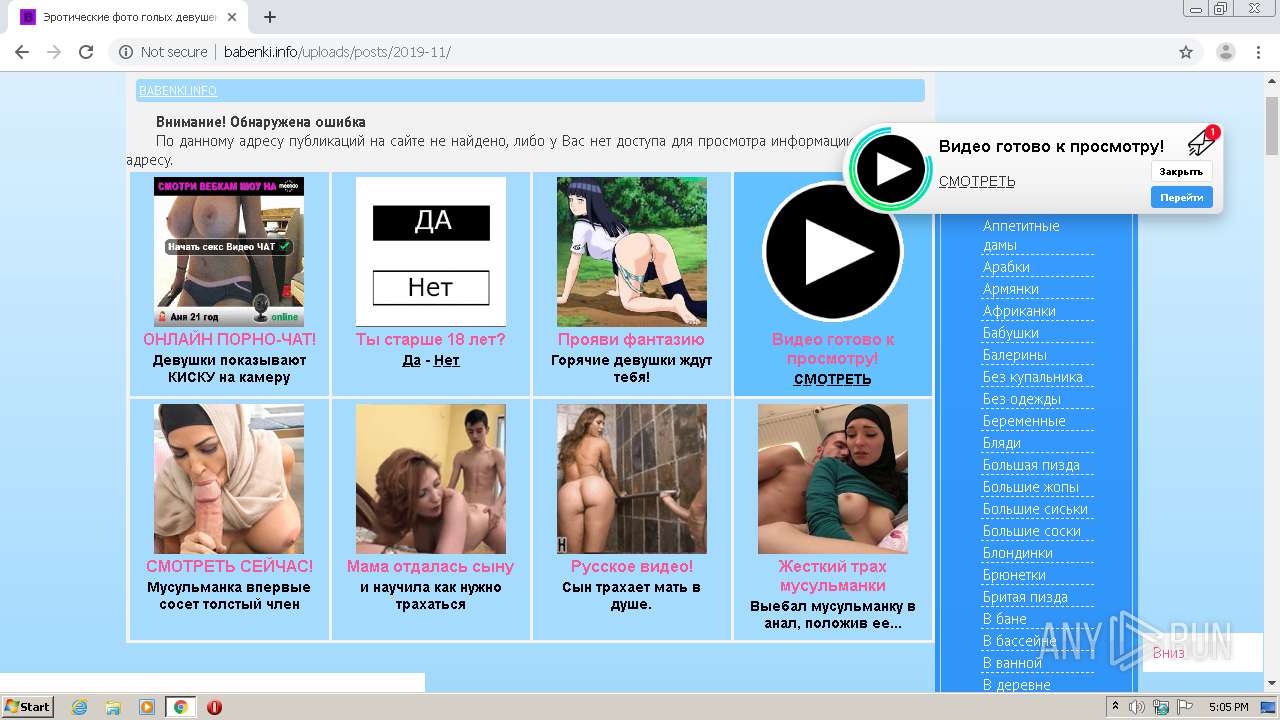
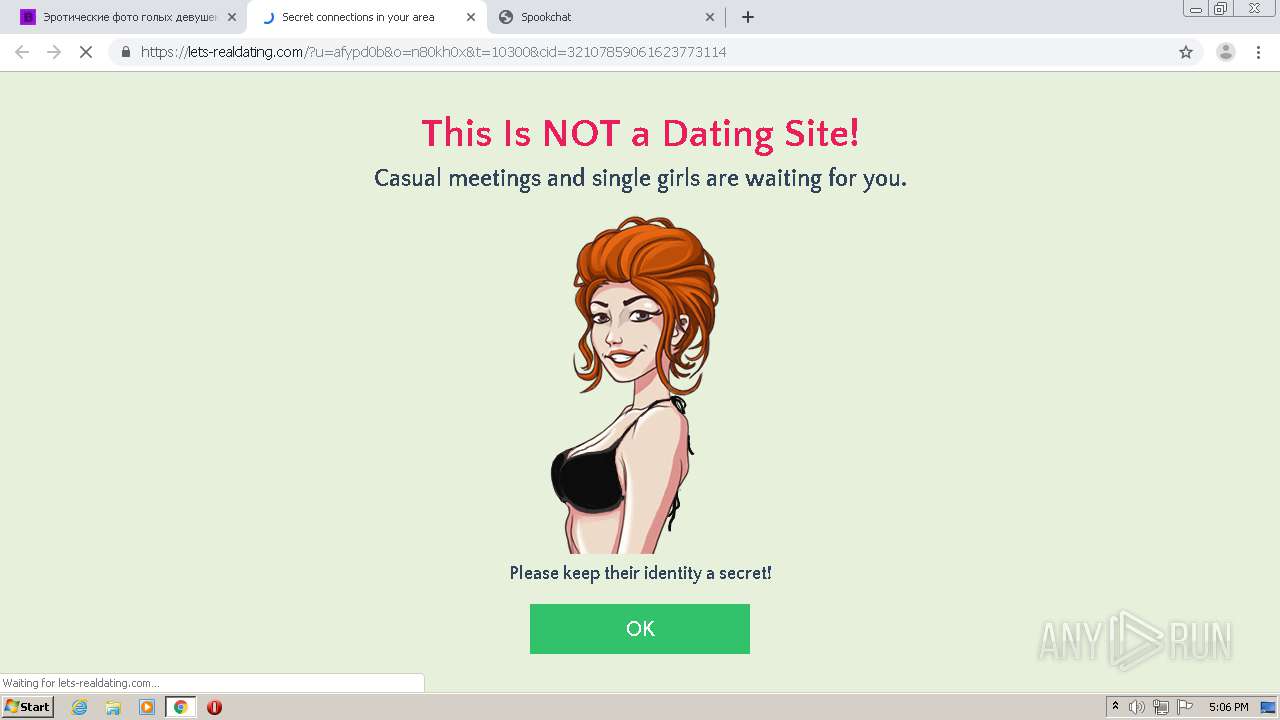
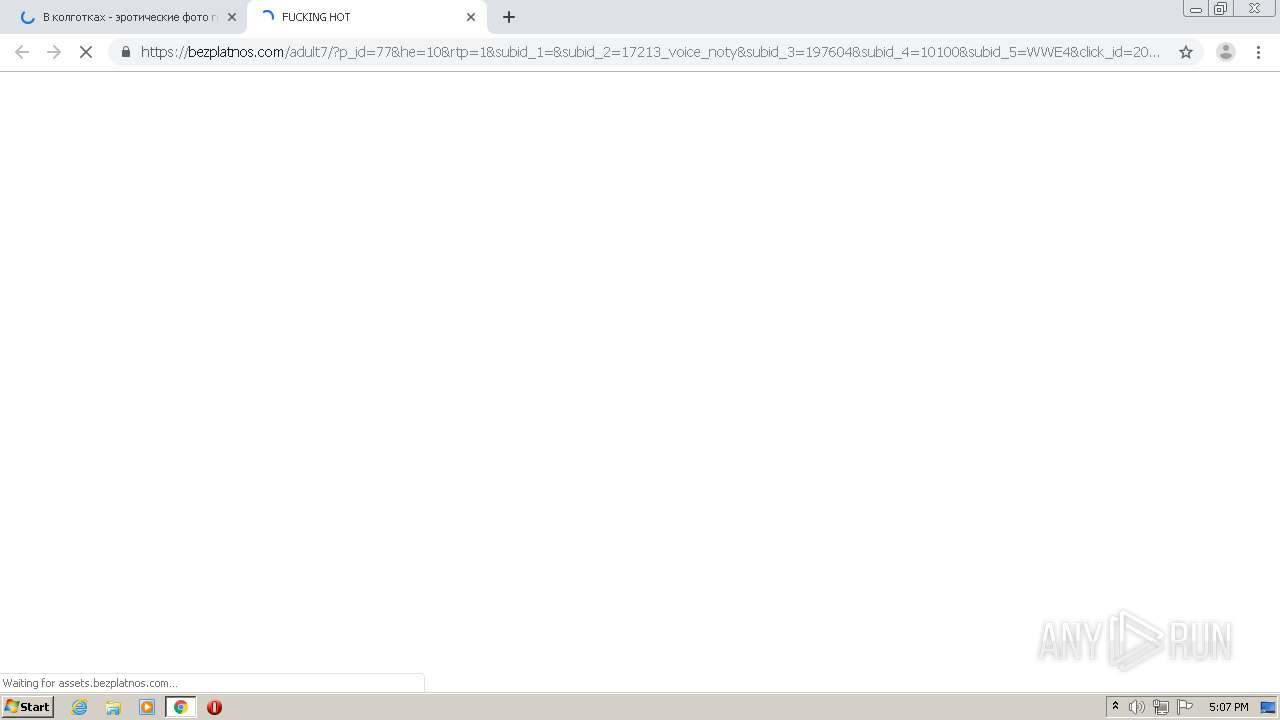
1748 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1748 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1748 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1748 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1748 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1748 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1748 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1748 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1748 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1748 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1 ETPRO signatures available at the full report