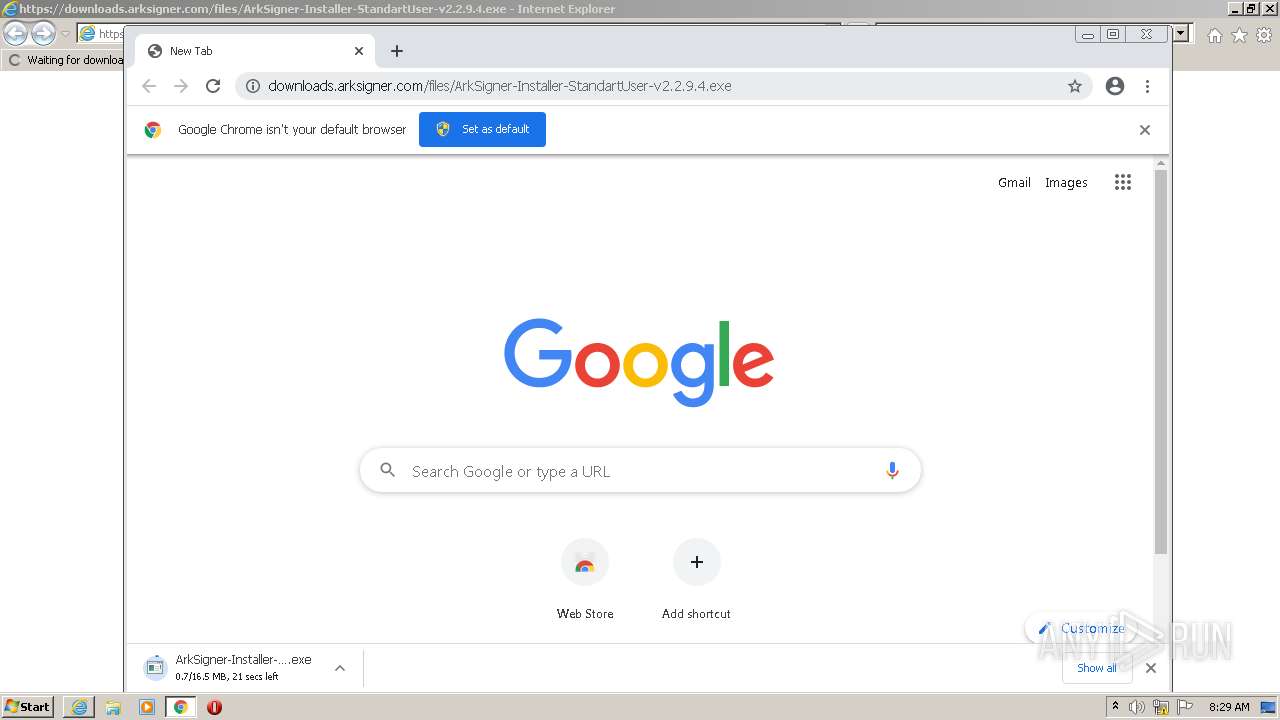
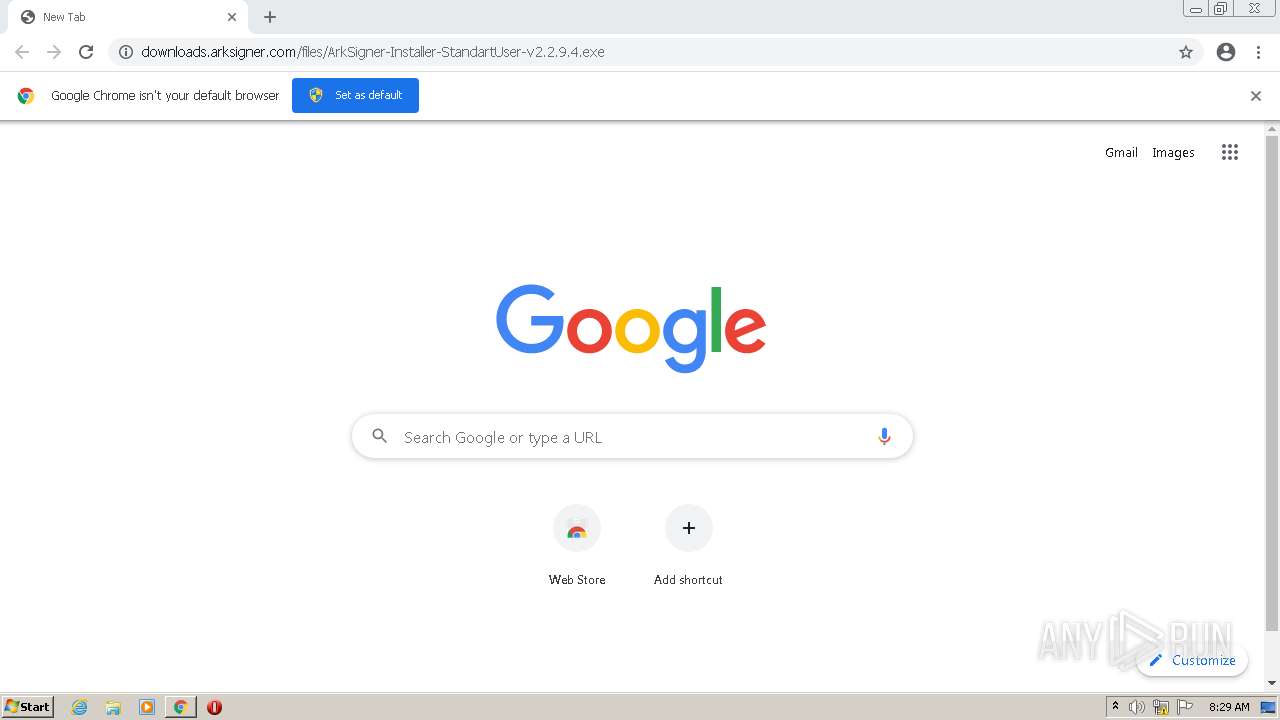
| URL: | https://downloads.arksigner.com/files/ArkSigner-Installer-StandartUser-v2.2.9.4.exe |
| Full analysis: | https://app.any.run/tasks/62f98bf0-9abe-4f5b-9f05-cc2f6208dadf |
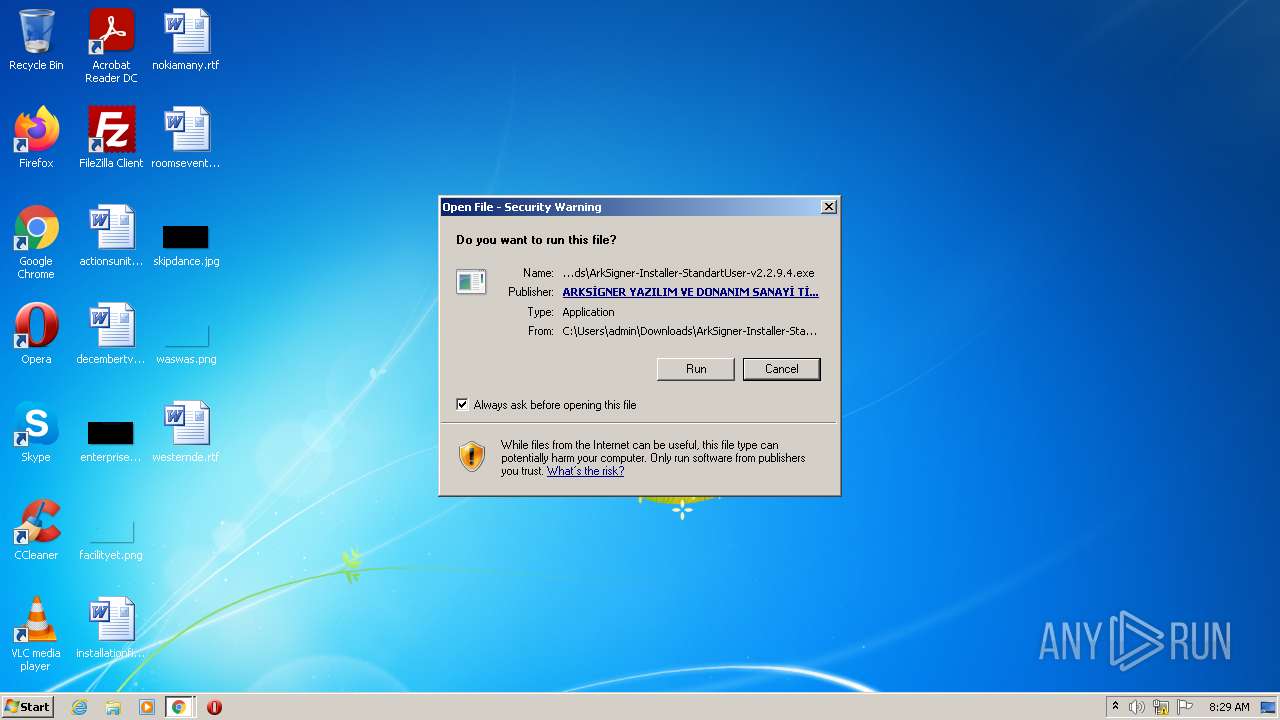
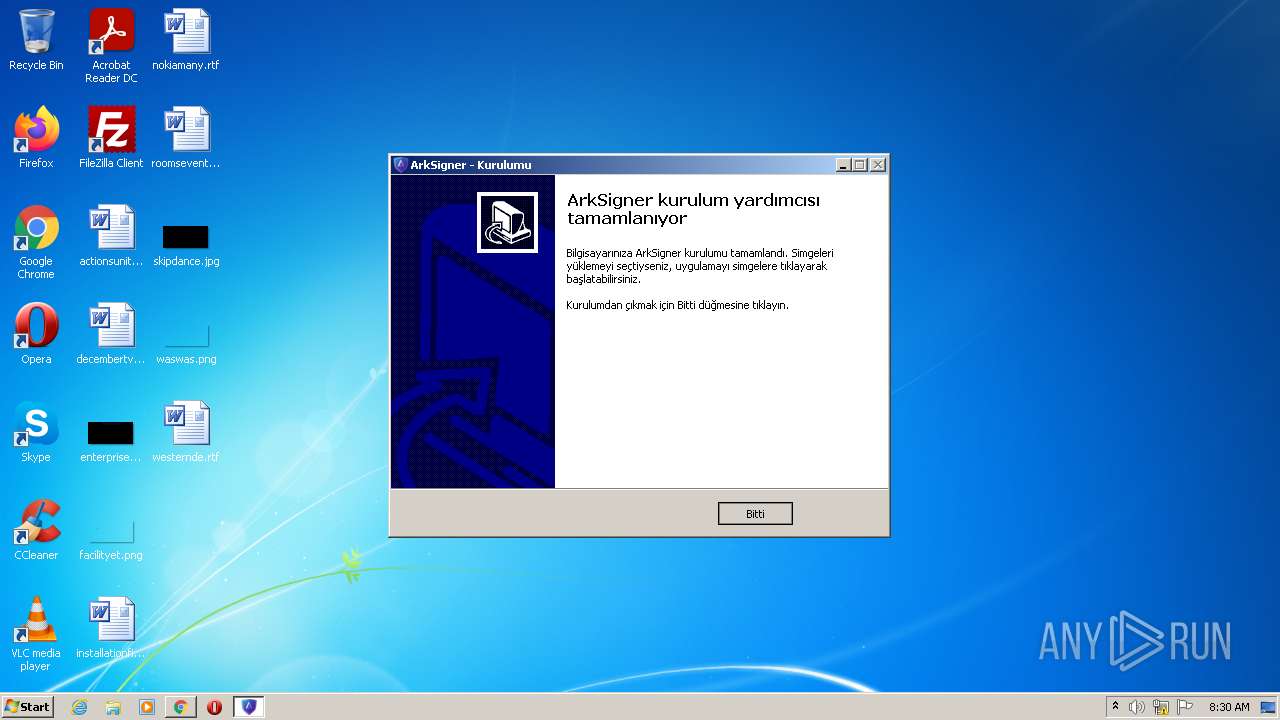
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2022, 07:29:17 |
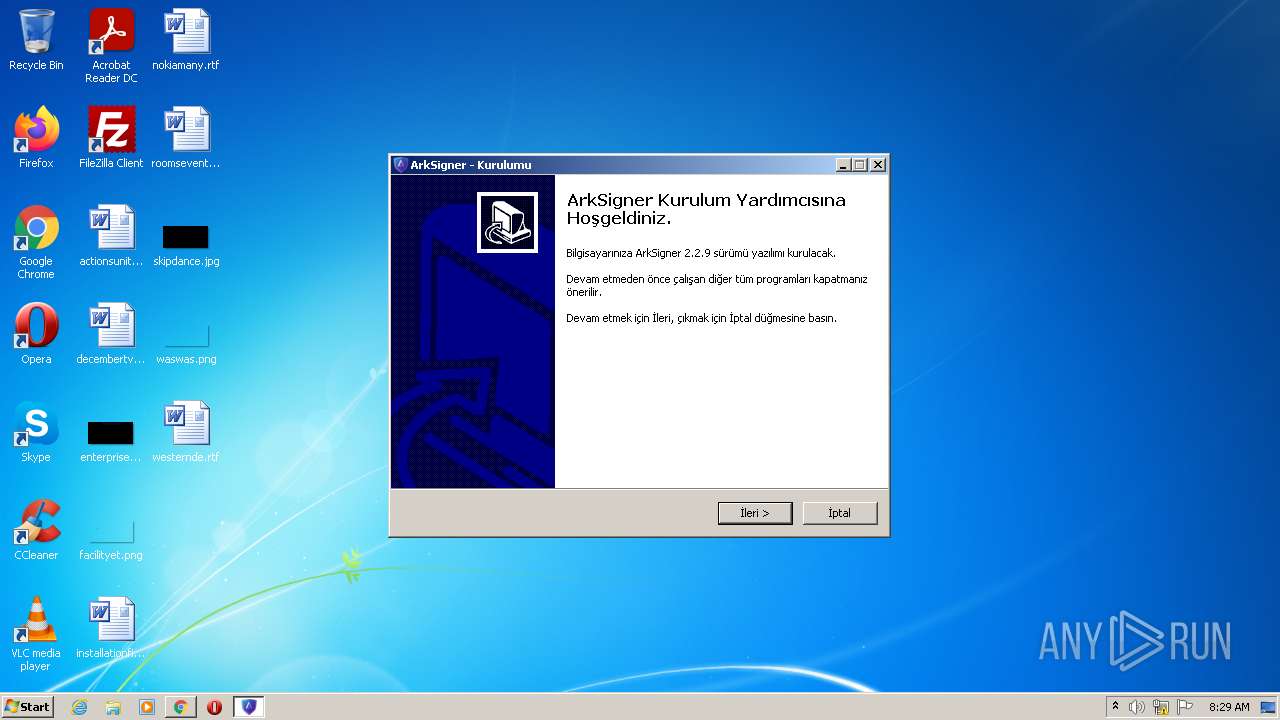
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | F319D23BB0D33C485A301B2046C36845 |
| SHA1: | AFD0C8DBDB90ECAB25CD132F926F0478A328AFA6 |
| SHA256: | F988DD548F87CE2A59D675A9139F458F9FB61B3EFE77AC11E020FF95B1ABA1B2 |
| SSDEEP: | 3:N8SE4L+O2LAX6KQQYsLWTXI2RE1+d4lkAn:2SSOhXB9WTXLRE1+K7n |
MALICIOUS
Drops executable file immediately after starts
- chrome.exe (PID: 2624)
- chrome.exe (PID: 2216)
- ArkSigner-Installer-StandartUser-v2.2.9.4.exe (PID: 2564)
- ArkSigner-Installer-StandartUser-v2.2.9.4.tmp (PID: 2656)
Application was dropped or rewritten from another process
- ArkSigner-Installer-StandartUser-v2.2.9.4.exe (PID: 2564)
- ArkSignerPostInstaller.exe (PID: 3040)
- ArkSignerPostInstaller.exe (PID: 1300)
- ArkSignerManagement.exe (PID: 2864)
- ArkSignerServiceConn.exe (PID: 2324)
- ArkSignerGuncelleme.exe (PID: 2500)
Loads dropped or rewritten executable
- ArkSignerPostInstaller.exe (PID: 3040)
- ArkSignerManagement.exe (PID: 2864)
- ArkSignerGuncelleme.exe (PID: 2500)
- ArkSignerServiceConn.exe (PID: 2324)
Writes to the hosts file
- ArkSignerPostInstaller.exe (PID: 3040)
Changes the autorun value in the registry
- ArkSigner-Installer-StandartUser-v2.2.9.4.tmp (PID: 2656)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3412)
- iexplore.exe (PID: 1972)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2624)
Executable content was dropped or overwritten
- chrome.exe (PID: 2624)
- chrome.exe (PID: 2216)
- ArkSigner-Installer-StandartUser-v2.2.9.4.exe (PID: 2564)
- ArkSigner-Installer-StandartUser-v2.2.9.4.tmp (PID: 2656)
Drops a file with a compile date too recent
- chrome.exe (PID: 2624)
- chrome.exe (PID: 2216)
- ArkSigner-Installer-StandartUser-v2.2.9.4.exe (PID: 2564)
- ArkSigner-Installer-StandartUser-v2.2.9.4.tmp (PID: 2656)
Checks supported languages
- ArkSigner-Installer-StandartUser-v2.2.9.4.exe (PID: 2564)
- ArkSigner-Installer-StandartUser-v2.2.9.4.tmp (PID: 2656)
- ArkSignerPostInstaller.exe (PID: 3040)
- WScript.exe (PID: 3804)
- ArkSignerManagement.exe (PID: 2864)
- ArkSignerGuncelleme.exe (PID: 2500)
- ArkSignerServiceConn.exe (PID: 2324)
Reads Windows owner or organization settings
- ArkSigner-Installer-StandartUser-v2.2.9.4.tmp (PID: 2656)
Reads the Windows organization settings
- ArkSigner-Installer-StandartUser-v2.2.9.4.tmp (PID: 2656)
Uses TASKKILL.EXE to kill process
- ArkSigner-Installer-StandartUser-v2.2.9.4.tmp (PID: 2656)
- ArkSignerManagement.exe (PID: 2864)
Reads the computer name
- ArkSigner-Installer-StandartUser-v2.2.9.4.tmp (PID: 2656)
- WScript.exe (PID: 3804)
- ArkSignerManagement.exe (PID: 2864)
- ArkSignerServiceConn.exe (PID: 2324)
Creates files in the user directory
- ArkSigner-Installer-StandartUser-v2.2.9.4.tmp (PID: 2656)
Executes scripts
- ArkSigner-Installer-StandartUser-v2.2.9.4.tmp (PID: 2656)
Uses NETSH.EXE for network configuration
- ArkSignerPostInstaller.exe (PID: 3040)
Reads Environment values
- netsh.exe (PID: 3260)
- netsh.exe (PID: 3392)
- netsh.exe (PID: 4036)
- netsh.exe (PID: 3156)
Uses TASKLIST.EXE to query information about running processes
- ArkSignerServiceConn.exe (PID: 2324)
Starts Internet Explorer
- ArkSignerManagement.exe (PID: 2864)
INFO
Checks supported languages
- iexplore.exe (PID: 3412)
- iexplore.exe (PID: 2932)
- chrome.exe (PID: 2624)
- chrome.exe (PID: 2668)
- chrome.exe (PID: 3248)
- chrome.exe (PID: 2216)
- chrome.exe (PID: 2776)
- chrome.exe (PID: 3460)
- chrome.exe (PID: 856)
- chrome.exe (PID: 508)
- chrome.exe (PID: 2256)
- chrome.exe (PID: 652)
- chrome.exe (PID: 3304)
- chrome.exe (PID: 1656)
- chrome.exe (PID: 3492)
- chrome.exe (PID: 1012)
- chrome.exe (PID: 272)
- chrome.exe (PID: 2160)
- chrome.exe (PID: 904)
- chrome.exe (PID: 1248)
- chrome.exe (PID: 2540)
- chrome.exe (PID: 2864)
- chrome.exe (PID: 3760)
- taskkill.exe (PID: 2020)
- taskkill.exe (PID: 120)
- taskkill.exe (PID: 2376)
- taskkill.exe (PID: 3672)
- taskkill.exe (PID: 2900)
- taskkill.exe (PID: 2484)
- netsh.exe (PID: 3260)
- netsh.exe (PID: 3392)
- netsh.exe (PID: 3156)
- netsh.exe (PID: 4036)
- taskkill.exe (PID: 1472)
- chrome.exe (PID: 3600)
- taskkill.exe (PID: 3412)
- tasklist.exe (PID: 3804)
- iexplore.exe (PID: 1972)
- chrome.exe (PID: 836)
- iexplore.exe (PID: 2172)
Reads the computer name
- iexplore.exe (PID: 3412)
- chrome.exe (PID: 2624)
- iexplore.exe (PID: 2932)
- chrome.exe (PID: 2216)
- chrome.exe (PID: 3248)
- chrome.exe (PID: 2256)
- chrome.exe (PID: 3492)
- chrome.exe (PID: 2540)
- chrome.exe (PID: 3760)
- taskkill.exe (PID: 2376)
- taskkill.exe (PID: 120)
- taskkill.exe (PID: 3672)
- taskkill.exe (PID: 2020)
- taskkill.exe (PID: 2900)
- taskkill.exe (PID: 2484)
- netsh.exe (PID: 3260)
- netsh.exe (PID: 3392)
- netsh.exe (PID: 4036)
- netsh.exe (PID: 3156)
- tasklist.exe (PID: 3804)
- chrome.exe (PID: 3600)
- taskkill.exe (PID: 1472)
- taskkill.exe (PID: 3412)
- chrome.exe (PID: 836)
- iexplore.exe (PID: 2172)
- iexplore.exe (PID: 1972)
Application launched itself
- iexplore.exe (PID: 2932)
- chrome.exe (PID: 2624)
- iexplore.exe (PID: 2172)
Manual execution by user
- chrome.exe (PID: 2624)
Reads settings of System Certificates
- iexplore.exe (PID: 3412)
- iexplore.exe (PID: 2932)
- chrome.exe (PID: 2216)
- chrome.exe (PID: 2624)
- ArkSignerServiceConn.exe (PID: 2324)
- iexplore.exe (PID: 1972)
- iexplore.exe (PID: 2172)
Checks Windows Trust Settings
- iexplore.exe (PID: 3412)
- iexplore.exe (PID: 2932)
- chrome.exe (PID: 2624)
- WScript.exe (PID: 3804)
- iexplore.exe (PID: 1972)
- iexplore.exe (PID: 2172)
Reads the hosts file
- chrome.exe (PID: 2624)
- chrome.exe (PID: 2216)
- ArkSignerPostInstaller.exe (PID: 3040)
Changes internet zones settings
- iexplore.exe (PID: 2932)
- iexplore.exe (PID: 2172)
Reads the date of Windows installation
- iexplore.exe (PID: 2932)
- chrome.exe (PID: 836)
- iexplore.exe (PID: 2172)
Application was dropped or rewritten from another process
- ArkSigner-Installer-StandartUser-v2.2.9.4.tmp (PID: 2656)
Creates a software uninstall entry
- ArkSigner-Installer-StandartUser-v2.2.9.4.tmp (PID: 2656)
Reads internet explorer settings
- iexplore.exe (PID: 1972)
Changes settings of System certificates
- iexplore.exe (PID: 2172)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2172)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
99
Monitored processes
48
Malicious processes
9
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Windows\system32\taskkill.exe" /f /im ArkSignerManagement.exe | C:\Windows\system32\taskkill.exe | — | ArkSigner-Installer-StandartUser-v2.2.9.4.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1048,9956112764237419243,9920086060580764785,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3632 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1048,9956112764237419243,9920086060580764785,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2812 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1048,9956112764237419243,9920086060580764785,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2956 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1048,9956112764237419243,9920086060580764785,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1676 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,9956112764237419243,9920086060580764785,131072 --enable-features=PasswordImport --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1948 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,9956112764237419243,9920086060580764785,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3600 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1048,9956112764237419243,9920086060580764785,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=3144 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1048,9956112764237419243,9920086060580764785,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=4172 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1300 | "C:\Users\admin\AppData\Local\Programs\Ark\ArkSigner\ArkSignerPostInstaller.exe" | C:\Users\admin\AppData\Local\Programs\Ark\ArkSigner\ArkSignerPostInstaller.exe | — | ArkSigner-Installer-StandartUser-v2.2.9.4.tmp | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
48 528
Read events
47 930
Write events
585
Delete events
13
Modification events
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 770975152 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30955638 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30955638 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
87
Suspicious files
144
Text files
135
Unknown types
53
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62664DD5-A40.pma | — | |
MD5:— | SHA256:— | |||
| 3412 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3412 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | binary | |
MD5:— | SHA256:— | |||
| 2216 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\index | binary | |
MD5:— | SHA256:— | |||
| 2624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RFf7a57.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 2624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 2216 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\data_0 | vxd | |
MD5:CF89D16BB9107C631DAABF0C0EE58EFB | SHA256:D6A5FE39CD672781B256E0E3102F7022635F1D4BB7CFCC90A80FFFE4D0F3877E | |||
| 3412 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 2624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 2624 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFf7a28.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
50
DNS requests
32
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3412 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
2216 | chrome.exe | GET | 302 | 142.250.185.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 557 b | whitelisted |
1972 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEGw1Yik%2BBw9wCsFmPcXqpzQ%3D | US | der | 471 b | whitelisted |
1972 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEEhX82IjykX0%2Bx3J%2FqKM50M%3D | US | der | 471 b | whitelisted |
2932 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
1972 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDZVQ0c3n%2F16xKL4oJJTrDj | US | der | 472 b | whitelisted |
1972 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
1972 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
2216 | chrome.exe | GET | 200 | 74.125.4.170:80 | http://r5---sn-aigzrne7.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=e_&mip=185.198.243.195&mm=28&mn=sn-aigzrne7&ms=nvh&mt=1650871461&mv=m&mvi=5&pl=25&rmhost=r2---sn-aigzrne7.gvt1.com&shardbypass=sd | US | crx | 242 Kb | whitelisted |
3412 | iexplore.exe | GET | 200 | 23.216.77.80:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?5532d3dab35cca7f | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3412 | iexplore.exe | 159.253.46.5:443 | downloads.arksigner.com | Netinternet Bilisim Teknolojileri AS | TR | unknown |
3412 | iexplore.exe | 23.216.77.80:80 | ctldl.windowsupdate.com | NTT DOCOMO, INC. | US | suspicious |
3412 | iexplore.exe | 104.18.32.68:80 | ocsp.usertrust.com | Cloudflare Inc | US | suspicious |
3412 | iexplore.exe | 172.64.155.188:80 | ocsp.usertrust.com | — | US | suspicious |
2932 | iexplore.exe | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2216 | chrome.exe | 142.250.186.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2216 | chrome.exe | 142.250.186.77:443 | accounts.google.com | Google Inc. | US | suspicious |
2216 | chrome.exe | 142.250.184.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
2216 | chrome.exe | 142.250.186.100:443 | www.google.com | Google Inc. | US | whitelisted |
2932 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
downloads.arksigner.com |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
Threats
Process | Message |
|---|---|
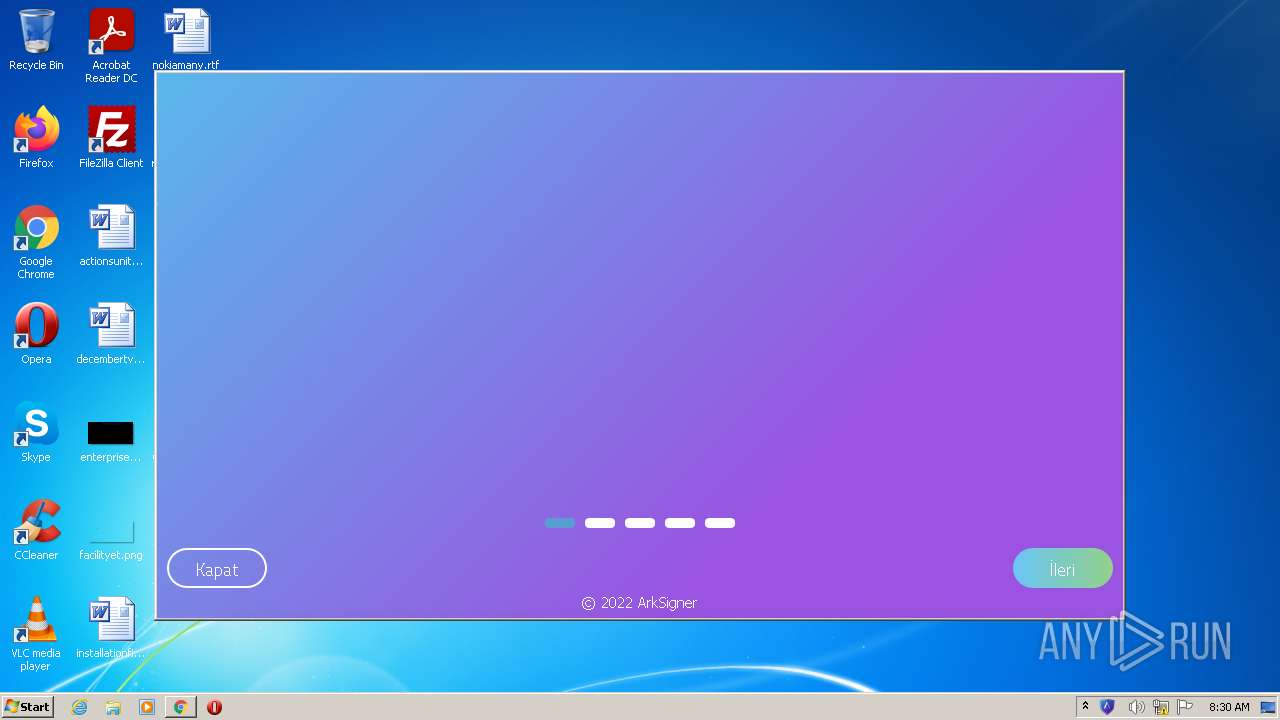
ArkSignerGuncelleme.exe | Starting auto update service
|
ArkSignerServiceConn.exe | HttpListener: Listening on port 16357
|
ArkSignerManagement.exe | QPixmap::scaled: Pixmap is a null pixmap
|
ArkSignerManagement.exe | QPropertyAnimation::updateState (opacity): Changing state of an animation without target
|
ArkSignerManagement.exe | QPropertyAnimation::updateState (geometry): Changing state of an animation without target
|