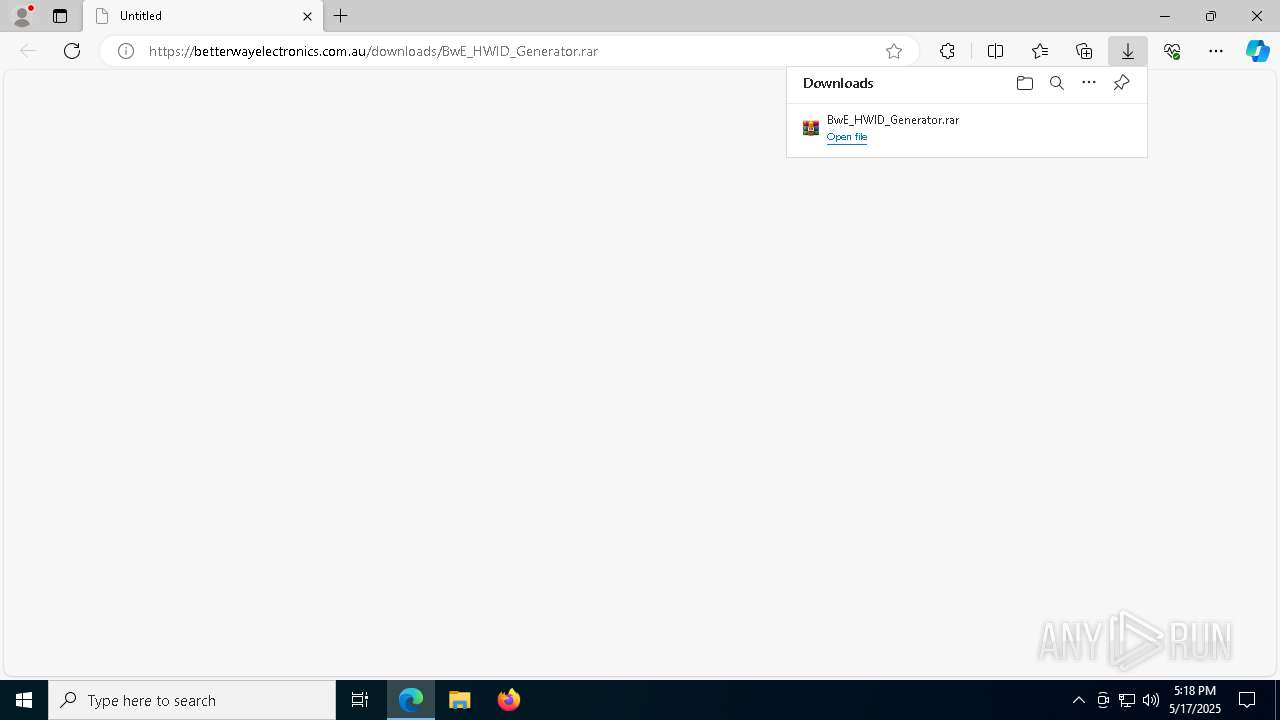
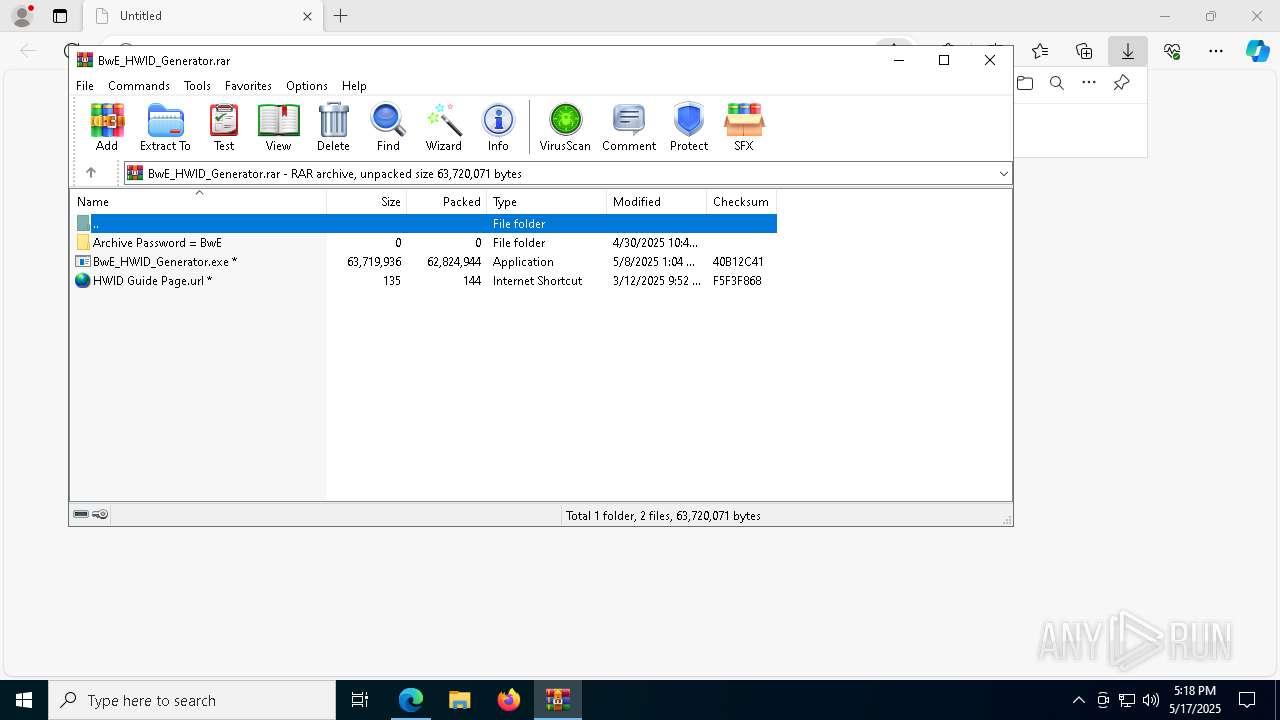
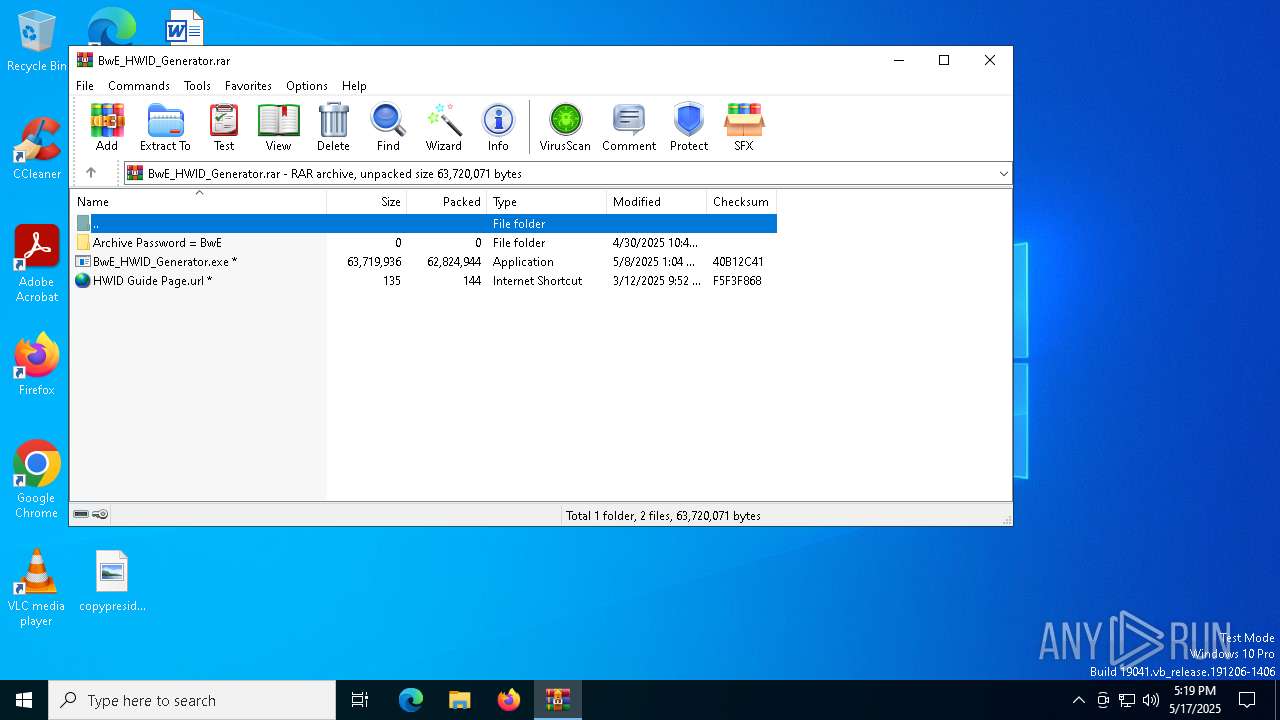
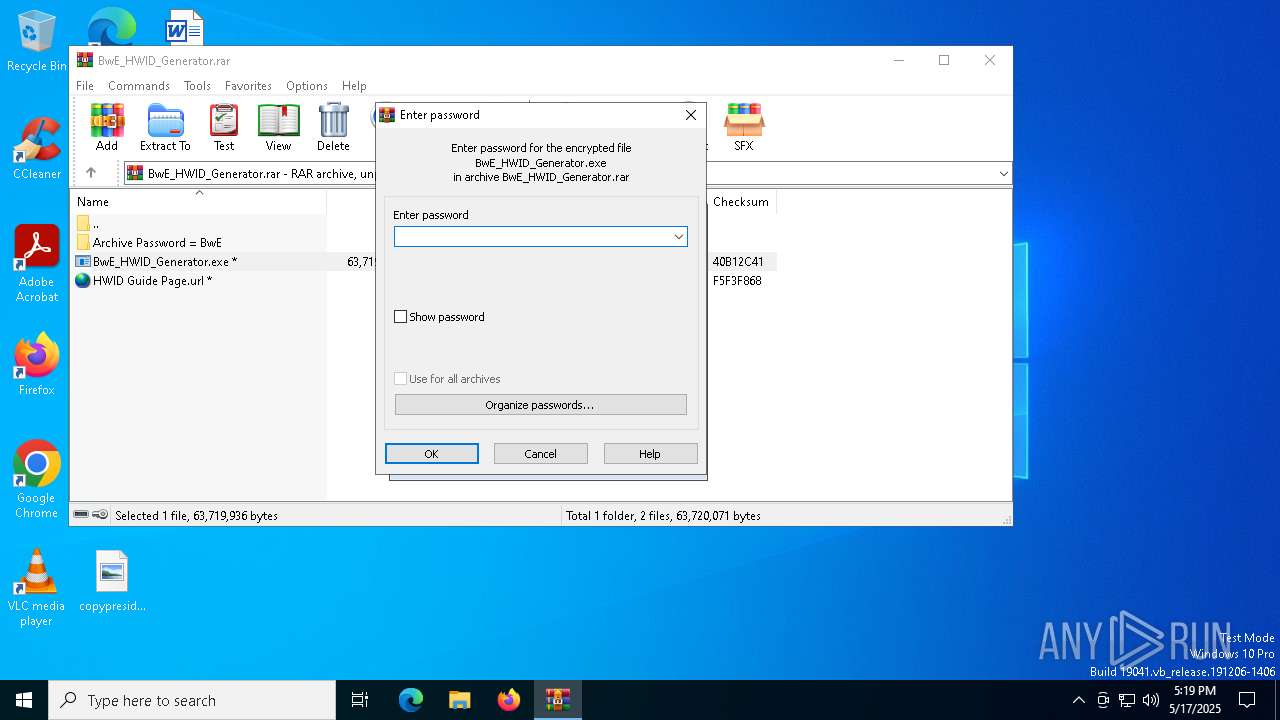
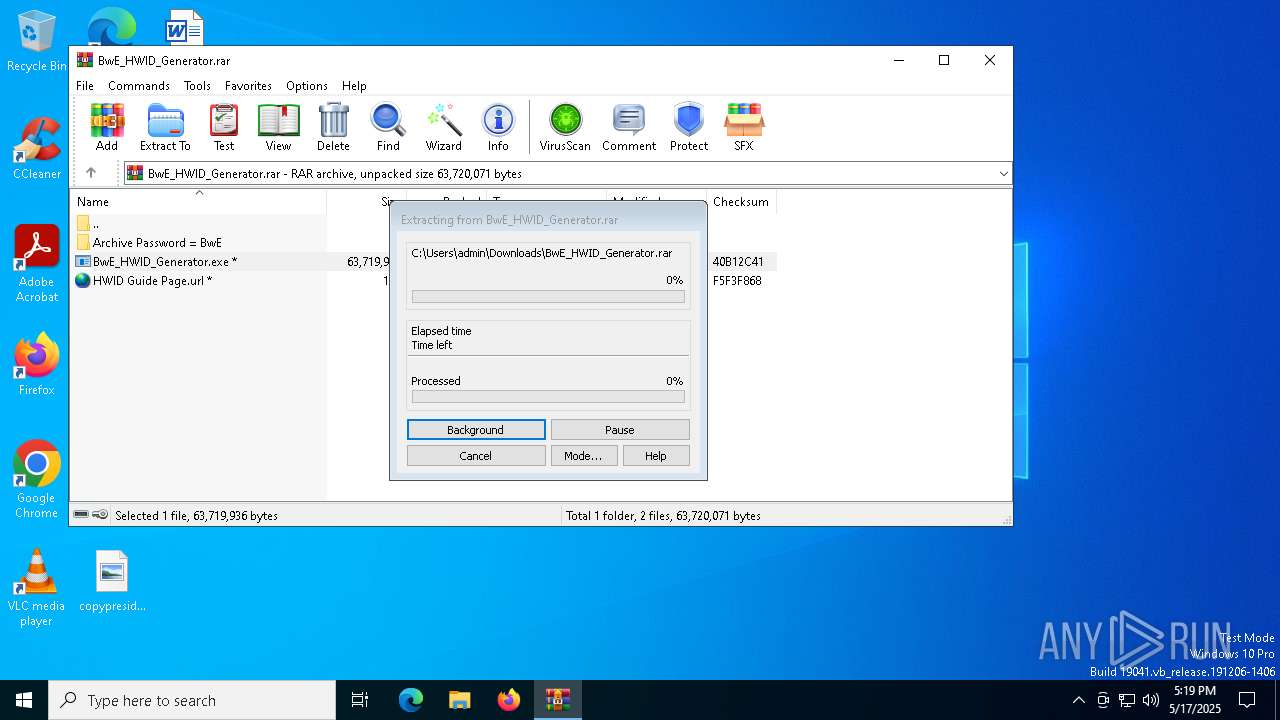
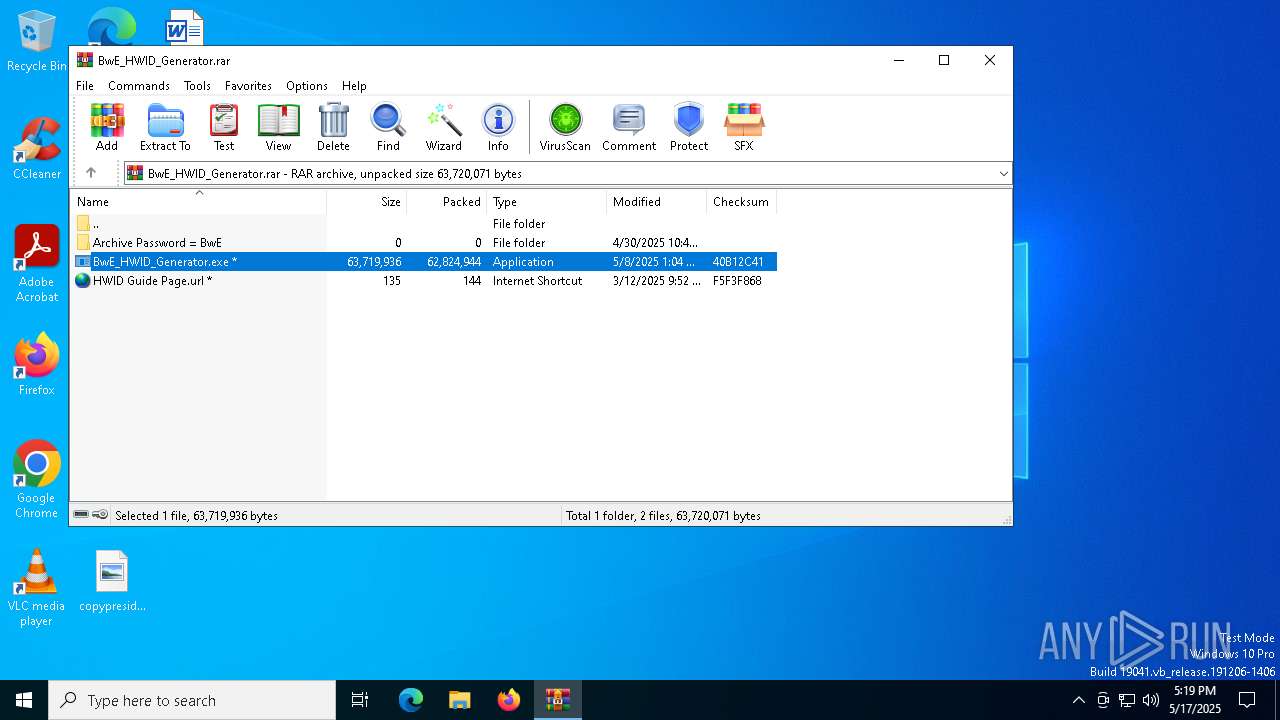
| URL: | https://betterwayelectronics.com.au/downloads/BwE_HWID_Generator.rar |
| Full analysis: | https://app.any.run/tasks/f2115e0b-59c1-4c84-aca9-3aaa7da860a1 |
| Verdict: | Malicious activity |
| Analysis date: | May 17, 2025, 17:18:06 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D3E41535ECBE64A46D70B8C0E3C1C512 |
| SHA1: | 8AFECBA7A7958DA5343BDDD49AF0F3ADAA47868B |
| SHA256: | F9864BFF3897CE3E4AE7977EC95CC6C3AA3BD25A033362E437366027F437EBC4 |
| SSDEEP: | 3:N8Oy34GxKo2BSLJ4KS/tyA6iq:2Oy34wfS/tUiq |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 5608)
Reads the BIOS version
- BwE_HWID_Generator.exe (PID: 7828)
- BwE_HWID_Generator.exe (PID: 7604)
- BwE_HWID.exe (PID: 4120)
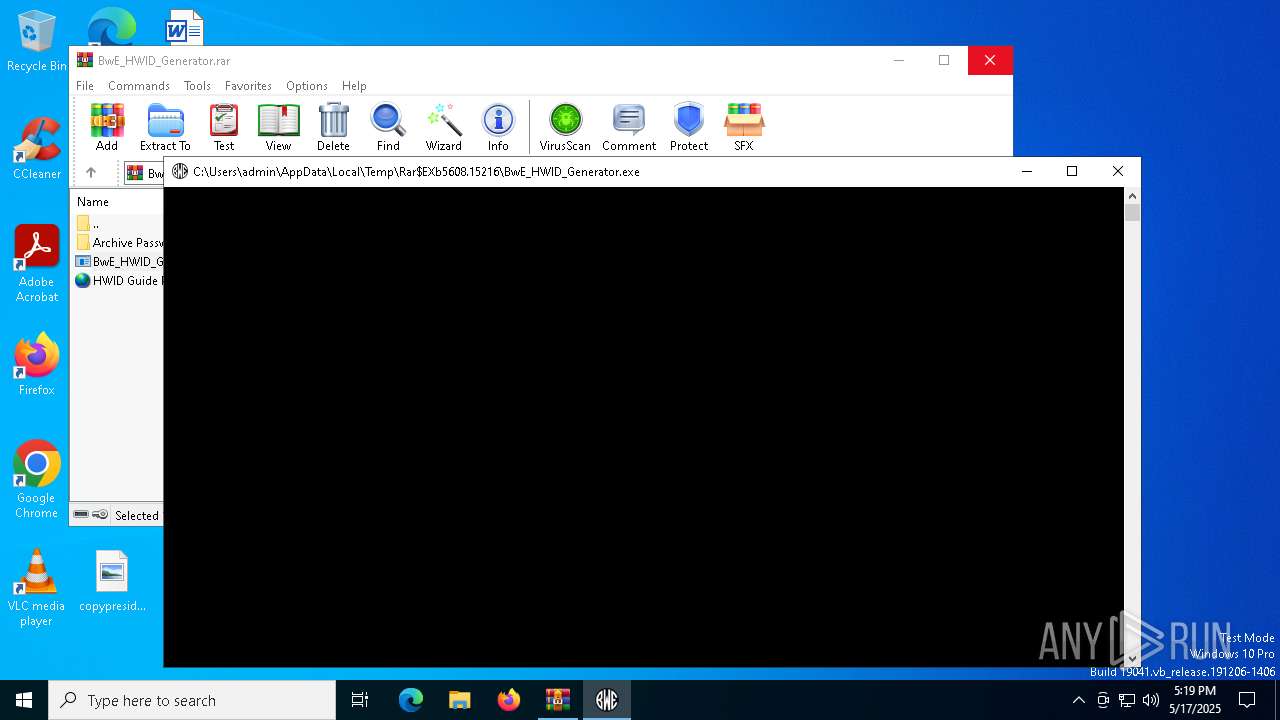
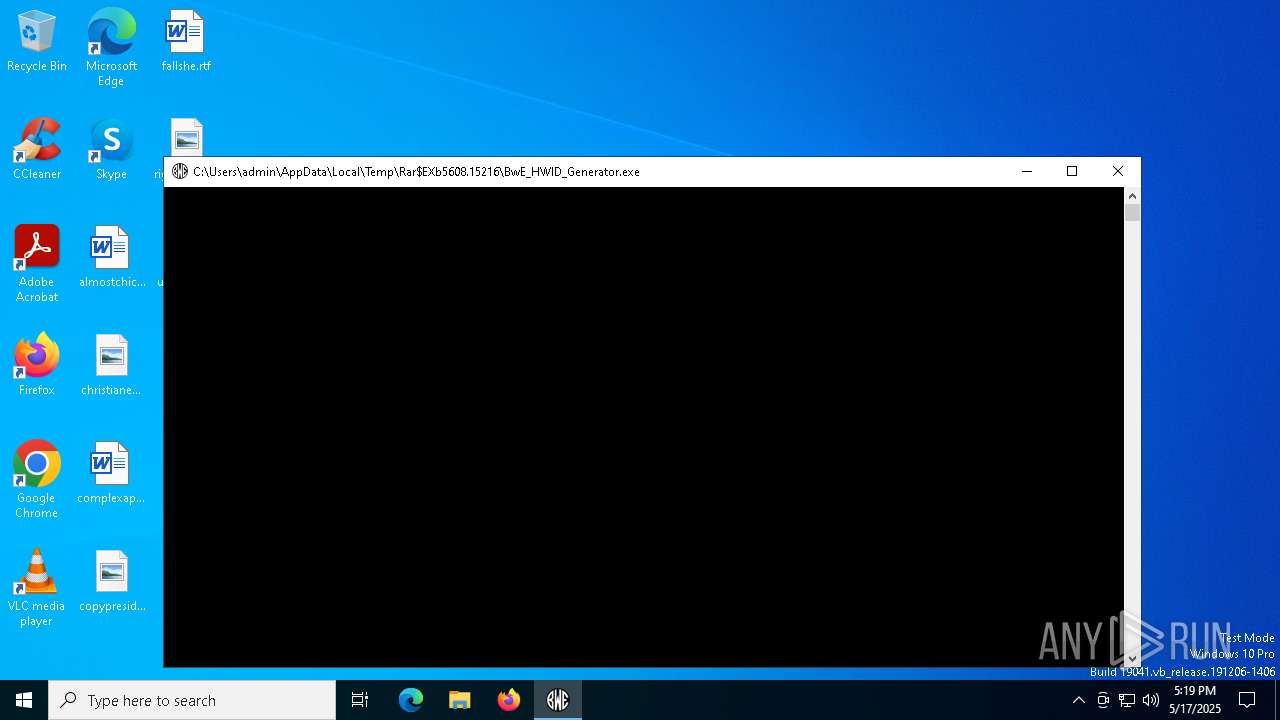
Process drops python dynamic module
- BwE_HWID_Generator.exe (PID: 7828)
Executable content was dropped or overwritten
- BwE_HWID_Generator.exe (PID: 7828)
- BwE_HWID_Generator.exe (PID: 7604)
The process drops C-runtime libraries
- BwE_HWID_Generator.exe (PID: 7828)
Process drops legitimate windows executable
- BwE_HWID_Generator.exe (PID: 7828)
There is functionality for taking screenshot (YARA)
- BwE_HWID_Generator.exe (PID: 7828)
There is functionality for VM detection VirtualBox (YARA)
- BwE_HWID_Generator.exe (PID: 7828)
There is functionality for VM detection antiVM strings (YARA)
- BwE_HWID_Generator.exe (PID: 7828)
Application launched itself
- BwE_HWID_Generator.exe (PID: 7828)
Loads Python modules
- BwE_HWID_Generator.exe (PID: 7604)
Checks for external IP
- svchost.exe (PID: 2196)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 7960)
- cmd.exe (PID: 7236)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 6156)
- WMIC.exe (PID: 8008)
Starts CMD.EXE for commands execution
- BwE_HWID_Generator.exe (PID: 7604)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7236)
INFO
Checks supported languages
- identity_helper.exe (PID: 5720)
- identity_helper.exe (PID: 3768)
- BwE_HWID_Generator.exe (PID: 7828)
- BwE_HWID_Generator.exe (PID: 7604)
- BwE_HWID.exe (PID: 4120)
Reads the computer name
- identity_helper.exe (PID: 5720)
- identity_helper.exe (PID: 3768)
- BwE_HWID_Generator.exe (PID: 7828)
- BwE_HWID_Generator.exe (PID: 7604)
Application launched itself
- msedge.exe (PID: 7268)
- msedge.exe (PID: 6372)
Reads Environment values
- identity_helper.exe (PID: 5720)
- identity_helper.exe (PID: 3768)
Reads Microsoft Office registry keys
- msedge.exe (PID: 7268)
Local mutex for internet shortcut management
- WinRAR.exe (PID: 5608)
Reads the software policy settings
- slui.exe (PID: 2432)
- slui.exe (PID: 536)
Creates files in the program directory
- BwE_HWID_Generator.exe (PID: 7828)
Create files in a temporary directory
- BwE_HWID_Generator.exe (PID: 7828)
- BwE_HWID_Generator.exe (PID: 7604)
- BwE_HWID.exe (PID: 4120)
Compiled with Borland Delphi (YARA)
- BwE_HWID_Generator.exe (PID: 7828)
PyInstaller has been detected (YARA)
- BwE_HWID_Generator.exe (PID: 7828)
Checks proxy server information
- BwE_HWID_Generator.exe (PID: 7604)
- slui.exe (PID: 536)
The sample compiled with english language support
- BwE_HWID_Generator.exe (PID: 7828)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 8008)
- WMIC.exe (PID: 6156)
Reads the machine GUID from the registry
- BwE_HWID.exe (PID: 4120)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
198
Monitored processes
66
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://betterwayelectronics.com.au/downloads/BwE_HWID_Generator.rar" | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 924 | reg query "HKCU\Control Panel\International\Geo" /v Name | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1056 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6812 --field-trial-handle=2408,i,10688434874705909448,10897742450750749108,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1056 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7048 --field-trial-handle=2408,i,10688434874705909448,10897742450750749108,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1128 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5632 --field-trial-handle=2408,i,10688434874705909448,10897742450750749108,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2064 | findstr /v UUID | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2088 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4352 --field-trial-handle=2436,i,7993439000096343039,11984614905291263737,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2240 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=1336 --field-trial-handle=2408,i,10688434874705909448,10897742450750749108,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
13 478
Read events
13 429
Write events
49
Delete events
0
Modification events
| (PID) Process: | (7268) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 83BEEB5DEE932F00 | |||
| (PID) Process: | (7268) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 2EE3F25DEE932F00 | |||
| (PID) Process: | (7268) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328524 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {50DEE102-2152-428C-8205-B00B0EA6A63F} | |||
| (PID) Process: | (7268) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328524 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {25FEE52D-2FCD-46A7-964D-1C9AD3740B3C} | |||
| (PID) Process: | (300) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (300) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (300) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (300) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (300) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (300) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
Executable files
205
Suspicious files
782
Text files
84
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b8e2.TMP | — | |
MD5:— | SHA256:— | |||
| 7268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b8e2.TMP | — | |
MD5:— | SHA256:— | |||
| 7268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b901.TMP | — | |
MD5:— | SHA256:— | |||
| 7268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b920.TMP | — | |
MD5:— | SHA256:— | |||
| 7268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b930.TMP | — | |
MD5:— | SHA256:— | |||
| 7268 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
69
DNS requests
56
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.21:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5544 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5544 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7756 | svchost.exe | HEAD | 200 | 208.89.74.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4b01f7e3-1016-48fe-9466-15e9587c9c82?P1=1747703938&P2=404&P3=2&P4=hoQ8bRyBLwiE1ldayioYCoX2b09wH81rYX3NgZKTueTXoibkL%2fMM6jhV8s7bH58QruAqkz9PKDryqB06Gzy%2fcg%3d%3d | unknown | — | — | whitelisted |
7756 | svchost.exe | GET | 206 | 208.89.74.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4b01f7e3-1016-48fe-9466-15e9587c9c82?P1=1747703938&P2=404&P3=2&P4=hoQ8bRyBLwiE1ldayioYCoX2b09wH81rYX3NgZKTueTXoibkL%2fMM6jhV8s7bH58QruAqkz9PKDryqB06Gzy%2fcg%3d%3d | unknown | — | — | whitelisted |
7756 | svchost.exe | GET | 206 | 208.89.74.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4b01f7e3-1016-48fe-9466-15e9587c9c82?P1=1747703938&P2=404&P3=2&P4=hoQ8bRyBLwiE1ldayioYCoX2b09wH81rYX3NgZKTueTXoibkL%2fMM6jhV8s7bH58QruAqkz9PKDryqB06Gzy%2fcg%3d%3d | unknown | — | — | whitelisted |
7756 | svchost.exe | GET | 206 | 208.89.74.27:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4b01f7e3-1016-48fe-9466-15e9587c9c82?P1=1747703938&P2=404&P3=2&P4=hoQ8bRyBLwiE1ldayioYCoX2b09wH81rYX3NgZKTueTXoibkL%2fMM6jhV8s7bH58QruAqkz9PKDryqB06Gzy%2fcg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.216.77.21:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7512 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7512 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7512 | msedge.exe | 13.107.253.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7512 | msedge.exe | 103.27.34.23:443 | betterwayelectronics.com.au | SYNERGY WHOLESALE PTY LTD | AU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
betterwayelectronics.com.au |
| unknown |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
edgeservices.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET INFO Observed External IP Lookup Domain in DNS Lookup (myip .wtf) |
7604 | BwE_HWID_Generator.exe | Misc activity | ET INFO Observed External IP Loopkup Domain (myip .wtf in TLS SNI) |
7604 | BwE_HWID_Generator.exe | Misc activity | ET INFO Observed External IP Loopkup Domain (myip .wtf in TLS SNI) |
7604 | BwE_HWID_Generator.exe | Misc activity | ET INFO Observed External IP Loopkup Domain (myip .wtf in TLS SNI) |