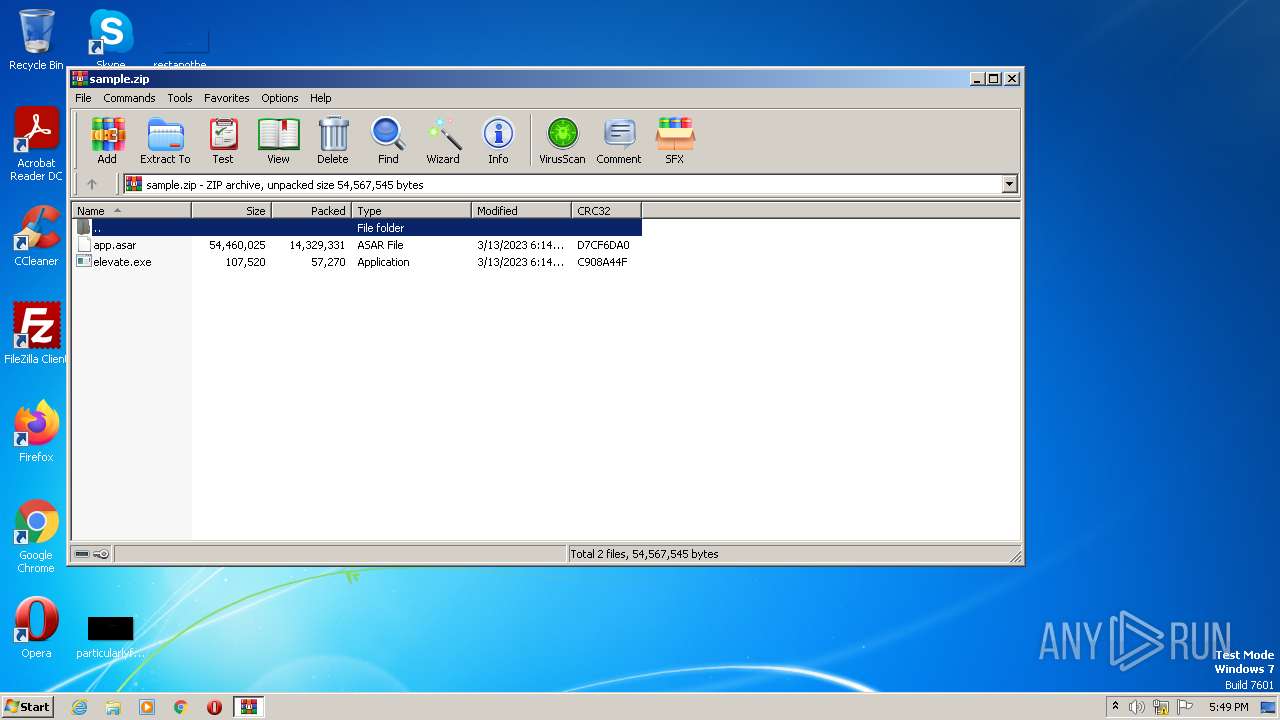
| File name: | sample.zip |
| Full analysis: | https://app.any.run/tasks/1a9b4db2-4b88-431e-a43e-86508a3f83d1 |
| Verdict: | Malicious activity |
| Analysis date: | March 15, 2023, 17:49:43 |
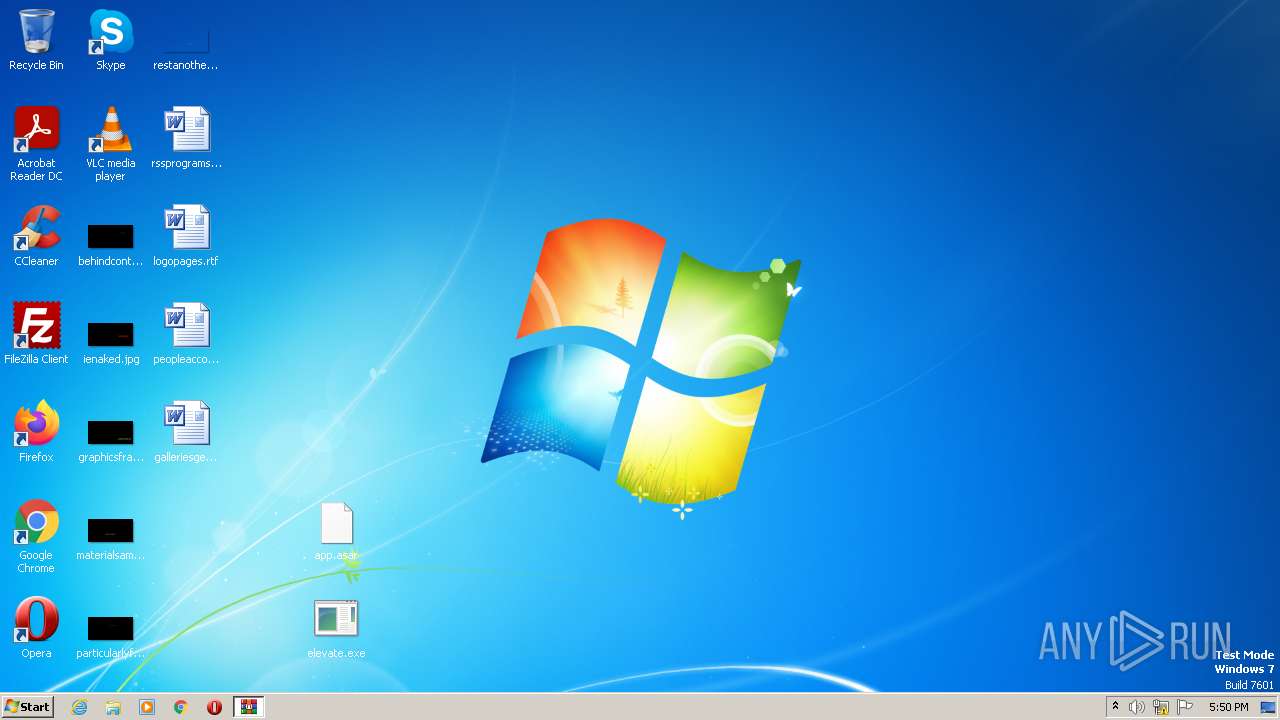
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 8EECAEE36E2DD7B00C930DD652086308 |
| SHA1: | FC66B76179D557B9CD81FA8F98A4A78059684467 |
| SHA256: | F96D31AD3DC0C02044331ECDC669F0F6C8A2F9C79A044A388B62886459500894 |
| SSDEEP: | 393216:k7ENg9OwIFH4GWqgxZH38sgn3jscKMqq/+gnA5IphIqW0:tgo5Bgxx8HnTsSqqn20 |
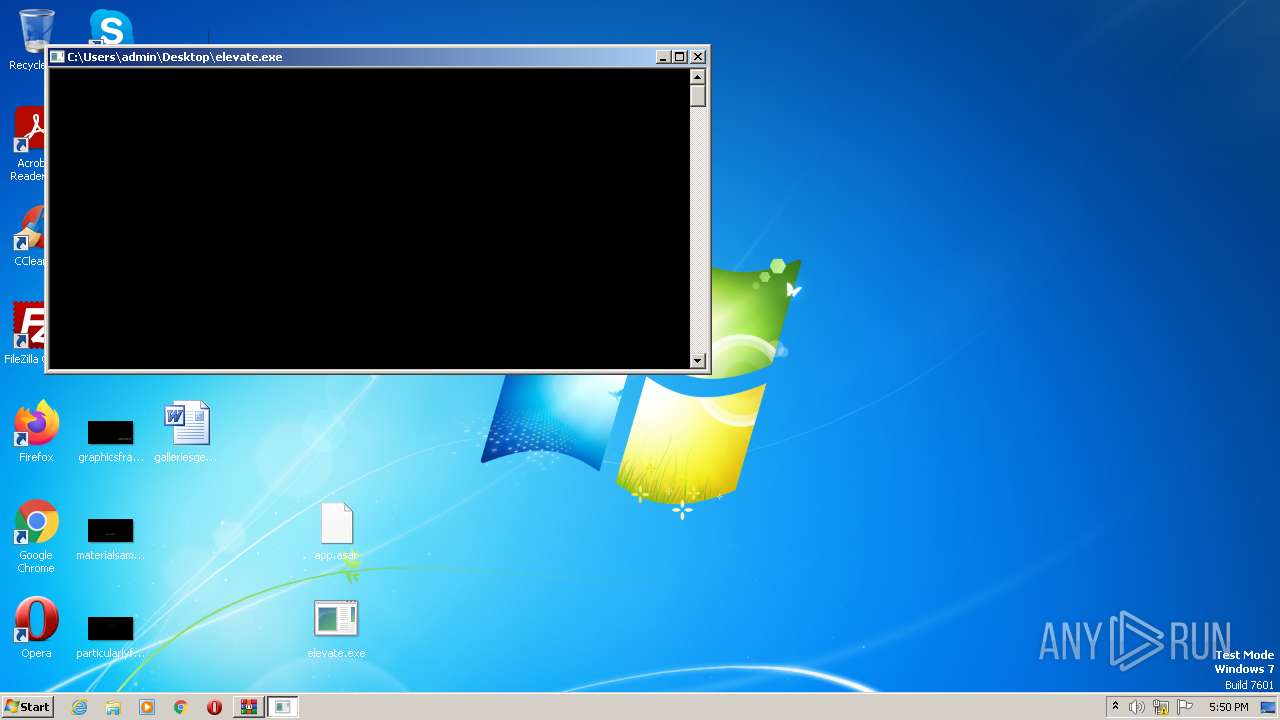
MALICIOUS
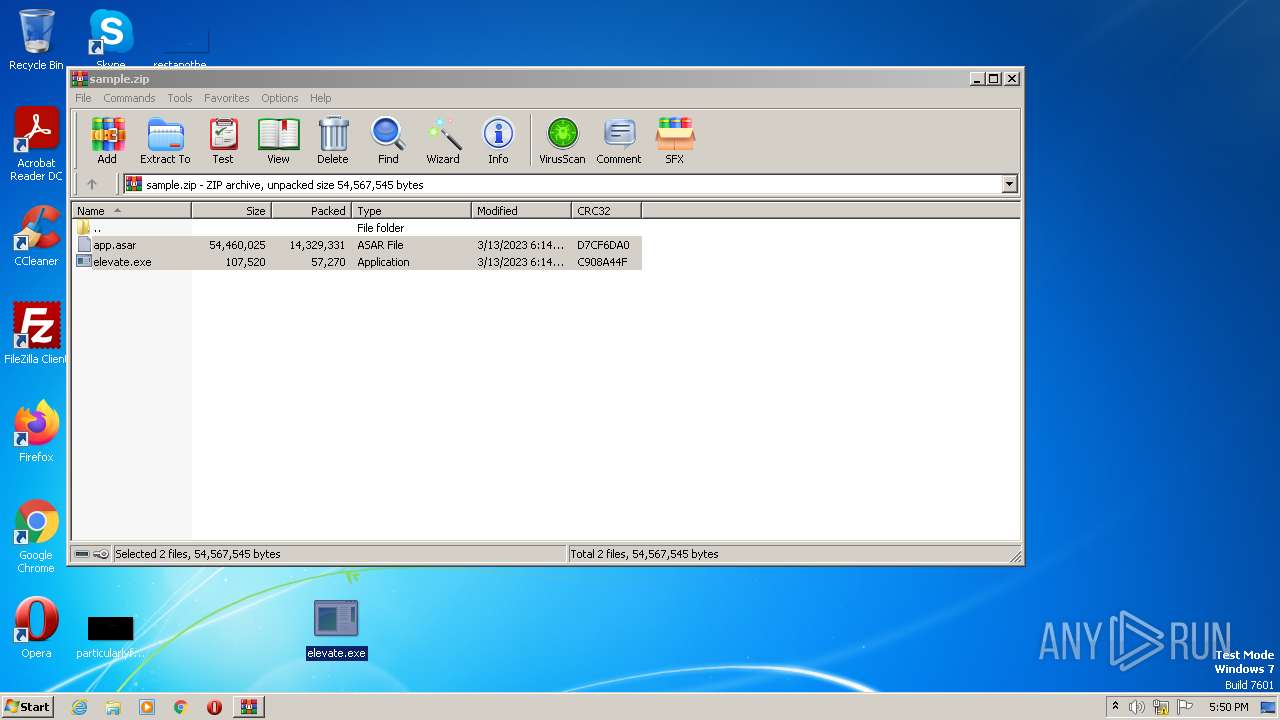
Application was dropped or rewritten from another process
- elevate.exe (PID: 1820)
- elevate.exe (PID: 3856)
- elevate.exe (PID: 1592)
- elevate.exe (PID: 2464)
SUSPICIOUS
No suspicious indicators.INFO
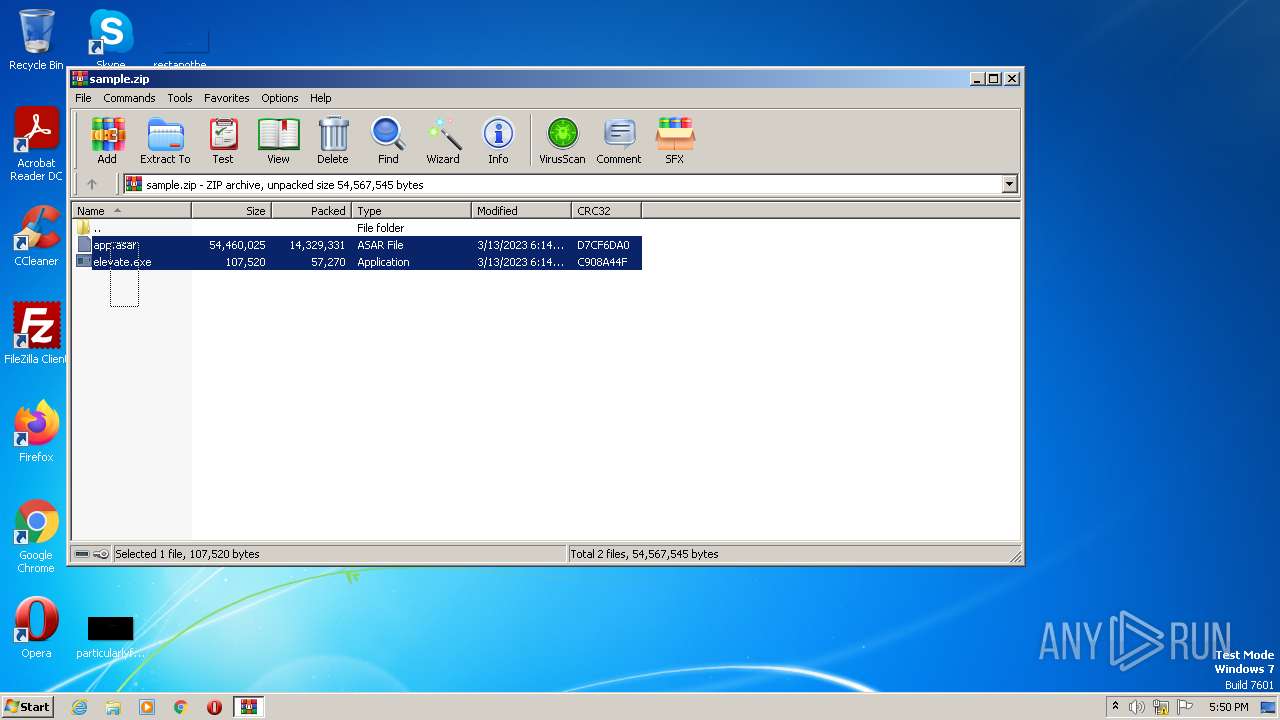
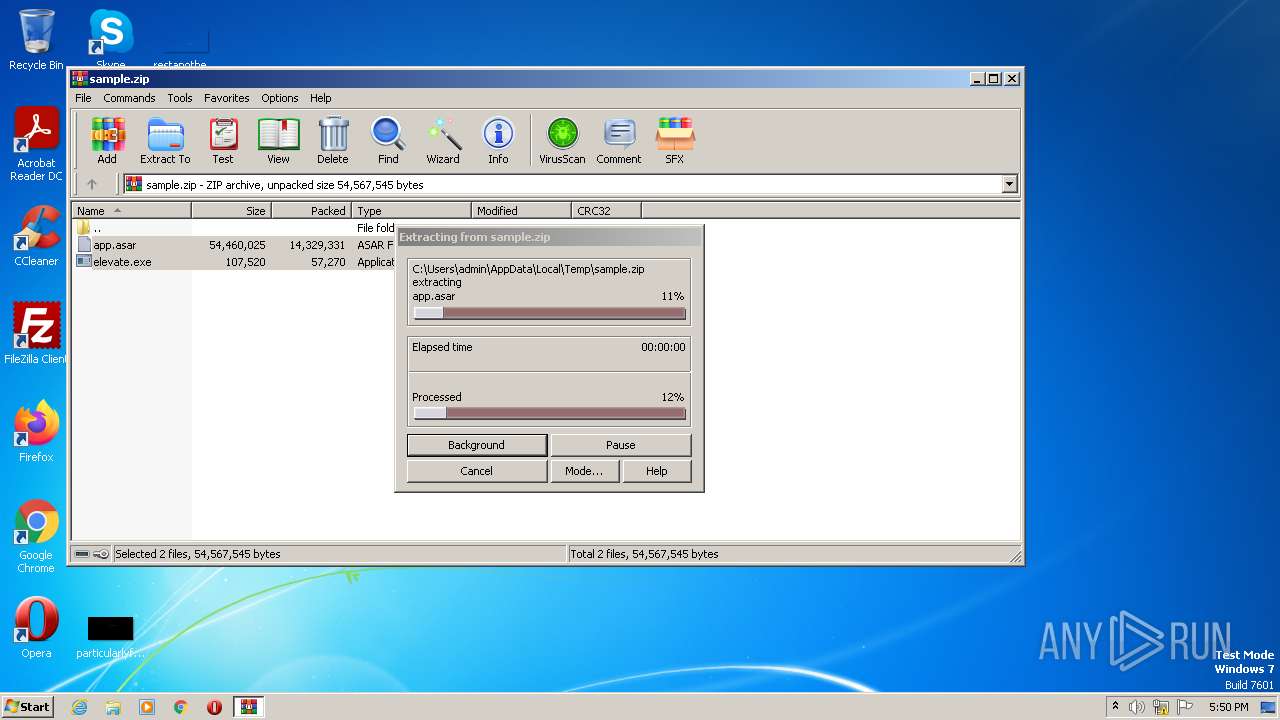
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2672)
Manual execution by a user
- elevate.exe (PID: 3856)
- elevate.exe (PID: 1820)
- elevate.exe (PID: 1592)
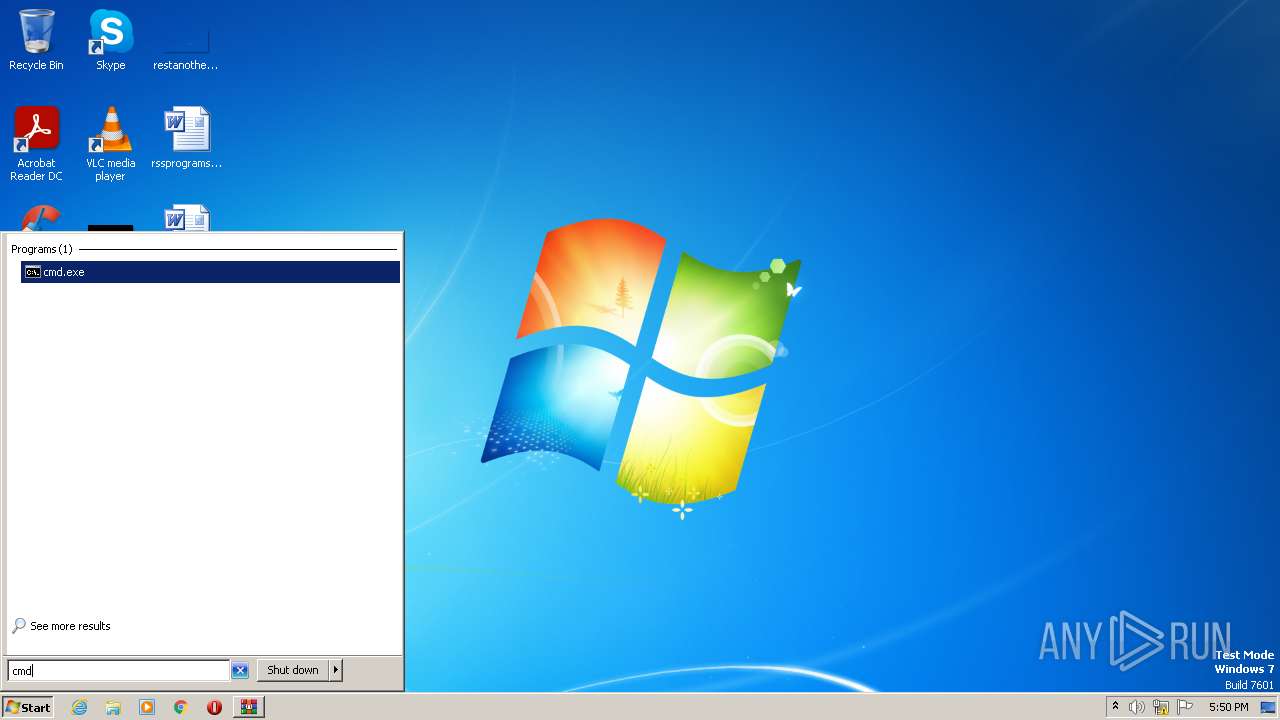
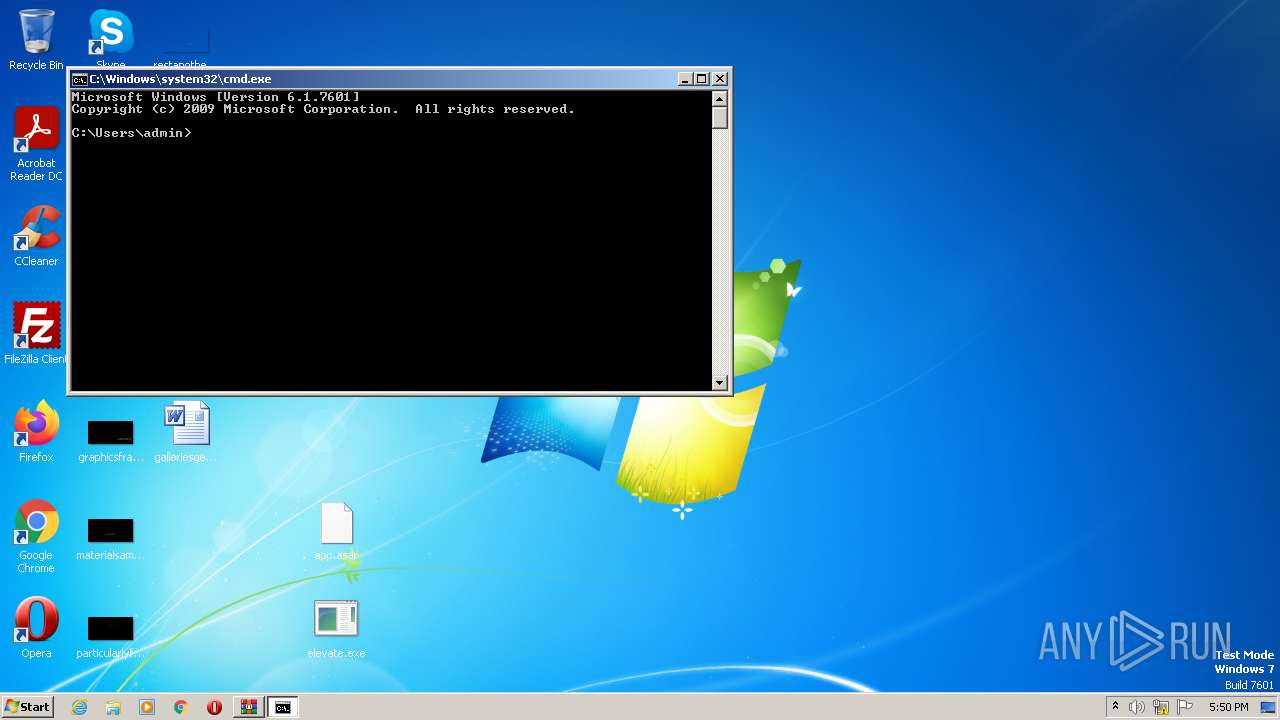
- cmd.exe (PID: 1012)
- chrome.exe (PID: 3608)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 2672)
Checks supported languages
- elevate.exe (PID: 3856)
- elevate.exe (PID: 1820)
- elevate.exe (PID: 1592)
- elevate.exe (PID: 2464)
The process checks LSA protection
- elevate.exe (PID: 1820)
- elevate.exe (PID: 1592)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 2672)
Application launched itself
- chrome.exe (PID: 3608)
Create files in a temporary directory
- chrome.exe (PID: 3608)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipFileName: | app.asar |
|---|---|
| ZipUncompressedSize: | 54460025 |
| ZipCompressedSize: | 14329331 |
| ZipCRC: | 0xd7cf6da0 |
| ZipModifyDate: | 2023:03:13 19:14:28 |
| ZipCompression: | Deflated |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 20 |
Total processes
70
Monitored processes
29
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1032,11124257950795601192,13915771213505298432,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=964 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1032,11124257950795601192,13915771213505298432,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1892 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1012 | "C:\Windows\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1592 | "C:\Users\admin\Desktop\elevate.exe" C:\Users\admin\Desktop\app.asar | C:\Users\admin\Desktop\elevate.exe | — | explorer.exe | |||||||||||
User: admin Company: Johannes Passing Integrity Level: MEDIUM Description: Elevate Exit code: 1 Version: 1, 0, 0, 2894 Modules
| |||||||||||||||
| 1820 | "C:\Users\admin\Desktop\elevate.exe" C:\Users\admin\Desktop\app.asar | C:\Users\admin\Desktop\elevate.exe | — | explorer.exe | |||||||||||
User: admin Company: Johannes Passing Integrity Level: MEDIUM Description: Elevate Exit code: 1 Version: 1, 0, 0, 2894 Modules
| |||||||||||||||
| 2236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1032,11124257950795601192,13915771213505298432,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=536 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2264 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1032,11124257950795601192,13915771213505298432,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2084 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6ec1d988,0x6ec1d998,0x6ec1d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,11124257950795601192,13915771213505298432,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2788 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2464 | elevate | C:\Users\admin\Desktop\elevate.exe | — | cmd.exe | |||||||||||
User: admin Company: Johannes Passing Integrity Level: MEDIUM Description: Elevate Exit code: 0 Version: 1, 0, 0, 2894 Modules
| |||||||||||||||
Total events
19 788
Read events
19 522
Write events
252
Delete events
14
Modification events
| (PID) Process: | (2672) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2672) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2672) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2672) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (2672) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2672) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2672) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2672) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3608) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3608) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
Executable files
2
Suspicious files
240
Text files
284
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2672 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2672.9401\app.asar | — | |
MD5:— | SHA256:— | |||
| 3608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6412057F-E18.pma | — | |
MD5:— | SHA256:— | |||
| 3608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 3608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e63f8575-2098-4ad3-8ccf-5a414b82ed5f.tmp | text | |
MD5:— | SHA256:— | |||
| 2916 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\index | binary | |
MD5:— | SHA256:— | |||
| 3608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:EF1D5606A483BB6C72C81A3F649BEB18 | SHA256:BA083E7585ADA9936944FE56BC0141A544F18A01C3424E5C9F02375B34FE3D45 | |||
| 2916 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\data_0 | vxd | |
MD5:CF89D16BB9107C631DAABF0C0EE58EFB | SHA256:D6A5FE39CD672781B256E0E3102F7022635F1D4BB7CFCC90A80FFFE4D0F3877E | |||
| 3608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 3608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 2672 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2672.9401\elevate.exe | executable | |
MD5:792B92C8AD13C46F27C7CED0810694DF | SHA256:9B1FBF0C11C520AE714AF8AA9AF12CFD48503EEDECD7398D8992EE94D1B4DC37 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
27
DNS requests
22
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
860 | svchost.exe | GET | — | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | — | — | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 5.84 Kb | whitelisted |
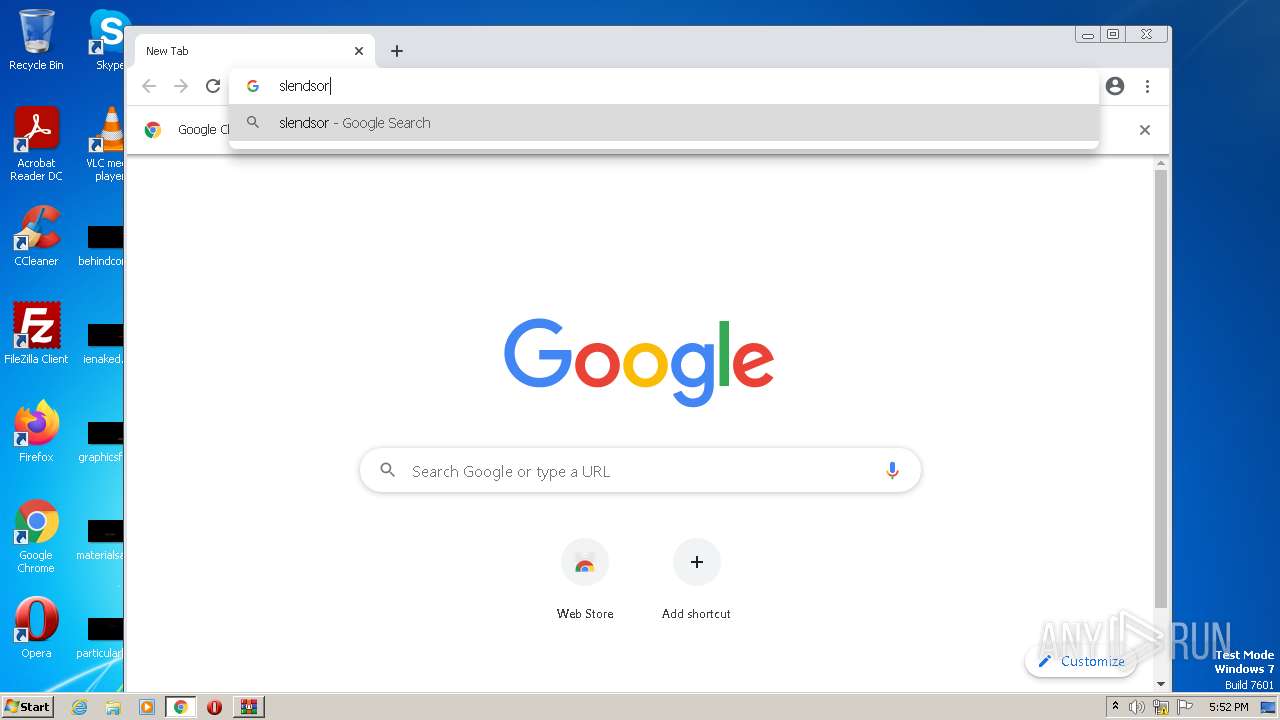
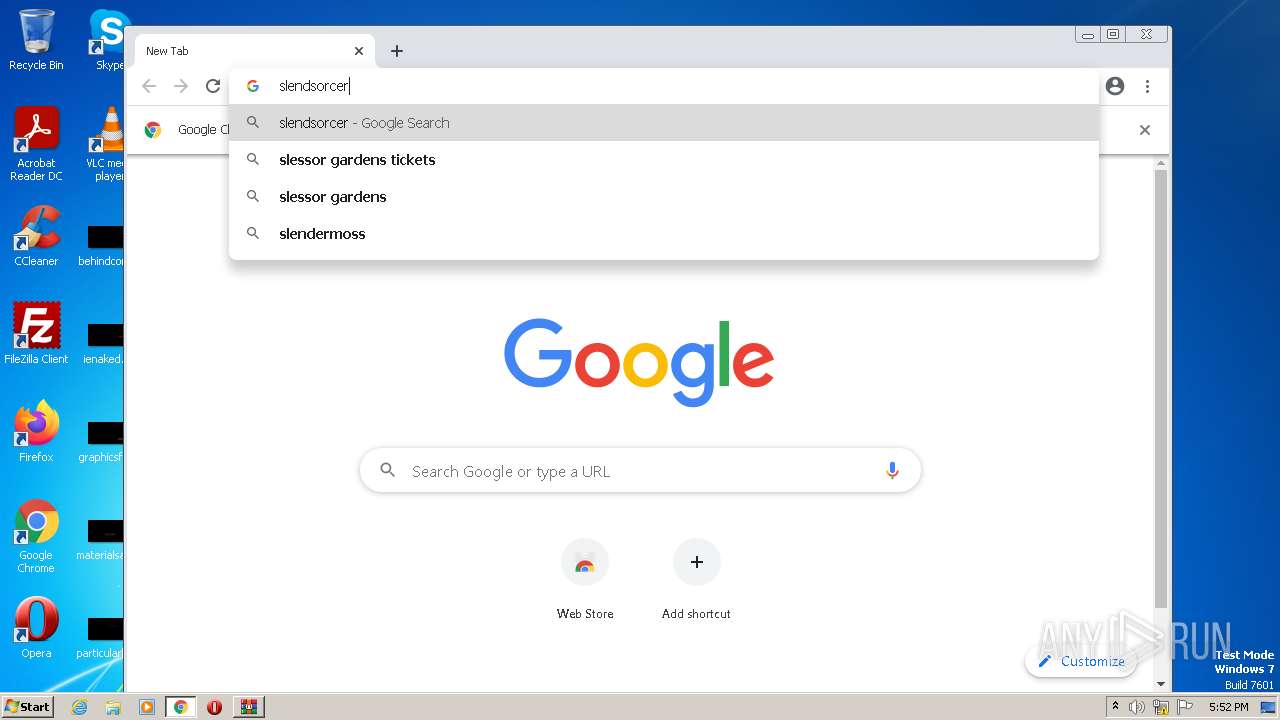
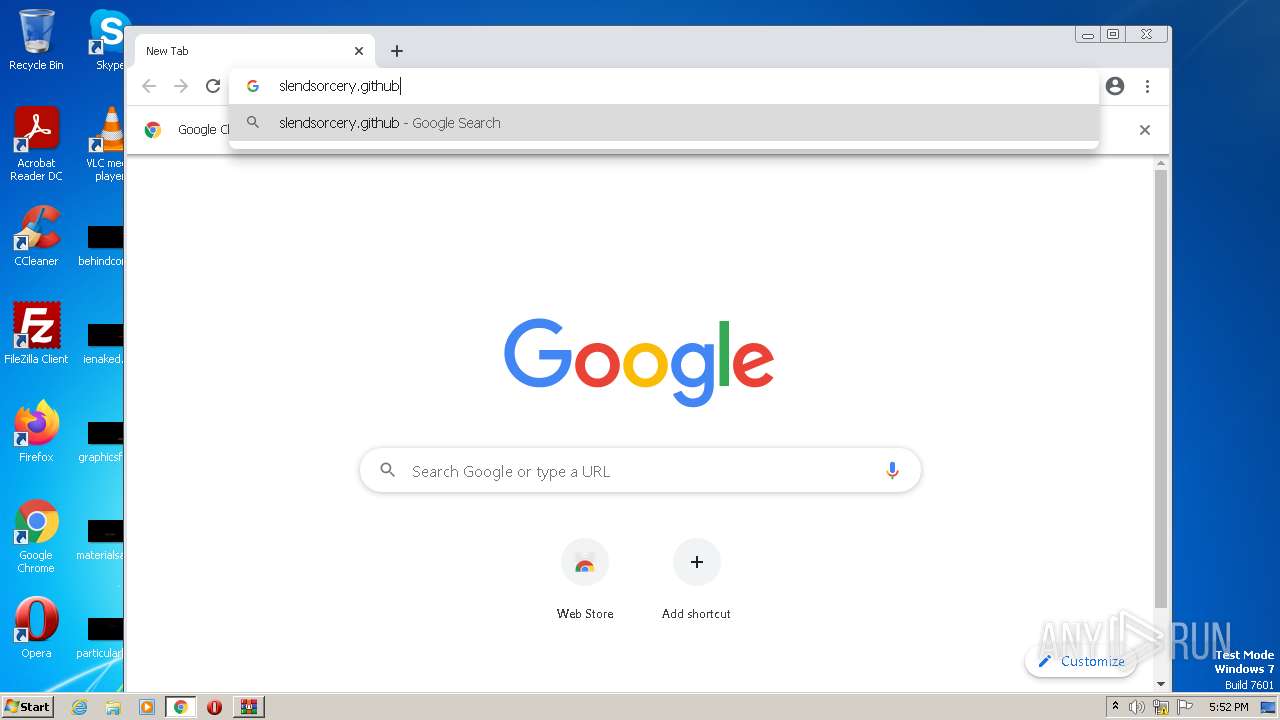
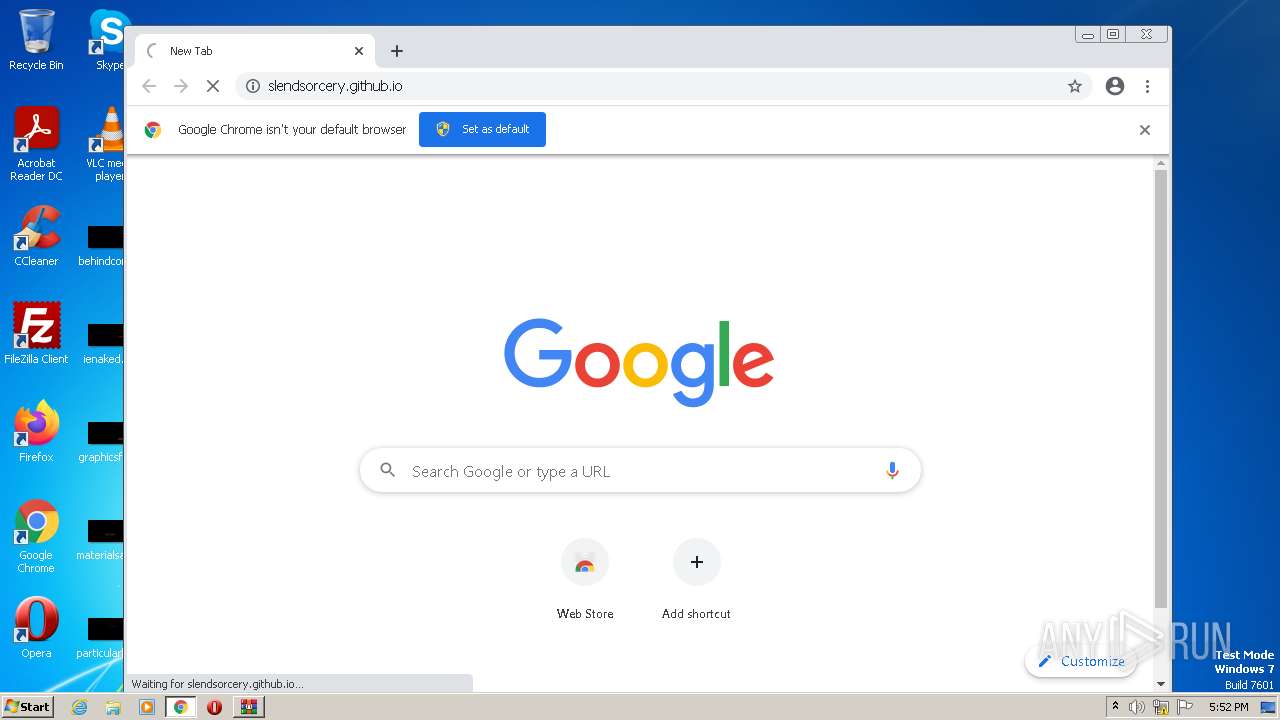
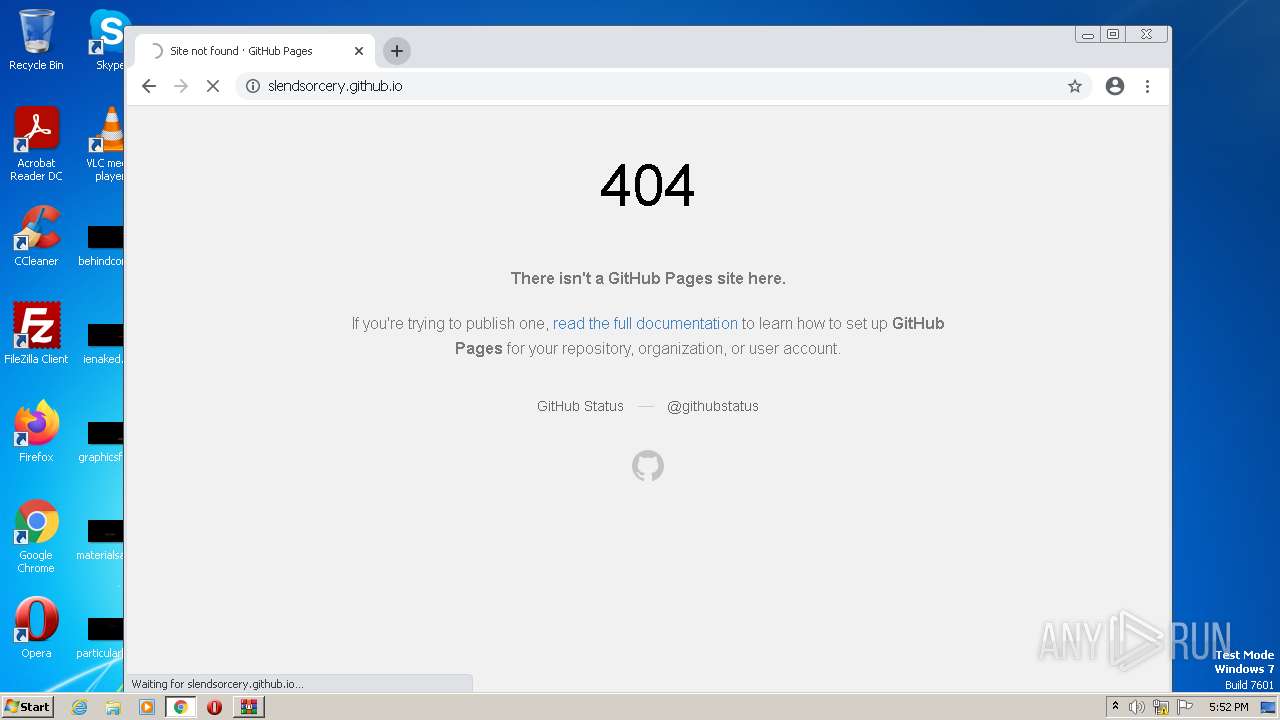
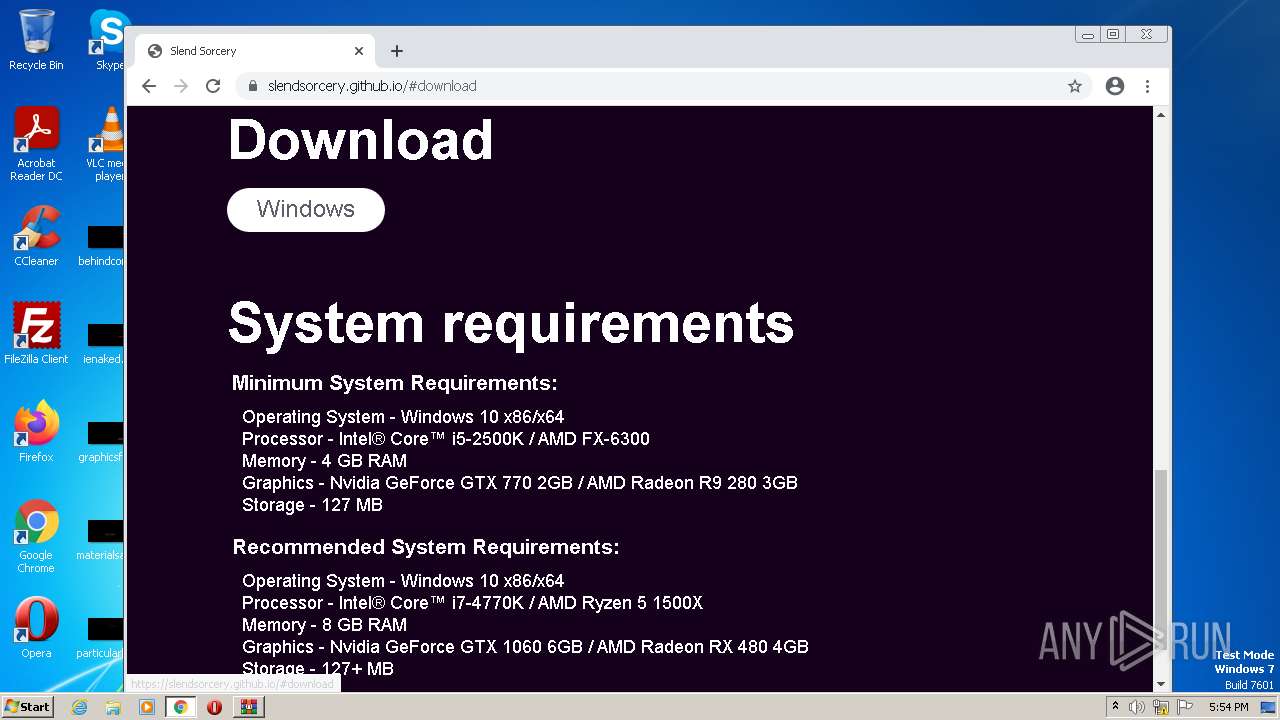
2916 | chrome.exe | GET | 301 | 185.199.110.153:80 | http://slendsorcery.github.io/ | NL | html | 162 b | malicious |
2916 | chrome.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | crx | 242 Kb | whitelisted |
2916 | chrome.exe | GET | 404 | 185.199.110.153:80 | http://slendsocery.github.io/ | NL | html | 5.02 Kb | malicious |
2916 | chrome.exe | GET | — | 185.199.110.153:80 | http://slendsorcery.github.io/ | NL | — | — | malicious |
860 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2916 | chrome.exe | 216.58.212.173:443 | accounts.google.com | GOOGLE | US | whitelisted |
2916 | chrome.exe | 142.250.186.36:443 | www.google.com | GOOGLE | US | whitelisted |
2916 | chrome.exe | 216.58.212.131:443 | ssl.gstatic.com | GOOGLE | US | whitelisted |
2916 | chrome.exe | 142.250.186.131:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
2916 | chrome.exe | 142.250.181.227:443 | update.googleapis.com | GOOGLE | US | whitelisted |
2916 | chrome.exe | 34.104.35.123:80 | edgedl.me.gvt1.com | GOOGLE | US | whitelisted |
— | — | 142.250.186.99:443 | www.gstatic.com | GOOGLE | US | whitelisted |
860 | svchost.exe | 34.104.35.123:80 | edgedl.me.gvt1.com | GOOGLE | US | whitelisted |
2916 | chrome.exe | 216.58.212.142:443 | clients1.google.com | GOOGLE | US | whitelisted |
2916 | chrome.exe | 185.199.110.153:80 | slendsorcery.github.io | FASTLY | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2916 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM TIMEWAIT ACK with wrong seq |
2916 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM TIMEWAIT ACK with wrong seq |
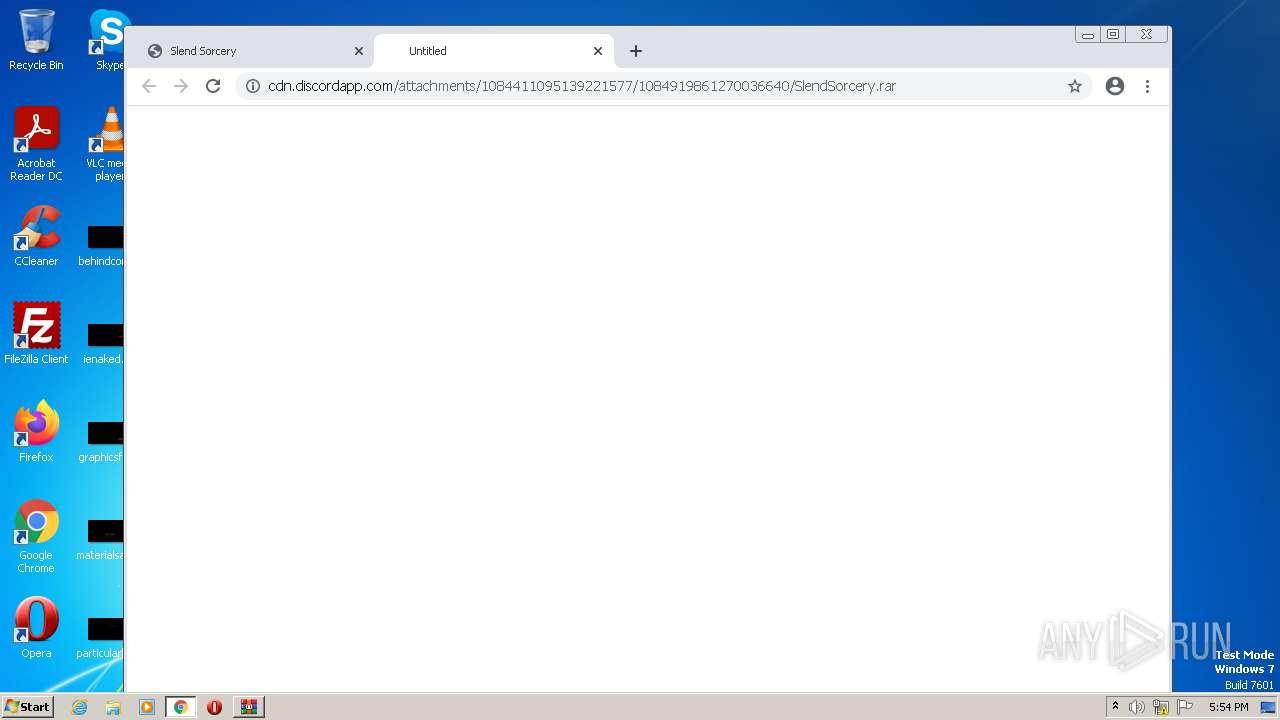
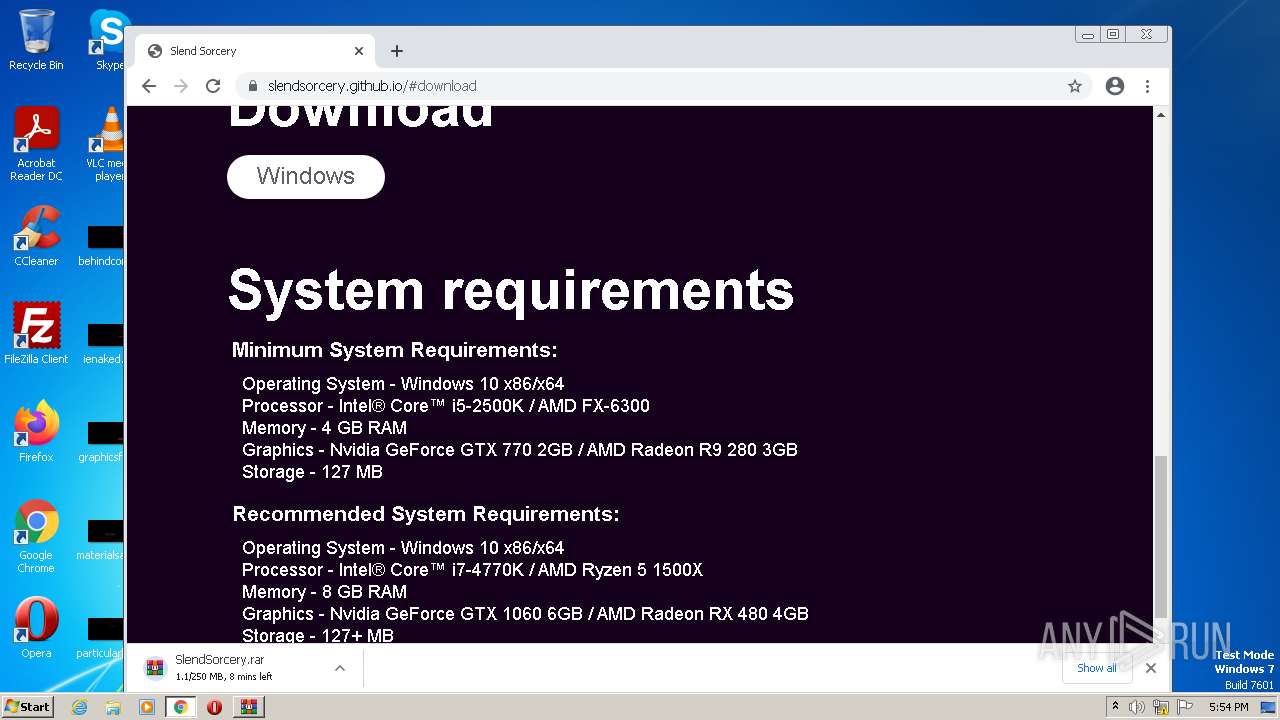
— | — | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
2916 | chrome.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |
2916 | chrome.exe | Misc activity | ET INFO Observed Discord Domain (discordapp .com in TLS SNI) |