| File name: | MediCat_Installer.exe |
| Full analysis: | https://app.any.run/tasks/1123a437-4fcf-4b29-b93b-227f387d3b35 |
| Verdict: | Malicious activity |
| Analysis date: | May 22, 2023, 17:33:45 |
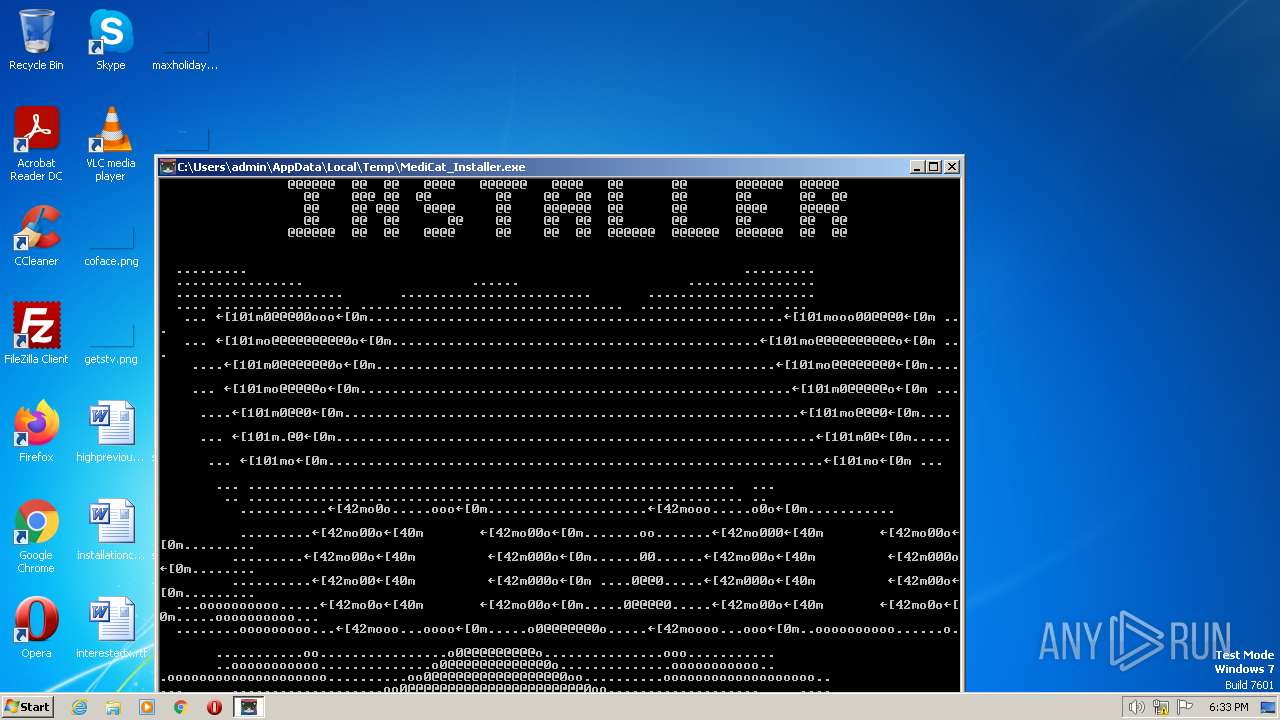
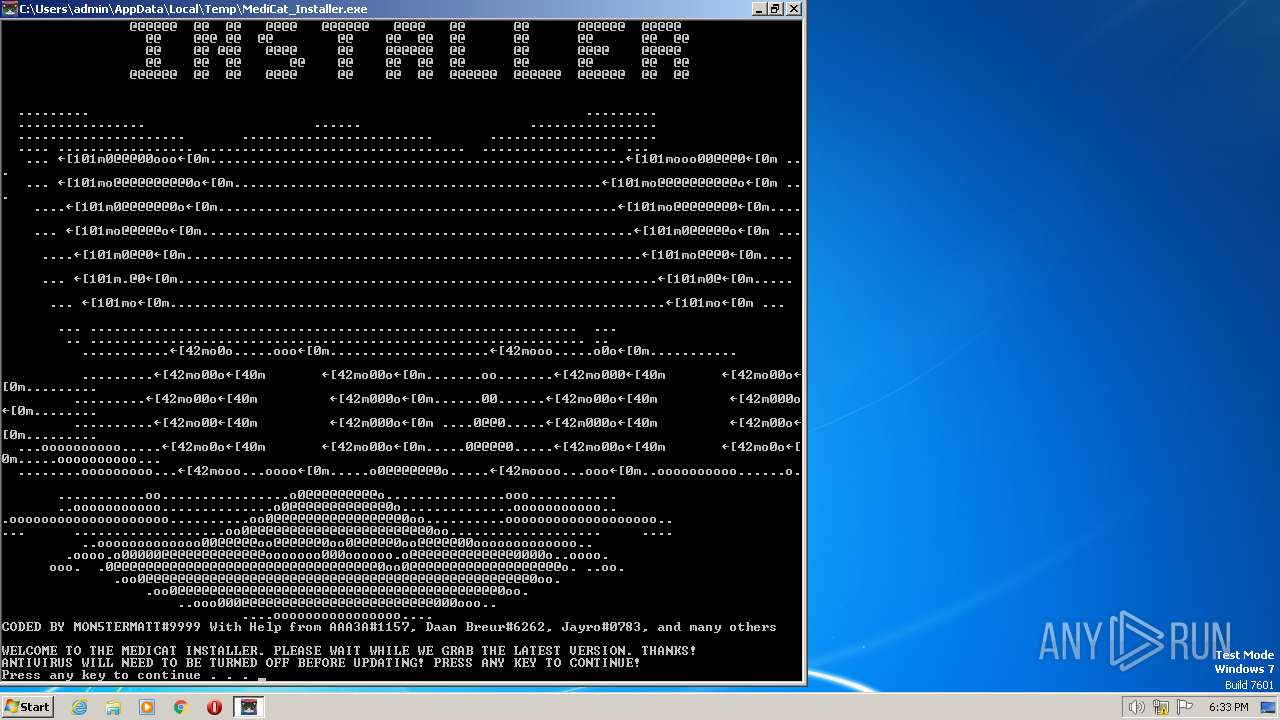
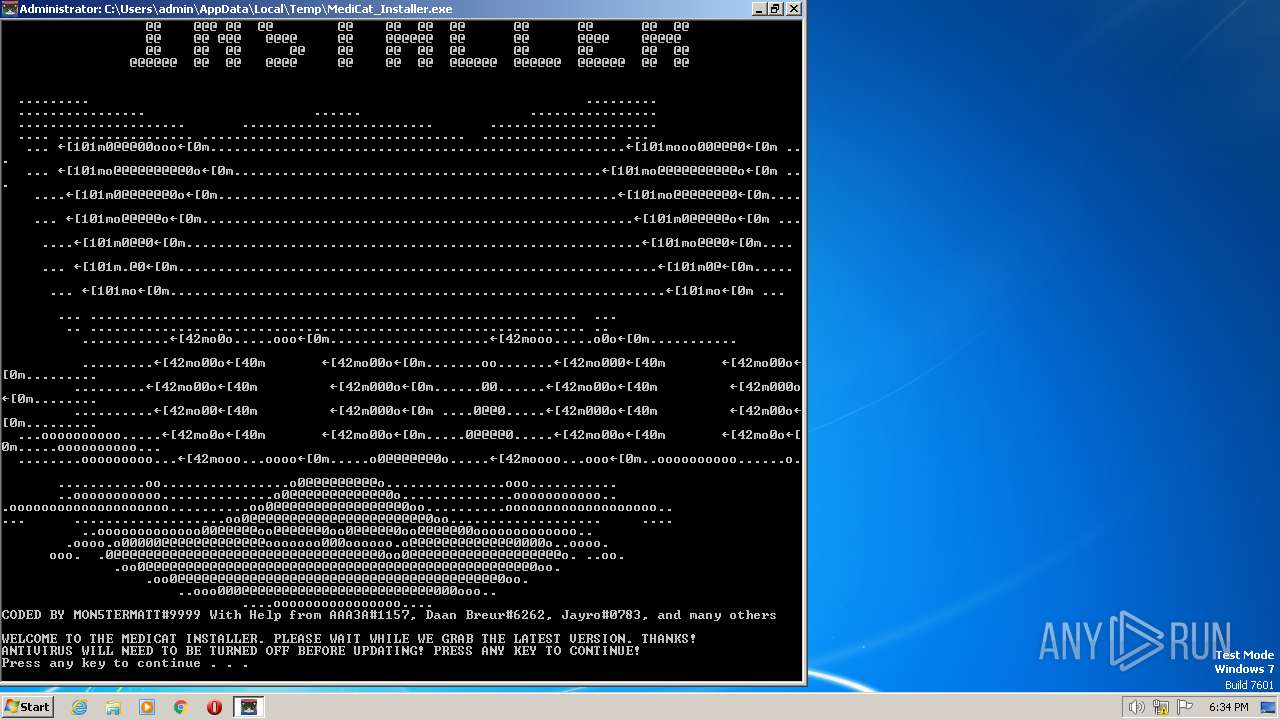
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | D189452FD279C9074B3A6FAAB5462D70 |
| SHA1: | E19DC7B20219D61C5587DC754F676B67F7B77956 |
| SHA256: | F9622474351E5548B63E5136081A50AA20AEFE42644CF57A4D5824D77BB42A2F |
| SSDEEP: | 6144:6bY3pmjANFdjohb1b3e2Ew1tCpxXDpIglzNu8:kY3pmDr1Ap9DV |
MALICIOUS
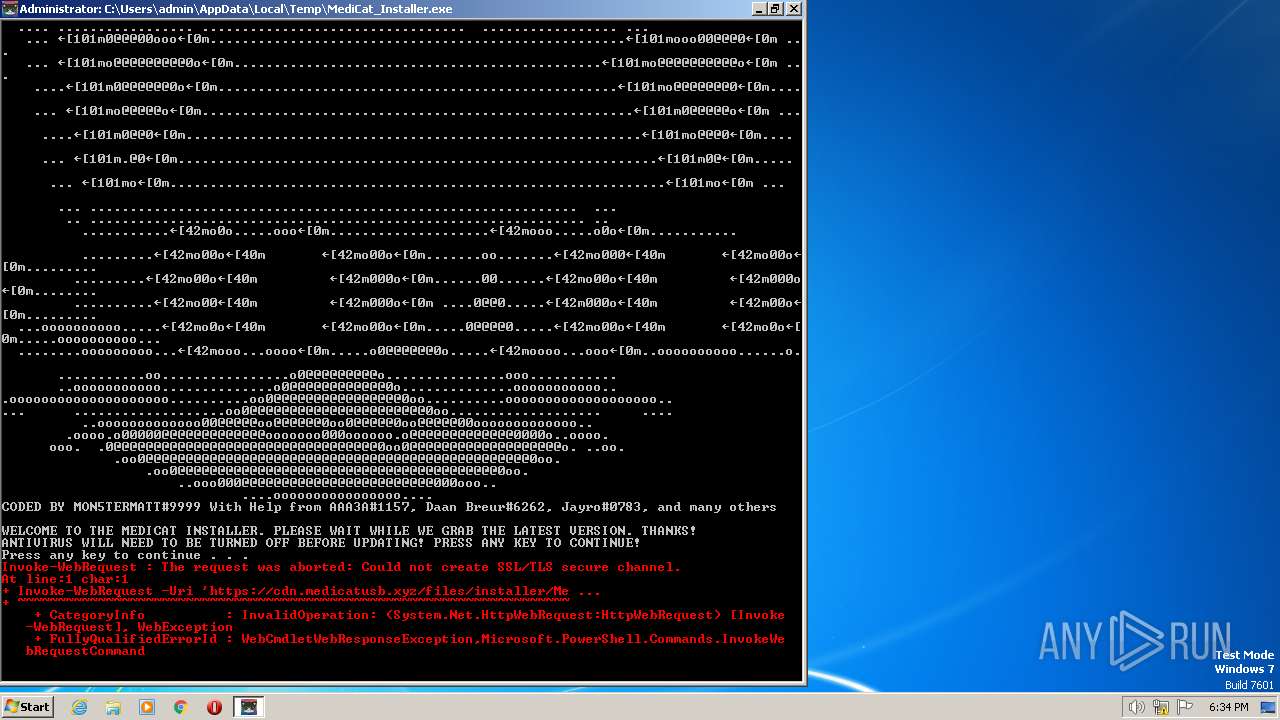
Request from PowerShell which ran from CMD.EXE
- powershell.exe (PID: 3232)
SUSPICIOUS
Starts CMD.EXE for commands execution
- MediCat_Installer.exe (PID: 3824)
- cmd.exe (PID: 888)
The Powershell connects to the Internet
- powershell.exe (PID: 3748)
- powershell.exe (PID: 3232)
Unusual connection from system programs
- powershell.exe (PID: 3748)
- powershell.exe (PID: 3232)
Application launched itself
- cmd.exe (PID: 888)
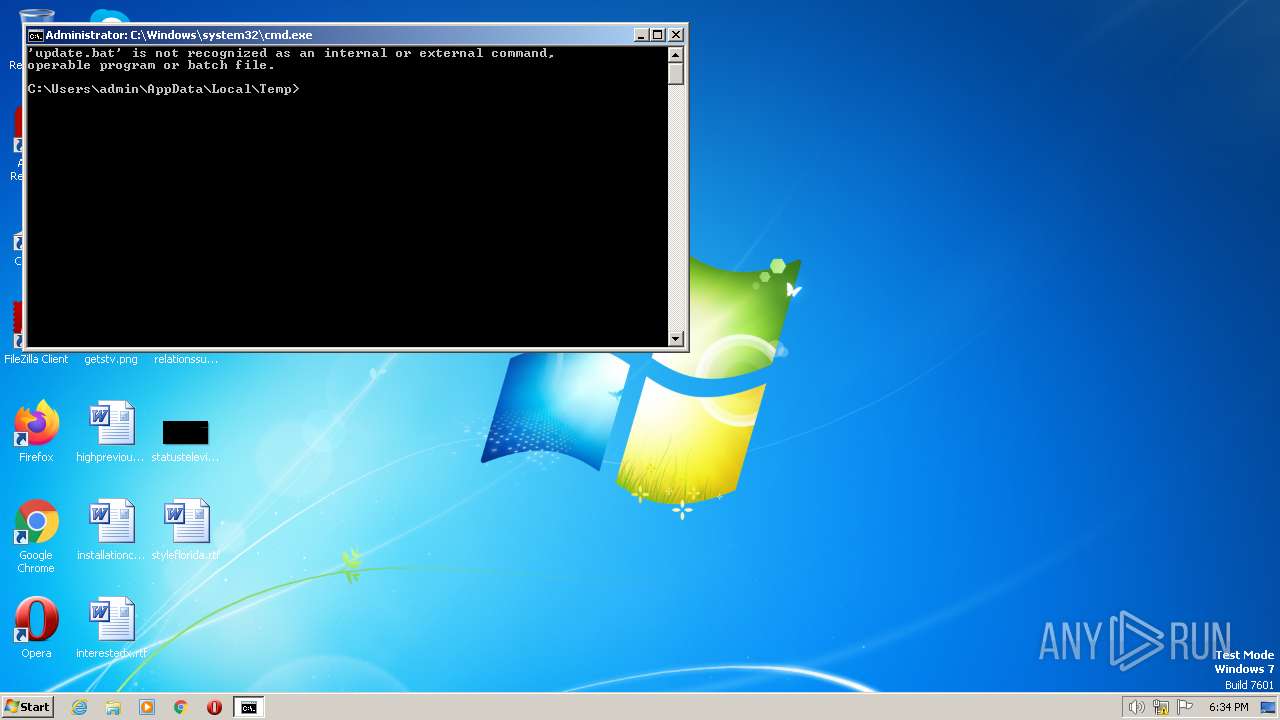
Executing commands from a ".bat" file
- cmd.exe (PID: 888)
- MediCat_Installer.exe (PID: 3824)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 1648)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 888)
Request a resource from the Internet using PowerShell's cmdlet
- cmd.exe (PID: 888)
Process requests binary or script from the Internet
- powershell.exe (PID: 3232)
Reads the Internet Settings
- powershell.exe (PID: 3748)
- powershell.exe (PID: 3232)
INFO
Checks supported languages
- MediCat_Installer.exe (PID: 3824)
- mode.com (PID: 2728)
Create files in a temporary directory
- MediCat_Installer.exe (PID: 3824)
- powershell.exe (PID: 3232)
- powershell.exe (PID: 3748)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| ProductName: | MEDICAT DOWNLOADER |
|---|---|
| LegalCopyright: | HTTPS://MON5TERMATT.CLUB |
| CompanyName: | HTTPS://MEDICATUSB.XYZ |
| FileDescription: | DOWNLOADS FULL INSTALLER FROM SITE |
| ProductVersion: | 1.0.0.1 |
| FileVersion: | 1.0.0.1 |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Dynamic link library |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.1 |
| FileVersionNumber: | 1.0.0.1 |
| Subsystem: | Windows command line |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x6444 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 192512 |
| CodeSize: | 49152 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| TimeStamp: | 2014:08:02 22:19:45+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 02-Aug-2014 22:19:45 |
| Detected languages: |
|
| FileVersion: | 1.0.0.1 |
| ProductVersion: | 1.0.0.1 |
| FileDescription: | DOWNLOADS FULL INSTALLER FROM SITE |
| CompanyName: | HTTPS://MEDICATUSB.XYZ |
| LegalCopyright: | HTTPS://MON5TERMATT.CLUB |
| ProductName: | MEDICAT DOWNLOADER |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 02-Aug-2014 22:19:45 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000BFF6 | 0x0000C000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.54069 |
.rdata | 0x0000D000 | 0x00000B60 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.29476 |
.data | 0x0000E000 | 0x00B00E98 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.71109 |
.rsrc | 0x00B0F000 | 0x0002BE48 | 0x0002C000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.88422 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.99409 | 786 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.58954 | 67624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 5.74632 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 5.78978 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 5.82226 | 6760 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 5.87514 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 5.94478 | 2440 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 5.94097 | 1720 | Latin 1 / Western European | UNKNOWN | RT_ICON |
9 | 5.87559 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
Imports
KERNEL32.dll |
WINMM.dll |
Total processes
54
Monitored processes
15
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 888 | C:\Windows\system32\cmd.exe /c C:\Users\admin\AppData\Local\Temp\ytmp\tmp255.bat "C:\Users\admin\AppData\Local\Temp\MediCat_Installer.exe" | C:\Windows\System32\cmd.exe | — | MediCat_Installer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1464 | C:\Windows\system32\cmd.exe /c if exist "C:\Users\admin\AppData\Local\Temp\ytmp\tmp5757.exe" del "C:\Users\admin\AppData\Local\Temp\ytmp\tmp5757.exe" | C:\Windows\System32\cmd.exe | — | MediCat_Installer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1648 | C:\Windows\system32\cmd.exe /c attrib +h C:\Users\admin\AppData\Local\Temp\ytmp | C:\Windows\System32\cmd.exe | — | MediCat_Installer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1756 | attrib +h C:\Users\admin\AppData\Local\Temp\ytmp | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1964 | C:\Windows\system32\cmd.exe /c if exist "C:\Users\admin\AppData\Local\Temp\ytmp\tmp255.bat" del "C:\Users\admin\AppData\Local\Temp\ytmp\tmp255.bat" | C:\Windows\System32\cmd.exe | — | MediCat_Installer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2228 | cmd /k update.bat | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2336 | C:\Windows\system32\cmd.exe /c if not exist "C:\Users\admin\AppData\Local\Temp\afolder" mkdir "C:\Users\admin\AppData\Local\Temp\afolder" | C:\Windows\System32\cmd.exe | — | MediCat_Installer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2400 | C:\Windows\system32\cmd.exe /c if exist "C:\Users\admin\AppData\Local\Temp\ytmp\tmp255.bat" del "C:\Users\admin\AppData\Local\Temp\ytmp\tmp255.bat" | C:\Windows\System32\cmd.exe | — | MediCat_Installer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2592 | C:\Windows\system32\cmd.exe /c if not exist "C:\Users\admin\AppData\Local\Temp\ytmp" mkdir "C:\Users\admin\AppData\Local\Temp\ytmp" | C:\Windows\System32\cmd.exe | — | MediCat_Installer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2636 | C:\Windows\system32\cmd.exe /c if exist "C:\Users\admin\AppData\Local\Temp\ytmp\tmp5757.exe" del "C:\Users\admin\AppData\Local\Temp\ytmp\tmp5757.exe" | C:\Windows\System32\cmd.exe | — | MediCat_Installer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 815
Read events
1 815
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
5
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3824 | MediCat_Installer.exe | C:\Users\admin\AppData\Local\Temp\ytmp\tmp255.bat | text | |
MD5:2712DC7C4D1C14CDD50ED74F95F51F9E | SHA256:795D6C8EF4FE02D56348BB2C7AF3776450EE6C418C5699E0176EC3181312DE88 | |||
| 3748 | powershell.exe | C:\Users\admin\AppData\Local\Temp\kvv0243b.uet.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3748 | powershell.exe | C:\Users\admin\AppData\Local\Temp\0speji1m.2vh.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3824 | MediCat_Installer.exe | C:\Users\admin\AppData\Local\Temp\ytmp\tmp5757.exe | text | |
MD5:3C52638971EAD82B5929D605C1314EE0 | SHA256:5614459EC05FDF6110FA8CE54C34E859671EEFFBA2B7BB4B1AD6C2C6706855AB | |||
| 3232 | powershell.exe | C:\Users\admin\AppData\Local\Temp\hr20kvxx.3zi.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3232 | powershell.exe | C:\Users\admin\AppData\Local\Temp\giry3wxp.0hc.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3748 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
9
DNS requests
1
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3232 | powershell.exe | GET | 301 | 108.165.179.30:80 | http://cdn.medicatusb.xyz/files/installer/update.bat | US | html | 166 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3412 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3748 | powershell.exe | 108.165.179.30:443 | cdn.medicatusb.xyz | NEXTARRAY-ASN-01 | US | suspicious |
3232 | powershell.exe | 108.165.179.30:80 | cdn.medicatusb.xyz | NEXTARRAY-ASN-01 | US | suspicious |
3232 | powershell.exe | 108.165.179.30:443 | cdn.medicatusb.xyz | NEXTARRAY-ASN-01 | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn.medicatusb.xyz |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3232 | powershell.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
3232 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
1 ETPRO signatures available at the full report