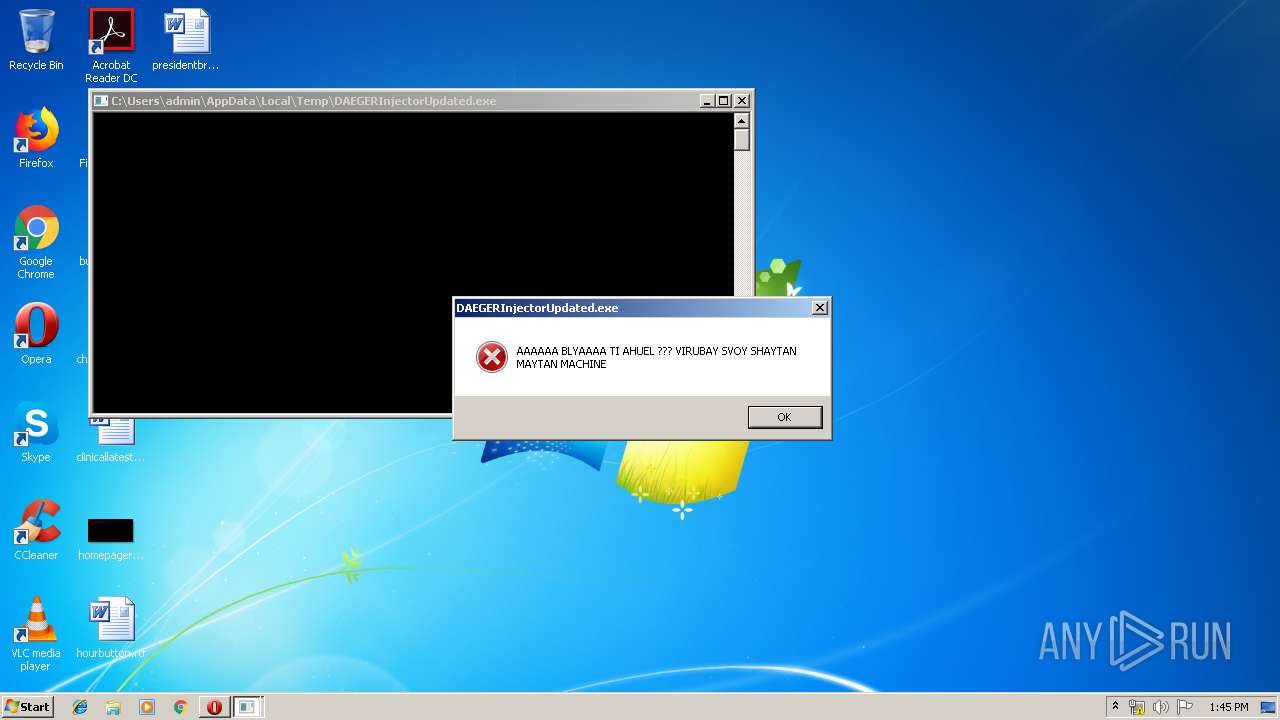
| File name: | DAEGERInjectorUpdated.exe |
| Full analysis: | https://app.any.run/tasks/bb6c5e1e-811a-4c99-92bb-ff0eee1ed582 |
| Verdict: | No threats detected |
| Analysis date: | July 20, 2019, 12:39:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | BF22403742720E04A713B0AD015EBDF7 |
| SHA1: | 9A0933B57E67A374DA59254F535DA21B26DB8148 |
| SHA256: | F959774F022D6DF89448FC562493FBC366158A3F28EEEC8666DC9211003C84AF |
| SSDEEP: | 98304:WZkSPM2uemRg8W4SfYFwLdQj0DneMSv2ZJlKLzh1TYB71rz4MpiLUH7k:WGEJunXSf55O0LeRvq7KB1MB71rdVA |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
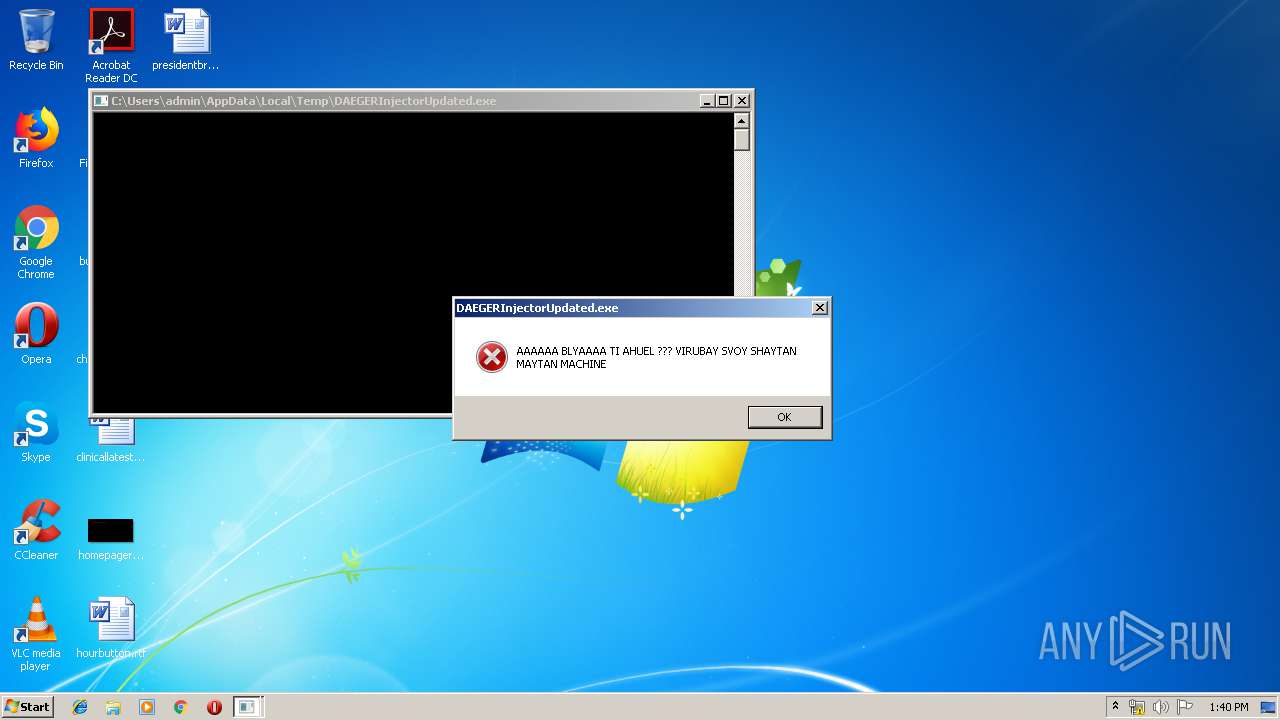
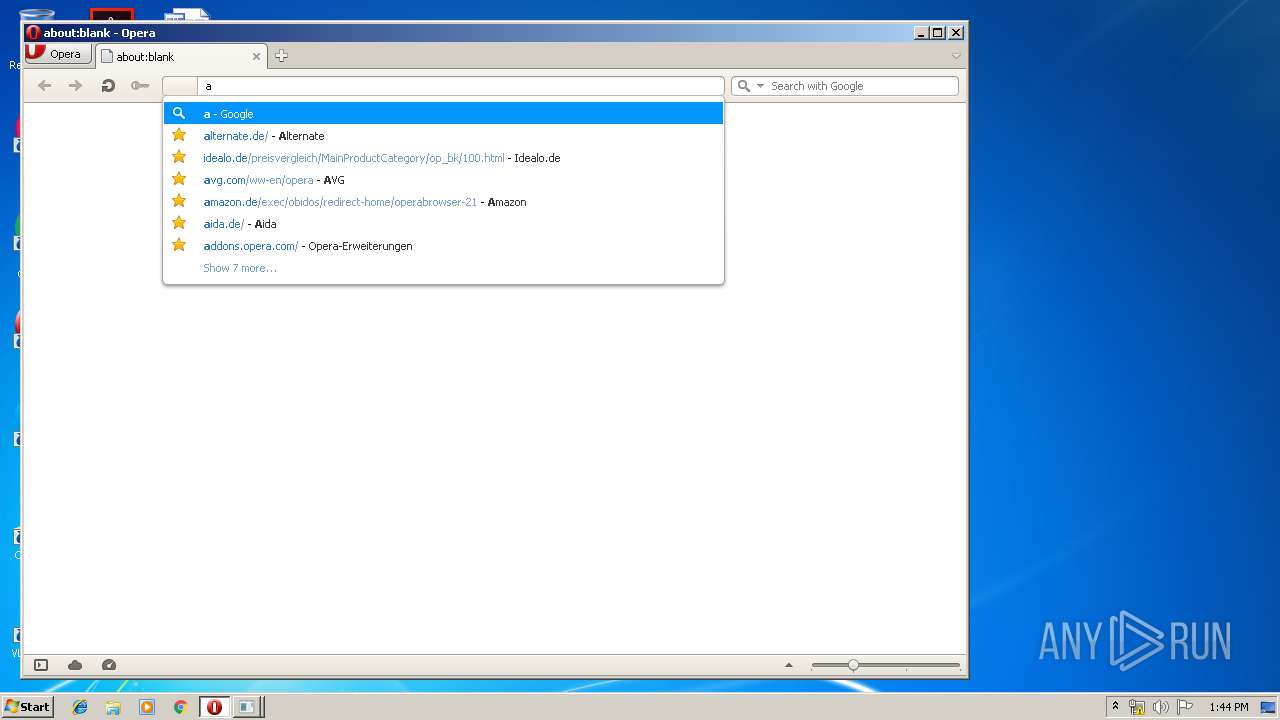
Manual execution by user
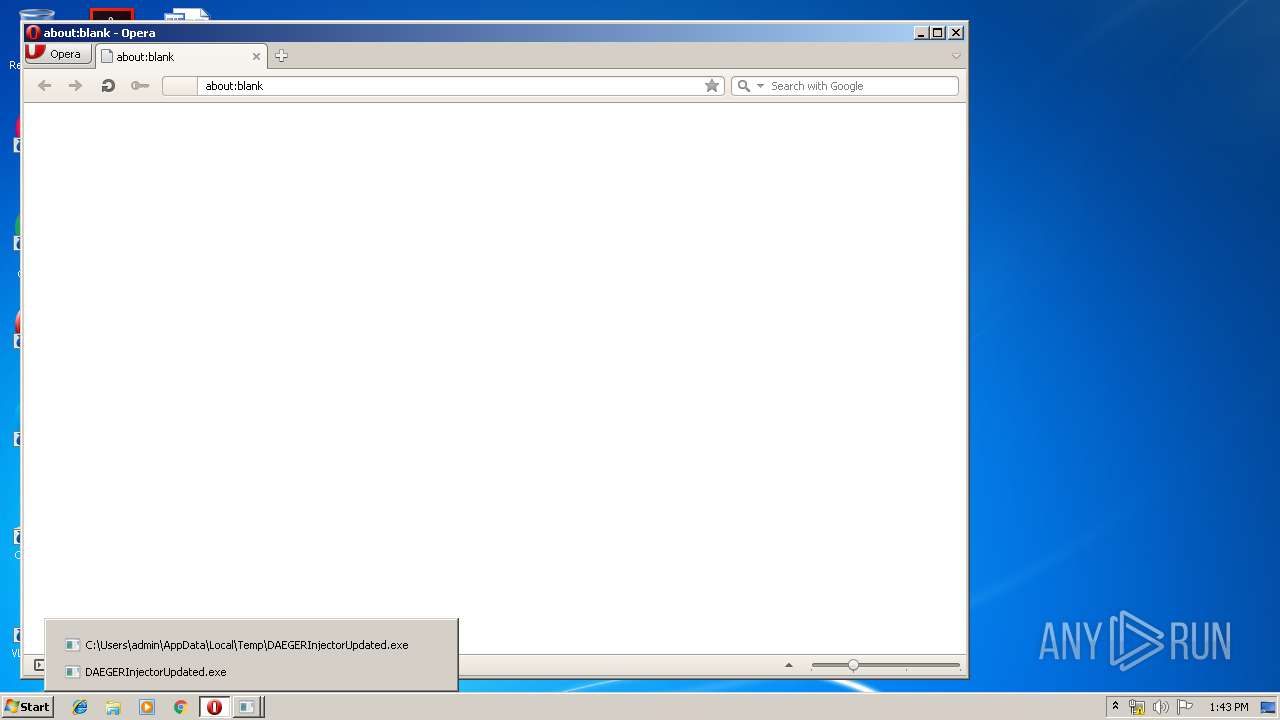
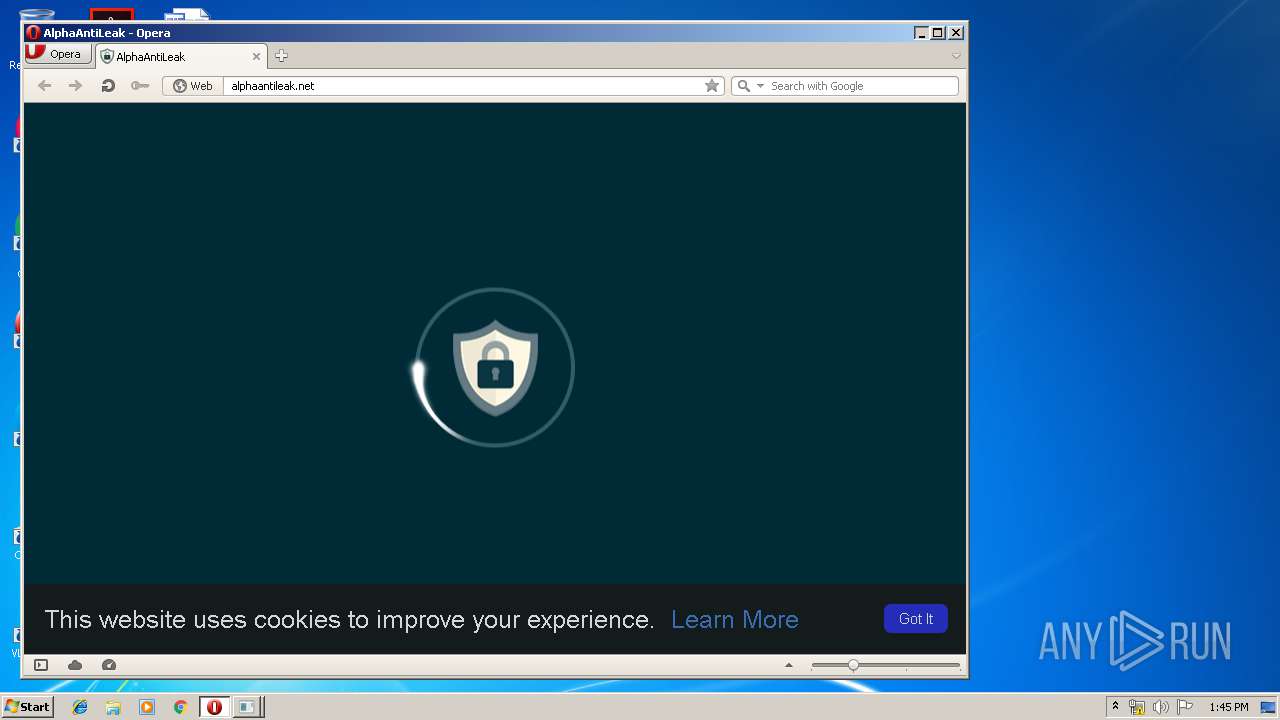
- opera.exe (PID: 2380)
Creates files in the user directory
- opera.exe (PID: 2380)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:06:01 15:27:40+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.2 |
| CodeSize: | 775680 |
| InitializedDataSize: | 170496 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x994750 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 01-Jun-2019 13:27:40 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 01-Jun-2019 13:27:40 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000BD488 | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0 |
.rdata | 0x000BF000 | 0x0001D95F | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0 |
.data | 0x000DD000 | 0x00003FDC | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x000E1000 | 0x00001295 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0 |
.00cfg | 0x000E3000 | 0x00000104 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0 |
.vmp0 | 0x000E4000 | 0x003514EE | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0 |
.vmp1 | 0x00436000 | 0x005B6690 | 0x005B6800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.96073 |
.reloc | 0x009ED000 | 0x0000059C | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.1824 |
.rsrc | 0x009EE000 | 0x000001D5 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.71768 |
Imports
KERNEL32.dll |
SHLWAPI.dll |
USER32.dll |
WTSAPI32.dll |
ntdll.dll |
urlmon.dll |
Total processes
41
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2120 | "C:\Users\admin\AppData\Local\Temp\DAEGERInjectorUpdated.exe" | C:\Users\admin\AppData\Local\Temp\DAEGERInjectorUpdated.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3735929054 Modules
| |||||||||||||||
| 2380 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
Total events
188
Read events
130
Write events
58
Delete events
0
Modification events
| (PID) Process: | (2380) opera.exe | Key: | HKEY_CURRENT_USER\Software\Opera Software |
| Operation: | write | Name: | Last CommandLine v2 |
Value: C:\Program Files\Opera\opera.exe | |||
| (PID) Process: | (2380) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
20
Text files
18
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2380 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr8C2F.tmp | — | |
MD5:— | SHA256:— | |||
| 2380 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr8C7E.tmp | — | |
MD5:— | SHA256:— | |||
| 2380 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00001.tmp | — | |
MD5:— | SHA256:— | |||
| 2380 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\EYRANMWCK83POHON176X.temp | — | |
MD5:— | SHA256:— | |||
| 2380 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\opr3D8F.tmp | — | |
MD5:— | SHA256:— | |||
| 2380 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\opr4967.tmp | — | |
MD5:— | SHA256:— | |||
| 2380 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\operaprefs.ini | text | |
MD5:— | SHA256:— | |||
| 2380 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\g_0000\opr00002.tmp | compressed | |
MD5:— | SHA256:— | |||
| 2380 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\16ec093b8f51508f.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
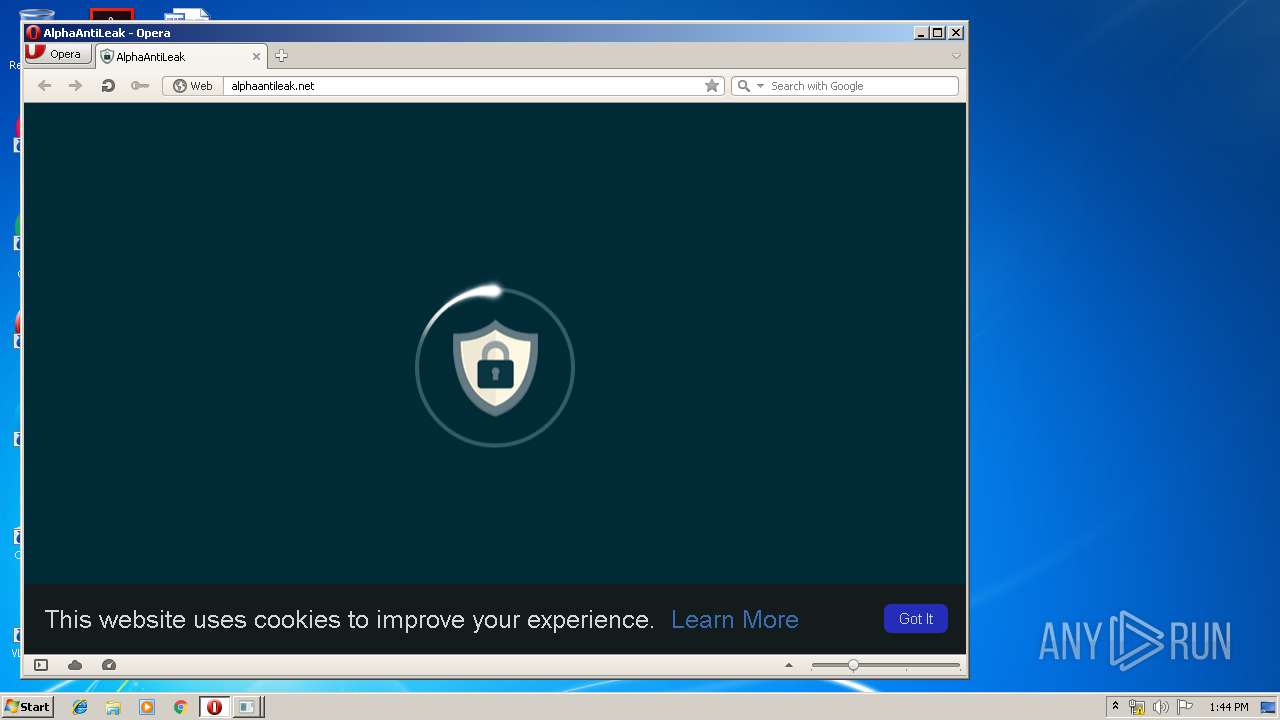
| 2380 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\icons\http%3A%2F%2Falphaantileak.net%2Fassets%2Fimg%2Flogo.png | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
15
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2380 | opera.exe | GET | — | 104.26.13.161:80 | http://alphaantileak.net/assets/js/include.js | US | — | — | shared |
2380 | opera.exe | GET | — | 104.26.13.161:80 | http://alphaantileak.net/assets/js/plotly-latest.min.js | US | — | — | shared |
2380 | opera.exe | GET | — | 104.26.13.161:80 | http://alphaantileak.net/assets/js/aalapi.js | US | — | — | shared |
2380 | opera.exe | GET | — | 104.26.13.161:80 | http://alphaantileak.net/cdn-cgi/apps/head/ZXBboRnjnPodRchOugN2oOVk1Ho.js | US | — | — | shared |
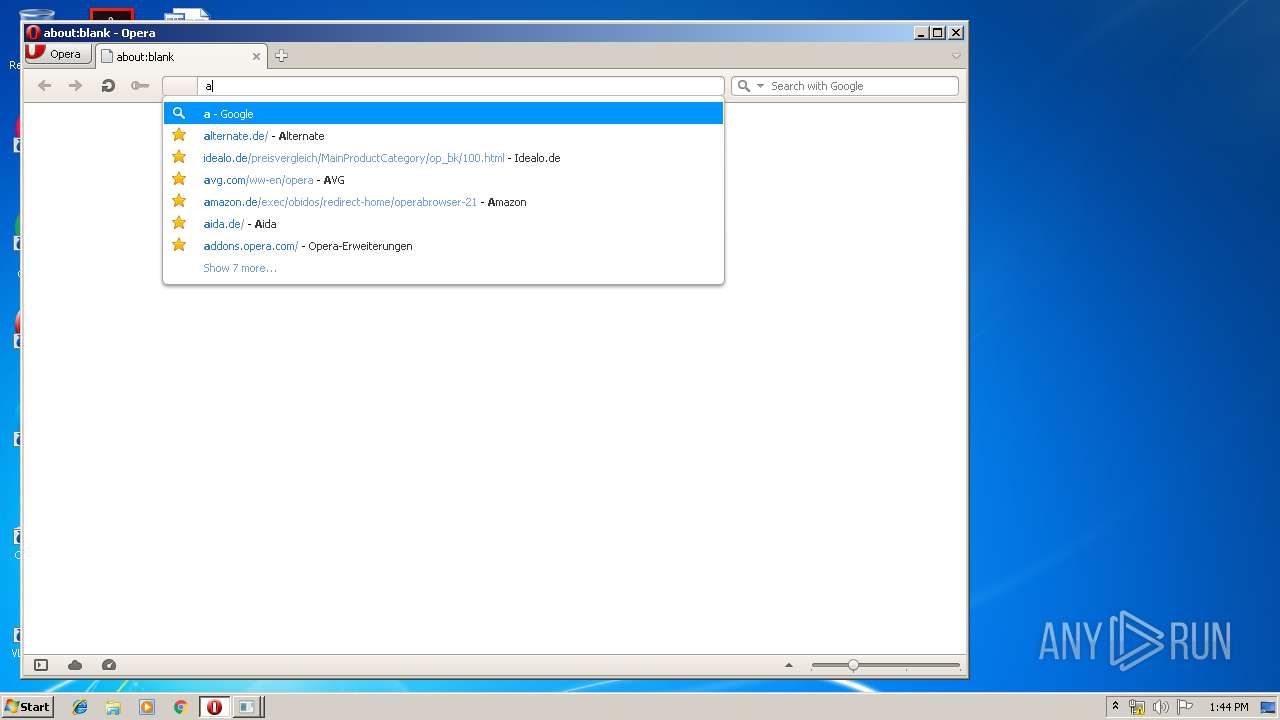
2380 | opera.exe | GET | 200 | 172.217.22.46:80 | http://clients1.google.com/complete/search?q=a%3B[&client=opera-suggest-omnibox&hl=de | US | text | 135 b | whitelisted |
2380 | opera.exe | GET | — | 104.26.13.161:80 | http://alphaantileak.net/assets/css/main.css | US | — | — | shared |
2380 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 528 b | whitelisted |
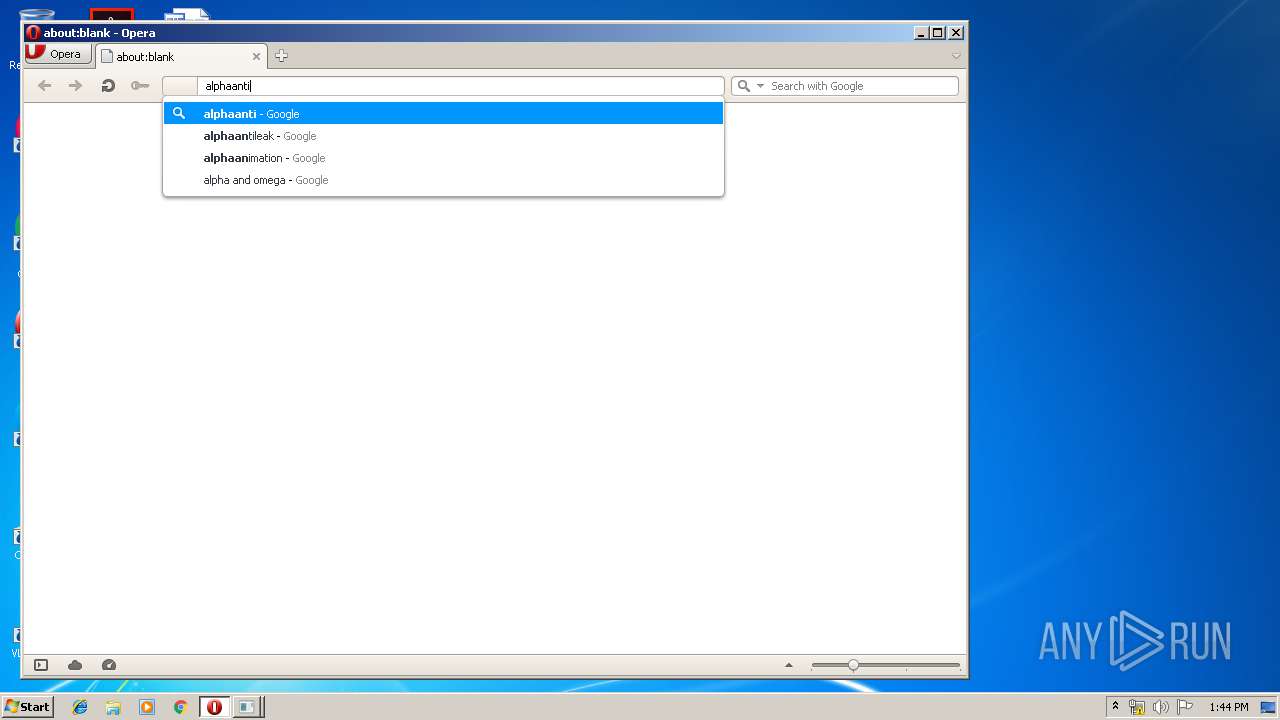
2380 | opera.exe | GET | 200 | 172.217.22.46:80 | http://clients1.google.com/complete/search?q=alpha&client=opera-suggest-omnibox&hl=de | US | text | 107 b | whitelisted |
2380 | opera.exe | GET | 200 | 172.217.22.46:80 | http://clients1.google.com/complete/search?q=alpj&client=opera-suggest-omnibox&hl=de | US | text | 111 b | whitelisted |
2380 | opera.exe | GET | 200 | 172.217.22.46:80 | http://clients1.google.com/complete/search?q=alpj&client=opera-suggest-omnibox&hl=de | US | text | 111 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2380 | opera.exe | 185.26.182.94:443 | certs.opera.com | Opera Software AS | — | whitelisted |
2380 | opera.exe | 93.184.220.29:80 | crl4.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2380 | opera.exe | 172.217.22.68:443 | www.google.com | Google Inc. | US | whitelisted |
2380 | opera.exe | 172.217.22.46:80 | clients1.google.com | Google Inc. | US | whitelisted |
2380 | opera.exe | 172.217.22.35:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2380 | opera.exe | 172.217.22.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2380 | opera.exe | 104.26.13.161:80 | alphaantileak.net | Cloudflare Inc | US | shared |
2380 | opera.exe | 185.26.182.111:80 | sitecheck2.opera.com | Opera Software AS | — | whitelisted |
2380 | opera.exe | 216.58.206.3:80 | crl.pki.goog | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
certs.opera.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
clients1.google.com |
| whitelisted |
alphaantileak.net |
| unknown |
sitecheck2.opera.com |
| whitelisted |
www.google.com |
| malicious |
crl.pki.goog |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.gstatic.com |
| whitelisted |