| File name: | Premium_Sp00fer.vmp.exe |
| Full analysis: | https://app.any.run/tasks/fcc3693d-04b2-4745-b1b3-6ac08d6963c6 |
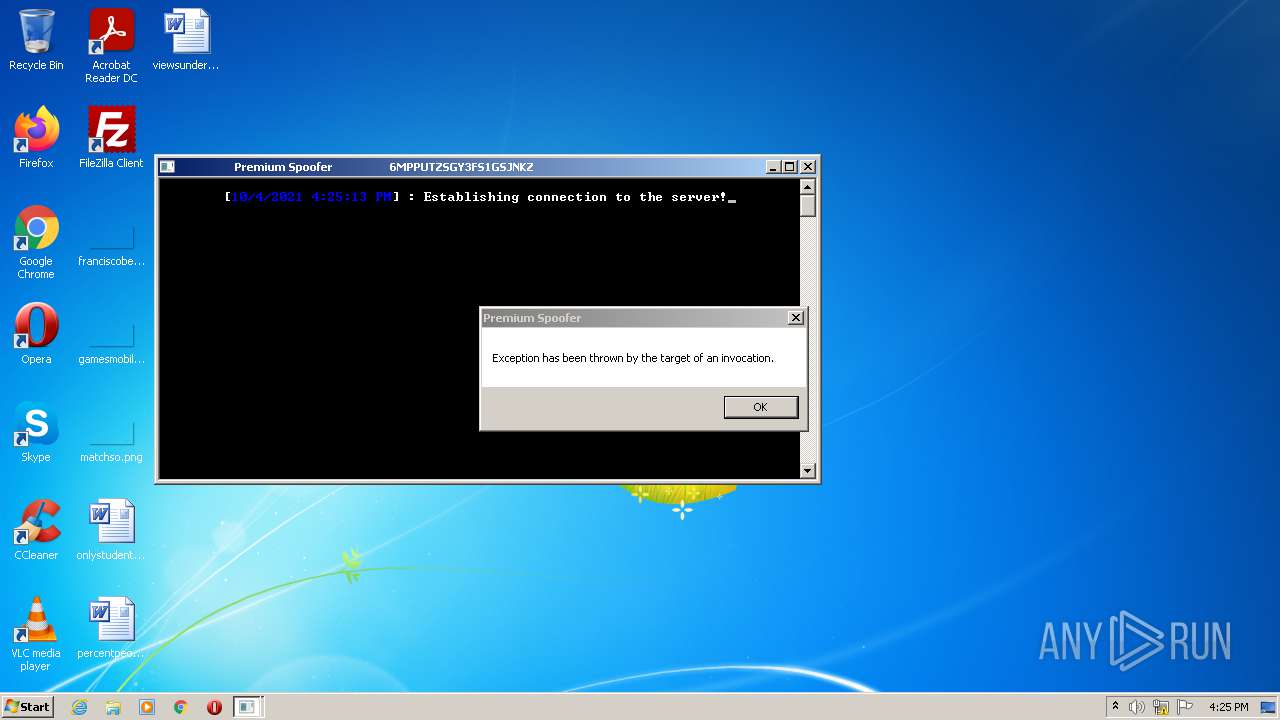
| Verdict: | Malicious activity |
| Analysis date: | October 04, 2021, 15:24:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 750487F309C55B1C13C51DDBA50598F6 |
| SHA1: | D884E6B4F17910FD567733D81258E1D5743DA040 |
| SHA256: | F9534A8E4CE6F01F70162B9A0E18D33D76AD73C658DD3E3AC4B4B4545477B677 |
| SSDEEP: | 6144:bPEkNfwAaIO2WQLk5AyrUKkmhnrWxuj+KpuQAx2Kb6TUfz9K/G142GY/2f:3qZ5rrUKknxuDuQ42yj142jW |
MALICIOUS
Runs app for hidden code execution
- Premium_Sp00fer.vmp.exe (PID: 3984)
SUSPICIOUS
Checks supported languages
- Premium_Sp00fer.vmp.exe (PID: 3984)
- cmd.exe (PID: 1608)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 1608)
Reads Environment values
- Premium_Sp00fer.vmp.exe (PID: 3984)
Reads the computer name
- Premium_Sp00fer.vmp.exe (PID: 3984)
Starts CMD.EXE for commands execution
- Premium_Sp00fer.vmp.exe (PID: 3984)
INFO
Reads the computer name
- taskkill.exe (PID: 3024)
- taskkill.exe (PID: 572)
- taskkill.exe (PID: 2492)
- taskkill.exe (PID: 1624)
- taskkill.exe (PID: 4076)
- taskkill.exe (PID: 2696)
- taskkill.exe (PID: 2584)
- taskkill.exe (PID: 2452)
- taskkill.exe (PID: 2180)
- taskkill.exe (PID: 3792)
- arp.exe (PID: 1532)
- arp.exe (PID: 1796)
- arp.exe (PID: 1372)
- arp.exe (PID: 2844)
- arp.exe (PID: 4084)
- arp.exe (PID: 2880)
- arp.exe (PID: 2816)
- arp.exe (PID: 3988)
- arp.exe (PID: 3380)
- arp.exe (PID: 2844)
- arp.exe (PID: 3744)
- taskkill.exe (PID: 2480)
- arp.exe (PID: 3116)
- arp.exe (PID: 2260)
Checks supported languages
- taskkill.exe (PID: 1624)
- taskkill.exe (PID: 2696)
- taskkill.exe (PID: 2180)
- taskkill.exe (PID: 2452)
- taskkill.exe (PID: 4076)
- taskkill.exe (PID: 3792)
- taskkill.exe (PID: 2584)
- taskkill.exe (PID: 572)
- arp.exe (PID: 2844)
- arp.exe (PID: 1796)
- arp.exe (PID: 1532)
- arp.exe (PID: 1372)
- arp.exe (PID: 2880)
- arp.exe (PID: 3380)
- arp.exe (PID: 2260)
- taskkill.exe (PID: 2492)
- taskkill.exe (PID: 2480)
- taskkill.exe (PID: 3024)
- arp.exe (PID: 4084)
- arp.exe (PID: 3988)
- arp.exe (PID: 2844)
- arp.exe (PID: 3116)
- arp.exe (PID: 2816)
- arp.exe (PID: 3744)
Reads settings of System Certificates
- Premium_Sp00fer.vmp.exe (PID: 3984)
Reads the hosts file
- Premium_Sp00fer.vmp.exe (PID: 3984)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (64.5) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (13.6) |
| .exe | | | Win32 Executable (generic) (9.3) |
| .exe | | | Win16/32 Executable Delphi generic (4.2) |
| .exe | | | Generic Win/DOS Executable (4.1) |
EXIF
EXE
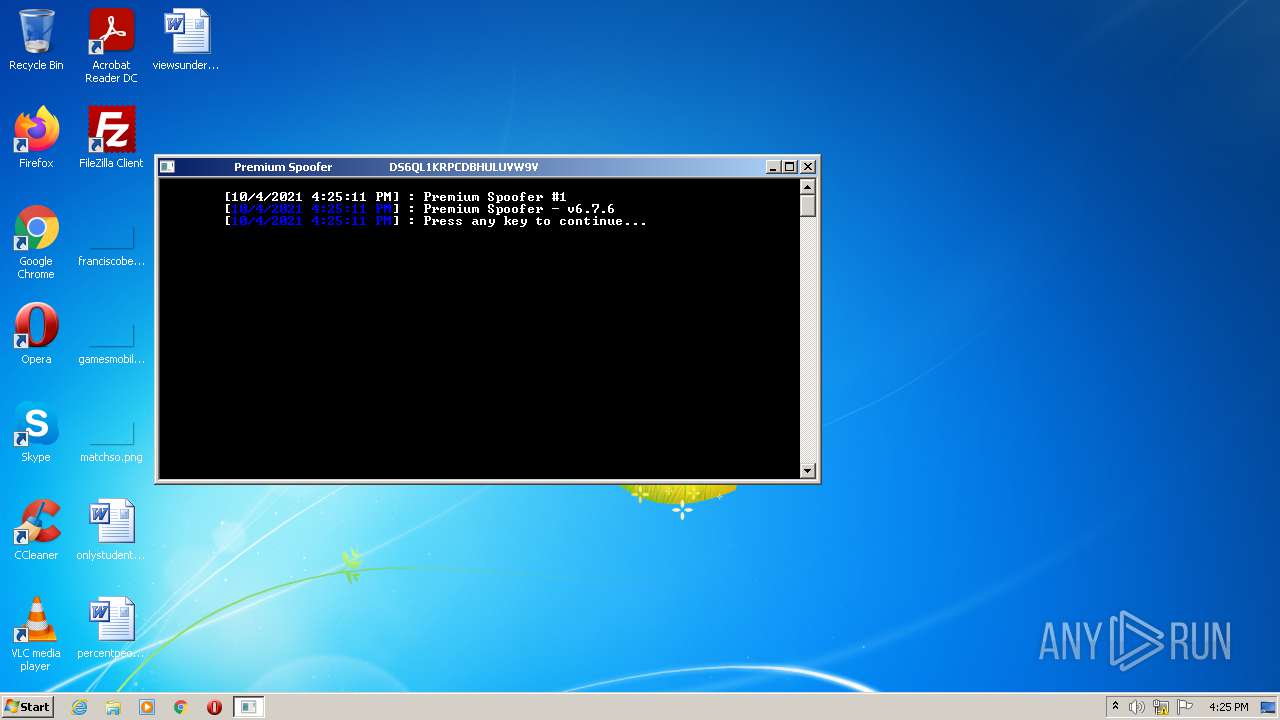
| AssemblyVersion: | 1.0.0.0 |
|---|---|
| ProductVersion: | 1.0.0.0 |
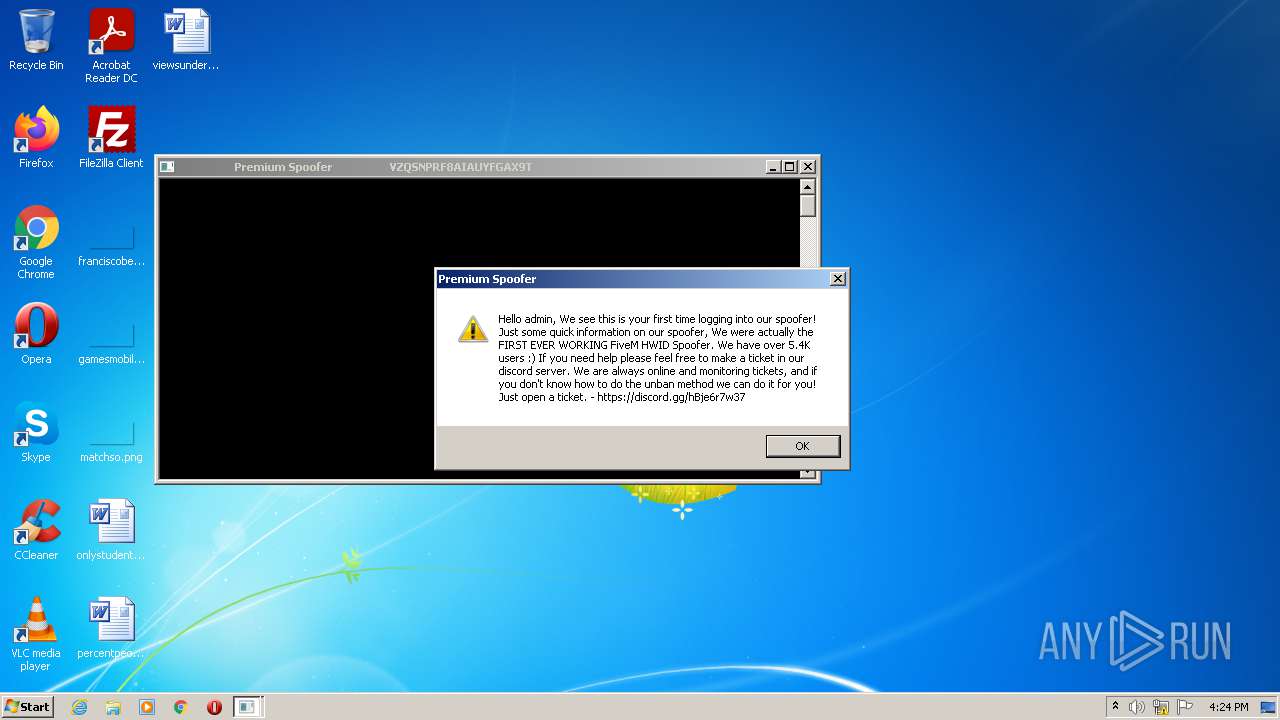
| ProductName: | HWID Spoofer by Vanity Premium |
| OriginalFileName: | Premium Sp00fer.exe |
| LegalTrademarks: | - |
| LegalCopyright: | Copyright © Vanity Premium 2020-2021 |
| InternalName: | Premium Sp00fer.exe |
| FileVersion: | 1.0.0.0 |
| FileDescription: | Premium Spooferino |
| CompanyName: | Vanity Premium |
| Comments: | A multi-game hardware ID spoofer. |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows command line |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x48001 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 185344 |
| CodeSize: | 180736 |
| LinkerVersion: | 48 |
| PEType: | PE32 |
| TimeStamp: | 2022:01:09 23:25:40+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 09-Jan-2022 22:25:40 |
| Comments: | A multi-game hardware ID spoofer. |
| CompanyName: | Vanity Premium |
| FileDescription: | Premium Spooferino |
| FileVersion: | 1.0.0.0 |
| InternalName: | Premium Sp00fer.exe |
| LegalCopyright: | Copyright © Vanity Premium 2020-2021 |
| LegalTrademarks: | - |
| OriginalFilename: | Premium Sp00fer.exe |
| ProductName: | HWID Spoofer by Vanity Premium |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 09-Jan-2022 22:25:40 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0002C140 | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0 |
.VanityPQ/\x01 | 0x00030000 | 0x00012F51 | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0 |
.VanityP\xec\xcc\x04 | 0x00044000 | 0x0004CCEC | 0x0004CE00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.24837 |
.rsrc | 0x00092000 | 0x000011E8 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.0158 |
.reloc | 0x00094000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.02015 | 3407 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
Total processes
65
Monitored processes
27
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 572 | taskkill /f /im BEServices.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1372 | "C:\Windows\System32\arp.exe" -a | C:\Windows\System32\arp.exe | — | Premium_Sp00fer.vmp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Arp Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1532 | "C:\Windows\System32\arp.exe" -a | C:\Windows\System32\arp.exe | — | Premium_Sp00fer.vmp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Arp Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1608 | "cmd.exe" | C:\Windows\system32\cmd.exe | — | Premium_Sp00fer.vmp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1624 | taskkill /f /im BattleEye.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1796 | "C:\Windows\System32\arp.exe" -a | C:\Windows\System32\arp.exe | — | Premium_Sp00fer.vmp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Arp Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2180 | taskkill /f /im FortniteClient-Win64-Shipping_EAC.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2260 | "C:\Windows\System32\arp.exe" -a | C:\Windows\System32\arp.exe | — | Premium_Sp00fer.vmp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Arp Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2452 | taskkill /f /im FortniteClient-Win64-Shipping.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2480 | taskkill /f /im UnrealCEFSubProcess.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
7 797
Read events
7 760
Write events
37
Delete events
0
Modification events
| (PID) Process: | (3984) Premium_Sp00fer.vmp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Premium_Sp00fer_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3984) Premium_Sp00fer.vmp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Premium_Sp00fer_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3984) Premium_Sp00fer.vmp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Premium_Sp00fer_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (3984) Premium_Sp00fer.vmp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Premium_Sp00fer_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (3984) Premium_Sp00fer.vmp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Premium_Sp00fer_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3984) Premium_Sp00fer.vmp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Premium_Sp00fer_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3984) Premium_Sp00fer.vmp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Premium_Sp00fer_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3984) Premium_Sp00fer.vmp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Premium_Sp00fer_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3984) Premium_Sp00fer.vmp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Premium_Sp00fer_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (3984) Premium_Sp00fer.vmp.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Premium_Sp00fer_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
2
Threats
2
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
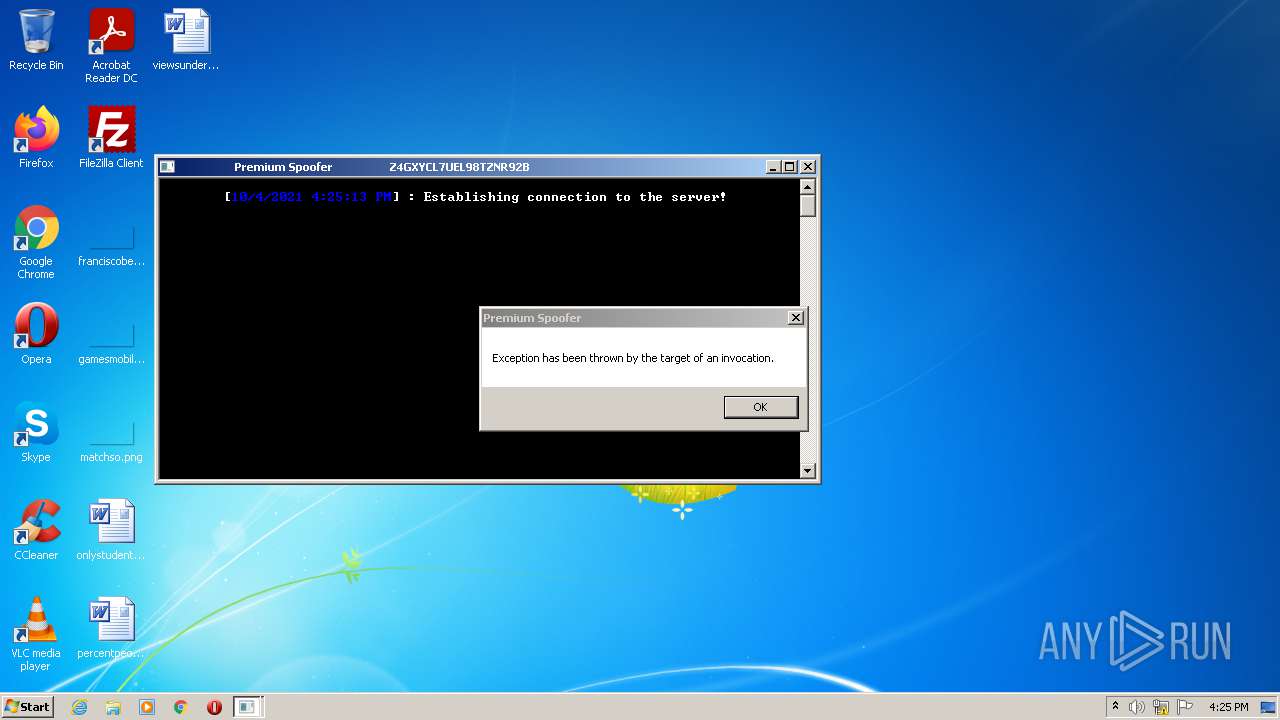
— | — | 172.67.164.78:443 | api.auth.gg | — | US | unknown |
3984 | Premium_Sp00fer.vmp.exe | 145.14.145.210:443 | spooferino.000webhostapp.com | Hostinger International Limited | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
spooferino.000webhostapp.com |
| shared |
api.auth.gg |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Not Suspicious Traffic | ET INFO Observed Free Hosting Domain (*.000webhostapp .com in DNS Lookup) |
3984 | Premium_Sp00fer.vmp.exe | Not Suspicious Traffic | ET INFO Observed SSL Cert for Free Hosting Domain (*.000webhostapp .com) |