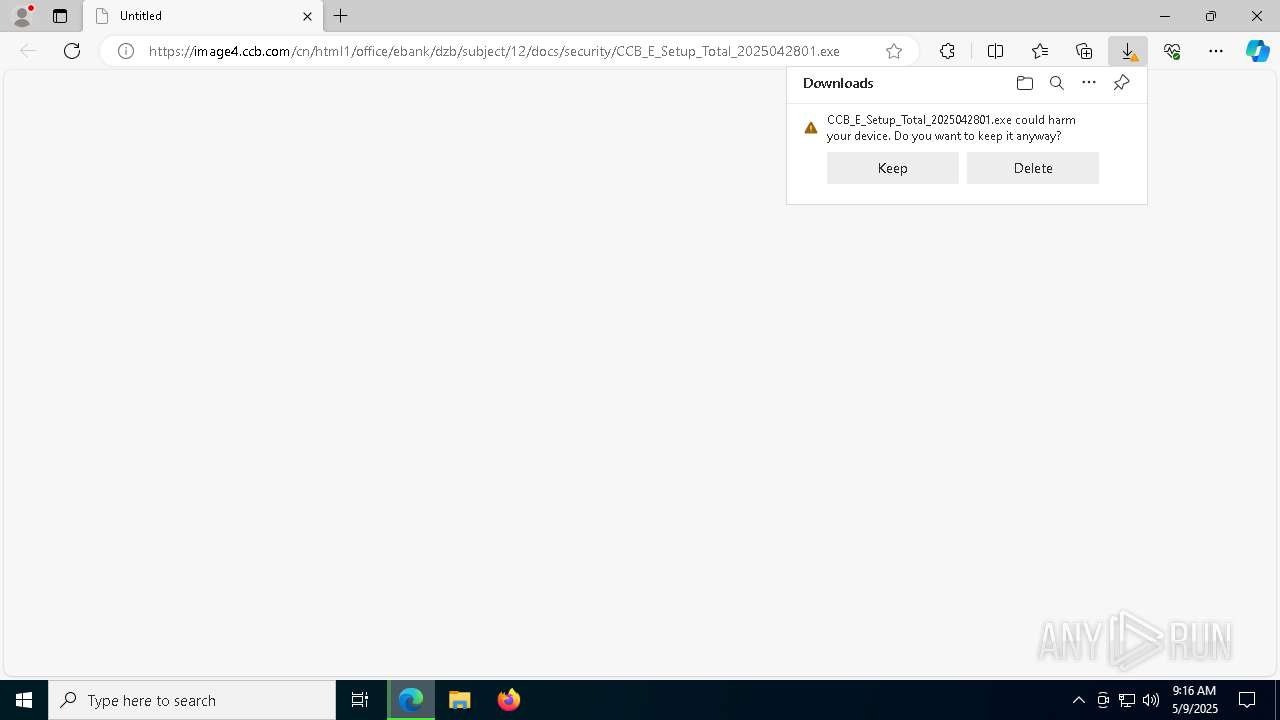
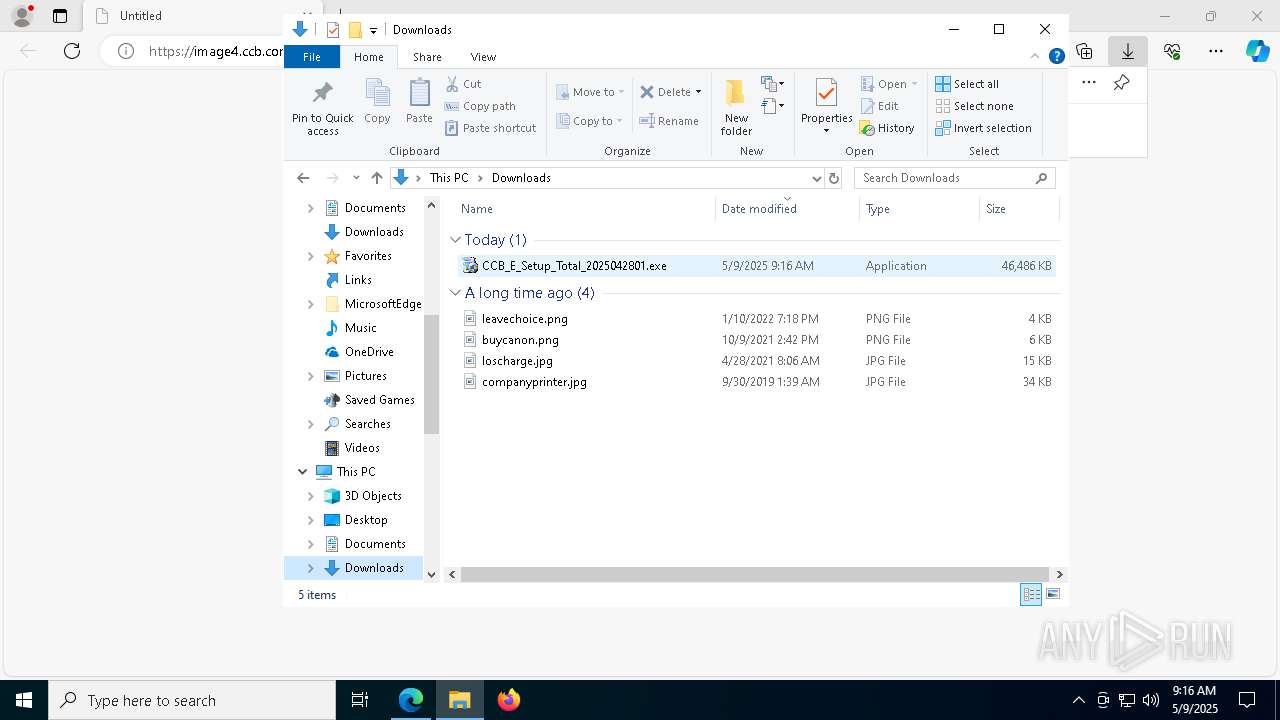
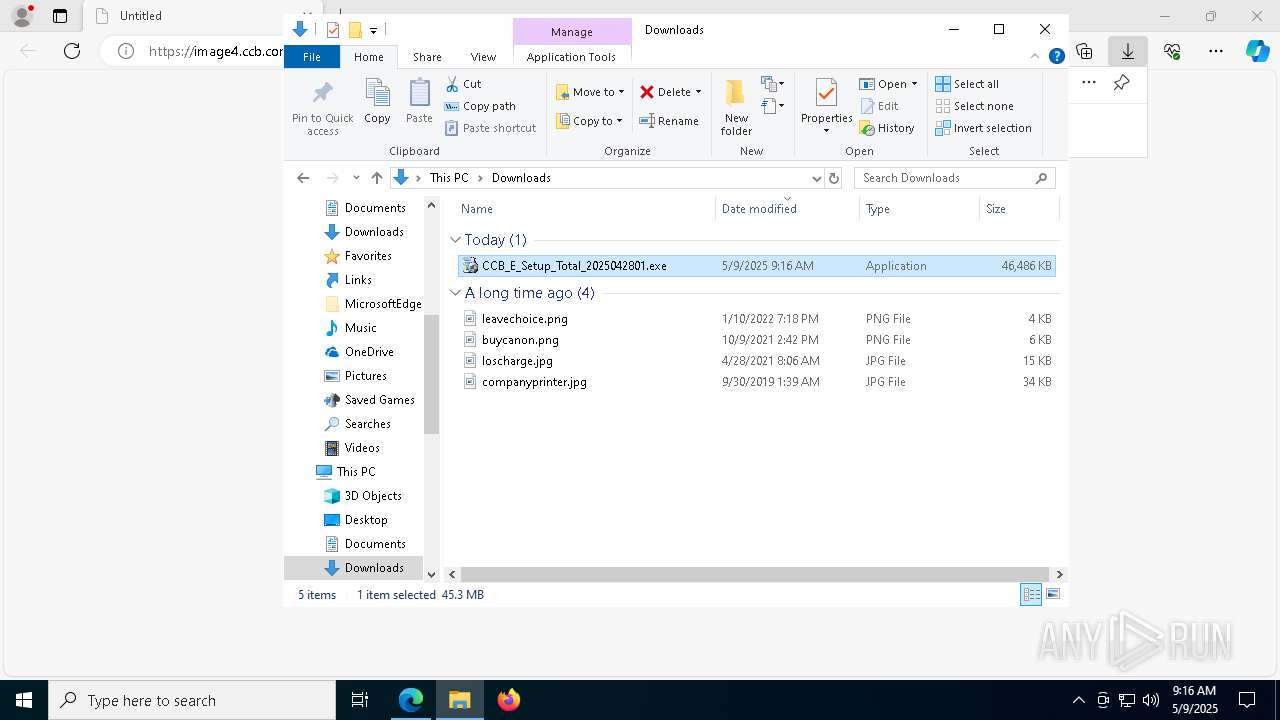
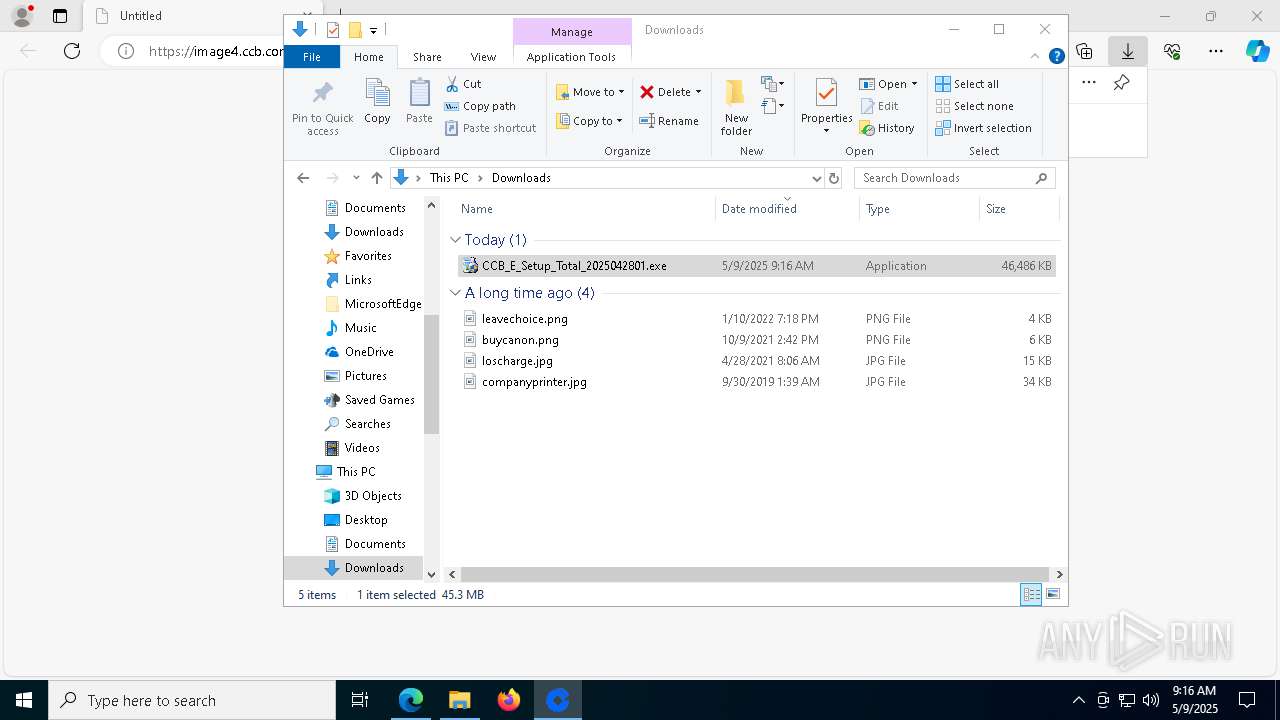
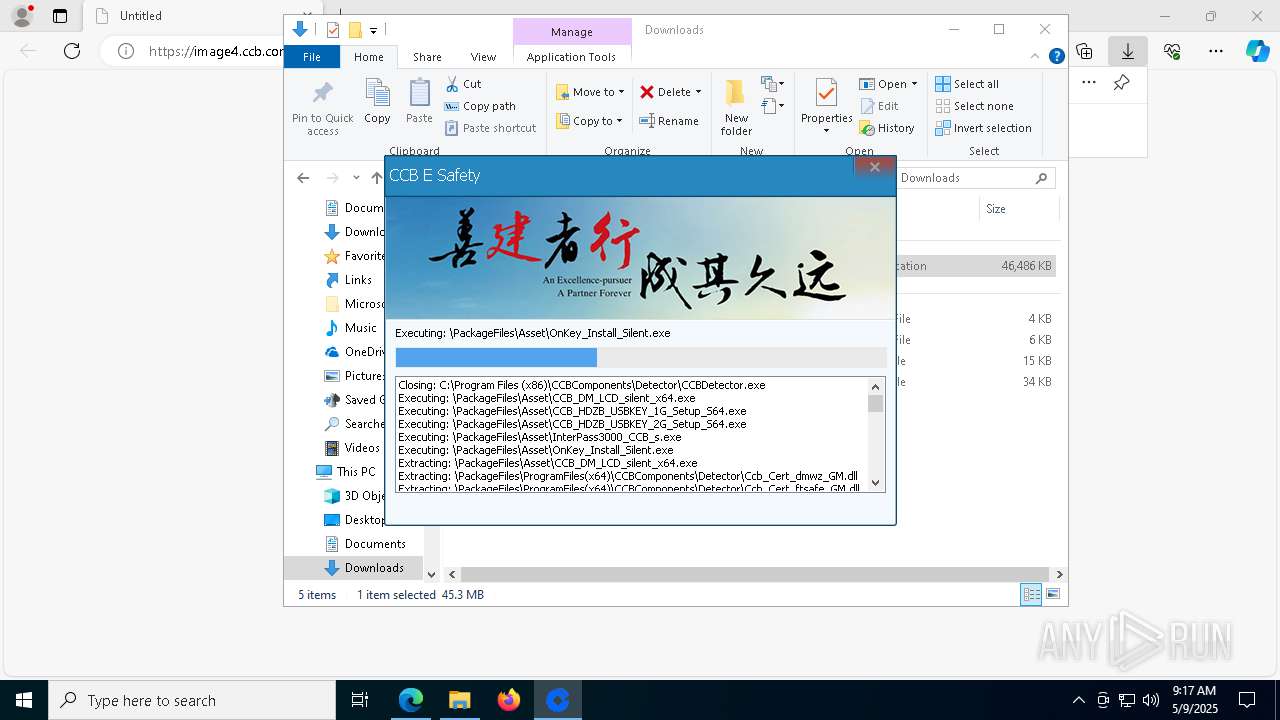
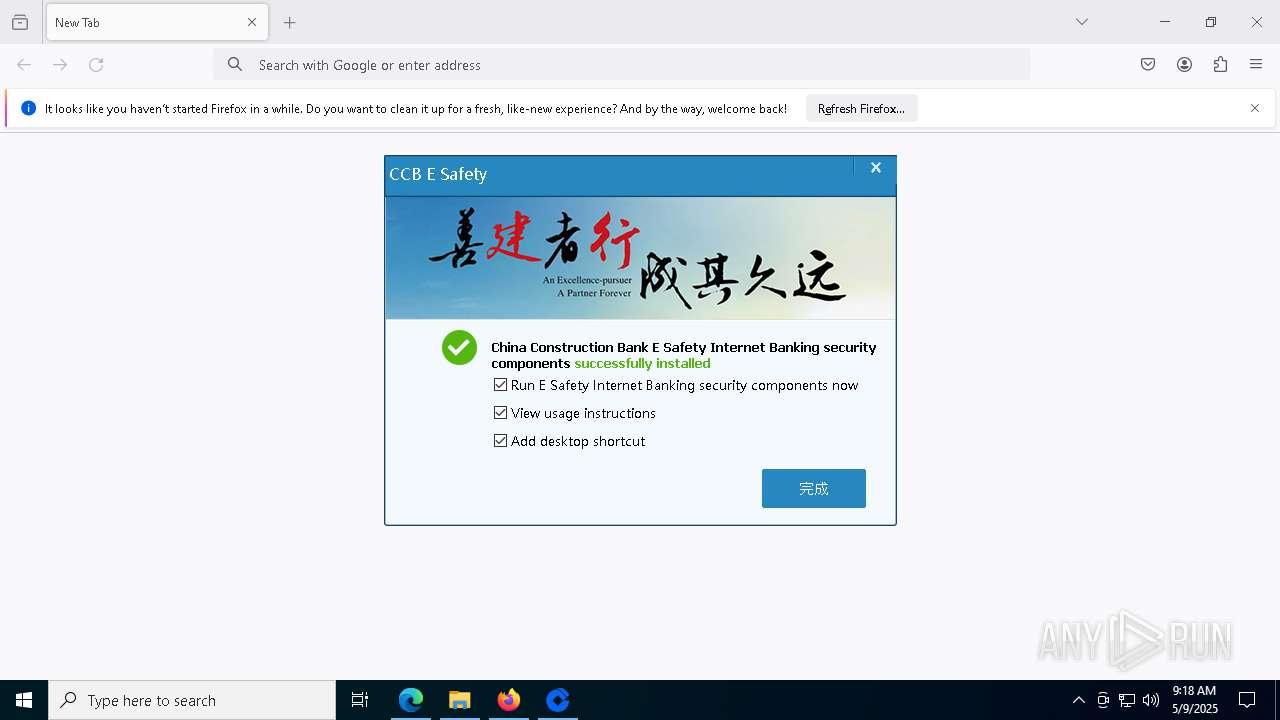
| URL: | https://image4.ccb.com/cn/html1/office/ebank/dzb/subject/12/docs/security/CCB_E_Setup_Total_2025042801.exe |
| Full analysis: | https://app.any.run/tasks/fe35cb90-df76-456c-85a4-e0a6774adf2c |
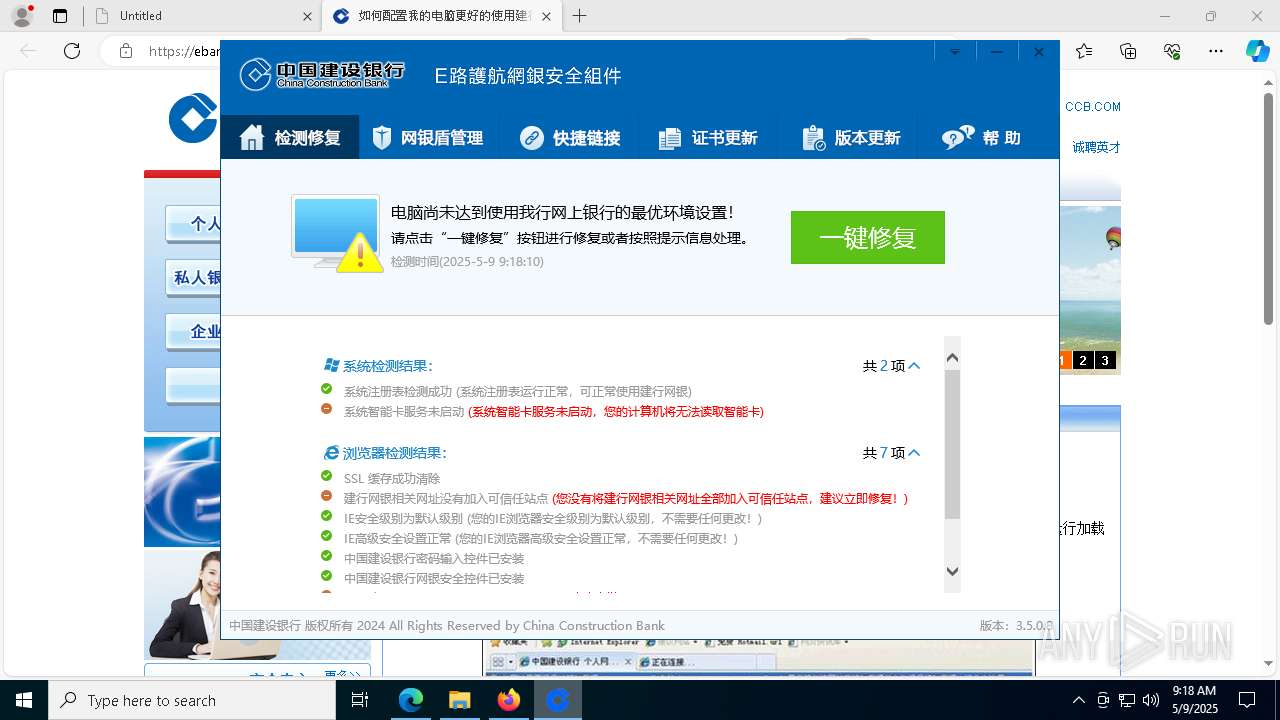
| Verdict: | Malicious activity |
| Analysis date: | May 09, 2025, 09:16:10 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 7E1A216735C96C9A27C3A21D21783B1C |
| SHA1: | A136371837921C783D729FB376FDE439BD7596AF |
| SHA256: | F93C6065FDE8DB47F48978E6CD26EDBAEF822990C325696D7ED5FFDCB861F7E6 |
| SSDEEP: | 3:N8XXK2LKQTDXjibSxKK8Wjp4uNg+QVRXW:2K2LKQTDXjibeBF4uNgvTW |
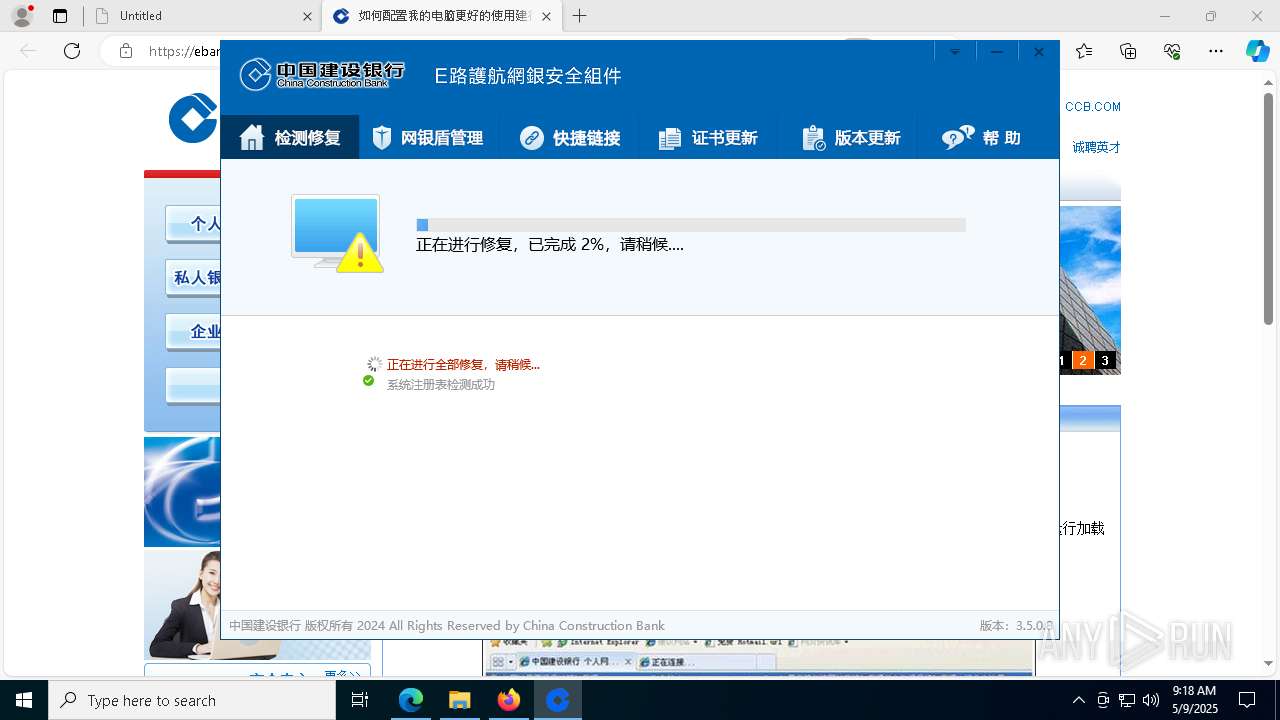
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- CCB_E_Setup_Total_2025042801.exe (PID: 7180)
- CCB_DM_LCD_silent_x64.exe (PID: 8008)
- cmd.exe (PID: 7220)
- cmd.exe (PID: 4180)
- InterPass3000_CCB_s.exe (PID: 6988)
- OnKey_Install_Silent.exe (PID: 7192)
- cmd.exe (PID: 7876)
- registerocx.exe (PID: 4868)
- ESKeySetup_CCB.exe (PID: 7876)
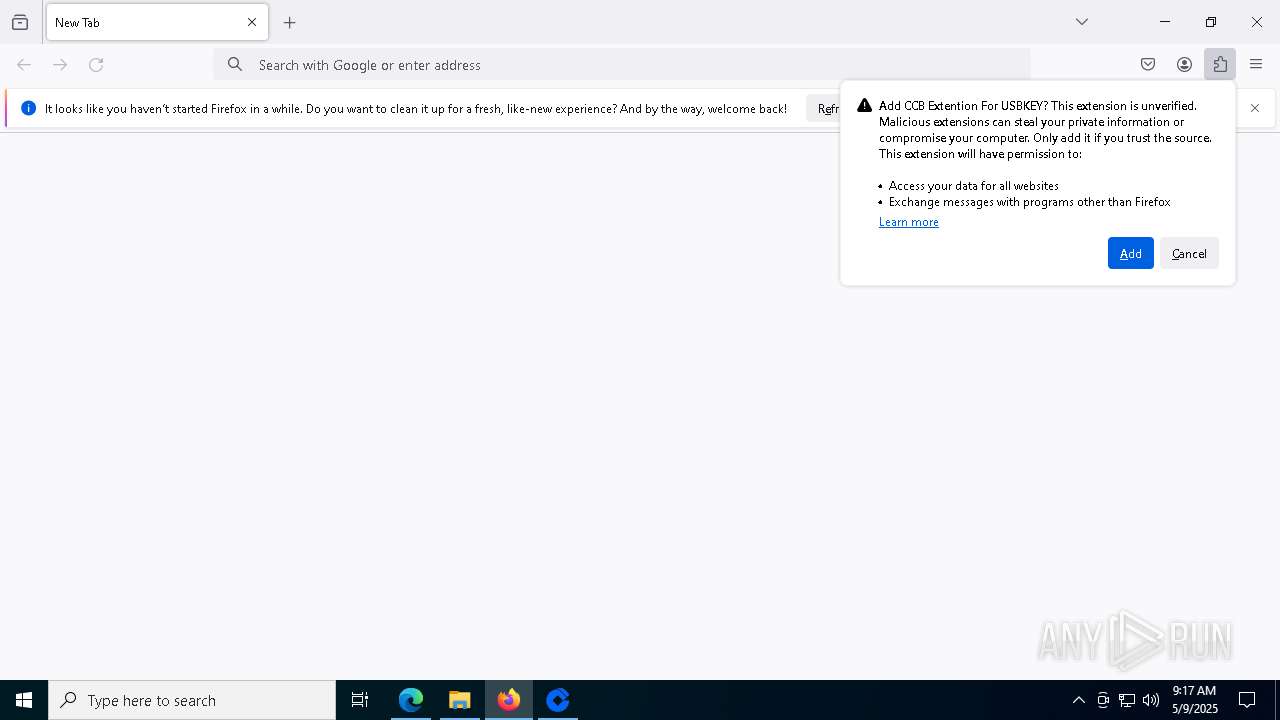
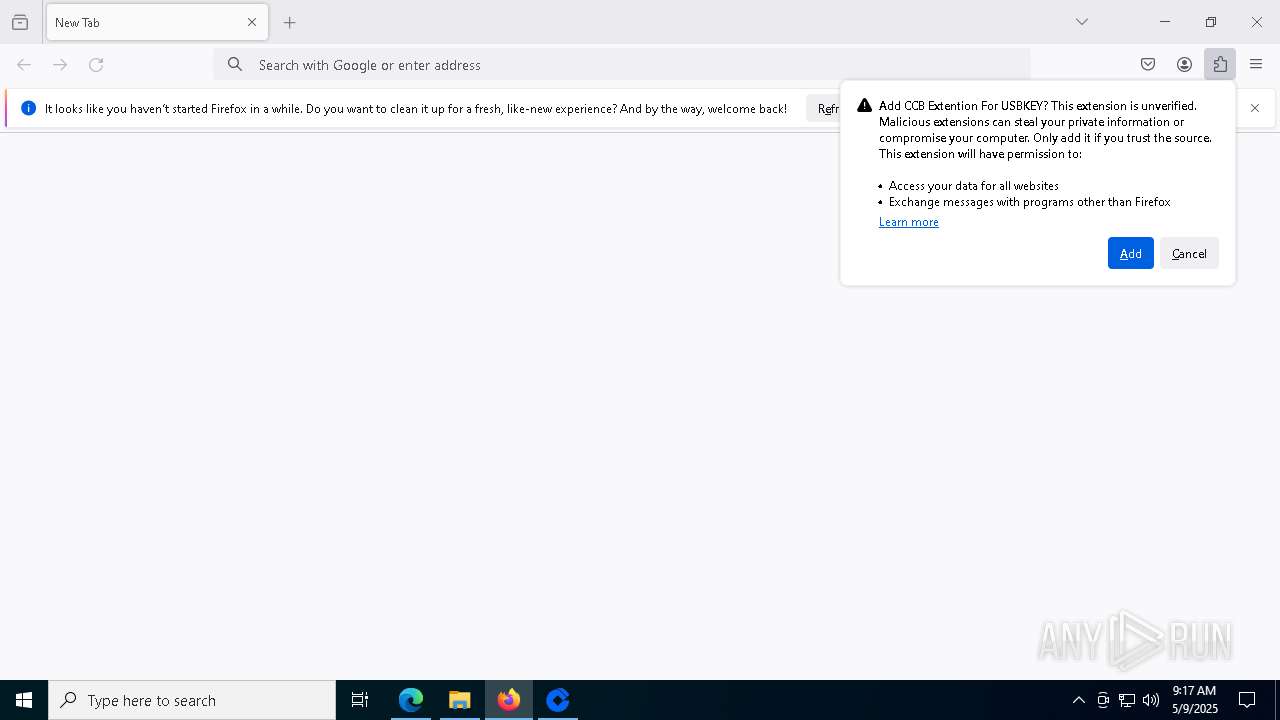
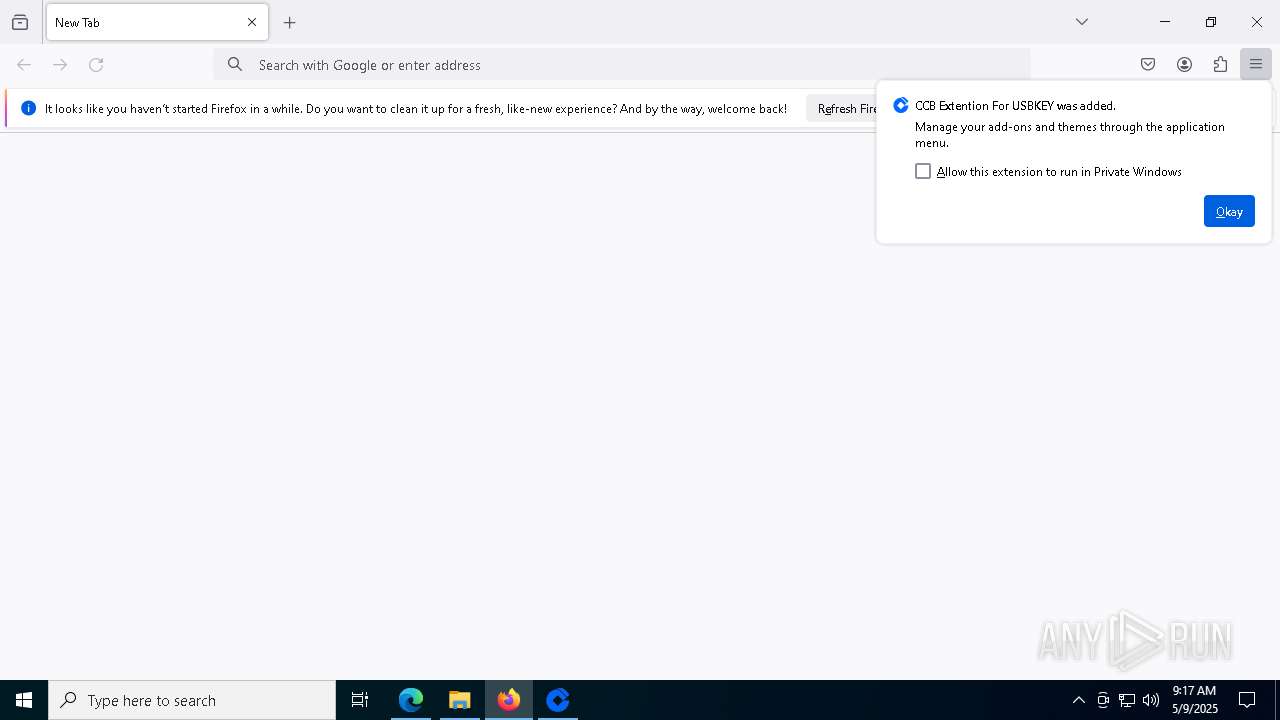
Executing a file with an untrusted certificate
- CCB_DM_LCD_silent_x64.exe (PID: 8008)
- InstallP11.exe (PID: 4164)
- CCBCertificate.exe (PID: 1088)
- HZ_CommSrv.exe (PID: 7424)
- InterPass3000_CCB_s.exe (PID: 6988)
- regFirefox.exe (PID: 5576)
- USBKeyTools.exe (PID: 4284)
- regFirefox64.exe (PID: 2344)
- registCCID.exe (PID: 8012)
- registerocx.exe (PID: 6136)
- WDKSPconfig.exe (PID: 4024)
- InstallUsbccid.exe (PID: 7248)
- InstallUsbccid.exe (PID: 3304)
- InstallUsbccid.exe (PID: 9072)
- InstallUsbccid.exe (PID: 7960)
- InstallUsbccid.exe (PID: 9376)
- InstallUsbccid.exe (PID: 9100)
Changes the autorun value in the registry
- CCB_DM_LCD_silent_x64.exe (PID: 8008)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 1600)
SUSPICIOUS
Executable content was dropped or overwritten
- CCB_E_Setup_Total_2025042801.exe (PID: 7180)
- CCB_DM_LCD_silent_x64.exe (PID: 8008)
- CCB_HDZB_USBKEY_2G_Setup_S64.exe (PID: 4400)
- CCB_HDZB_USBKEY_1G_Setup_S64.exe (PID: 8144)
- InterPass3000_CCB_s.exe (PID: 6988)
- OnKey_Install_Silent.exe (PID: 7192)
- WDCCB_32+64bit.exe (PID: 8124)
- CCBExtension_installer.exe (PID: 7864)
- ESKeySetup_CCB.exe (PID: 7876)
Process drops legitimate windows executable
- CCB_E_Setup_Total_2025042801.exe (PID: 7180)
- CCB_DM_LCD_silent_x64.exe (PID: 8008)
- CCB_HDZB_USBKEY_2G_Setup_S64.exe (PID: 4400)
- OnKey_Install_Silent.exe (PID: 7192)
- WDCCB_32+64bit.exe (PID: 8124)
- ESKeySetup_CCB.exe (PID: 7876)
The process drops C-runtime libraries
- CCB_E_Setup_Total_2025042801.exe (PID: 7180)
- ESKeySetup_CCB.exe (PID: 7876)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 664)
- regsvr32.exe (PID: 4120)
- regsvr32.exe (PID: 6644)
- regsvr32.exe (PID: 5392)
- regsvr32.exe (PID: 3008)
- regsvr32.exe (PID: 6660)
- regsvr32.exe (PID: 5136)
- regsvr32.exe (PID: 7424)
- regsvr32.exe (PID: 7232)
- regsvr32.exe (PID: 2268)
- regsvr32.exe (PID: 7492)
- regsvr32.exe (PID: 5596)
- regsvr32.exe (PID: 1300)
- regsvr32.exe (PID: 6816)
- regsvr32.exe (PID: 2340)
- regsvr32.exe (PID: 1040)
- regsvr32.exe (PID: 8080)
- regsvr32.exe (PID: 8140)
- regsvr32.exe (PID: 7012)
- regsvr32.exe (PID: 7240)
- regsvr32.exe (PID: 856)
- CCB_HDZB_USBKEY_2G_Setup_S64.exe (PID: 4400)
- regsvr32.exe (PID: 8064)
There is functionality for taking screenshot (YARA)
- CCB_E_Setup_Total_2025042801.exe (PID: 7180)
- CCBCertificate.exe (PID: 1088)
The process creates files with name similar to system file names
- CCB_DM_LCD_silent_x64.exe (PID: 8008)
- CCB_HDZB_USBKEY_2G_Setup_S64.exe (PID: 4400)
Malware-specific behavior (creating "System.dll" in Temp)
- CCB_DM_LCD_silent_x64.exe (PID: 8008)
- CCB_HDZB_USBKEY_2G_Setup_S64.exe (PID: 4400)
- CCB_HDZB_USBKEY_1G_Setup_S64.exe (PID: 8144)
- InterPass3000_CCB_s.exe (PID: 6988)
- OnKey_Install_Silent.exe (PID: 7192)
- WDCCB_32+64bit.exe (PID: 8124)
- CCBExtension_installer.exe (PID: 7864)
Drops a system driver (possible attempt to evade defenses)
- CCB_DM_LCD_silent_x64.exe (PID: 8008)
- CCB_HDZB_USBKEY_2G_Setup_S64.exe (PID: 4400)
- OnKey_Install_Silent.exe (PID: 7192)
- WDCCB_32+64bit.exe (PID: 8124)
Reads security settings of Internet Explorer
- CCB_DM_LCD_silent_x64.exe (PID: 8008)
Starts CMD.EXE for commands execution
- CCB_DM_LCD_silent_x64.exe (PID: 8008)
- CCB_HDZB_USBKEY_2G_Setup_S64.exe (PID: 4400)
- CCB_HDZB_USBKEY_1G_Setup_S64.exe (PID: 8144)
- WDCCB_32+64bit.exe (PID: 8124)
- wSpawn.exe (PID: 9100)
- CcbFfxP11Loader_x64.exe (PID: 3268)
- wSpawn.exe (PID: 8540)
- wSpawn.exe (PID: 1748)
- wSpawn.exe (PID: 9116)
- CcbFfxP11Loader.exe (PID: 7440)
- wSpawn.exe (PID: 4688)
- wSpawn.exe (PID: 8544)
Windows service management via SC.EXE
- sc.exe (PID: 2908)
- sc.exe (PID: 6760)
- sc.exe (PID: 7020)
- sc.exe (PID: 7484)
- sc.exe (PID: 968)
- sc.exe (PID: 7864)
- sc.exe (PID: 3024)
- sc.exe (PID: 4164)
- sc.exe (PID: 7972)
- sc.exe (PID: 2692)
Creates a new Windows service
- sc.exe (PID: 6456)
- sc.exe (PID: 6252)
Executes as Windows Service
- CCB_HDZB_2G_DeviceService.exe (PID: 6108)
- HZ_CommSrv.exe (PID: 7424)
- D4Ser_CCB.exe (PID: 2240)
- WDKeyMonitorCCB.exe (PID: 2420)
- EsCcbDriverSrv.exe (PID: 8488)
Creates or modifies Windows services
- CCB_HDZB_USBKEY_2G_Setup_S64.exe (PID: 4400)
Creates a software uninstall entry
- CCB_HDZB_USBKEY_2G_Setup_S64.exe (PID: 4400)
Adds/modifies Windows certificates
- CCB_HDZB_USBKEY_2G_Setup_S64.exe (PID: 4400)
Sets the service to start on system boot
- sc.exe (PID: 5600)
Application launched itself
- D4Svr_CCB.exe (PID: 4424)
Uses REG/REGEDIT.EXE to modify registry
- OnKey_Install_Silent.exe (PID: 7192)
The process executes via Task Scheduler
- WDCertM_CCB.exe (PID: 8496)
INFO
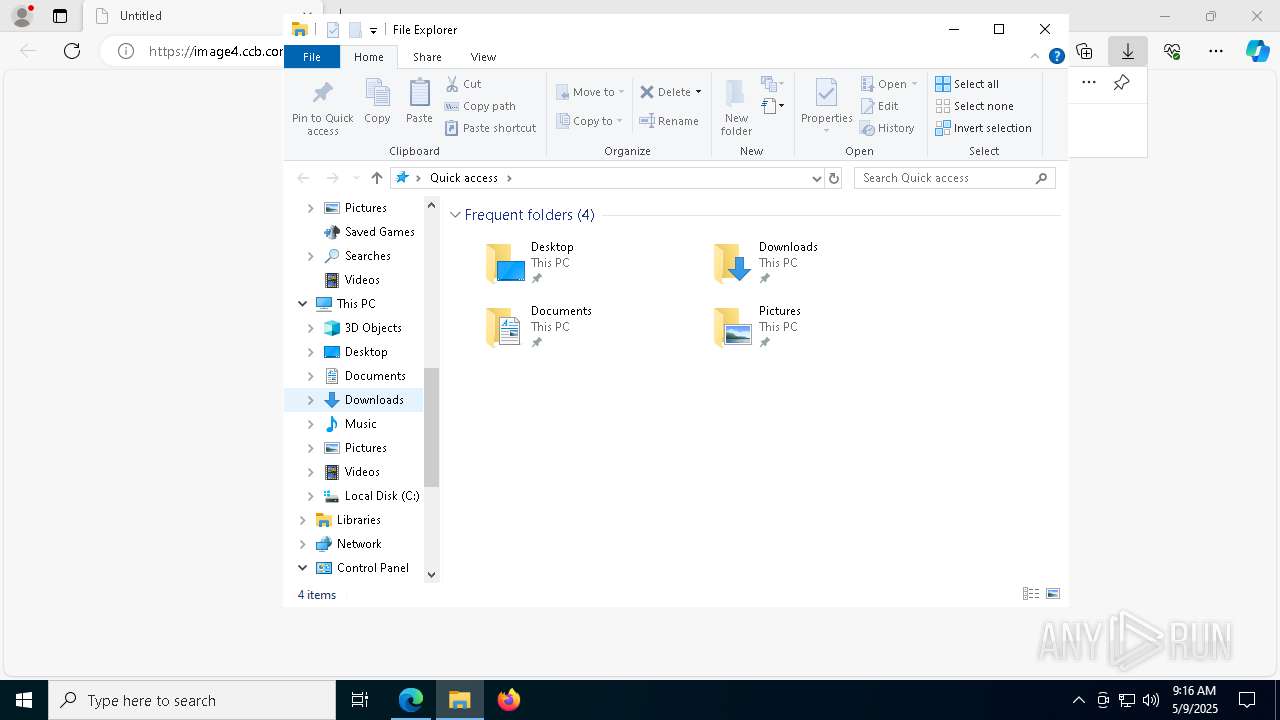
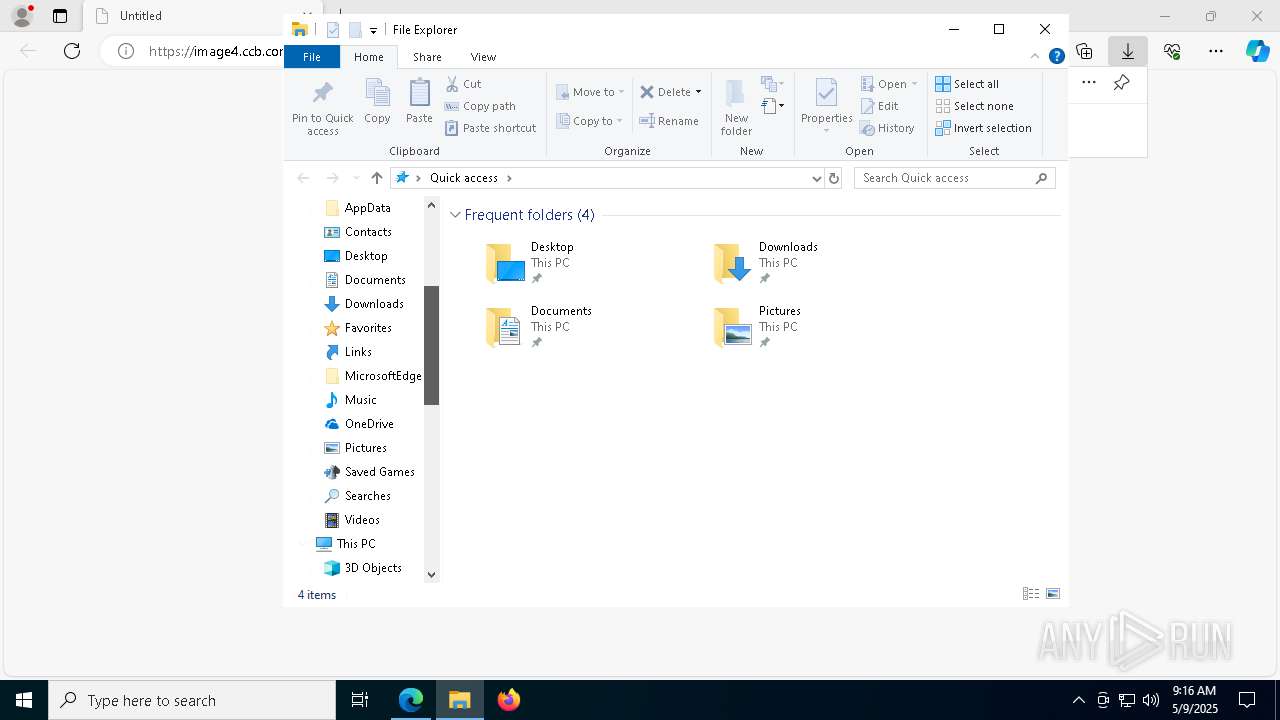
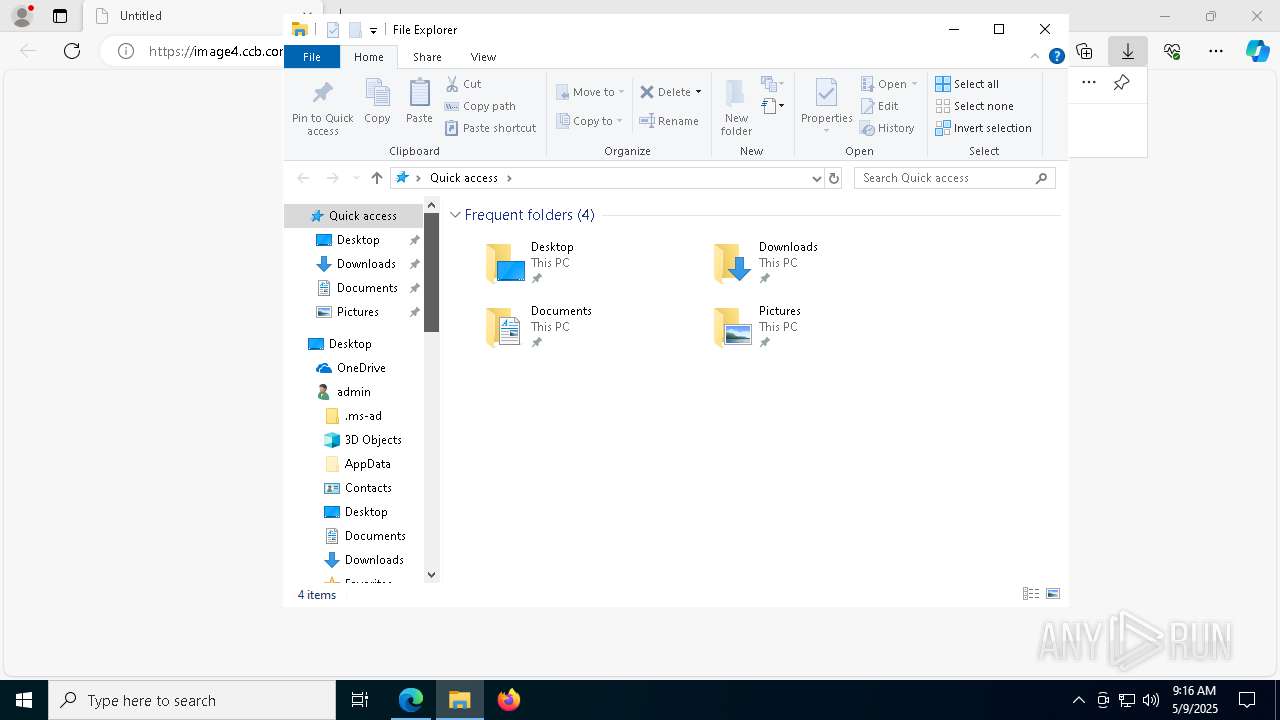
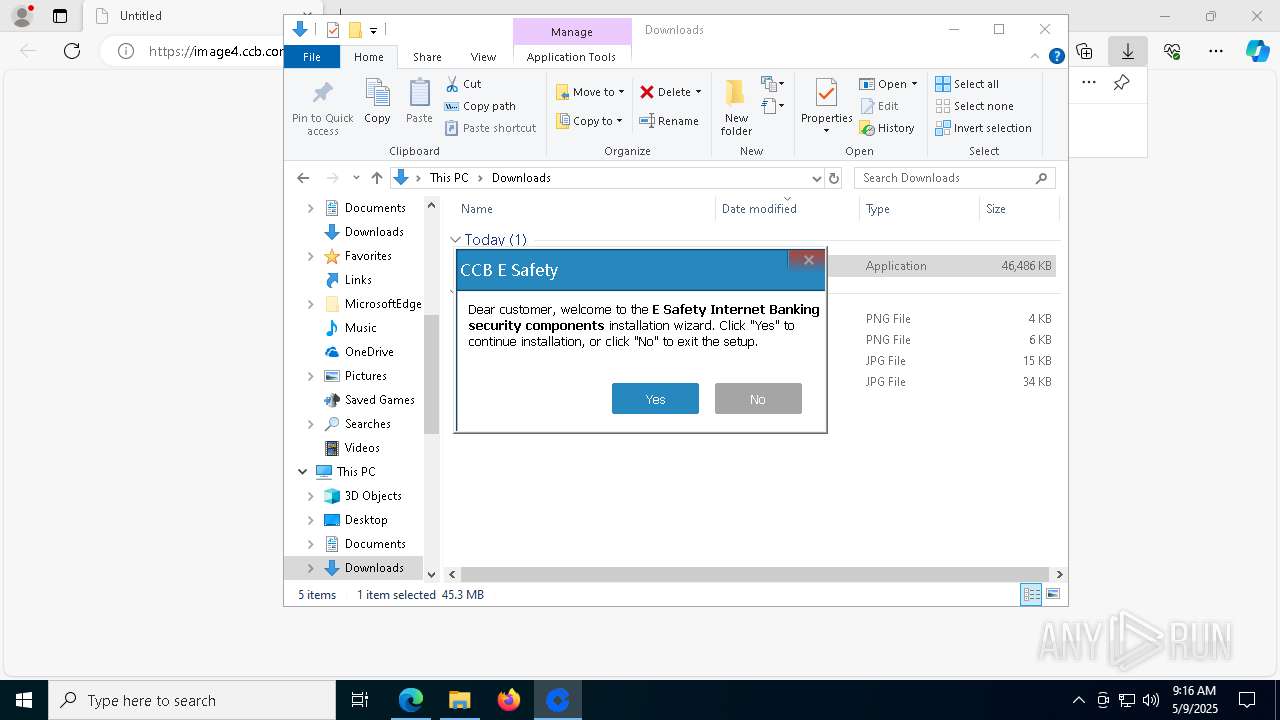
Manual execution by a user
- CCB_E_Setup_Total_2025042801.exe (PID: 5608)
- CCB_E_Setup_Total_2025042801.exe (PID: 7180)
- firefox.exe (PID: 6136)
Application launched itself
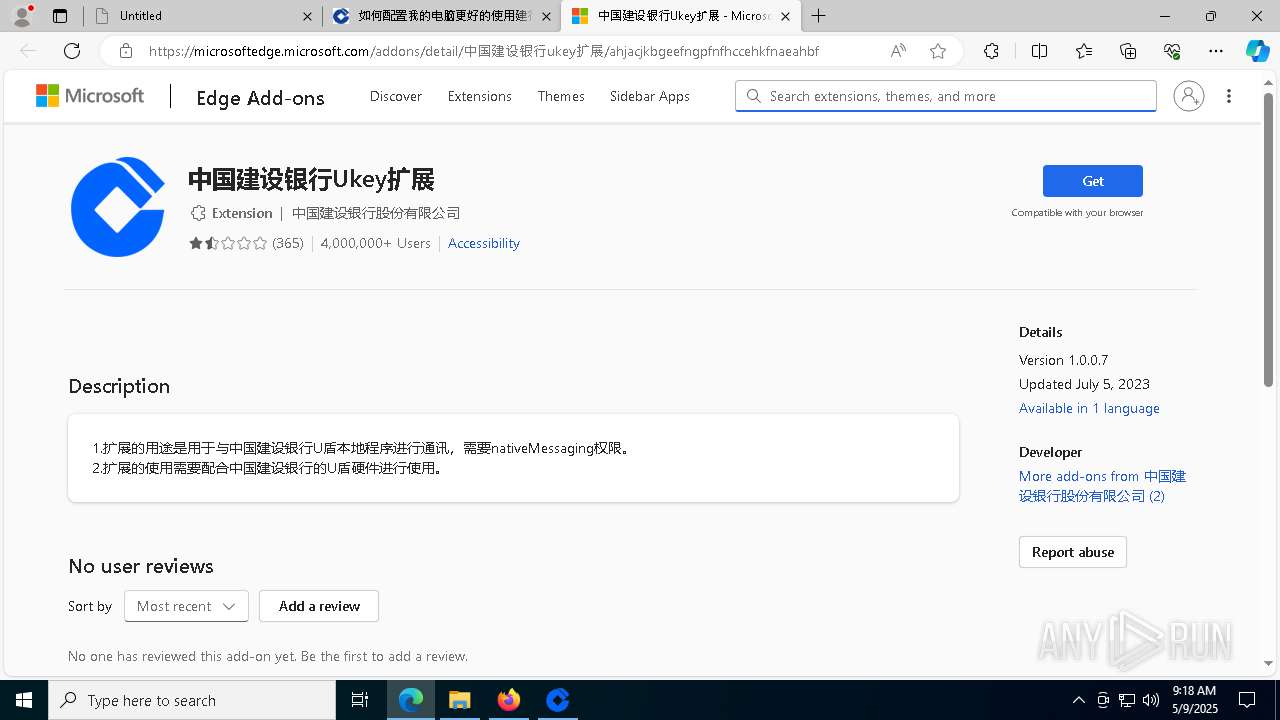
- msedge.exe (PID: 7284)
- firefox.exe (PID: 6136)
- firefox.exe (PID: 5556)
Executable content was dropped or overwritten
- msedge.exe (PID: 7284)
Reads the computer name
- CCB_E_Setup_Total_2025042801.exe (PID: 7180)
- CCB_DM_LCD_silent_x64.exe (PID: 8008)
- InstallP11.exe (PID: 4164)
- CCBCertificate.exe (PID: 1088)
- CCB_HDZB_2G_DeviceService.exe (PID: 6108)
- CCB_HDZB_USBKEY_2G_Setup_S64.exe (PID: 4400)
Checks supported languages
- CCB_E_Setup_Total_2025042801.exe (PID: 7180)
- CCB_DM_LCD_silent_x64.exe (PID: 8008)
- InstallP11.exe (PID: 4164)
- CCBCertificate.exe (PID: 1088)
- CCB_HDZB_USBKEY_2G_Setup_S64.exe (PID: 4400)
- CCB_HDZB_2G_DeviceService.exe (PID: 6108)
Create files in a temporary directory
- CCB_E_Setup_Total_2025042801.exe (PID: 7180)
- CCB_DM_LCD_silent_x64.exe (PID: 8008)
- CCB_HDZB_USBKEY_2G_Setup_S64.exe (PID: 4400)
Creates files in the program directory
- CCB_E_Setup_Total_2025042801.exe (PID: 7180)
- CCB_DM_LCD_silent_x64.exe (PID: 8008)
- CCB_HDZB_USBKEY_2G_Setup_S64.exe (PID: 4400)
The sample compiled with english language support
- CCB_E_Setup_Total_2025042801.exe (PID: 7180)
- CCB_DM_LCD_silent_x64.exe (PID: 8008)
- CCB_HDZB_USBKEY_2G_Setup_S64.exe (PID: 4400)
- CCB_HDZB_USBKEY_1G_Setup_S64.exe (PID: 8144)
- InterPass3000_CCB_s.exe (PID: 6988)
- OnKey_Install_Silent.exe (PID: 7192)
- WDCCB_32+64bit.exe (PID: 8124)
- ESKeySetup_CCB.exe (PID: 7876)
The sample compiled with chinese language support
- CCB_E_Setup_Total_2025042801.exe (PID: 7180)
- CCB_DM_LCD_silent_x64.exe (PID: 8008)
- CCB_HDZB_USBKEY_2G_Setup_S64.exe (PID: 4400)
- CCB_HDZB_USBKEY_1G_Setup_S64.exe (PID: 8144)
- InterPass3000_CCB_s.exe (PID: 6988)
- WDCCB_32+64bit.exe (PID: 8124)
- ESKeySetup_CCB.exe (PID: 7876)
Aspack has been detected
- CCB_E_Setup_Total_2025042801.exe (PID: 7180)
Process checks computer location settings
- CCB_DM_LCD_silent_x64.exe (PID: 8008)
Creates files or folders in the user directory
- InstallP11.exe (PID: 4164)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
398
Monitored processes
259
Malicious processes
11
Suspicious processes
16
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 540 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | CcbFfxP11Loader.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | regsvr32 /s "C:\WINDOWS\system32\CCBKCSPV2.dll" | C:\Windows\SysWOW64\regsvr32.exe | — | CCB_DM_LCD_silent_x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 664 | C:\WINDOWS\SysWow64\regsvr32.exe /s "C:\WINDOWS\SysWow64\CCBSignCom.ocx" | C:\Windows\SysWOW64\regsvr32.exe | — | CCB_E_Setup_Total_2025042801.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6496 --field-trial-handle=2484,i,9884033901894072359,4993888192932102366,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 684 | C:\WINDOWS\SysWow64\regsvr32.exe /s "C:\Program Files\CCBComponents\Detector\CCBSignCom.dll" | C:\Windows\SysWOW64\regsvr32.exe | — | CCB_E_Setup_Total_2025042801.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 856 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 856 | regsvr32 /s "C:\WINDOWS\system32\GetID.ocx" | C:\Windows\System32\regsvr32.exe | — | CCB_DM_LCD_silent_x64.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 900 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 904 | C:\WINDOWS\system32\REGSVR32.EXE /s "C:\WINDOWS\system32\Ccb_SN_ftsafe.dll" | C:\Windows\SysWOW64\regsvr32.exe | — | InterPass3000_CCB_s.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 968 | C:\WINDOWS\system32\sc.exe start CertPropSvc | C:\Windows\SysWOW64\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
53 828
Read events
49 771
Write events
3 416
Delete events
641
Modification events
| (PID) Process: | (7284) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7284) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7284) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7284) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7284) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 89339FB346932F00 | |||
| (PID) Process: | (7284) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 83FAA8B346932F00 | |||
| (PID) Process: | (7284) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262920 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A488278E-9630-439D-9A49-980A8C6B9FC3} | |||
| (PID) Process: | (7284) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262920 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {EE4426E1-A92F-402E-AE30-F8D3709731DB} | |||
| (PID) Process: | (7284) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: A708CDB346932F00 | |||
| (PID) Process: | (7284) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
570
Suspicious files
610
Text files
283
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b596.TMP | — | |
MD5:— | SHA256:— | |||
| 7284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b5b5.TMP | — | |
MD5:— | SHA256:— | |||
| 7284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b5b5.TMP | — | |
MD5:— | SHA256:— | |||
| 7284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b5d5.TMP | — | |
MD5:— | SHA256:— | |||
| 7284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b603.TMP | — | |
MD5:— | SHA256:— | |||
| 7284 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
47
TCP/UDP connections
129
DNS requests
189
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
2104 | svchost.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
— | — | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 868 b | whitelisted |
2104 | svchost.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 868 b | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 868 b | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
5256 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1747173316&P2=404&P3=2&P4=kw8tamETxwtOtodu2yVTadl6i2jZgJj46DuulDJDD8vb0HIJPo7UFEqb54s7PPsprmyZdQeBEREYrxn9Y4l9Rg%3d%3d | US | — | — | whitelisted |
5256 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1747173316&P2=404&P3=2&P4=kw8tamETxwtOtodu2yVTadl6i2jZgJj46DuulDJDD8vb0HIJPo7UFEqb54s7PPsprmyZdQeBEREYrxn9Y4l9Rg%3d%3d | US | binary | 1.09 Kb | whitelisted |
5256 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/a575cead-e662-4f4d-b0c3-81f1438d0388?P1=1747173316&P2=404&P3=2&P4=kw8tamETxwtOtodu2yVTadl6i2jZgJj46DuulDJDD8vb0HIJPo7UFEqb54s7PPsprmyZdQeBEREYrxn9Y4l9Rg%3d%3d | US | binary | 9.51 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.53.40.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
image4.ccb.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7592 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |
7592 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |