| File name: | AntivirusBypass.exe |
| Full analysis: | https://app.any.run/tasks/c6f140a1-a188-4bb0-996e-4a39f6bbdd9f |
| Verdict: | Malicious activity |
| Analysis date: | March 22, 2025, 21:46:37 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 6 sections |
| MD5: | 70B284B8324BFD438BFACB27355E94E7 |
| SHA1: | 0CA539FAE5E1205B354274D4EA0DE45B56FDEFA4 |
| SHA256: | F937D7D3A29CDF9BD7D8388C6C020AE57DB047251F03160D03EDE9B2CC1B3932 |
| SSDEEP: | 12288:QmhzpE0nbIMB0e8UbBLLZrsvBULikZzZPSRP5wgn4LACFzgFpzR0VmEHXRBWKltF:QW9rNLO0btDzRlKcm06RjA |
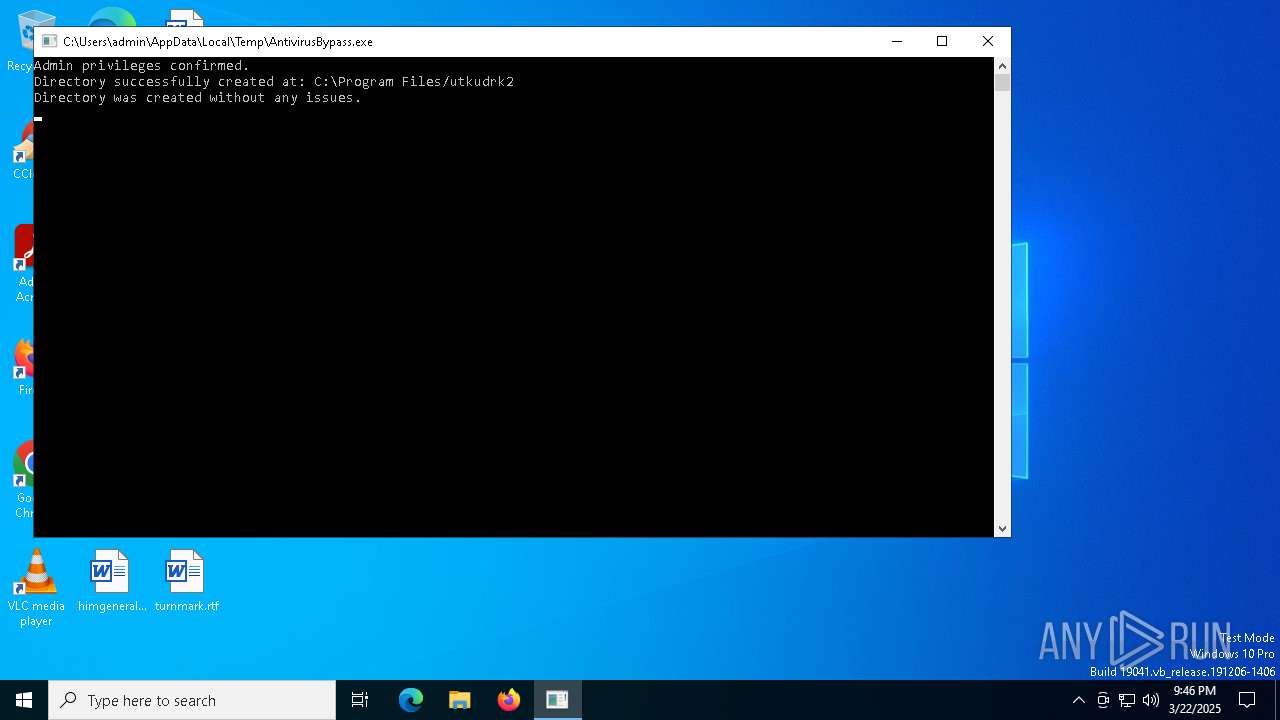
MALICIOUS
Executing a file with an untrusted certificate
- AntivirusBypass.exe (PID: 1276)
- AntivirusBypass.exe (PID: 2284)
Changes the login/logoff helper path in the registry
- AntivirusBypass.exe (PID: 1276)
SUSPICIOUS
Creates file in the systems drive root
- AntivirusBypass.exe (PID: 1276)
Executable content was dropped or overwritten
- AntivirusBypass.exe (PID: 1276)
Starts CMD.EXE for commands execution
- AntivirusBypass.exe (PID: 1276)
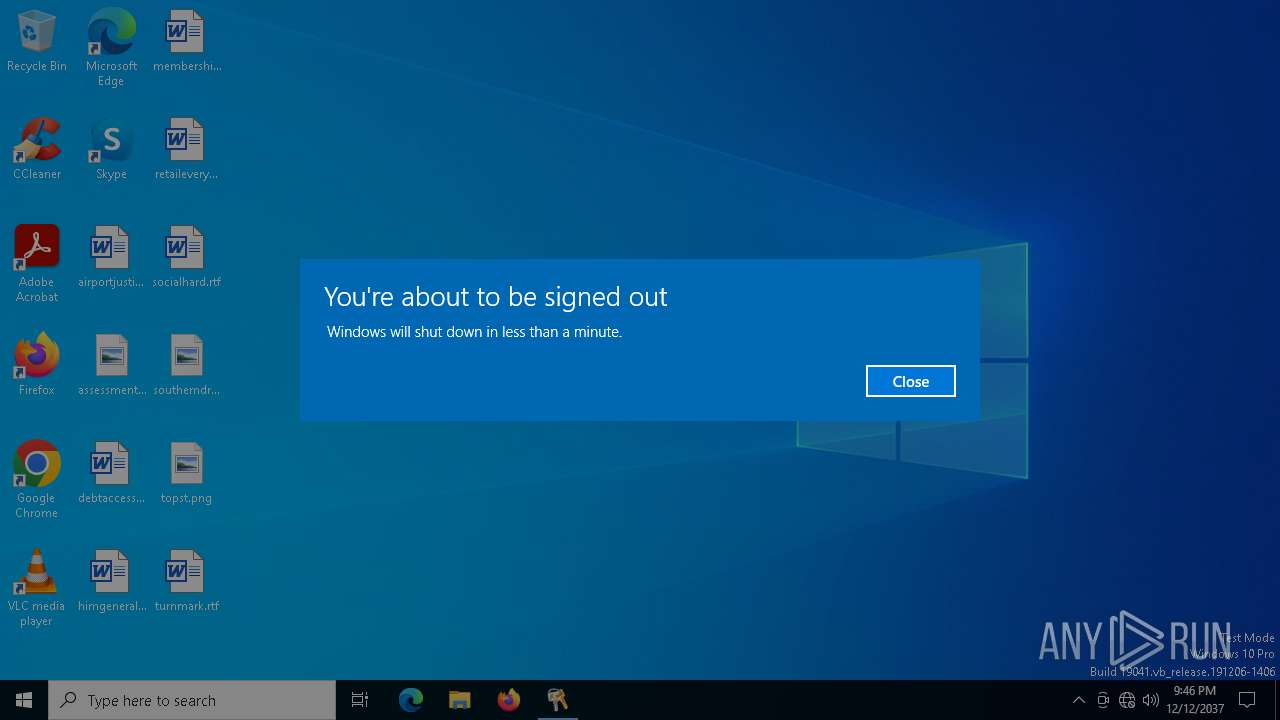
The system shut down or reboot
- AntivirusBypass.exe (PID: 1276)
Suspicious use of NETSH.EXE
- AntivirusBypass.exe (PID: 1276)
Executes as Windows Service
- upfc.exe (PID: 7436)
The process creates files with name similar to system file names
- AntivirusBypass.exe (PID: 1276)
Identifying current user with WHOAMI command
- AntivirusBypass.exe (PID: 1276)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 3976)
INFO
Creates files in the program directory
- AntivirusBypass.exe (PID: 1276)
- PLUGScheduler.exe (PID: 3976)
Checks supported languages
- AntivirusBypass.exe (PID: 1276)
- PLUGScheduler.exe (PID: 3976)
Disables trace logs
- netsh.exe (PID: 7224)
- netsh.exe (PID: 2320)
Reads the computer name
- PLUGScheduler.exe (PID: 3976)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:02:12 18:49:58+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.41 |
| CodeSize: | 222208 |
| InitializedDataSize: | 696832 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3529c |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 0.1.0.0 |
| ProductVersionNumber: | 0.1.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | AntivirusBypass |
| ProductName: | AntivirusBypass |
| FileVersion: | 0.1.0 |
| ProductVersion: | 0.1.0 |
Total processes
245
Monitored processes
22
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1276 | "C:\Users\admin\AppData\Local\Temp\AntivirusBypass.exe" | C:\Users\admin\AppData\Local\Temp\AntivirusBypass.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: AntivirusBypass Exit code: 0 Version: 0.1.0 Modules
| |||||||||||||||
| 2284 | "C:\Users\admin\AppData\Local\Temp\AntivirusBypass.exe" | C:\Users\admin\AppData\Local\Temp\AntivirusBypass.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: AntivirusBypass Exit code: 3221226540 Version: 0.1.0 Modules
| |||||||||||||||
| 2320 | "netsh" interface show interface | C:\Windows\System32\netsh.exe | — | AntivirusBypass.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3976 | "C:\Program Files\RUXIM\PLUGscheduler.exe" | C:\Program Files\RUXIM\PLUGScheduler.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Update LifeCycle Component Scheduler Exit code: 0 Version: 10.0.19041.3623 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5576 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | AntivirusBypass.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5968 | "whoami" /groups | C:\Windows\System32\whoami.exe | — | AntivirusBypass.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: whoami - displays logged on user information Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7224 | "netsh" interface set interface Connection disable | C:\Windows\System32\netsh.exe | — | AntivirusBypass.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7412 | "bcdedit.exe" /set {current} safeboot minimal | C:\Windows\System32\bcdedit.exe | — | AntivirusBypass.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Configuration Data Editor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7420 | "cmd" /C "date 12-12-2037" | C:\Windows\System32\cmd.exe | — | AntivirusBypass.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7436 | C:\WINDOWS\System32\Upfc.exe /launchtype periodic /cv r/tw1e3/j0mP58jUkz7IlA.0 | C:\Windows\System32\upfc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Updateability From SCM Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 209
Read events
1 191
Write events
9
Delete events
9
Modification events
| (PID) Process: | (1276) AntivirusBypass.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | Shell |
Value: cmd.exe /c explorer.exe | |||
| (PID) Process: | (7412) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7412) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | write | Name: | Element |
Value: 0000000000000000000000000000000006000000000000004800000000000000715E5C2FA985EB1190A89A9B763584210000000000000000745E5C2FA985EB1190A89A9B7635842100000000000000000000000000000000 | |||
| (PID) Process: | (7412) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\12000002 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7412) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\12000002 |
| Operation: | write | Name: | Element |
Value: \EFI\Microsoft\Boot\bootmgfw.efi | |||
| (PID) Process: | (7412) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{5b970157-8568-11eb-b45c-806e6f6e6963}\Elements\11000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7412) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{5b970157-8568-11eb-b45c-806e6f6e6963}\Elements\11000001 |
| Operation: | write | Name: | Element |
Value: 0000000000000000000000000000000006000000000000004800000000000000715E5C2FA985EB1190A89A9B763584210000000000000000745E5C2FA985EB1190A89A9B7635842100000000000000000000000000000000 | |||
| (PID) Process: | (7412) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{5b970157-8568-11eb-b45c-806e6f6e6963}\Elements\12000002 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7412) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{5b970157-8568-11eb-b45c-806e6f6e6963}\Elements\12000002 |
| Operation: | write | Name: | Element |
Value: \EFI\Boot\Loader.efi | |||
| (PID) Process: | (7412) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{a5a30fa2-3d06-4e9f-b5f4-a01df9d1fcba}\Description |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
1
Suspicious files
44
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3976 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.050.etl | binary | |
MD5:C8834D365FAE073DEDE1F1620454CE71 | SHA256:C6DD793EEE1D5551CA507A3C5BFFECA82DD3E29C63C2C6DD218A7D4BFB37046B | |||
| 3976 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.044.etl | binary | |
MD5:B53B2070E686FFB1FBC8B06994E7C8D7 | SHA256:A3ABD06F4E40CB700B1908AB6BCD2E27455E13EF076E0BF2345BB2FA369EF802 | |||
| 3976 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.046.etl | binary | |
MD5:A7A21FBC9D00F33F186B34A50E170C13 | SHA256:64CAC91E46D4FC832958232A658431CBF9D8D9F265653ACA2BEB32428D4688EC | |||
| 1276 | AntivirusBypass.exe | C:\explorer.exe | executable | |
MD5:63ABFBF7E6A5F5A6F0191F6488F7E85D | SHA256:91861669F00CB712D5A8C60026030674038B9B5924DA5C1B570EF2BF48C21DC4 | |||
| 3976 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.048.etl | binary | |
MD5:A23907B6FDD47DCABFDFD7CF2FCD7671 | SHA256:0C9C33FE9E984A2E5A70EBA51F36B9929A86199E424AF2F8080E1267B87DC970 | |||
| 3976 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.036.etl | binary | |
MD5:A477FE56C25FCDB850EA1AAB8D01B5C2 | SHA256:5C85DC2B41C2D076D6B2653C0BA5F5681ADABFEBDA8883C704E625EB9338F505 | |||
| 3976 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.030.etl | binary | |
MD5:4558A195AA3B11F3AF5D839B627BF95A | SHA256:C6F97F8924A2199569D3B36355531D342FDDC2F84DADF410F34E0D7E8C5A50B2 | |||
| 3976 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.041.etl | binary | |
MD5:09359EE89B0634478ADFF73CDA7BFB12 | SHA256:4D800AC7C55960B107C9D3E40F63130407835E69DF4F5C558C500FC0BD20D8ED | |||
| 3976 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.037.etl | binary | |
MD5:B787593A02A4E0A601164A65952D0CB9 | SHA256:3594AD496D8E1771BCC3E8B6F68B4C2B4190A9A331FB43F068A7DF4E1894E2CF | |||
| 3976 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.038.etl | binary | |
MD5:F9485F2BA891697F8B6CF8FB1E7F42C0 | SHA256:69146D4AAEFB8609745B6CA780B48ABC66054AA3CDB8061248CF7B32F3B32617 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
7
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.19.11.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.19.11.120:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
3216 | svchost.exe | 20.198.162.76:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |