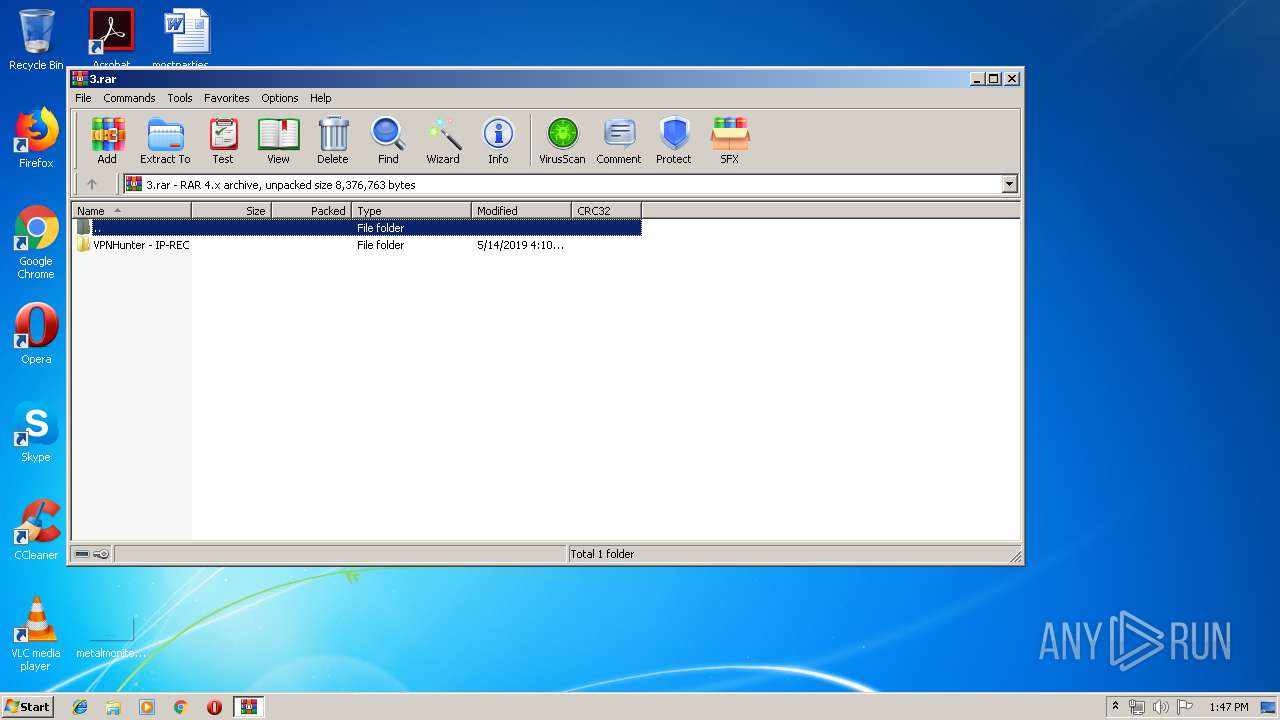
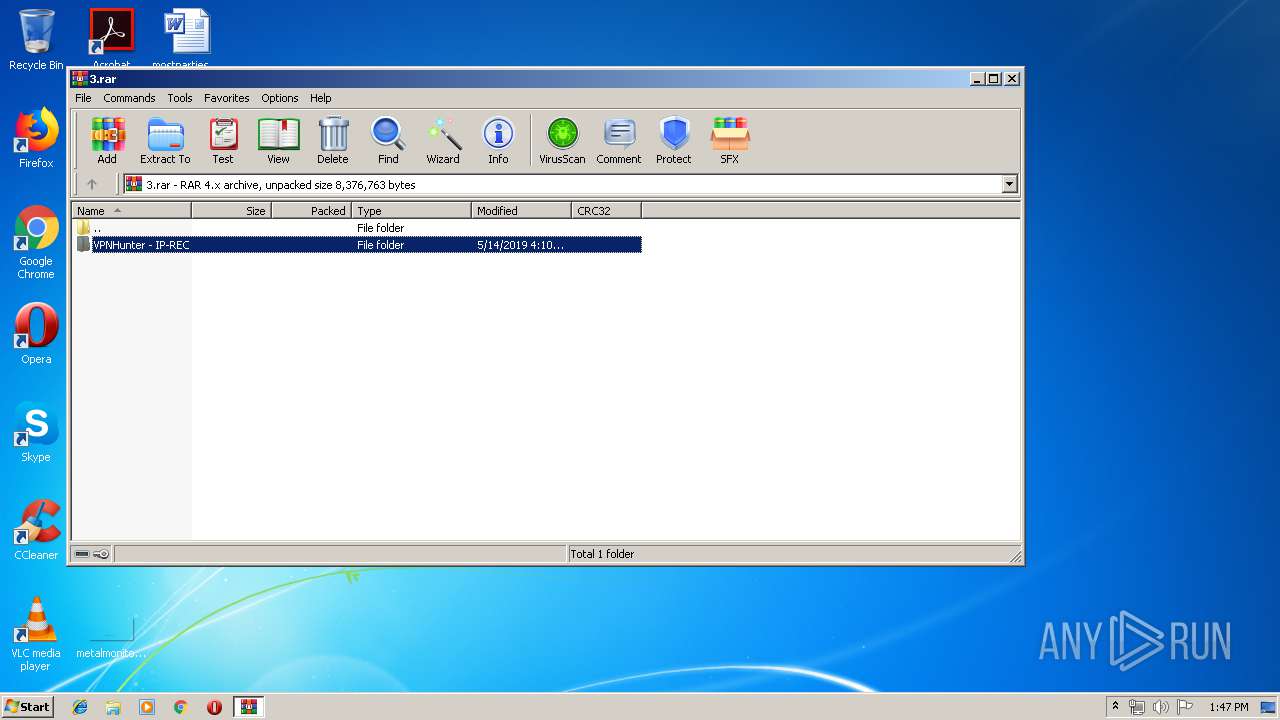
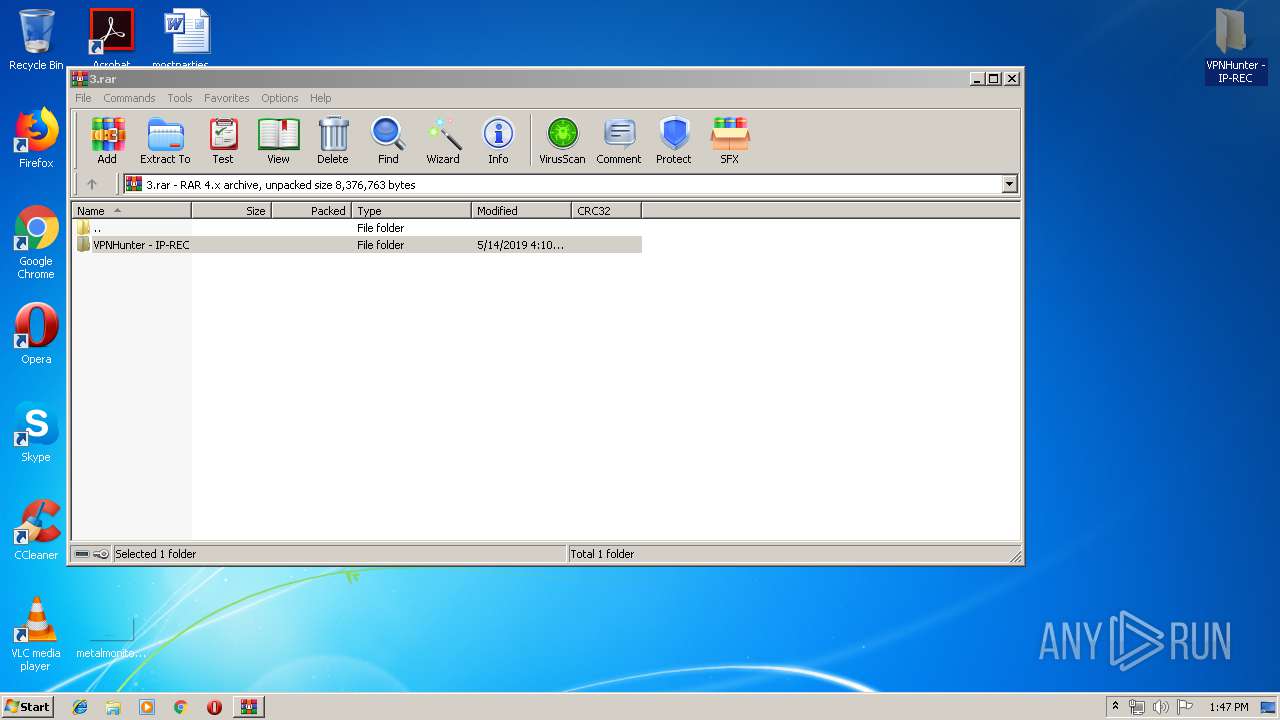
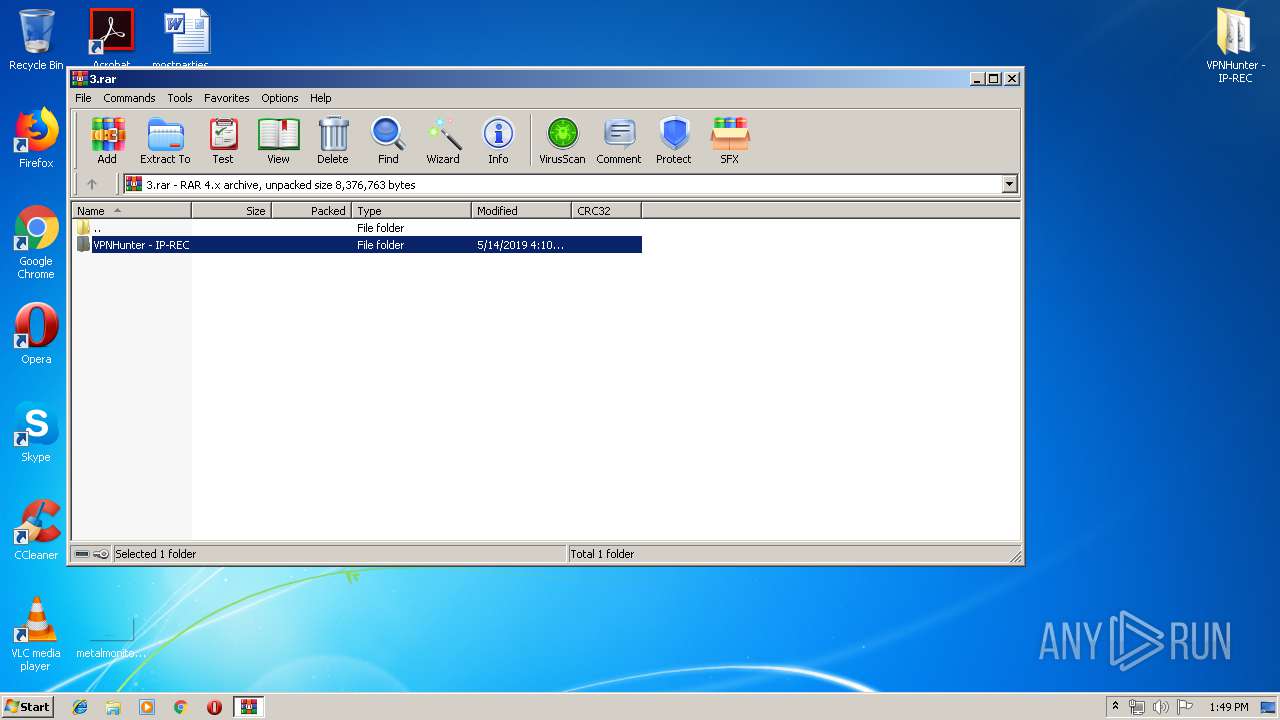
| File name: | 3.rar |
| Full analysis: | https://app.any.run/tasks/3f4b54d7-d677-41b9-a8e5-7d81da83767e |
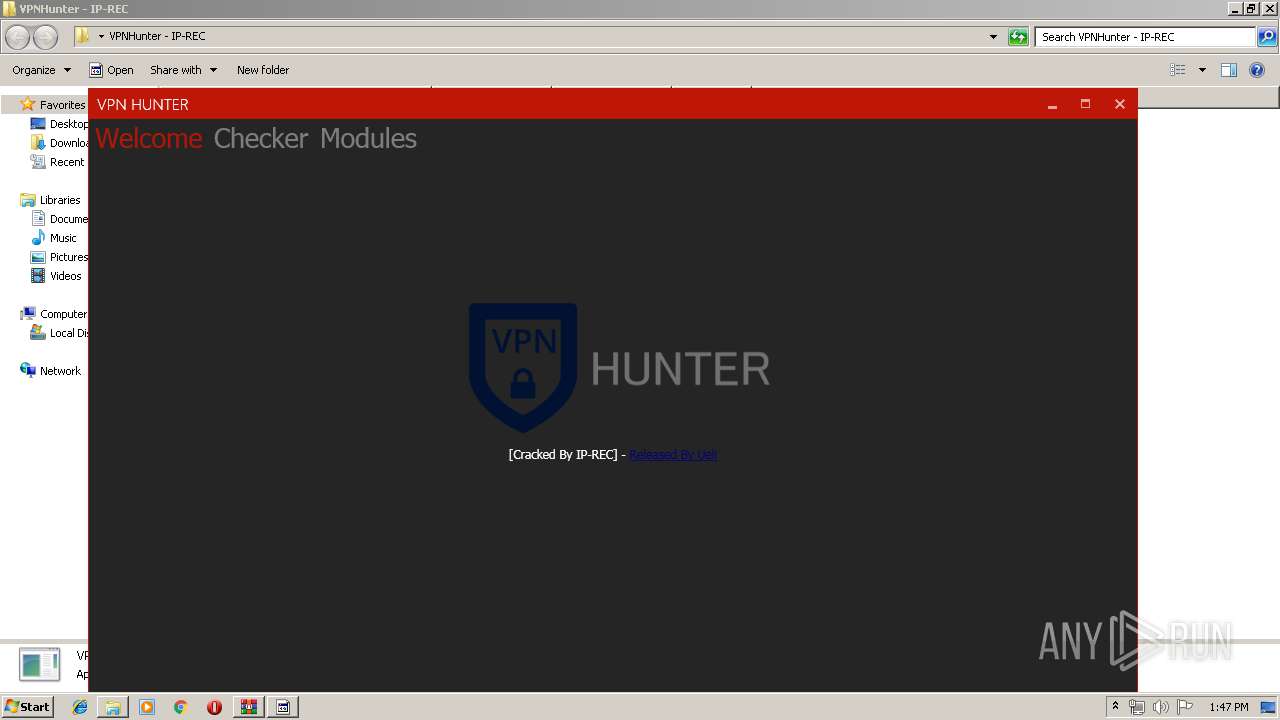
| Verdict: | Malicious activity |
| Analysis date: | May 24, 2019, 12:47:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | AAD53F8F48F25CA4E46F02DA4BF7C0B8 |
| SHA1: | CCEF70315E452F1B8EEE35EB020D9258B4E1A217 |
| SHA256: | F93611D1DC34BA5E3F6725D9769A637D77099D64C21FCF143A3B029FC9DFE551 |
| SSDEEP: | 49152:wC1DolxcVYSPuW9OwXm1XMyPubcGmasXBNPCXlO/y7oJxc0aV0nNx9dtZS:VDobcV/uW9FIXXPPGcXB9CeXxc/KnNDA |
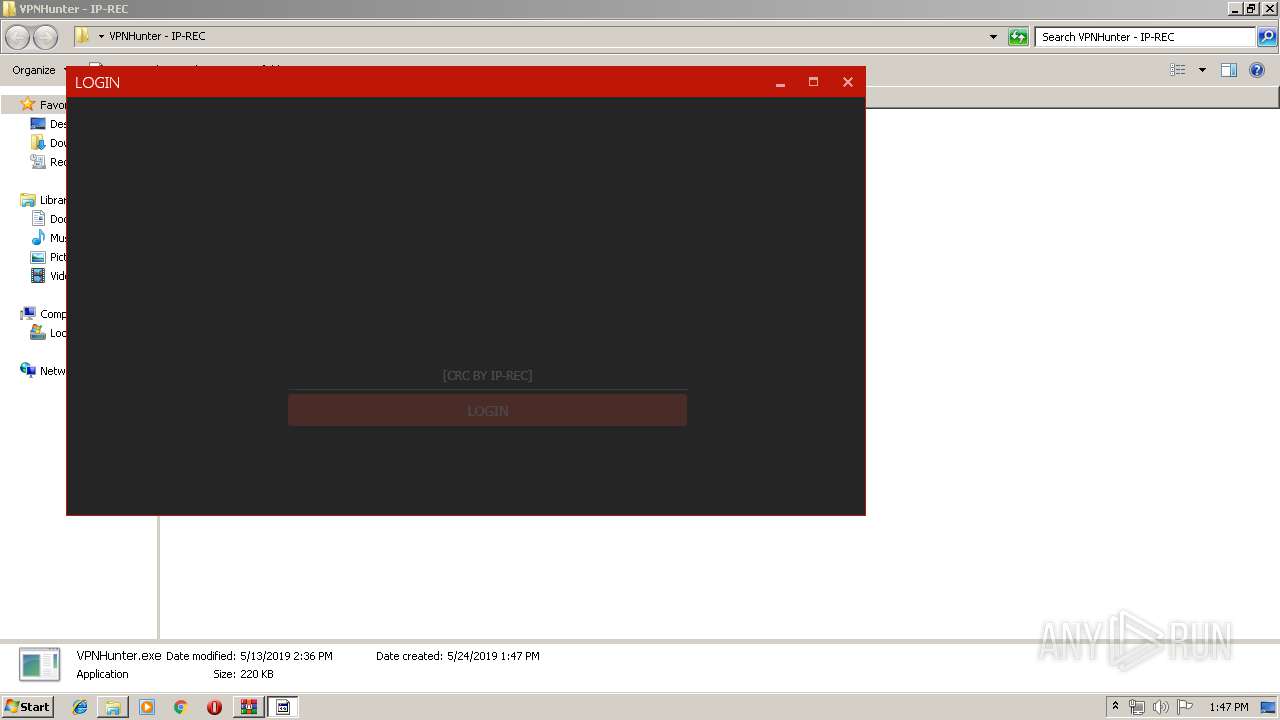
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3572)
- VPNHunter.exe (PID: 584)
Changes settings of System certificates
- VPNHunter.exe (PID: 584)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2088)
Reads Internet Cache Settings
- VPNHunter.exe (PID: 584)
Reads Environment values
- VPNHunter.exe (PID: 584)
Adds / modifies Windows certificates
- VPNHunter.exe (PID: 584)
INFO
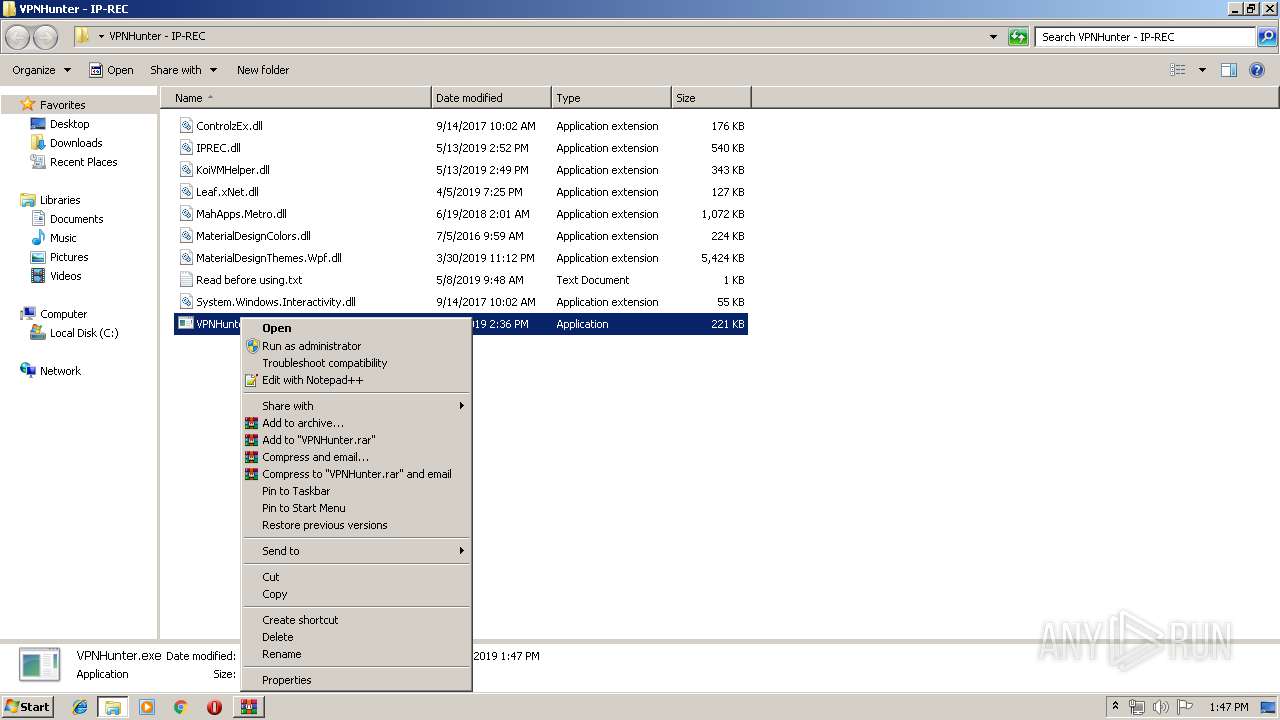
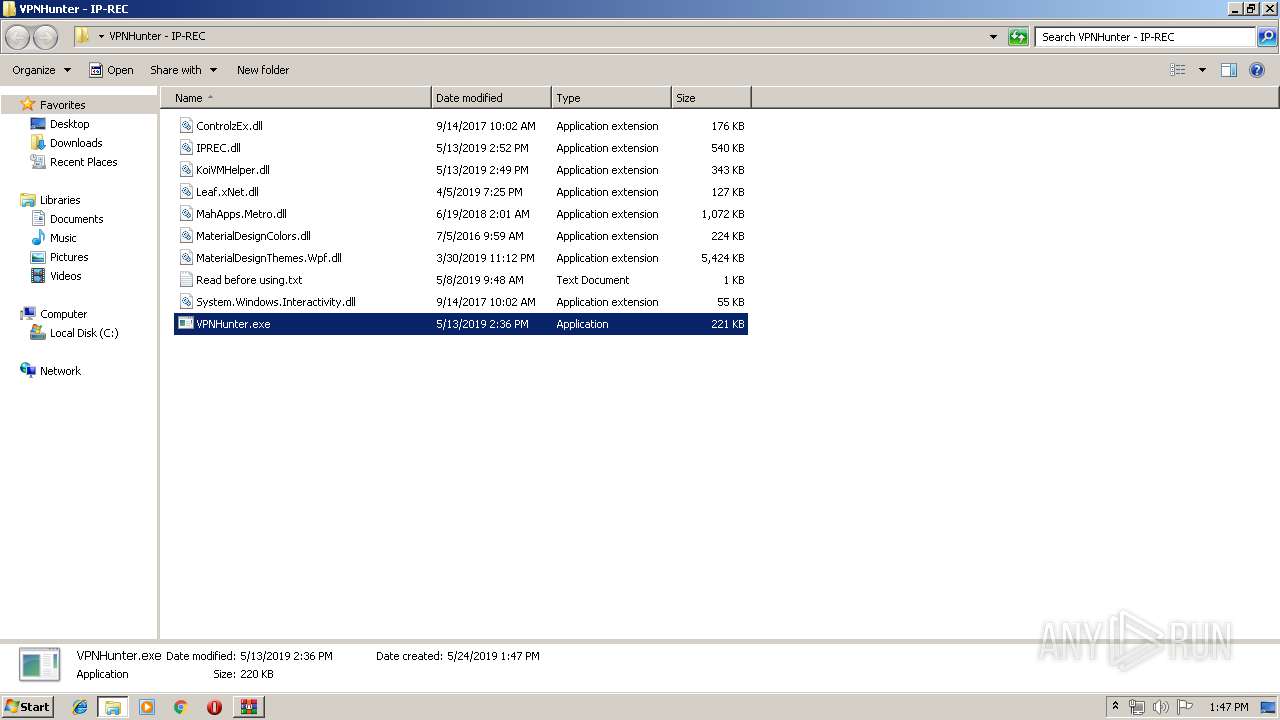
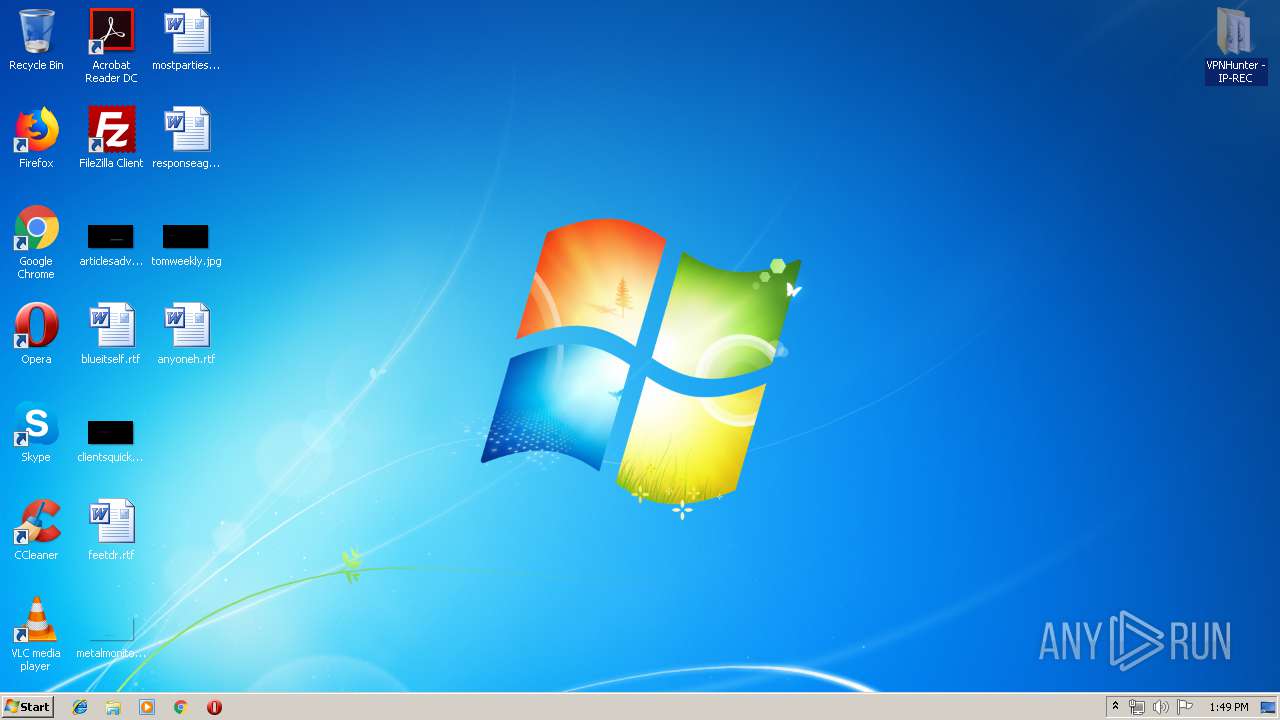
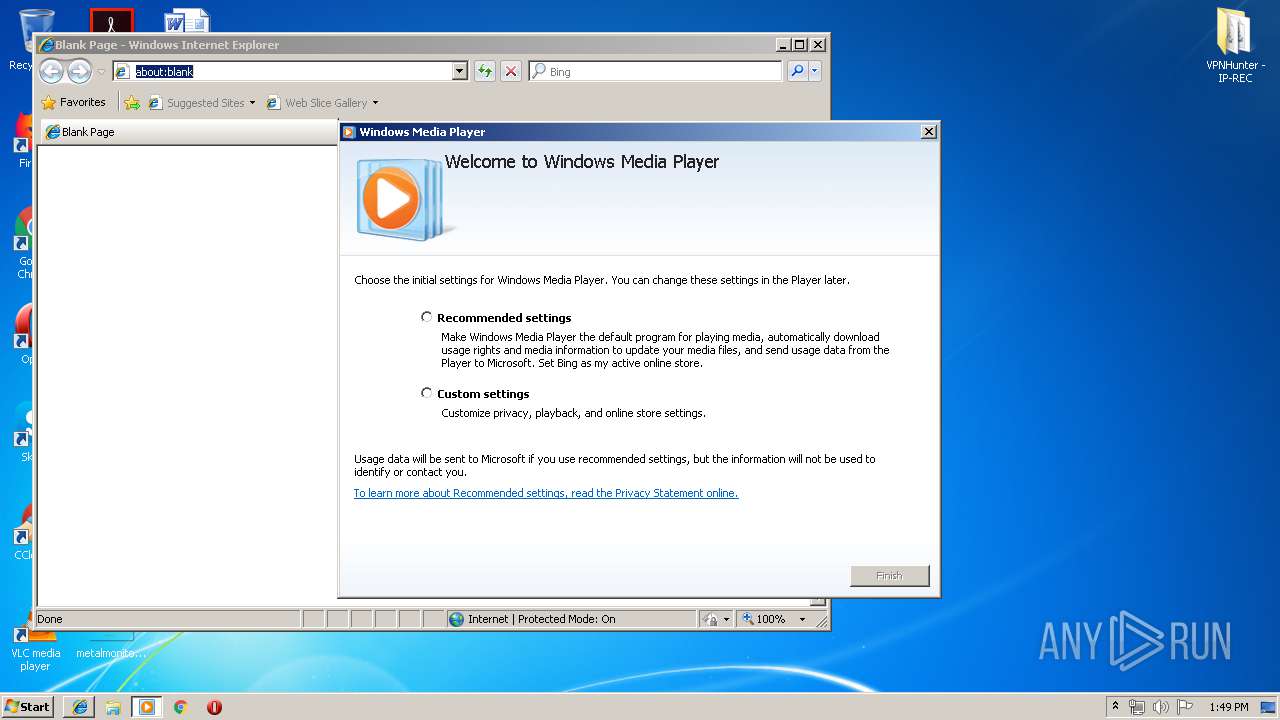
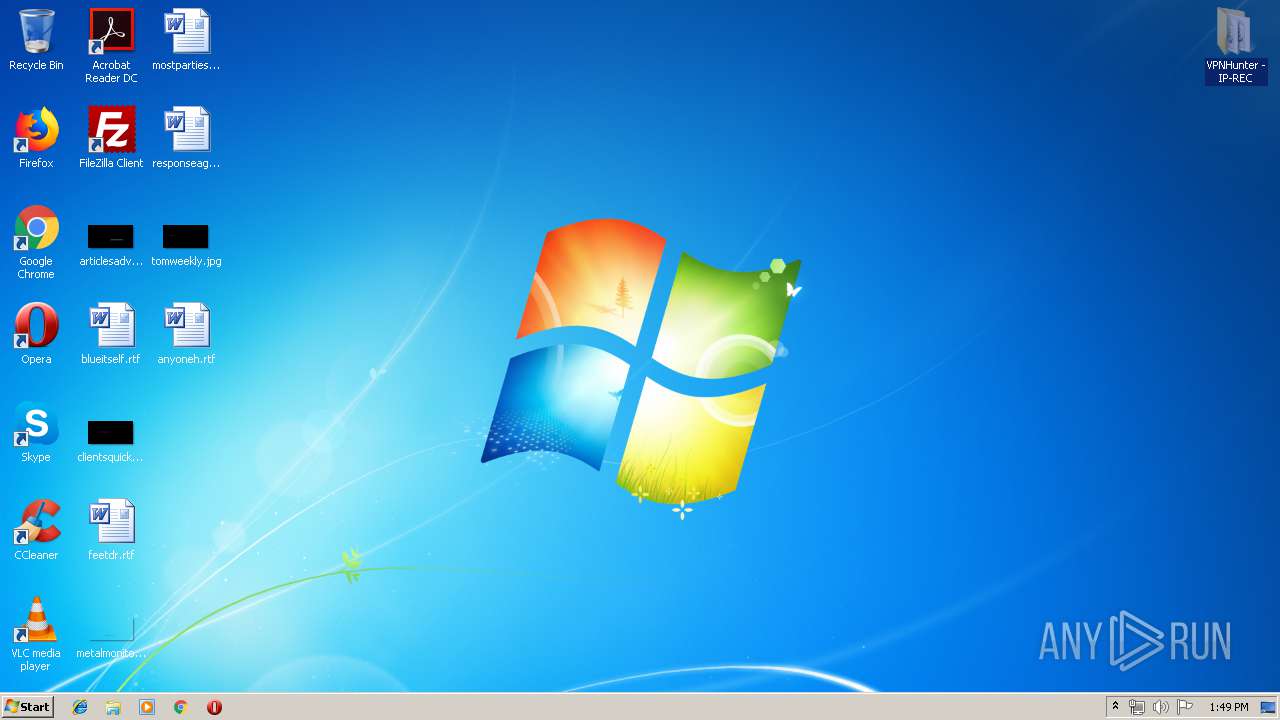
Manual execution by user
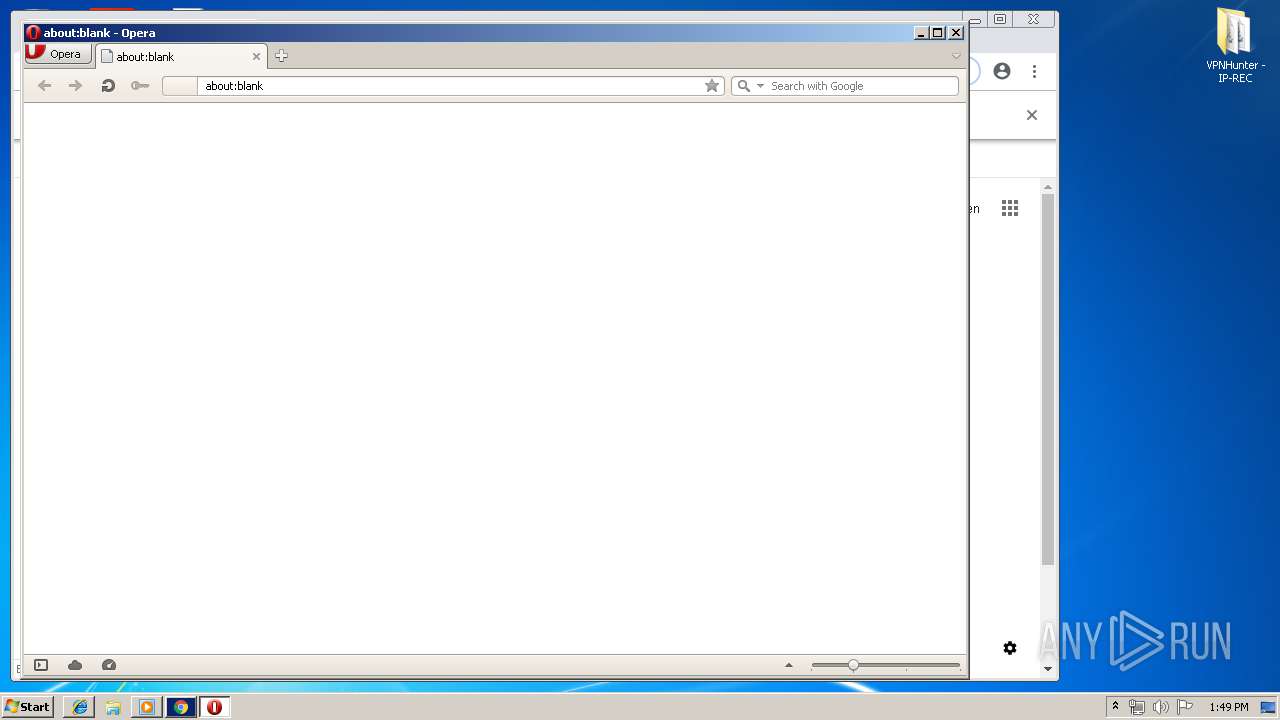
- VPNHunter.exe (PID: 584)
- explorer.exe (PID: 2892)
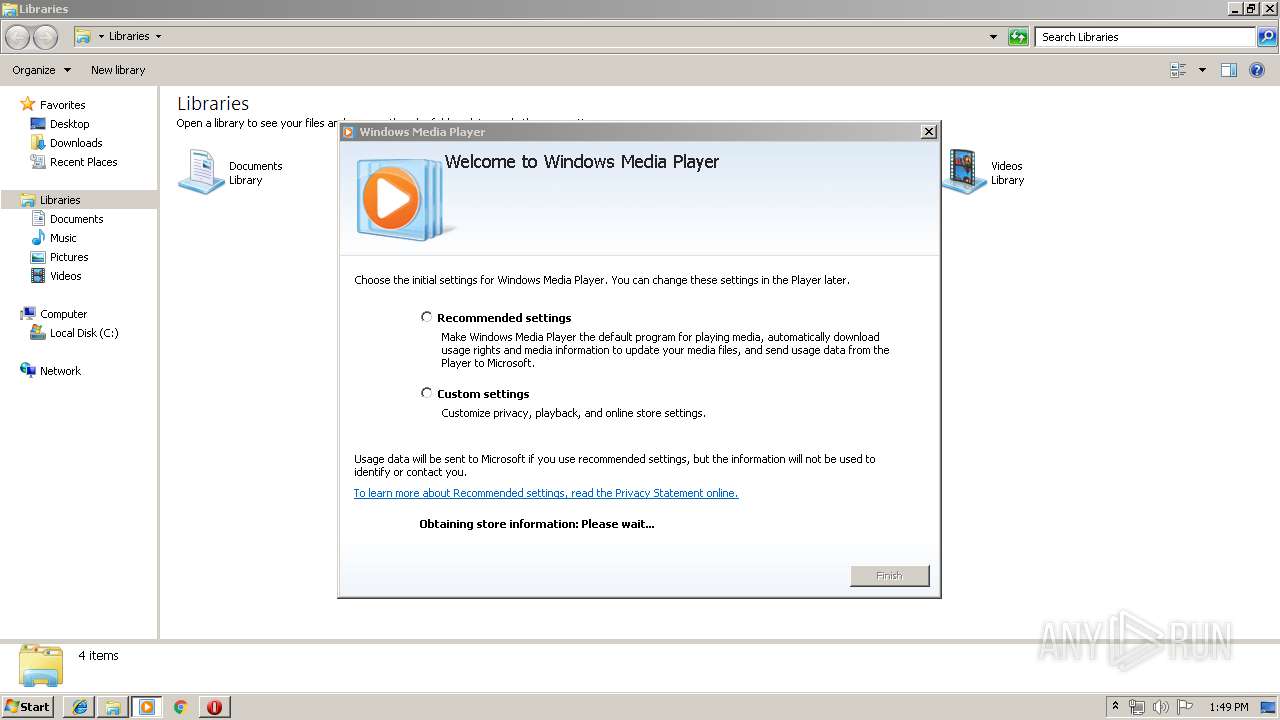
- wmplayer.exe (PID: 1336)
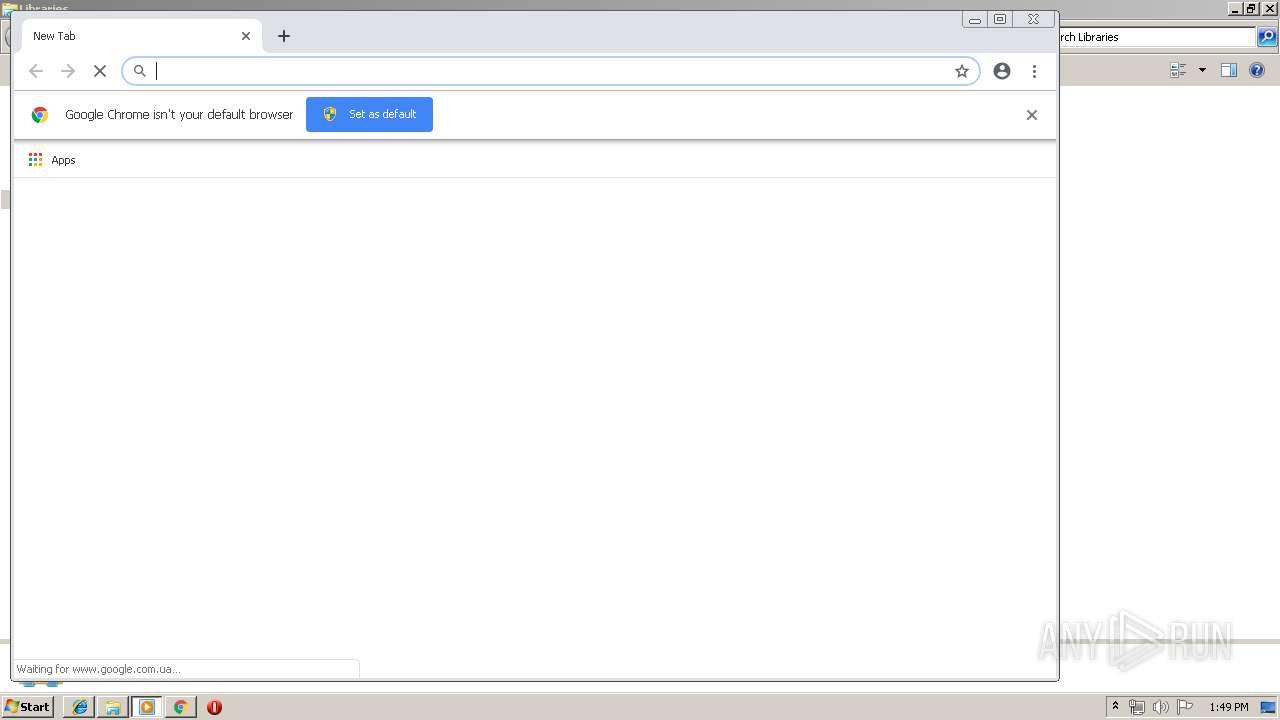
- chrome.exe (PID: 2308)
- opera.exe (PID: 756)
- iexplore.exe (PID: 4080)
Reads settings of System Certificates
- VPNHunter.exe (PID: 584)
Application launched itself
- iexplore.exe (PID: 4080)
- chrome.exe (PID: 2308)
Reads internet explorer settings
- iexplore.exe (PID: 1660)
Changes internet zones settings
- iexplore.exe (PID: 4080)
Reads Internet Cache Settings
- iexplore.exe (PID: 1660)
Creates files in the user directory
- iexplore.exe (PID: 1660)
- opera.exe (PID: 756)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 72186 |
|---|---|
| UncompressedSize: | 180224 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2017:09:14 10:02:26 |
| PackingMethod: | Normal |
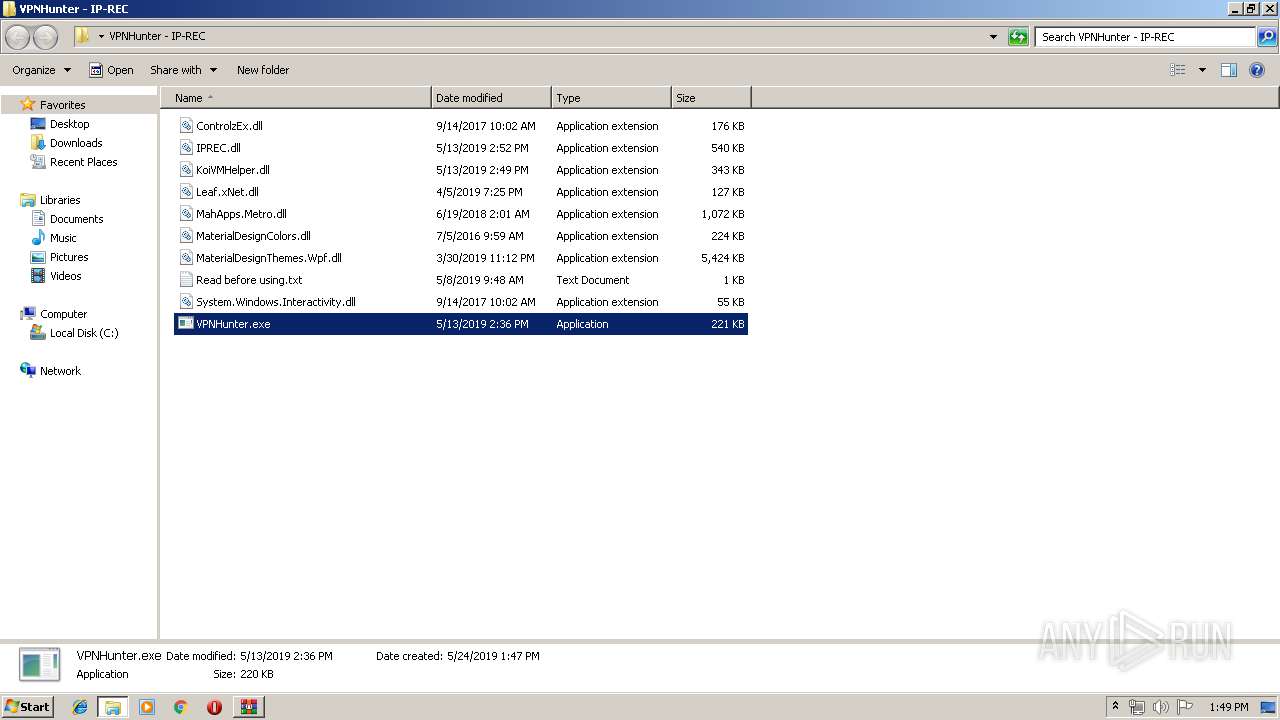
| ArchivedFileName: | VPNHunter - IP-REC\ControlzEx.dll |
Total processes
53
Monitored processes
17
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 584 | "C:\Users\admin\Desktop\VPNHunter - IP-REC\VPNHunter.exe" | C:\Users\admin\Desktop\VPNHunter - IP-REC\VPNHunter.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: VPNHunter Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 756 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,11485467604797651091,10243434183983554082,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=10611921019700951408 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10611921019700951408 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3860 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,11485467604797651091,10243434183983554082,131072 --enable-features=PasswordImport --service-pipe-token=115346305549322312 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=115346305549322312 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2092 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1336 | "C:\Program Files\Windows Media Player\wmplayer.exe" /prefetch:1 | C:\Program Files\Windows Media Player\wmplayer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1660 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:4080 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2088 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\3.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2144 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,11485467604797651091,10243434183983554082,131072 --enable-features=PasswordImport --service-pipe-token=13791041058057241287 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13791041058057241287 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2232 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=304 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
1 765
Read events
1 476
Write events
285
Delete events
4
Modification events
| (PID) Process: | (2088) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2088) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2088) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2088) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\3.rar | |||
| (PID) Process: | (2088) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2088) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2088) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2088) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3572) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3572) SearchProtocolHost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\notepad.exe,-469 |
Value: Text Document | |||
Executable files
4
Suspicious files
68
Text files
64
Unknown types
16
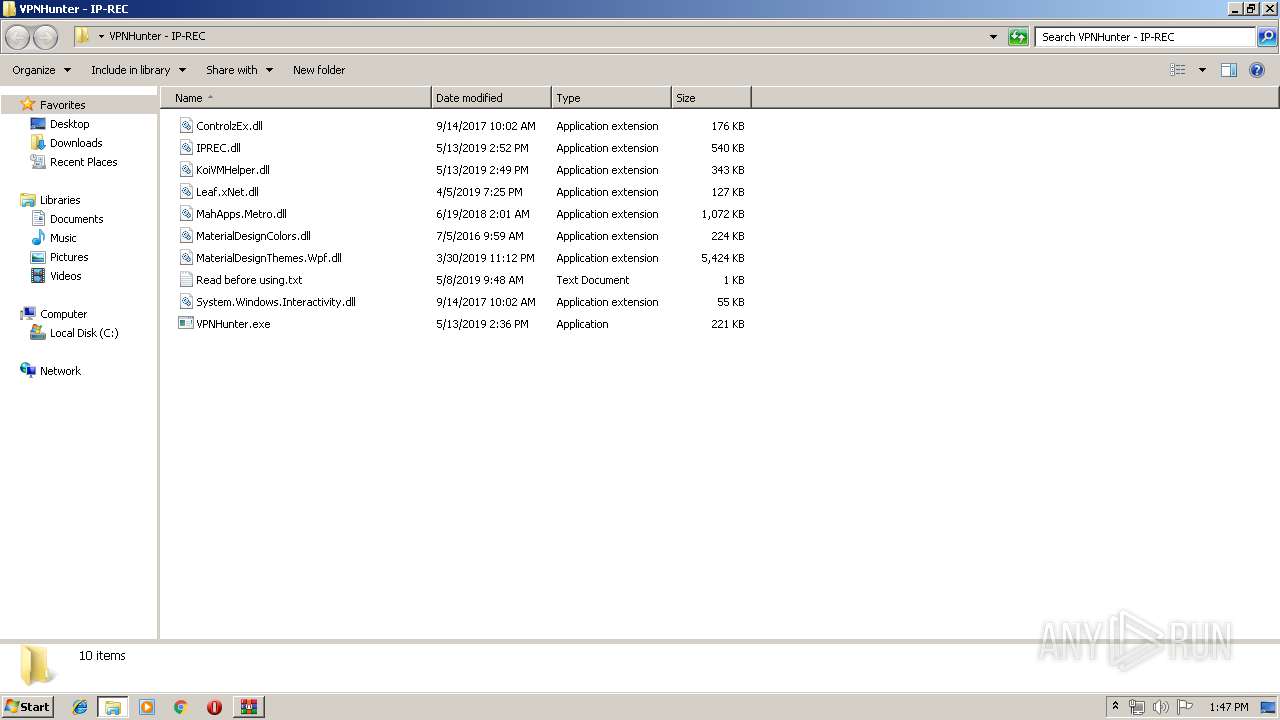
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2088 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2088.5559\VPNHunter - IP-REC\MahApps.Metro.dll | — | |
MD5:— | SHA256:— | |||
| 2088 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2088.5559\VPNHunter - IP-REC\MaterialDesignColors.dll | — | |
MD5:— | SHA256:— | |||
| 2088 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2088.5559\VPNHunter - IP-REC\MaterialDesignThemes.Wpf.dll | — | |
MD5:— | SHA256:— | |||
| 2088 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2088.5559\VPNHunter - IP-REC\Read before using.txt | — | |
MD5:— | SHA256:— | |||
| 2088 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2088.5559\VPNHunter - IP-REC\System.Windows.Interactivity.dll | — | |
MD5:— | SHA256:— | |||
| 2088 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2088.5559\VPNHunter - IP-REC\VPNHunter.exe | — | |
MD5:— | SHA256:— | |||
| 4080 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 4080 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2308 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
17
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2928 | setup_wm.exe | GET | 302 | 2.16.186.11:80 | http://redir.metaservices.microsoft.com/redir/allservices/?sv=5&version=12.0.7601.17514&locale=409&userlocale=409&geoid=f4&parch=x86&arch=x86 | unknown | — | — | whitelisted |
756 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 543 b | whitelisted |
4080 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2928 | setup_wm.exe | GET | 200 | 2.16.186.98:80 | http://onlinestores.metaservices.microsoft.com/serviceswitching/AllServices.aspx?sv=5&version=12.0.7601.17514&locale=409&userlocale=409&geoid=f4&parch=x86&arch=x86 | unknown | xml | 546 b | whitelisted |
2928 | setup_wm.exe | GET | 200 | 2.16.186.98:80 | http://onlinestores.metaservices.microsoft.com/bing/bing.xml | unknown | text | 523 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2308 | chrome.exe | 172.217.18.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
756 | opera.exe | 185.26.182.93:443 | certs.opera.com | Opera Software AS | — | whitelisted |
2308 | chrome.exe | 172.217.18.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
756 | opera.exe | 93.184.220.29:80 | crl4.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2308 | chrome.exe | 172.217.22.110:443 | apis.google.com | Google Inc. | US | whitelisted |
2308 | chrome.exe | 172.217.23.163:443 | www.google.be | Google Inc. | US | whitelisted |
2308 | chrome.exe | 216.58.208.36:443 | www.google.com | Google Inc. | US | whitelisted |
2308 | chrome.exe | 172.217.21.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2308 | chrome.exe | 172.217.16.142:443 | clients1.google.com | Google Inc. | US | whitelisted |
2308 | chrome.exe | 172.217.16.138:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
i.imgur.com |
| malicious |
www.bing.com |
| whitelisted |
redir.metaservices.microsoft.com |
| whitelisted |
onlinestores.metaservices.microsoft.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |