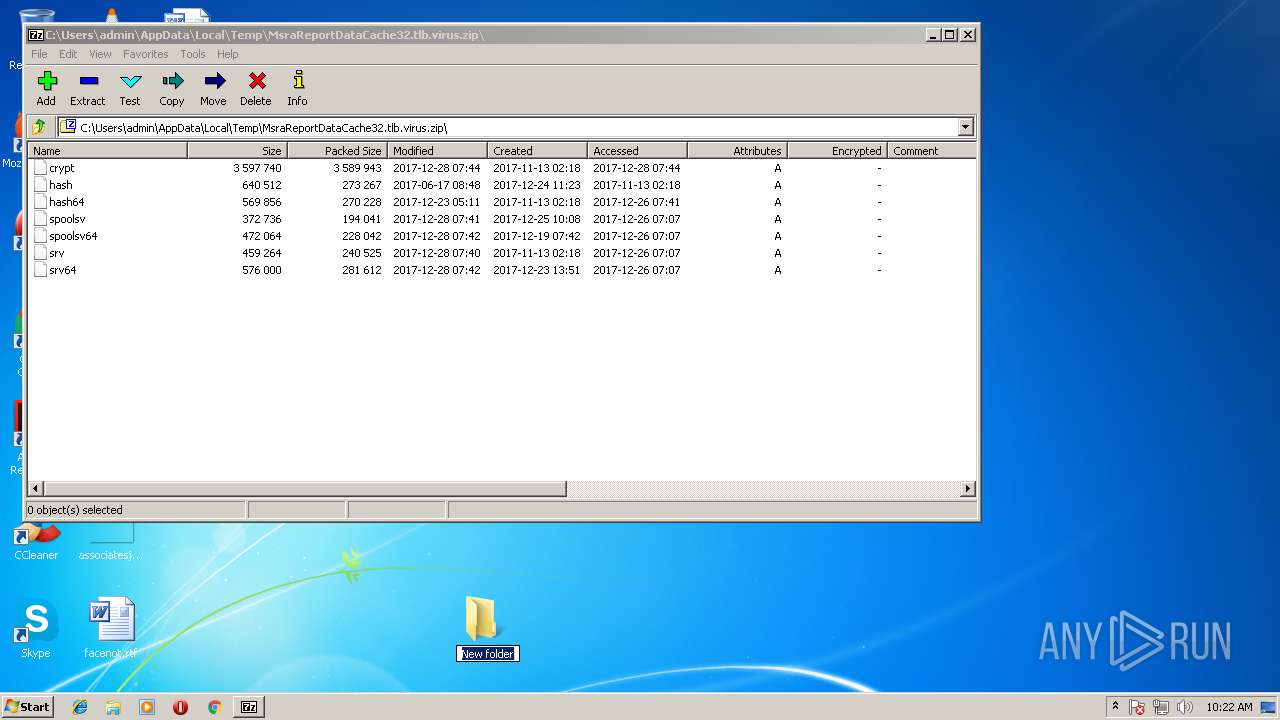
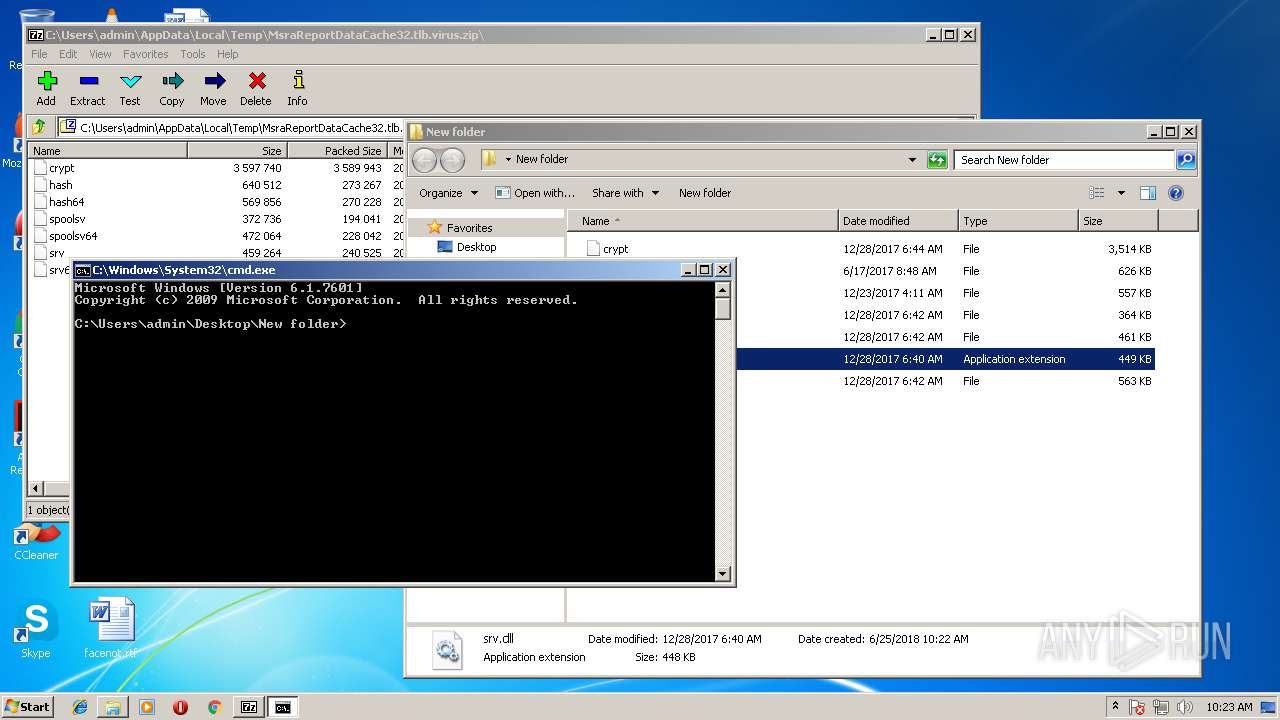
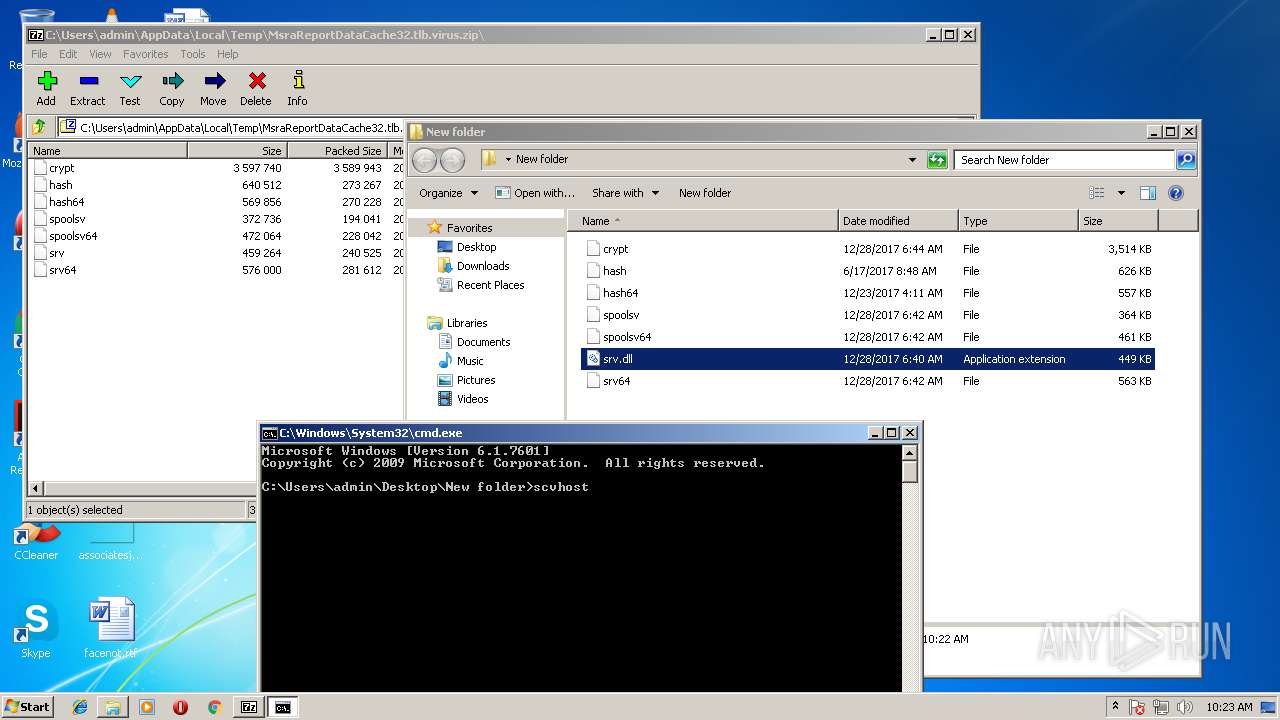
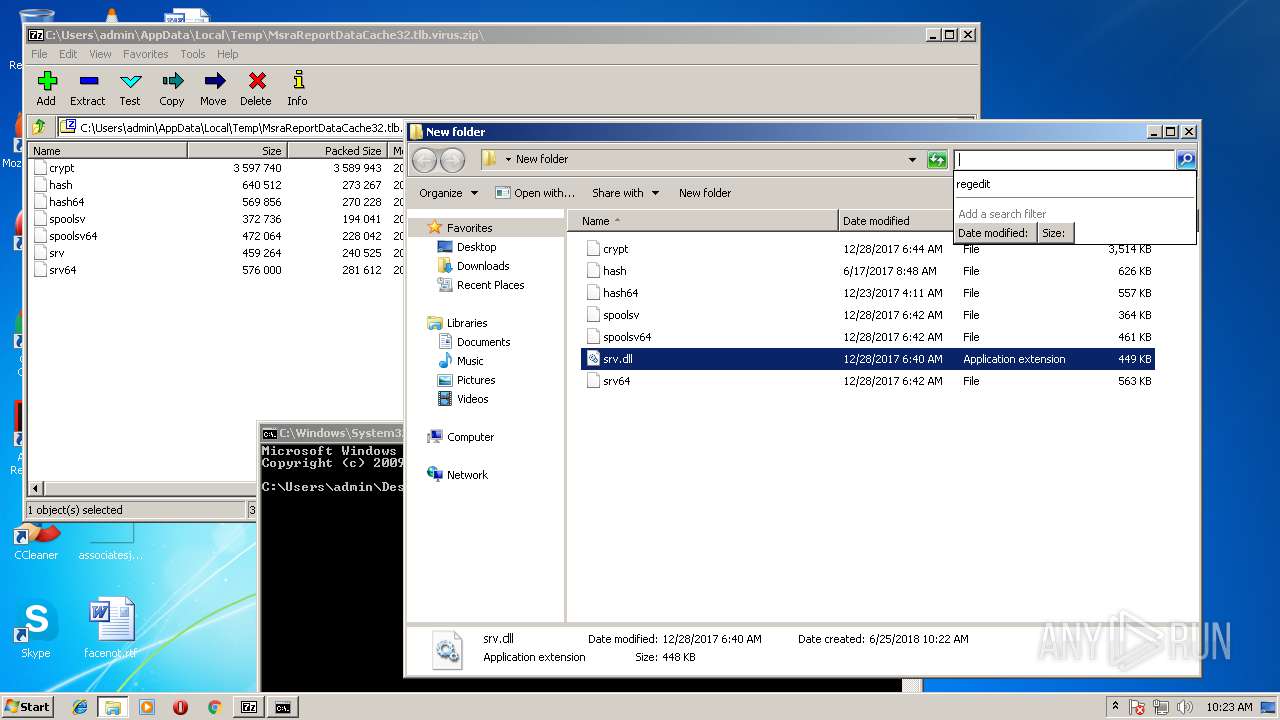
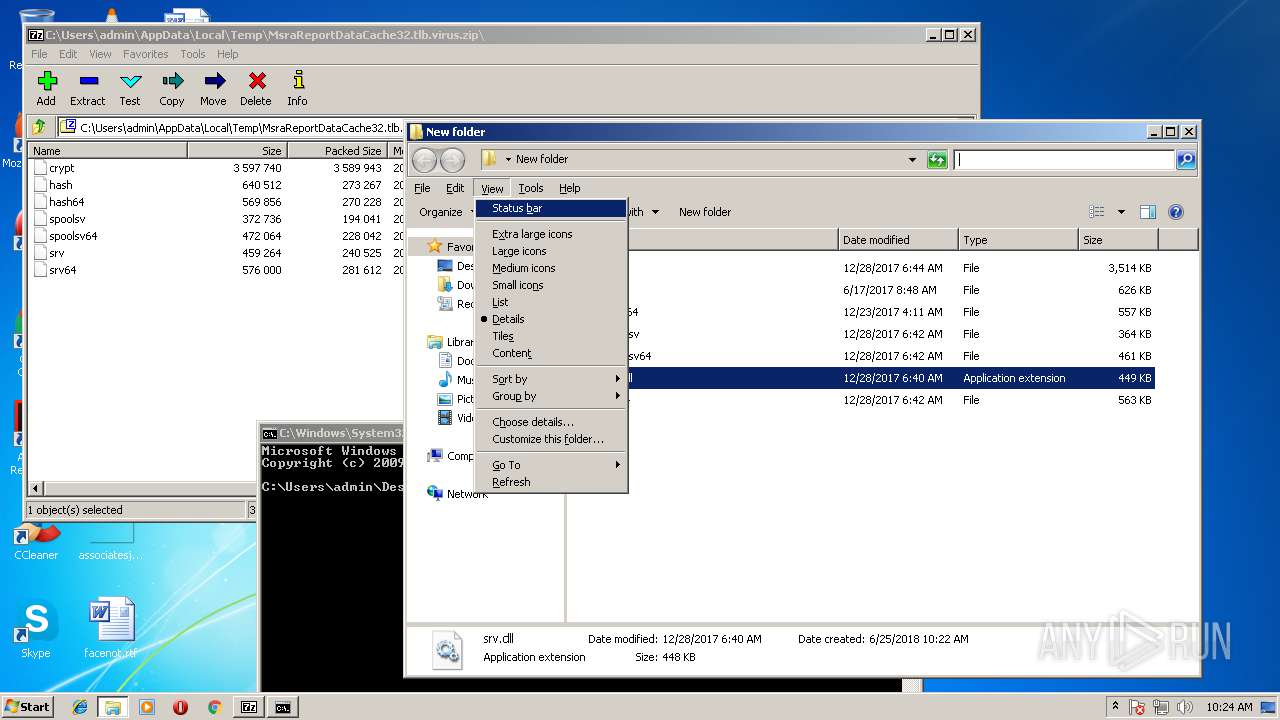
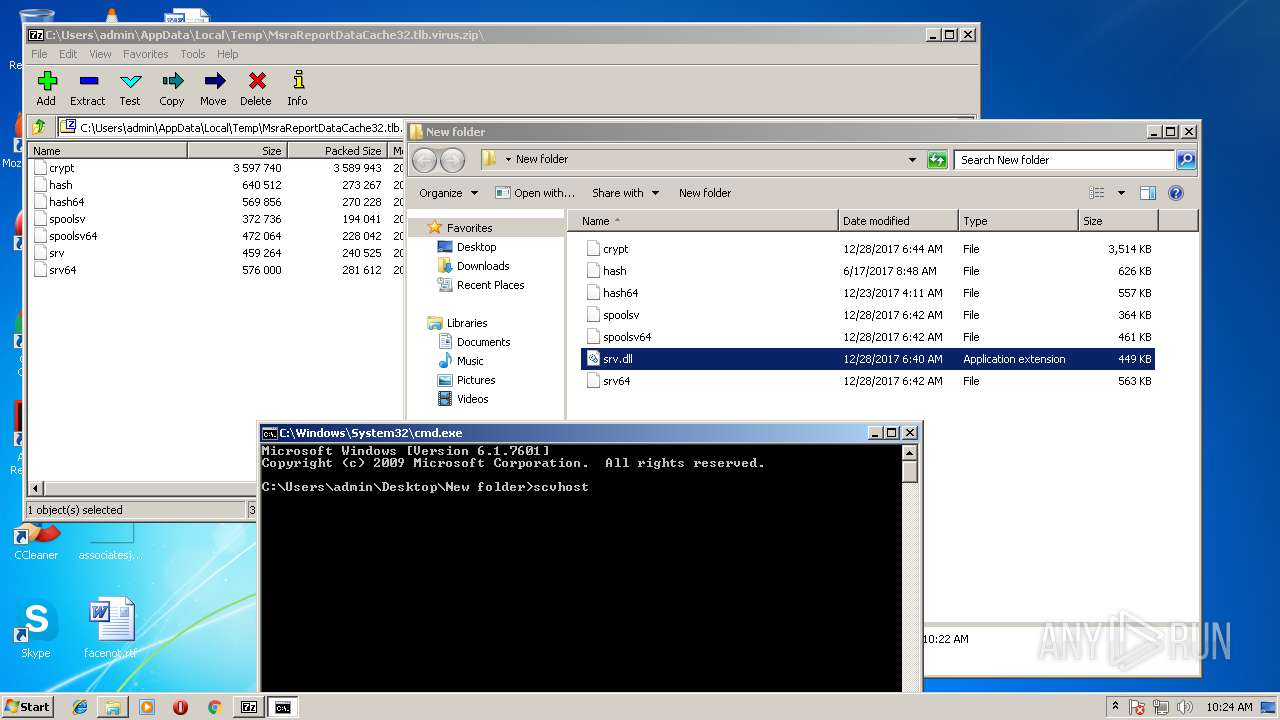
| File name: | MsraReportDataCache32.tlb.virus |
| Full analysis: | https://app.any.run/tasks/127bcb3d-b998-43b5-a911-0d6582cad624 |
| Verdict: | Malicious activity |
| Analysis date: | June 25, 2018, 09:21:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 8524909B6BBD4BFE39F30983784B0B24 |
| SHA1: | 7943C0E5A2648B1AEC60986E6000E1BE9EC5F41C |
| SHA256: | F935A462FAC0DFA20AD0144CEA2CA12CBC50FEFCEF5FED0E16C83F7FB97ED490 |
| SSDEEP: | 98304:1qaZN/0ofmS7dOHxpZMbpimi9cNVchRXOD68iInrTgvI8adtUst/k5HdL:kaf0oeEgHjZHmi9ck82IIvUdtUTN |
MALICIOUS
Loads dropped or rewritten executable
- explorer.exe (PID: 1676)
- SearchProtocolHost.exe (PID: 3132)
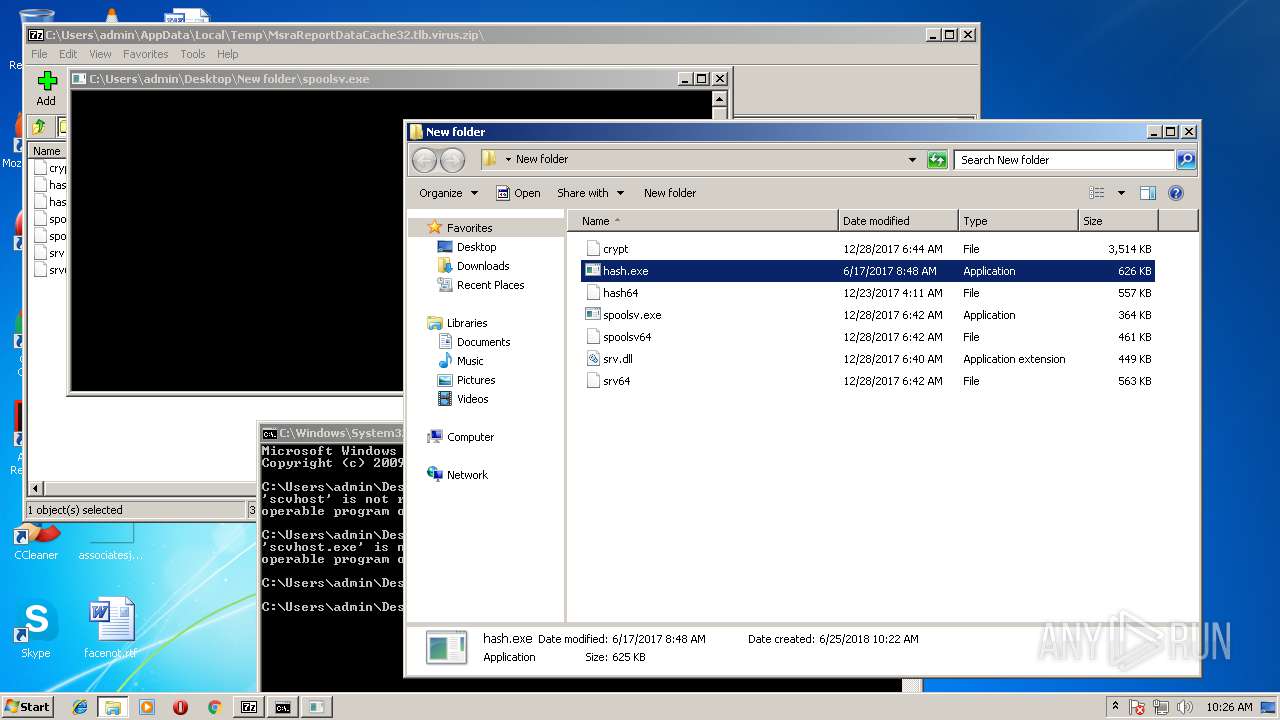
Application was dropped or rewritten from another process
- spoolsv.exe (PID: 3396)
- hash.exe (PID: 2084)
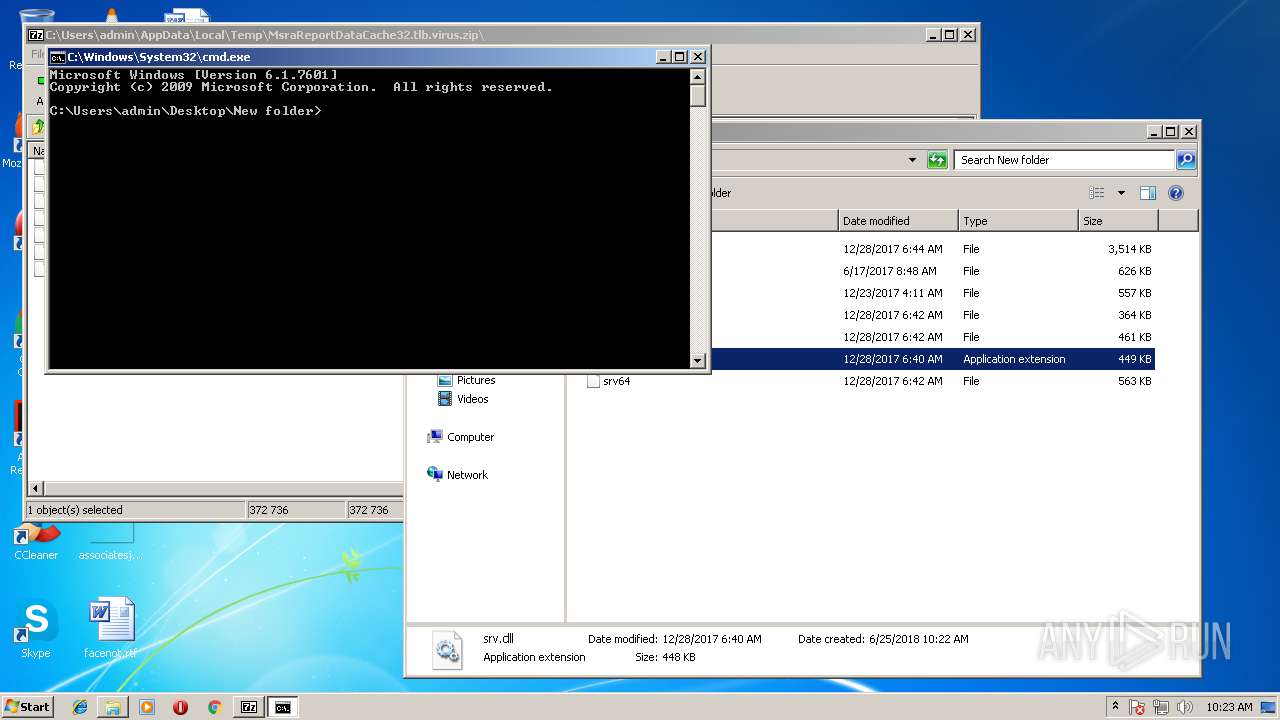
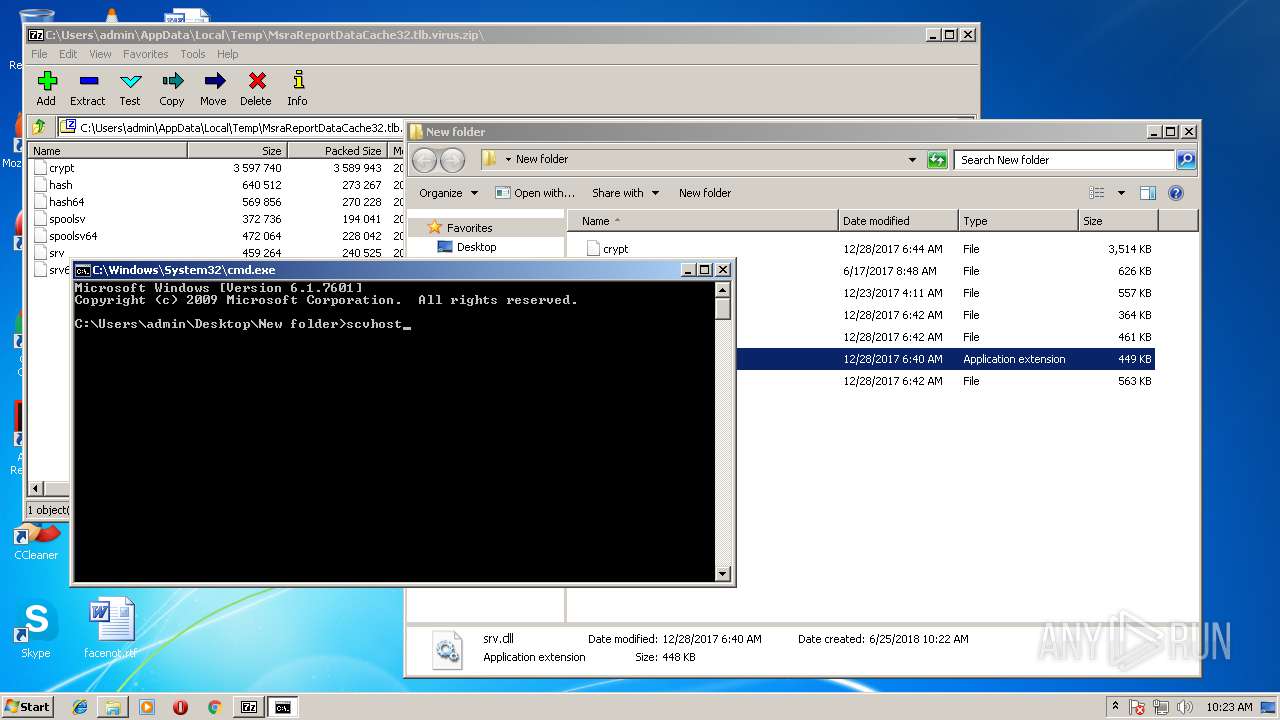
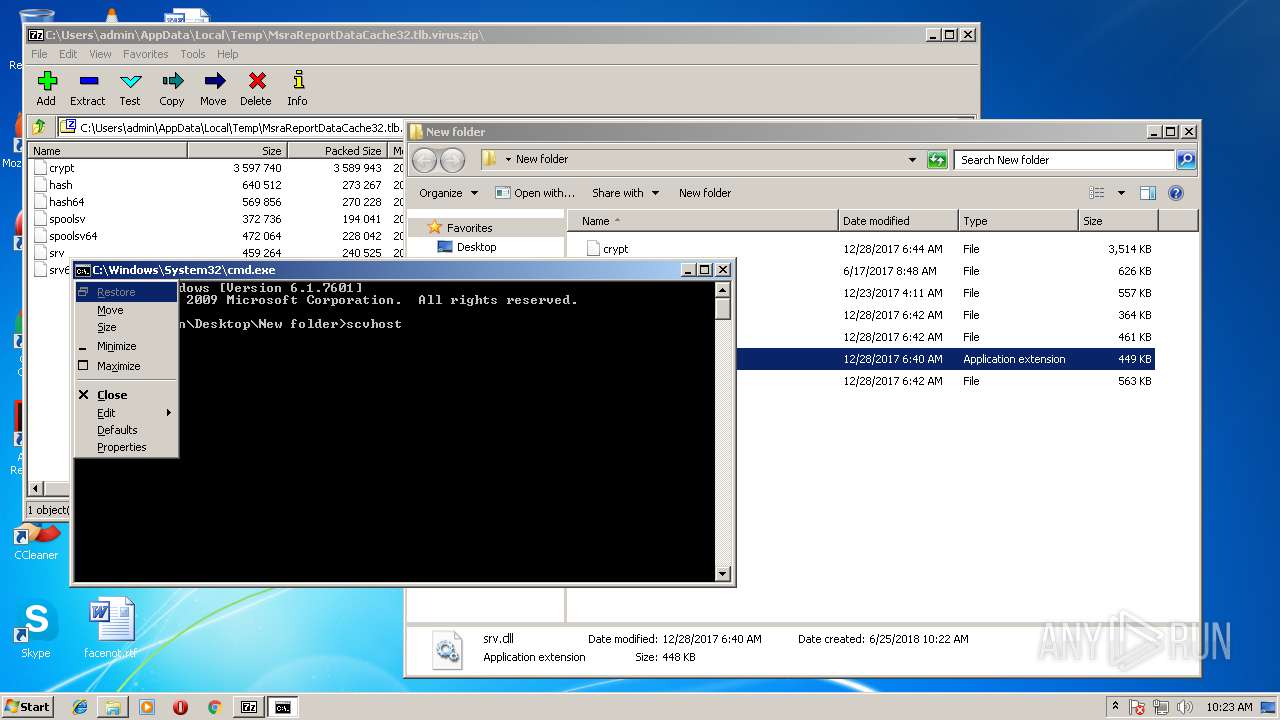
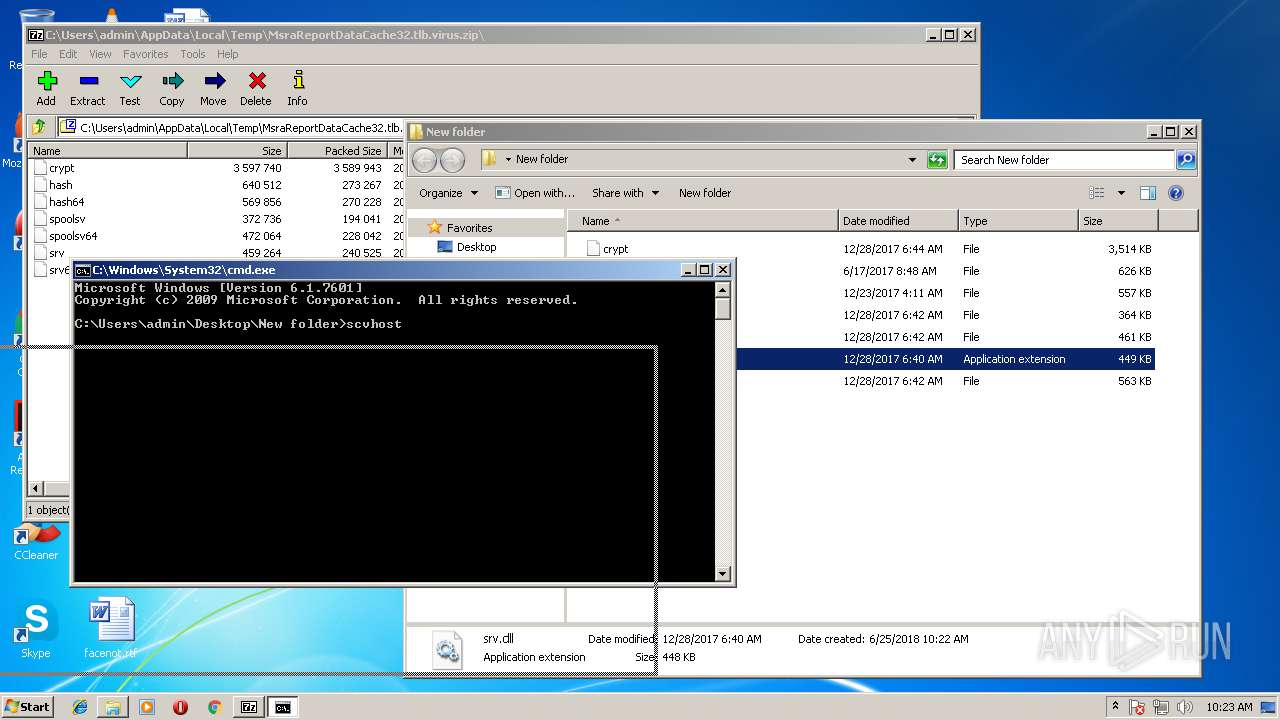
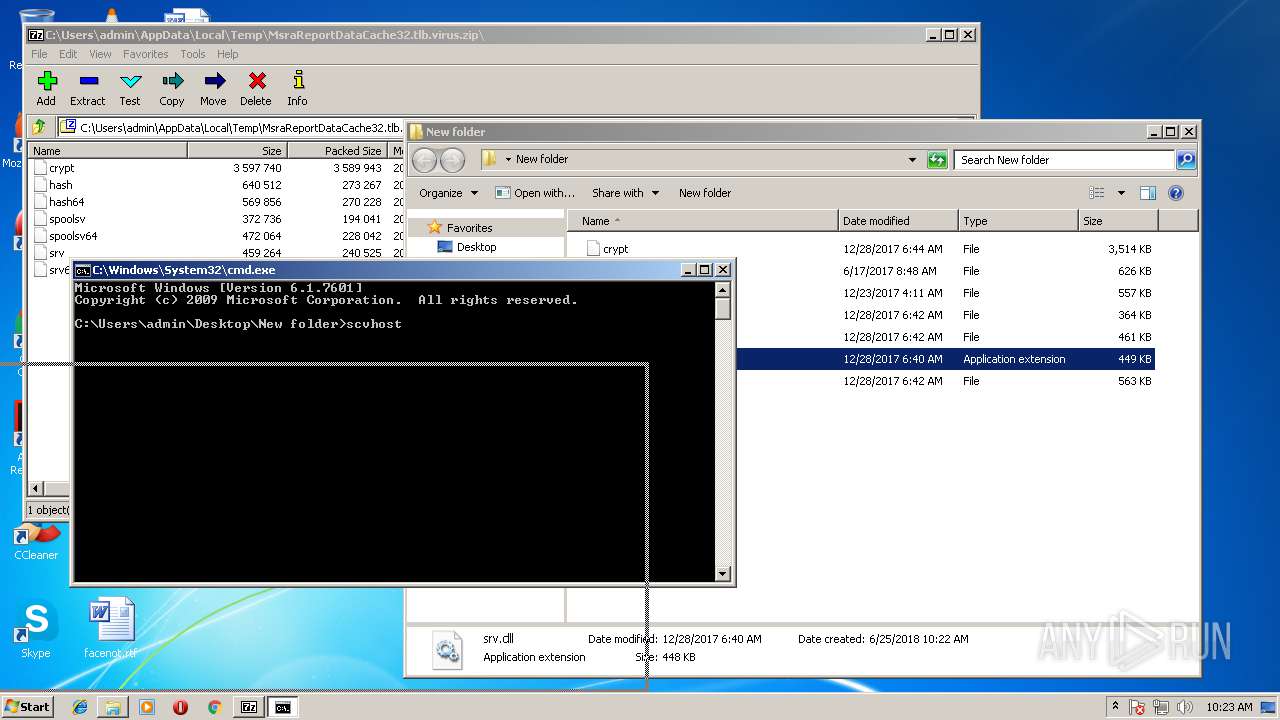
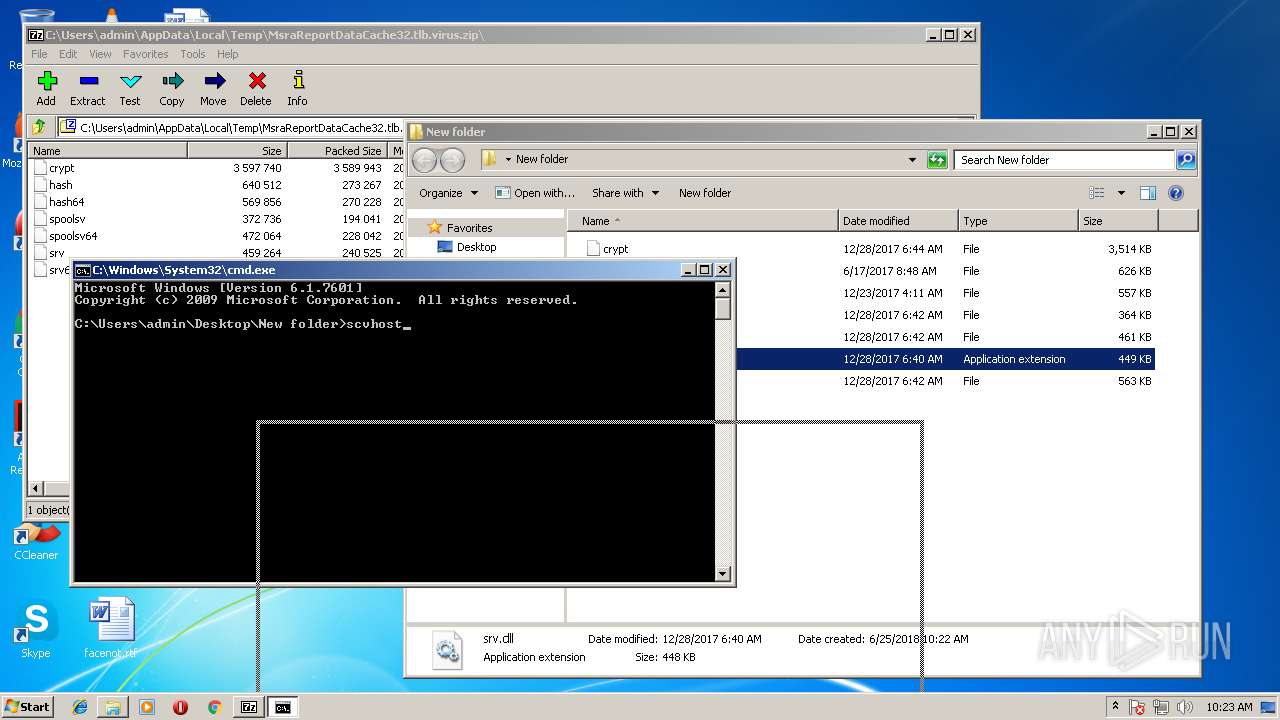
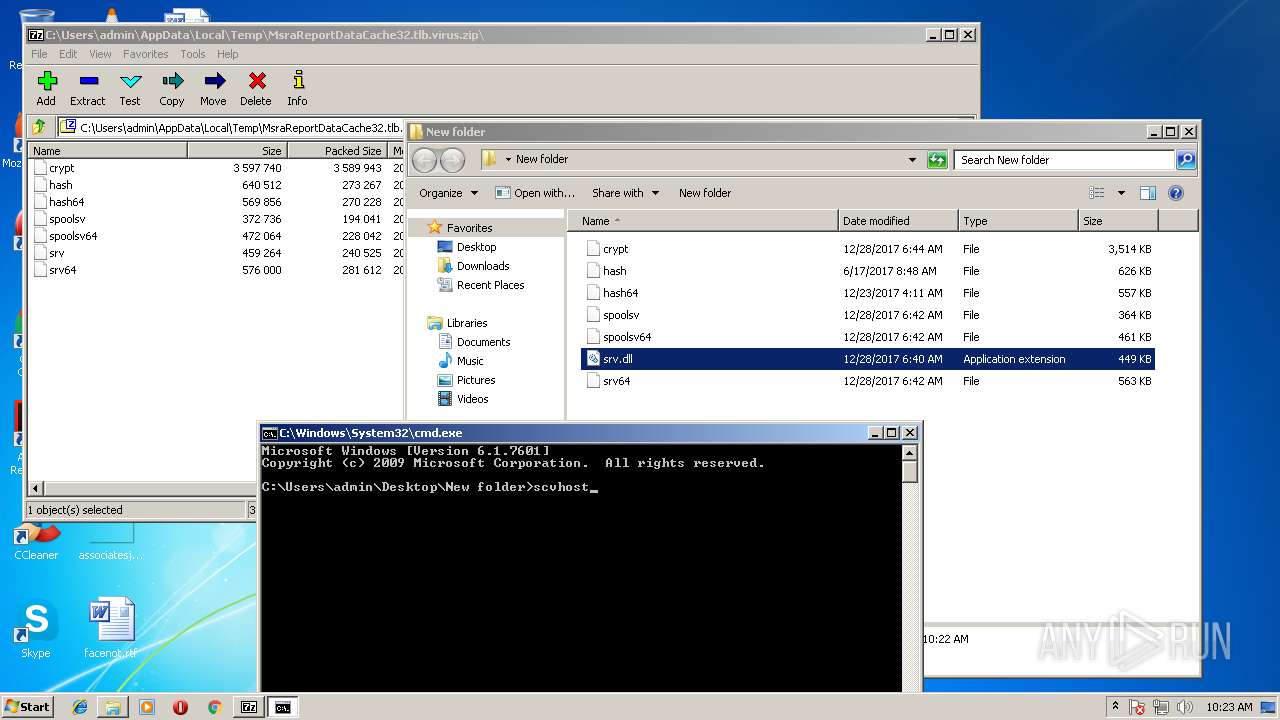
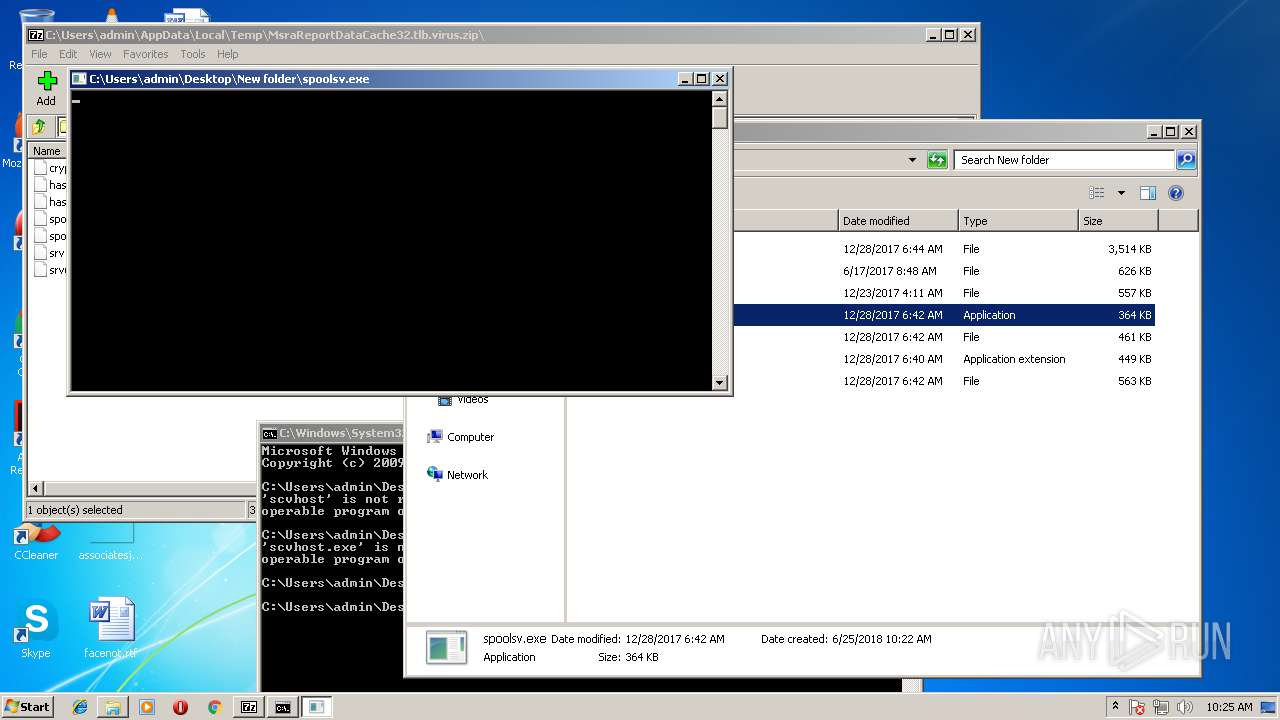
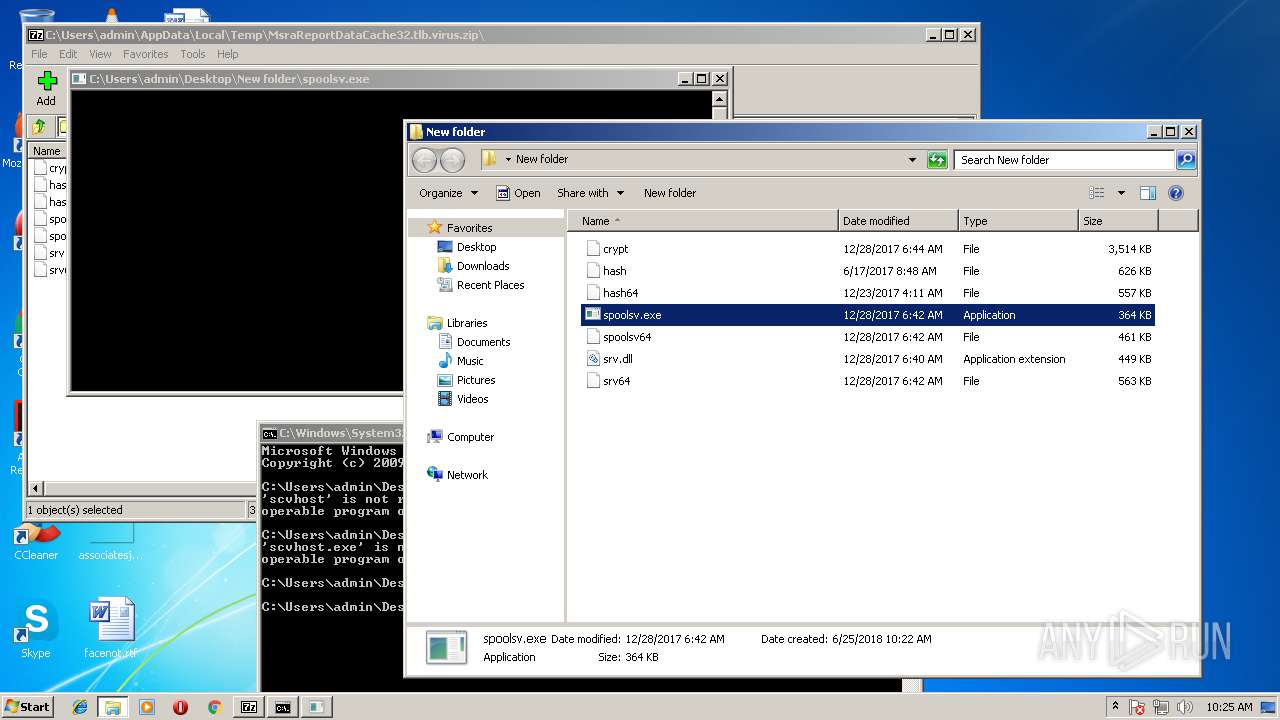
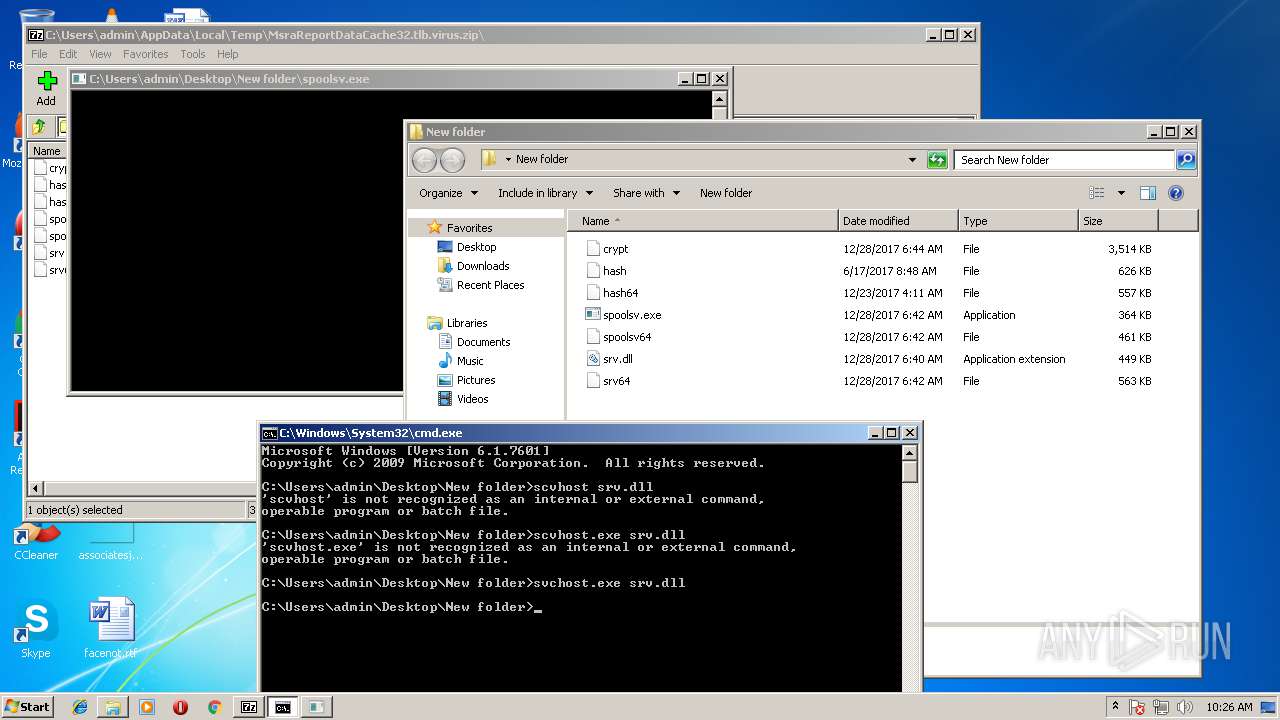
Uses SVCHOST.EXE for hidden code execution
- cmd.exe (PID: 1388)
Runs app for hidden code execution
- explorer.exe (PID: 1676)
SUSPICIOUS
Executable content was dropped or overwritten
- explorer.exe (PID: 1676)
Starts CMD.EXE for commands execution
- explorer.exe (PID: 1676)
Connects to unusual port
- spoolsv.exe (PID: 3396)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
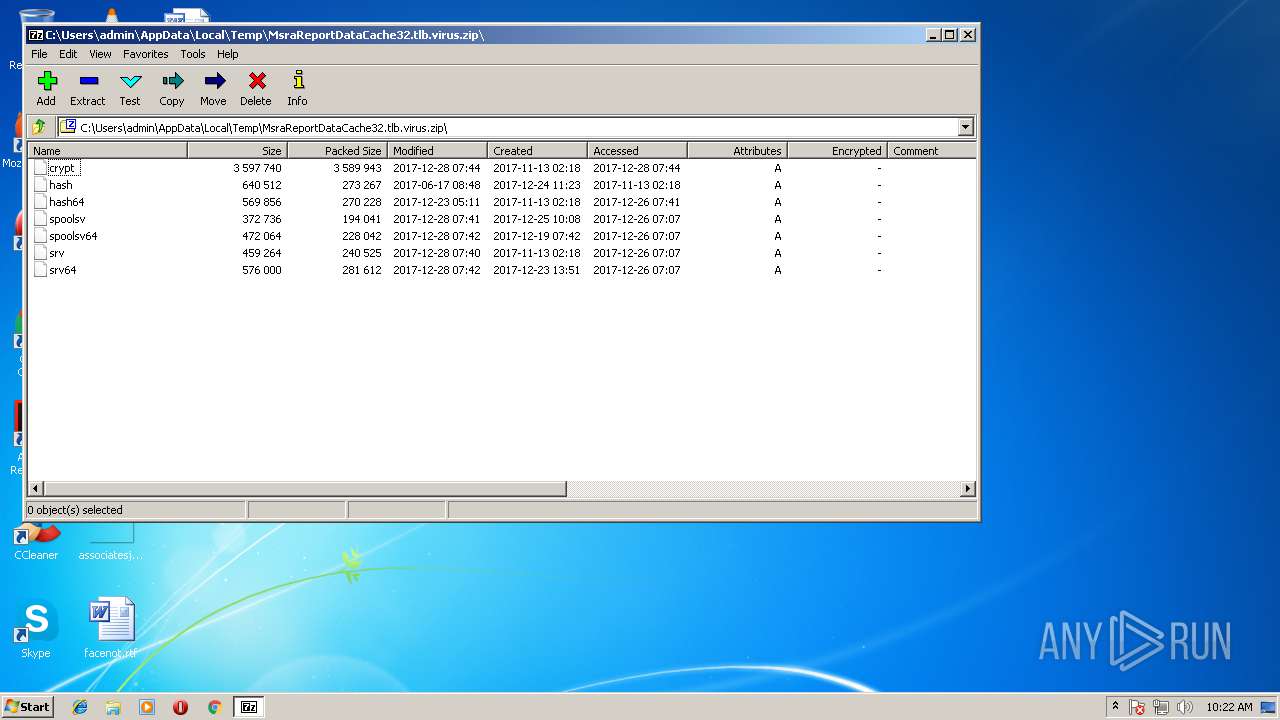
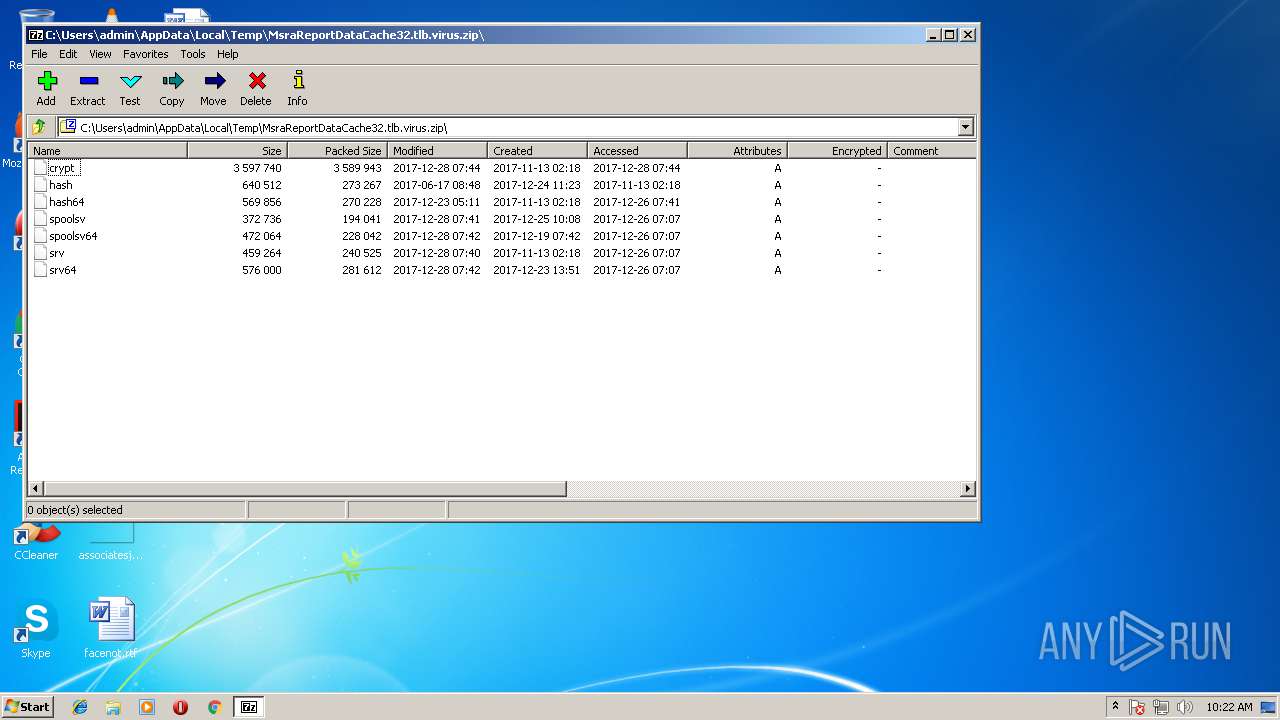
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2017:12:28 14:44:06 |
| ZipCRC: | 0xa2b4e540 |
| ZipCompressedSize: | 3589943 |
| ZipUncompressedSize: | 3597740 |
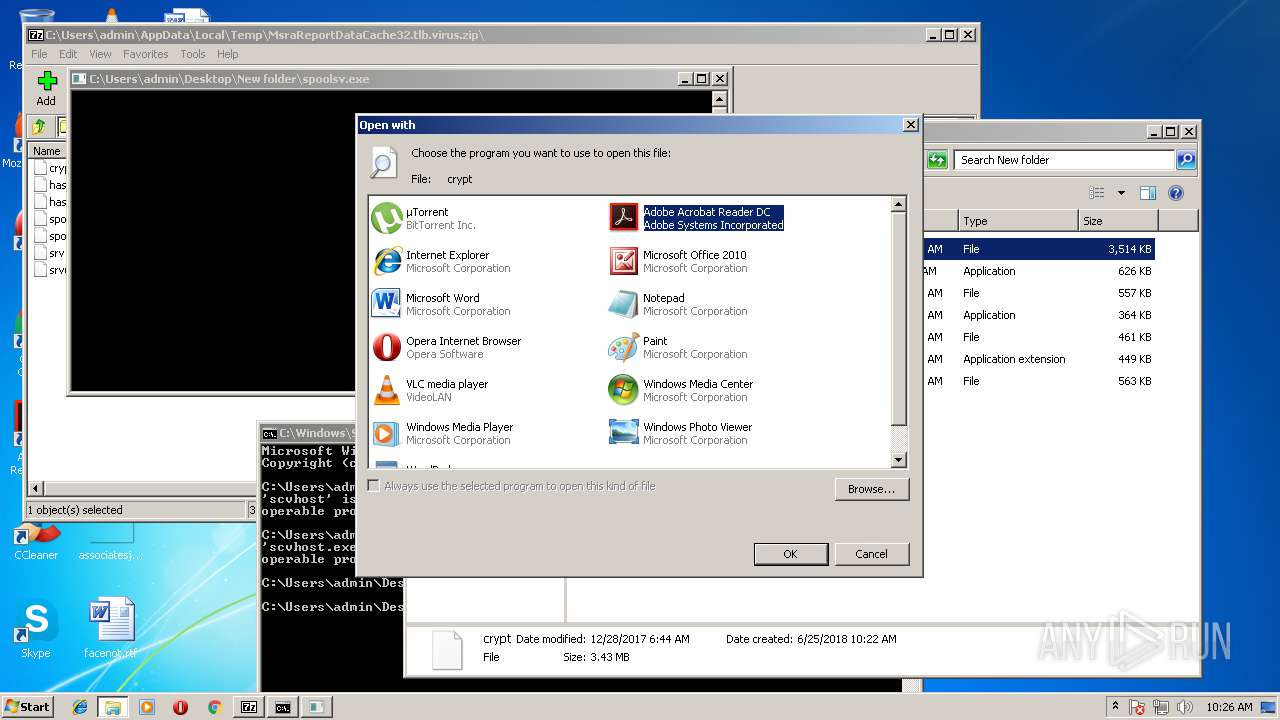
| ZipFileName: | crypt |
Total processes
48
Monitored processes
8
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
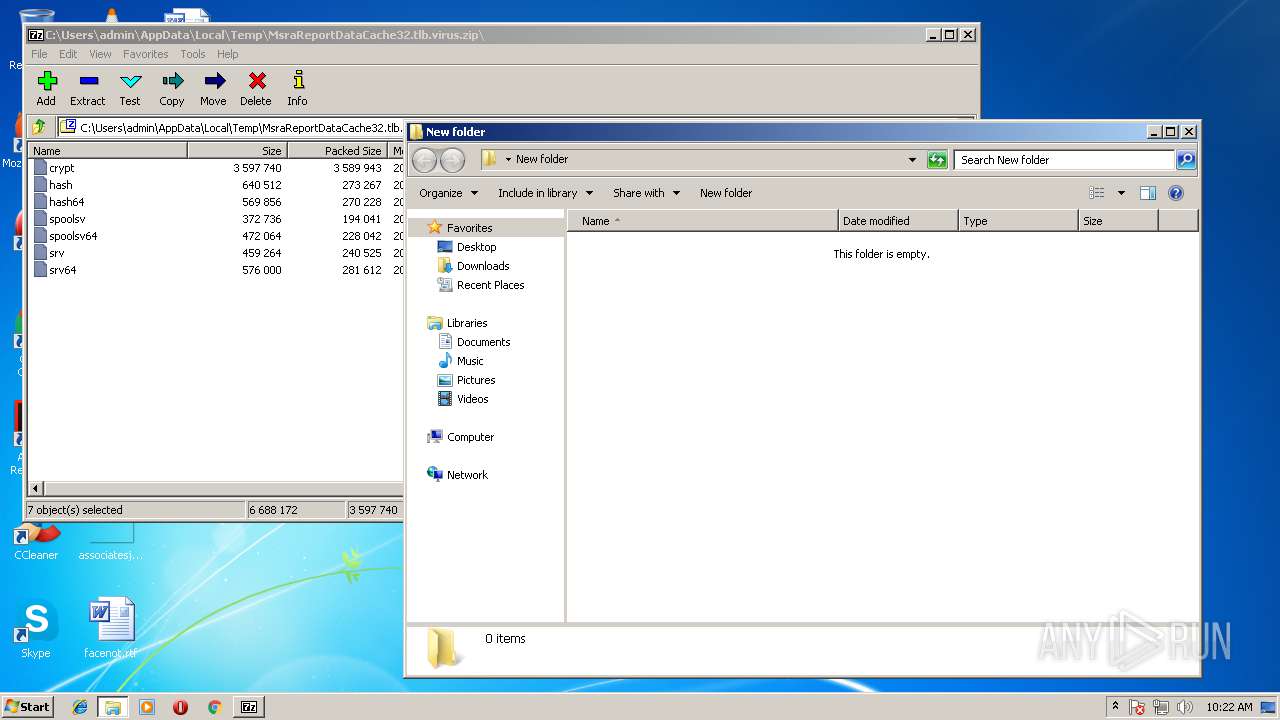
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
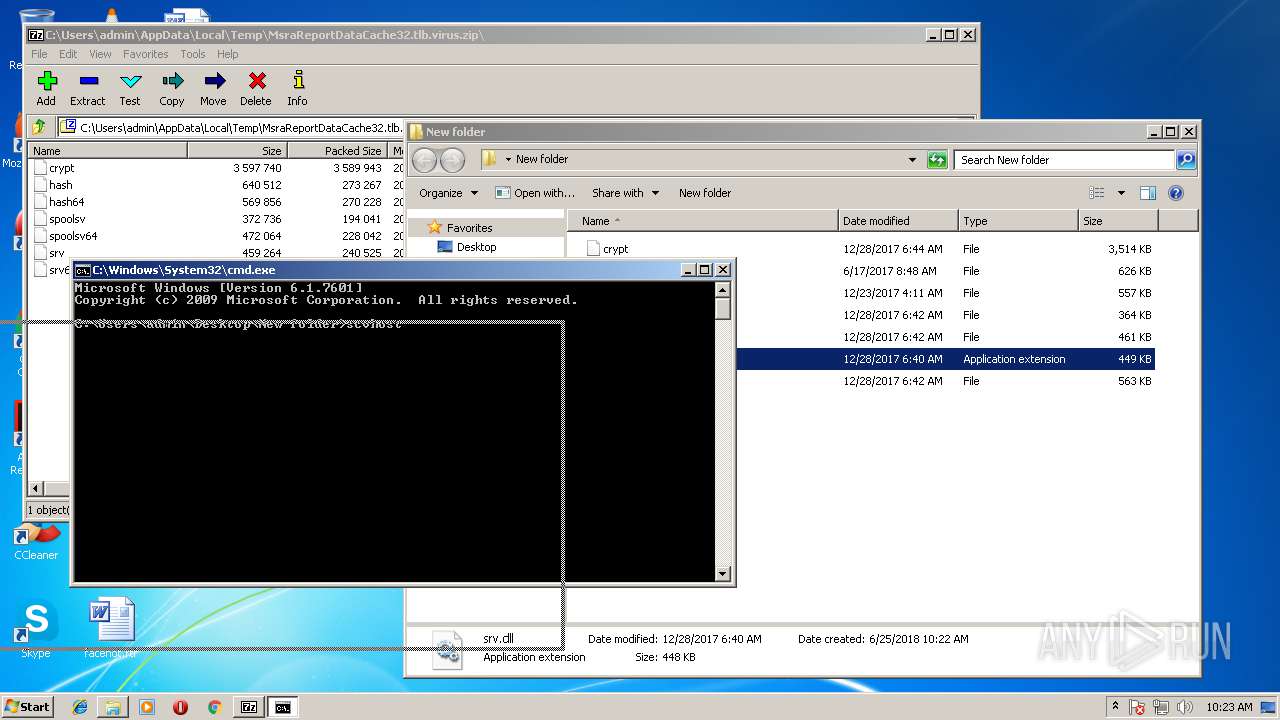
| 716 | "C:\Program Files\7-Zip\7zFM.exe" "C:\Users\admin\AppData\Local\Temp\MsraReportDataCache32.tlb.virus.zip" | C:\Program Files\7-Zip\7zFM.exe | — | explorer.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip File Manager Exit code: 0 Version: 16.04 Modules
| |||||||||||||||
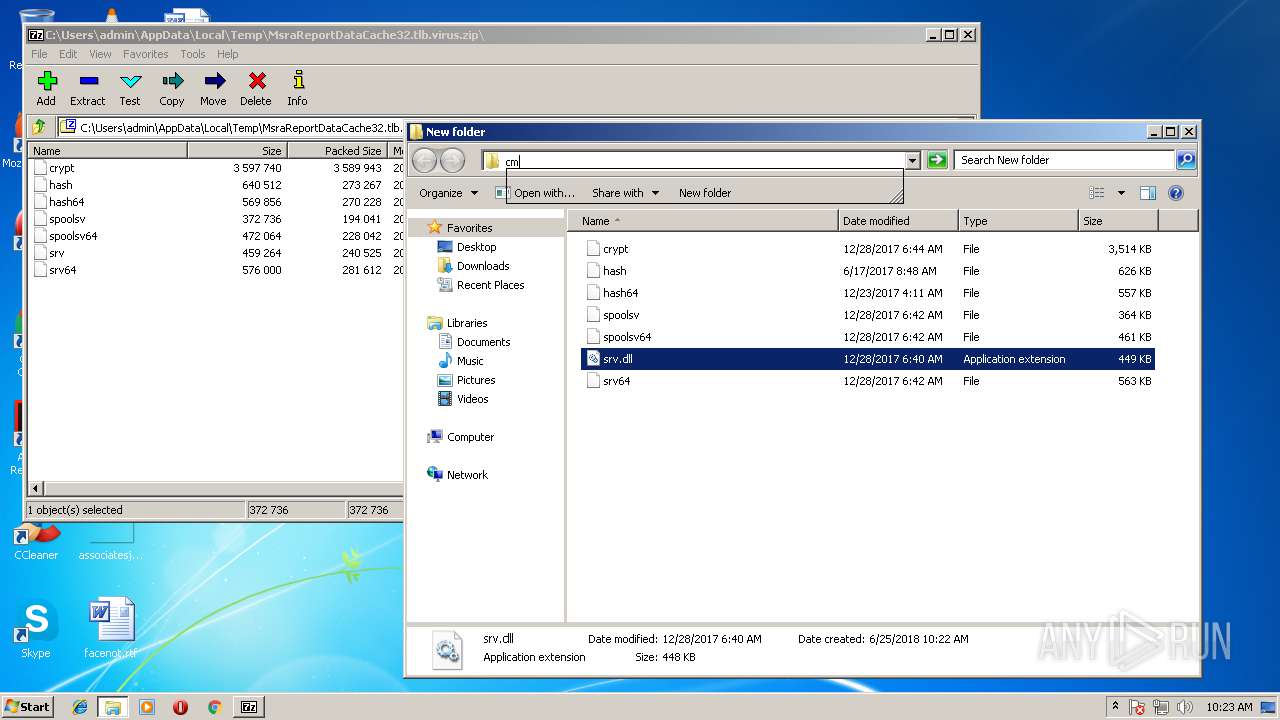
| 1388 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1676 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2008 | svchost.exe srv.dll | C:\Windows\system32\svchost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2084 | "C:\Users\admin\Desktop\New folder\hash.exe" | C:\Users\admin\Desktop\New folder\hash.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2284 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\New folder\crypt | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3132 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe3_ Global\UsGthrCtrlFltPipeMssGthrPipe3 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3396 | "C:\Users\admin\Desktop\New folder\spoolsv.exe" | C:\Users\admin\Desktop\New folder\spoolsv.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
5 368
Read events
5 175
Write events
192
Delete events
1
Modification events
| (PID) Process: | (1676) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Action Center\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 23004100430042006C006F00620000000000000000000000010000000100000001000000 | |||
| (PID) Process: | (1676) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | {7P5N40RS-N0SO-4OSP-874N-P0S2R0O9SN8R}\7-Mvc\7mSZ.rkr |
Value: 000000000000000000000000022C0000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (1676) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000000E000000130000001E4F0D000400000001000000190801004D006900630072006F0073006F00660074002E0049006E007400650072006E00650074004500780070006C006F007200650072002E00440065006600610075006C007400000000000000000000000000230000000000000000000000000000000000000000000000000000002A0C580260E9180213005802E20B58026FA9A5750600000005000000E20B580230B5580204E91802E8AAA5757B030119F8E8180200EB180230B55802000000000500000001000000DCE918026229A8757B03011930B5580206000000C80C58020000000000EB180208EB180210A65802CC0A580210000000000000000000000000000000000000000600000000000000230000006C61746E64666C740000000040000000AC54A57500000000C054A5757B03011930B55802000000000000000000000000E00B580230B55802ACE9183138EE18023F0400009021230038EA18021100000010471E0008471E00000000003F040000D6160E747B03011928EA0000150DB2ADD8E918028291E67528EA1802448B0000010DB2ADECE91802B69CE675488B25004C06000004EA1802B886250010EA1802789CE6753691E67540B018761100000010471E0008471E00D88625007CEA0000C10EB2AD2CEA18028291E6757CEA180230EA18022795E67500000000448B250058EA1802CD94E675448B250004EB1802B8862500E194E67500000000B886250004EB180260EA180200000000070000003FE402007B00440036003500320033003100420030002D0042003200460031002D0034003800350037002D0041003400430045002D004100380045003700430036004500410037004400320037007D005C007400610073006B006D00670072002E0065007800650000005802EC0A5802D0E818025869A67500000000D0075802F0E818020B8CA5750100000000000000537AA575560401020020000000000000010000003CE918023617DB7556040102100858020500000000000000FFFFFFFFD00758020000000038E9180264E9180200000000000000000000000090E9180218EC2300000000004091A4750900800188E918023559DB7556040102D09028000500000070E91802506AA6751CC0AA7501000000EF7AA575560401021D0000000020000088E918026359DB7590E918020000000000000000560401024066A07501000000F4E91802A13673750000000000000000C80B2300F4E91802B8367375E09276750000000000001B00D090280000000000F0E91802070014006AC2C1C10000000000000000CF6771758890280001000000C8902800FCE91802E82C0677C80B2300CF67717518EC1802C89028001100000010471E0008471E00000000007CEA0000C10EB2AD2CEA18028291E6757CEA180230EA18022795E67500000000448B250058EA1802CD94E675448B250004EB1802B8862500E194E67500000000B886250004EB180260EA180200000000070000003FE402007B00440036003500320033003100420030002D0042003200460031002D0034003800350037002D0041003400430045002D004100380045003700430036004500410037004400320037007D005C007400610073006B006D00670072002E0065007800650000005802EC0A5802D0E818025869A67500000000D0075802F0E818020B8CA5750100000000000000537AA575560401020020000000000000010000003CE918023617DB7556040102100858020500000000000000FFFFFFFFD00758020000000038E9180264E9180200000000000000000000000090E9180218EC2300000000004091A4750900800188E918023559DB7556040102D09028000500000070E91802506AA6751CC0AA7501000000EF7AA575560401021D0000000020000088E918026359DB7590E918020000000000000000560401024066A07501000000F4E91802A13673750000000000000000C80B2300F4E91802B8367375E09276750000000000001B00D090280000000000F0E91802070014006AC2C1C10000000000000000CF6771758890280001000000C8902800FCE91802E82C0677C80B2300CF67717518EC1802C89028001100000010471E0008471E00000000007CEA0000C10EB2AD2CEA18028291E6757CEA180230EA18022795E67500000000448B250058EA1802CD94E675448B250004EB1802B8862500E194E67500000000B886250004EB180260EA1802 | |||
| (PID) Process: | (1676) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\93\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1676) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\93\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\display.dll,-4 |
Value: S&creen resolution | |||
| (PID) Process: | (1676) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\93\52C64B7E |
| Operation: | write | Name: | @C:\Program Files\Common Files\System\wab32res.dll,-4602 |
Value: Contact file | |||
| (PID) Process: | (1676) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\93\52C64B7E |
| Operation: | write | Name: | @C:\Program Files\Windows Sidebar\sidebar.exe,-11100 |
Value: &Gadgets | |||
| (PID) Process: | (1676) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\93\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\themecpl.dll,-10 |
Value: Pe&rsonalize | |||
| (PID) Process: | (1676) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\93\52C64B7E |
| Operation: | write | Name: | @"C:\Program Files\Windows Journal\Journal.exe",-3072 |
Value: Journal Document | |||
| (PID) Process: | (1676) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Discardable\PostSetup\ShellNew |
| Operation: | write | Name: | Classes |
Value: .bmp | |||
Executable files
9
Suspicious files
1
Text files
0
Unknown types
0
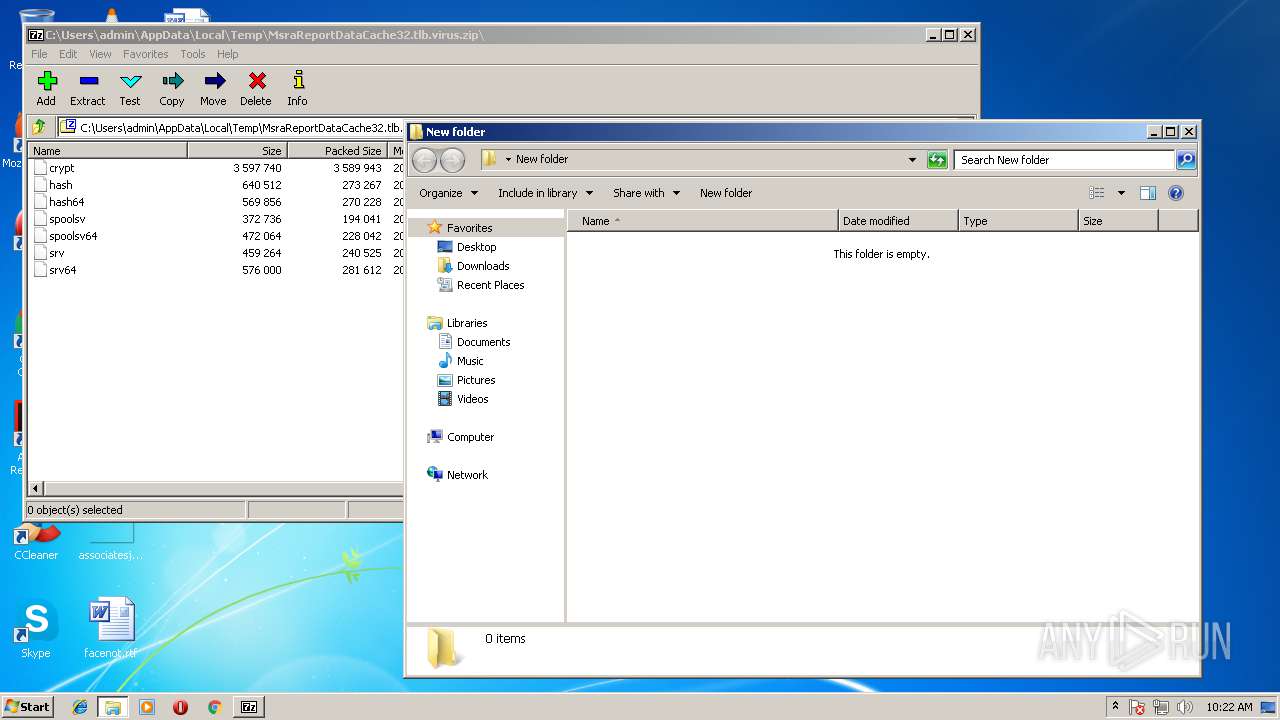
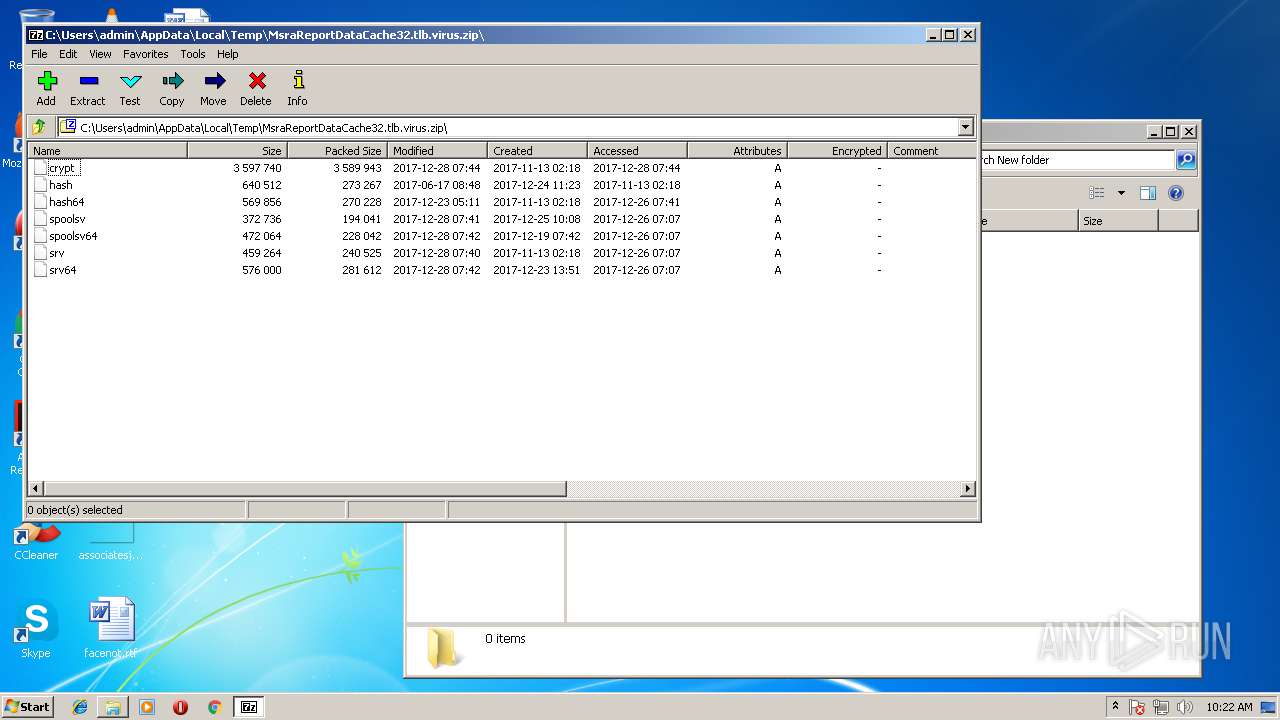
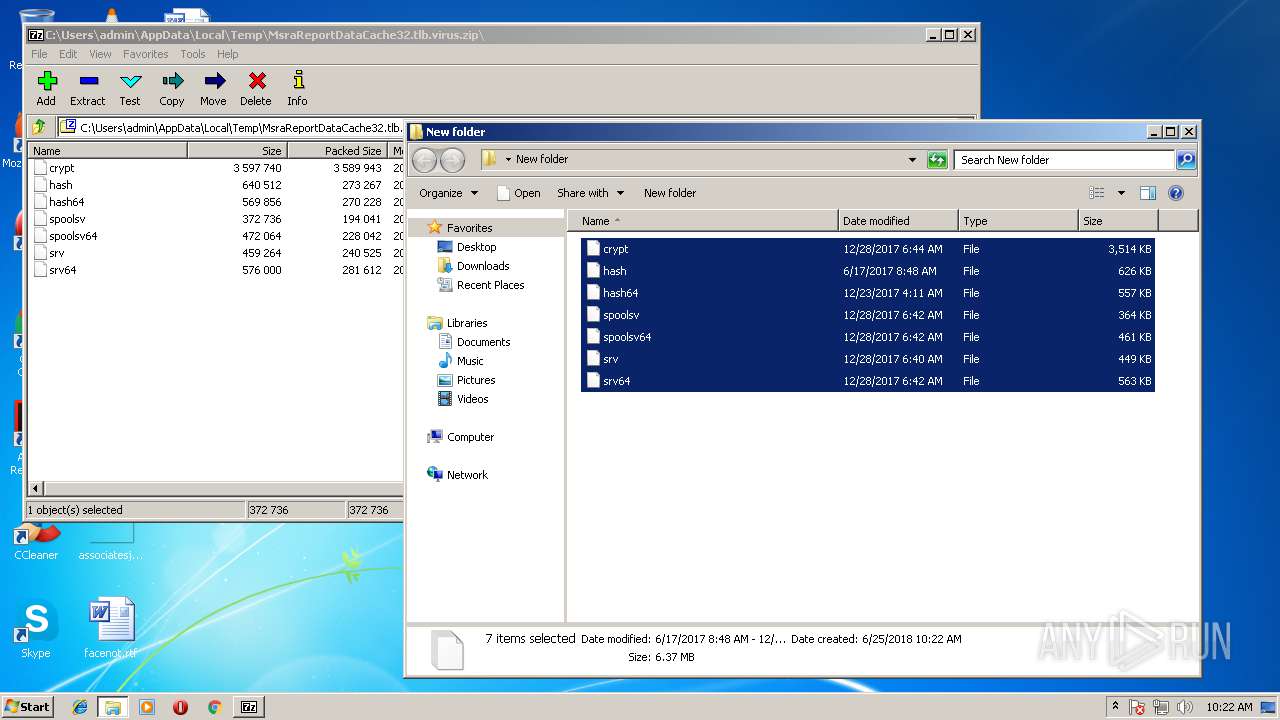
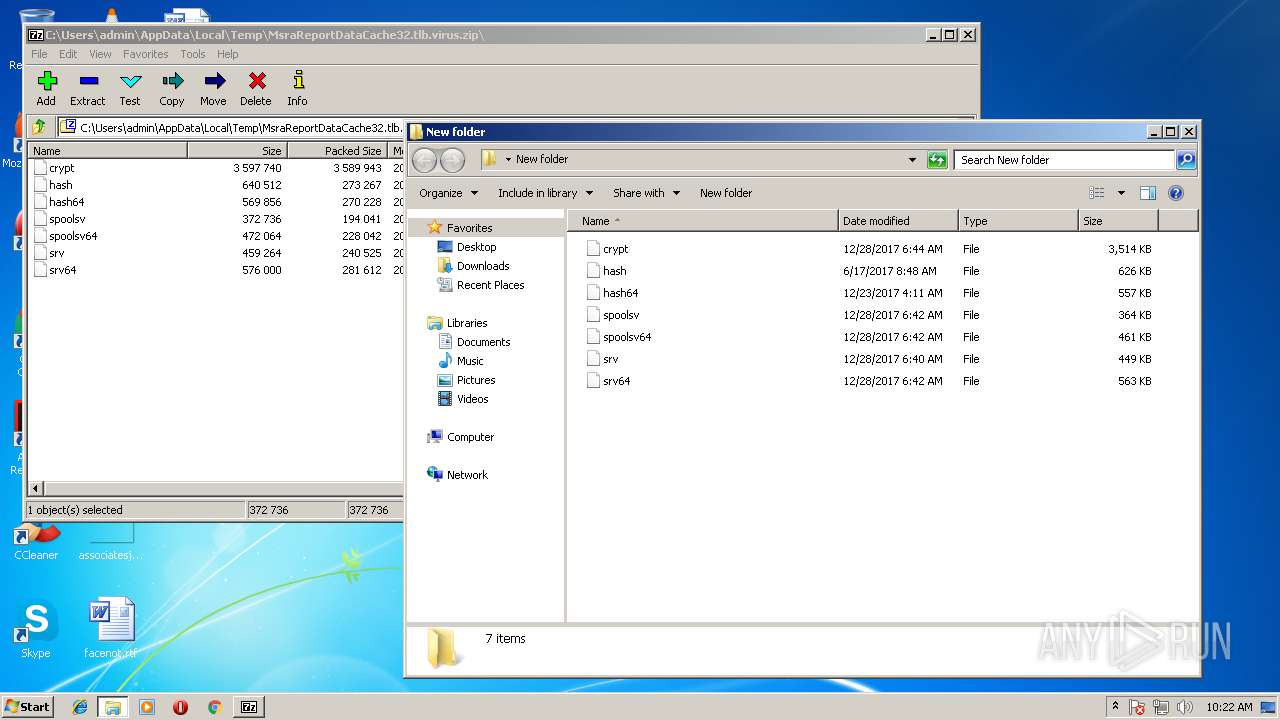
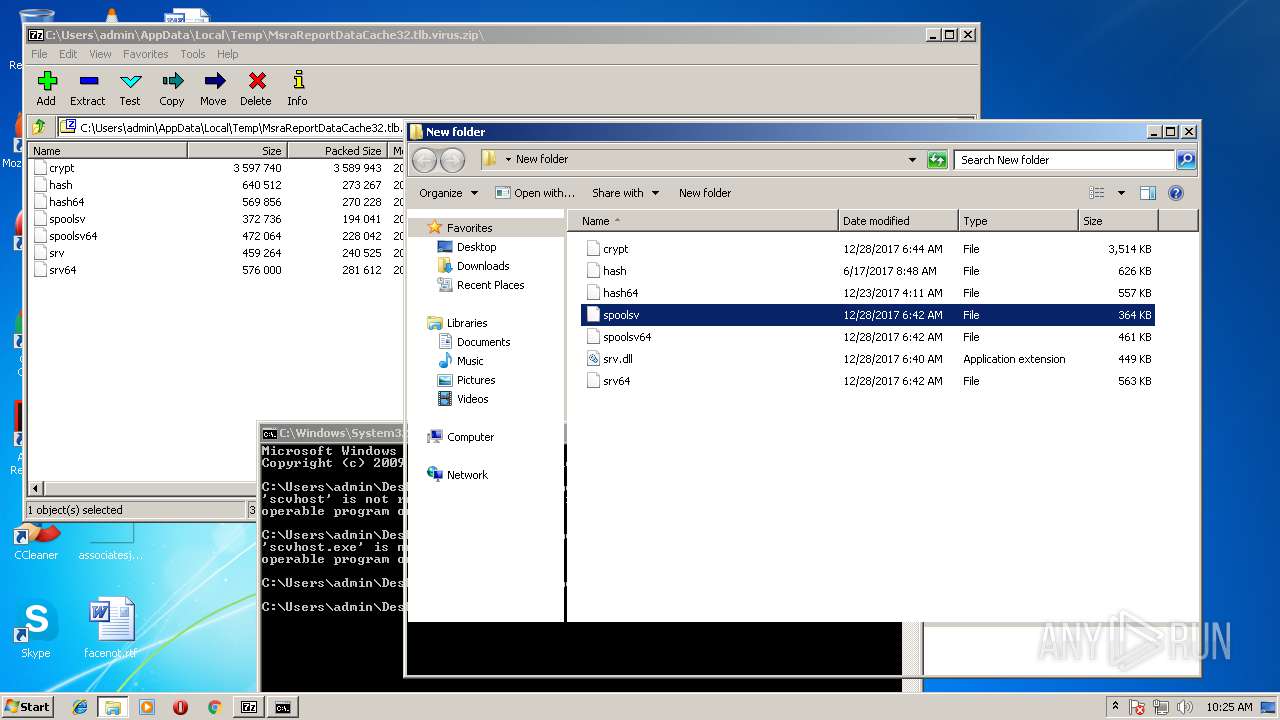
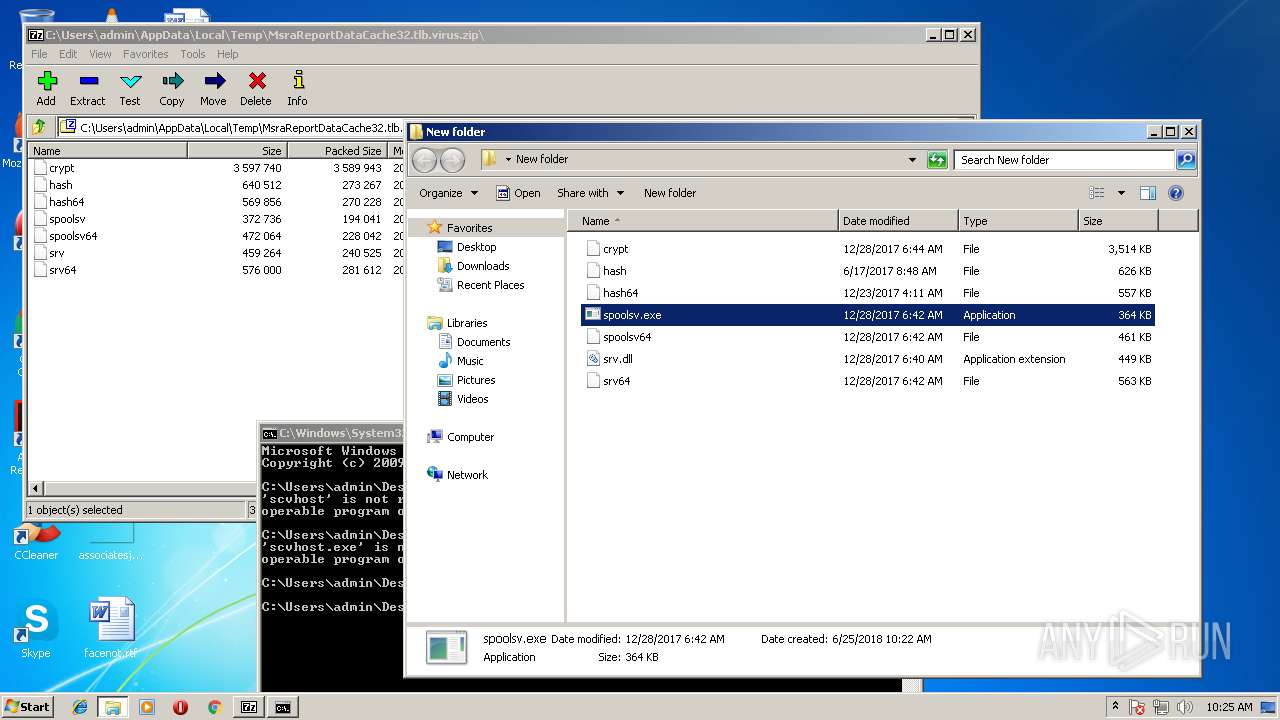
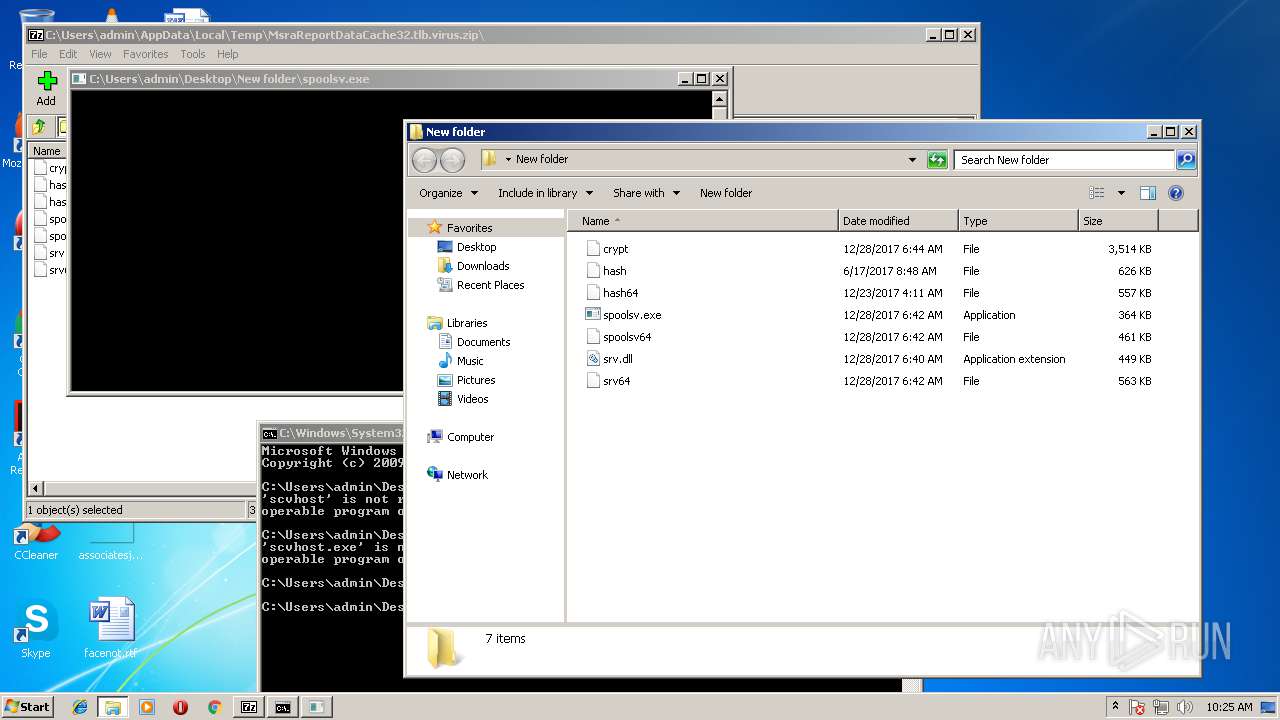
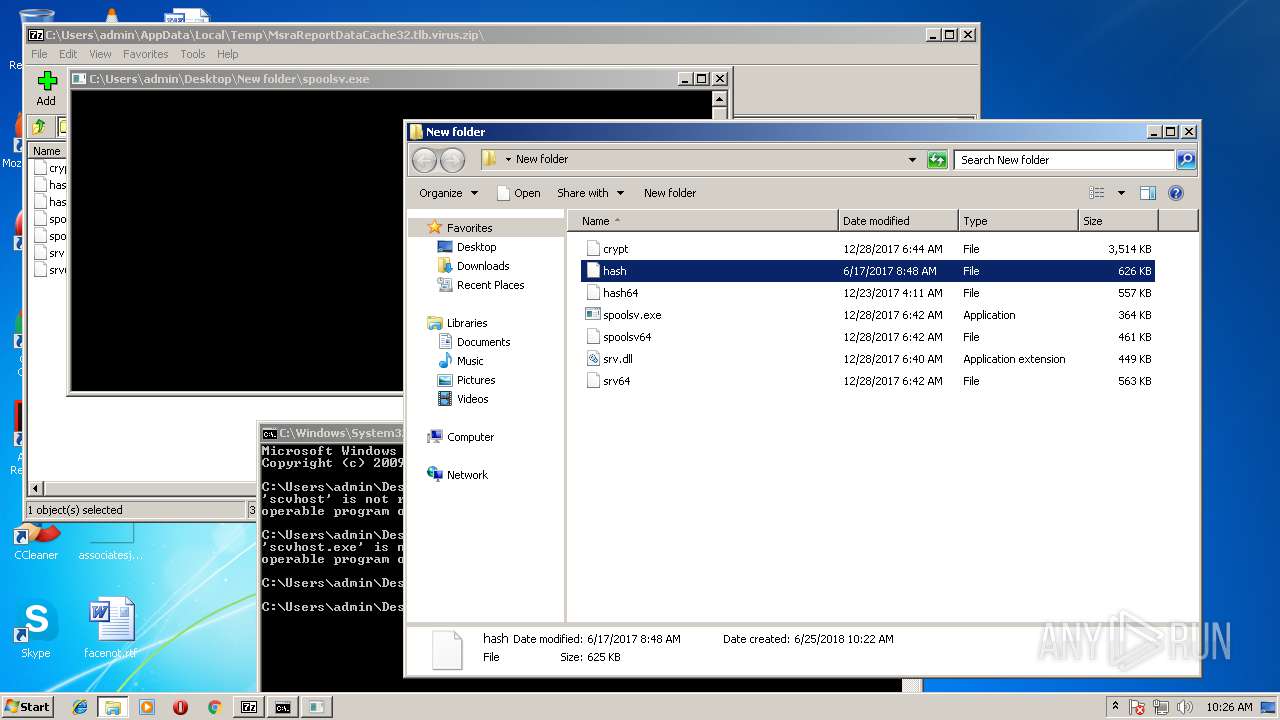
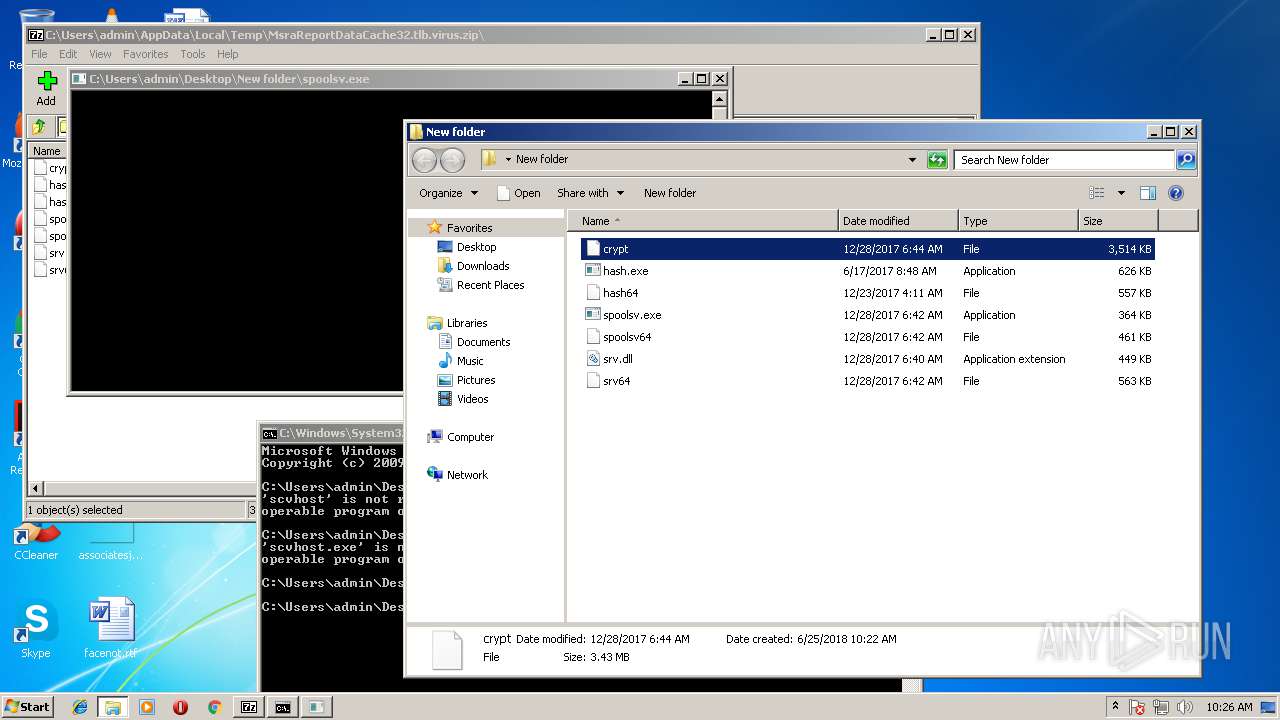
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 716 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zECC277F0B\crypt | — | |
MD5:— | SHA256:— | |||
| 716 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zECC277F0B\hash | — | |
MD5:— | SHA256:— | |||
| 716 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zECC277F0B\hash64 | — | |
MD5:— | SHA256:— | |||
| 716 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zECC277F0B\spoolsv | — | |
MD5:— | SHA256:— | |||
| 716 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zECC277F0B\spoolsv64 | — | |
MD5:— | SHA256:— | |||
| 716 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zECC277F0B\srv | — | |
MD5:— | SHA256:— | |||
| 716 | 7zFM.exe | C:\Users\admin\AppData\Local\Temp\7zECC277F0B\srv64 | — | |
MD5:— | SHA256:— | |||
| 1676 | explorer.exe | C:\Users\admin\Desktop\New folder\spoolsv | executable | |
MD5:— | SHA256:— | |||
| 1676 | explorer.exe | C:\Users\admin\Desktop\New folder\spoolsv.exe | executable | |
MD5:— | SHA256:— | |||
| 1676 | explorer.exe | C:\Users\admin\Desktop\New folder\spoolsv64 | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3396 | spoolsv.exe | 45.32.127.108:4431 | ccc.njaavfxcgk3.club | Choopa, LLC | SG | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ccc.njaavfxcgk3.club |
| malicious |