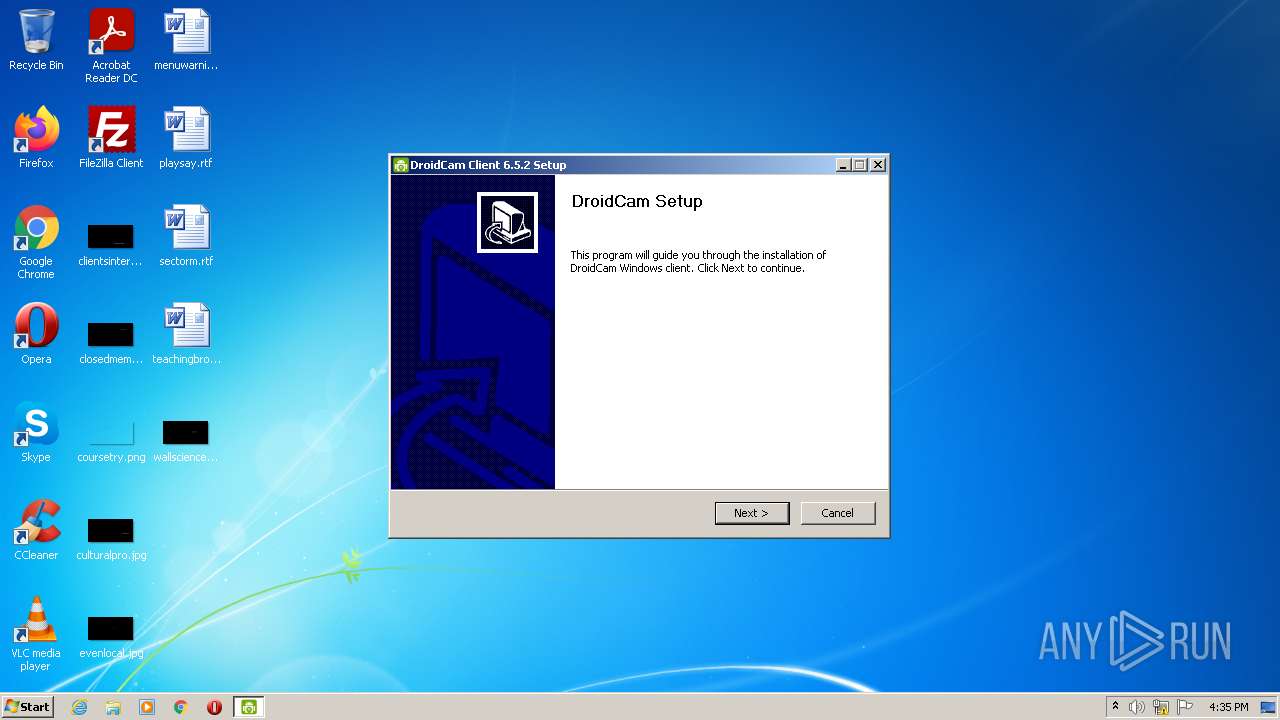
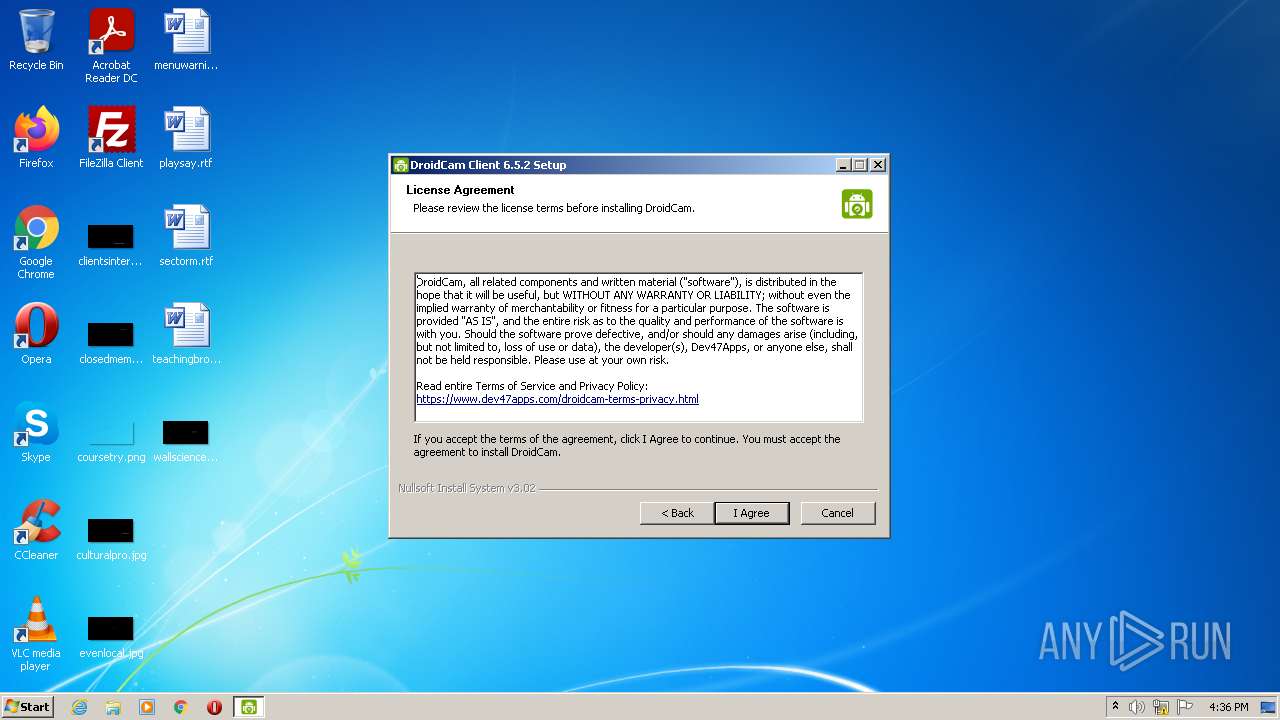
| File name: | DroidCam.Setup.6.5.2.exe |
| Full analysis: | https://app.any.run/tasks/7e083bea-b57a-4c9c-bf8e-7bc892571a04 |
| Verdict: | Malicious activity |
| Analysis date: | March 08, 2022, 16:35:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | D952D907646A522CAF6EC5D00D114CE1 |
| SHA1: | 75AD9BACB60DED431058A50A220E22A35E3D03F7 |
| SHA256: | F92AD1E92780A039397FD62D04AFFE97F1A65D04E7A41C9B5DA6DD3FD265967E |
| SSDEEP: | 393216:oZsfK4YUD12zS7SEOegn4j7BgNE9O+wcDGFdClu8ZLzzpC4:gsfKPUD1kS7249O3cDGvClnlC4 |
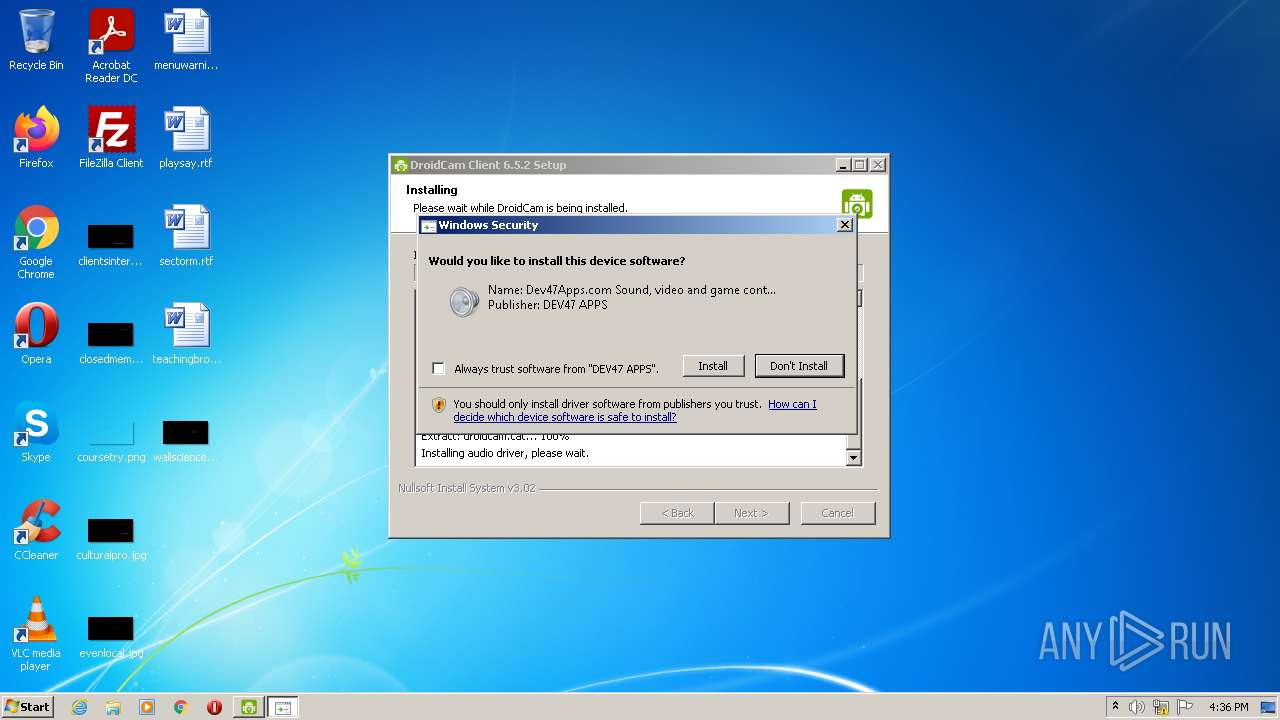
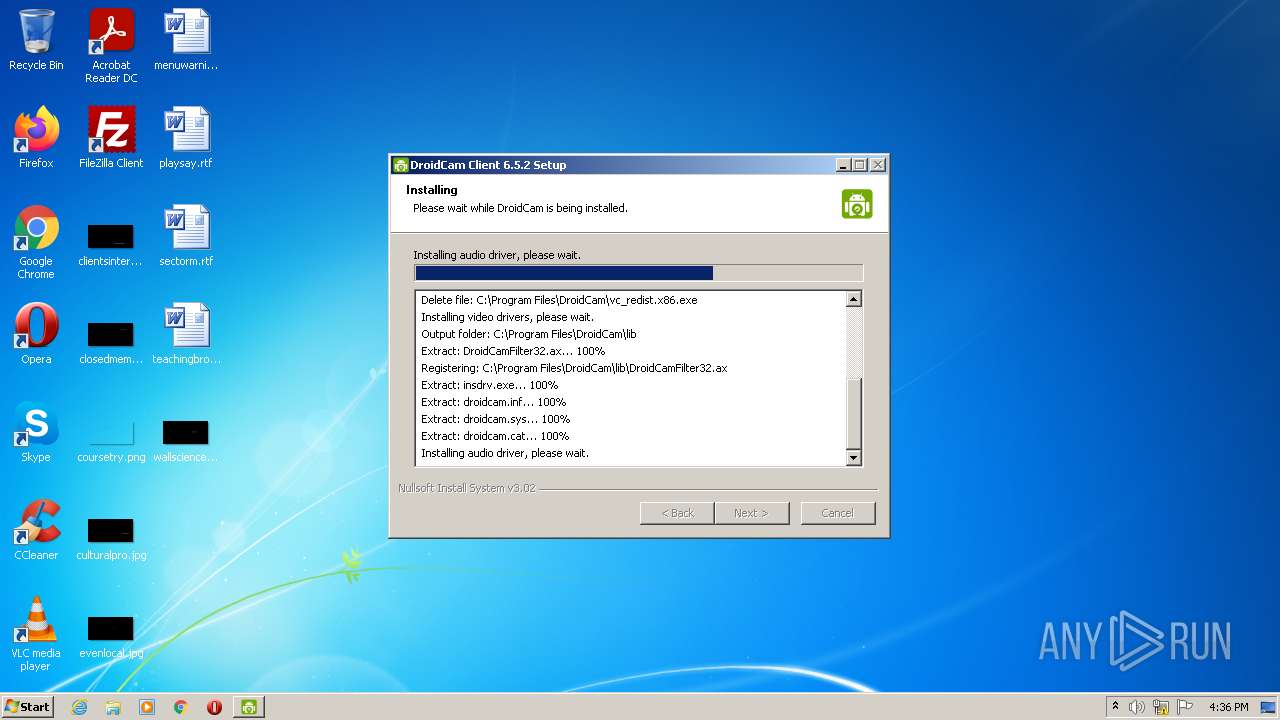
MALICIOUS
Loads dropped or rewritten executable
- DroidCam.Setup.6.5.2.exe (PID: 4012)
- vc_redist.x86.exe (PID: 2716)
- DroidCamApp.exe (PID: 508)
Drops executable file immediately after starts
- DroidCam.Setup.6.5.2.exe (PID: 4012)
- vc_redist.x86.exe (PID: 2716)
- DrvInst.exe (PID: 4028)
Application was dropped or rewritten from another process
- vc_redist.x86.exe (PID: 3388)
- vc_redist.x86.exe (PID: 2716)
- insdrv.exe (PID: 2052)
- DroidCamApp.exe (PID: 508)
SUSPICIOUS
Checks supported languages
- DroidCam.Setup.6.5.2.exe (PID: 4012)
- ns29B0.tmp (PID: 2236)
- vc_redist.x86.exe (PID: 3388)
- vc_redist.x86.exe (PID: 2716)
- ns2C13.tmp (PID: 2992)
- insdrv.exe (PID: 2052)
- DrvInst.exe (PID: 4028)
- DrvInst.exe (PID: 3848)
- DroidCamApp.exe (PID: 508)
Reads the computer name
- DroidCam.Setup.6.5.2.exe (PID: 4012)
- vc_redist.x86.exe (PID: 2716)
- insdrv.exe (PID: 2052)
- DrvInst.exe (PID: 4028)
- DrvInst.exe (PID: 3848)
- DroidCamApp.exe (PID: 508)
- vc_redist.x86.exe (PID: 3388)
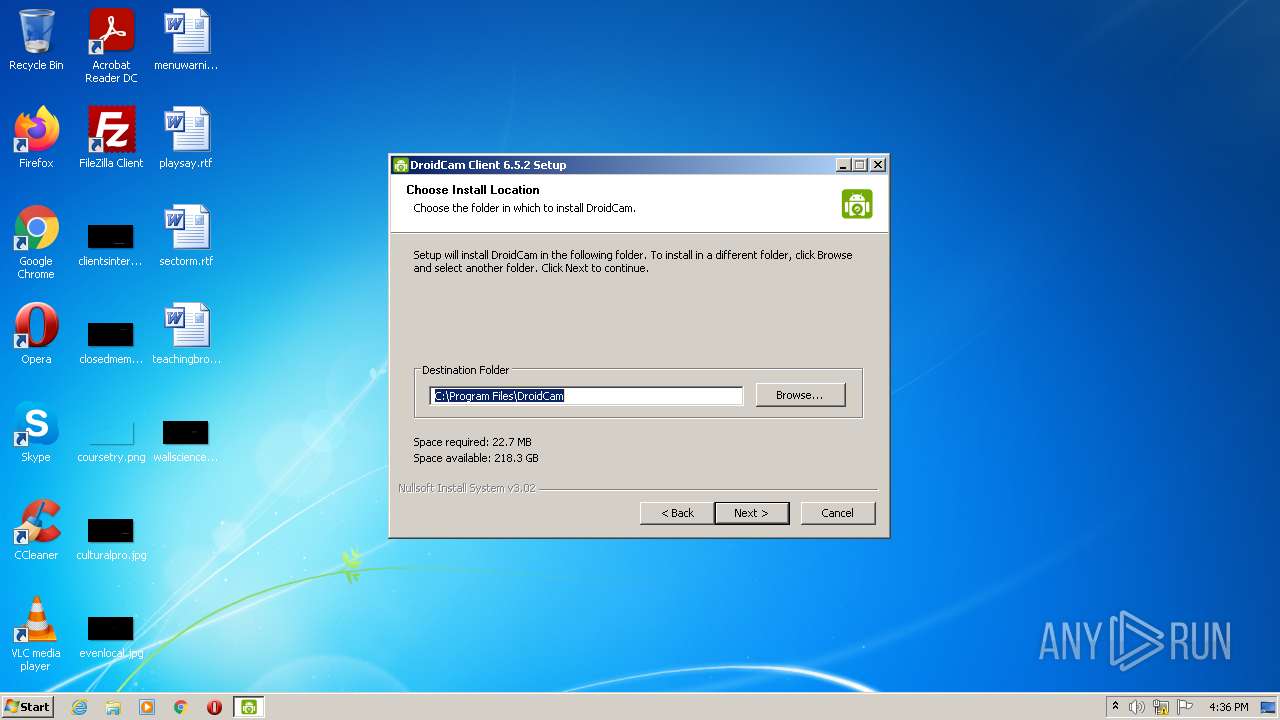
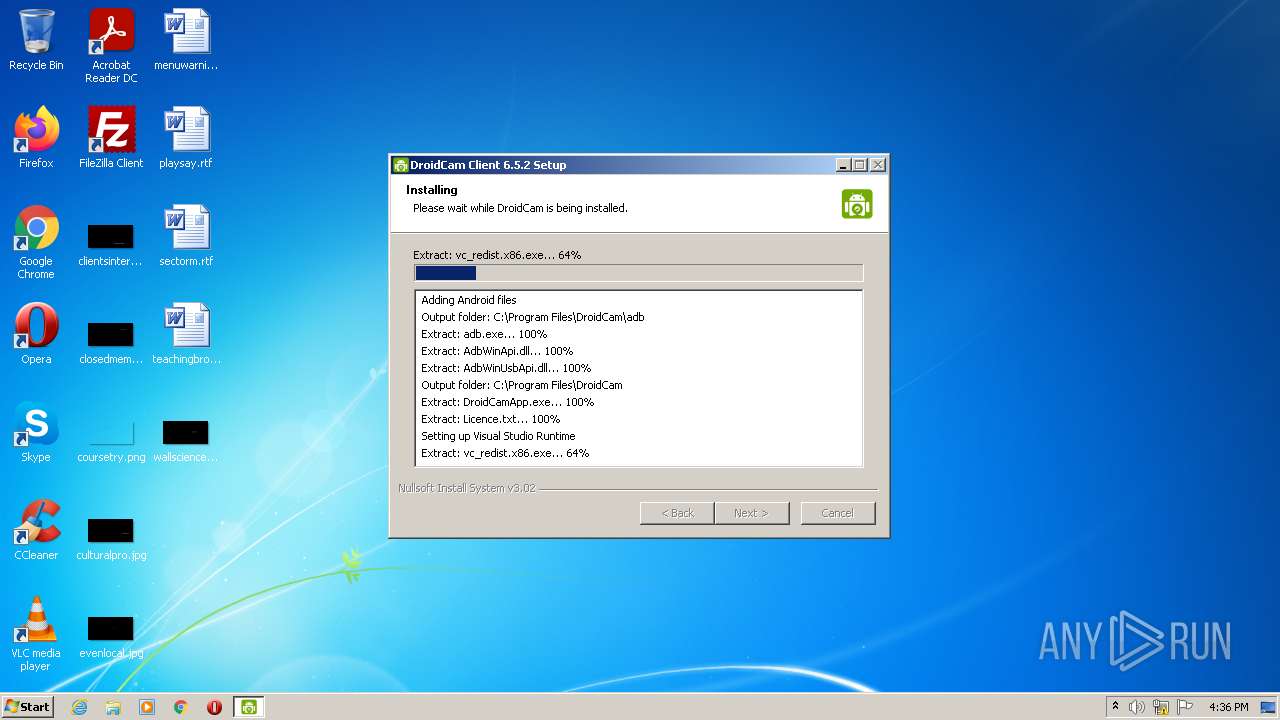
Creates a directory in Program Files
- DroidCam.Setup.6.5.2.exe (PID: 4012)
Starts application with an unusual extension
- DroidCam.Setup.6.5.2.exe (PID: 4012)
Drops a file with too old compile date
- DroidCam.Setup.6.5.2.exe (PID: 4012)
Executable content was dropped or overwritten
- DroidCam.Setup.6.5.2.exe (PID: 4012)
- vc_redist.x86.exe (PID: 2716)
- insdrv.exe (PID: 2052)
- DrvInst.exe (PID: 4028)
- DrvInst.exe (PID: 3848)
Drops a file that was compiled in debug mode
- DroidCam.Setup.6.5.2.exe (PID: 4012)
- vc_redist.x86.exe (PID: 2716)
- insdrv.exe (PID: 2052)
- DrvInst.exe (PID: 4028)
- DrvInst.exe (PID: 3848)
Creates files in the program directory
- DroidCam.Setup.6.5.2.exe (PID: 4012)
Application launched itself
- vc_redist.x86.exe (PID: 3388)
Executed via COM
- DrvInst.exe (PID: 4028)
- DrvInst.exe (PID: 3848)
Removes files from Windows directory
- DrvInst.exe (PID: 4028)
- DrvInst.exe (PID: 3848)
Creates files in the driver directory
- DrvInst.exe (PID: 4028)
- DrvInst.exe (PID: 3848)
Searches for installed software
- vc_redist.x86.exe (PID: 2716)
Creates files in the Windows directory
- DrvInst.exe (PID: 4028)
- DrvInst.exe (PID: 3848)
Uses RUNDLL32.EXE to load library
- DrvInst.exe (PID: 4028)
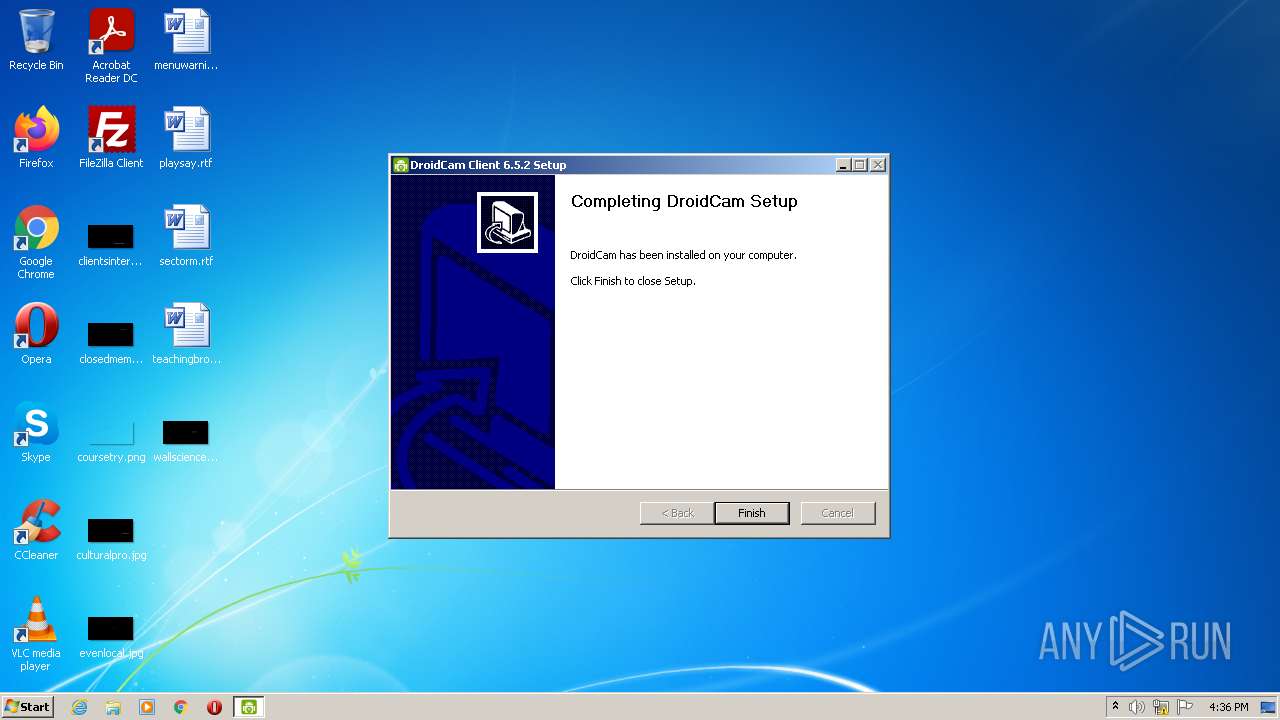
Creates a software uninstall entry
- DroidCam.Setup.6.5.2.exe (PID: 4012)
Creates files in the user directory
- DroidCam.Setup.6.5.2.exe (PID: 4012)
Executed as Windows Service
- vssvc.exe (PID: 3380)
Reads Environment values
- vssvc.exe (PID: 3380)
INFO
Dropped object may contain Bitcoin addresses
- DroidCam.Setup.6.5.2.exe (PID: 4012)
Reads settings of System Certificates
- insdrv.exe (PID: 2052)
- DrvInst.exe (PID: 4028)
- rundll32.exe (PID: 2024)
- DrvInst.exe (PID: 3848)
Checks Windows Trust Settings
- insdrv.exe (PID: 2052)
- DrvInst.exe (PID: 4028)
- rundll32.exe (PID: 2024)
- DrvInst.exe (PID: 3848)
Checks supported languages
- rundll32.exe (PID: 2024)
- vssvc.exe (PID: 3380)
Reads the computer name
- rundll32.exe (PID: 2024)
- vssvc.exe (PID: 3380)
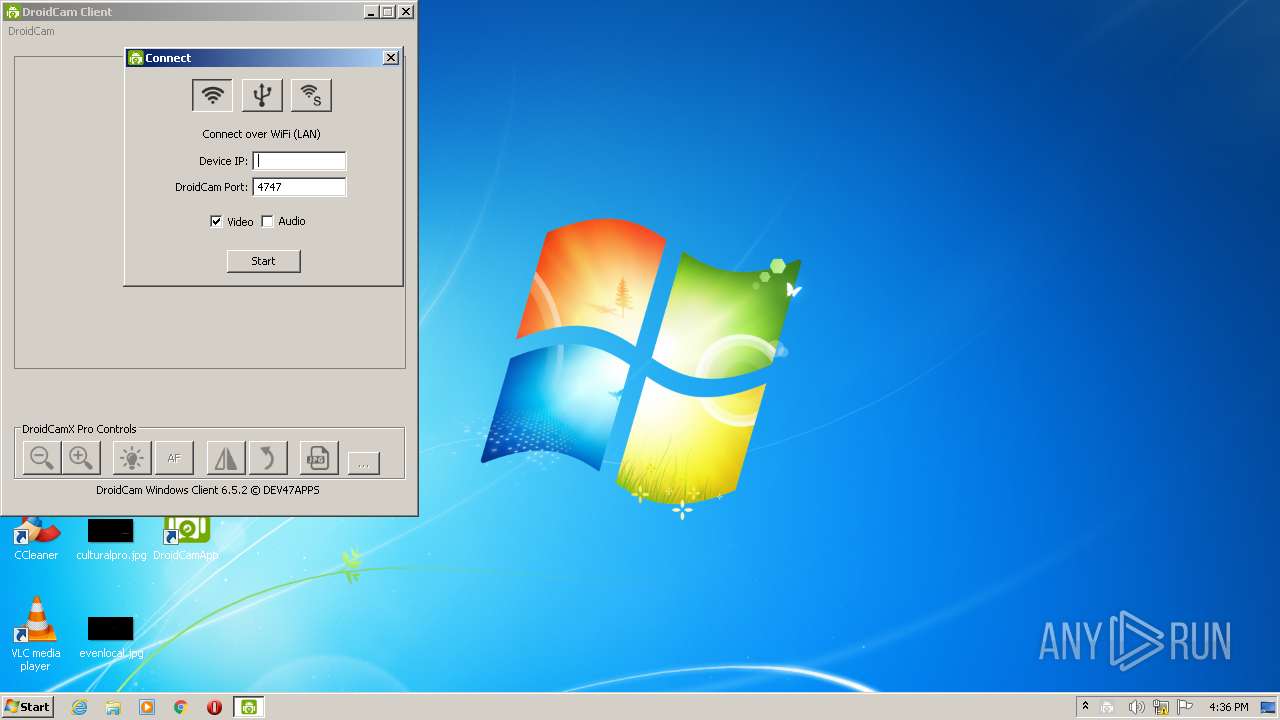
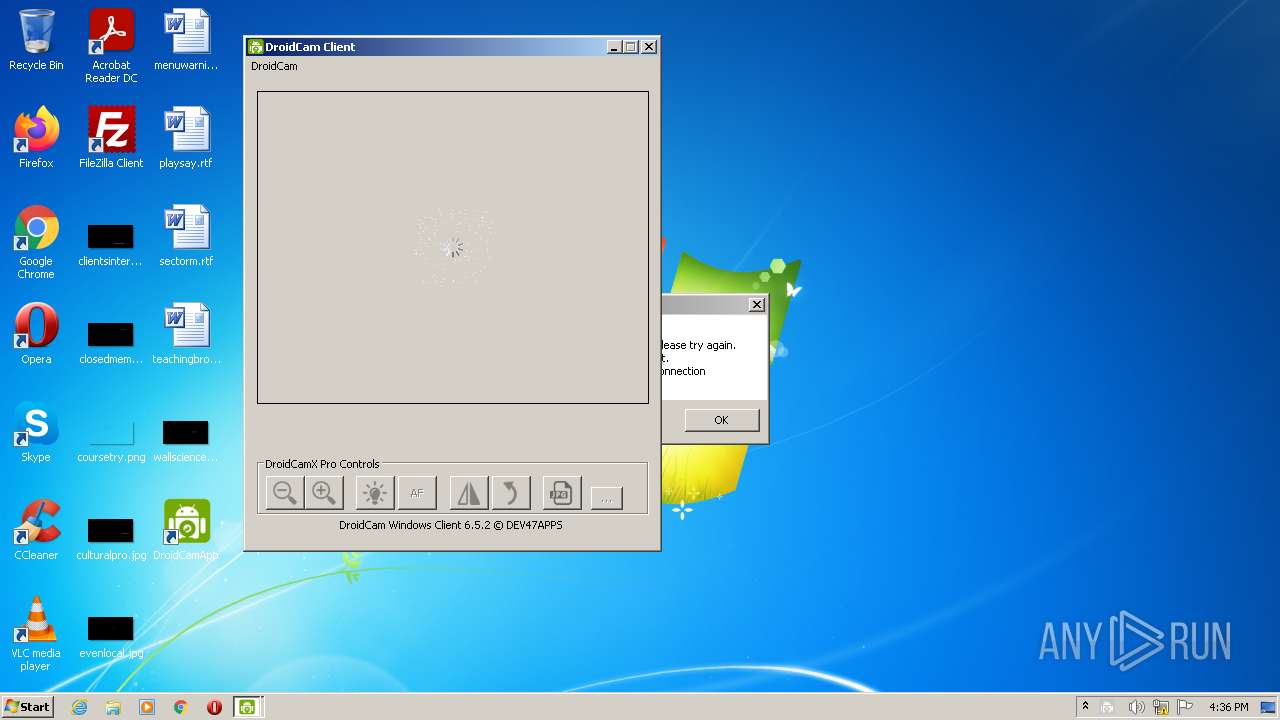
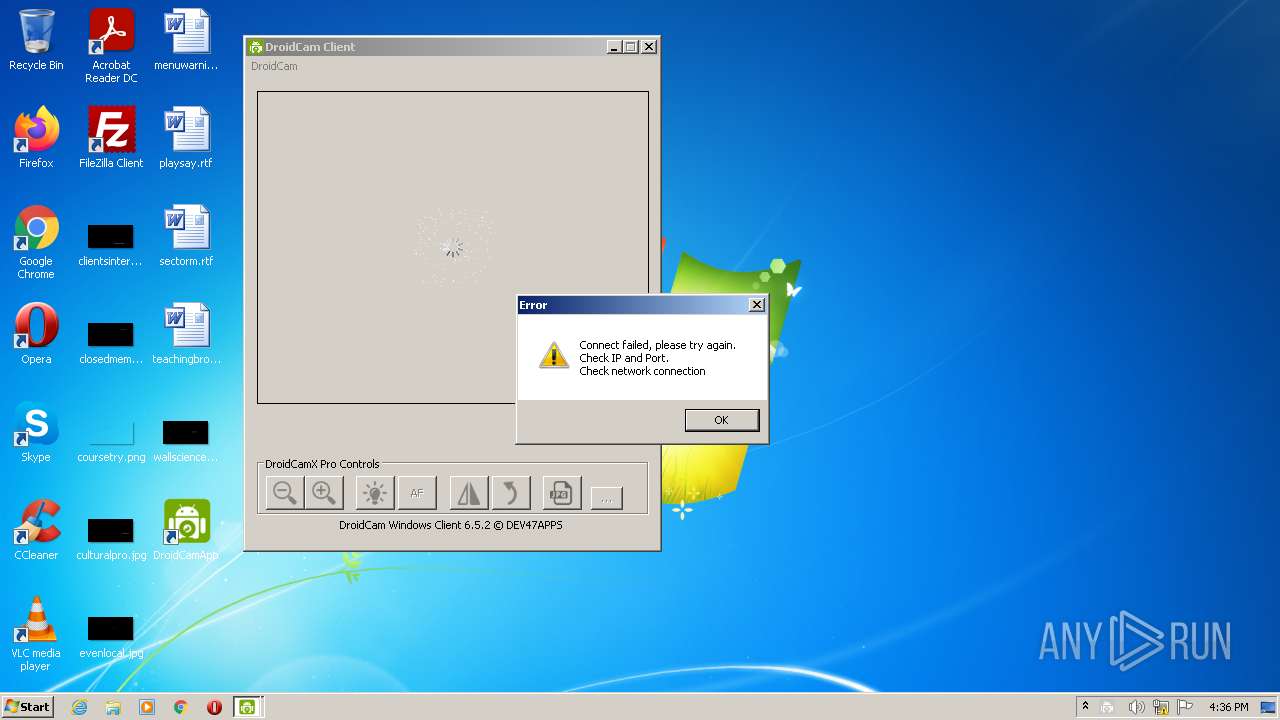
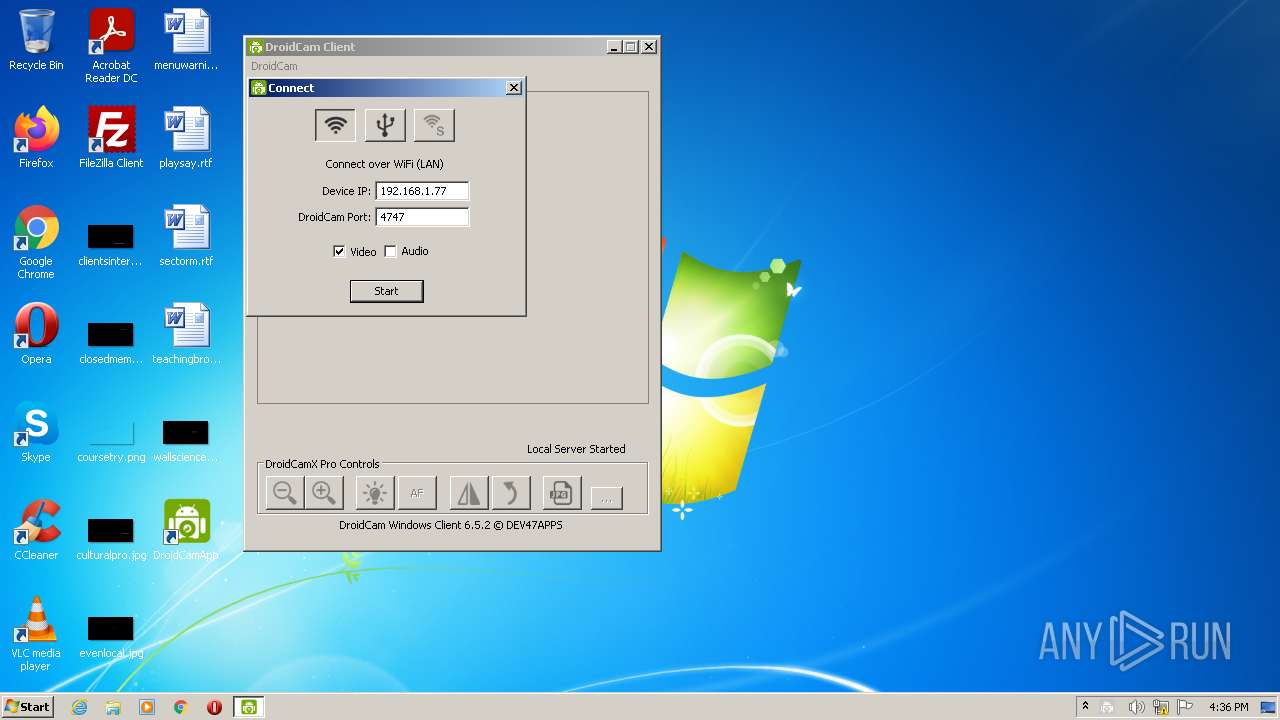
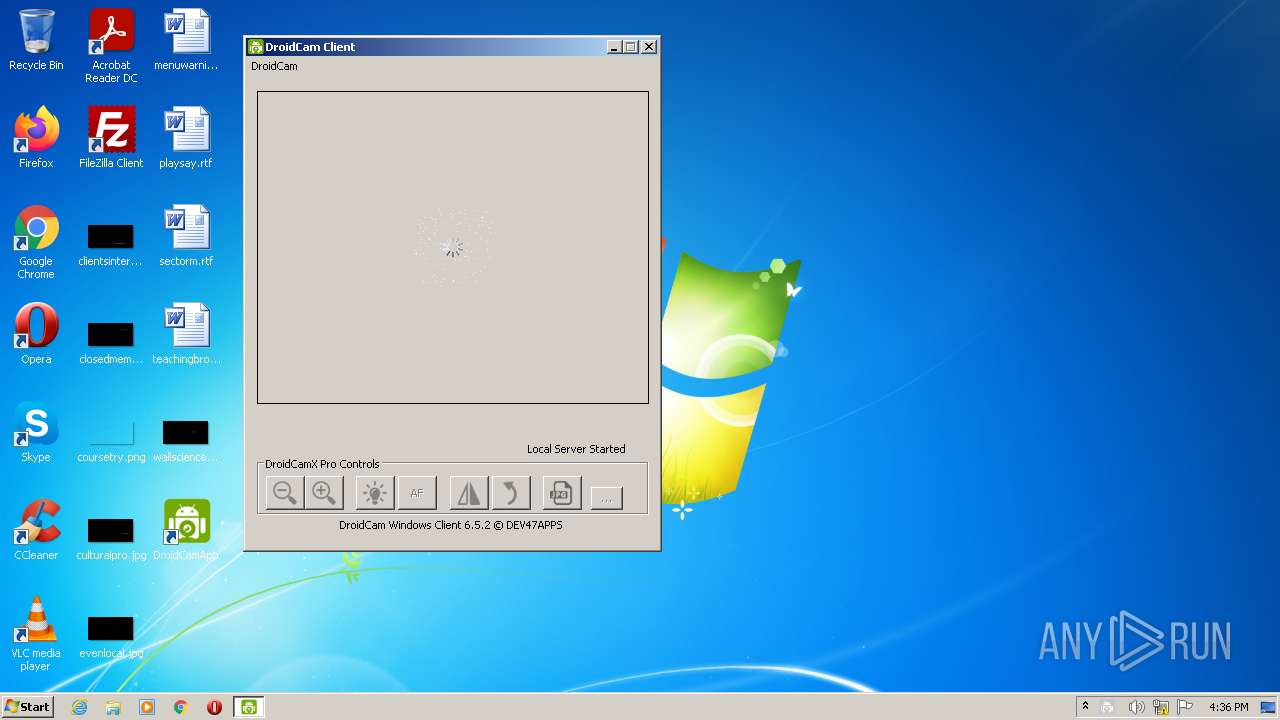
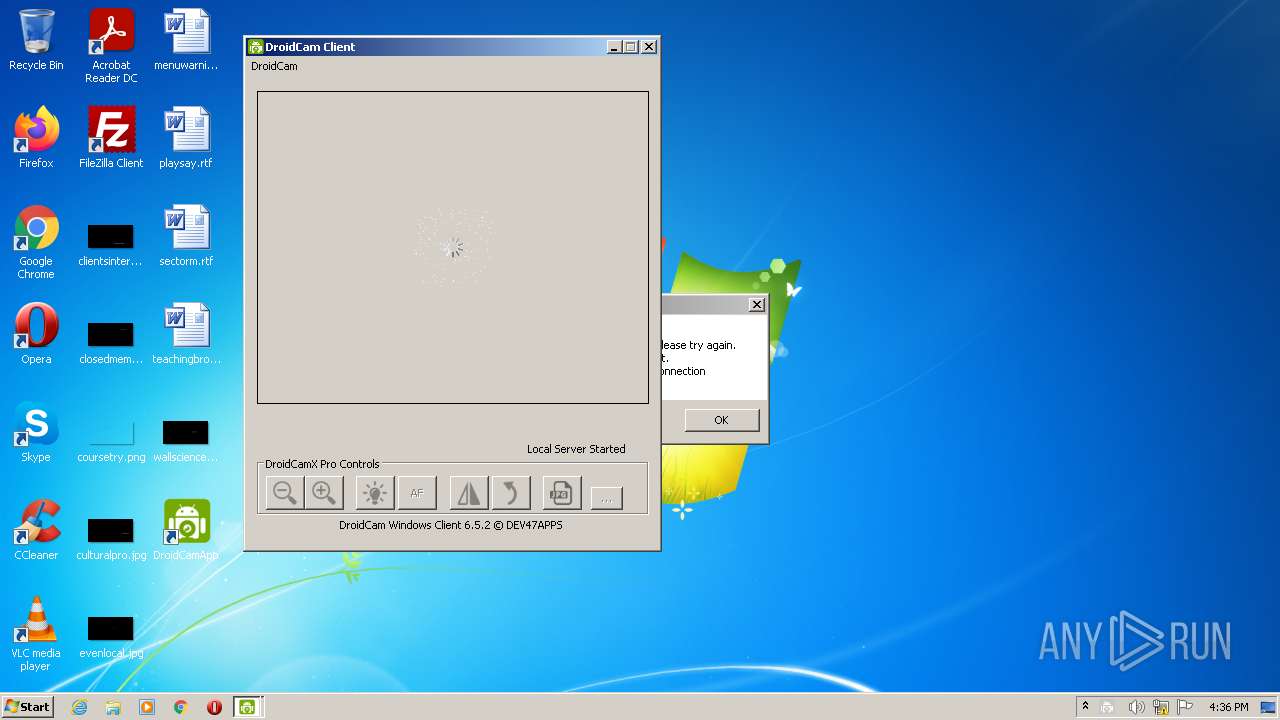
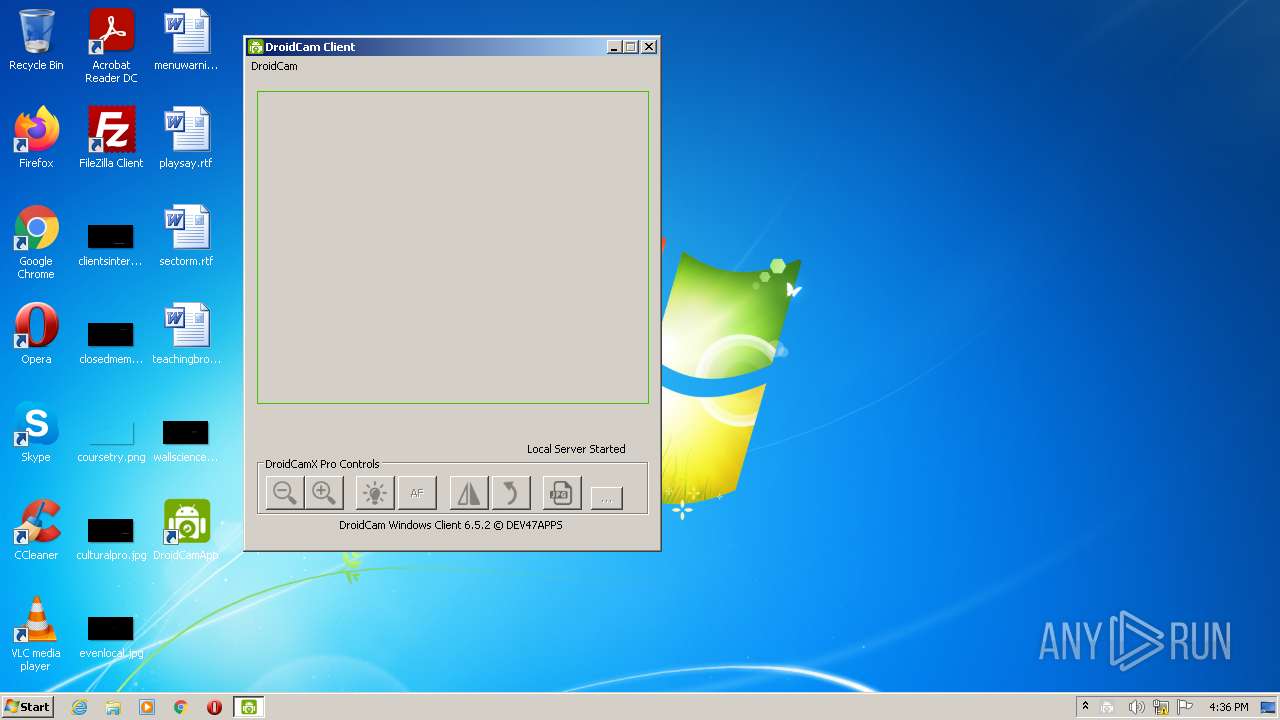
Manual execution by user
- DroidCamApp.exe (PID: 508)
Searches for installed software
- DrvInst.exe (PID: 4028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0x31bb |
| UninitializedDataSize: | 1024 |
| InitializedDataSize: | 118784 |
| CodeSize: | 24576 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 2017:07:24 08:35:15+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Jul-2017 06:35:15 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 24-Jul-2017 06:35:15 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005ED2 | 0x00006000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44218 |
.rdata | 0x00007000 | 0x00001248 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.00765 |
.data | 0x00009000 | 0x0001A818 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.13586 |
.ndata | 0x00024000 | 0x00018000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0003C000 | 0x00009C90 | 0x00009E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.66465 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28847 | 1070 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.96986 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 4.73845 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 5.11387 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 0 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 0 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 0 | 296 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.86816 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.65946 | 280 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
52
Monitored processes
12
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 508 | "C:\Program Files\DroidCam\DroidCamApp.exe" | C:\Program Files\DroidCam\DroidCamApp.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2024 | rundll32.exe C:\Windows\system32\pnpui.dll,InstallSecurityPromptRunDllW 20 Global\{53da982c-56c0-2543-f5d0-c21aee0d8876} Global\{7e94b9a3-d10e-4cf6-c1a4-947e88f73a34} C:\Windows\System32\DriverStore\Temp\{4c4280a7-70cb-6ada-bfbf-da0680d05f1a}\droidcam.inf C:\Windows\System32\DriverStore\Temp\{4c4280a7-70cb-6ada-bfbf-da0680d05f1a}\droidcam.cat | C:\Windows\system32\rundll32.exe | — | DrvInst.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2052 | "C:\Program Files\DroidCam\lib\insdrv.exe" +a | C:\Program Files\DroidCam\lib\insdrv.exe | ns2C13.tmp | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2236 | "C:\Users\admin\AppData\Local\Temp\nsgFF63.tmp\ns29B0.tmp" "C:\Program Files\DroidCam\vc_redist.x86.exe" /install /quiet | C:\Users\admin\AppData\Local\Temp\nsgFF63.tmp\ns29B0.tmp | — | DroidCam.Setup.6.5.2.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1638 Modules
| |||||||||||||||
| 2716 | "C:\Program Files\DroidCam\vc_redist.x86.exe" /install /quiet -burn.unelevated BurnPipe.{5319AE99-A3CD-40FD-A175-E3E4871DF2E0} {1851C245-5AD2-4EF2-8F7A-1A3CC8C4E030} 3388 | C:\Program Files\DroidCam\vc_redist.x86.exe | vc_redist.x86.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015 Redistributable (x86) - 14.0.23026 Exit code: 1638 Version: 14.0.23026.0 Modules
| |||||||||||||||
| 2992 | "C:\Users\admin\AppData\Local\Temp\nsgFF63.tmp\ns2C13.tmp" "C:\Program Files\DroidCam\lib\insdrv.exe" +a | C:\Users\admin\AppData\Local\Temp\nsgFF63.tmp\ns2C13.tmp | — | DroidCam.Setup.6.5.2.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3380 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft� Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3388 | "C:\Program Files\DroidCam\vc_redist.x86.exe" /install /quiet | C:\Program Files\DroidCam\vc_redist.x86.exe | — | ns29B0.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015 Redistributable (x86) - 14.0.23026 Exit code: 1638 Version: 14.0.23026.0 Modules
| |||||||||||||||
| 3412 | "C:\Users\admin\AppData\Local\Temp\DroidCam.Setup.6.5.2.exe" | C:\Users\admin\AppData\Local\Temp\DroidCam.Setup.6.5.2.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3848 | DrvInst.exe "2" "211" "ROOT\MEDIA\0000" "C:\Windows\INF\oem5.inf" "droidcam.inf:MicrosoftDS:DroidCam_PCMEX:1.0.0.1:droidcam" "6e67c8bbf" "0000057C" "00000574" "000005FC" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
17 760
Read events
17 223
Write events
537
Delete events
0
Modification events
| (PID) Process: | (4012) DroidCam.Setup.6.5.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{9E2FBAC0-C951-4AA8-BFA9-4B196644964C} |
| Operation: | write | Name: | (default) |
Value: DroidCam Source 2 | |||
| (PID) Process: | (4012) DroidCam.Setup.6.5.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{9E2FBAC0-C951-4AA8-BFA9-4B196644964C}\InprocServer32 |
| Operation: | write | Name: | (default) |
Value: C:\Program Files\DroidCam\lib\DroidCamFilter32.ax | |||
| (PID) Process: | (4012) DroidCam.Setup.6.5.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{9E2FBAC0-C951-4AA8-BFA9-4B196644964C}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Both | |||
| (PID) Process: | (4012) DroidCam.Setup.6.5.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{860BB310-5D01-11d0-BD3B-00A0C911CE86}\Instance\{9E2FBAC0-C951-4AA8-BFA9-4B196644964C} |
| Operation: | write | Name: | FriendlyName |
Value: DroidCam Source 2 | |||
| (PID) Process: | (4012) DroidCam.Setup.6.5.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{860BB310-5D01-11d0-BD3B-00A0C911CE86}\Instance\{9E2FBAC0-C951-4AA8-BFA9-4B196644964C} |
| Operation: | write | Name: | CLSID |
Value: {9E2FBAC0-C951-4AA8-BFA9-4B196644964C} | |||
| (PID) Process: | (4012) DroidCam.Setup.6.5.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{860BB310-5D01-11d0-BD3B-00A0C911CE86}\Instance\{9E2FBAC0-C951-4AA8-BFA9-4B196644964C} |
| Operation: | write | Name: | FilterData |
Value: 02000000000060000100000000000000307069330800000000000000010000000000000000000000307479330000000038000000480000007669647300001000800000AA00389B7100000000000000000000000000000000 | |||
| (PID) Process: | (4012) DroidCam.Setup.6.5.2.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{860BB310-5D01-11d0-BD3B-00A0C911CE86}\Instance\{9E2FBAC0-C951-4AA8-BFA9-4B196644964C} |
| Operation: | write | Name: | DevicePath |
Value: droidcam:2 | |||
| (PID) Process: | (2052) insdrv.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.app.log |
Value: 4096 | |||
| (PID) Process: | (2052) insdrv.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.dev.log |
Value: 4096 | |||
| (PID) Process: | (2052) insdrv.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
25
Suspicious files
12
Text files
45
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4012 | DroidCam.Setup.6.5.2.exe | C:\Users\admin\AppData\Local\Temp\nsgFF63.tmp\System.dll | executable | |
MD5:C9473CB90D79A374B2BA6040CA16E45C | SHA256:B80A5CBA69D1853ED5979B0CA0352437BF368A5CFB86CB4528EDADD410E11352 | |||
| 4012 | DroidCam.Setup.6.5.2.exe | C:\Users\admin\AppData\Local\Temp\nsgFF63.tmp\nsDialogs.dll | executable | |
MD5:12465CE89D3853918ED3476D70223226 | SHA256:5157FE688CCA27D348171BD5A8B117DE348C0844CA5CB82BC68CBD7D873A3FDC | |||
| 4012 | DroidCam.Setup.6.5.2.exe | C:\Users\admin\AppData\Local\Temp\nsgFF63.tmp\nsExec.dll | executable | |
MD5:0A6F707FA22C3F3E5D1ABB54B0894AD6 | SHA256:370E47364561FA501B1300B056FB53FAE12B1639FDF5F113275BEE03546081C0 | |||
| 4012 | DroidCam.Setup.6.5.2.exe | C:\Program Files\DroidCam\adb\AdbWinUsbApi.dll | executable | |
MD5:0E24119DAF1909E398FA1850B6112077 | SHA256:25207C506D29C4E8DCEB61B4BD50E8669BA26012988A43FBF26A890B1E60FC97 | |||
| 4012 | DroidCam.Setup.6.5.2.exe | C:\Program Files\DroidCam\Licence.txt | text | |
MD5:6D6FDAD34E3230EC837F6661AB545129 | SHA256:8558A2793108D6973D94B0D7475570D1FCECDC15F0D7EB1AA5515868AD03C64E | |||
| 4012 | DroidCam.Setup.6.5.2.exe | C:\Users\admin\AppData\Local\Temp\nsgFF63.tmp\ns29B0.tmp | executable | |
MD5:0A6F707FA22C3F3E5D1ABB54B0894AD6 | SHA256:370E47364561FA501B1300B056FB53FAE12B1639FDF5F113275BEE03546081C0 | |||
| 2716 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\1040\license.rtf | text | |
MD5:1D07E27F97CE22A58780A04227BE6465 | SHA256:F1214784C57AA3323426AF64D132045970717994EBA500B25283684DC1ADEBAA | |||
| 2716 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\1029\license.rtf | text | |
MD5:FD8353F3BC88A47B8880B59A5DAD3F03 | SHA256:2428E8BA8FC9648422333B6B4B92FB476741FC1022DE7CB59D030EC35CC21AC7 | |||
| 2716 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\1041\license.rtf | text | |
MD5:0D9DD57746D5609494B35314FA88FD93 | SHA256:AC0D8E0EAAB1875909A6A6F106A37CD7468F87F71887A44263F5F0178F99C40B | |||
| 2716 | vc_redist.x86.exe | C:\Users\admin\AppData\Local\Temp\{74d0e5db-b326-4dae-a6b2-445b9de1836e}\.ba1\1042\license.rtf | text | |
MD5:F6E7A2A05EFB4413295C156A179578A3 | SHA256:DCEFD9B37D78F37ED8AAEF70AC2BFCDE441DCFB97469A6AA6AF89C1FFADBF814 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
508 | DroidCamApp.exe | 104.21.31.133:80 | update.dev47apps.net | Cloudflare Inc | US | suspicious |
— | — | 192.168.100.158:62415 | — | — | — | malicious |
— | — | 192.168.100.158:62611 | — | — | — | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
update.dev47apps.net |
| suspicious |