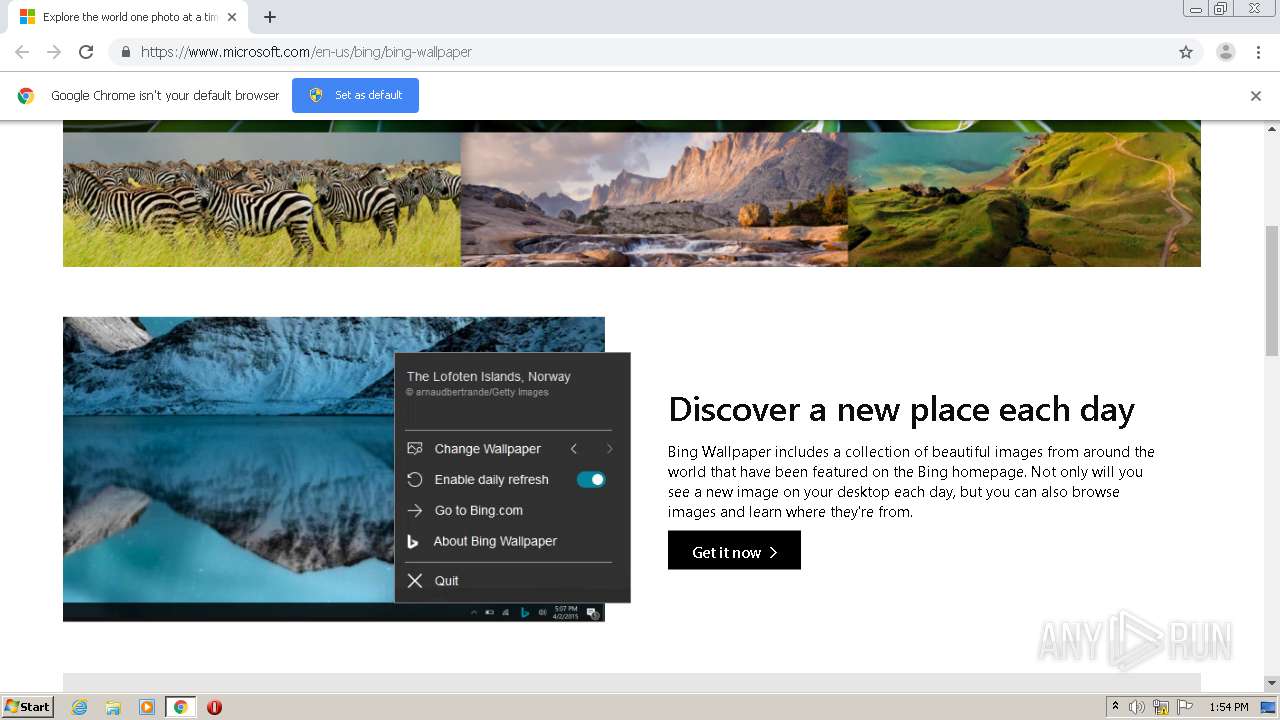
| URL: | https://www.microsoft.com/en-us/bing/bing-wallpaper |
| Full analysis: | https://app.any.run/tasks/097c053e-8217-4840-8486-c27e931eb003 |
| Verdict: | Malicious activity |
| Analysis date: | October 07, 2020, 12:54:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | EA7649E651AFE97598FCDEAD6355DABA |
| SHA1: | 77BA999C9468370DDE2A0E35BECBB52E6F972697 |
| SHA256: | F928C392A41F56DEAA16DD00C13A53844799D0048DAD482C2B4334E2B12446D7 |
| SSDEEP: | 3:N8DSLZRtRHVEHayn:2OLTDH0 |
MALICIOUS
Application was dropped or rewritten from another process
- BingWallpaper.exe (PID: 3564)
- BWInstaller.exe (PID: 1736)
- StartupInstaller.exe (PID: 2068)
- BingWallpaperApp.exe (PID: 948)
Actions looks like stealing of personal data
- BWInstaller.exe (PID: 1736)
- DefaultSetup.exe (PID: 4072)
Loads dropped or rewritten executable
- BWInstaller.exe (PID: 1736)
- rundll32.exe (PID: 3132)
- rundll32.exe (PID: 1712)
- rundll32.exe (PID: 3360)
- BingWallpaperApp.exe (PID: 948)
Changes the autorun value in the registry
- BWInstaller.exe (PID: 1736)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2564)
- BingWallpaper.exe (PID: 3564)
- chrome.exe (PID: 1044)
- msiexec.exe (PID: 1732)
- rundll32.exe (PID: 1712)
- rundll32.exe (PID: 3360)
- BingWallpaperApp.exe (PID: 948)
Reads Environment values
- BWInstaller.exe (PID: 1736)
- BingWallpaperApp.exe (PID: 948)
Creates files in the user directory
- msiexec.exe (PID: 1732)
- DefaultSetup.exe (PID: 4072)
Changes the autorun value in the registry
- msiexec.exe (PID: 1732)
Uses RUNDLL32.EXE to load library
- MsiExec.exe (PID: 2796)
Reads Internet Cache Settings
- rundll32.exe (PID: 1712)
- BWInstaller.exe (PID: 1736)
- DefaultSetup.exe (PID: 4072)
Creates files in the program directory
- firefox.exe (PID: 3700)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2564)
Changes the desktop background image
- BingWallpaperApp.exe (PID: 948)
INFO
Application launched itself
- chrome.exe (PID: 2564)
- msiexec.exe (PID: 1732)
- chrome.exe (PID: 2360)
- firefox.exe (PID: 984)
- firefox.exe (PID: 3700)
Reads the hosts file
- chrome.exe (PID: 2564)
- chrome.exe (PID: 1044)
Reads Internet Cache Settings
- chrome.exe (PID: 2564)
- firefox.exe (PID: 3700)
Creates a software uninstall entry
- msiexec.exe (PID: 1732)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2796)
Reads CPU info
- firefox.exe (PID: 3700)
Creates files in the user directory
- firefox.exe (PID: 3700)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
82
Monitored processes
45
Malicious processes
11
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 948 | "C:\Users\admin\AppData\Local\Microsoft\BingWallpaperApp\BingWallpaperApp.exe" | C:\Users\admin\AppData\Local\Microsoft\BingWallpaperApp\BingWallpaperApp.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Bing Wallpaper Exit code: 0 Version: 1.0.7.7 Modules
| |||||||||||||||
| 984 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://go.microsoft.com/fwlink/?linkid=2120579&partnerCode=W011&machineID=6FEE334A56564CC296AF9861B82ECB69&mkt=en-us | C:\Program Files\Mozilla Firefox\firefox.exe | — | DefaultSetup.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 68.0.1 Modules
| |||||||||||||||
| 1044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,17651025050428408322,13771355512206763069,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=11053342524616910759 --mojo-platform-channel-handle=1504 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,17651025050428408322,13771355512206763069,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2616763380540078775 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4456 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1516 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,17651025050428408322,13771355512206763069,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=4096575710756402005 --mojo-platform-channel-handle=3272 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1532 | "C:\Windows\System32\msiexec.exe" /q /i BWCInstaller.msi /norestart | C:\Windows\System32\msiexec.exe | — | BWInstaller.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1712 | rundll32.exe "C:\Windows\Installer\MSI4C5E.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_3034953 1 CustomActions!CustomActions.CustomActions.InstallPing | C:\Windows\system32\rundll32.exe | MsiExec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1732 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1736 | "C:\Users\admin\AppData\Local\Temp\IXP000.TMP\BWInstaller.exe" | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\BWInstaller.exe | StartupInstaller.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: BWInstaller Exit code: 0 Version: 1.0.7.7 Modules
| |||||||||||||||
| 1756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,17651025050428408322,13771355512206763069,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6580669353408273982 --mojo-platform-channel-handle=3460 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 426
Read events
2 042
Write events
365
Delete events
19
Modification events
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3552) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2564-13246548860090500 |
Value: 259 | |||
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2564) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
25
Suspicious files
109
Text files
231
Unknown types
51
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F7DBA7C-A04.pma | — | |
MD5:— | SHA256:— | |||
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\182ee15d-f16d-4eb8-ac8b-7f620b81eb3f.tmp | — | |
MD5:— | SHA256:— | |||
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF2d40c7.TMP | text | |
MD5:— | SHA256:— | |||
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF2d40c7.TMP | text | |
MD5:— | SHA256:— | |||
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF2d4105.TMP | text | |
MD5:— | SHA256:— | |||
| 2564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
71
DNS requests
105
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1712 | rundll32.exe | GET | — | 20.41.62.11:80 | http://g.ceipmsn.com/8SE/44?MI=6FEE334A56564CC296AF9861B82ECB69&LV=6.1.7600.16385&OS=6.1.7601.1&TE=40&TV=isW011%7cpkBingWallpaper%7ctmen-us%7cvr1.0.7.7%7cat1%7crt1%7cpt2 | US | — | — | suspicious |
4072 | DefaultSetup.exe | GET | — | 20.41.62.11:80 | http://g.ceipmsn.com/8SE/44?MI=6FEE334A56564CC296AF9861B82ECB69&LV=1.7.73.0&OS=6.1.7601.1&TE=24&TV=isW011%7cpkBrowserDefMgr%7crt1%7ctmen-us%7chdGC75.0.3770.100%2c1%7csdGC75.0.3770.100%2c1%7cseGC75.0.3770.100%2c1%7chpGC75.0.3770.100%2c1%7ccd2020-10-07%7cct12:55:56:168 | US | — | — | suspicious |
4072 | DefaultSetup.exe | GET | 200 | 20.41.62.11:80 | http://g.ceipmsn.com/8SE/44?MI=6FEE334A56564CC296AF9861B82ECB69&LV=1.7.73.0&OS=6.1.7601.1&TE=23&TV=isW011%7cpkBrowserDefMgr%7crt1%7ctmen-us%7chdMF68.0.0.0%2c1%7csdMF68.0.0.0%2c1%7cseMF68.0.0.0%2c1%7chpMF68.0.0.0%2c1%7ccd2020-10-07%7cct12:55:56:168 | US | — | — | suspicious |
1044 | chrome.exe | GET | 200 | 20.41.62.11:80 | http://g.ceipmsn.com/8SE/44?MI=6FEE334A56564CC296AF9861B82ECB69&LV=0.0.0.6&OS=WindowsNT6.1&TE=37&TV=isW011%7CpkBingHomepageandSearchEngine%7Ctmen-US%7CbvChrome75.0.3770.100%7Cexicempppimphheennghpecpkheibidefo%7Ces1 | US | — | — | suspicious |
4072 | DefaultSetup.exe | GET | 200 | 20.41.62.11:80 | http://g.ceipmsn.com/8SE/44?MI=6FEE334A56564CC296AF9861B82ECB69&LV=1.7.73.0&OS=6.1.7601.1&TE=24&TV=isW011%7cpkBrowserDefMgr%7crt1%7ctmen-us%7chdGC75.0.3770.100%2c1%7csdGC75.0.3770.100%2c1%7cseGC75.0.3770.100%2c1%7chpGC75.0.3770.100%2c1%7ccd2020-10-07%7cct12:55:56:168 | US | — | — | suspicious |
3700 | firefox.exe | GET | — | 20.41.62.11:80 | http://g.ceipmsn.com/8SE/44?MI=92BC5C46956A00B756C6574B36687B03&LV=0.0.0.6&OS=WindowsNT6.1;rv:68.0&TE=37&TV=isW011%7CpkBingSearchEngine%7Ctmen-US%7CbvFirefox68.0%7Cexbingwallpaperdse@microsoft.com%7Ces1 | US | — | — | suspicious |
3700 | firefox.exe | GET | 200 | 20.41.62.11:80 | http://g.ceipmsn.com/8SE/44?MI=92BC5C46956A00B756C6574B36687B03&LV=0.0.0.6&OS=WindowsNT6.1;rv:68.0&TE=37&TV=isW011%7CpkBingSearchEngine%7Ctmen-US%7CbvFirefox68.0%7Cexbingwallpaperdse@microsoft.com%7Ces1 | US | — | — | suspicious |
4072 | DefaultSetup.exe | GET | 200 | 20.41.62.11:80 | http://g.ceipmsn.com/8SE/44?MI=6FEE334A56564CC296AF9861B82ECB69&LV=1.7.73.0&OS=6.1.7601.1&TE=25&TV=isW011%7cpkBrowserDefMgr%7crt1%7ctmen-us%7chdIE11.0.9600.17843%2c0%7csdIE11.0.9600.17843%2c0%7cse%7chp%7ccd2020-10-07%7cct12:55:56:168 | US | — | — | suspicious |
3700 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3700 | firefox.exe | POST | 200 | 104.18.24.243:80 | http://ocsp.msocsp.com/ | US | der | 1.75 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1044 | chrome.exe | 172.217.22.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1044 | chrome.exe | 92.123.16.55:443 | go.microsoft.com | Telia Company AB | FR | malicious |
1044 | chrome.exe | 172.217.16.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1044 | chrome.exe | 172.217.21.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
1044 | chrome.exe | 2.21.38.54:443 | www.microsoft.com | GTT Communications Inc. | FR | malicious |
1044 | chrome.exe | 13.107.246.10:443 | wcpstatic.microsoft.com | Microsoft Corporation | US | whitelisted |
1044 | chrome.exe | 172.217.22.14:443 | clients2.google.com | Google Inc. | US | whitelisted |
1044 | chrome.exe | 52.173.134.115:443 | bingwallpaper.microsoft.com | Microsoft Corporation | US | unknown |
— | — | 216.58.207.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1044 | chrome.exe | 104.108.144.114:443 | download.microsoft.com | TOT Public Company Limited | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
accounts.google.com |
| shared |
safebrowsing.googleapis.com |
| whitelisted |
wcpstatic.microsoft.com |
| whitelisted |
img-prod-cms-rt-microsoft-com.akamaized.net |
| whitelisted |
web.vortex.data.microsoft.com |
| whitelisted |
c.s-microsoft.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1052 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |