| File name: | download |
| Full analysis: | https://app.any.run/tasks/d1d7f1c7-3467-47e4-b141-4c3ee25ce718 |
| Verdict: | Malicious activity |
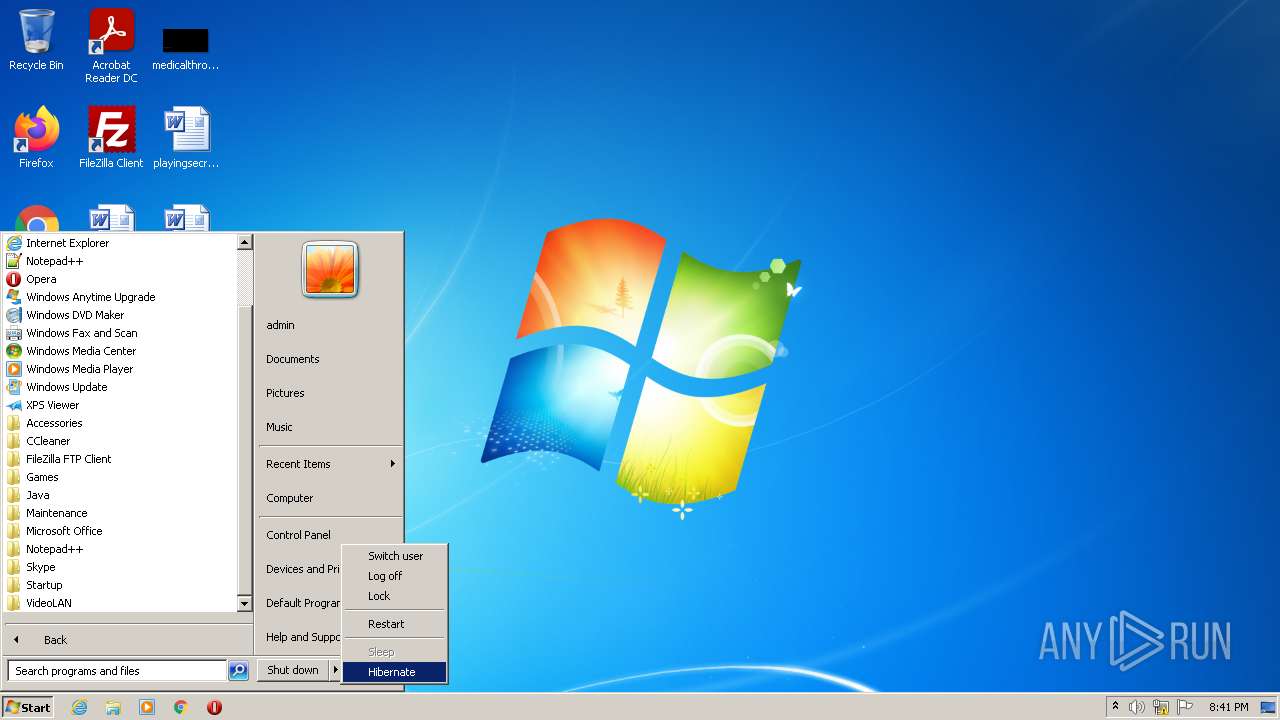
| Analysis date: | May 20, 2022, 19:41:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 55B8CD36E44B25C09DEA14962C8C7F6D |
| SHA1: | 59E79003E9622FFFD9713226809DB5FC8283E5F0 |
| SHA256: | F9070B1B18BC47B2960A64F9DAB234FE20D180F06A1FB0013D7E98A8A206E601 |
| SSDEEP: | 12288:bhKOW0MHT4SKhW3sow9Umm94rgUHyYfGxDg2pRMWgTD1MdjSY:bkpT4SKhW3Fw9Uf4E4fGiIng/6YY |
MALICIOUS
Drops executable file immediately after starts
- WinRAR.exe (PID: 2088)
- LogoManager 1.4.exe (PID: 1592)
- LogoManager 1.4.exe (PID: 1008)
- LogoManager 1.4.tmp (PID: 3744)
- 7za.exe (PID: 2524)
Application was dropped or rewritten from another process
- LogoManager 1.4.exe (PID: 1592)
- LogoManager 1.4.exe (PID: 1008)
- sitool.exe (PID: 616)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3228)
- schtasks.exe (PID: 3340)
Uses Task Scheduler to run other applications
- sitool.exe (PID: 616)
SUSPICIOUS
Reads the computer name
- WinRAR.exe (PID: 2088)
- LogoManager 1.4.tmp (PID: 2056)
- LogoManager 1.4.tmp (PID: 3744)
- sitool.exe (PID: 616)
Checks supported languages
- WinRAR.exe (PID: 2088)
- LogoManager 1.4.exe (PID: 1592)
- LogoManager 1.4.tmp (PID: 2056)
- LogoManager 1.4.exe (PID: 1008)
- LogoManager 1.4.tmp (PID: 3744)
- 7za.exe (PID: 3284)
- sitool.exe (PID: 616)
- 7za.exe (PID: 2524)
- 7za.exe (PID: 1916)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2088)
- LogoManager 1.4.exe (PID: 1592)
- LogoManager 1.4.exe (PID: 1008)
- LogoManager 1.4.tmp (PID: 3744)
- 7za.exe (PID: 2524)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 2088)
- LogoManager 1.4.exe (PID: 1592)
- LogoManager 1.4.exe (PID: 1008)
- LogoManager 1.4.tmp (PID: 3744)
- 7za.exe (PID: 2524)
Reads Windows owner or organization settings
- LogoManager 1.4.tmp (PID: 3744)
Reads the Windows organization settings
- LogoManager 1.4.tmp (PID: 3744)
Creates files in the user directory
- LogoManager 1.4.tmp (PID: 3744)
- sitool.exe (PID: 616)
Executed via COM
- explorer.exe (PID: 2132)
INFO
Application was dropped or rewritten from another process
- LogoManager 1.4.tmp (PID: 2056)
- LogoManager 1.4.tmp (PID: 3744)
- 7za.exe (PID: 3284)
- 7za.exe (PID: 2524)
- 7za.exe (PID: 1916)
Checks supported languages
- schtasks.exe (PID: 3228)
- schtasks.exe (PID: 3340)
- explorer.exe (PID: 1348)
- explorer.exe (PID: 2132)
Reads the computer name
- explorer.exe (PID: 2132)
- schtasks.exe (PID: 3340)
- explorer.exe (PID: 1348)
- schtasks.exe (PID: 3228)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
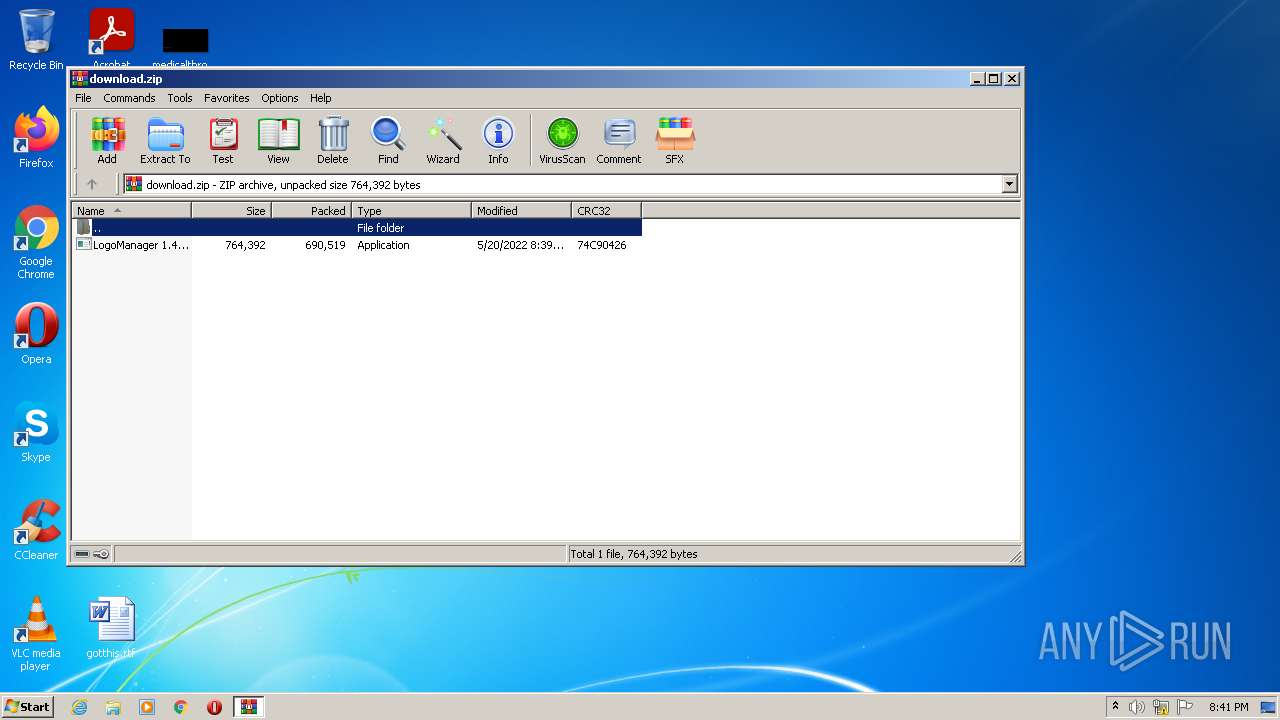
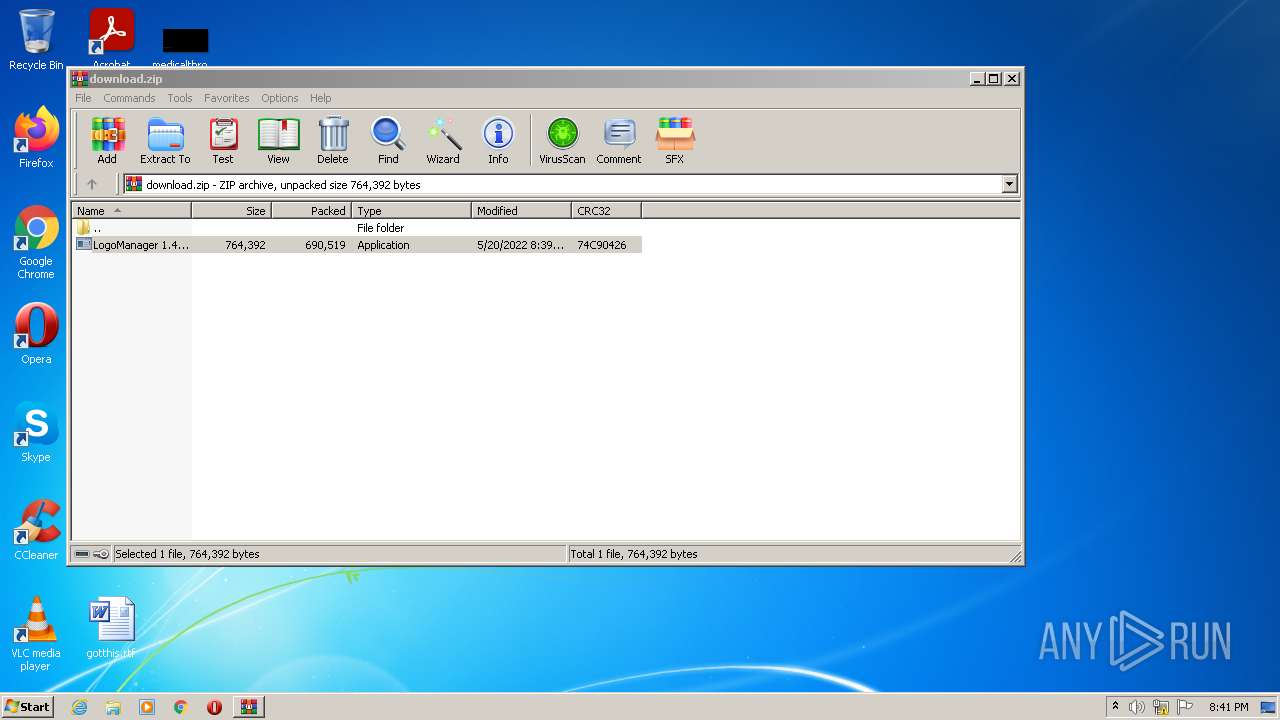
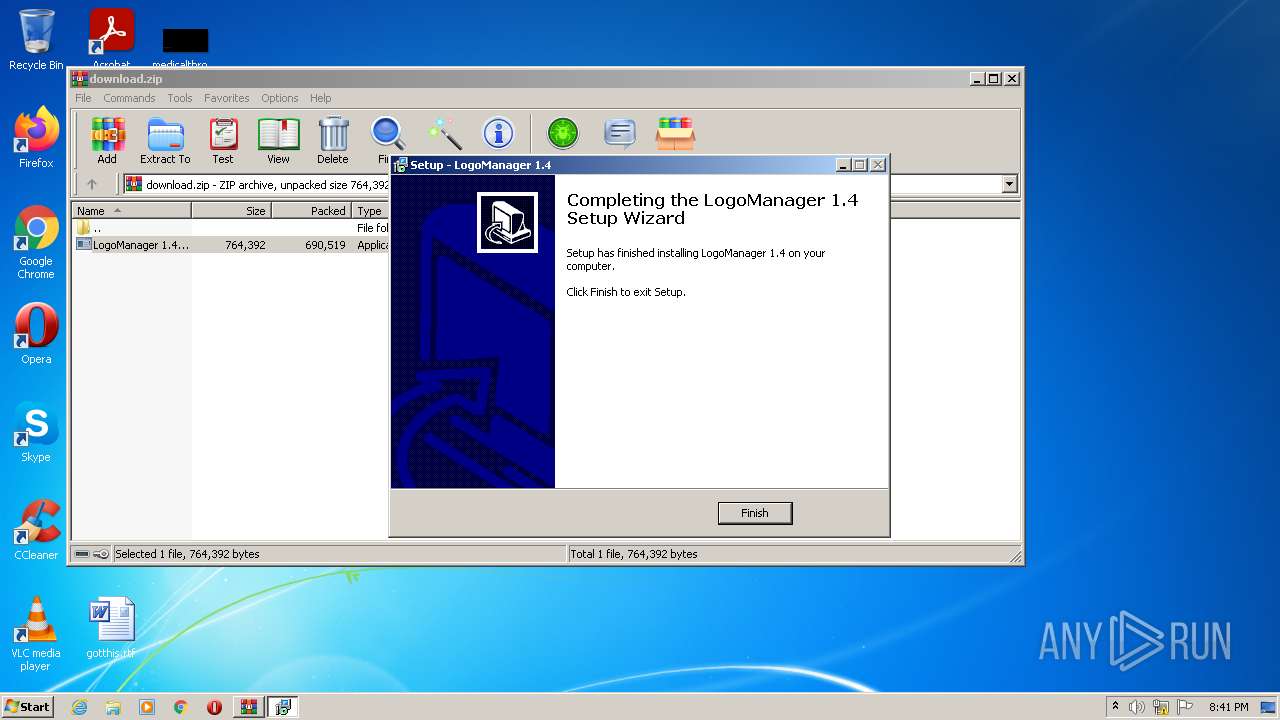
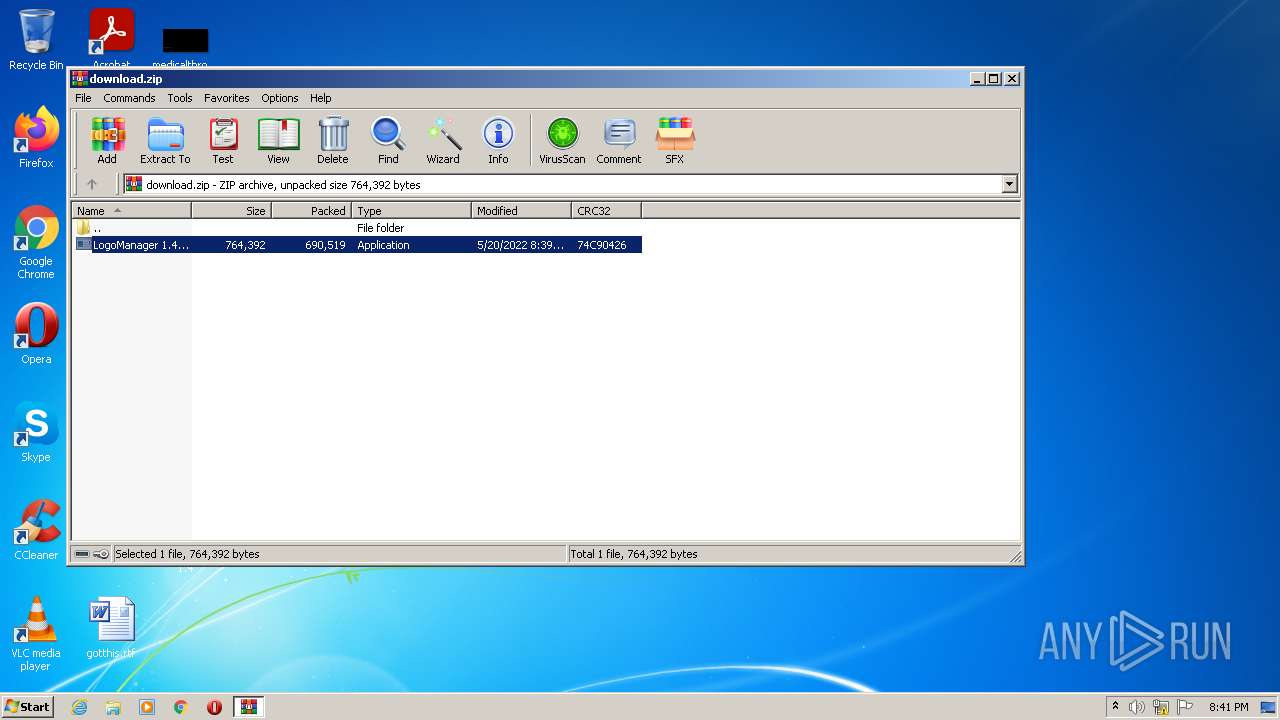
| ZipFileName: | LogoManager 1.4.exe |
|---|---|
| ZipUncompressedSize: | 764392 |
| ZipCompressedSize: | 690519 |
| ZipCRC: | 0x74c90426 |
| ZipModifyDate: | 2022:05:20 22:39:16 |
| ZipCompression: | Deflated |
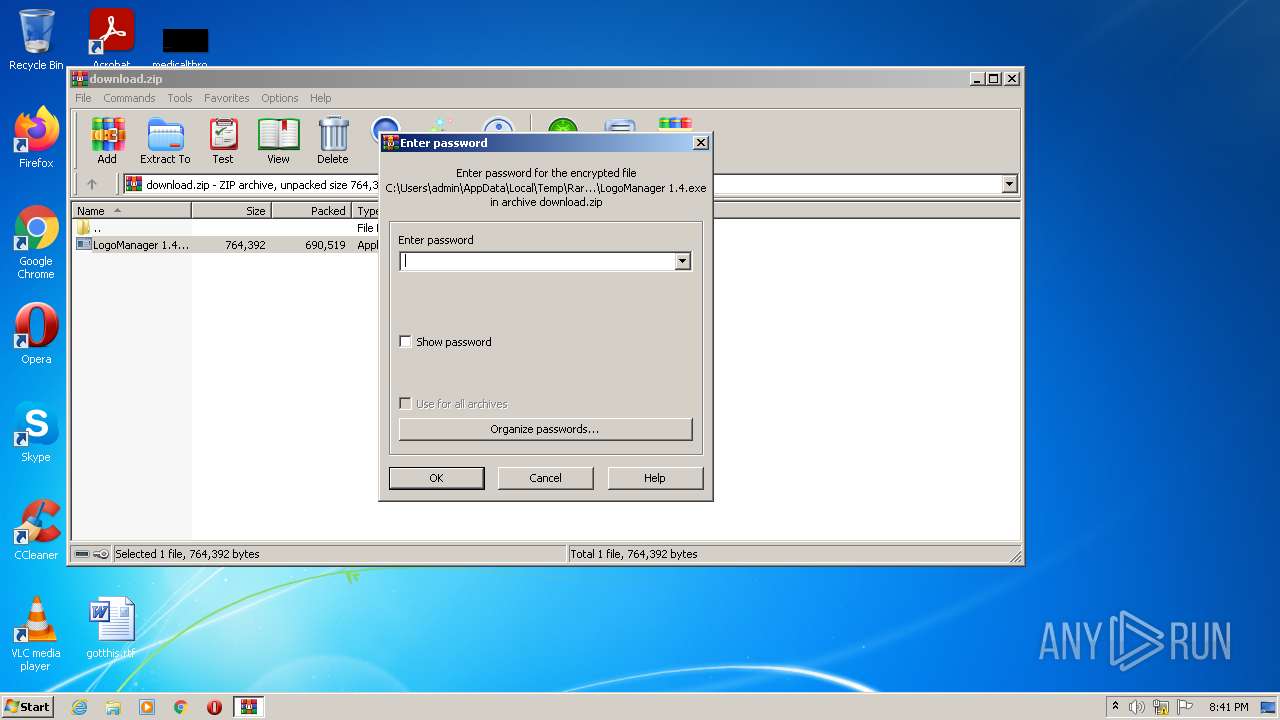
| ZipBitFlag: | 0x0001 |
| ZipRequiredVersion: | 20 |
Total processes
55
Monitored processes
13
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | "C:\Users\admin\AppData\Roaming\SysInfoTool\sitool.exe" -cr -tu 7 | C:\Users\admin\AppData\Roaming\SysInfoTool\sitool.exe | — | LogoManager 1.4.tmp | |||||||||||
User: admin Integrity Level: HIGH Description: SystemInfo Host Client Exit code: 0 Version: 2.0.160.182 Modules
| |||||||||||||||
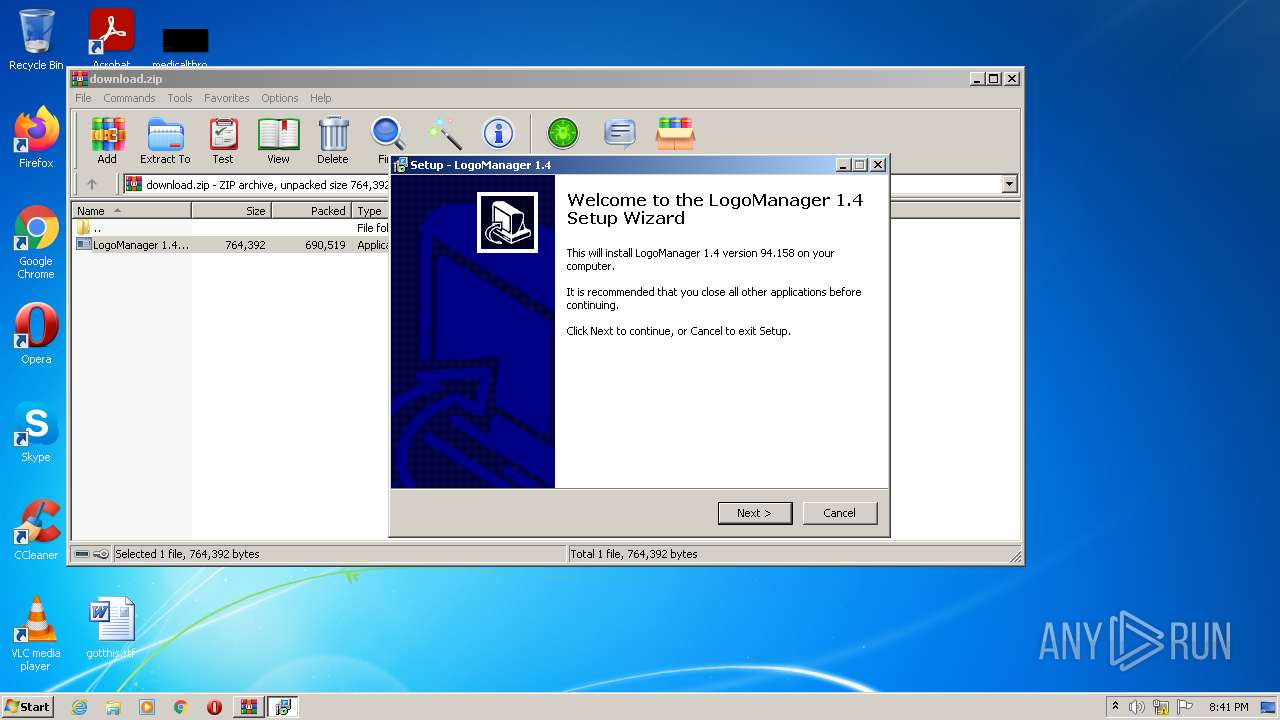
| 1008 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb2088.34041\LogoManager 1.4.exe" /SPAWNWND=$20178 /NOTIFYWND=$4015A | C:\Users\admin\AppData\Local\Temp\Rar$EXb2088.34041\LogoManager 1.4.exe | LogoManager 1.4.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Exit code: 0 Version: 94.158 Modules
| |||||||||||||||
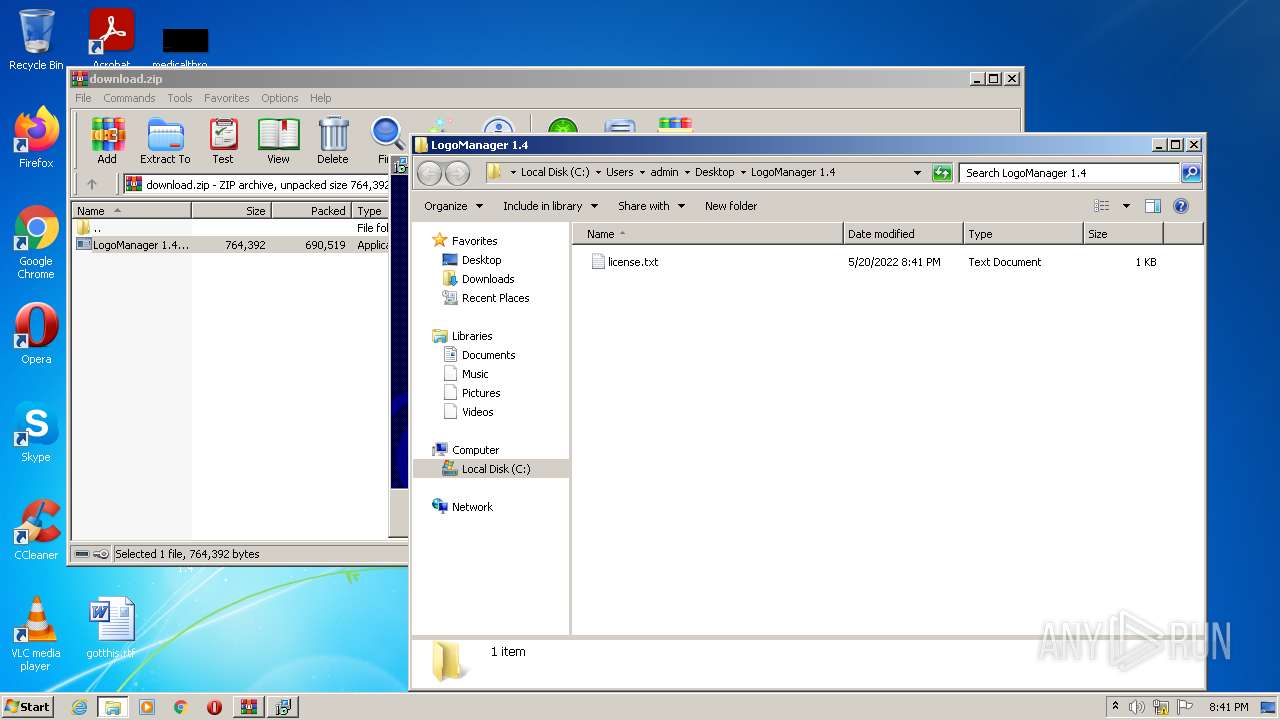
| 1348 | "explorer.exe" "C:\Users\admin\Desktop\LogoManager 1.4" | C:\Windows\explorer.exe | — | LogoManager 1.4.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1592 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb2088.34041\LogoManager 1.4.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb2088.34041\LogoManager 1.4.exe | WinRAR.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Exit code: 0 Version: 94.158 Modules
| |||||||||||||||
| 1916 | "C:\Users\admin\AppData\Local\Temp\is-LU7QL.tmp\7za.exe" x "C:\Users\admin\AppData\Local\Temp\is-LU7QL.tmp\misc.res" -p"dRm-b1gig@n_vd" | C:\Users\admin\AppData\Local\Temp\is-LU7QL.tmp\7za.exe | — | LogoManager 1.4.tmp | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Standalone Console Exit code: 0 Version: 4.65 Modules
| |||||||||||||||
| 2056 | "C:\Users\admin\AppData\Local\Temp\is-UQ873.tmp\LogoManager 1.4.tmp" /SL5="$4015A,373986,121344,C:\Users\admin\AppData\Local\Temp\Rar$EXb2088.34041\LogoManager 1.4.exe" | C:\Users\admin\AppData\Local\Temp\is-UQ873.tmp\LogoManager 1.4.tmp | — | LogoManager 1.4.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2088 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\download.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2132 | C:\Windows\explorer.exe /factory,{75dff2b7-6936-4c06-a8bb-676a7b00b24b} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1073807364 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2524 | "C:\Users\admin\AppData\Local\Temp\is-LU7QL.tmp\7za.exe" x "C:\Users\admin\AppData\Local\Temp\is-LU7QL.tmp\form.res" -p"dRm-b1gig@n_vd" | C:\Users\admin\AppData\Local\Temp\is-LU7QL.tmp\7za.exe | LogoManager 1.4.tmp | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Standalone Console Exit code: 0 Version: 4.65 Modules
| |||||||||||||||
| 3228 | "C:\Windows\system32\schtasks.exe" /Delete /tn "Microsoft\Windows\Windows Error Reporting\SystemInfo" /f | C:\Windows\system32\schtasks.exe | — | sitool.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 595
Read events
4 499
Write events
92
Delete events
4
Modification events
| (PID) Process: | (2088) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2088) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2088) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2088) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2088) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2088) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\download.zip | |||
| (PID) Process: | (2088) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2088) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2088) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2088) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
6
Suspicious files
3
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3744 | LogoManager 1.4.tmp | C:\Users\admin\AppData\Local\Temp\{6594A004-5923-45CF-B69C-A2A6EF0BF3A4}\is-F9GPB.tmp | — | |
MD5:— | SHA256:— | |||
| 3744 | LogoManager 1.4.tmp | C:\Users\admin\AppData\Local\Temp\{6594A004-5923-45CF-B69C-A2A6EF0BF3A4}\license.txt | — | |
MD5:— | SHA256:— | |||
| 2088 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb2088.34041\LogoManager 1.4.exe | executable | |
MD5:— | SHA256:— | |||
| 3744 | LogoManager 1.4.tmp | C:\Users\admin\AppData\Roaming\SysInfoTool\sitool.exe | executable | |
MD5:— | SHA256:— | |||
| 3744 | LogoManager 1.4.tmp | C:\Users\admin\Desktop\LogoManager 1.4\license.txt | text | |
MD5:— | SHA256:— | |||
| 3744 | LogoManager 1.4.tmp | C:\Users\admin\AppData\Local\Temp\is-LU7QL.tmp\form.res | compressed | |
MD5:— | SHA256:— | |||
| 2524 | 7za.exe | C:\Users\admin\AppData\Local\Temp\is-LU7QL.tmp\form.exe | executable | |
MD5:— | SHA256:— | |||
| 3744 | LogoManager 1.4.tmp | C:\Users\admin\AppData\Local\Temp\is-LU7QL.tmp\7za.exe | executable | |
MD5:E92604E043F51C604B6D1AC3BCD3A202 | SHA256:FA252E501332B7486A972E7E471CF6915DAA681AF35C6AA102213921093EB2A3 | |||
| 3744 | LogoManager 1.4.tmp | C:\Users\admin\AppData\Local\Temp\is-LU7QL.tmp\sub.res | compressed | |
MD5:8D73039C2CB9F36A357144A3129F272D | SHA256:6DAD5E75288D348E73D13FE8454C71700C56790CC067ACBDDA839759BD5E7C3B | |||
| 3284 | 7za.exe | C:\Users\admin\AppData\Local\Temp\is-LU7QL.tmp\sub.xml | xml | |
MD5:C047508A4A1F583B7ED31EC7B0DF9695 | SHA256:CD999BAA036D44D442FE43A541D69F04BA206C58938F3C22EC0F226493C63E35 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
2
DNS requests
2
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3744 | LogoManager 1.4.tmp | POST | 200 | 142.250.185.206:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
3744 | LogoManager 1.4.tmp | GET | 200 | 188.114.97.10:80 | http://video-box.org/getchannel | US | binary | 1 b | malicious |
3744 | LogoManager 1.4.tmp | POST | 200 | 142.250.185.206:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3744 | LogoManager 1.4.tmp | 142.250.185.206:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
3744 | LogoManager 1.4.tmp | 188.114.97.10:80 | video-box.org | Cloudflare Inc | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google-analytics.com |
| whitelisted |
video-box.org |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3744 | LogoManager 1.4.tmp | Unknown Traffic | ET INFO Suspicious User-Agent (1 space) |
1 ETPRO signatures available at the full report