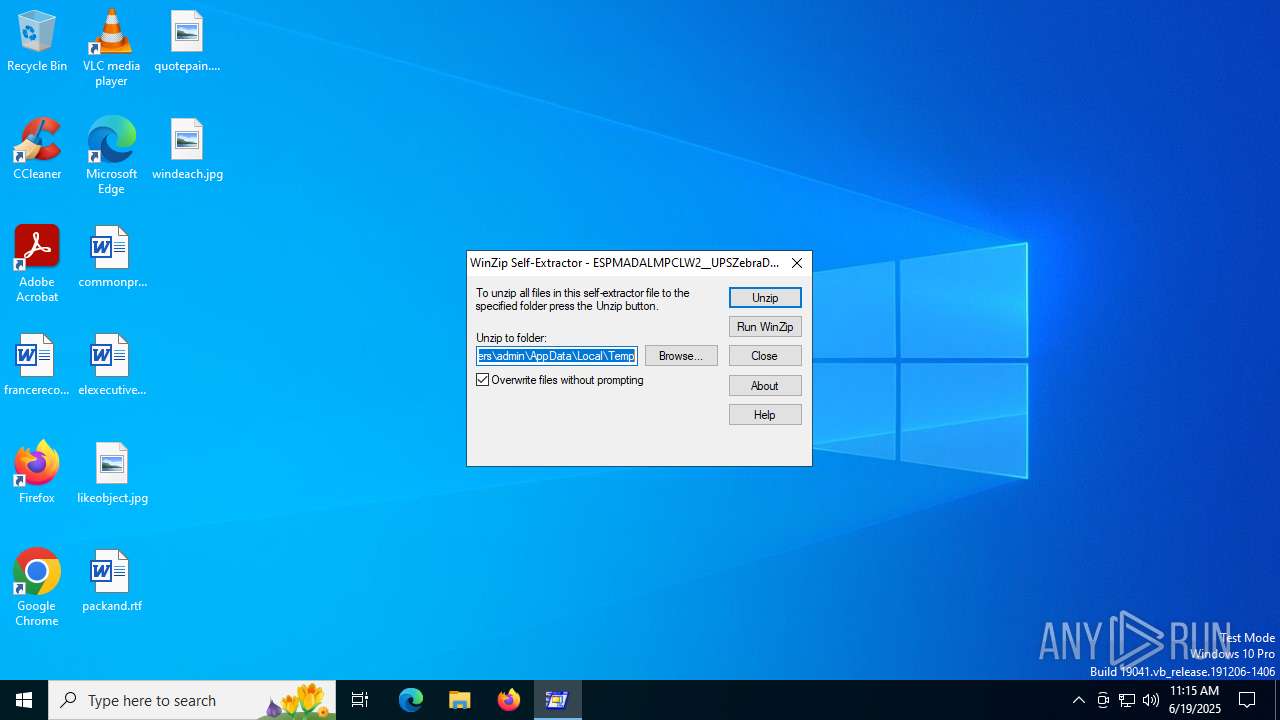
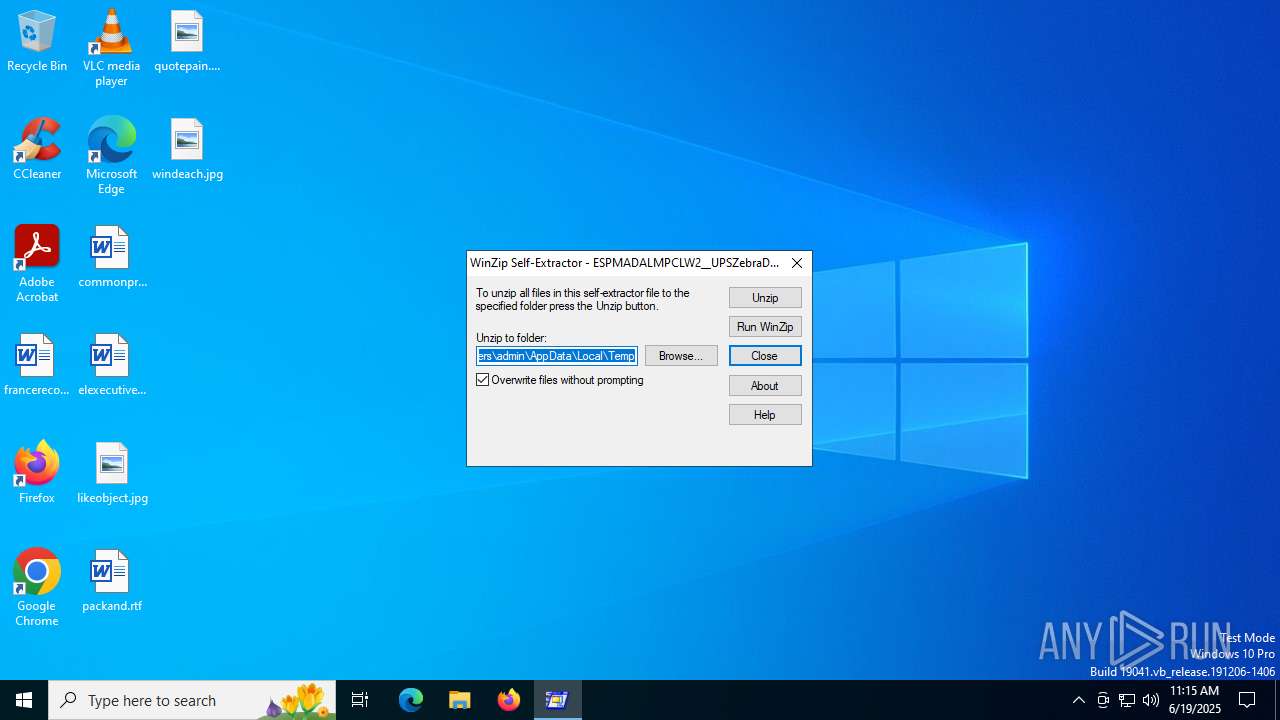
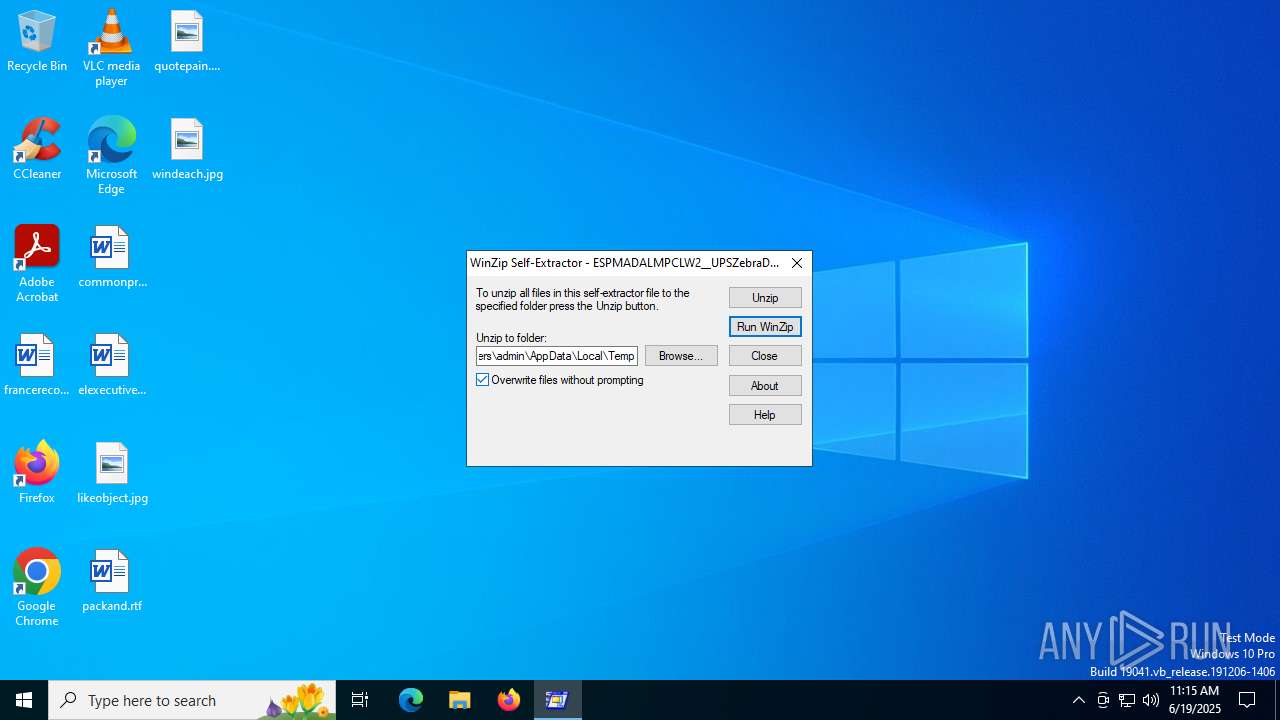
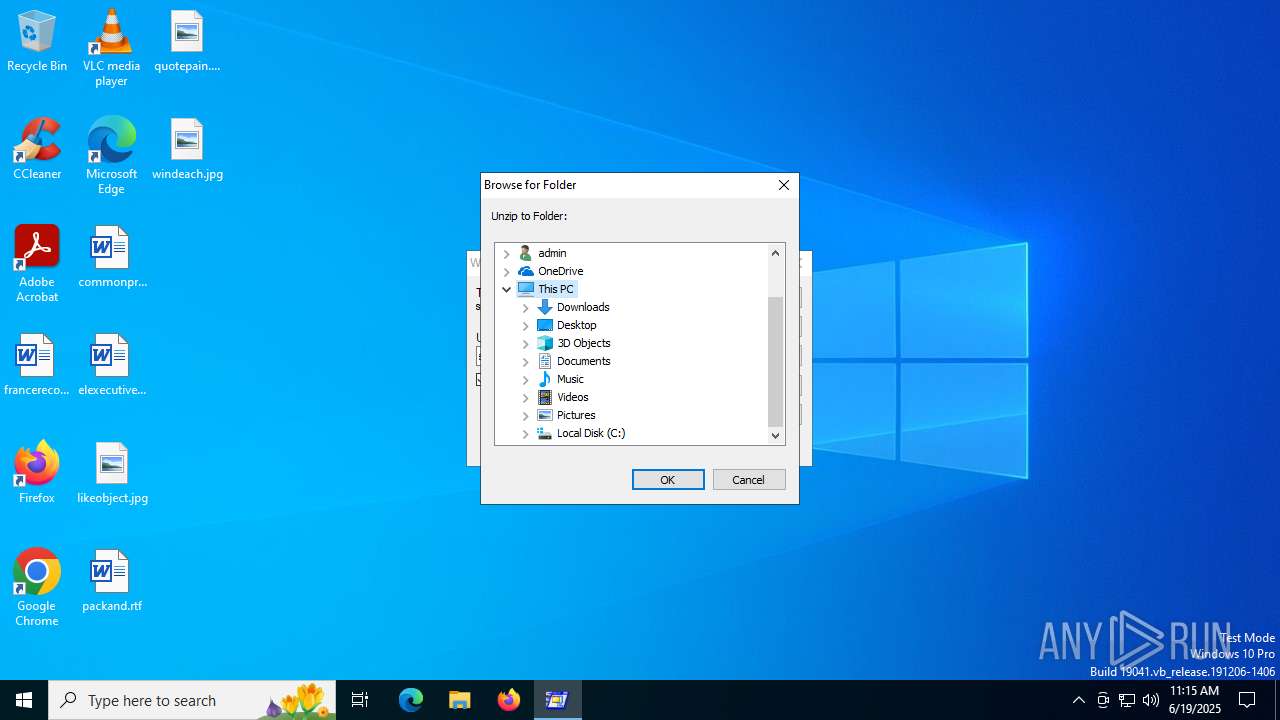
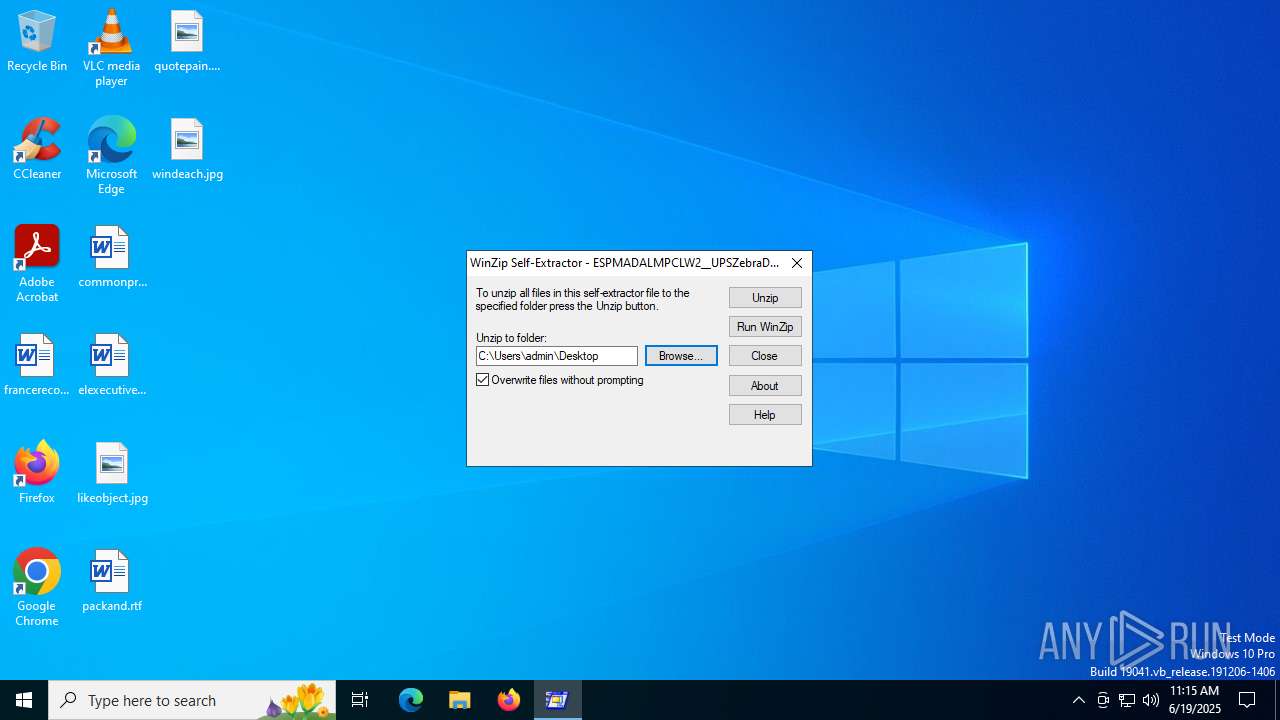
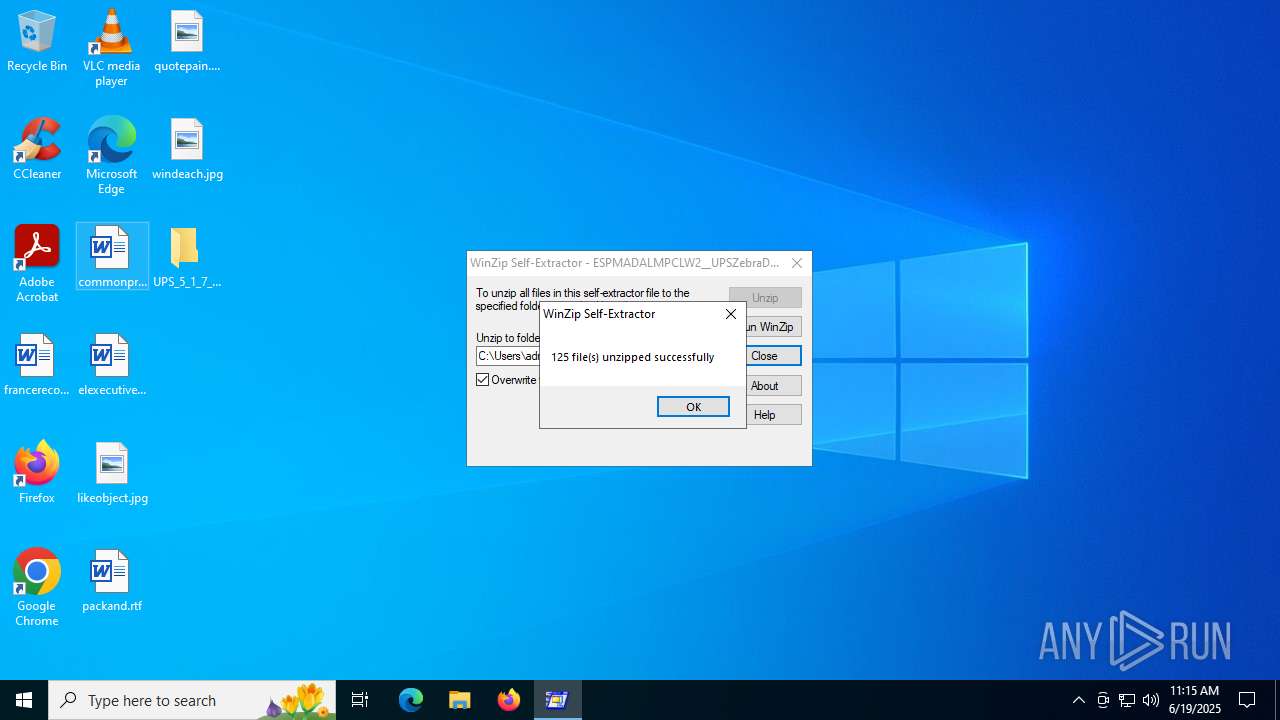
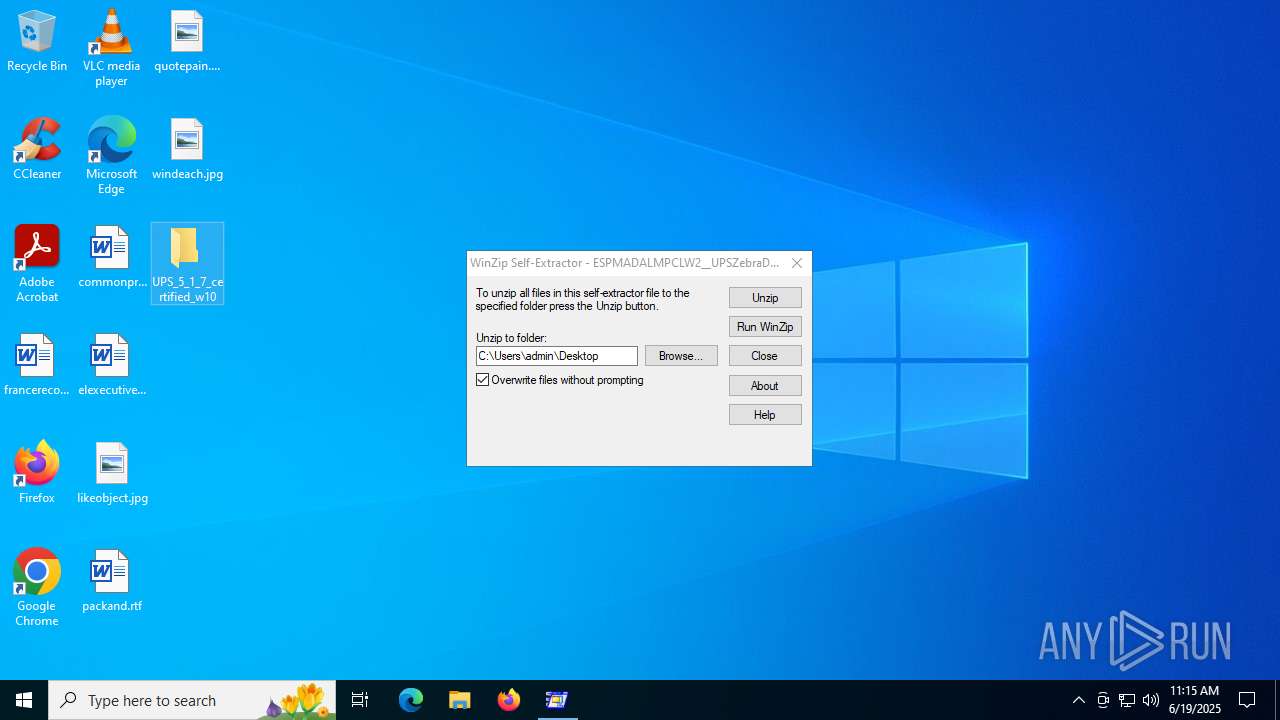
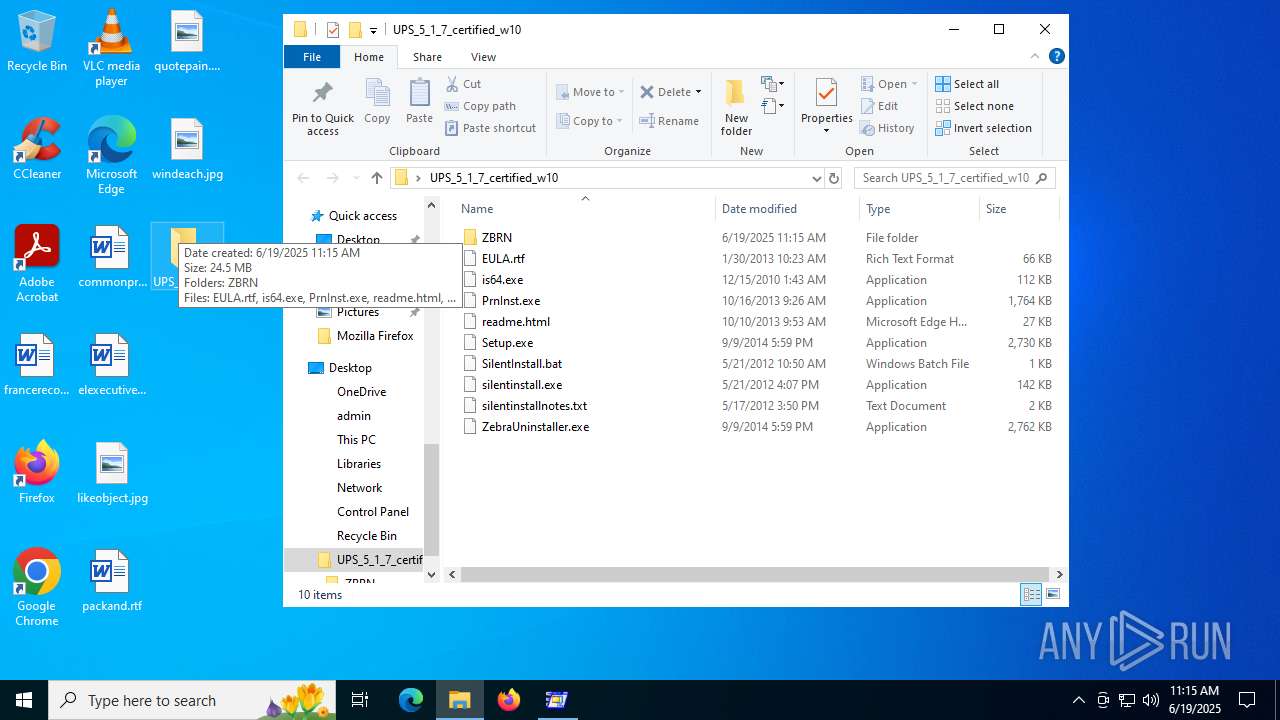
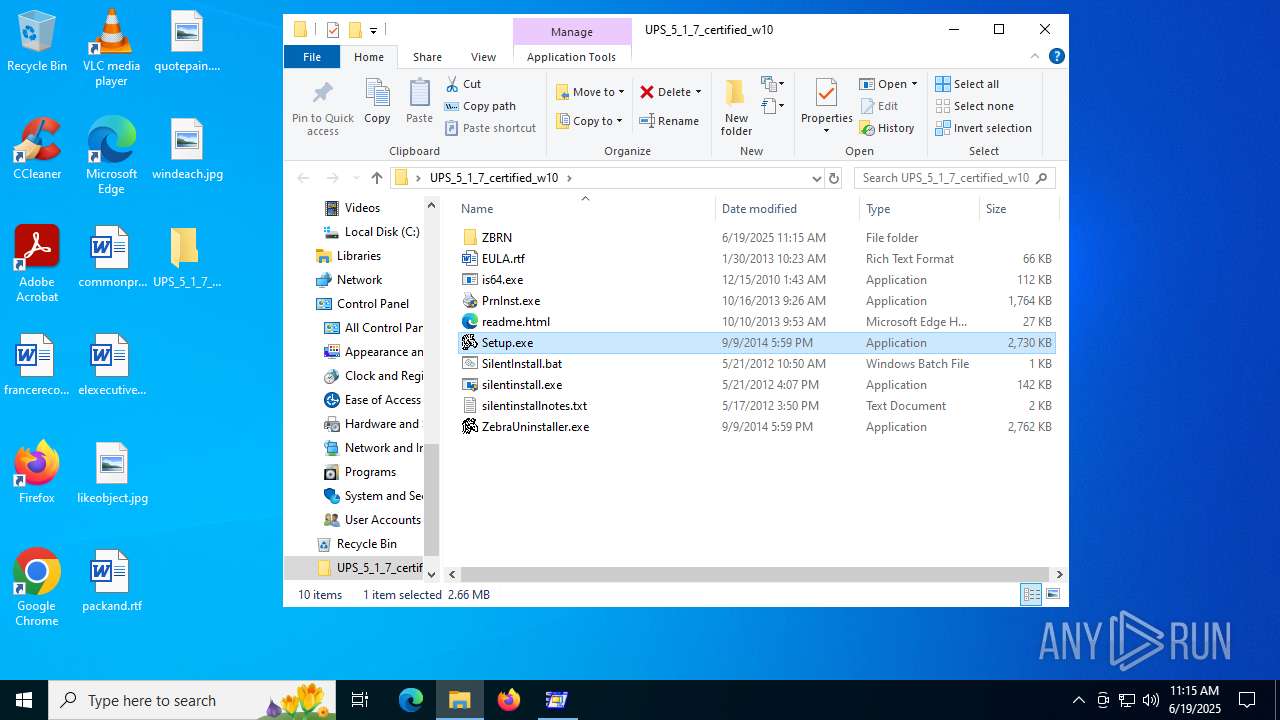
| File name: | ESPMADALMPCLW2__UPSZebraDriver__c4198da1d17e013b99784df31fbf7d1d7e97b865.exe |
| Full analysis: | https://app.any.run/tasks/ec73e9f9-586b-4c30-ba7a-6183e92ed3b6 |
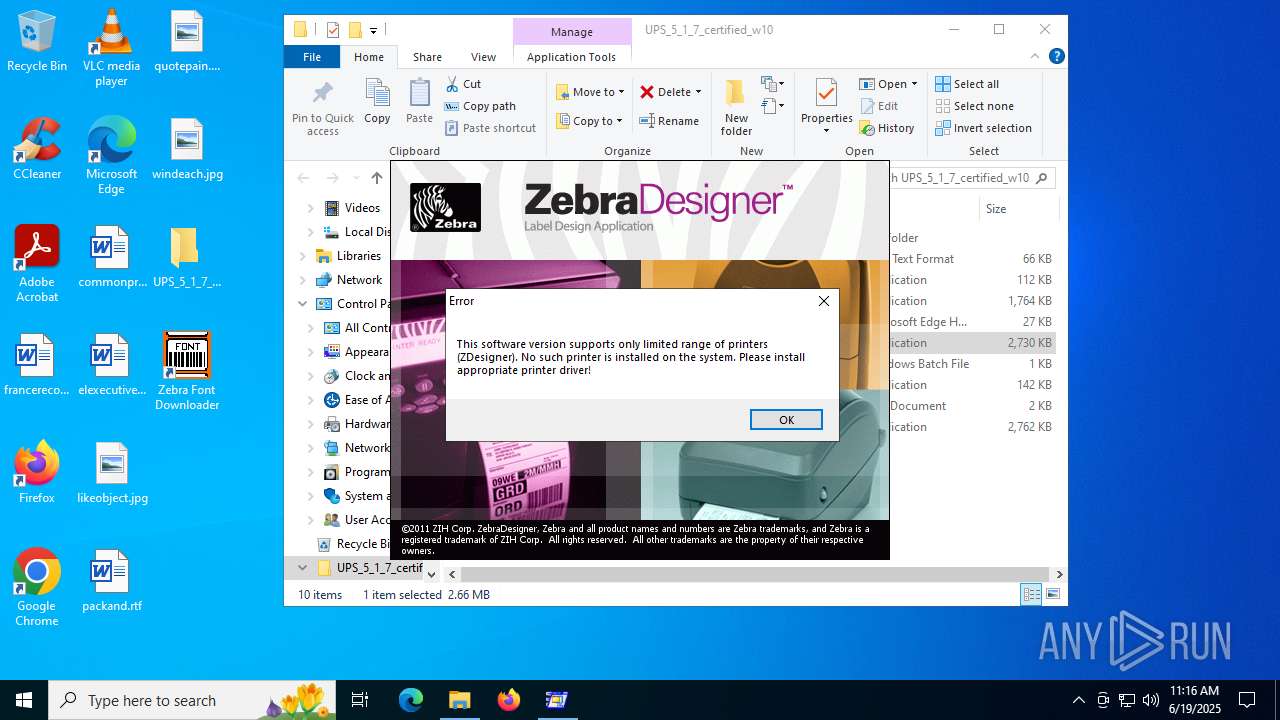
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2025, 11:15:06 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | C1FEA9D4CEE53F4D7B094AEF4EBBF8DD |
| SHA1: | C4198DA1D17E013B99784DF31FBF7D1D7E97B865 |
| SHA256: | F9049AAC4336EE2AE89A25EFA6EBAA88A759BFE1FB36A30952832C67B0E9CE4A |
| SSDEEP: | 98304:02brBxEoZwUPnOtDCeDJKLfsINRV9tct07RX1VS5PYNnfJ9SJ9uyOHT+PEL1EgwU:iKzutQ5pHzc0RMWzkg |
MALICIOUS
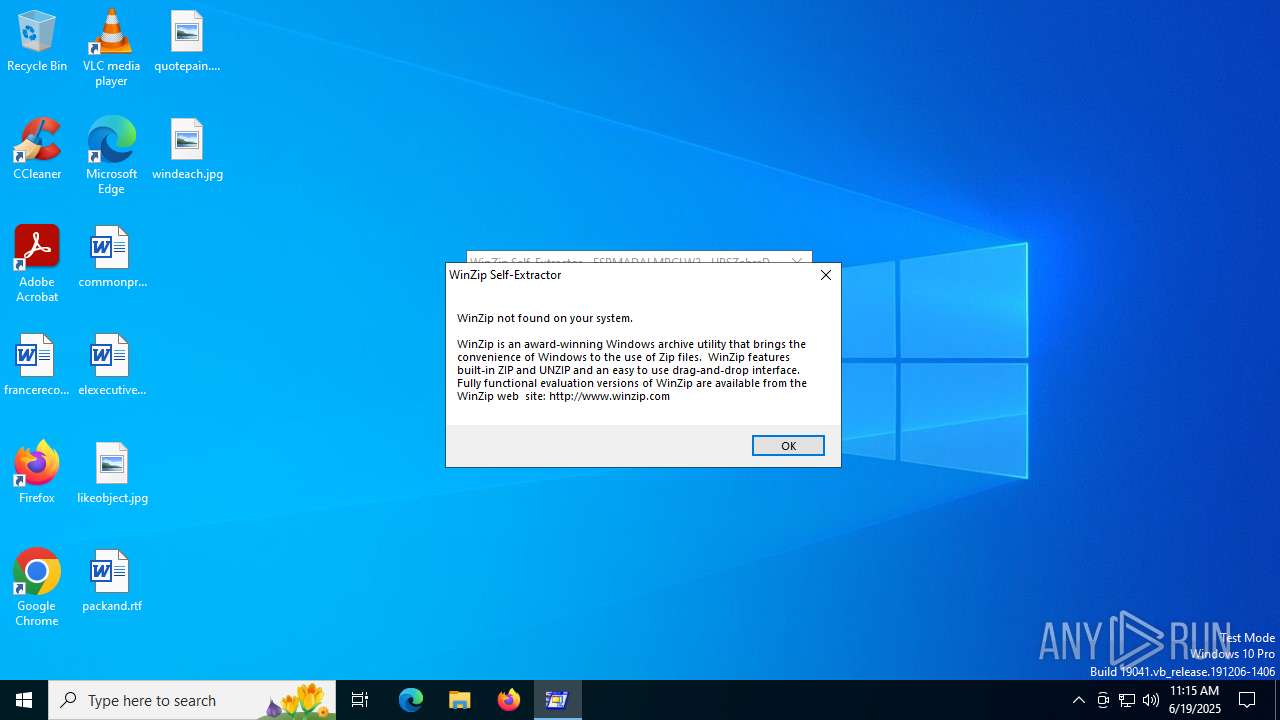
Executing a file with an untrusted certificate
- Setup.exe (PID: 1816)
- PrnInst.exe (PID: 592)
- PrnInst.exe (PID: 3980)
- ZebraFD.exe (PID: 6656)
SUSPICIOUS
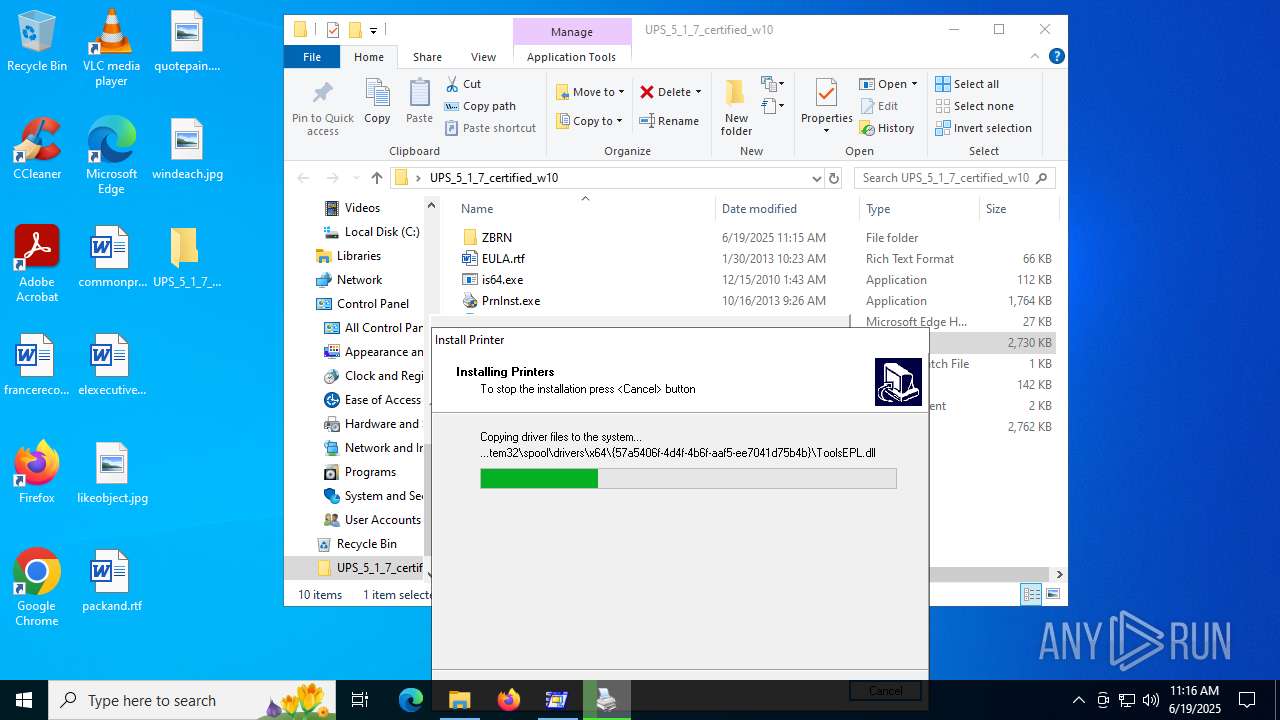
Process drops legitimate windows executable
- ESPMADALMPCLW2__UPSZebraDriver__c4198da1d17e013b99784df31fbf7d1d7e97b865.exe (PID: 3752)
- is-C2RN5.tmp (PID: 6636)
Executable content was dropped or overwritten
- ESPMADALMPCLW2__UPSZebraDriver__c4198da1d17e013b99784df31fbf7d1d7e97b865.exe (PID: 3752)
- PrnInst.exe (PID: 592)
- drvinst.exe (PID: 1964)
- spoolsv.exe (PID: 2324)
- ZebraFD.exe (PID: 6656)
- is-C2RN5.tmp (PID: 6636)
Reads security settings of Internet Explorer
- Setup.exe (PID: 1816)
Creates files in the driver directory
- drvinst.exe (PID: 1964)
Starts application with an unusual extension
- PrnInst.exe (PID: 592)
There is functionality for taking screenshot (YARA)
- PrnInst.exe (PID: 592)
Executes as Windows Service
- spoolsv.exe (PID: 2324)
- spoolsv.exe (PID: 7060)
Creates/Modifies COM task schedule object
- is-C2RN5.tmp (PID: 6636)
INFO
Reads the computer name
- ESPMADALMPCLW2__UPSZebraDriver__c4198da1d17e013b99784df31fbf7d1d7e97b865.exe (PID: 3752)
- Setup.exe (PID: 1816)
- PrnInst.exe (PID: 592)
- drvinst.exe (PID: 1964)
- Prn64.bin (PID: 3720)
- Prn64.bin (PID: 5560)
- is-C2RN5.tmp (PID: 6636)
- ZDDownloader2.exe (PID: 6956)
- identity_helper.exe (PID: 3048)
Checks supported languages
- ESPMADALMPCLW2__UPSZebraDriver__c4198da1d17e013b99784df31fbf7d1d7e97b865.exe (PID: 3752)
- Setup.exe (PID: 1816)
- PrnInst.exe (PID: 592)
- Prn64.bin (PID: 3720)
- drvinst.exe (PID: 1964)
- Prn64.bin (PID: 5560)
- ZebraFD.exe (PID: 6656)
- is-C2RN5.tmp (PID: 6636)
- ZDDownloader2.exe (PID: 6956)
- ZDDownloader2.exe (PID: 1132)
- identity_helper.exe (PID: 3048)
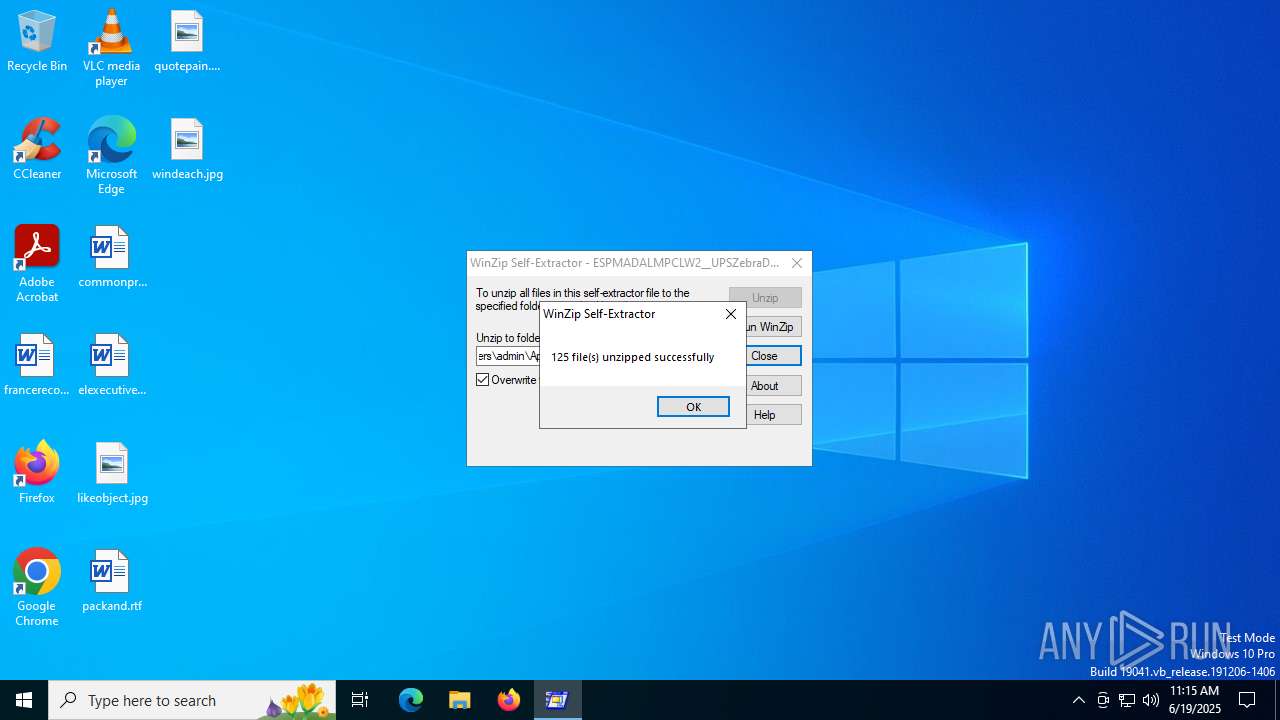
Create files in a temporary directory
- ESPMADALMPCLW2__UPSZebraDriver__c4198da1d17e013b99784df31fbf7d1d7e97b865.exe (PID: 3752)
- PrnInst.exe (PID: 592)
- Prn64.bin (PID: 3720)
- Prn64.bin (PID: 5560)
- is-C2RN5.tmp (PID: 6636)
The sample compiled with arabic language support
- ESPMADALMPCLW2__UPSZebraDriver__c4198da1d17e013b99784df31fbf7d1d7e97b865.exe (PID: 3752)
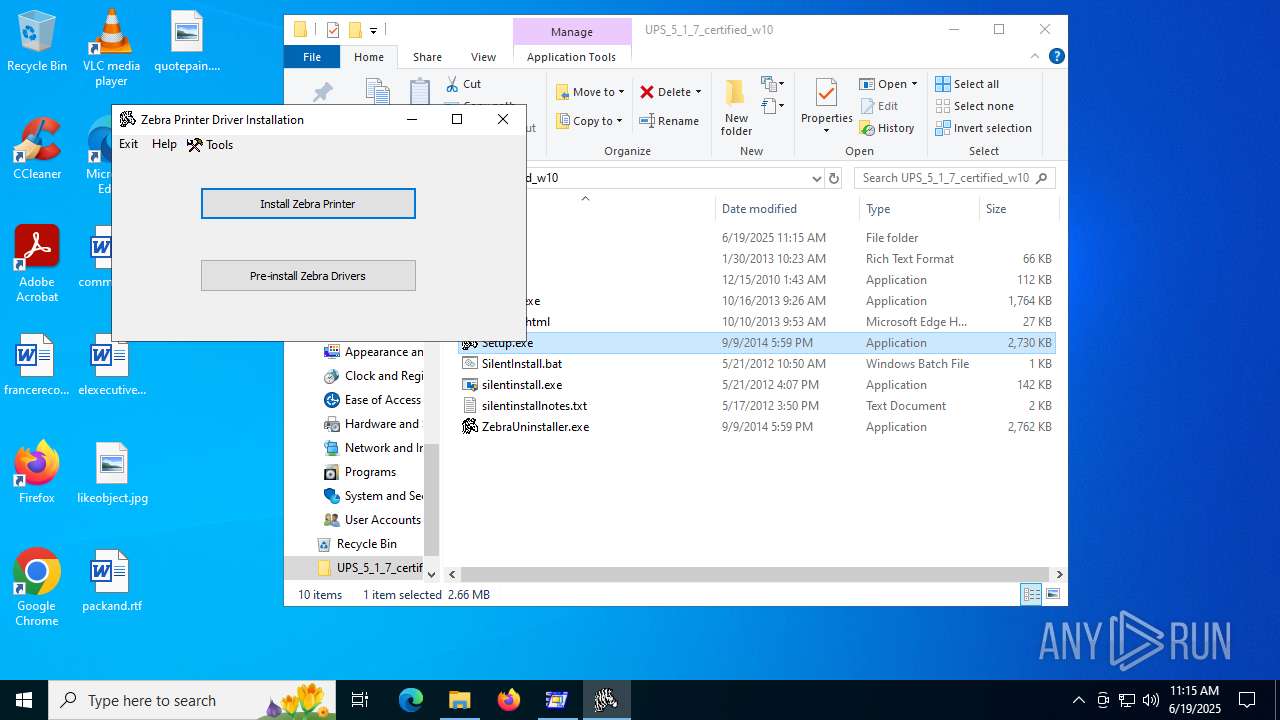
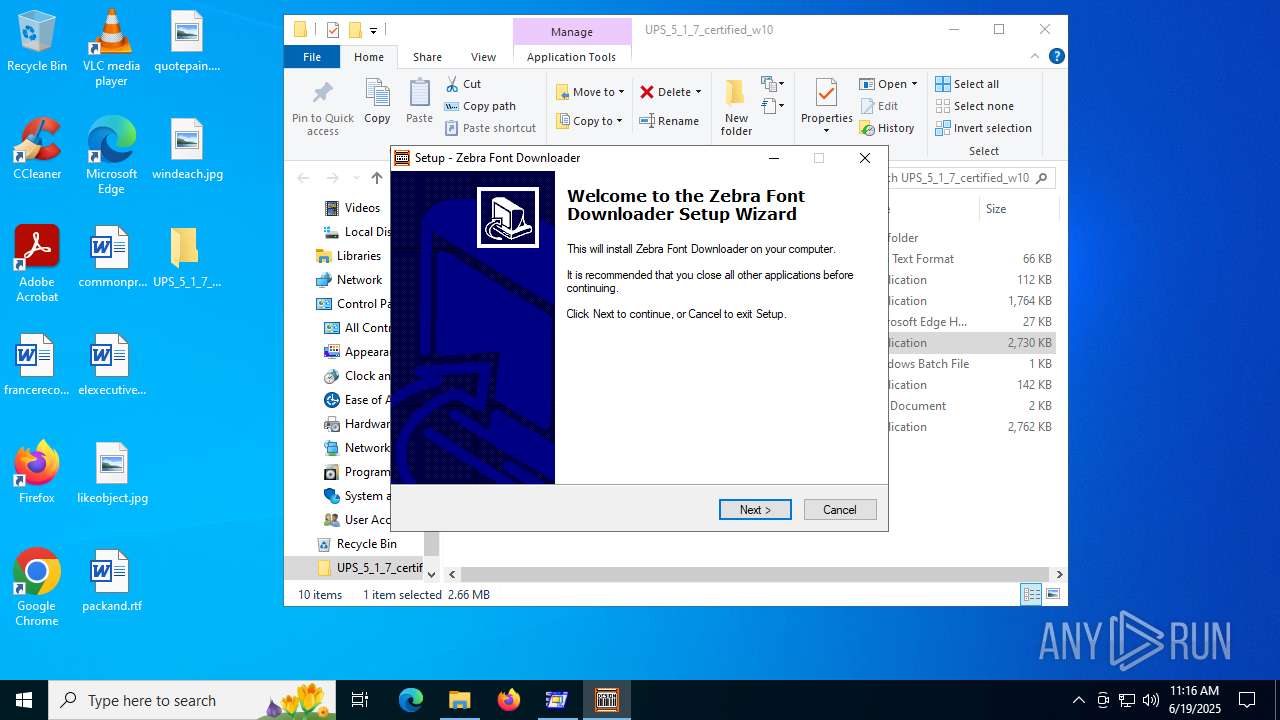
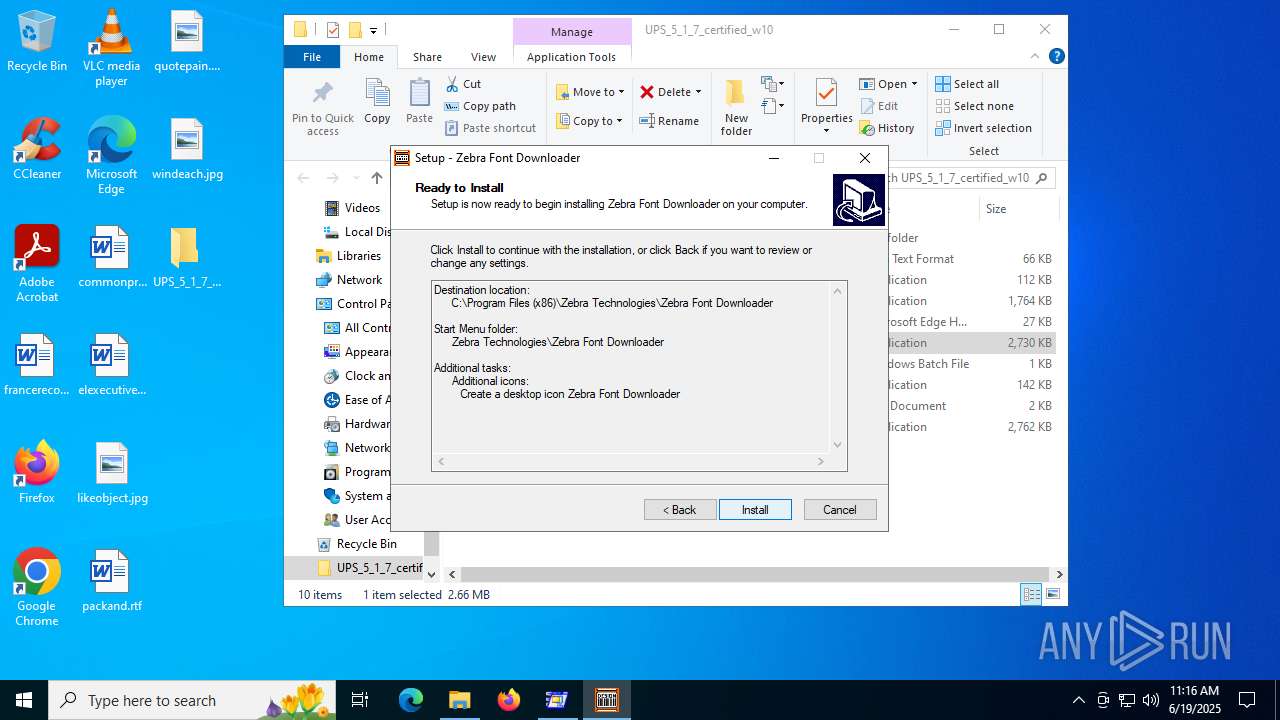
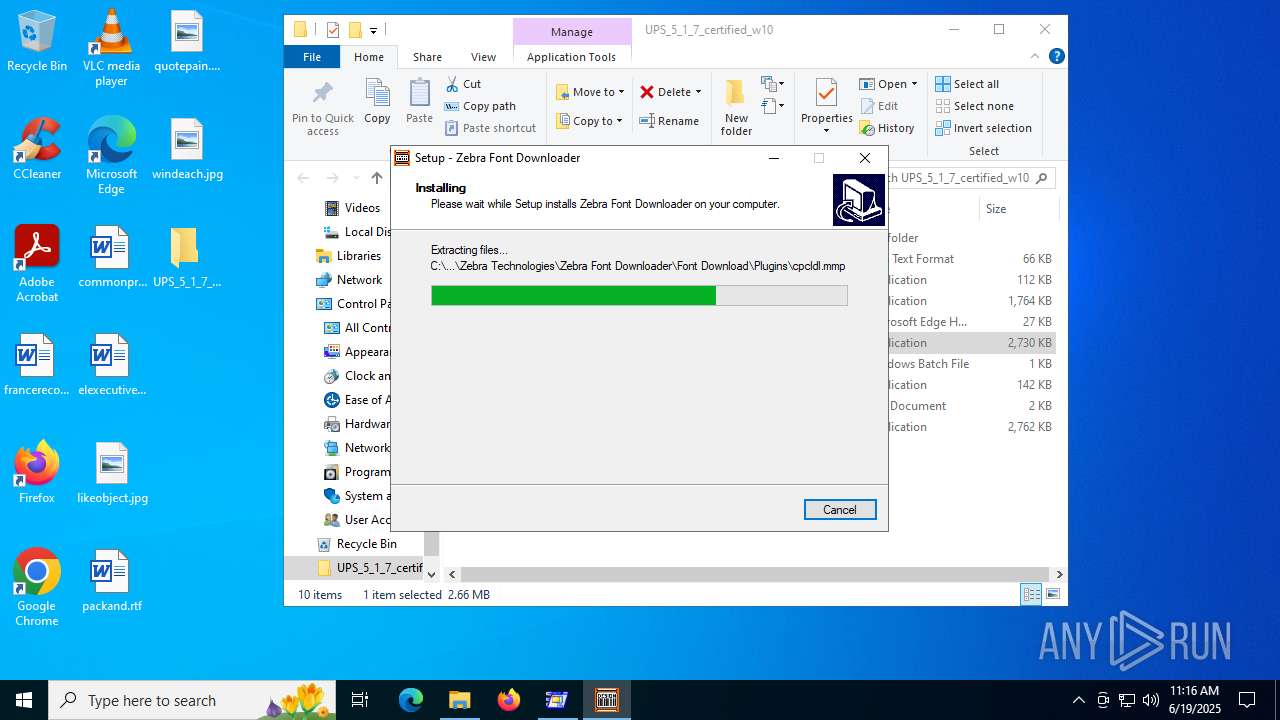
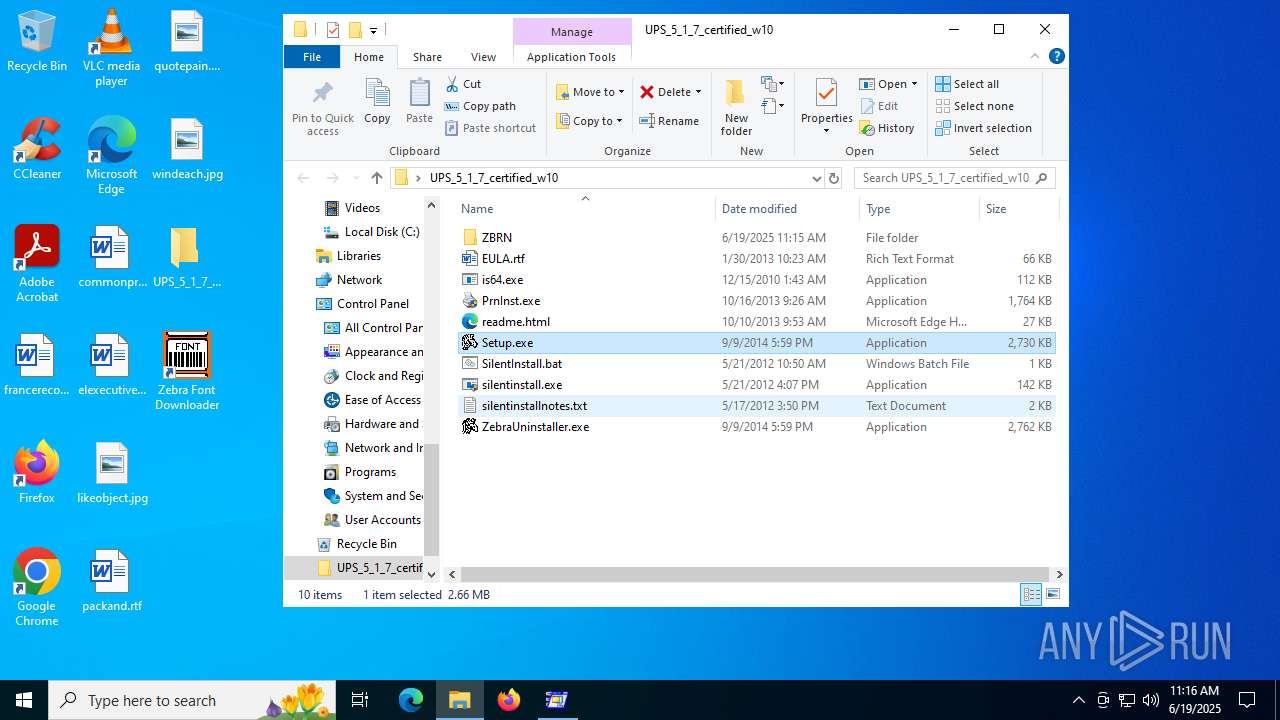
Manual execution by a user
- Setup.exe (PID: 1816)
- ZDDownloader2.exe (PID: 1132)
- msedge.exe (PID: 7096)
The sample compiled with english language support
- ESPMADALMPCLW2__UPSZebraDriver__c4198da1d17e013b99784df31fbf7d1d7e97b865.exe (PID: 3752)
- PrnInst.exe (PID: 592)
- drvinst.exe (PID: 1964)
- spoolsv.exe (PID: 2324)
- ZebraFD.exe (PID: 6656)
- is-C2RN5.tmp (PID: 6636)
Process checks computer location settings
- Setup.exe (PID: 1816)
Reads the software policy settings
- drvinst.exe (PID: 1964)
Reads the machine GUID from the registry
- drvinst.exe (PID: 1964)
Compiled with Borland Delphi (YARA)
- PrnInst.exe (PID: 592)
- slui.exe (PID: 7092)
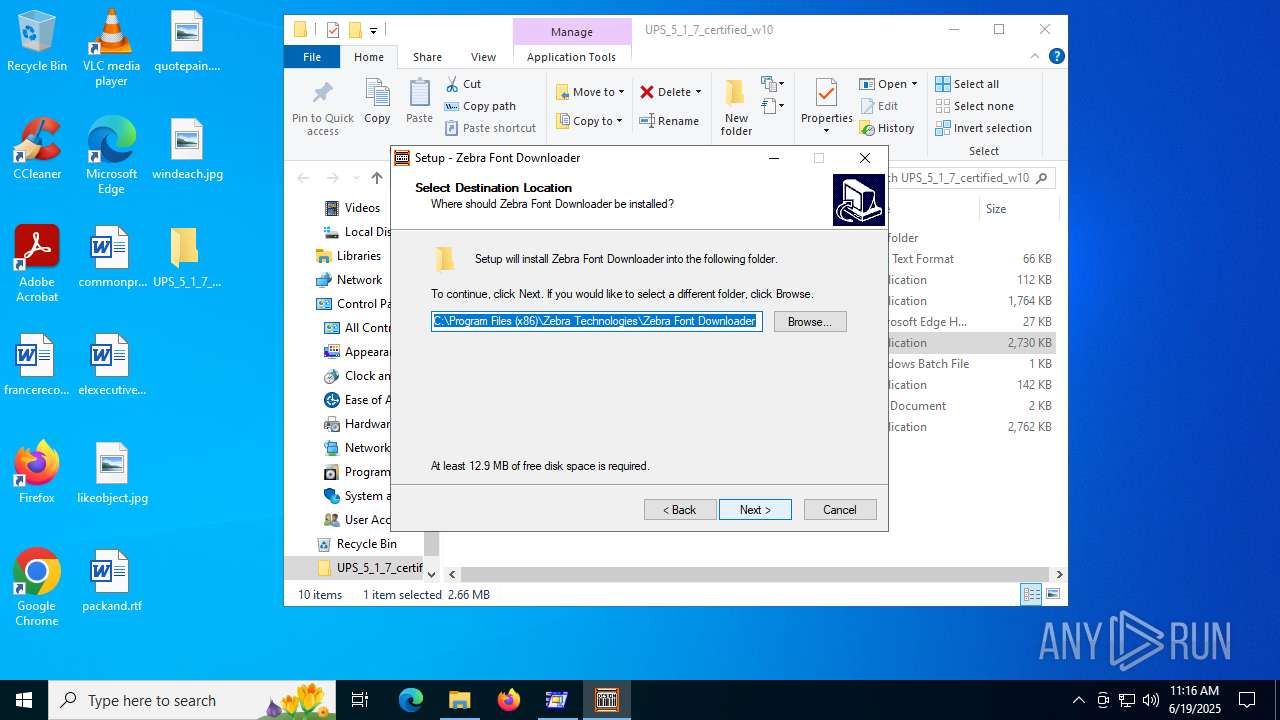
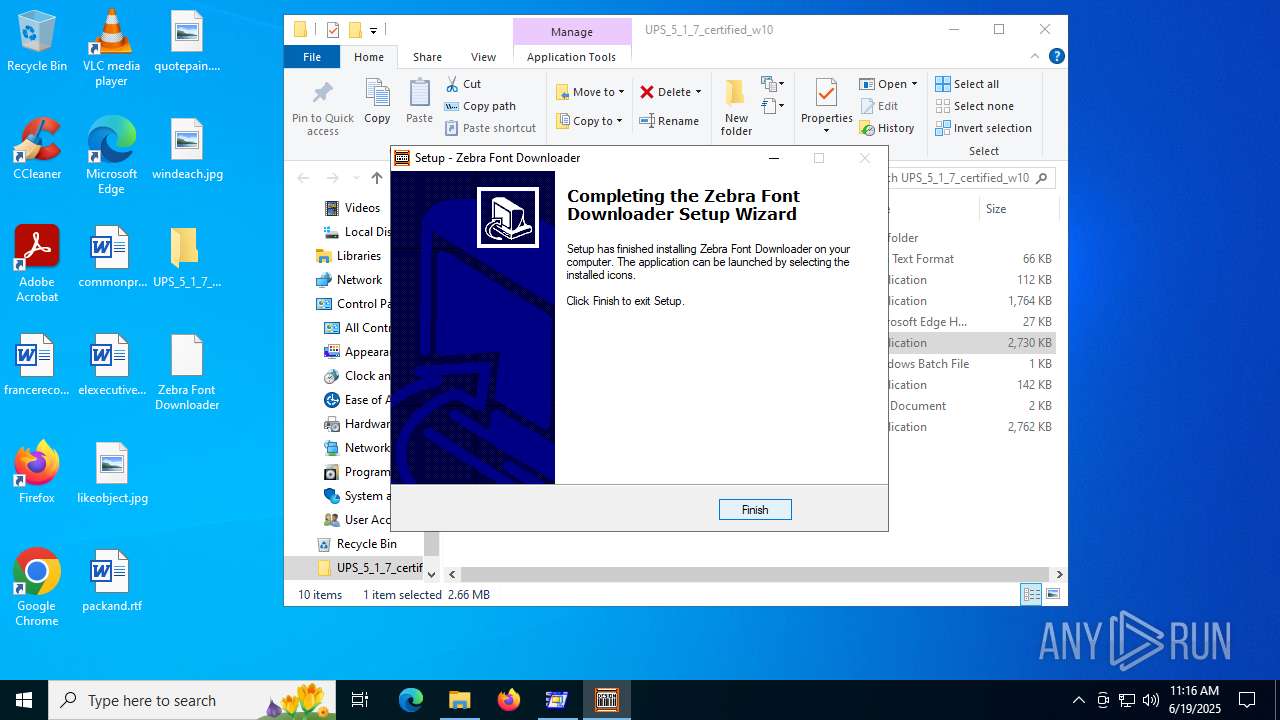
Creates files in the program directory
- is-C2RN5.tmp (PID: 6636)
Creates a software uninstall entry
- is-C2RN5.tmp (PID: 6636)
Application launched itself
- msedge.exe (PID: 7096)
Reads Environment values
- identity_helper.exe (PID: 3048)
Checks proxy server information
- slui.exe (PID: 7092)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (32.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (28.5) |
| .exe | | | Winzip Win32 self-extracting archive (generic) (23.7) |
| .dll | | | Win32 Dynamic Link Library (generic) (6.7) |
| .exe | | | Win32 Executable (generic) (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:01:15 07:43:02+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 52736 |
| InitializedDataSize: | 77824 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6791 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Total processes
175
Monitored processes
33
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
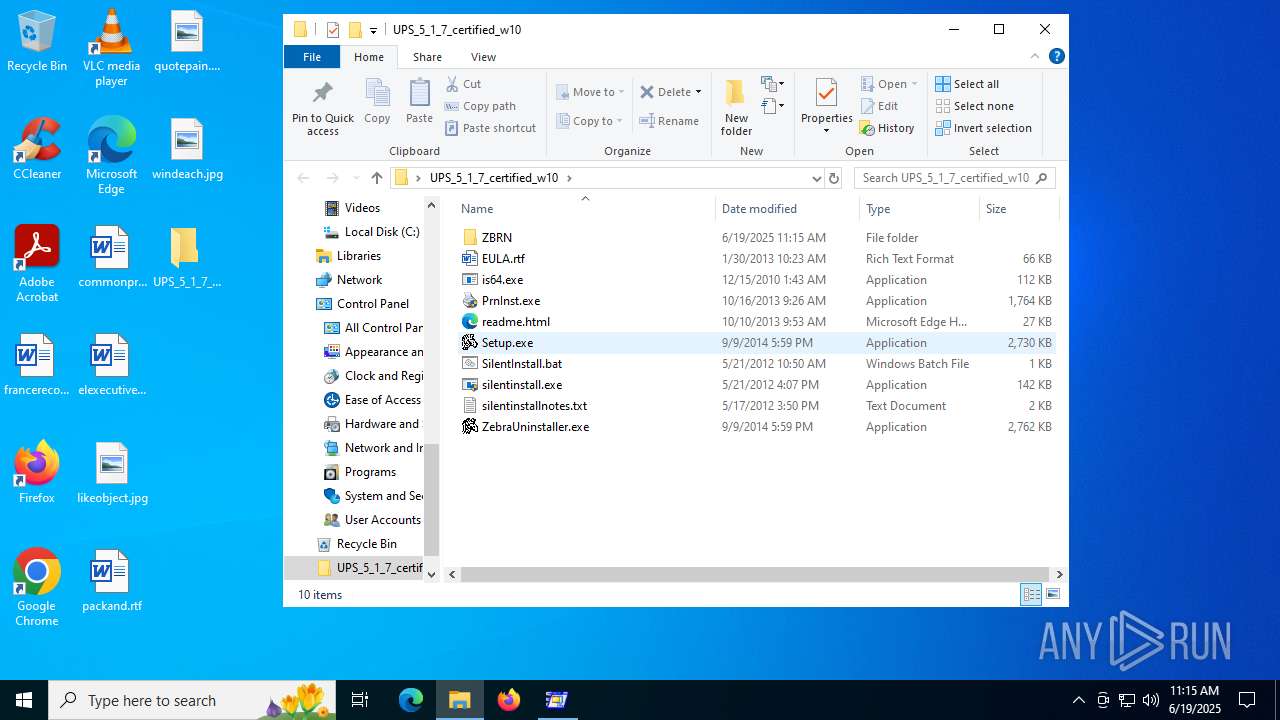
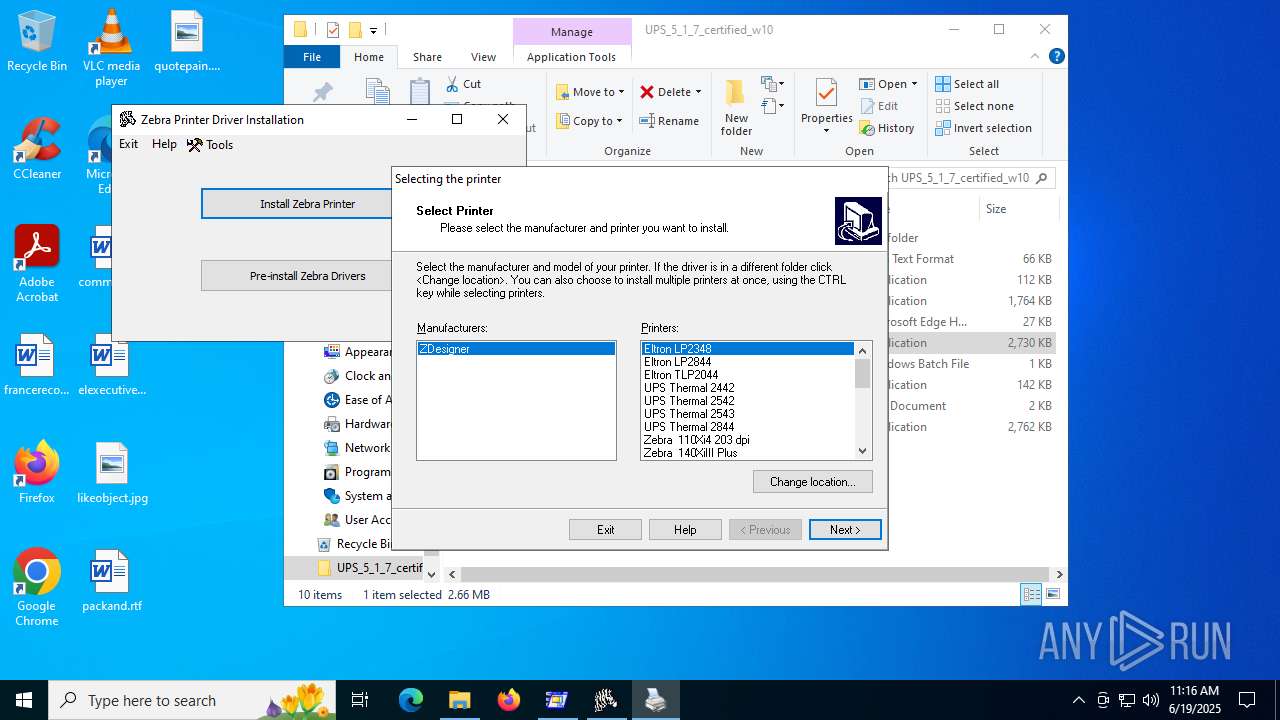
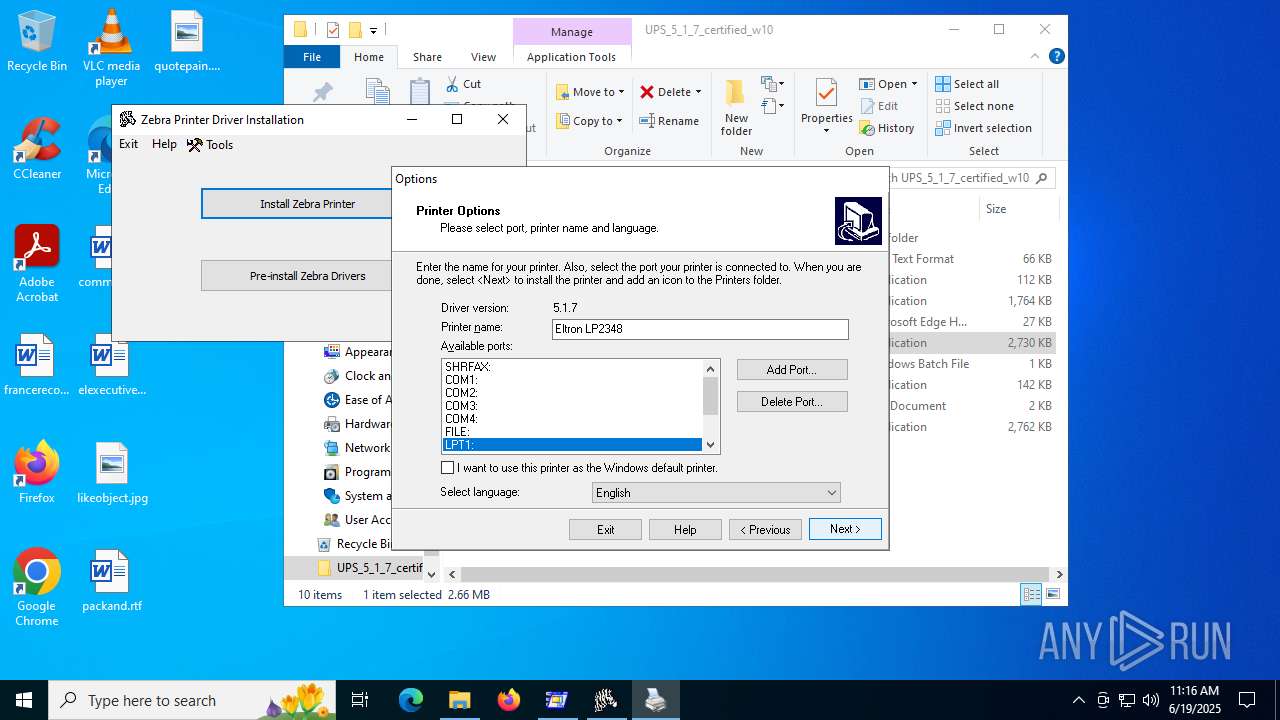
| 592 | "C:\Users\admin\Desktop\UPS_5_1_7_certified_w10\PrnInst.exe" /NOWEL | C:\Users\admin\Desktop\UPS_5_1_7_certified_w10\PrnInst.exe | Setup.exe | ||||||||||||
User: admin Company: Zebra Technologies International, LLC Integrity Level: HIGH Description: Printer Installation Wizard Exit code: 0 Version: 5.0.3 Modules
| |||||||||||||||
| 1132 | "C:\Program Files (x86)\Zebra Technologies\Zebra Font Downloader\Font Download\ZDDownloader2.exe" | C:\Program Files (x86)\Zebra Technologies\Zebra Font Downloader\Font Download\ZDDownloader2.exe | — | explorer.exe | |||||||||||
User: admin Company: Zebra Technologies Corporation Integrity Level: MEDIUM Description: ZebraDesigner Font Downloader Exit code: 0 Version: 2.2.3.4267 Modules
| |||||||||||||||
| 1192 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6244,i,18192612094965179873,18165495170678196755,262144 --variations-seed-version --mojo-platform-channel-handle=6176 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1644 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3268,i,18192612094965179873,18165495170678196755,262144 --variations-seed-version --mojo-platform-channel-handle=3700 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1816 | "C:\Users\admin\Desktop\UPS_5_1_7_certified_w10\Setup.exe" | C:\Users\admin\Desktop\UPS_5_1_7_certified_w10\Setup.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1964 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{7153c8cc-c025-b845-9c5a-9d558cc50a49}\ZBRN.inf" "9" "48c15e673" "00000000000001C8" "WinSta0\Default" "00000000000001DC" "208" "C:\Users\admin\Desktop\UPS_5_1_7_certified_w10\ZBRN" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2320 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3652,i,18192612094965179873,18165495170678196755,262144 --variations-seed-version --mojo-platform-channel-handle=3664 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2324 | C:\WINDOWS\System32\spoolsv.exe | C:\Windows\System32\spoolsv.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Spooler SubSystem App Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3048 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5764,i,18192612094965179873,18165495170678196755,262144 --variations-seed-version --mojo-platform-channel-handle=5880 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3504 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x304,0x308,0x30c,0x2fc,0x314,0x7ffc44bff208,0x7ffc44bff214,0x7ffc44bff220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
16 406
Read events
15 204
Write events
1 201
Delete events
1
Modification events
| (PID) Process: | (592) PrnInst.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.dev.log |
Value: 4096 | |||
| (PID) Process: | (592) PrnInst.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\EuroPlus\PrinterInstallWizard |
| Operation: | write | Name: | InstallInProgress |
Value: 1 | |||
| (PID) Process: | (7060) spoolsv.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Devices |
| Operation: | write | Name: | OneNote (Desktop) |
Value: winspool,nul: | |||
| (PID) Process: | (7060) spoolsv.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\Windows NT\CurrentVersion\PrinterPorts |
| Operation: | write | Name: | OneNote (Desktop) |
Value: winspool,nul:,15,45 | |||
| (PID) Process: | (7060) spoolsv.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Ports |
| Operation: | write | Name: | Ne00: |
Value: | |||
| (PID) Process: | (7060) spoolsv.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Devices |
| Operation: | write | Name: | Microsoft XPS Document Writer |
Value: winspool,Ne00: | |||
| (PID) Process: | (7060) spoolsv.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\Windows NT\CurrentVersion\PrinterPorts |
| Operation: | write | Name: | Microsoft XPS Document Writer |
Value: winspool,Ne00:,15,45 | |||
| (PID) Process: | (7060) spoolsv.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Ports |
| Operation: | write | Name: | Ne01: |
Value: | |||
| (PID) Process: | (7060) spoolsv.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Devices |
| Operation: | write | Name: | Microsoft Print to PDF |
Value: winspool,Ne01: | |||
| (PID) Process: | (7060) spoolsv.exe | Key: | HKEY_USERS\S-1-5-19\SOFTWARE\Microsoft\Windows NT\CurrentVersion\PrinterPorts |
| Operation: | write | Name: | Microsoft Print to PDF |
Value: winspool,Ne01:,15,45 | |||
Executable files
424
Suspicious files
40
Text files
305
Unknown types
38
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
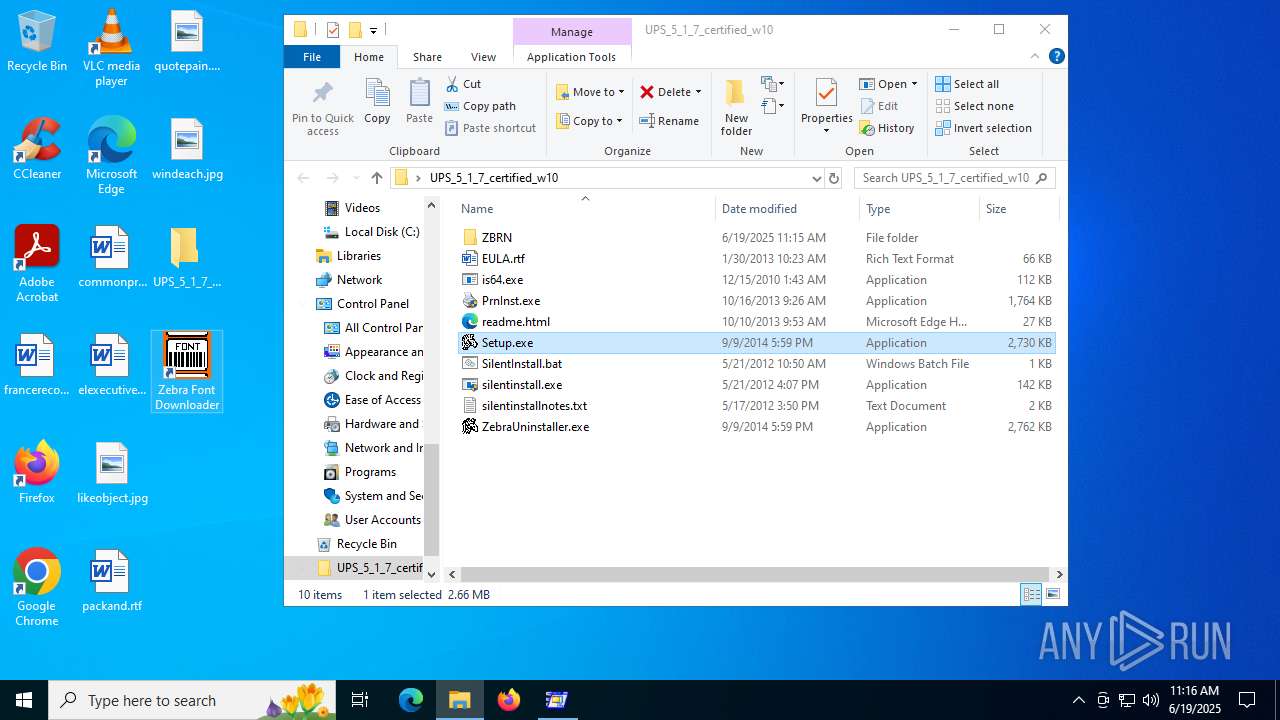
| 3752 | ESPMADALMPCLW2__UPSZebraDriver__c4198da1d17e013b99784df31fbf7d1d7e97b865.exe | C:\Users\admin\AppData\Local\Temp\UPS_5_1_7_certified_w10\Setup.exe | executable | |
MD5:0CF4517CAF54650DA69DD92C1069A058 | SHA256:1A62E8F499357C6DF188452F30C082FB984053B68874F37A0F6C523D7185FFAF | |||
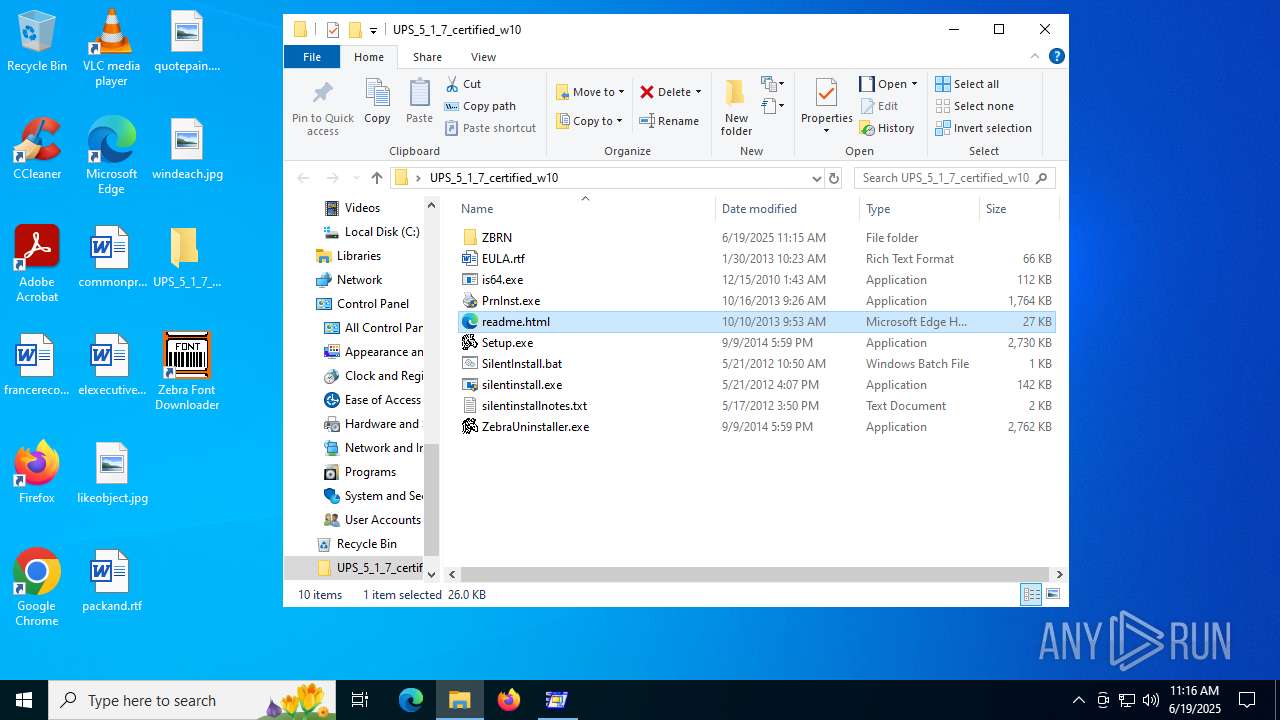
| 3752 | ESPMADALMPCLW2__UPSZebraDriver__c4198da1d17e013b99784df31fbf7d1d7e97b865.exe | C:\Users\admin\AppData\Local\Temp\UPS_5_1_7_certified_w10\readme.html | html | |
MD5:7C7DAB3DC27B67A03A6F57B691B18243 | SHA256:C3D8A327CD6678789FBFDBD8779965FE895D941FADB17E3D505CF893BB22737F | |||
| 3752 | ESPMADALMPCLW2__UPSZebraDriver__c4198da1d17e013b99784df31fbf7d1d7e97b865.exe | C:\Users\admin\AppData\Local\Temp\UPS_5_1_7_certified_w10\is64.exe | executable | |
MD5:27CFBF5022B722271C69544C7E828F60 | SHA256:17157E0E7DA68D8CA49B0FC84A31019046C47674CBD15BE029F204CAA09FE902 | |||
| 3752 | ESPMADALMPCLW2__UPSZebraDriver__c4198da1d17e013b99784df31fbf7d1d7e97b865.exe | C:\Users\admin\AppData\Local\Temp\UPS_5_1_7_certified_w10\PrnInst.exe | executable | |
MD5:114B44EA18B1788790F28DE1F9AA08D6 | SHA256:0FDB891146991D8FEE25D9A950A52D5F0412CB8FD43EFD2EE4AF39334BB8F43D | |||
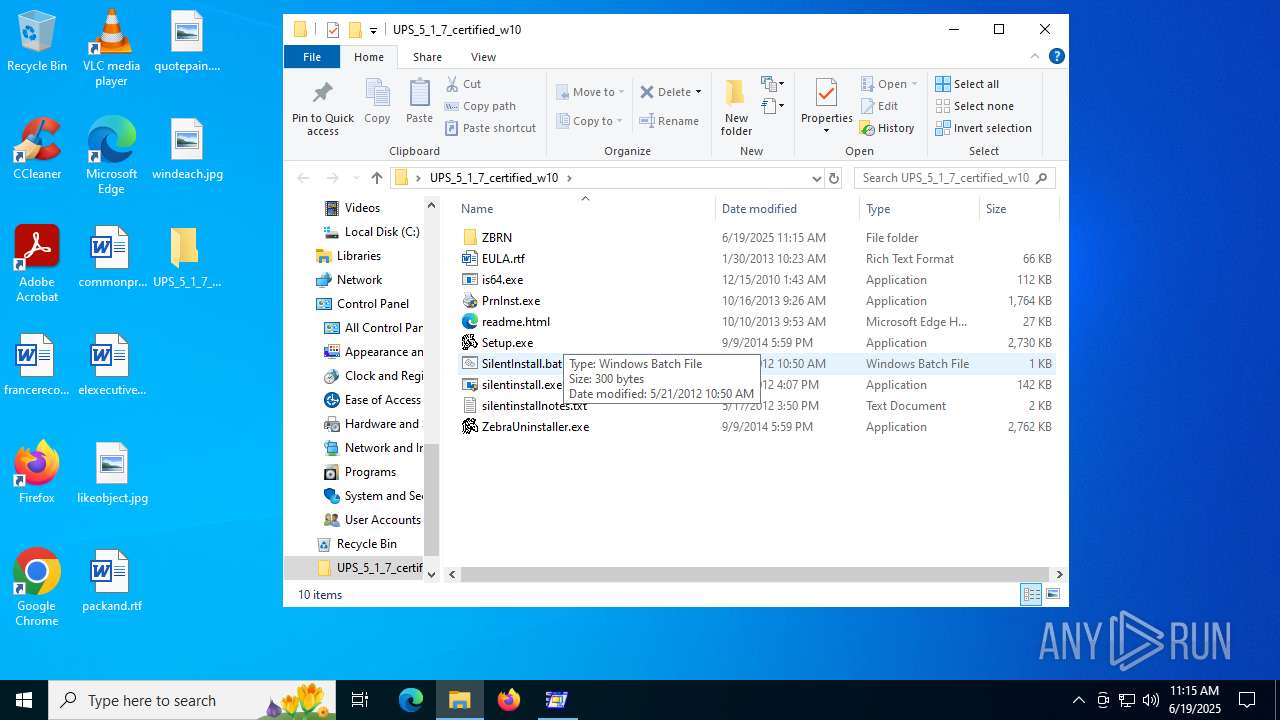
| 3752 | ESPMADALMPCLW2__UPSZebraDriver__c4198da1d17e013b99784df31fbf7d1d7e97b865.exe | C:\Users\admin\AppData\Local\Temp\UPS_5_1_7_certified_w10\SilentInstall.bat | text | |
MD5:93DDBCB6EADDA3BB0BF05A377D9E1318 | SHA256:B4B64459FBABBBC1BE070035B6090C77503CBA7F2F599503CB272E4628C35E44 | |||
| 3752 | ESPMADALMPCLW2__UPSZebraDriver__c4198da1d17e013b99784df31fbf7d1d7e97b865.exe | C:\Users\admin\AppData\Local\Temp\UPS_5_1_7_certified_w10\silentinstallnotes.txt | text | |
MD5:BF20916F4BE68091EEF267ACB88514A2 | SHA256:B5419FB07E638872776E9CADD1FEC836CA5C136AB521ED75439C869661195E4F | |||
| 3752 | ESPMADALMPCLW2__UPSZebraDriver__c4198da1d17e013b99784df31fbf7d1d7e97b865.exe | C:\Users\admin\AppData\Local\Temp\UPS_5_1_7_certified_w10\silentinstall.exe | executable | |
MD5:F2E46D78604F743D4A685B19218FB14B | SHA256:2E06A99007E298B6A5E3FE4DFC8B19FF07C5577A8BAE09056C3411E9B0B62015 | |||
| 3752 | ESPMADALMPCLW2__UPSZebraDriver__c4198da1d17e013b99784df31fbf7d1d7e97b865.exe | C:\Users\admin\AppData\Local\Temp\UPS_5_1_7_certified_w10\ZBRN\Common\BA110XI42.DAT | ini | |
MD5:CEC392C0A1F0405485D8980A356D4BF3 | SHA256:8E1E8E266855EC30488891E03CE6B7A5B22B7CC7CAEC206A310341B89CEA5BB6 | |||
| 3752 | ESPMADALMPCLW2__UPSZebraDriver__c4198da1d17e013b99784df31fbf7d1d7e97b865.exe | C:\Users\admin\AppData\Local\Temp\UPS_5_1_7_certified_w10\ZBRN\Common\AndaleT.MMF | ini | |
MD5:D6905B8439BFFDDFC4D24F92B412C19D | SHA256:FED3EDF18EFB65863597AFD1AF8EDB0EF97E43E98E6D0E9164A6F58BD8F28D72 | |||
| 3752 | ESPMADALMPCLW2__UPSZebraDriver__c4198da1d17e013b99784df31fbf7d1d7e97b865.exe | C:\Users\admin\AppData\Local\Temp\UPS_5_1_7_certified_w10\ZBRN\Common\Angsana.MMF | ini | |
MD5:A76D521AF9D4EAEA89B67C1EBA0F9E63 | SHA256:C440A4E50DB54B6418E85D9D0A5F34A8C6257AEF83A45AB67896AF5A69C60368 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
56
DNS requests
35
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1336 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3724 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3724 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
4844 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:wnb-haJuCwj_pUeSCcdH5kNHaUKaM2j1FlkpcMaHsE4&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2140 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1336 | svchost.exe | 40.126.31.0:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1336 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2336 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
1268 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |