| File name: | gvju6u-lse19-698411 |
| Full analysis: | https://app.any.run/tasks/d880c66f-ee99-4a6b-b278-aef48563b52a |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 06, 2019, 15:52:55 |
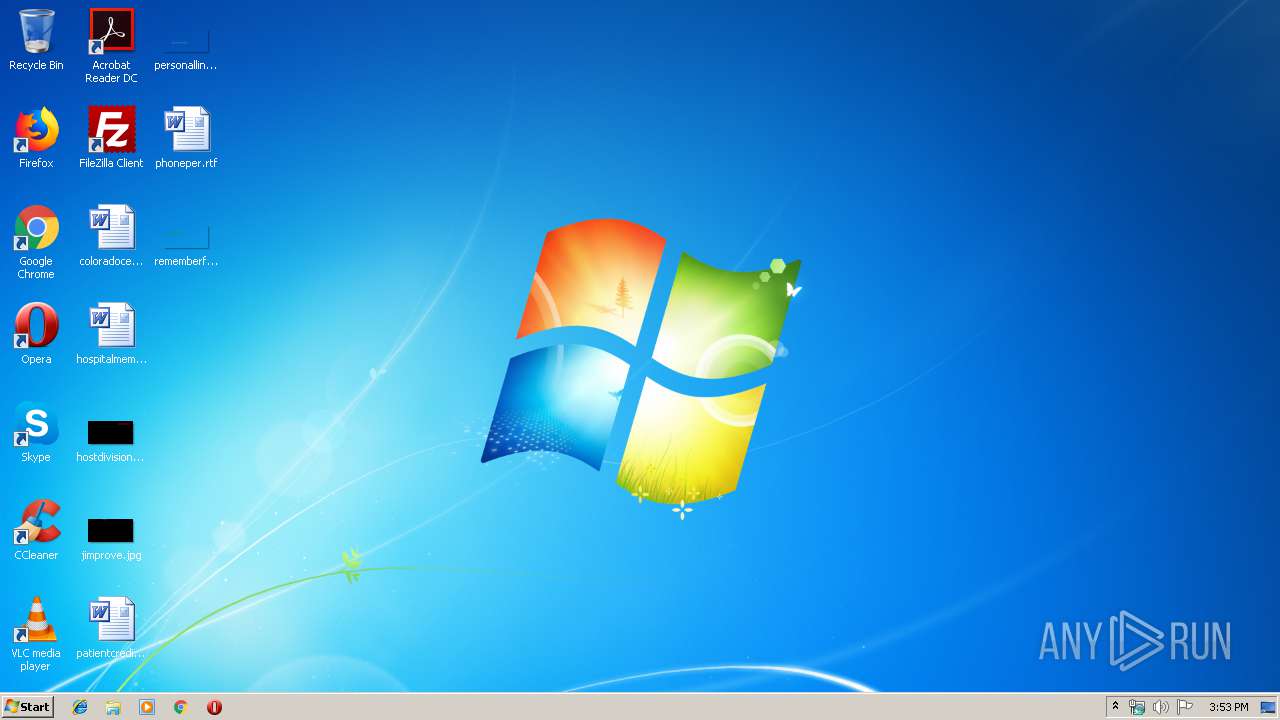
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
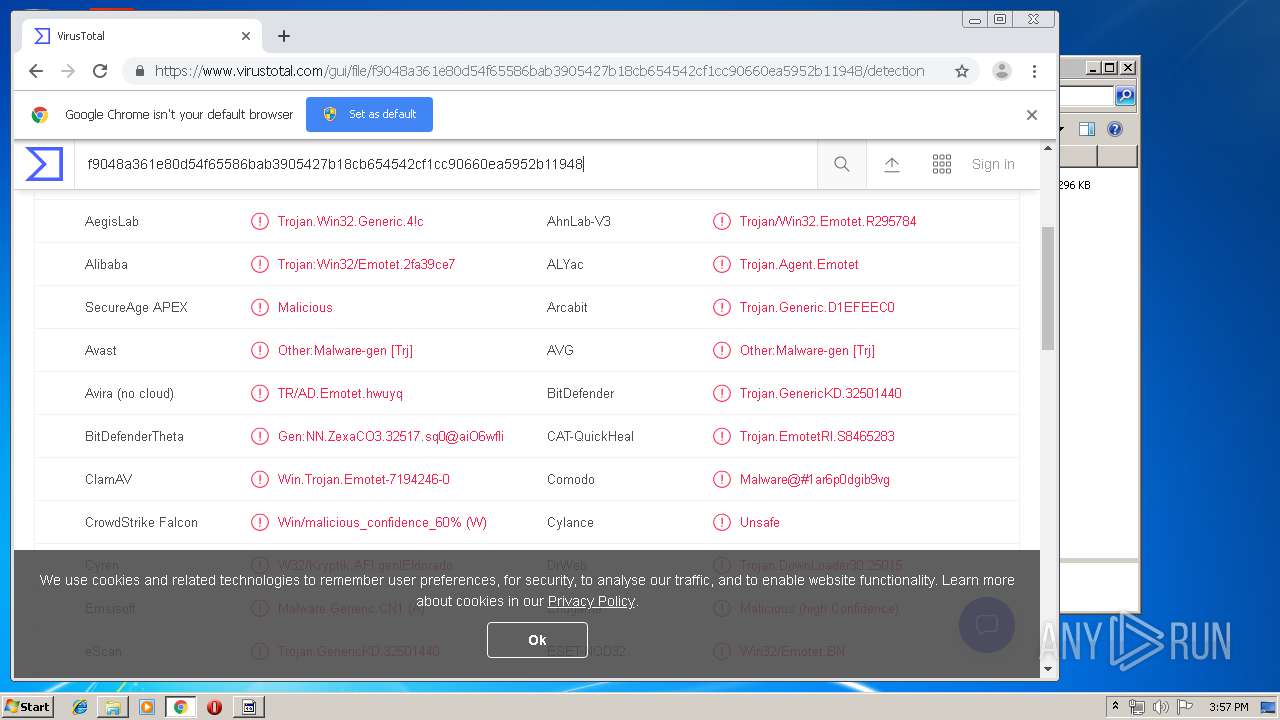
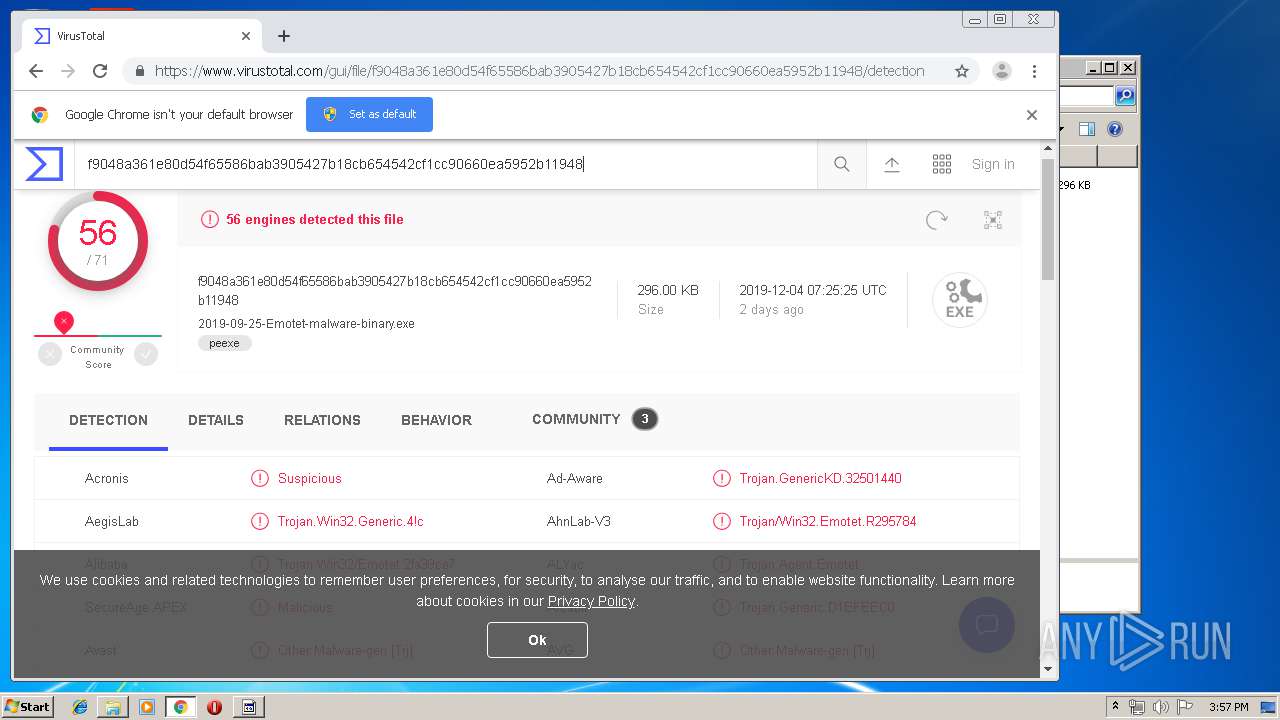
| MD5: | 51E9B4FF43307A393B63C7E3A4324E6C |
| SHA1: | 9A4A80066C31FDE5596031F5D3623CFFB9B0EC6F |
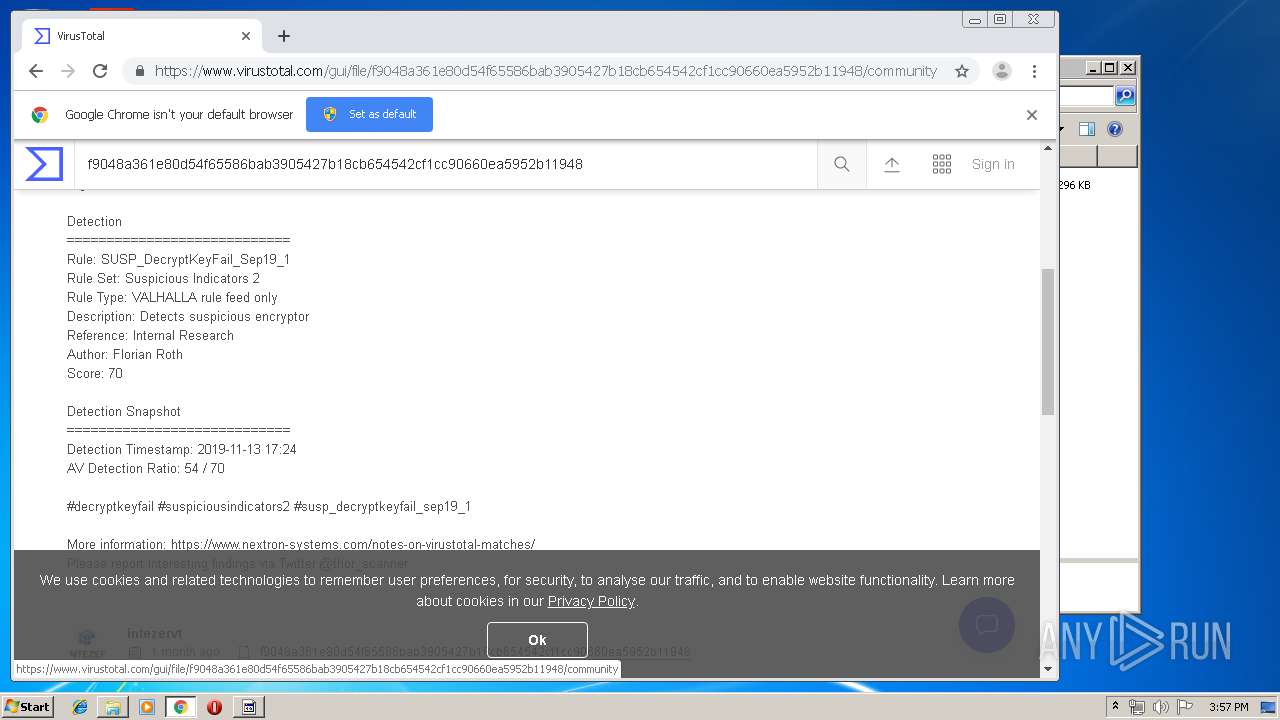
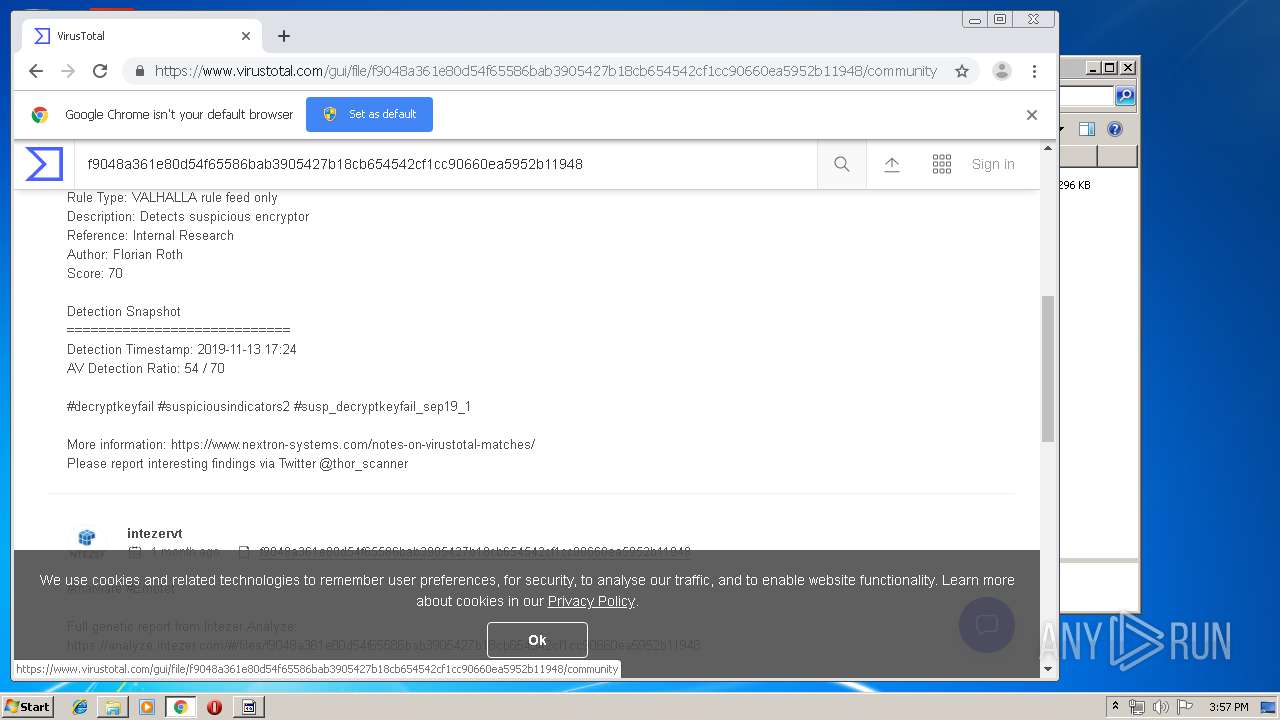
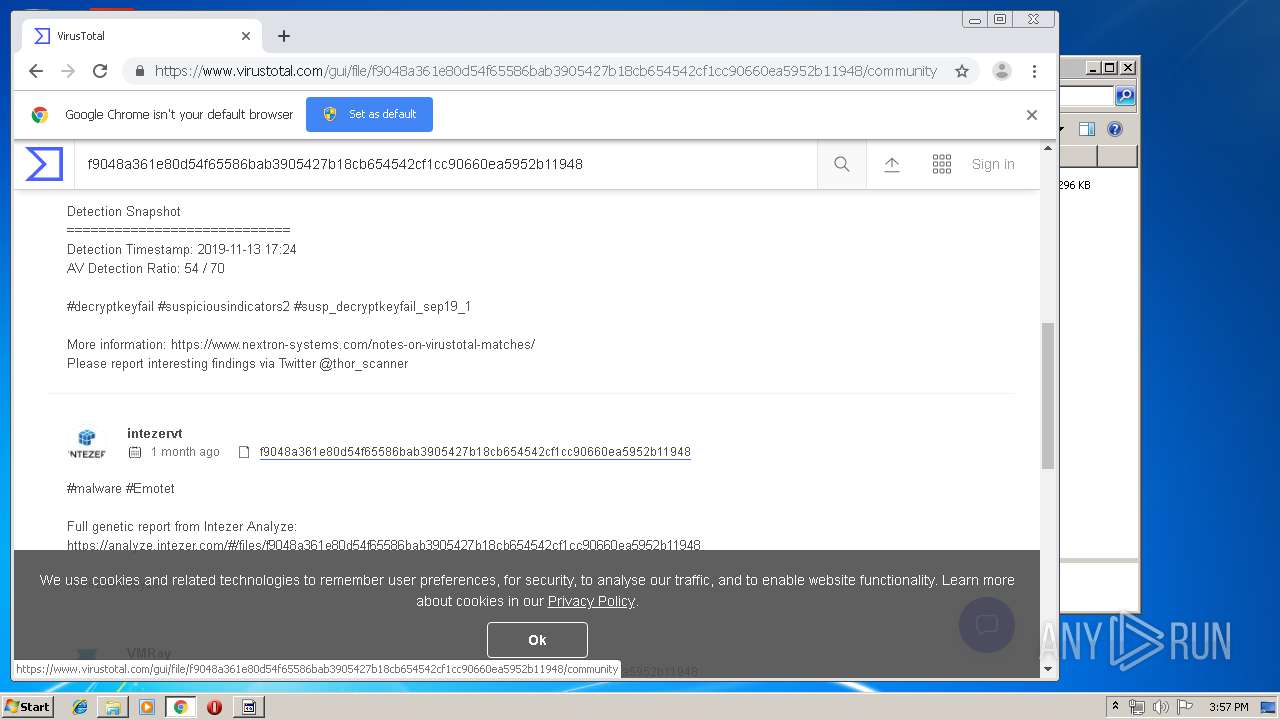
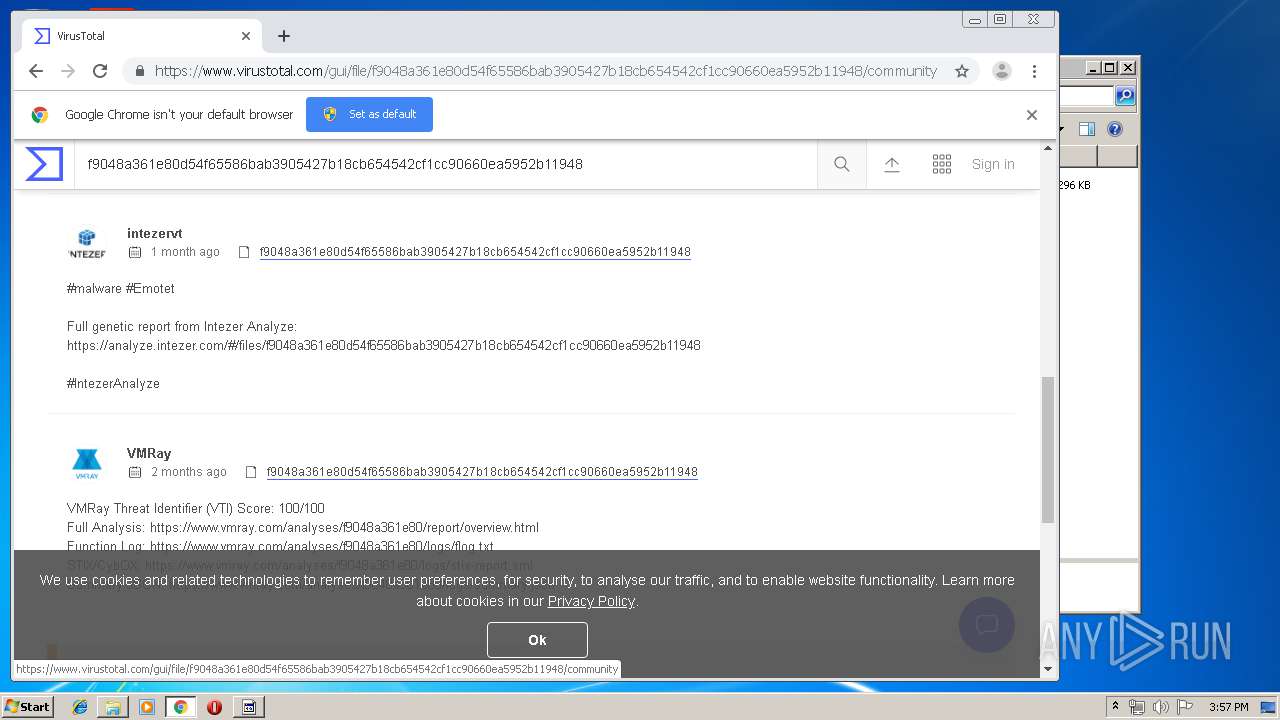
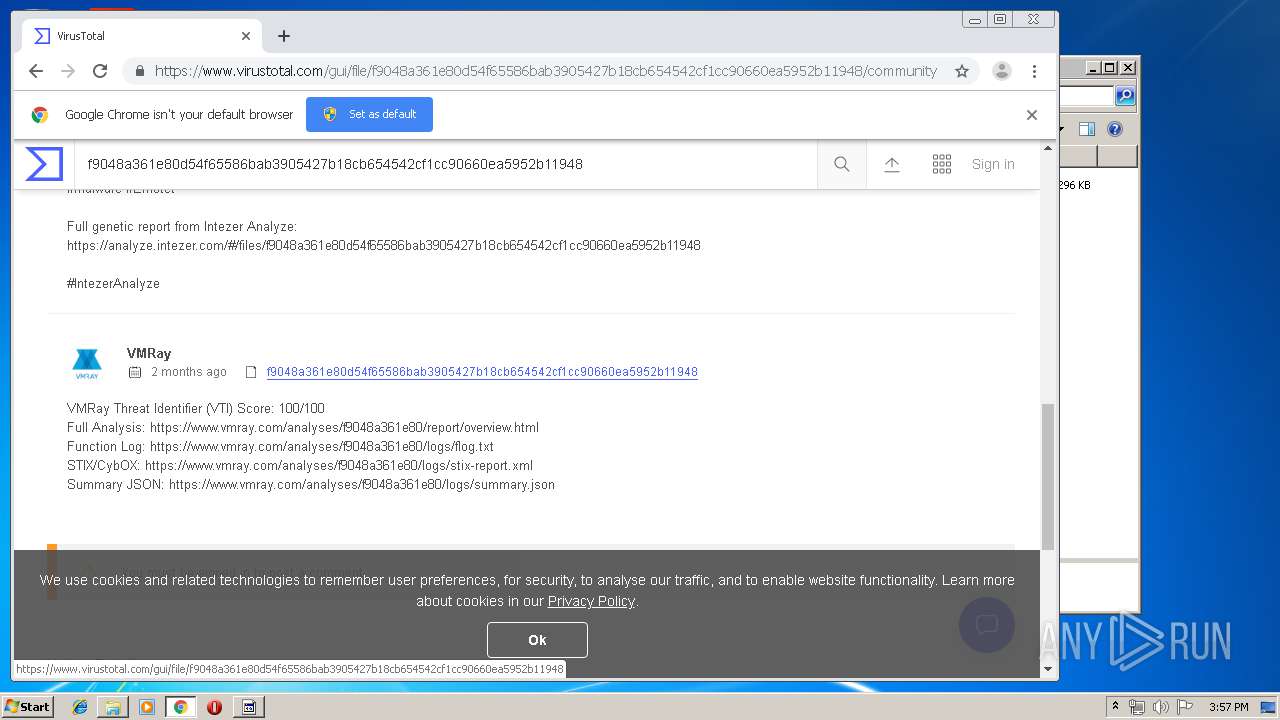
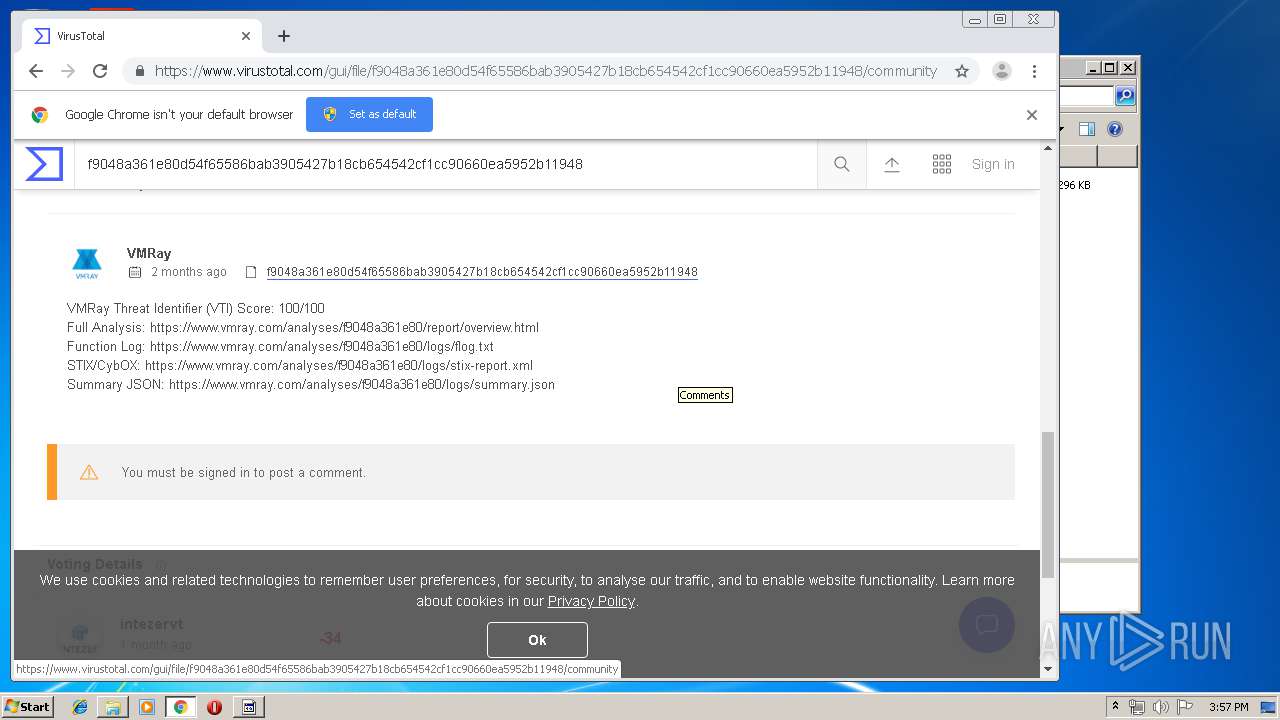
| SHA256: | F9048A361E80D54F65586BAB3905427B18CB654542CF1CC90660EA5952B11948 |
| SSDEEP: | 6144:fWAg+sr2J9xoWZcb0lI3yFNwGgcWwZevkW:fxJEqcIlM5vNh |
MALICIOUS
Emotet process was detected
- gvju6u-lse19-698411.exe (PID: 564)
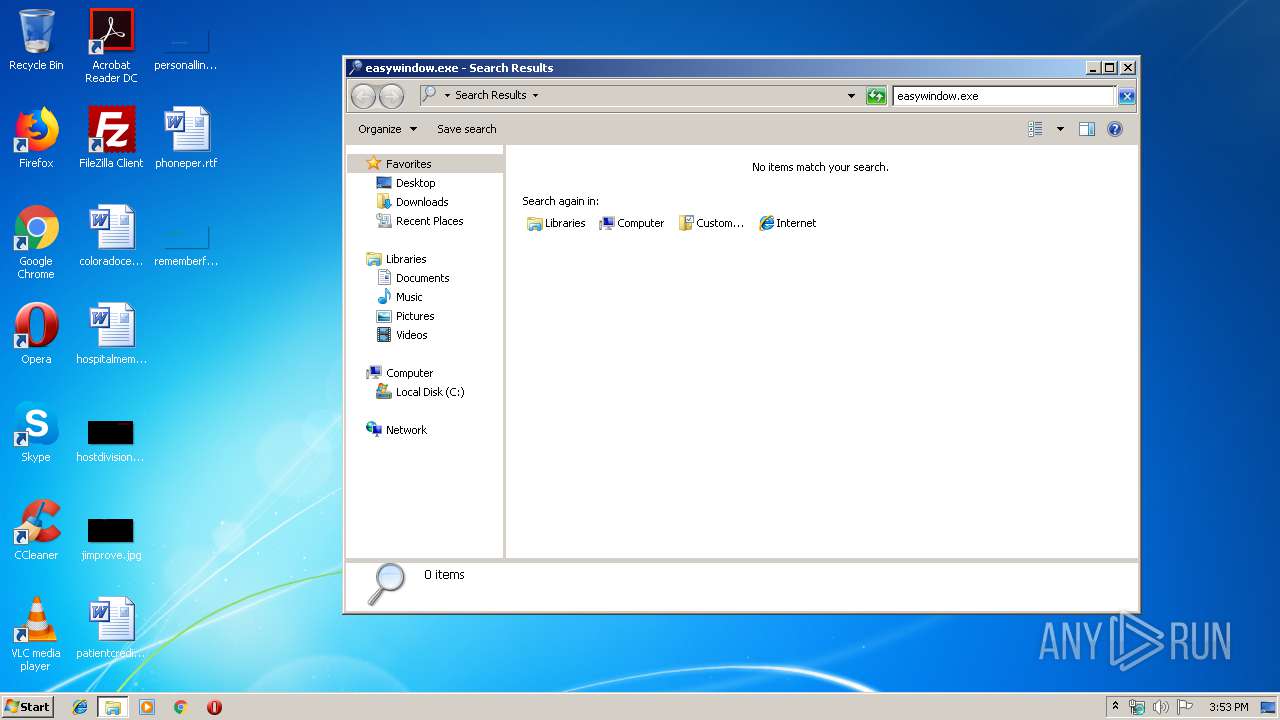
Connects to CnC server
- easywindow.exe (PID: 2004)
- easywindow.exe (PID: 388)
EMOTET was detected
- easywindow.exe (PID: 2004)
- easywindow.exe (PID: 388)
SUSPICIOUS
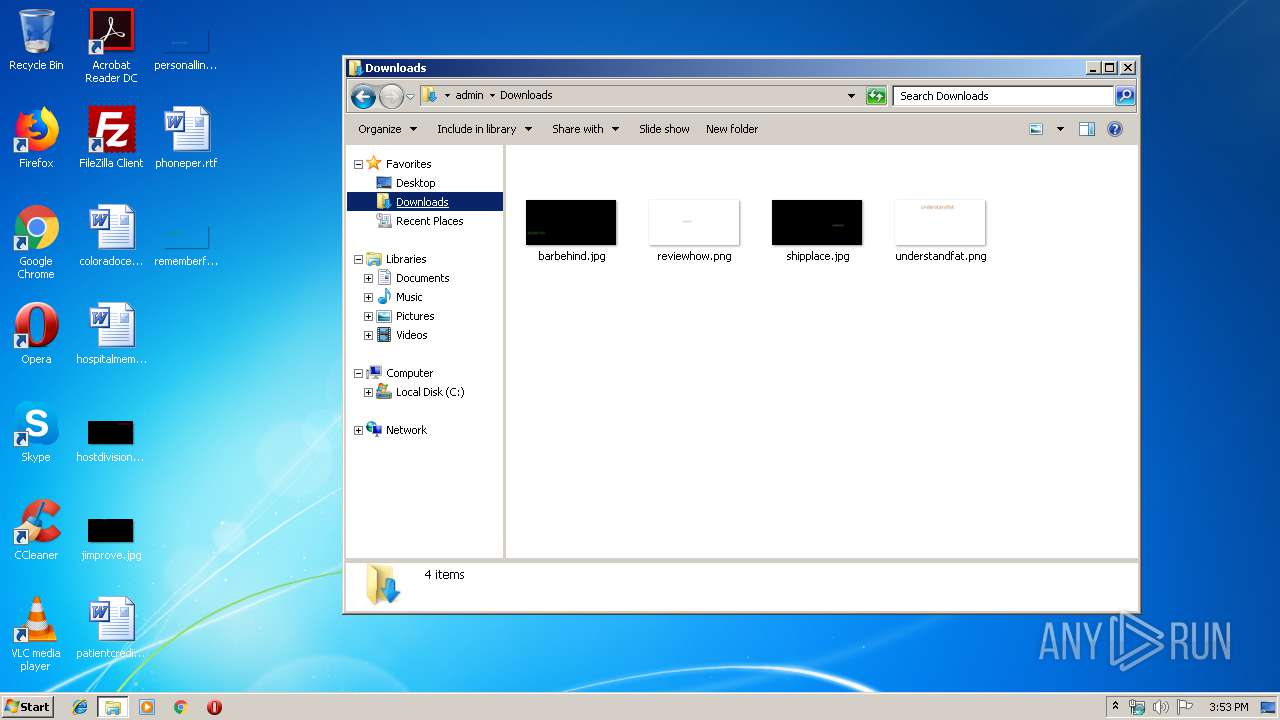
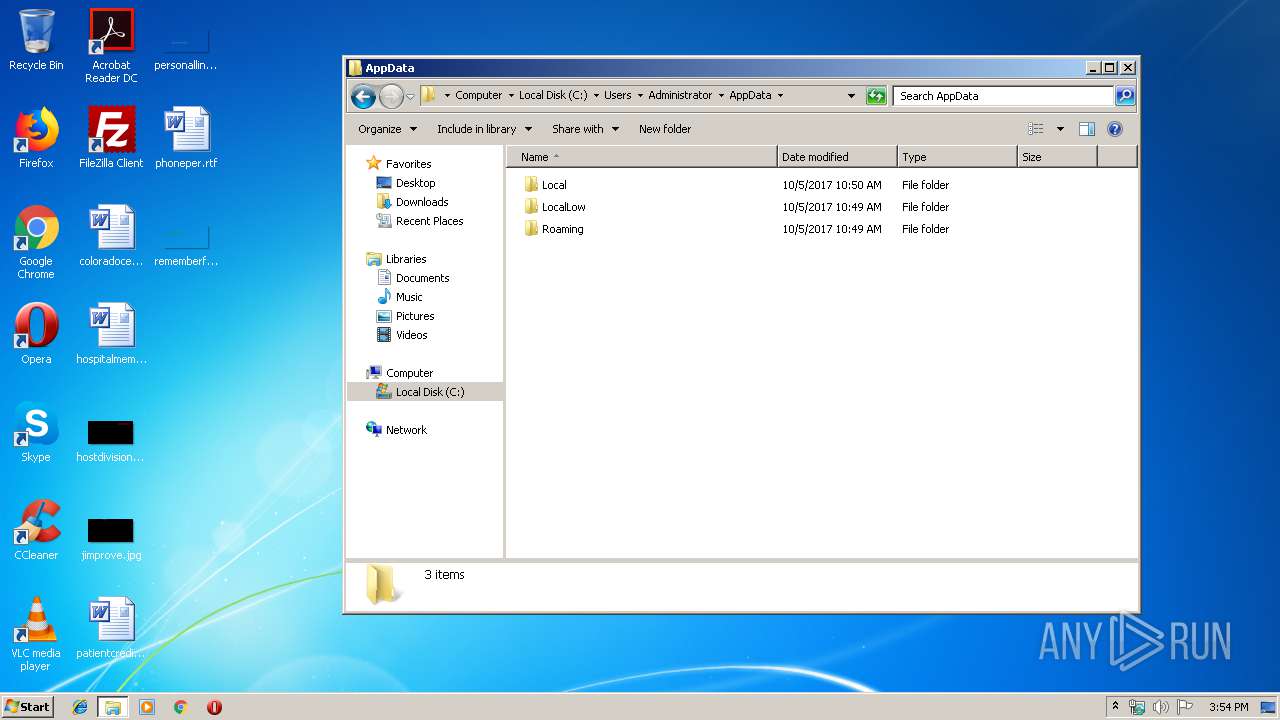
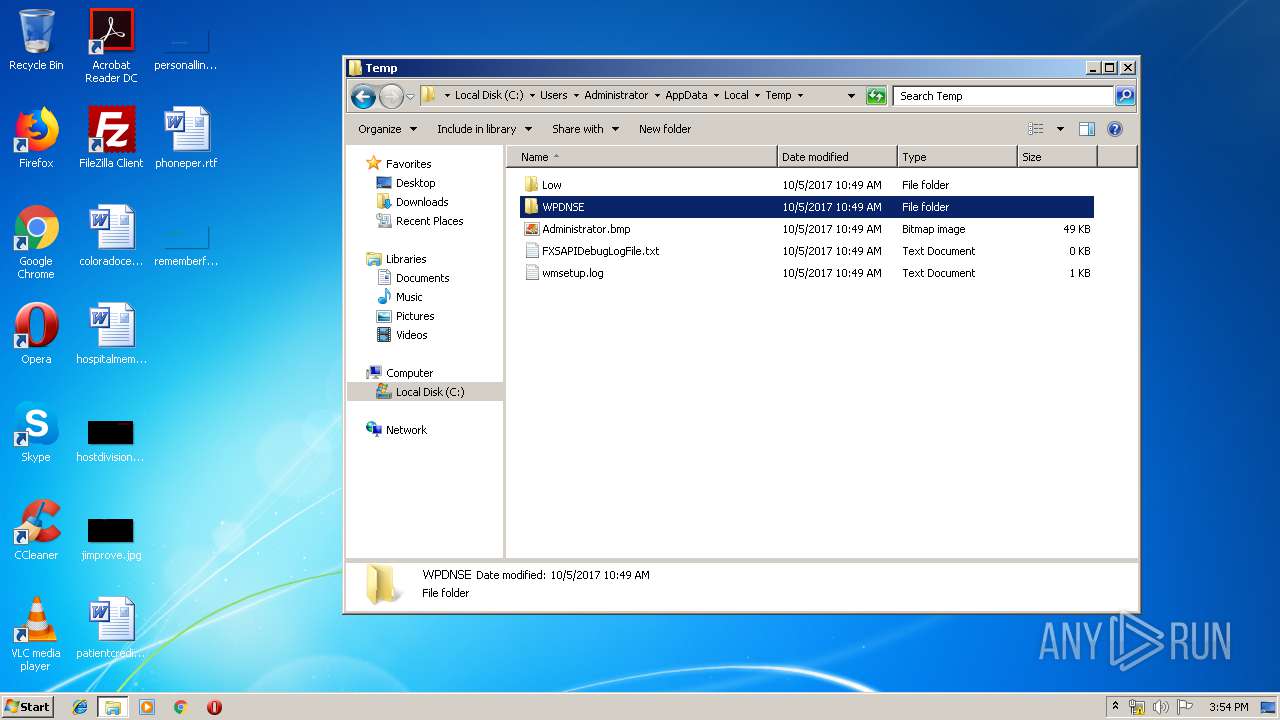
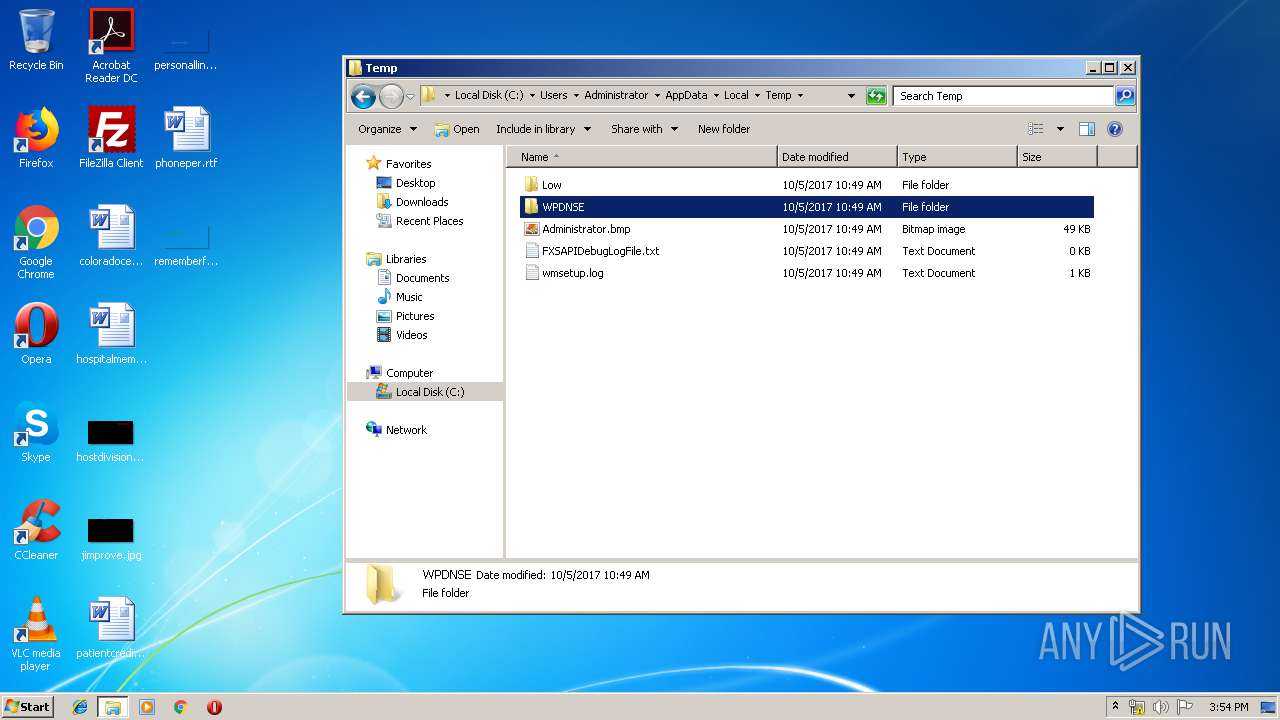
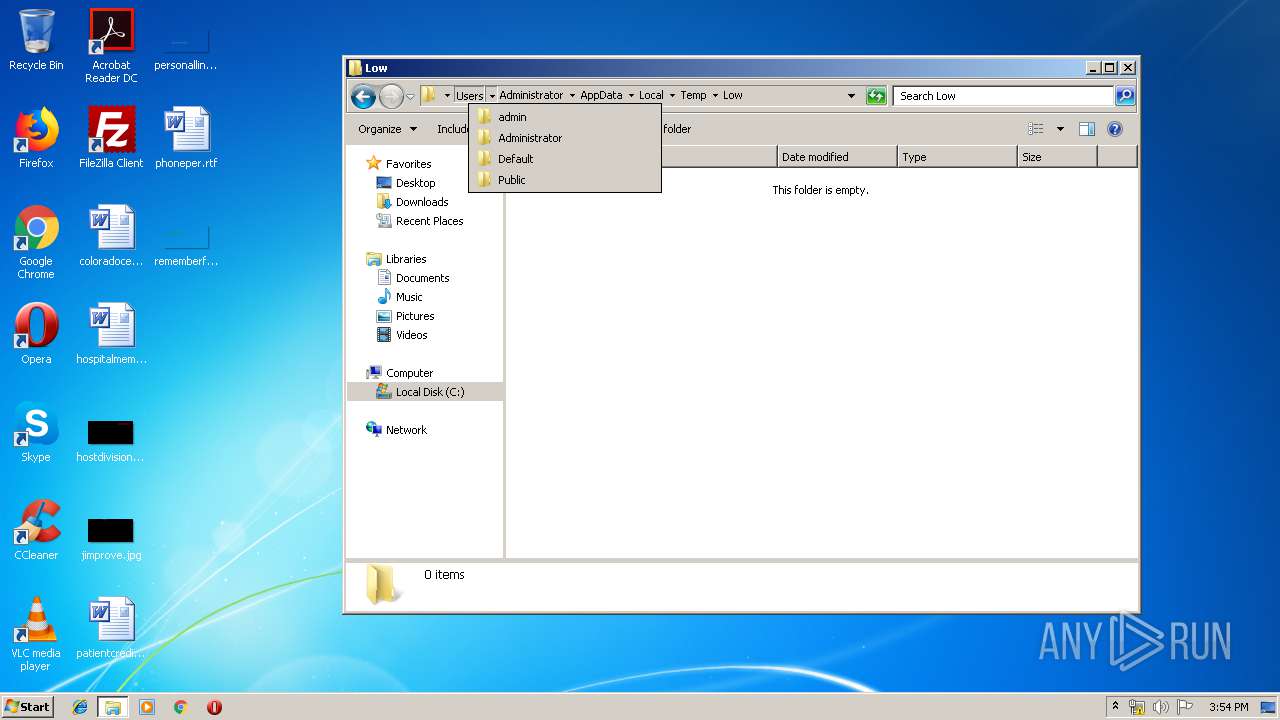
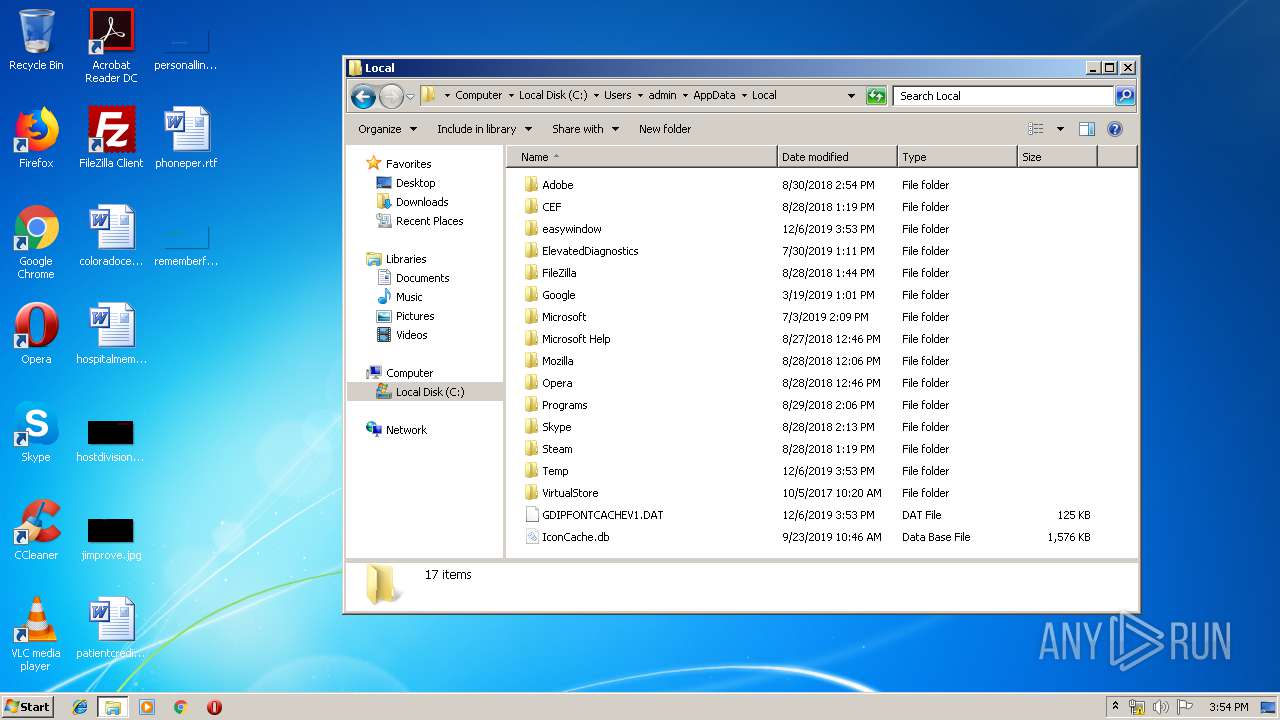
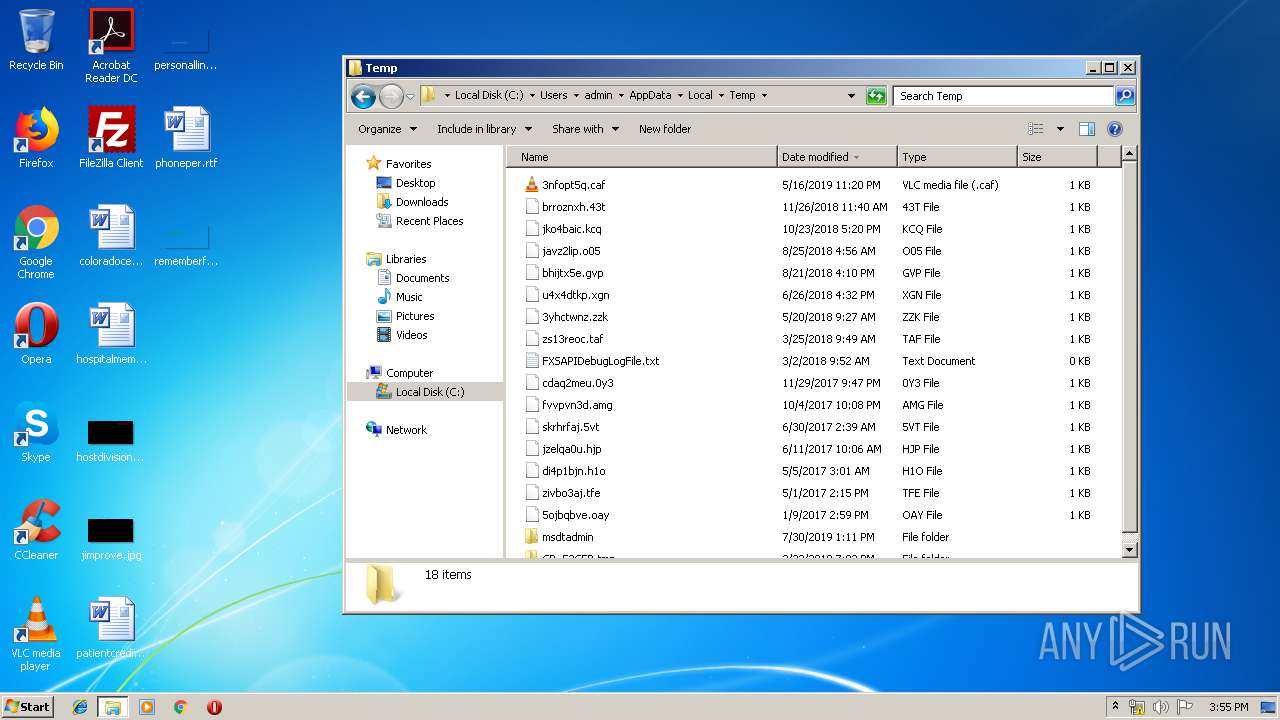
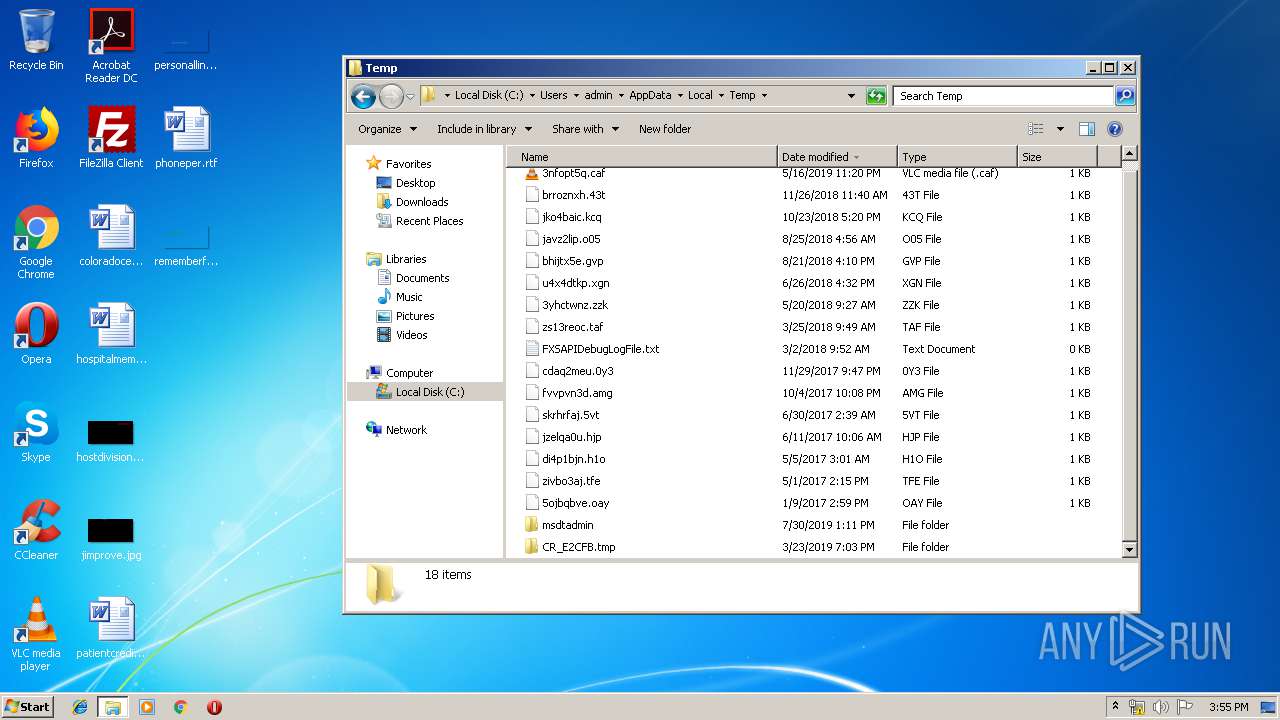
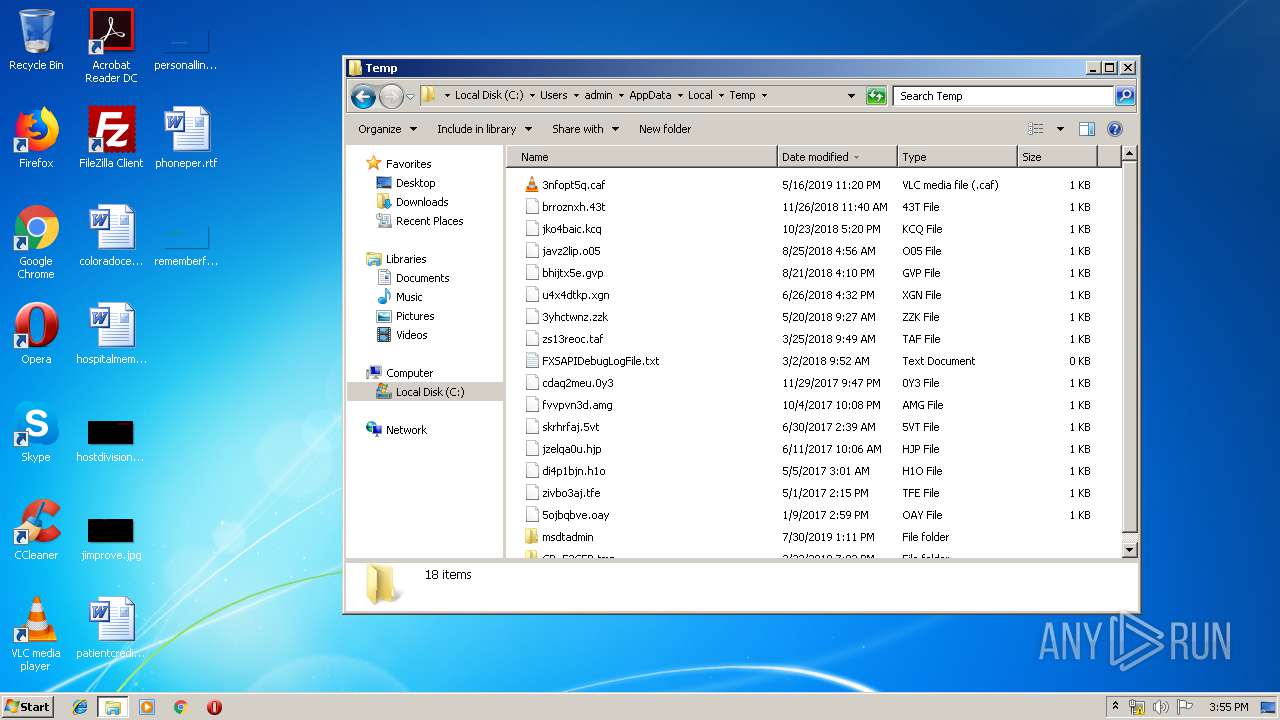
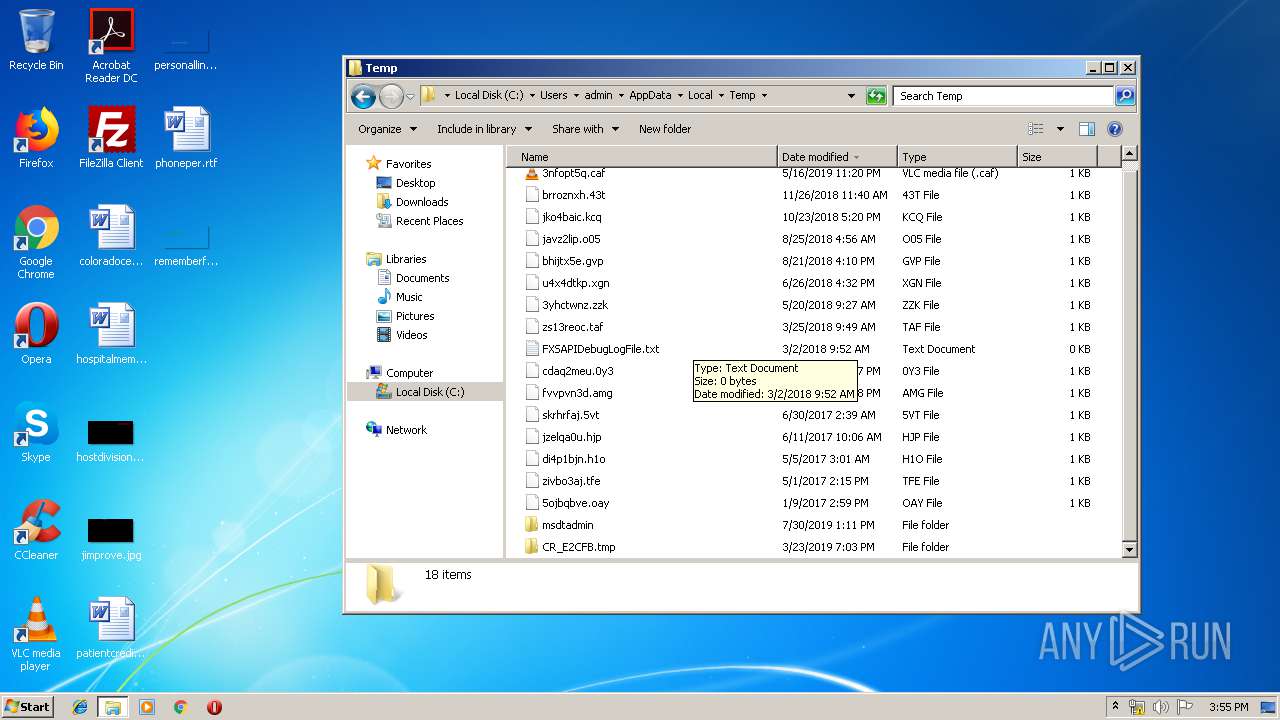
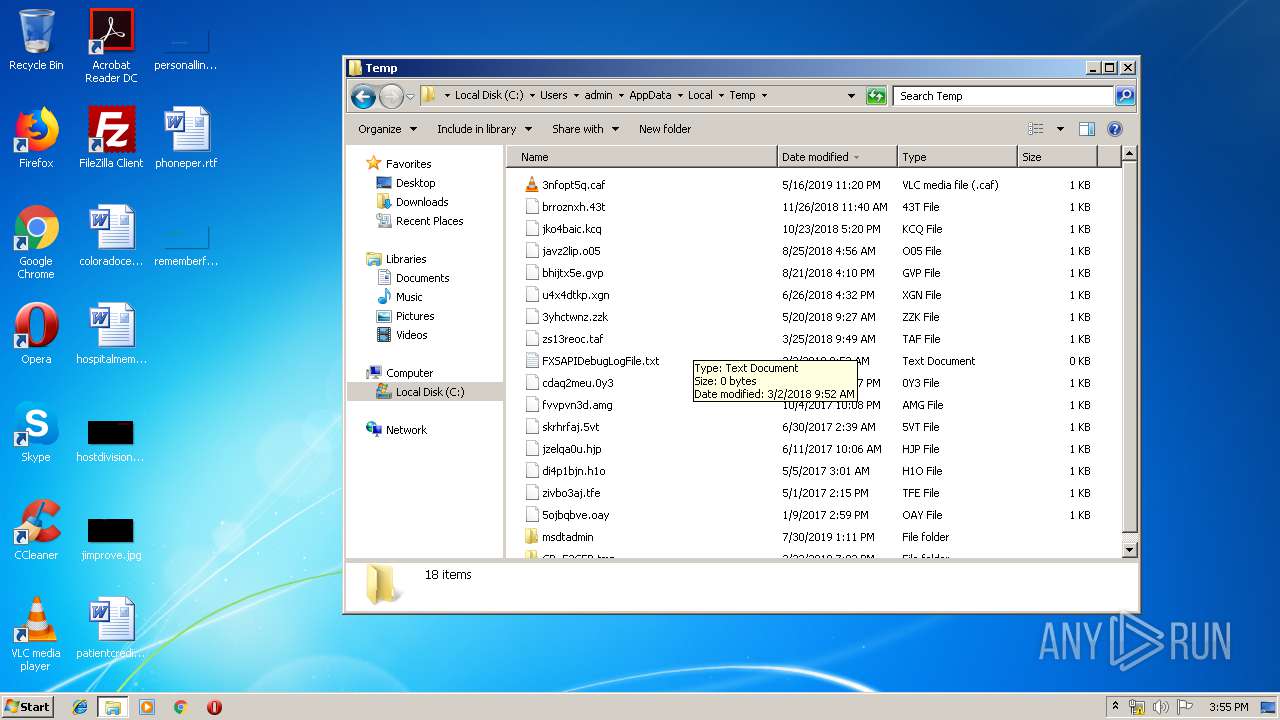
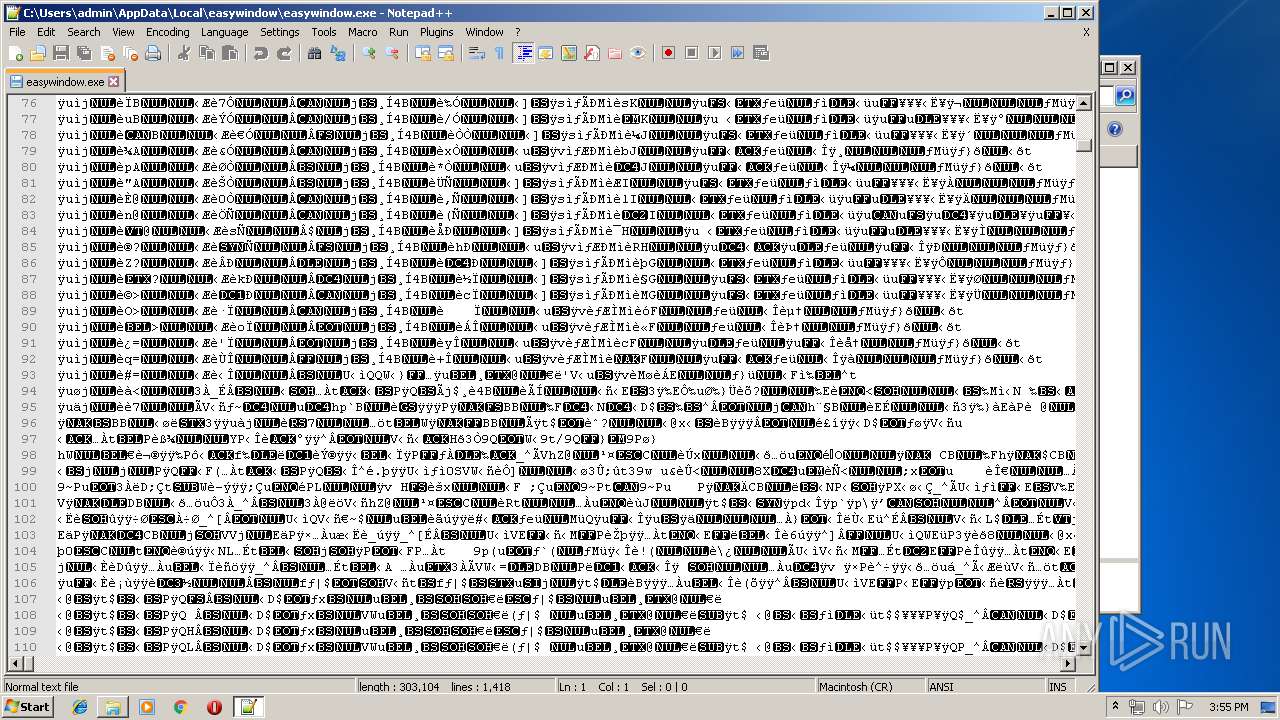
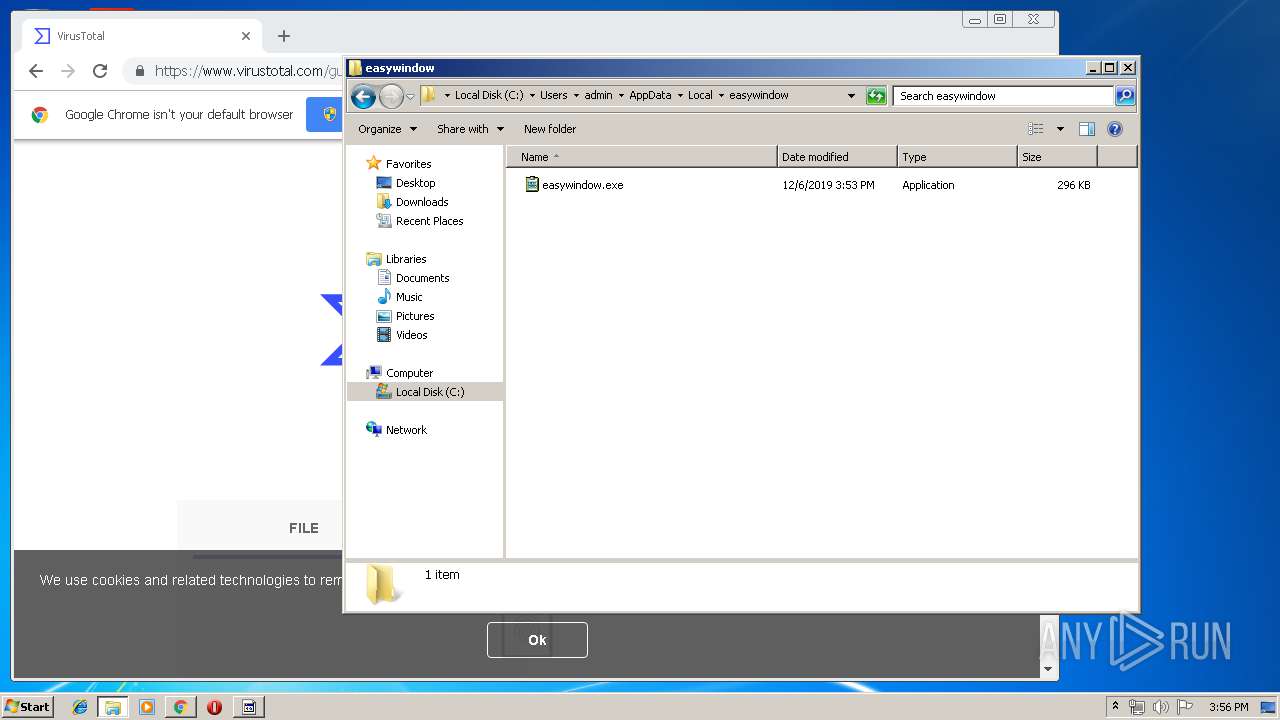
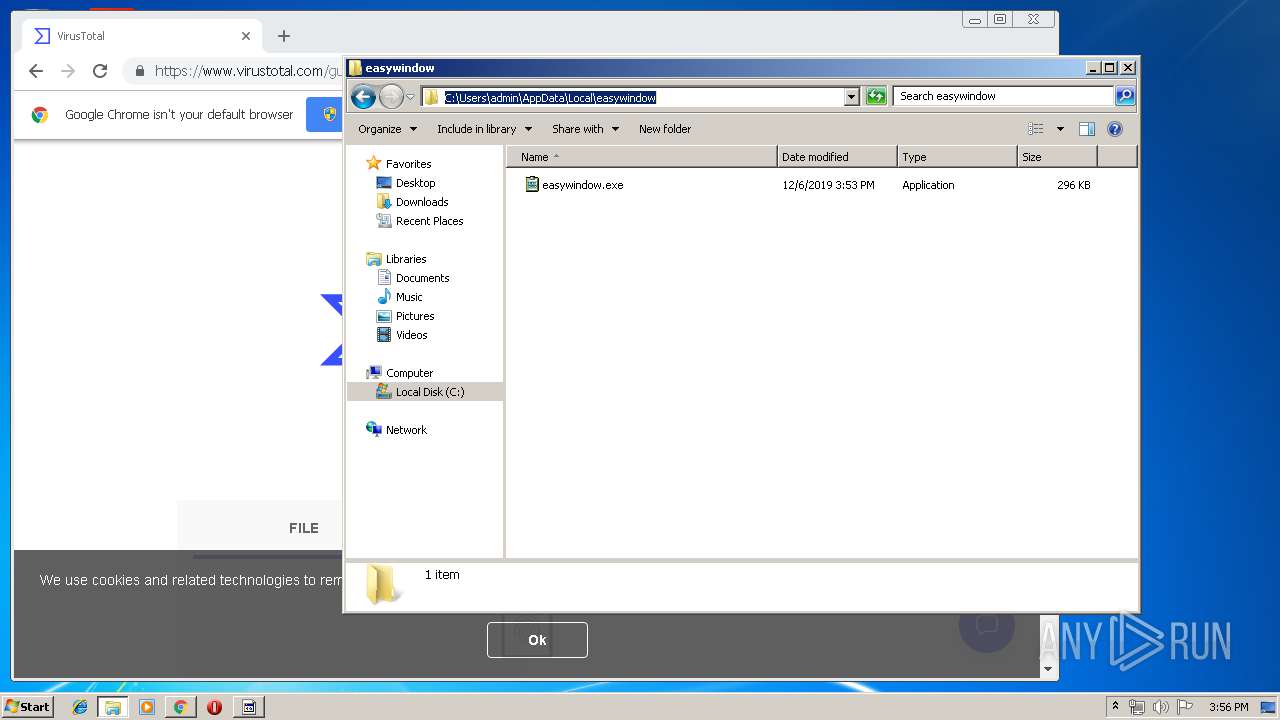
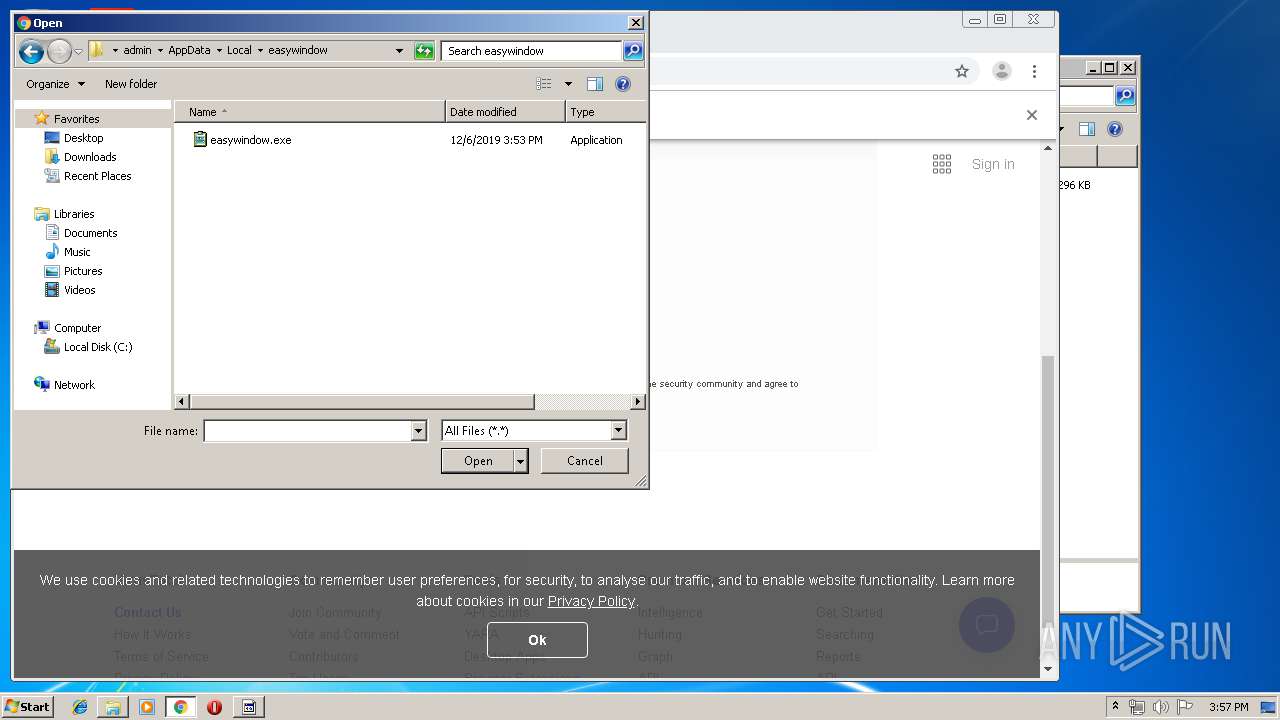
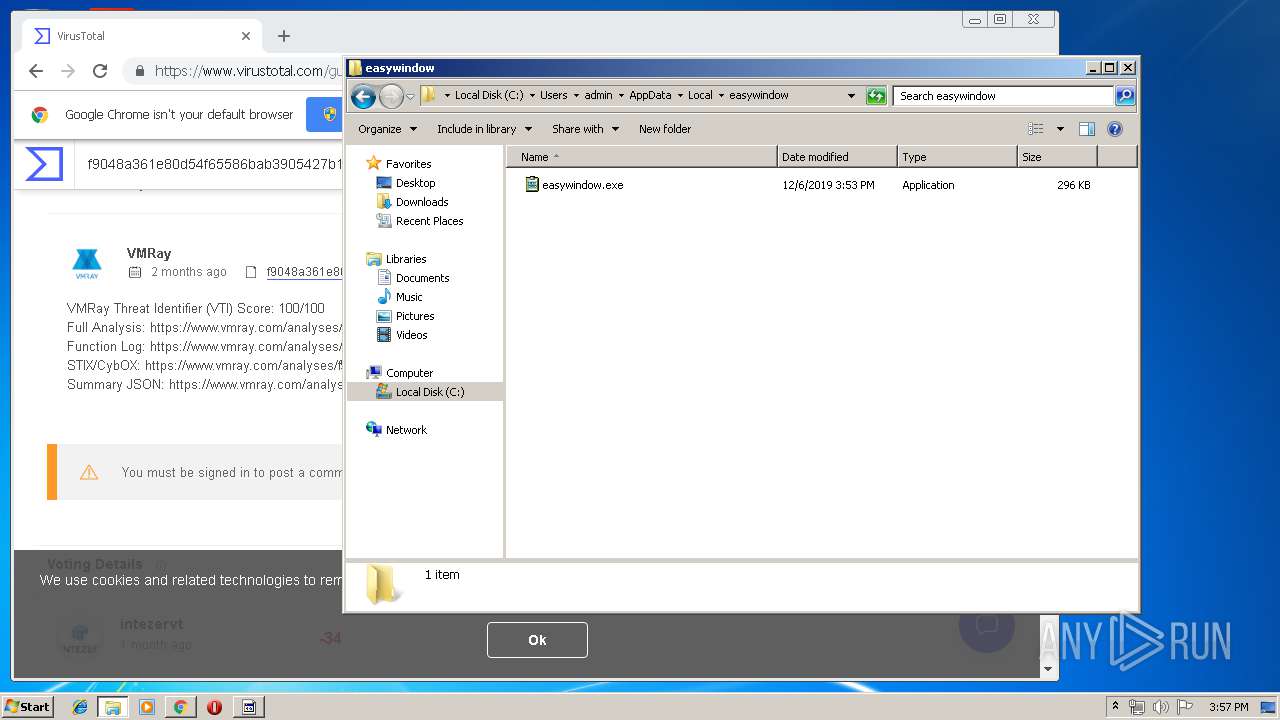
Executable content was dropped or overwritten
- gvju6u-lse19-698411.exe (PID: 564)
Connects to server without host name
- easywindow.exe (PID: 2004)
- easywindow.exe (PID: 388)
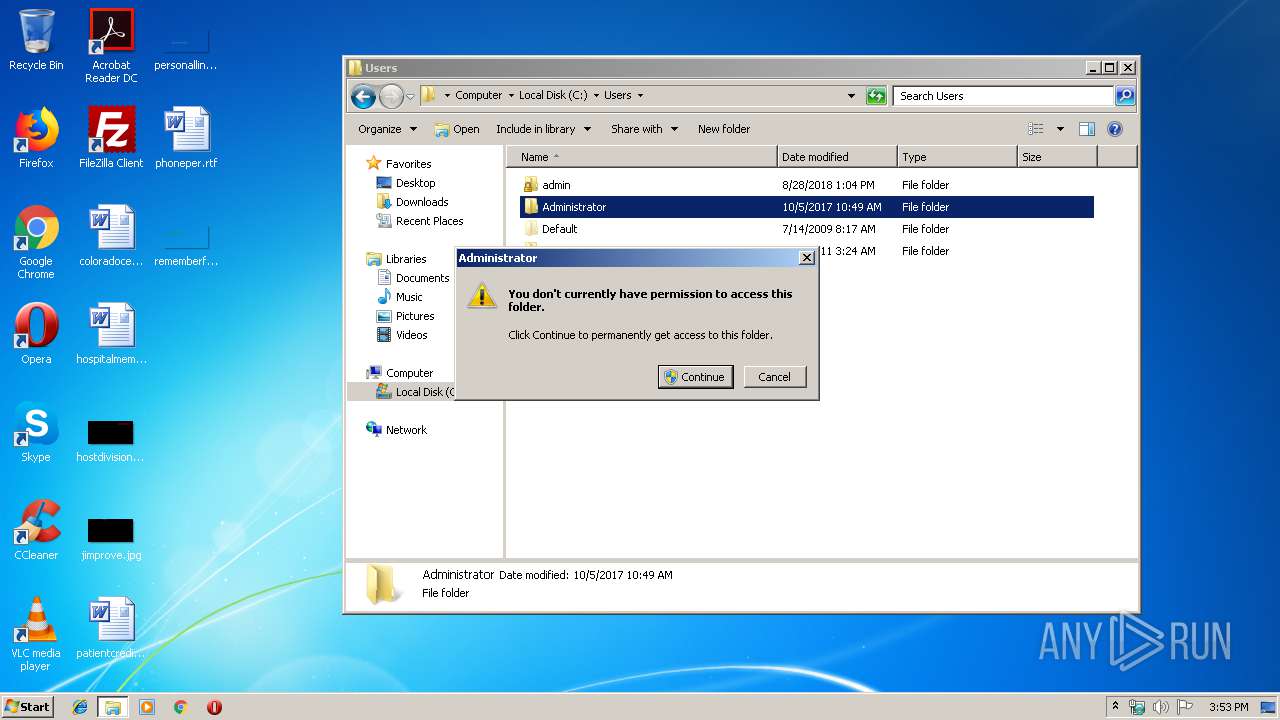
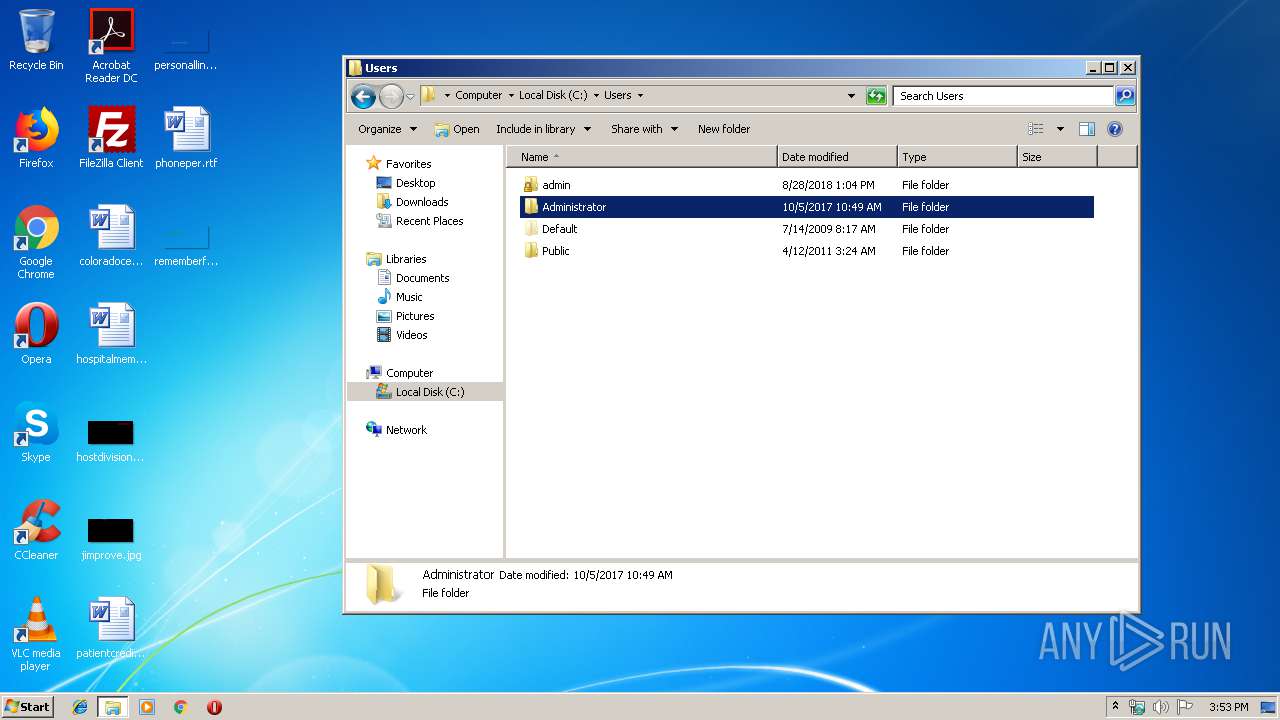
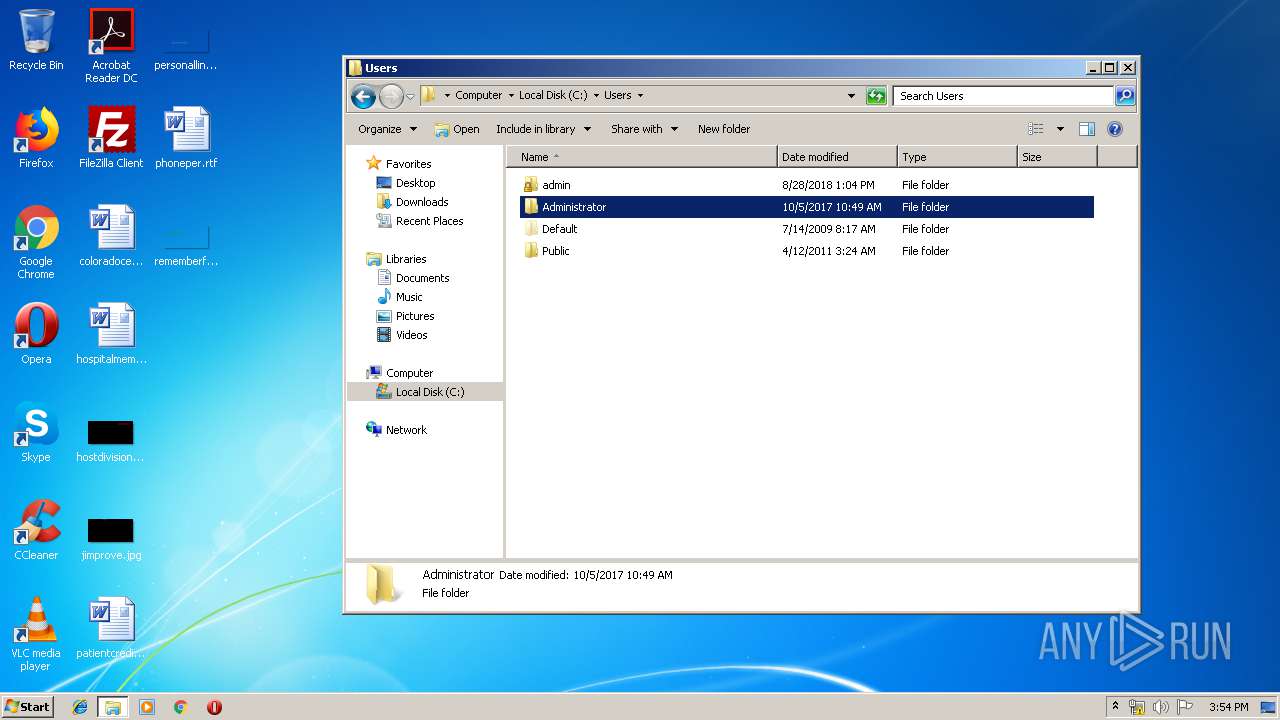
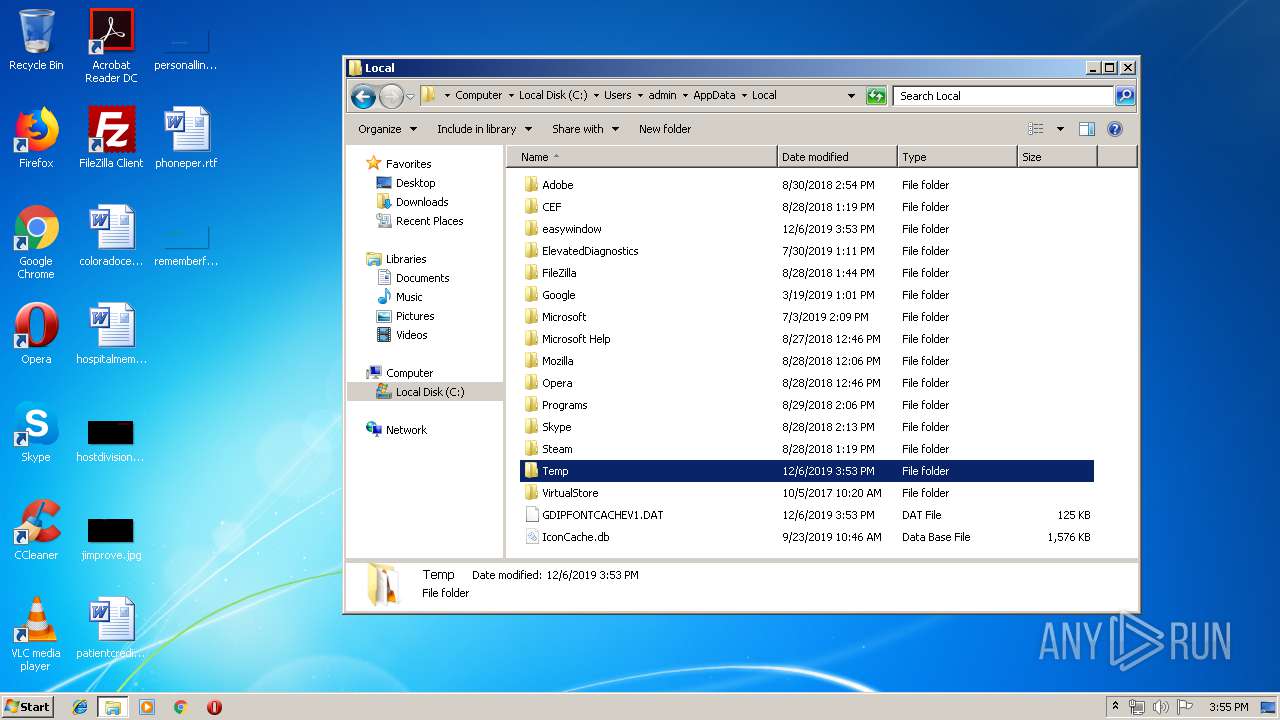
Starts itself from another location
- gvju6u-lse19-698411.exe (PID: 564)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2200)
Executed via COM
- DllHost.exe (PID: 2308)
Connects to unusual port
- easywindow.exe (PID: 2004)
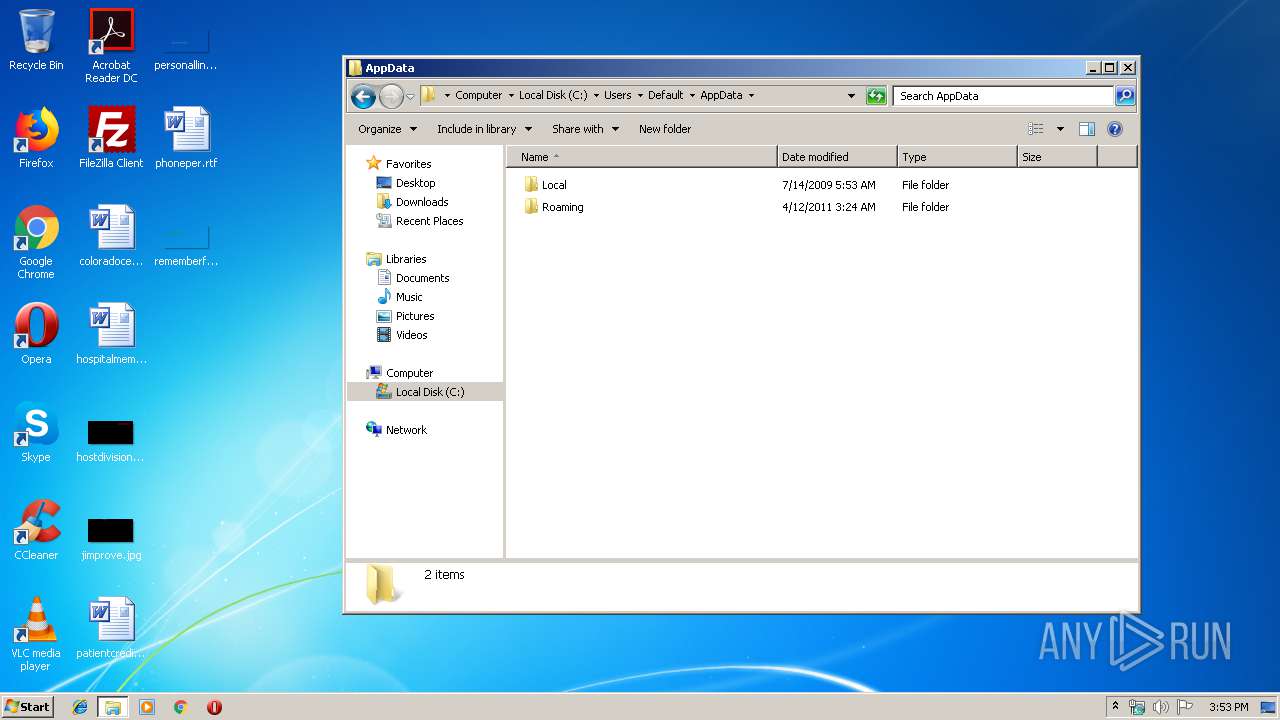
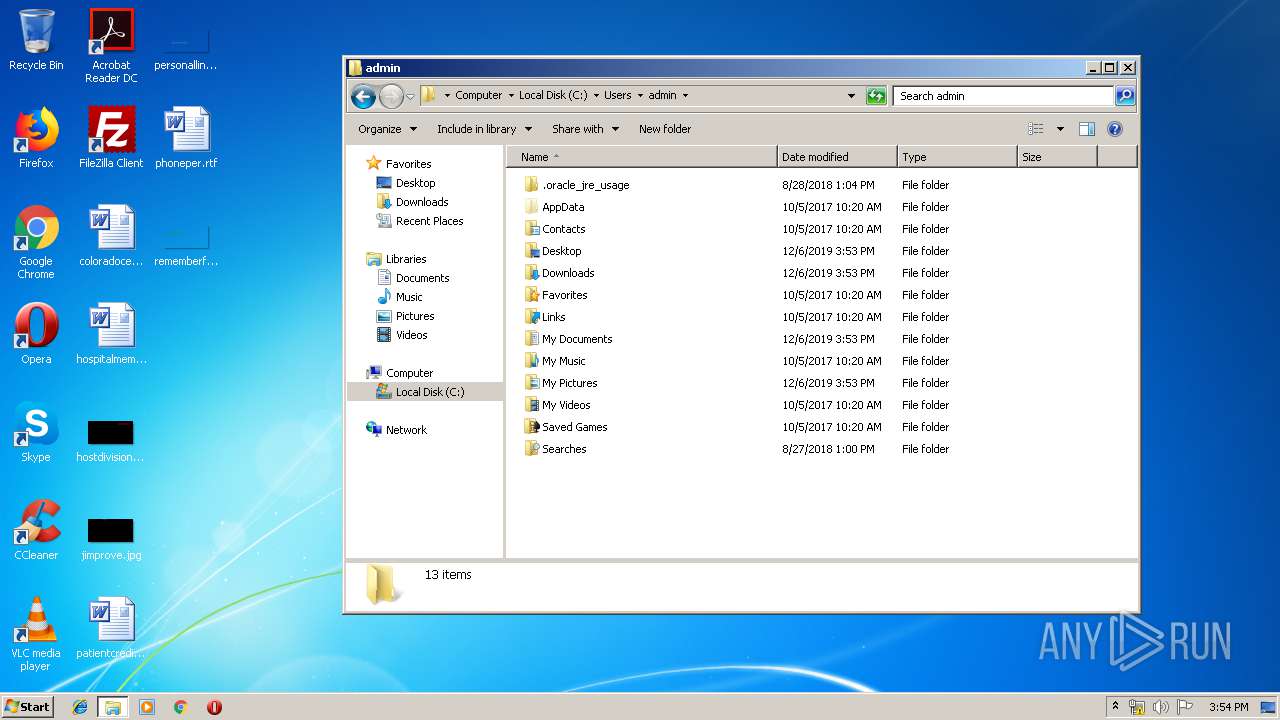
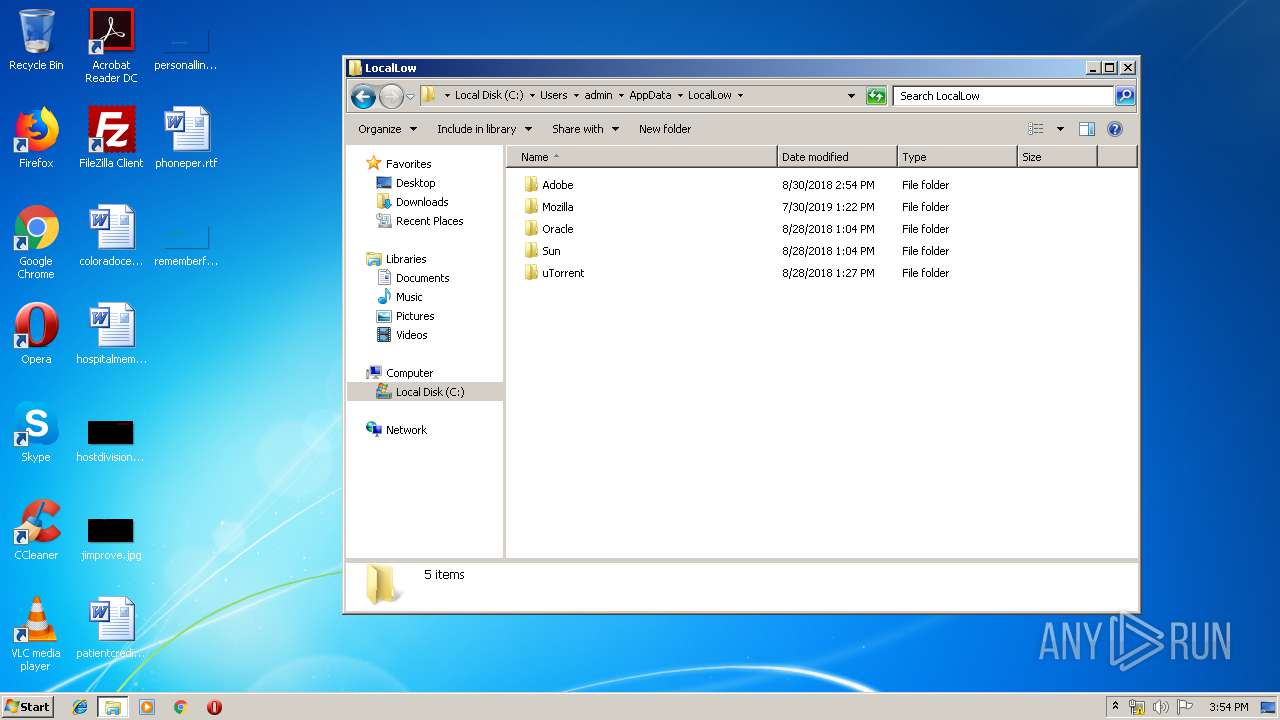
Creates files in the user directory
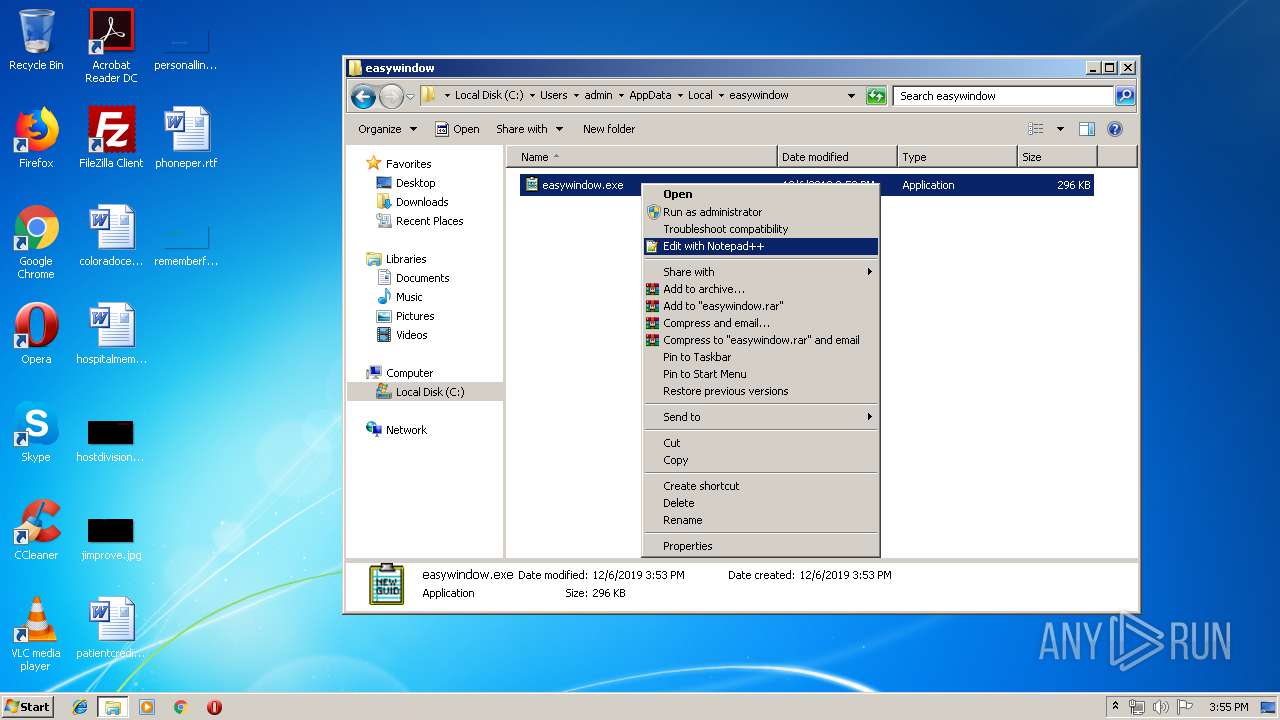
- notepad++.exe (PID: 3312)
INFO
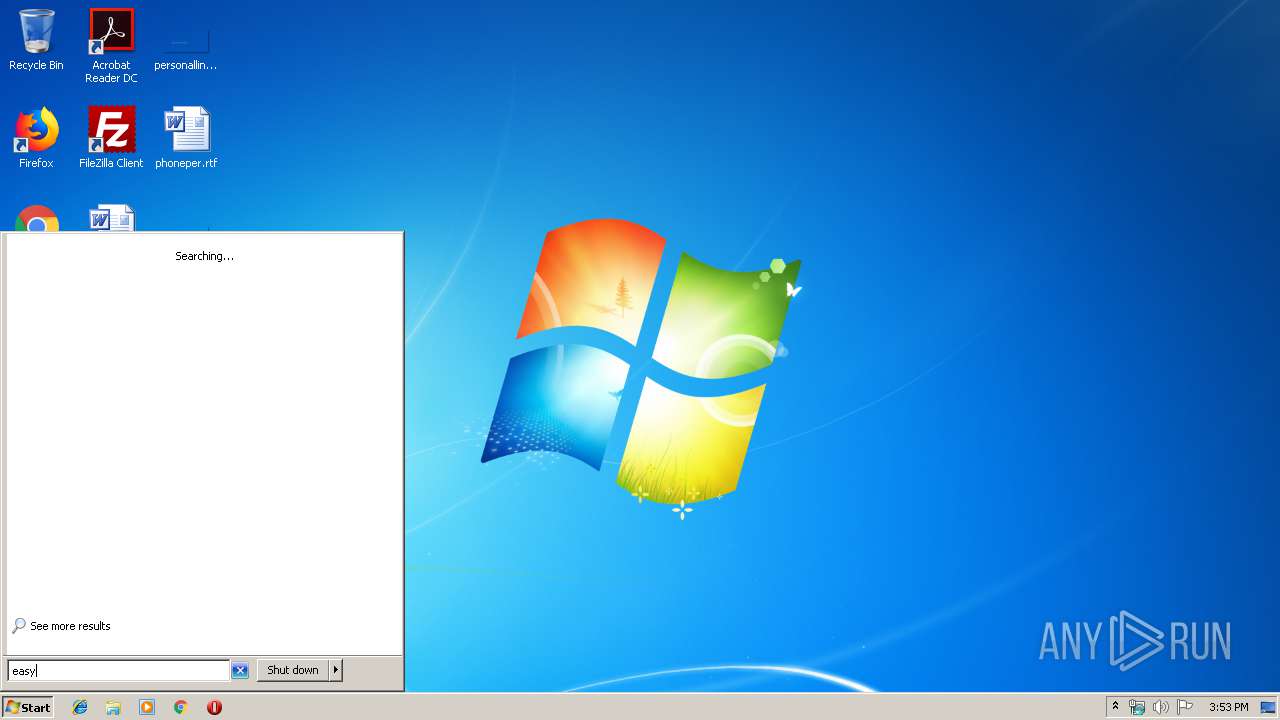
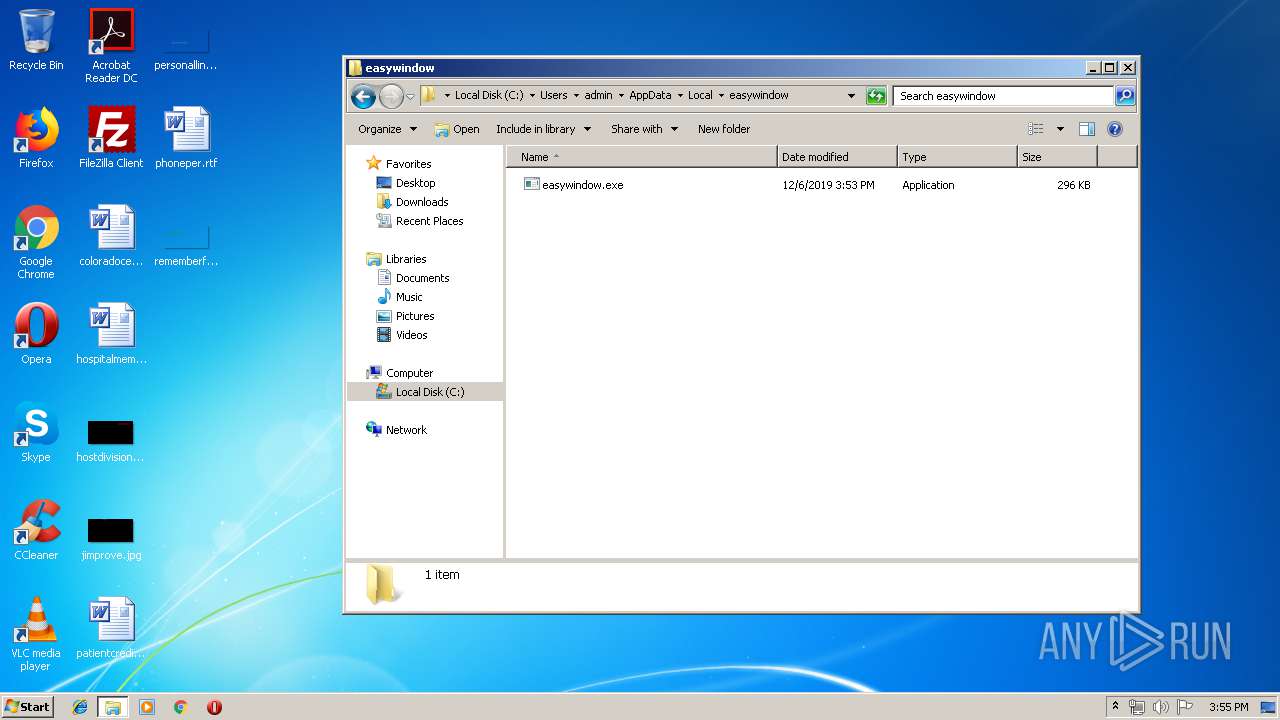
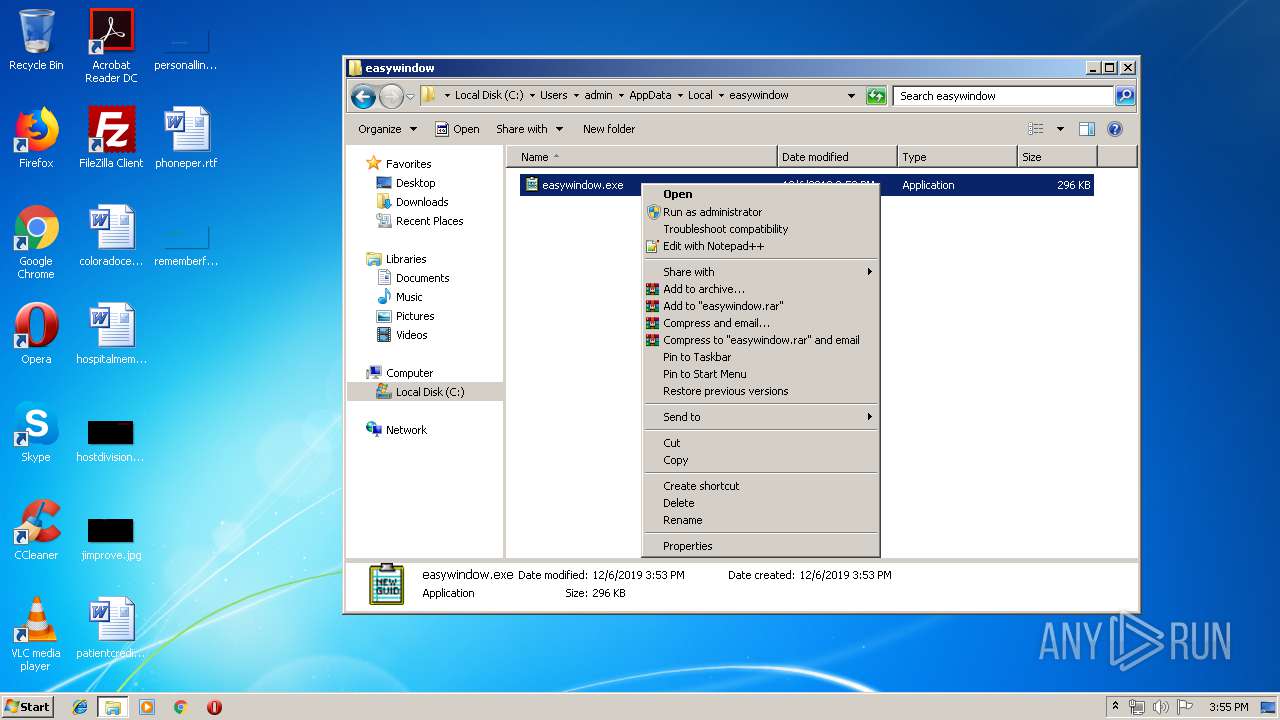
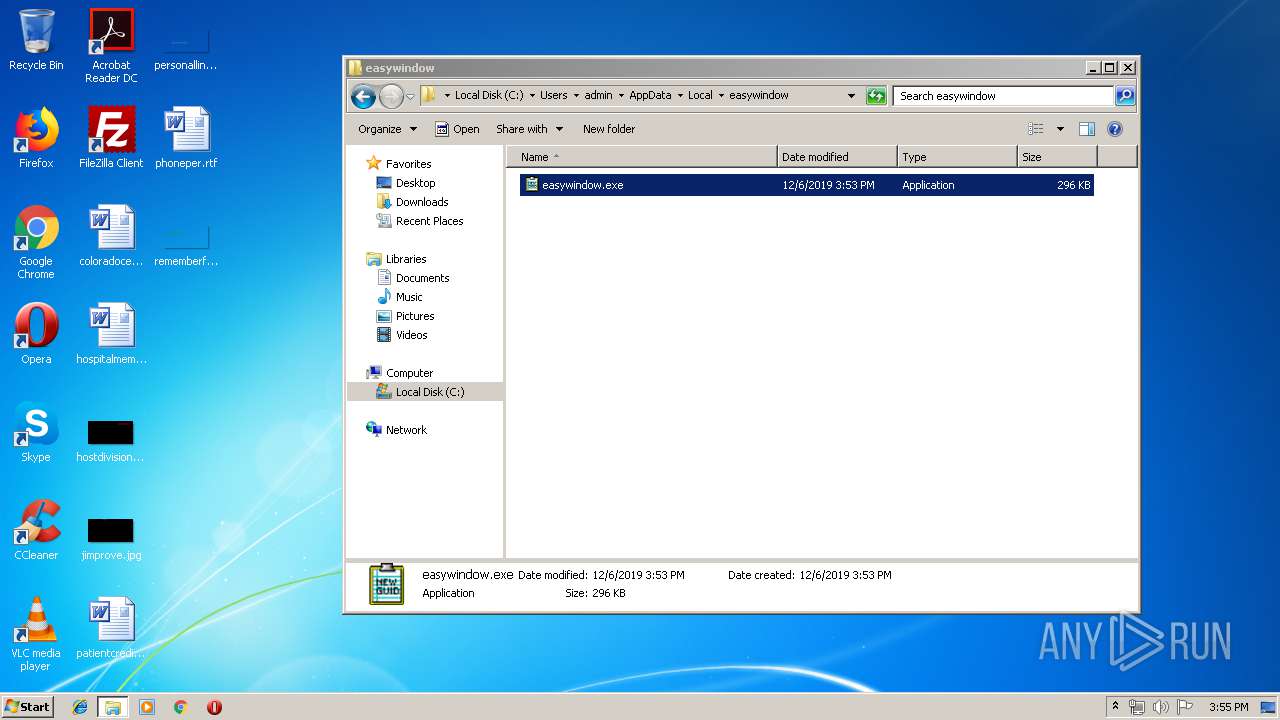
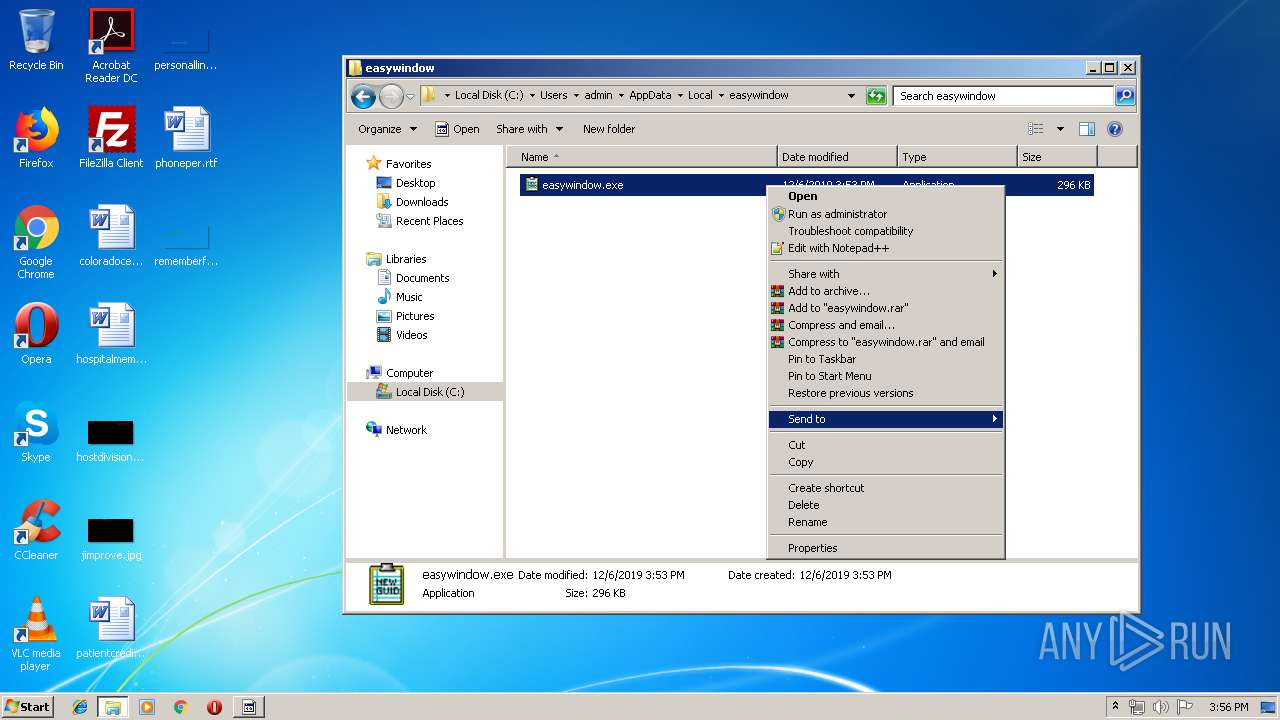
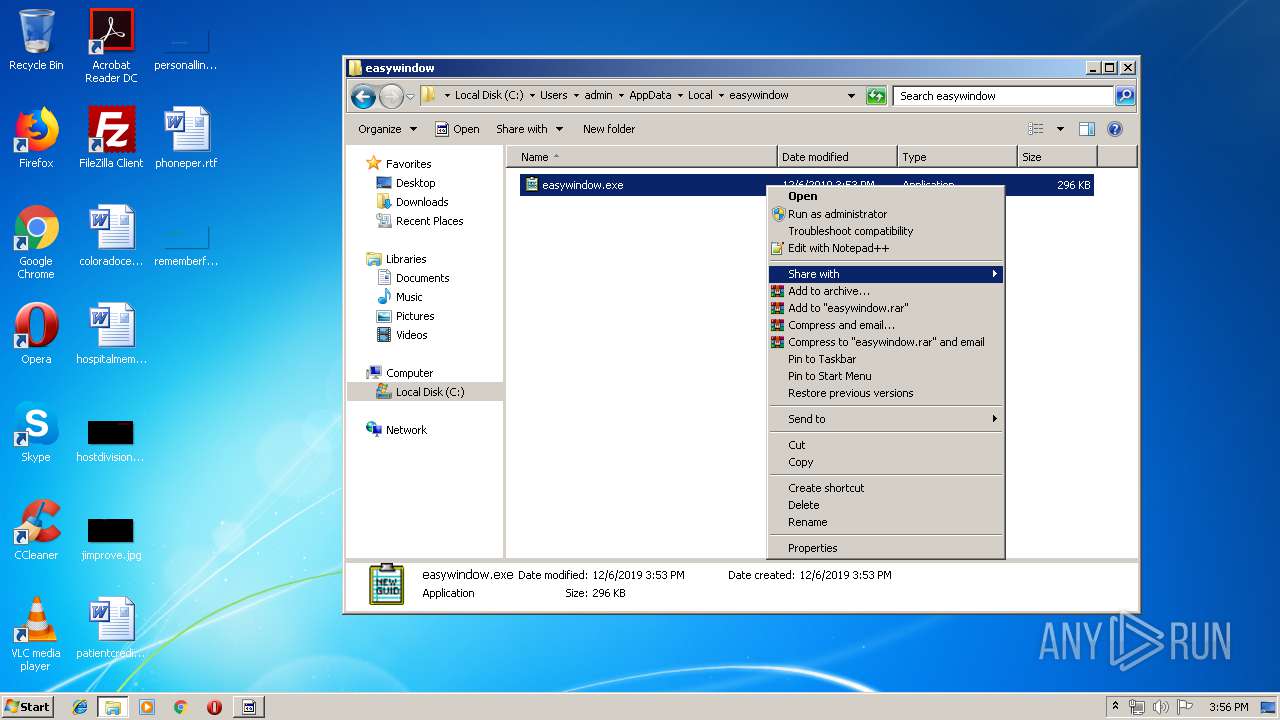
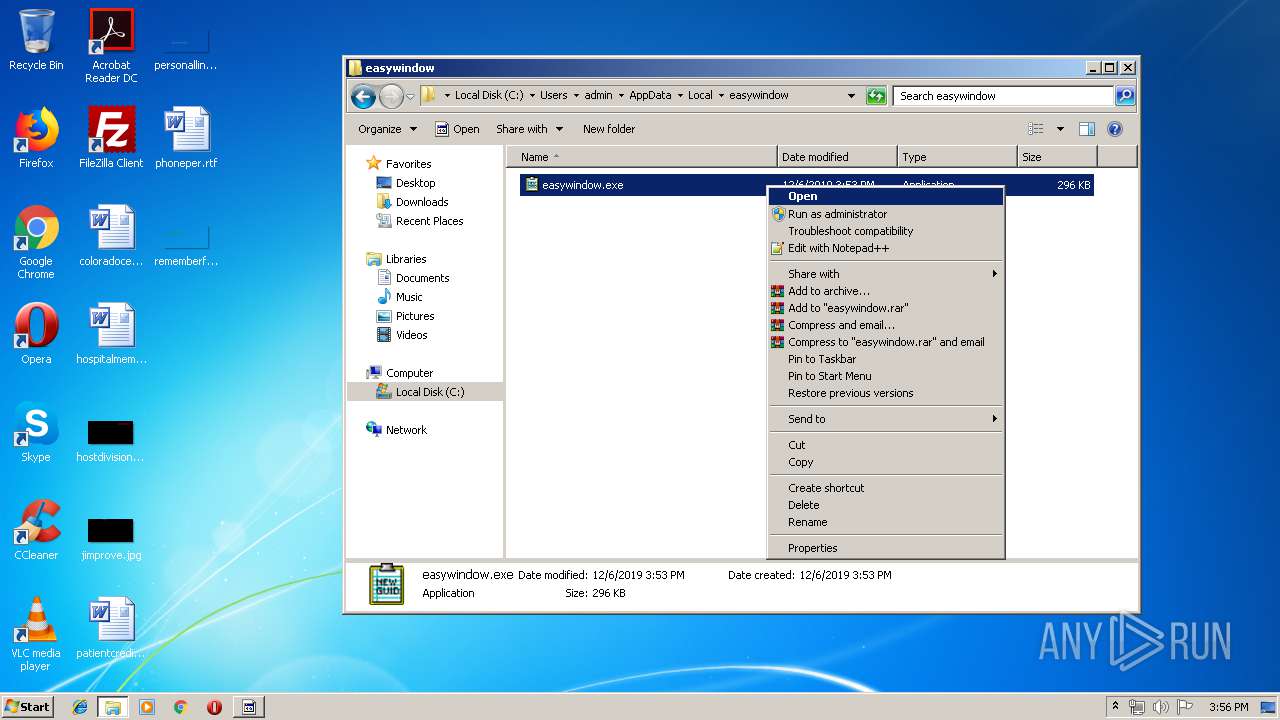
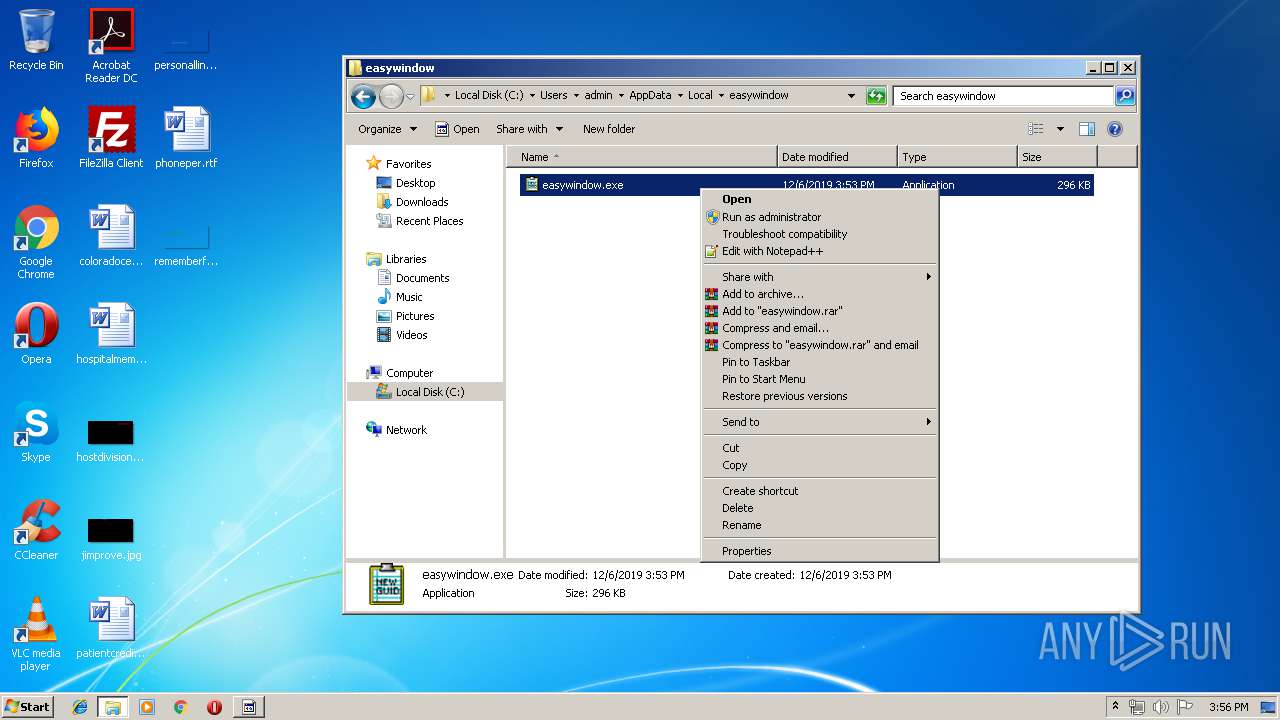
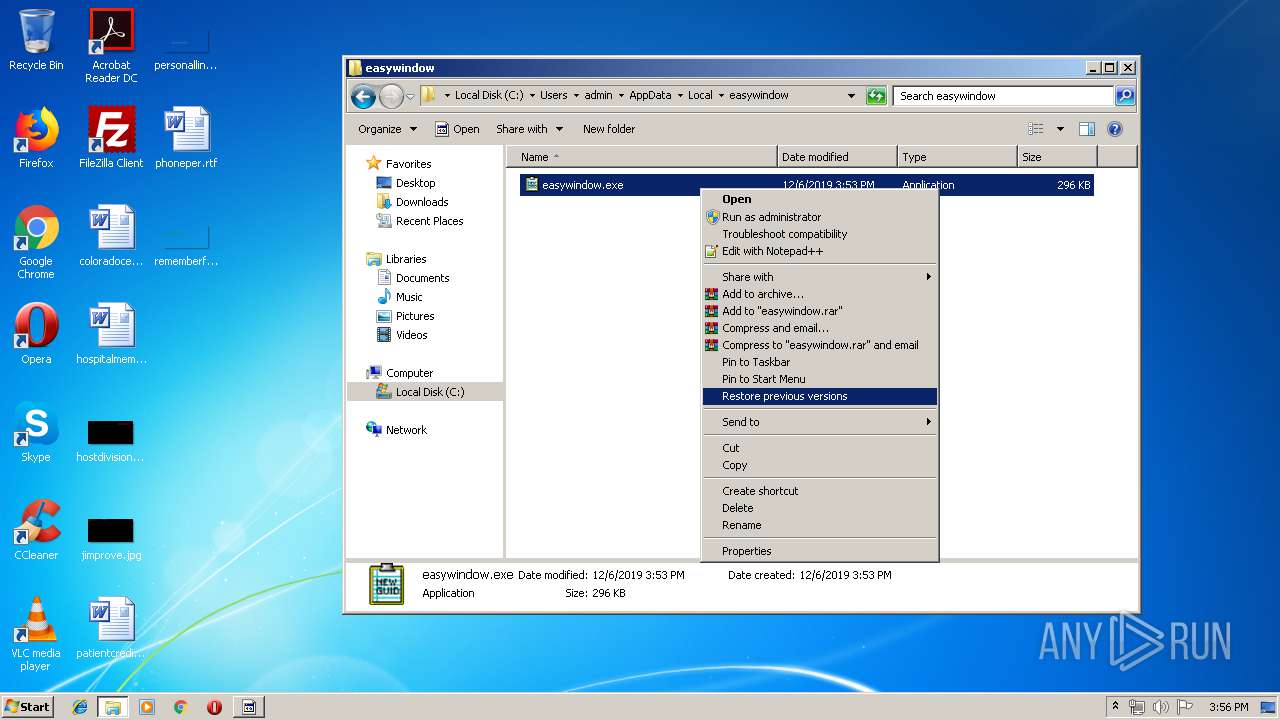
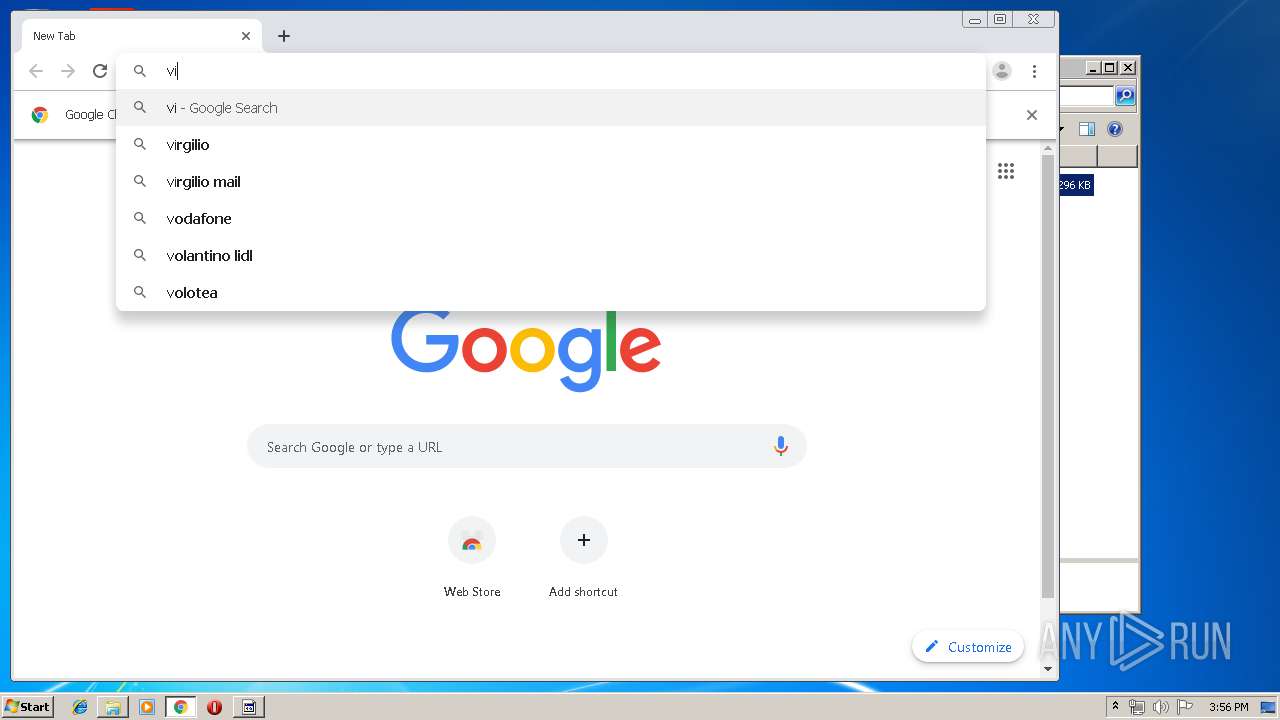
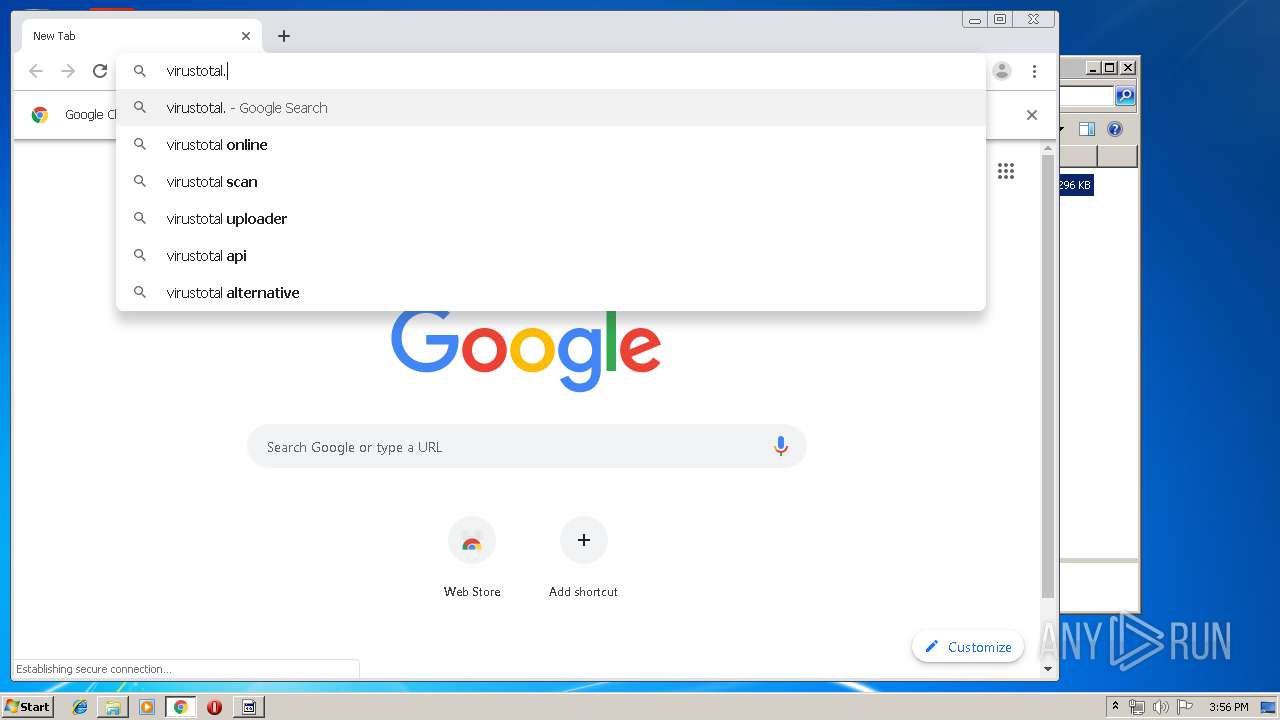
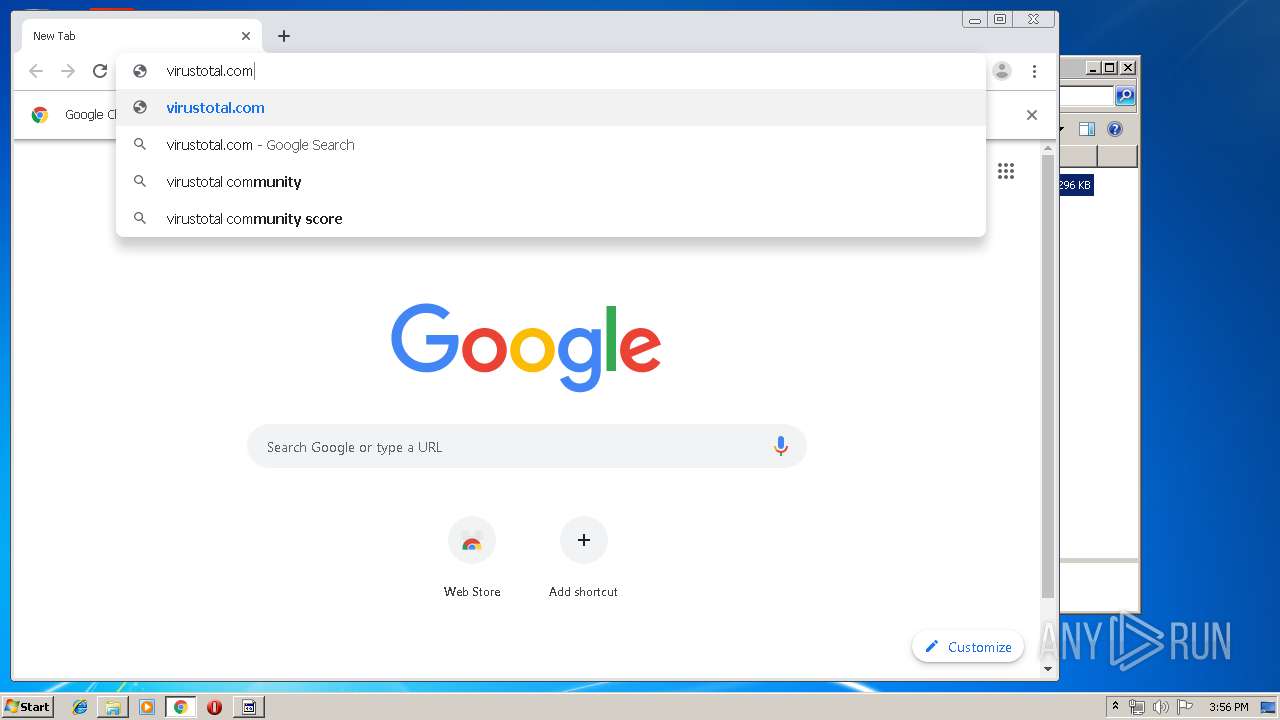
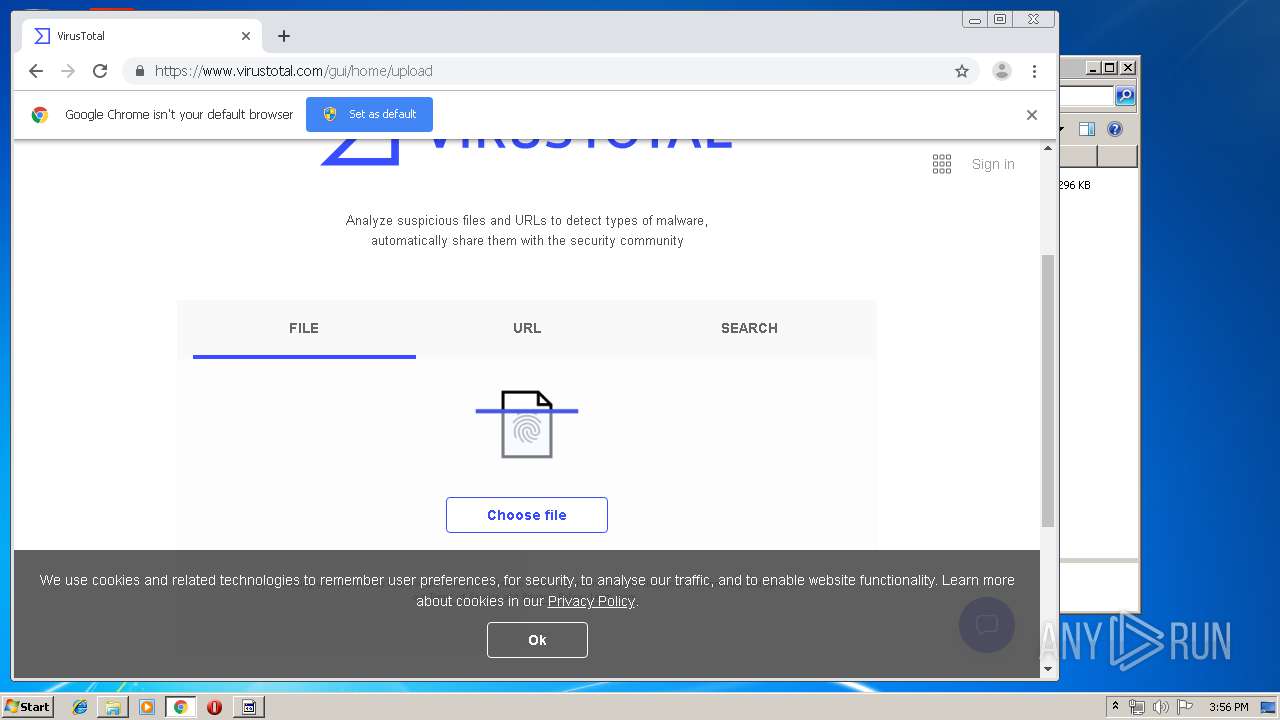
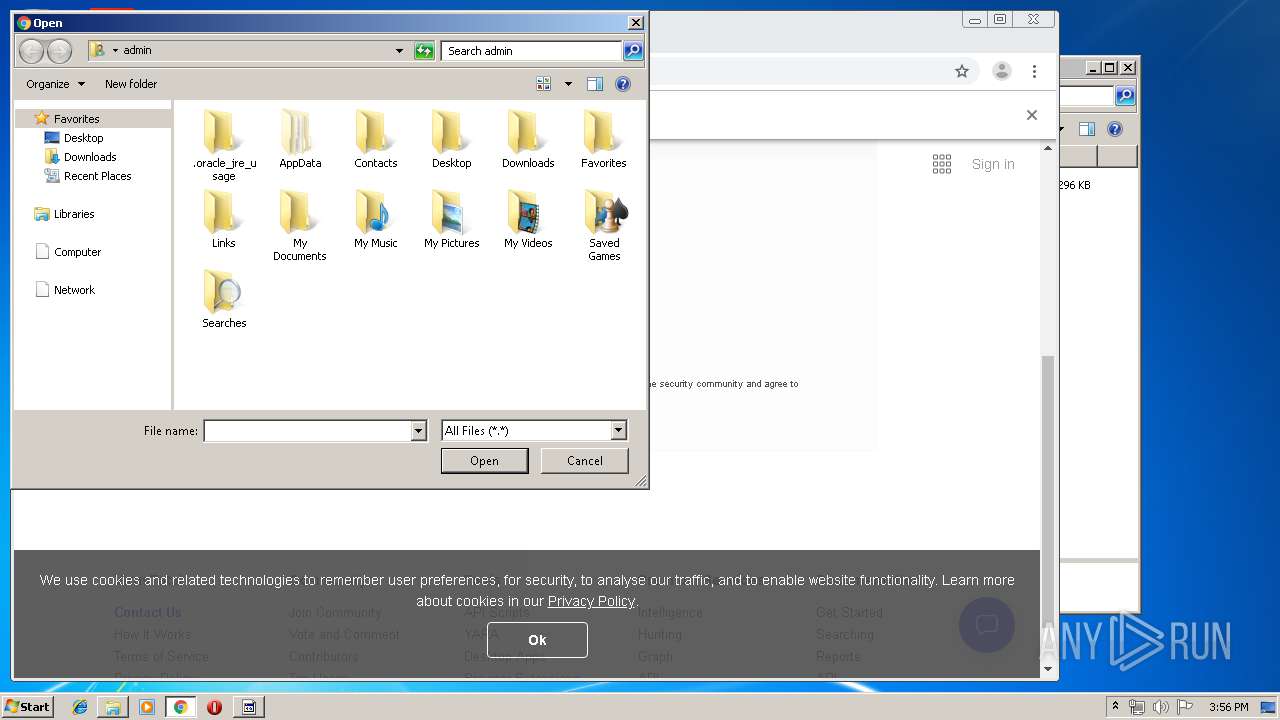
Manual execution by user
- notepad++.exe (PID: 3312)
- chrome.exe (PID: 2200)
- easywindow.exe (PID: 1800)
Application launched itself
- chrome.exe (PID: 2200)
Reads the hosts file
- chrome.exe (PID: 2200)
- chrome.exe (PID: 592)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2200)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:09:25 20:29:40+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 143360 |
| InitializedDataSize: | 155648 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x11193 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.0.9272.0 |
| ProductVersionNumber: | 7.0.9272.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | GUIDGEN MFC Application |
| FileVersion: | 7.00.9272.0 |
| InternalName: | GUIDGEN |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| ProductName: | Microsoft® Visual Studio .NET |
| OriginalFileName: | GUIDGEN.EXE |
| ProductVersion: | 7.00.9272.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Sep-2019 18:29:40 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | GUIDGEN MFC Application |
| FileVersion: | 7.00.9272.0 |
| InternalName: | GUIDGEN |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| ProductName: | Microsoft® Visual Studio .NET |
| OriginalFilename: | GUIDGEN.EXE |
| ProductVersion: | 7.00.9272.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 25-Sep-2019 18:29:40 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00022F3B | 0x00023000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.64614 |
.rdata | 0x00024000 | 0x00009122 | 0x0000A000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.92317 |
.data | 0x0002E000 | 0x00005E78 | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.83603 |
.rsrc | 0x00034000 | 0x00018682 | 0x00019000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.16963 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.65542 | 86 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.02695 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
3 | 2.74274 | 180 | Latin 1 / Western European | English - United States | RT_CURSOR |
4 | 2.56332 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
5 | 2.79381 | 180 | Latin 1 / Western European | English - United States | RT_CURSOR |
6 | 2.42654 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
7 | 3.27172 | 1228 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 2.22891 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
9 | 2.39122 | 180 | Latin 1 / Western European | English - United States | RT_CURSOR |
10 | 3.59889 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
OLEACC.dll (delay-loaded) |
OLEAUT32.dll |
RPCRT4.dll |
SHLWAPI.dll |
USER32.dll |
WINSPOOL.DRV |
ole32.dll |
Total processes
94
Monitored processes
48
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
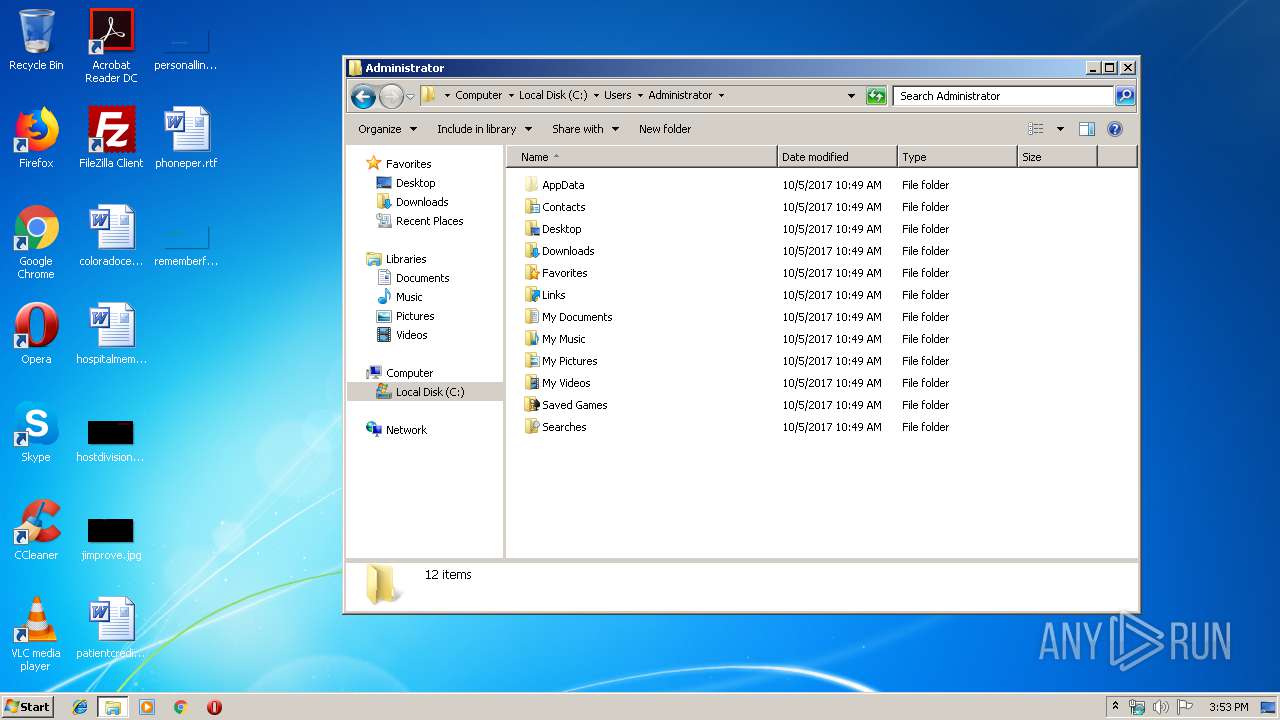
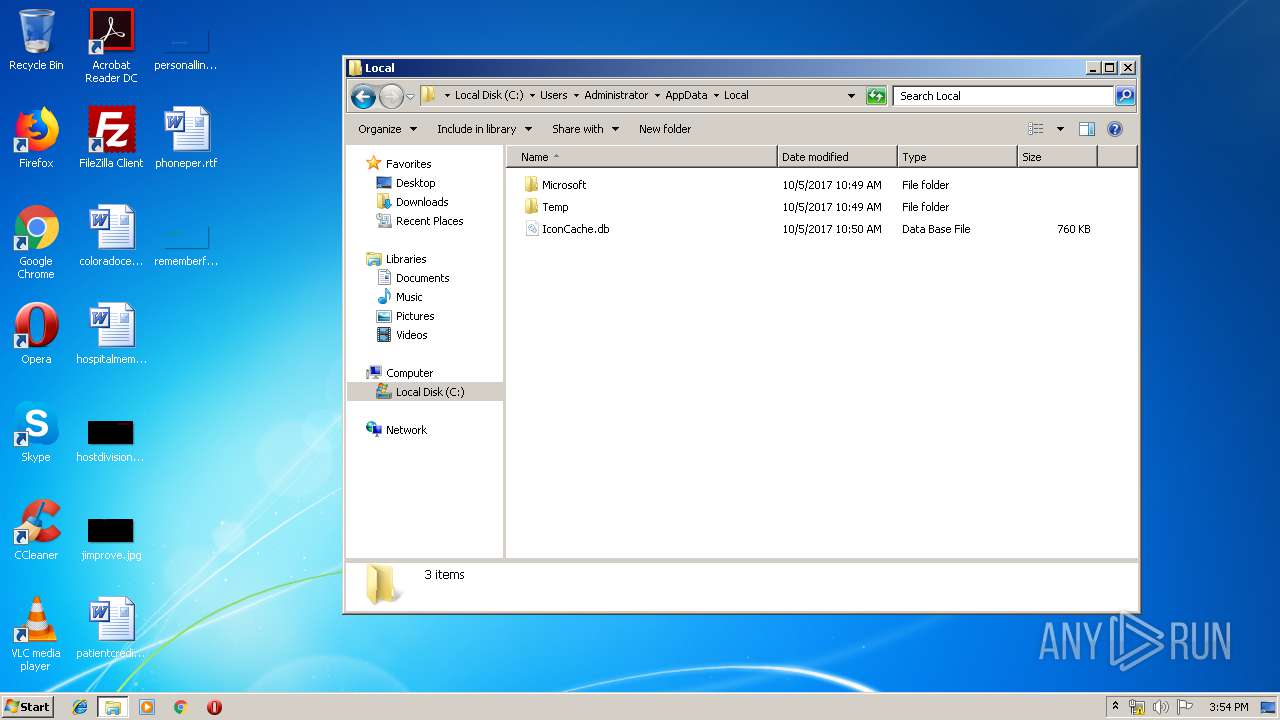
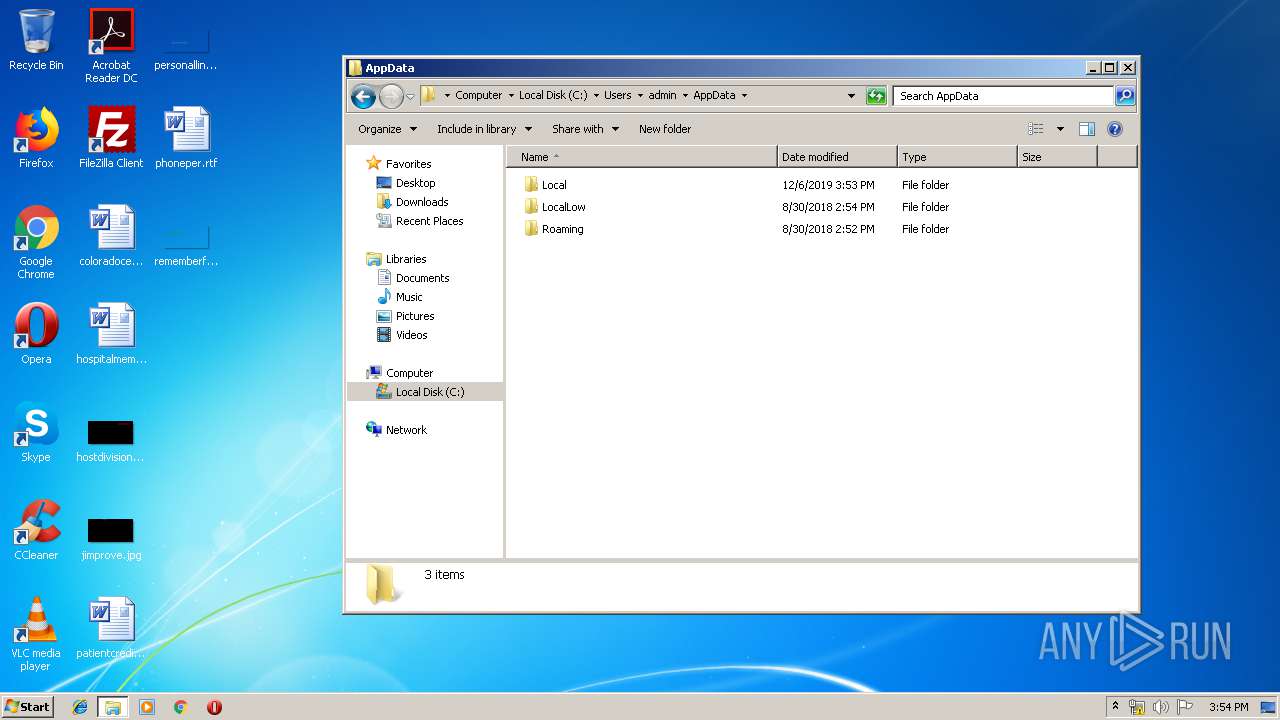
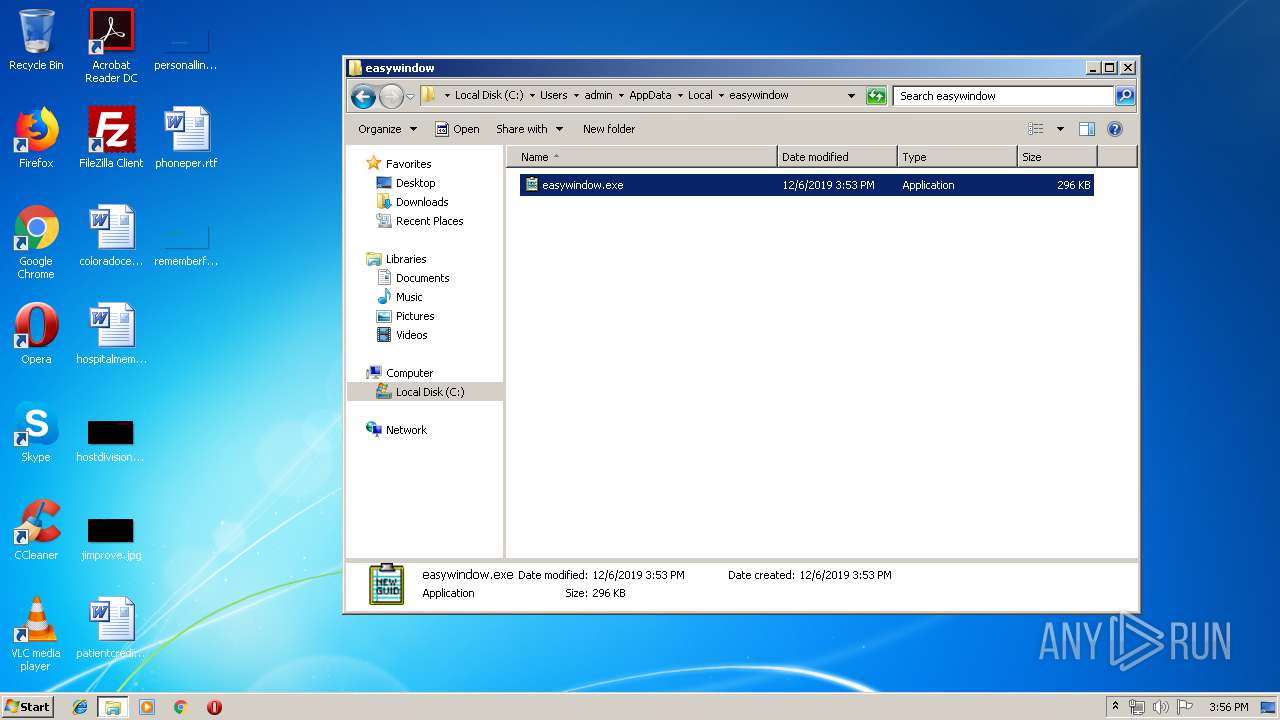
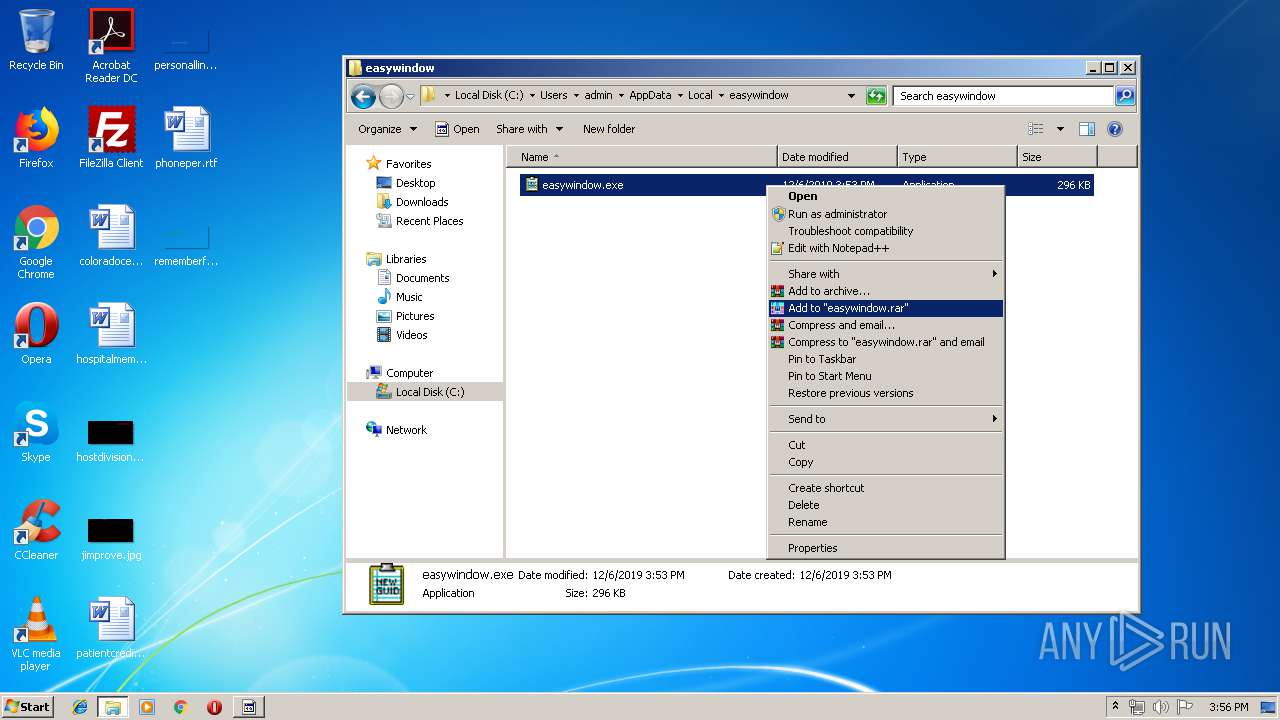
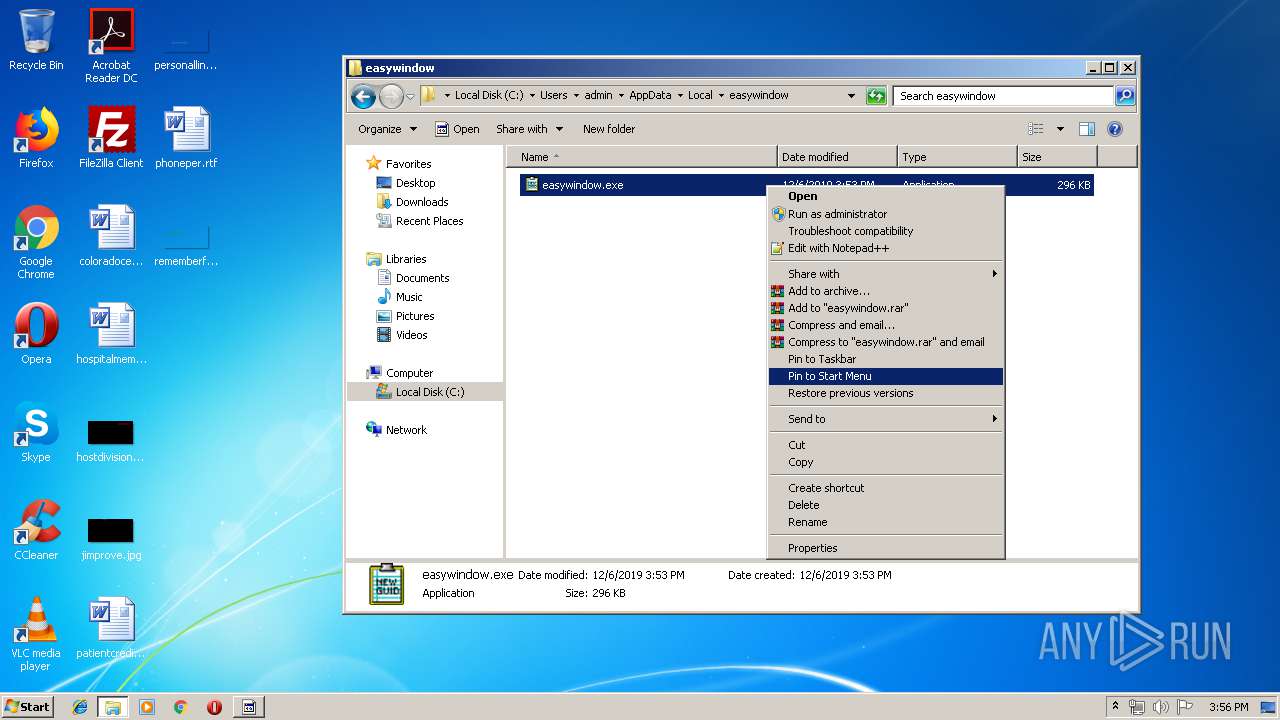
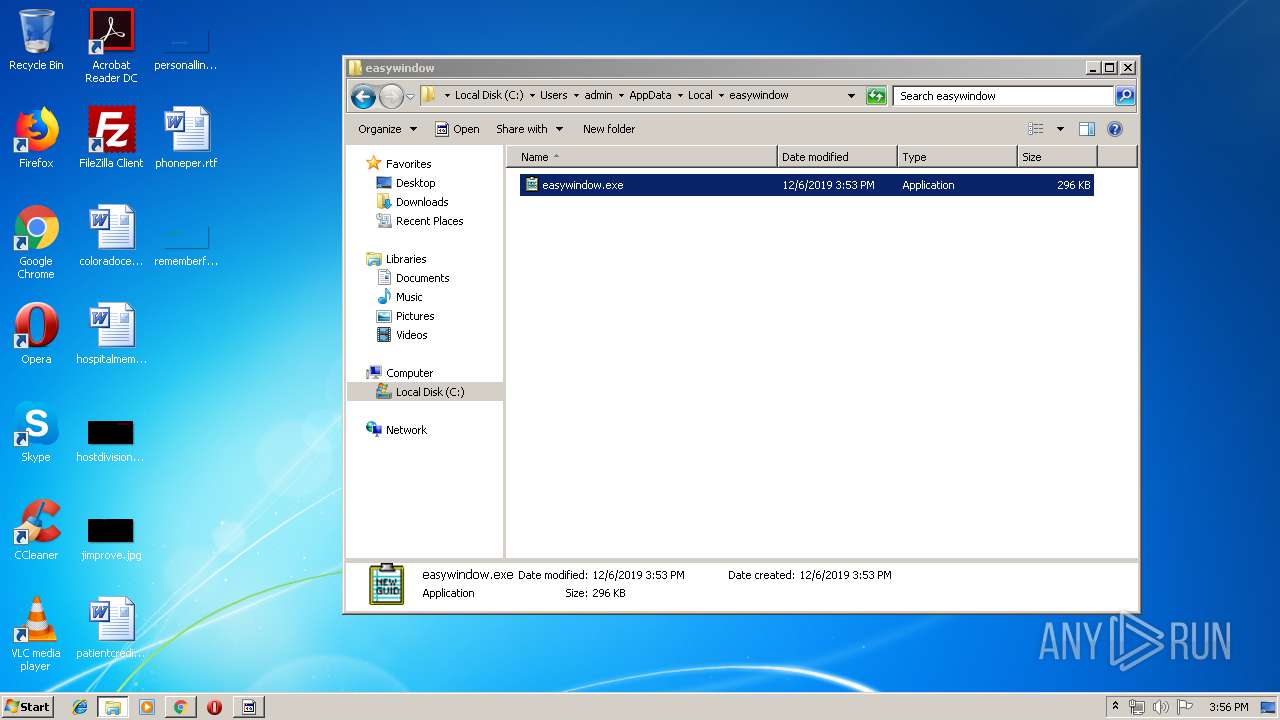
| 328 | "C:\Users\admin\AppData\Local\easywindow\easywindow.exe" | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | — | easywindow.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: GUIDGEN MFC Application Exit code: 0 Version: 7.00.9272.0 Modules
| |||||||||||||||
| 388 | --fd47f3b8 | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | easywindow.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: GUIDGEN MFC Application Exit code: 0 Version: 7.00.9272.0 Modules
| |||||||||||||||
| 444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1012,15799783092362184697,18041497087479547387,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9819019533618023176 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3628 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 564 | --fade2f3e | C:\Users\admin\AppData\Local\Temp\gvju6u-lse19-698411.exe | gvju6u-lse19-698411.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: GUIDGEN MFC Application Exit code: 0 Version: 7.00.9272.0 Modules
| |||||||||||||||
| 592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,15799783092362184697,18041497087479547387,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=16476959551645724917 --mojo-platform-channel-handle=1636 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1012,15799783092362184697,18041497087479547387,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=11098479315036048796 --mojo-platform-channel-handle=2760 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,15799783092362184697,18041497087479547387,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13807713375407626466 --mojo-platform-channel-handle=3844 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,15799783092362184697,18041497087479547387,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4355413977177590769 --mojo-platform-channel-handle=4248 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1012,15799783092362184697,18041497087479547387,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=232999082990162833 --mojo-platform-channel-handle=3492 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1784 | --fd47f3b8 | C:\Users\admin\AppData\Local\easywindow\easywindow.exe | — | easywindow.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: GUIDGEN MFC Application Exit code: 0 Version: 7.00.9272.0 Modules
| |||||||||||||||
Total events
1 622
Read events
1 361
Write events
255
Delete events
6
Modification events
| (PID) Process: | (2004) easywindow.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\easywindow_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2004) easywindow.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\easywindow_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2004) easywindow.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\easywindow_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2004) easywindow.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\easywindow_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2004) easywindow.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\easywindow_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2004) easywindow.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\easywindow_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2004) easywindow.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\easywindow_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2004) easywindow.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\easywindow_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2004) easywindow.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\easywindow_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2004) easywindow.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
Executable files
1
Suspicious files
48
Text files
256
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
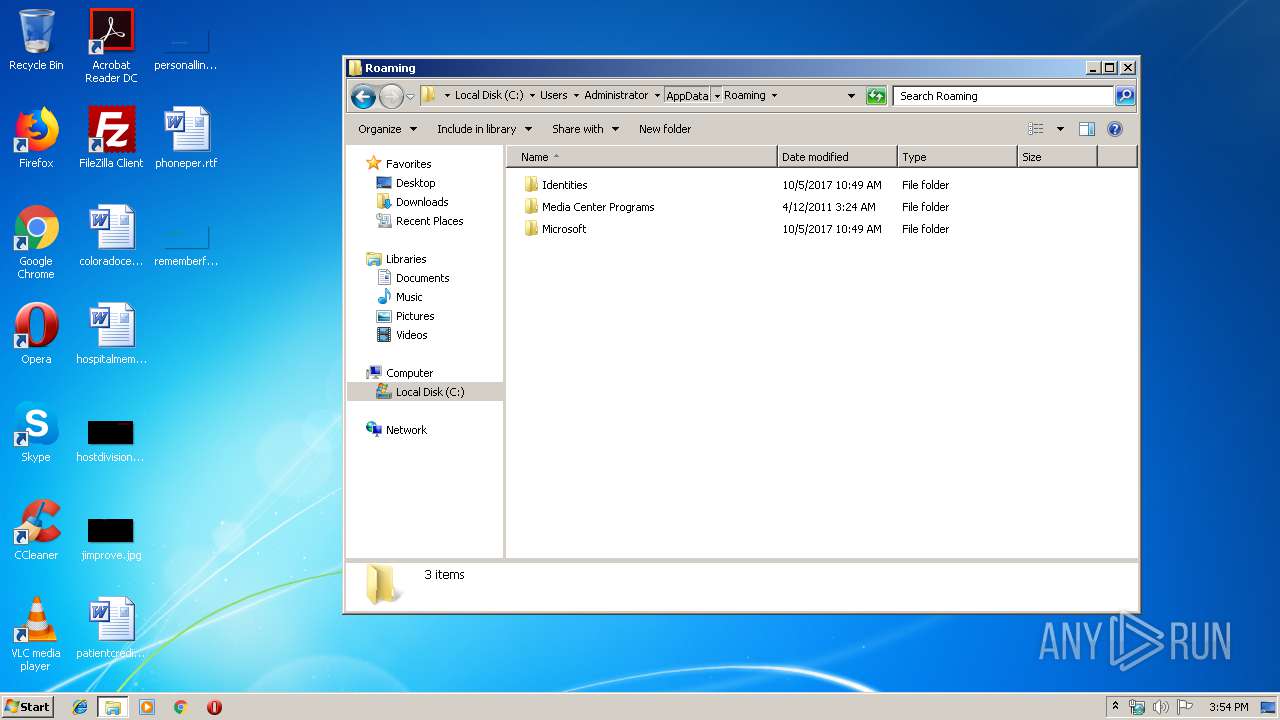
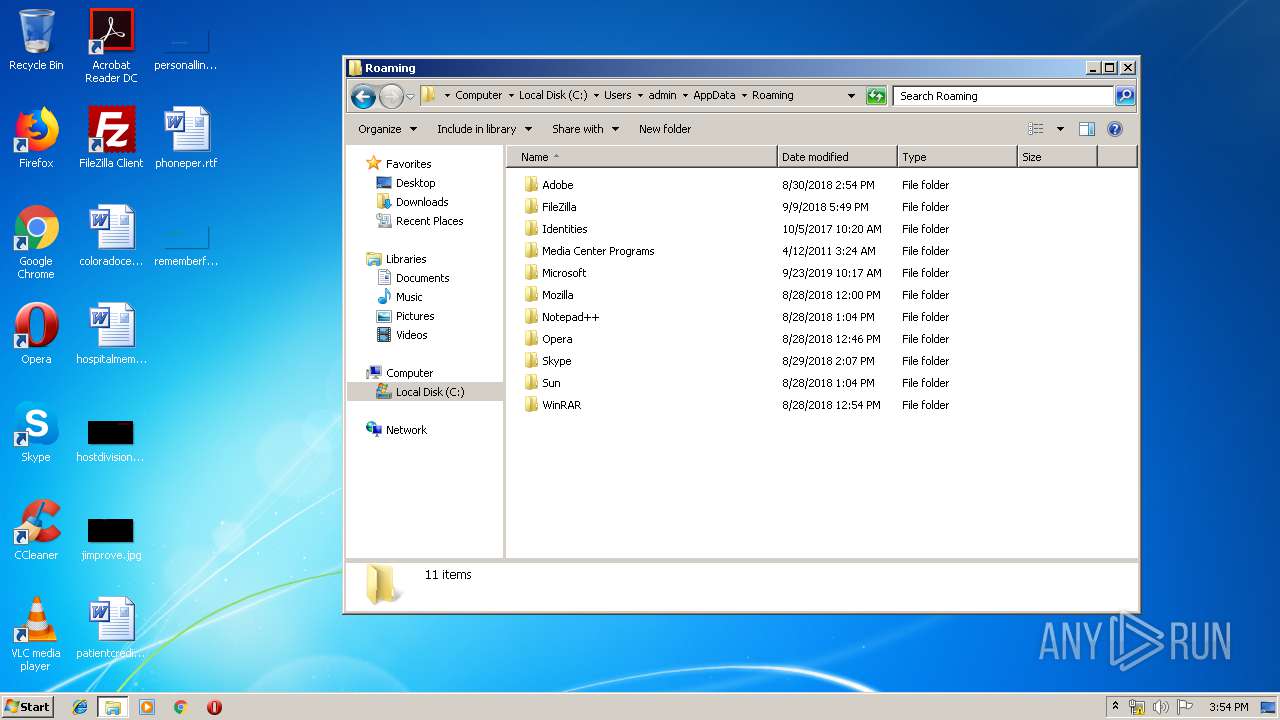
| 3312 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\session.xml | text | |
MD5:— | SHA256:— | |||
| 2200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\bc5d3e35-6119-4f82-b836-03ee7989df7b.tmp | — | |
MD5:— | SHA256:— | |||
| 2200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF3ccd5e.TMP | text | |
MD5:— | SHA256:— | |||
| 2200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF3ccd9c.TMP | text | |
MD5:— | SHA256:— | |||
| 3312 | notepad++.exe | C:\Users\admin\AppData\Roaming\Notepad++\config.xml | xml | |
MD5:— | SHA256:— | |||
| 2200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2200 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF3ccd5e.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
41
DNS requests
23
Threats
31
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
2004 | easywindow.exe | POST | — | 179.62.18.56:443 | http://179.62.18.56:443/free/report/add/merge/ | AR | — | — | malicious |
2004 | easywindow.exe | POST | — | 203.150.19.63:443 | http://203.150.19.63:443/results/ban/add/ | TH | — | — | malicious |
592 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 511 b | whitelisted |
592 | chrome.exe | GET | 302 | 216.239.32.21:80 | http://virustotal.com/ | US | — | — | whitelisted |
2004 | easywindow.exe | POST | — | 194.50.163.106:8080 | http://194.50.163.106:8080/scripts/cookies/add/ | NL | — | — | malicious |
592 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 516 b | whitelisted |
2004 | easywindow.exe | POST | — | 148.240.52.172:80 | http://148.240.52.172/loadan/scripts/ | MX | — | — | malicious |
2004 | easywindow.exe | POST | — | 186.93.167.147:443 | http://186.93.167.147:443/report/sess/ | VE | — | — | malicious |
388 | easywindow.exe | POST | — | 179.62.18.56:443 | http://179.62.18.56:443/merge/stubs/add/merge/ | AR | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2004 | easywindow.exe | 148.240.52.172:80 | — | Axtel, S.A.B. de C.V. | MX | malicious |
2004 | easywindow.exe | 162.214.27.219:7080 | — | Unified Layer | US | malicious |
2004 | easywindow.exe | 194.50.163.106:8080 | — | CJ2 Hosting B.V. | NL | malicious |
2004 | easywindow.exe | 216.154.222.52:7080 | — | Packet Host, Inc. | US | malicious |
2004 | easywindow.exe | 203.150.19.63:443 | — | Internet Thailand Company Limited | TH | malicious |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
388 | easywindow.exe | 148.240.52.172:80 | — | Axtel, S.A.B. de C.V. | MX | malicious |
592 | chrome.exe | 216.58.207.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
592 | chrome.exe | 216.58.207.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
592 | chrome.exe | 172.217.16.163:443 | www.google.com.ua | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
notepad-plus-plus.org |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2004 | easywindow.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
2004 | easywindow.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2004 | easywindow.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2004 | easywindow.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
2004 | easywindow.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2004 | easywindow.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
2004 | easywindow.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
2004 | easywindow.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
2004 | easywindow.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 17 |
2004 | easywindow.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
18 ETPRO signatures available at the full report
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|